
Online disclaimer for Gooken
Firewall linfw3 from year 2010: End of trojans, spyware and hacker for Linux-PC
With our online excusion your PC (and Smartphone) will get allround protected !
 Worth at mind report from uncut-news.ch: Worth at mind report from uncut-news.ch:
Principles For Anonymizing Your Online Activity, uncut-news.ch, 11.20.2023
A beginner´s guide to protecting your identity online.
By default, almost everything you do online is tracked. Your browsing activity is linked to an Internet Protocol (IP) address that’s associated with your physical location and your internet service provider (ISP). And the accounts you create to access online services are often associated with your real identity.
Not only does this allow private companies to surveil your online activity but there are usually no technical barriers in place that prevent them from willingly or inadvertently ...
[...] 1: Separate your anonymous activities from your real identitity.
[...] 2: Mask your IP-address.
[...] 3: Hide your E-Mail-address.
[...] 4: Hide your personal onlince-accounts
Principles for advanced users to achieve anonymity in the internet
[...] 1: Hide your telephone number.
[...] 2: Stop the data transfer from your operating system to Big Tech.
Google Android, Windows, macOS und iOS dominieren den Markt für Betriebssysteme und alle vier senden regelmäßig Daten an ihre Erfinder - Apple, Google und Microsoft. Durch die Verwendung eines datenschutzfreundlichen Betriebssystems können Sie den Datenfluss von Ihrem Betriebssystem zu diesen Big-Tech-Unternehmen unterbrechen und Ihre Anonymität und Privatsphäre verbessern.
[...] 5: Use crypto-currencies for anonymous payments.
[...] 6: Mask your identitiy by an anonymous private limited company (LLC).
[...] Nevertheless you have to care for the separation of your anonymous activities from your real identity!
Quelle: https://reclaimthenet.org/online-anonymity-principles
https://uncutnews.ch/grundsaetze-zur-anonymisierung-ihrer-online-aktivitaeten/
Computer technology - mobil phone
The most dangerous technology ever invented - partl II, Artur Firstenberg, uncut-news.ch, 10.31.2021
[...] Die größte Lüge ist, dass es sich hierbei um "stromsparende" Geräte handelt, und dass; sie deshalb sicher sind. Das ist eine doppelte Lüge. Es ist eine Lüge, weil sie nicht stromsparend sind. Wenn Sie ein Mobiltelefon - egal welches - in der Hand oder an Ihren Körper halten, werden Sie von Ihrem Telefon mit mehr Mikrowellen bestrahlt als von jedem Mobilfunkmast und mit zehn Milliarden Mal mehr als von der Sonne, der Milchstraße oder anderen natürlichen Quellen. Die von der Federal Communications Commission* festgelegten Expositionsrichtlinien spiegeln diese Realität wider: Mobilfunkmasten dürfen Ihren Körper mit einer festgelegten Absorptionsrate von 0,08 Watt pro Kilogramm belasten, während Mobiltelefone Ihr Gehirn mit einer spezifischen Absorptionsrate von 1,6 Watt pro Kilogramm belasten dürfen, was dem Zwanzigfachen dessen entspricht.
https://uncutnews.ch/die-gefaehrlichste-technologie-die-jemals-erfunden-wurde-teil-ii/
Gooken - independent - fairminded - impartial - facts based - opinion friendly
Gooken: Meta and local Search engine - Online Excurs IT Security / information technology and society - News &Links
Reports from our websides must not present our opinion, Red., Gooken, 2017.
 Again (for the forth time ..., 81/82/83, ...) weaseling, surface covering US-INVASION ( with our online-excursion we get more or less prepared ...) ! Again (for the forth time ..., 81/82/83, ...) weaseling, surface covering US-INVASION ( with our online-excursion we get more or less prepared ...) !
Defendeded object and its main component
PC: (configured) UNIX/Linux with Full System Encryption (FSE), TOR, firejail (Sandbox), Pale Moon (Browser) and iptables/ebtables/arptables/nftables (->, firewall like linfw3 (by Gooken))
Smartphone: Orbot (TOR with VPN and VPN-Firewall), system security settings, Firefox nightly (Firefox still with about:config)
Internet search engine: Gooken and (perhaps) further more
 Censorship instead of protection: VPNs do block uncutnews.ch and other israeli-crirtical contents and websites Censorship instead of protection: VPNs do block uncutnews.ch and other israeli-crirtical contents and websites, uncut-news.ch, 09.24.2025
VPN underer controle: How israeli-critital contents are gaged
IMore and more reader complain, that our webseite can not be called by VPN.
Who does control the most poputlar VPNs?
Schätzungsweise 1,6 Milliarden Menschen weltweit verlassen sich auf VPN-Dienste, um ihre Privatsphäre zu schützen und zensurfreie Zugänge zum Internet zu erhalten. Doch nur wenige wissen, dass einige der bekanntesten VPNs - darunter ExpressVPN, CyberGhost und Private Internet Access - längst in den Händen von Kape Technologies sind, einem Unternehmen mit engen Verbindungen zu israelischen Geheimdiensteinheiten wie Unit 8200 und Duvdevan.
Was du jetzt tun kannst
Teste deinen VPN bewusst mit Seiten, von denen du weißt, dass sie oft zensiert werden (z. B. UncutNews). Funktioniert der Zugriff? Wenn nicht, Alarmstufe Rot.
Sieh dir Eigentumsverhältnisse an, z. B. wer hinter dem VPN steht, wer in der Holding sitzt.
Achte auf unabhängige Audits und Transparenzberichte - insbesondere Daten zur Zensur, Sperrung von Inhalten, Mitwirkung mit Geheimdiensten.
Verteile Risiko: Nutze nicht "nur ein VPN". Ergänze durch Tor, verschlüsselte Tunnel, eigene Infrastruktur, alternative Dienste - je nach Bedrohungslage.
https://uncutnews.ch/zensur-statt-schutz-vpns-blockieren-uncutnews-ch-und-andere-israel-kritische-inhalte-und-webseiten/
https://uncutnews.ch/zensur-statt-schutz-warum-viele-vpns-inzwischen-fragmente-staatlicher-kontrolle-sein-koennten-proton-nordvpn-co-wer-bietet-echten-datenschutz/
https://uncutnews.ch/mullvad-tarnt-wireguard-uber-quic-sodass-vpn-verkehr-wie-normaler-internettraffic-aussieht-und-zensur-sowie-sperren-umgeht/
 Zensur statt Schutz: VPNs blockieren uncutnews.ch und andere Israel-kritische Inhalte und Webseiten, Zensur statt Schutz: VPNs blockieren uncutnews.ch und andere Israel-kritische Inhalte und Webseiten, uncut-news.ch, 24.09.2025
VPN unter Kontrolle: Wie Israel-kritische Stimmen mundtot gemacht werden
Immer mehr Leser beklagen sich, dass unsere Webseite mittels VPN nicht aufrufbar ist.
Wer kontrolliert die beliebtesten VPNs?
Schätzungsweise 1,6 Milliarden Menschen weltweit verlassen sich auf VPN-Dienste, um ihre Privatsphäre zu schützen und zensurfreie Zugänge zum Internet zu erhalten. Doch nur wenige wissen, dass einige der bekanntesten VPNs - darunter ExpressVPN, CyberGhost und Private Internet Access - längst in den Händen von Kape Technologies sind, einem Unternehmen mit engen Verbindungen zu israelischen Geheimdiensteinheiten wie Unit 8200 und Duvdevan.
Ein Bericht von MintPress News (Alan Macleod, 2024) legt detailliert dar, wie dieses Firmengeflecht aus ehemaligen Militärs, Geheimdienstlern und einem dubiosen Unternehmer-Imperium entstanden ist.
Israel-kritische Webseiten verschwinden hinter dem VPN
Was Nutzer eigentlich als Schutz vor Überwachung sehen, entpuppt sich zunehmend als Zensur-Werkzeug: Immer mehr Anwender berichten, dass israelkritische Webseiten mit aktiviertem Expres
ExpressVPN oder anderen Kape-Produkten nicht mehr erreichbar sind - obwohl diese Seiten ohne VPN problemlos laden.
Damit wird das Grundprinzip des VPN ad absurdum geführt: Statt den Zugang zu sichern, filtert der Anbieter.
Von Webseiten zu Social Media: Telegram &Co. betroffen
Die Folgen reichen weit über klassische Webseiten hinaus. Wer über diese VPNs Telegram-Kanäle aufruft, die kritisch über Israel, Gaza oder Palästina berichten, stellt fest: Kanäle verschwinden, Inhalte laden nicht, Zugänge brechen ab.
Das Gleiche kann auch Facebook, Instagram oder X betreffen. Durch die vollständige Kontrolle über den Datenverkehr könnten diese VPNs nicht nur blockieren, sondern auch Metadaten über Nutzeraktivitäten sammeln - und damit Aktivisten, Journalisten oder einfache Kritiker identifizierbar machen.
Immer mehr Nutzer schlagen Alarm
Die Zahl der Erfahrungsberichte wächst: In Foren, Kommentaren und privaten Gruppen melden Menschen, dass mit aktiviertem ExpressVPN oder CyberGhost kritische Inhalte verschwinden, während sie ohne VPN normal zugänglich sind.
Diese Beobachtungen passen exakt zu den Befürchtungen, die MintPress News beschreibt: VPNs könnten zum verlängerten Arm staatlicher Zensur und Überwachung werden.
Eigene Erfahrungen bei uncutnews.ch
Auch wir von uncutnews.ch haben bereits zahlreiche Mails von Lesern erhalten, die berichten, dass unsere Seite über bestimmte VPNs nicht erreichbar ist. Ebenso melden Nutzer, dass unser Telegram-Kanal nicht mehr vorgeschlagen wird - ein klarer Hinweis auf Shadowbanning.
Das bedeutet: Nicht nur kritische Webseiten, auch ganze alternative Medienplattformen werden so gezielt in ihrer Reichweite eingeschränkt.
Warnung an die Nutzer
Wer glaubt, mit einem VPN automatisch sicher zu sein, täuscht sich. Wenn die Anbieter selbst eng mit Geheimdiensten verknüpft sind, besteht die Gefahr, dass man ihnen die eigenen Daten und Kommunikationswege freiwillig in die Hände spielt.
Besonders Aktivisten, Journalisten und politisch engagierte Nutzer sollten deshalb Vorsicht walten lassen.
Die klare Botschaft lautet: Finger weg von Kape-VPNs wie ExpressVPN, CyberGhost oder Private Internet Access.
https://uncutnews.ch/zensur-statt-schutz-vpns-blockieren-uncutnews-ch-und-andere-israel-kritische-inhalte-und-webseiten/
 The wide network of israeli spy-technologiy behing the modern surveillance state The wide network of israeli spy-technologiy behing the modern surveillance state, uncut-news.ch, 08.08.2025
Nate Bear via IDo Not Panic!
Secret agencies/NSA/Surveilance/BigData, Surveilance
Quelle (source in english): https://reclaimthenet.org/germanys-mass-surveillance-plan
https://uncutnews.ch/deutschland-wendet-sich-mit-einem-weitreichenden-ueberwachungsgesetz-vom-jahrzehntealten-schutz-der-privatsphaere-ab/
 The background behind harmless phone ringing often is fraud The background behind harmless phone ringing often is fraud
ACTUAL FRAUD WARNINGS
Calls from Austria: This is more behind +43-numbers, netzwelt.de, 09.04.2025 at 08:21 o´clock
Gerrit Gerbig
Actually there are more and more messages in Germany about calls from Austrria - what can be recgonized by the prefix phone number +43. Whenever you accept the call, you can loose plenty of money.
The amount of fraudulent calls by +43-numbers are increasing day by day.
Fraud attempts are very often the background behind them.
[...] Problems with the PayPal-account
[...] Crypto-Scam
[...] Aggrressive advertisment
Do avoid these numbers.BR>
Spam Calls: Behind this ten numbers are frauds hiding
Phone fraud
Attention before unknown numbers! The background behind harmless phone ringing often is fraud.
Actually an increasing amount of numbers with prefix number +48 are calling in Germany. The background of dubios calls from Poland is shown on https://www.netzwelt.de/news/244868-anruf-polen-steckt-plus-48-nummern.html
Similar calls are from Great Britain, Hamburg, Düsseldorf, Mönchengladbach and the netherlands.
Netherlands- https://www.netzwelt.de/news/230550-nervtoetende-anrufe-niederlande-steckt-hinter-31-nummern.html
England - https://www.netzwelt.de/news/235752-telefonterror-england-steckt-hinter-diesen-plus-44-nummern2207.html
Düsseldorf - https://www.netzwelt.de/news/244266-achtung-spam-calls-0211-nummern-gefaehrlich2107.html
Mönchengladbach - https://www.netzwelt.de/news/243950-rangehen-steckt-nummer-moenchengladbach2207.html
Polen - https://www.netzwelt.de/news/244868-anruf-polen-steckt-plus-48-nummern.html
https://www.netzwelt.de/news/236487-anrufe-oesterreich-steckt-hinter-plus-43-nummern2407.html
 Some years ago: ALL SMARTPHONES WITHOUT (spy-free virtual) KEYBOARD ! Some years ago: ALL SMARTPHONES WITHOUT (spy-free virtual) KEYBOARD !
Beware your smartphone-keyboard for transfering data to server, especially keystrokes!
In this excusion we recommend "Simple Keyboards", but there are two Apps in this name. As we notced in spite of blocked Wifi and mobile in system-settings->data usage the data-transfer in the size of many KB of one of both, we clarify the App we mean: Simple Keyboards (821 KB Apk) from Raimondas Rimkus and not Simple Keyboards (34 MB Apk) from Simple Mobile Tools !, gooken, 07.30.2025.
 Smartphone: Orbot Smartphone: Orbot
The previous version from July 2025 from apkcombo.com blocked the traffic of too many blocked Apps in the net, what caused in the local DNS, if set to 127.0.0.1 (localhost, Orbot-TorDNS).
This version (almost) solved this problem:
Orbot latest version, https://www.heise.de/download/product/orbot-93611/download
There the size of the Apk increased from around 20 MB to over 130 MB. So this version might provide new and overworked Android-librariries too, Gooken, rem., the red., 08.03.2025.
 An old friend of mine recommended the messenger Ginlo ( once ) from the Deutschen Post AG An old friend of mine recommended the messenger Ginlo ( once ) from the Deutschen Post AG, gooken, 05.12.2024
...
- End-tou-end-encryption with encrypted storage of all the news on the server.
- made in Germany, the server is not in the USA, but in Germany: confrom with the DSGVO
...
-- but: company from Munich instaed of Deutsche Post AG, like WhatsApp closed source, NO OpenSource!
USA/The Empire
Data collection centers, KI
At heart you will disappear
All you can do, in order to become a suspicious person marked for surveillance to get put into the surveillance list of the government, is live in the United States of America
Watchlisted: Probably you are listed withn the extremist list of the government, T.H.G., uncut-news.ch, 01.29.2024
Von Tyler Durden
Verfasst von John & Nisha Whitehead über das Rutherford Institute
"In einer geschlossenen Gesellschaft, in der jeder schuldig ist, ist das einzige Verbrechen, erwischt zu werden."
Hunter S. Thompson
Dem FBI zufolge sind Sie möglicherweise ein Anti-Regierungs-Extremist, wenn Sie:
a) eine Bibel oder andere religiöse Materialien gekauft haben,
b) Begriffe wie "MAGA" und "Trump" verwendet haben,
c) bei Dick´s Sporting Goods, Cabela´s oder Bass Pro Shops eingekauft haben,
d) Tickets für Reisen mit dem Bus, Auto oder Flugzeug gekauft haben,
e) alle der oben genannten Punkte.
Wenn Sie in den letzten Jahren eine dieser Optionen gewählt haben, stehen Sie wahrscheinlich bereits auf einer Beobachtungsliste der Regierung.
So weit ist das Netz der Regierung bei der Verfolgung von Extremisten im Inland gespannt.
Wir sind jetzt alle Freiwild, leichte Ziele für die Aufnahme in die eine oder andere FBI-Beobachtungsliste.
Wenn das FBI Banken und andere Finanzinstitute auffordert, stichprobenartig Untersuchungen bei Kundentransaktionen durchzuführen - ohne Berechtigung und ohne wahrscheinlichen Grund - nach "Extremismus"-Indikatoren, die im Großen und Ganzen darauf basieren, wo Sie einkaufen, was Sie lesen und wie Sie reisen, dann sind wir das alle in Schwierigkeiten.
Natürlich müssen Sie nichts Illegales tun.
Sie müssen nicht einmal die Autorität der Regierung in Frage stellen.
Offen gesagt, Sie müssen sich nicht einmal für Politik interessieren oder etwas über Ihre Rechte wissen.
Alles, was Sie tun müssen, um als verdächtige Person eingestuft, zur Überwachung markiert und schließlich auf eine Überwachungsliste der Regierung gesetzt zu werden, ist in den Vereinigten Staaten zu leben.
So einfach ist es, mit den vielen roten Fahnen der Regierung in Konflikt zu geraten.
Um auf einer Überwachungsliste der Regierung zu landen oder einer verschärften Kontrolle unterworfen zu werden, muss man heutzutage nur bestimmte Auslösewörter (wie Wolke, Schwein und Piraten) verwenden, im Internet surfen, mit einem Mobiltelefon kommunizieren, hinken oder stottern, Auto fahren, in einem Hotel wohnen, an einer politischen Kundgebung teilnehmen, sich in den sozialen Medien äußern, psychisch krank erscheinen, im Militär dienen, einem Strafverfolgungsbeamten widersprechen, sich bei der Arbeit krank melden, Material in einem Baumarkt kaufen, Flug- oder Bootsfahrunterricht nehmen, verdächtig erscheinen, verwirrt oder nervös wirken, zappeln oder pfeifen oder schlecht riechen, in der Öffentlichkeit mit einer Spielzeugwaffe oder etwas, das einer Waffe auch nur im Entferntesten ähnelt (z. B. einer Wasserdüse oder einer Fernbedienung oder einem Gehstock), einen Polizeibeamten anstarren, die Autorität der Regierung in Frage stellen oder den Anschein erwecken, für Waffen oder die Freiheit zu sein.
Wir gelten jetzt alle als schuldig, bis unsere Unschuld bewiesen ist.
Es ist nur eine Frage der Zeit, bis Sie zu Unrecht beschuldigt werden und von der Polizei auf der Grundlage eines datengesteuerten Algorithmus oder einer Risikobewertung, die von einem mit künstlicher Intelligenz betriebenen Computerprogramm erstellt wurde, untersucht und konfrontiert werden.
[...] Um auf einer Überwachungsliste der Regierung zu landen oder einer verschärften Kontrolle unterworfen zu werden, muss man heutzutage nur bestimmte Auslösewörter (wie Wolke, Schwein und Piraten) verwenden, im Internet surfen, mit einem Mobiltelefon kommunizieren, hinken oder stottern, Auto fahren, in einem Hotel wohnen, an einer politischen Kundgebung teilnehmen, sich in den sozialen Medien äußern, psychisch krank erscheinen, im Militär dienen, einem Strafverfolgungsbeamten widersprechen, sich bei der Arbeit krank melden, Material in einem Baumarkt kaufen, Flug- oder Bootsfahrunterricht nehmen, verdächtig erscheinen, verwirrt oder nervös wirken, zappeln oder pfeifen oder schlecht riechen, in der Öffentlichkeit mit einer Spielzeugwaffe oder etwas, das einer Waffe auch nur im Entferntesten ähnelt (z. B. einer Wasserdüse oder einer Fernbedienung oder einem Gehstock), einen Polizeibeamten anstarren, die Autorität der Regierung in Frage stellen oder den Anschein erwecken, für Waffen oder die Freiheit zu sein.
Wir gelten jetzt alle als schuldig, bis unsere Unschuld bewiesen ist.
Es ist nur eine Frage der Zeit, bis Sie zu Unrecht beschuldigt werden und von der Polizei auf der Grundlage eines datengesteuerten Algorithmus oder einer Risikobewertung, die von einem mit künstlicher Intelligenz betriebenen Computerprogramm erstellt wurde, untersucht und konfrontiert werden.
[...] Entscheidend wird sein, was die Regierung - oder wer auch immer gerade das Sagen hat - denkt. Und wenn die Machthaber der Meinung sind, dass Sie eine Bedrohung für die Nation sind und eingesperrt werden sollten, dann werden Sie eingesperrt und haben keinen Zugang zu den Schutzmaßnahmen, die unsere Verfassung vorsieht.
Im Grunde genommen werden Sie verschwinden.
Quelle (source in english): https://www.zerohedge.com/political/watchlisted-youre-probably-already-government-extremism-list
https://uncutnews.ch/watchlisted-wahrscheinlich-stehen-sie-schon-auf-einer-extremismusliste-der-regierung/
The digital revolution was a disastrous mistake, uncut-news.ch, 10.28.2024
Paul Craig Roberts
Quelle: The Digital Revolution Was a Disastrous Mistake, https://www.paulcraigroberts.org/2024/10/23/the-digital-revolution-was-a-disastrous-mistake-2/
https://uncutnews.ch/die-digitale-revolution-war-ein-verhaengnisvoller-irrtum/
Wiretaps exposed: How encryption backdoors open the floodgates for hackers, uncut-news.ch, 10.28.2024
reclaimthenet
Geheimdienste/NSA/Überwachung/BigData
Quelle: https://reclaimthenet.org/wiretaps-exposed-how-encryption-backdoors-open-the-floodgates-for-hackers
https://uncutnews.ch/wiretaps-exposed-wie-verschluesselungs-hintertueren-den-hackern-tuer-und-tor-oeffnen/
This only works out to reliable with highly respected standards
Emergency rescue fails in many regions in Germany,tagesschau.de, 07.16.2024
In emergencies the chance to survive is very different the region. A reason for this are large differences in quality in the procdure of rescue. Report from J. Russezki, M. Krämer, P. Hünerfeld and L. Kube.
[...] A weak point are the Emergency Operations Centers. They have to react fast during a recognized cardiovascular desease. This only can be prevented with highly respected starndards.
https://www.tagesschau.de/wissen/gesundheit/notfallrettung-100.html
Gooken
Recognized well (... but can you tell us date and time again for noticing it?)!
"Better blau (english: drunken) than gray...", / "Lieber blau als grau", from today I´m extrabreit the 80th
"What shall we do? People vote the mafia!", a fireman meant to us the 80th too.
"Because we are all so greedy", a west-german bankier confessed in one of our following reports. We dare to explore this fact in the mainstream like tagesschau.de, ferner netzpolitik.org, FOCUS Online, Spiegel Online, "die Zeit", "SZ" bzw. PCWelt und Chip.de and further on as much as in the stream uncut-news.ch and epochtimes.de. .
Neuer Höchstwert durch Waldbrände
Bislang 660.000 Hektar in Europa verbrannt, tagesschau.de, 14.08.2022
Noch immer lodern in Europa verheerende Waldbrände und hinterlassen verkohlte Landschaften. In diesem Jahr sind bereits 660.000 Hektar Land verbrannt - ein neuer Höchstwert. Dabei ist die Brandsaison noch lange nicht vorbei.
Durch die verschiedenen Großfeuer in Europa sind in diesem Jahr bereits rund 660.000 Hektar Land verbrannt - der höchste Wert seit Beginn der Aufzeichnungen im Jahr 2006.
https://www.tagesschau.de/ausland/europa/waldbrand-europa-rekord-hitze-klima-101.html
Umsagter Feuerwehrmann verlor Jahre spä,ter beide Beine. Angeblich Raucherbeine, Anm., Gooken.
Please notice the next hyperlink (!!!), rem., Gooken, the edit. :
Onlinehändler Temu unterschreibt Unterlassungserklärung, spiegel.de
Wegen manipulativen Designs und irreführender Rabatthöhen wurde die Shopping-App Temu von der Verbraucherzentrale abgemahnt. Künftig will der Billiganbieter auf derartige Tricks verzichten.
https://metager.de/partner/r?link=https%3A%2F%2Fwww.spiegel.de%2Fwirtschaft%2Funternehmen%2F
temu-onlinehaendler-unterschreibt-unterlassungserklaerung-verzicht-auf-irrefuehrende-tricks-a-ab23def5-8ac9-471f-889a-9ab459fd2786
&affillink=https%3A%2F%2Ftatrck.com%2Fredir%2FclickGate.php%3Fu%3Du68EH62H%26p%3DbnV328d8N7%26m%3D30%26url%3Dhttps%253A%252F%252Fwww.spiegel.de
%252Fwirtschaft%252Funternehmen%252Ftemu-onlinehaendler-unterschreibt-
unterlassungserklaerung-verzicht-auf-irrefuehrende-tricks-a-ab23def5-8ac9-471f-889a-9ab459fd2786%26s%3D
metager_de&password=7fdf508b5cdb46c3a6fb7b873982c22143c5e01d21bfb0d743d3d35e92f5617a
Welcome, "Willy, go!"
"More respect for one old people´s nurse than for the bosses from industry all together", seen in the Facebook-Profil from a Maja Schmidt, 01.18.2021
"Each old people´s nurse does perform more than all investment bankers together."
Passage from Stefan Klein of today I´m extrabreit in year 1986: "Amis forces us to buy, all the scrap, that we don´t need."
Der insanity of the world: The decline of tthe TPTB (the powsers, that be): nuclear power stations, weapon deals, environmenet pollution, corruption, lubbyism, ...: The reigning class smells its decline approching - and wants to cause msichief as much as possible, Kolumne, Spiegel Online, 08.24.2015
All people confident with the 80th know, that USA is a criminal state, who takes his superiority ... / Allen mit der Geschichte der vergangenen 80er Jahre vertrauten denkenden Menschen ist doch bekannt, dass die USA ein verbrecherischer Staat ist, der seine Übermacht mit ..."
www.compact-online.de/us-strategie-weltpolizei-oder-beobachtender-raushalter
The "european leader" are ready to destroy their own continent, in order to please their american masters
Past France, Netherlands are ready to send their amriy to Ukraine, uncut-news.ch, 29.02.2024
dissident.one
Krieg/Kriegsverbrechen/Militär/Armee/Rüstung
Quelle: https://dissident.one/nederland-bereid-om-troepen-te-sturen-naar-oekraine
https://uncutnews.ch/nach-frankreich-niederlande-zu-truppenentsendung-in-die-ukraine-bereit/
Focus, August 2014: The former ARD-Tagesschau-spokeswoman Eva Hermann bloggs for the russion sender "Voice of Russia". In her newest article she explains, why war between the great power USA and Russland were implaceable. The reason: "They certain need money - for what they would do everything. Bankrupt USA provokate Russia so long, until war takes place.", click here
Reagan´s world of starving bank directors and weeping bailiffs (-> Rio Reiser the 80th)
Because of high demand - empty store in Eastern Gemany: Russia discount must close temporarily for the next time, STERN.de, 02.04.2019
Aus seiner (Reagans´) Welt der hungernden Bankdirektoren und weinenden Gerichtsvollzieher, Rio Reiser, the 80th
 ... and if, such decades ago, even my own mother meant... / ... und wenn vor Jahrzehnten sogar die eigene Mutter zum Thema Maja Schmidt schon meinte ( ist das aber fertig: die eigene Mutter dann auch noch, das kriegt ihr aber wieder...!):
"We are no present-give-away-institution for the Germans and no social station of the USA. / Wir sind keine Verschenkanstalt (Deutschland, Reagans Westen alias ( das vermeintliche ) Judas Judäa) der Deutschen und keine Sozialstation der USA (Asoziale) !"
... and if, such decades ago, even my own mother meant... / ... und wenn vor Jahrzehnten sogar die eigene Mutter zum Thema Maja Schmidt schon meinte ( ist das aber fertig: die eigene Mutter dann auch noch, das kriegt ihr aber wieder...!):
"We are no present-give-away-institution for the Germans and no social station of the USA. / Wir sind keine Verschenkanstalt (Deutschland, Reagans Westen alias ( das vermeintliche ) Judas Judäa) der Deutschen und keine Sozialstation der USA (Asoziale) !",
dann frage ich mich ( schau an: Die eigene Mutter meinte das allein aus sich heraus sogar, echt Seltenheitswert, da denkt man, das gibts doch wohl gar nicht, die eigene Mutter auch noch ... ), ob und inwiefern das eigentlich nicht stimmt.
Up to now she uses neither smartphone nor computer: This is the best, one can do (if possible). It´s so ridiculous. How right she is !
 1981, 1982, 1983: Der Elefant macht ernst! Inmitten auf dieser ach so verratenen und verkauften Welt: Clever und Smart, USA, N.Y., 1983:Null Problemo: "If you do not know, how to go on, you have two possibilities: either you explode, or you cry for help. / Wenn man nicht mehr weiter weiß, hat man zwei Möglichkeiten: entweder man explodiert oder schreit nach Hilfe"
1981, 1982, 1983: Der Elefant macht ernst! Inmitten auf dieser ach so verratenen und verkauften Welt: Clever und Smart, USA, N.Y., 1983:Null Problemo: "If you do not know, how to go on, you have two possibilities: either you explode, or you cry for help. / Wenn man nicht mehr weiter weiß, hat man zwei Möglichkeiten: entweder man explodiert oder schreit nach Hilfe" (Magnum, TV-Serie, Januar 2016).
Science in comics: When research scientists speak in bubbles, tagesschau.de, 06.12.2023
Ob Atomkraft oder Klimawandel - die Szene der Comiczeichner hat diese Themen für sich entdeckt. Gerade trifft sie sich zum Münchner Comicfestival. Auch Forscher nutzen das Medium, um ihre Inhalte zu erklären.
https://www.tagesschau.de/wissen/forschung/comics-wissenschaft-100.html
Advertisement? Testing out journal!
.. and wer (Gooken) are no advertising space, but a search engine.
Now finally there is a search engine betterr than Google, uncut-news.ch, Dr. Joseph Mercola 07/29/2024
https://uncut-news.ch
It´strange: The author doesn´t mean us, Gooken, remark, the red. .
Gooken - independent - fairminded - impartial - facts based - opinion friendly
Reports from our websides must not present our opinion, Red., Gooken, 2017.
Uncut-news.ch: "We are not supported by clubs, associtains, parties or lobby groups. We do not shift advertisment, we do not annoy with bothersome pop-ups or force our visitors to deactivate the adblocker. Support us for our Independency!"
USA/The Empire - depopulation programs?, from Gooken-News&Links: uncut-news.ch and other news
rC3: Cory Doctorow warns against the "digital equivalents with the atom bomb", trojaner-info.de, 01.03.2020
Der Science-Fiction-Autor Cory Doctorow hat auf dem remote Chaos Communication Congress (rC3) am Sonntag schärfere kartellrechtliche Vorgaben insbesondere für interoperable Online-Dienste gefordert, um den Wettbewerb im digitalen Zeitalter zu erhalten. Mit den fünf Größen des US-Überwachungskapitalismus - Google, Amazon, Facebook, Apple und Microsoft (GAFAM) - seien "die schlimmsten Albträume" der frühen Verfechter von Bürgerrechten im Internet wahr geworden. Ein politisches und rechtliches Gegensteuern sei daher überfällig.
https://www.trojaner-info.de/daten-sichern-verschluesseln/aktuelles/
rc3-cory-doctorow-warnt-vor-digitalen-aequivalenten-der-atombombe-8145.html
"They destroy and rob EVERYTHING !!! The health, peace, children, elder ones, joy, the last shirt!, Pia Berling @ krone.at, 08.21.2020, Profil auf Facebook,
"Versteht ihr Systemschaafe noch immer nicht, woraus es hinausläuft? Das C-Phantom nur ein Vorwand ist, um ALLES zu zerstören?
Ihr Wachkomaschafe werdet euren realen Albtraum noch erleben - aber nur einen Sekundenbruchteil, bis ihr in der wahren Realität- Hölle dieser Welt erwachen werdet.
Abermillionen Menschen werden sterben, abermillionen werden Selbstmord begehen, abermillionen werden ihr Hab und Gut verlieren, abermillionen werden durchdrehen, abermillionen werden verhungern, abermillionen werden dauerhaft krank sein... der Rest, der es überleben und überdauern soll, wird für die Menschenhasser die lebenden Zombies und die Sklaven sein!
Steht endlich auf? Auf was wartet ihr eigentlich noch, dass dies alles nur zu unserem Wohle geschieht, dass Politiker es gut mit uns meinen, dass die Dame oder der Herr bei den Systemmedien euch um 20h die Wahrheit erzählt?! Dass die meisten Ärzte euch etwa heilen wollen, dass Lehrer euch die Wahrheit lehren?
Wissenschaftler über alles erhaben sind?
Ihr erwartet, dass der Pfarrer am Sonntag euch ein Kuschelevangelium predigt - welches weichgespült ist und nicht der Wahrheit entspricht!
Geht raus aus der Wohlfühlzone und schützt wenigstens eure Kinder vor den Menschenfresser und Seelenvernichtern!!"
https://mobil.krone.at/2215247
Computer technology - mobil phone
The most dangerous technology ever invented - partl II, Artur Firstenberg, uncut-news.ch, 10.31.2021
[...] Die größte Lüge ist, dass es sich hierbei um "stromsparende" Geräte handelt, und dass; sie deshalb sicher sind. Das ist eine doppelte Lüge. Es ist eine Lüge, weil sie nicht stromsparend sind. Wenn Sie ein Mobiltelefon - egal welches - in der Hand oder an Ihren Körper halten, werden Sie von Ihrem Telefon mit mehr Mikrowellen bestrahlt als von jedem Mobilfunkmast und mit zehn Milliarden Mal mehr als von der Sonne, der Milchstraße oder anderen natürlichen Quellen. Die von der Federal Communications Commission* festgelegten Expositionsrichtlinien spiegeln diese Realität wider: Mobilfunkmasten dürfen Ihren Körper mit einer festgelegten Absorptionsrate von 0,08 Watt pro Kilogramm belasten, während Mobiltelefone Ihr Gehirn mit einer spezifischen Absorptionsrate von 1,6 Watt pro Kilogramm belasten dürfen, was dem Zwanzigfachen dessen entspricht.
https://uncutnews.ch/die-gefaehrlichste-technologie-die-jemals-erfunden-wurde-teil-ii/
Germany
Bitkom presents numbers and amounts
206 billion Euro harm because of cyber crimes the year, tagesschau.de, 09.01.2023
Durch Diebstahl von IT-Ausrüstung und Daten sowie durch Industriespionage und Sabotage entstehen der deutschen Wirtschaft dieses Jahr 206 Milliarden Euro Schaden. Das ergab eine Bitkom-Umfrage. Immer mehr Attacken kommen aus Russland und China.
https://www.tagesschau.de/wirtschaft/cybercrime-deutschland-100.html
Cybercrime in Germany: eight of ten companies are affected, trojaner-info.de, 12.04.2023
Immer mehr Unternehmen in Deutschland sind von Cybersicherheitsvorfällen betroffen. Laut einer aktuellen Umfrage mussten 81 Prozent der deutschen Unternehmen in den vergangenen zwei Jahren mindestens einmal auf einen gravierenden Sicherheitsvorfall reagieren.
https://www.trojaner-info.de/sicher-anonym-im-internet/aktuelles/cyber-
icherheitsvorfaelle-in-deutschland-acht-von-zehn-unternehmen-betroffen.html
 How I prepare myself for the war, T.H.G., uncut-news.ch, 11.10.2023 How I prepare myself for the war, T.H.G., uncut-news.ch, 11.10.2023
Katastrophen/Krisen/Unfälle/Unglücke
Von Daisy Luther
Wir alle hoffen, dass die Welt wieder einmal einer Kugel ausweicht und nicht in den Dritten Weltkrieg stürzt. Aber es sieht nicht gut aus. Abgesehen von den Spannungen im Nahen Osten, in die wir nicht direkt verwickelt sind, haben die USA gestern Abend als Vergeltung für die jüngsten Angriffe auf amerikanische Soldaten in der Region Luftangriffe in Syrien gegen vom Iran finanzierte Milizen durchgeführt. Und dann ist da noch der Ärger im Innern - wir können uns auf nichts einigen, jeder streitet über Israel gegen Palästina, und diese Einschätzung legt nahe, dass wir auch reif für einen Bürgerkrieg sind.
Das alles liegt natürlich nicht in unserer Hand. Die Entscheidungen, sich an globalen Konflikten zu beteiligen, werden nicht von Leuten wie uns getroffen, und ein Bürgerkrieg ist eine ganz andere Sache. Was kann ein Prepper also tun?
Nun, wir können die Trommeln des Krieges nicht aufhalten, aber wir können uns auf ihn vorbereiten.
Warum ich mich auf den Krieg vorbereite
Ein Freund von mir hat sich mit den Engpässen im Zweiten Weltkrieg beschäftigt, und das ist ein guter Ausgangspunkt. In Amerika waren wir mit der Rationierung von Dingen wie Lebensmitteln, Schuhen, Metall, Papier und Gummi konfrontiert. Priorität hatten die Soldaten, und was übrig blieb, wurde unter den Zivilisten aufgeteilt. Ich bin mir nicht sicher, ob wir dieses Mal genau die gleichen Engpässe haben werden, da der Krieg, wie viele andere Dinge auch, in das digitale Zeitalter übergegangen ist, aber die Soldaten werden immer noch Lebensmittel, Schuhe, Gummiwaren wie Reifen und Metall für die Herstellung von Fahrzeugen und Waffen benötigen.
[...] Kommunikation
Stellen Sie sich vor, Sie befinden sich in einer Situation, in der Sie wissen, dass das Land überfallen wurde, aber die Telekommunikation ausgefallen ist. Ihr Telefon funktioniert nicht, im Fernsehen gibt es keine Nachrichten, und es gibt kein Internet. Sie MÜSSEN in der Lage sein, zu kommunizieren und zu erfahren, was vor sich geht, damit Sie Ihre Familie in Sicherheit bringen können. Sie werden nach Ihren Lieben in der Ferne sehen wollen.
Amateurfunk ist die Antwort. Aden stellt in diesem Artikel einige kostengünstige, einfache Geräte vor. Ich arbeite daran, meine Lizenz zu bekommen, indem ich seinen Studienführer benutze, den ich hier gefunden habe (er ist großartig!), und schließlich kann ich sein Buch über Notfallkommunikation hier lesen.
Quelle: https://www.lewrockwell.com/2023/10/daisy-luther/how-im-prepping-for-war/
https://uncutnews.ch/wie-ich-mich-auf-den-krieg-vorbereite/
Confiscated smartphones: a crime of unknown dimension, netzpolitik.org, 30.10.2023
Den Innenministerien fehlt der Überblick, wie oft ihre Polizeibehörden Smartphones beschlagnahmen. Eine verlässliche Statistik über den tiefen Grundrechtseingriff fehlt. Juristen sehen noch weitere Probleme im Umgang mit der Ermittlungsmaßnahme.
https://netzpolitik.org/2023/beschlagnahmte-smartphones-ein-grundrechtseingriff-unbekannten-ausmasses/
 The most dangerous technology ever invented - partl II, Artur Firstenberg @ uncut-news.ch, 10.31.2021 The most dangerous technology ever invented - partl II, Artur Firstenberg @ uncut-news.ch, 10.31.2021
[...] Die größte Lüge ist, dass es sich hierbei um "stromsparende" Geräte handelt, und daß sie deshalb sicher sind. Das ist eine doppelte Lüge. Es ist eine Lüge, weil sie nicht stromsparend sind. Wenn Sie ein Mobiltelefon - egal welches - in der Hand oder an Ihren Körper halten, werden Sie von Ihrem Telefon mit mehr Mikrowellen bestrahlt als von jedem Mobilfunkmast und mit zehn Milliarden Mal mehr als von der Sonne, der Milchstraße oder anderen natürlichen Quellen. Die von der Federal Communications Commission* festgelegten Expositionsrichtlinien spiegeln diese Realität wider: Mobilfunkmasten dürfen Ihren Körper mit einer festgelegten Absorptionsrate von 0,08 Watt pro Kilogramm belasten, während Mobiltelefone Ihr Gehirn mit einer spezifischen Absorptionsrate von 1,6 Watt pro Kilogramm belasten dürfen, was dem Zwanzigfachen dessen entspricht.
https://uncutnews.ch/die-gefaehrlichste-technologie-die-jemals-erfunden-wurde-teil-ii/
US-West-Nix-Niue (sincet Reagan) - Worse than Stasi ago allowed:
Spongebob - TV-Comic-classic Spongebob Spongebobhead - The Autopilot
Video on Facebook
 "Human trafficking like cattle" "Human trafficking like cattle"
"We, the exploited": on the way to "Soylent Green"!, uncut-news.ch, 11.23.2023
Secret services/NSA/monitoring/bigdata
John Whitehead vividly explains the basic features of the scientific dictatorship and the digital panopticon that forms the control network. The government is the scapegoat for Big Tech, the driving force behind technocracy. You will see how we are made, shaped and pressed into products that are then fed back to ourselves ... like Soylent Green.
Technocrats have used governments to release Tornado´s endless data that are fed into AI programs. Patrick McGoohan, Creator and Star of the Miniserie The Prisoner from 1967, was ahead of his time when he said: “I don´t let myself be pushed, classified, stamping, inducing, letters, questioning or numbering. My life is my life. ”⁃ TN editor
The Americans have become a slight prey for hackers, fraudsters, spies, spies and swindler.
But don´t believe that the government protects it.
On the contrary, the US government sells us (or better our data) to the highest bidder.
Incidentally, these highest bidder also includes America´s political class and the politicians who want to be elected or re -elected. The Los Angeles Times reports: “If you have participated in a political rally or a citizens´ meeting or just fit into the target group of a campaign, the chances are good that your movements will be followed with worrying accuracy of data providers on the list of campaigns stand.
They sell their phones, televisions and digital devices to politicians who want their voice.
“Welcome to the new world of campaign technology, in which downloading a weather app or a game, making a Wi-Fi connection in a café or switching on a router at home can make it easy for a data broker to monitor your movements To collect your location data and sell you to a political candidate who can use them to bomb them with messages, ”writes journalist Evan Halper.
In this way, “we, people”, were degraded into economic units that can be bought, exchanged and sold by everyone and everyone.
Every day, the Americans are forced to reveal the most intimate details of their personality -their biological constitution, their genetic blueprints and their biometric data (facial features and structure, fingerprints, Iris scans, etc.) -to find their way into an increasingly technological world.
In turn, these intimate details have become building blocks of huge databases to which the state and its criminal partners have access to business and which are susceptible to data breakdowns by hackers, cyber attacks and espionage.
For years, the government has been building huge databases with all possible sensitive information about the citizens without real control or restriction.
Biographical information. Biometric data. Prevent. Travel records.
There is no person in the United States who are not recorded in one or the other state database, and these databases are increasingly being used by authorities, merger centers and the police.
In addition, the government has expanded its huge inventory of data about Americans by purchasing commercially available information (Commercial Available Information, CAI) of third -party providers with little control and little guidelines. A report by the Office of the Director of National Intelligence revealed:
[Commercially acquired data] can reveal sensitive and intimate information about personal characteristics, private behavior, social relationships and language of US citizens and non-US citizens. They can be abused to penetrate privacy, ruin the call, cause emotional suffering and to threaten the safety of people. Even if it is subject to adequate controls, the CAI can raise the possibilities of the government to penetrate private life to a level that goes beyond our constitutional traditions or other social expectations.
In other words, it is the devilishly understood way in which the government tries to avoid the fourth constitutional addition that stipulates that government officials must have a sufficient reason and a search order before spying on Americans or browse and confiscated their private property.
It is bad enough that the government creates huge databases with our personal data without our knowledge or our consent, but then they are also hacked and we have to suffer.
At the beginning of this year, for example, several federal
Authorities, state governments and universities aim of a global cyber attack that endangered the sensitive data of millions of Americans.
Did the government prevent this from further expanding these databases that endanger our privacy and security? No of course not.
In fact, the government also sold our private information. According to VICE, the states´ car authorities have sold the personal data of drivers "to thousands of companies across the country, including private investigators who spy on people for payment".
Where a will is, there is also a way and the government is a master in finding loopholes to exploit its citizens.
In 1994 the Congress adopted the Driver´s Privacy Protection Act (DPPA) to prevent the transfer of personal data, but that did not prevent the state traffic authorities from selling millions (names, birth data, addresses and cars, to earn third parties.
This is only a small part of how the state buys its citizens and sells to the highest bidder.
The reason is always the same: it´s about profit and power.
Welcome to the era of surveillance capitalism.
Have you ever bought from Whole Foods? Practiced the target on a shooting range? Drunk a coffee at Starbucks and surfed on the Internet? Visited an abortion clinic? Seen Fox News or MSNBC? Candy Crush played on her cell phone? Schlendert by a shopping center? Passed on a government building?
This is all necessary to collect, sell and use your data to address you.
Incredible: Once you have been identified and persecuted, data dealers can digitally travel back to find out where they were, with whom they were together, what they did, what they read, saw, bought, etc.
As soon as they are identified in this way, they can be followed endlessly.
Nobody is spared.
In this regard, we are all the same: We all suffer from the humiliation that every piece of privacy is stolen from us and the most intimate details of our life become food for marketers and data professionals.
This scary new era of profit -oriented surveillance capitalism, in which we overheard, observe, persecute, cartographed, bought, sell and target, is enabled by our cooperation.
All the exclusions of liability that you fly over, without reading them, which are written in tiny letters, only to quickly click on the "Consent" button so that you can go to the next step - downloading software, opening one Accounts on social media, adding a new app to your telephone or computer - mean that you give your written consent that your activities monitors, recorded and passed on.
Think about it.
Every movement you make is monitored, searched for data, analyzed, analyzed and saved to get an idea of who you are, how you tick and how to best influence and/or control it.
With every smartphone we buy, with every GPS device that we install, with every Twitter, Facebook and Google account that we open, with every customer card with which we go shopping-whether in the supermarket, in yogurt -Saden, at the airline or in the department store- and with every credit or debit card with which we pay for our purchases, we help American companies to create a dossier for their government partners, who we know, how we think, how we think our money Spend and how we spend our time.
The technology is now so far advanced that advertisers (political campaigns are among the worst taverns) actually "digital fences" around their home, their workplace, the houses of friends and relatives and other places they can visit to build them Bombarding with tailor -made messages that aim at a certain result.
If someone was bothering us in this way - by following us at every step, listening to our calls, reading our correspondence, reading, spying on our secrets, creating profiles of us and targeting us because of our interests and activities - we would call the police .
Unfortunately, police officers (who are equipped with Stingray devices and other tensioner technologies) are also involved in this special fraud.
It is not just the surveillance and the purchase and sale of your data that give the reason to worry.
The effects of a government -whatever kind -that has so much unregulated and non -accountable power to pursue their citizens, to pursue, pursue together
And to arrest are more than scary.
Just imagine what a totalitarian regime like Nazi Germany could have done with such a power.
Imagine what the nearest police state will enter into the footsteps of Germany with this type of power. Society definitely moves quickly in this direction.
We made it so easy for the government to monitor ourselves.
The government´s eyes see each of your steps: what you read, how much you spend, where you go, with whom you run with, when you wake up in the morning, what you see on TV and read on the Internet.
Every movement that you make is monitored, searched for data, evaluated, and brought in a table to get an idea of who you are, how to tick and how best to control it if necessary, you to bring on line.
As the Washington Post reports, it is likely that they have already received a color -encoded threat - green, yellow or red - so that the police are informed about their potential tendency to unrest, depending on whether they have had a military career behind them have posted as a threatening comment on Facebook, suffer from a certain illness or know someone who knows someone who might have committed a crime.
In other words: You could already be marked as potentially anti-government in a state database-for example in the main core database-that identifies and persecuted people (to arrest them in an emergency) who do not bow to the police state dictation want.
The government has the know-how.
As The Intercept reports, the FBI, the CIA, the NSA and other government agencies are increasingly in and rely on surveillance technologies of companies that can analyze constitutionally protected statements on social media platforms such as Facebook, Twitter and Instagram to provide potential extremists Identify and predict who could behave hostile to government in the future.
Monitoring, digital stalking and data mining of the American population - weapons of conformity and control in the hands of the government, especially if the government is able to listen to telephone interviews, monitor driving habits, pursue movements, to pursue purchases Control and peek through the walls of the house - lead to a society in which there is little space for indiscretions, imperfections or acts of independence.
This is the uncanny, calculating and at the same time devilish ingenuity of the American police state: the technology that we celebrated as revolutionary and liberating is to our prison, prison attendant, probation helper, stalker, Big Brother and Father - everything in one Person.
As it turns out, we are Soylent Green.
The film of the same name from 1973 with Charlton Heston and Edward G. Robinson in the leading roles plays in 2022 in a overpopulated, dirty and starving New York, the residents of which are dependent on the survival of synthetic food that is made by the Soylent Corporation.
Heston plays a policeman who determines in a murder case and finds out the cruel truth about the main component of Soylent Green, the main source of food for the starving population. "They are people. Soylent Green is made of humans, ”explains Heston´s character. “You make our food out of people. Next they will breed us like cattle to feed us. "
How right he is.
Soylent Green indeed consists of people, or in our case, Soylent Green is our own personal data that is confiscated, re -packed and used by the company and the government to catch us.
We are also bred like cattle, but not to eat.
Rather, as I am in my book Battlefield America: The War on the American People and his fictional counterpart The Erik Blair Diaries, are bought, branded, branded and sold because of our data.
Since the insidious partnership between the US government and the American company becomes more invasive and subtle from day to day, there is practically no way to escape these attacks on digital privacy, unless you are a modern Luddit that is completely decoupled from any technology.
What we urgently need is an "Electronic Bill of Rights" that protects "us, the people" from predatory surveillance and data processing business practices.
Quelle: https://www.technocracy.news/we-the-exploited-slouching-toward-soylent-green/
https://uncutnews.ch/wir-die-ausgebeuteten-auf-dem-weg-zu-soylent-green/
This online-excursion is not suitable much for smartphones. Please start it on a PC!
But if you want to go on with your smartphone inspite of this, your smartphone-browser might still consist of code-errors or code-failures, by not presenting this webside in the full width of 100%. In this case, please touch the free place at the right of the side two times. Now this webside should fullfill the whole screen-width.
 Gooken - the at times breaking full, large "china restaurant"... Do you want the everlasting peace with your computer as a system (backported Fedora Core (fc): updates from year 2010-2026 resp. lifetime) with covering software (backported too) on powersaving and cheap lifetime-hardware, providing the incredible high security level? Contribute to Gooken for the manufacturing of the (consistent) IT-security-standard! For correspondent please click here! Gooken - the at times breaking full, large "china restaurant"... Do you want the everlasting peace with your computer as a system (backported Fedora Core (fc): updates from year 2010-2026 resp. lifetime) with covering software (backported too) on powersaving and cheap lifetime-hardware, providing the incredible high security level? Contribute to Gooken for the manufacturing of the (consistent) IT-security-standard! For correspondent please click here!
Spend or pay Gooken by PayPal.me :
Spend or pay Gooken by Paypal.me: Please click here!
Customer support (this might include customer service and customer care too
The starting situation: The information flow of new hard- and software routes almost to manufacturer, companies and authorities by default (default settings), especially those right from USA (and from itself it might be NY).
Depending on the hard- and software, you as a customer can more or less restrict, even if not forbid this way, but only, if you really want to, by following the steps of our excursion for computer and smartphone ( similar for other devices too) stepwise green hook by hook (what might costs some efforts...).
Notice, that guarantee of manufacturers might run off during it in some, quit seldom cases like unscrewing any devices and unlocking the bootloader of a smartphone, in order to root it.
In advance:
 Who can see your browser history and the websites you visit?, Marko Grjuic, vpnoverview.com, 02.06.2023 Who can see your browser history and the websites you visit?, Marko Grjuic, vpnoverview.com, 02.06.2023
Protect yourself from snoopy eyes online!
Whenever you are online, there are tons of parties trying to spy out you, from Websites, you visit, up to governments and search engines like Google. Even the internet provider can see plenty of what you are doing online. It becomes more and more important to protect from parties, spying you out.
https://vpnoverview.com/de/privatsphaere/anonym-surfen/wer-kann-internetverhalten-browserverlauf-sehen/
 What does your internet provider know about you?, Marko Grujic, vpnoverview.com, 01.10.2023 What does your internet provider know about you?, Marko Grujic, vpnoverview.com, 01.10.2023
He probably knows more about you as you thought of. He sees:
The domains, you visited
The sides you visit (for example the videos, you see)
All information you entered into websites.
There is a simple possibility to protect from spying providers: VPN. A VPN hides the IP-address and encrypts your online data traffic, so that it isn´t readable for your ISP and third parties. More options are:
The usage of a proxy-server
The Tor-Browser
... Tor-Browser: Threefold protection against your ISP?
The Tor-browser is an excellent for protecting privacy. Correctly applied and configured, the ISP can not see anymore, what you are doing only in practice. The Tor-browser leads all internet traffic through three at least three of a high amount of server from all over the world.
At each server (node, relais) the data traffic gets encrypted again, so that the data traffic gets extremly high protected. For even better protection we recommend the combination of Tor and VPN ( ... already both in one: Orbot (Tor), remark, Gooken ).
https://vpnoverview.com/de/privatsphaere/anonym-surfen/was-weiss-ihr-internetdienstanbieter/
From News&Links
Probably satire, remark by Gooken:
A conversation in Davos spyed out in a adjoining room, uncut-news.ch, 15.02.2023
Bill Gates: Diese neue Betrugsdemie - ich meine Pandemie - wird ein echter Humdinger werden.
Klaus Schwab: Ein echtes Prachtexemplar.
Yuval Harari: Was ist ein Humdinger?
Tedros Ghebreyesus: Ein Killer, könnte man sagen. Wir haben die Impfstoffe, die Killshots parat. Und wir werden alle billigen alternativen Therapien, die funktionieren, unterdrücken, verleumden und verbieten - genau wie wir es mit der Covid-Operation getan haben.
Gates: Ganz recht, Tedros, die Impfstoffe sind einsatzbereit! Dieses Mal werden wir vielleicht 2-3 Milliarden durch Impfungen verursachte Todesfälle und Verletzungen erleben. Der Covid-Betrug, ich meine die Pandemie, war eine Aufwärmübung. Alles, was wir jetzt tun müssen, ist, das nächste weltzerstörende Virus anzukündigen. Dabei kann es sich um ein theoretisches Computermodell handeln - genau wie bei Covid-19, das nur als Computersimulation existiert, die von unseren Partnern in China bereitgestellt wurde. Dieser nächste "große katastrophale Virus" wird von… nun, das werden Sie noch früh genug herausfinden.
Albert Bourla (CEO von Pfizer): Absolut fantastisch!
Anthony Fauci: Ich komme dafür aus dem Ruhestand.
Harari: Ich werde ein neues Buch über den unaufhaltsamen Lauf der Geschichte schreiben. Es wird ein weiterer New York Times-Bestseller werden.
Gates: Das Beste von allem ist, dass wir die heilige, heilige, immer schädliche, nicht zugelassene mRNA-Technologie in das Trinkwasser der Welt eingebracht haben.
Quelle: https://www.lewrockwell.com/2023/02/walter-gelles/
conversation-overheard-at-davos-in-a-world-economic-forum-side-room/
https://uncutnews.ch/gespraech-das-in-davos-in-einem-nebenraum-des-weltwirtschaftsforums-mitgehoert-wurde/
Hersh in an interview: "I would ask german chancelor Scholz many questions" uncutnews.ch, 16.02.2023
A worth reading interview with Seymour Hersh by the Berliner Zeitung.
Quelle: Berliner Zeitung and https://www.anti-spiegel.ru/2023/
hersh-im-interview-ich-wuerde-bundeskanzler-scholz-eine-menge-fragen-stellen/?doing_wp_cron=1676550302.6984059810638427734375
https://uncutnews.ch/hersh-im-interview-ich-wuerde-bundeskanzler-scholz-eine-menge-fragen-stellen/
Kim Dotcom: States secrets are onle secret for usual humans, not for the nations involved in the global cyber war, uncut-news.ch, 04.11.2022
"Top secret" doen´t mean for the worldwide best spy agencies anything. Secrecy is only there, in order to keep populates in the dark.
[...] Let me explain it four you:
Alle big technical databases are equipped with backdoors by all the biggest spy agencies. Each smartphone is on open microphone for them. Each computer connectd in the net, gets opened. All important chips and the most hardware gets equipped with trojans. All data, a spy agencies does collect, gets stolen by the others.
The commiters of main events know, that their opponents do know exactly, who it was, and that it is a game, they play against eachother on the costs of normal people getting victims of stupid contests. It is a secret war during the last decades.
In former times I was a hacker, became a consultant for data security, hiring the worldwide best hacker and getting paid by Fortune-500-companies, to hack them. We never got a customer not getting hacked successfully. That is the truth. There does not exist any effective data security. All is wide open.
Spy agenencies with budgets of billions do have programmers in all leading technology companies, building backdoors into programs. It´s impossible to keep them secret. Competing agencies, cybercriminals and security experts find them. For this reason security patches have to be installed again and again.
I know exactly, how this all functions, and as the NSA worked together with the partner agency GCSB in New Zealand, in order to spy out my devices (in a copyright matter), I catched and unmasked them right before law, in order to enforce a change of the law, so that the primary minister has to excuse himself for it in front of my own.
All state leaders are in the visor of the spy technique,and noone else, even not the US-president, does not get eavedropped by serveral foreign and domestic agencies around the clock. Even encrypted devices put state leaders by them at disposal, do have backdoors. That is the reality.
In zero-technolgy-environments some confidential talks are possible, but they belong the the seldom exceptions.
https://uncutnews.ch/kim-dotcom-staatsgeheimnisse-sind-nur-fuer-die-gewoehnlichen-
menschen-geheim-nicht-aber-fuer-nationen-die-in-den-globalen-cyberkrieg-verwickelt-sind/
BSI-update
Cyber security endangers like never before, tagesschau.de, 10.25.2022
https://www.tagesschau.de/inland/bsi-bericht-cybersicherheit-101.html
From News&Links#Windows and News&Links#NSA&Co.
 Allicance: Five Eyes, Nine Eyes, ... Allicance: Five Eyes, Nine Eyes, ...
"We kill people on the base of meta-data"
Hacking and Eavesdropping, netzpolitik.org, 24.02.2020
https://netzpolitik.org/2020/ist-whatsapp-sicher-genug-fuer-die-diplomatie/
https://netzpolitik.org/2020/is-whatsapp-safe-for-diplomats/
Hacking is his job: programmed (in-)security
11KM: the tagesschau-podcast, tagesschau.de, 02.28.2023
Benjamin Gnahm is a hacker, belonging to the international hacker elite. ... Documentation about him: With hacking to the top money earners:
https://1.ard.de/Money_Maker
https://www.ardaudiothek.de/episode/11km-der-tagesschau-podcast/
von-beruf-hacker-programmierte-un-sicherheit/tagesschau/12419277/
Step 1 - Information technology and society - IT security, applied security in the information technology, multiple protection - security in the information technology ( according to theory by Prof. Dr. Kersten, first edition, Oldenbourg Verlag, the 80th - The Basic Security Level, report from Gooken.de, the meta and local internet search engine
Gain your trust back, and gain the trust in you back!
1000% security for your computer:05.26.2020, since 2010: Computer without needing any care: (paranoid-) secure and standarded stable computer-system, self-repairing, free from wide restrictions, total free from maintenance, surface covering opensourced software, with emulators and virtual machines of many operating systems, always mouseclick-fast (free from hacker and trojan etc.), most comfortable, endless durable (lifetimed soft- and hardware), power-saving, free from royalities and all in all (quit) for free; presented by Gooken
COMPROMIZLESS GOOD, SINGLE USER - DESKTOP - CLIENT - SERVER and ROUTER-FIREWALL IN ONE TESTED ON LAN/WAN/GAN - SECURE, TRANSPARENT AND EASY TO HANDLE
For beginners and advanced on their look out for the really secure solution up to the expert for formulation of high-end ones
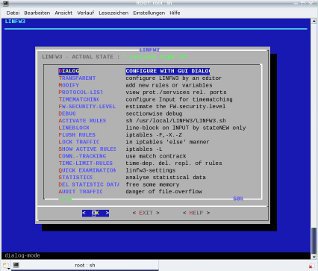
With this firewall you WON´T GET ANY HACKER, TROJANS AND SPYWARE anymore!
The general authorized superuser root (of foreign systems) does not have any rights anymore, what is performed by Linfw3 ! Even the X-Server (X, X11) and all other device drivers can not do any unwanted communication over the net anymore!
Together with it and the steps in this excursion, not any system and user passwords can be cracked anymore, even if known by other ones!
Browser-extensions and settings in user.js free from all tracking scripts, webbugs, adware, localization, unwanted connections and further on, this means from all risks completely for browser like Mozila Firefox and the upon Firefox 29 resp. 36 or Firefox Quantum working, always well patched Pale Moon!
 Online Banking and Online Shopping etc. with internet-browser Pale Moon, Text by Gooken, 06.12.2023 Online Banking and Online Shopping etc. with internet-browser Pale Moon, Text by Gooken, 06.12.2023
Online-Banking und Online Shopping etc. mit dem Internet-Browser Pale Moon
For online banking and shopping like Ebay create one more new profile as free from Pale Moon- and Firefox-extensions as possible.
Für Online-Banking und Online-Shopping etc. wie z.B. auf Ebay empfiehlt sich in Pale Moon die Anlage eines weiteren, neuen Profils frei von Erweiterungen.
Brave Browser
The Web-Browser Brave wants to protect user against tracking through ads too. For the blinding out of the advertisement, Brave uses filter lists like those used by Adblock Plus for all browser. Beyond this Brave offers altenative advertising space marketed by the ad service of the manufacturer of the browser. This ad keeps user data untrackable and he can decide by himself, if he wants to see the ads. If he agrees to see them, he shall party in the earnings of ads. The Brave Browser does his work in Windows, Linux, Mac OS X and Android. It is also possible to download his source (OpenSource, Engine: Chrome).
Quelle: Brave | Heise Download, https://www.heise.de/download/product/brave-97522
Suggestive download size: 270 MB (in comparison with Pale Moon of about 40 MB)...
 Firefox and Google Firefox and Google
Deactivate Safebrowsing in Firefox, wiki.systemli.org
"about:config"
"safebrowsing"
"browser.safebrowsing.enabled" to "false" setzen
"browser.safebrowsing.malware.enabled" to "false"
https://wiki.systemli.org/security/firefox/safebrowsing
We do also recommend the anonymization with Tor (The Onion Router).
Alternatively spend by our bank correspondence see impressum or contact us: You can buy the complete rights of Gooken (over all websides and products) to become its owner for some septrillions per agreement, more details with "News&Links" from left menu!
It might be such an unbearing serious hard imagination for parents small offspings prattling their views and opinions already at school and anywhere...
Stiftung Warentest, TÜV Rheinland, Öko-Test, GS - Checked out Security, AUSTest (for all, that can´t get out of order, lifetime products), ISO-certified company, ISO, DIN, DLG gold, ..., Tagesschau, Spiegel, Stern, ..., OpenSource / LSB-compliance, patent right:
So where the hell is all advertisement (also upon the costs of tax payers) good for, as one can´t imagine better adverstisement?
Tor, The Anonymizing Network - Äh, ... Looking out for GOOD Tor Nodes (entry-, middle- and exit-nodes / relais) now ..., text 2019 by Gooken
How Bill Gates hijacked a failing pharma system and smashed it: A tale of incompetence, deceit, greed, and an unmitigated thirst for power, T.H.G., uncut-news.ch, 03.03.2023
Big-Pharma
All began with strategic incompetence.
Quelle: https://www.ukcolumn.org/article/how-bill-gates-hijacked-a-failing-pharma-system-and-smashed-it-a-tale-of-incompetence
https://uncutnews.ch/wie-bill-gates-ein-gescheitertes-pharmasystem-in-seine-gewalt-brachte-u
nd-es-zerschlug-eine-geschichte-von-inkompetenz-betrug-gier-und-
unbaendigem-machthunger/
British journalist shows CIA directly parted in the foundation of Google, uncut-news.ch, 03.03.2023
"Google fundamentally started as a CIA-Projekt", so the journalist and author of "Propaganda in the information century", Alan MacLeod, who has warned ago, that the relations to the tech-gigants of the secret agencies cause serious hard problems for the freedom of information and opinion.
Quelle: https://www.lifesitenews.com/news/british-journalist-shows-how-
the-cia-played-a-direct-role-in-the-creation-of-google/
https://uncutnews.ch/britischer-journalist-zeigt-wie-die-cia-eine-direkte-rolle-bei-der-gruendung-von-google-spielte/
"We have warned you! Reading further on at your own risk."
"Google knows everything? Yes, and much more!"
Technique
"Data security" - This is, what Google, Facebook and Microsoft really know about you, Epoch Times, 05.18.2019
Schnell etwas googlen, dann hier und da etwas liken und anschließend mit Cortana etwas im Internet bestellen: Alltag für viele Menschen, doch mit jeder Aktion geben wir bereitwillig unsere Daten preis. Wie viel das Internet über jeden einzelnen von uns weiß, ist erschreckend.
Google weiß alles? Ja, und noch viel mehr! Und manchmal weiß Google sogar Dinge, die wir selbst nicht wissen, bestes Beispiel: Was Google tatsächlich über uns weiß. Dieter Bohn, Chefredakteur von "The Verge", formulierte es sehr elegant:
Unsere fortschrittlichen KI-Algorithmen können vorhersagen, welches Auto Sie mieten möchten, und dann das Webformular für Sie ausfüllen. Es weiß, was Sie wollen und tut es einfach."
Mark Vang vom World Community Computing Grid, einem IBM-Projekt, bei dem Menschen der Forschung ihre PCs und Rechenleistung zur Verfügung stellen, ergänzte:
Alle diese Daten, die wir gesammelt haben und weiterhin sammeln, bleiben direkt auf unseren Servern, wo wir sie an jeden verkaufen können … Aber zögern Sie nicht, Ihr Konto jederzeit zu ‚löschen‘."
Wenn Sie einen kostenlosen Service nutzen, sind Sie das Produkt
Doch Google ist nicht der einzige Internet-Riese, der es auf unsere Daten abgesehen hat. Microsoft und Facebook, autonome Fahrzeuge und Smart Homes sammeln ebenso Daten in beträchtlichem Umfang. Wieso? Weil wir, zumindest im Fall Facebook, ihnen bereitwillig alles erzählen, was sie gar nicht wissen wollen - und weil es Geld bringt.
Sie wollen auch wissen, was das Internet über Sie weiß? Die Antwort ist erschreckend.
Wir haben Sie gewarnt! Weiterlesen auf eigene Gefahr.
Dylan Curran, Datenschutzberater für Presearch.org und ehemaliger Berater der Amerikanischen Bürgerrechtsunion ACLU, hat die Daten, die die großen Firmen über ihn gesammelt haben, genauer untersucht. Dies sind seine Ergebnisse:
Bewegungsprofil
Google speichert alle Orte, an denen Sie in den letzten Wochen, Monaten und Jahren waren, wann Sie dort waren und wie viel Zeit Sie benötigt haben, um von einem Ort zum Nächsten zu kommen.
Auch wenn Sie die Geolokalisierung deaktiviert haben, speichert Google die Ortsdaten, die aus anderen Quellen stammen. Dazu zählen unter anderem Information, welches W-LAN-Netz sie nutzen oder Suchanfragen auf Google Maps.
Unter https://www.google.com/maps/timeline?pb können Sie Ihr eigenes Bewegungsprofil abrufen.
Google weiß alles, was sie je gesucht - und gelöscht - haben
Neben Ihrem Bewegungsprofil erstellt Google ein geräteübergreifendes persönliches Suchprofil aus all Ihren Suchanfragen. Das bedeutet, selbst wenn Sie Ihren Suchverlauf auf einem Gerät löschen, sind die Daten noch immer vorhanden.
Unter https://myactivity.google.com/myactivity können Sie Ihr Aktivitätsprotokoll abrufen und -einstellungen ändern.
Werbung
Google speichert nicht nur Daten, sondern kombiniert diese auch auf verschiedene Art und Weise. Sie haben nie nach "Wie nehme ich 10 kg in 2 Wochen ab" gesucht? Brauchen Sie auch nicht. Google genügt es zu wissen, dass Sie weiblich, Anfang dreißig sind und nach Bioläden in Ihrer Umgebung gesucht haben.
Die Kombination von Ortsdaten, Geschlecht, Alter, Hobbys (Suchanfragen), Karriere, Interessen, Beziehungsstatus und ungefähres Gewicht sowie Einkommen führt zu einem einzigartigen Marketingprofil, auf dessen Grundlage Sie Werbung erhalten.
Unter https://www.google.com/settings/ads/ können Sie Ihr Werbeprofil einsehen.
App-Nutzung
Sie nutzen einen Ad-Blocker? Google weiß es. Sie übersetzten oft Texte? Google weiß es. Sie nutzen eine Doodle-Liste, um ein internationales Geschäftsmeeting zu planen. Google weiß es, denn es speichert sämtliche Daten über Apps und Erweiterungen die Sie nutzen.
Diese Informationen umfassen, welche Apps Sie nutzen, wann und wo Sie sie benutzen, wie oft, wie lange und mit wem Sie damit kommunizieren, einschließlich mit wem sie auf Facebook chatten, wo diese Person lebt und wann Sie schlafen gehen.
Unter https://myaccount.google.com/permissions können Sie die Apps mit Zugriff auf Ihr Konto abrufen.
Google kennt alle YouTube Videos, die Sie je angeschaut haben
Google speichert alle Videos, die Sie je auf YouTube gesucht und angeschaut haben - auch wenn Sie es nach Sekunden geschlossen haben.
Dementsprechend weiß Google, ob Sie in Kürze Eltern werden, welche politische Einstellung Sie haben, welcher Religion Sie angehören, ob sie depressiv oder sogar selbstmordgefährdet sind.
Mehr: https://www.youtube.com/feed/history/search_history
Drei Millionen Word-Dokumente Daten
Das Gute an Google ist, Sie können all diese Daten anfordern und einsehen. Dylan Curran hat genau das getan und erhielt eine Archive-Datei mit 5,5 GB. Das entspricht etwa drei Millionen Seiten Fließtext.
Wenn Sie neugierig sind: Unter dem Motto "Ihr Konto, Ihre Daten" kann man unter https://takeout.google.com/settings/takeout "eine Kopie der Inhalte aus Ihrem Google-Konto exportieren, wenn Sie sie mit einem Dienst eines anderen Anbieters sichern oder nutzen möchten" so Google.
Diese Daten umfassen alle zuvor genannten Informationen, hinzu kommen noch Lesezeichen, E-Mails, Kontakte, Google Drive Dateien, Fotos, die mit Ihrem Handy aufgenommen wurden, die Geschäfte, bei denen Sie etwas gekauft haben und die Produkte, die Sie über Google gekauft haben.
Außerdem Ihren Kalender, Hangout-Konversationen, Musik, Bücher, Gruppen, Webseiten, die sie erstellt haben, Telefone, die sie besessen haben, geteilte Seiten, wie viele Schritte Sie pro Tag gemacht haben - eine nahezu endlose Liste.
Wie Google an Ihre Daten kommt
Auch wenn Sie diese Antwort vermutlich nicht gern hören: Sie geben Ihre Daten freiwillig. Das Google-Archiv der gesammelten Daten zeigt Ihnen, wie.
1. Suchverlauf
Der Suchverlauf von Dylan Curran umfasste mehr als 90.000 Einträge und zeigt unter anderem, welche Bilder er heruntergeladen und welche Webseiten er besucht hat. Natürlich bietet der Suchverlauf auch alle Suchanfragen zu Webseiten für das illegale Herunterladen von Programmen, Filmen und Musik, sodass diese Daten bei einer Gerichtsverhandlung durchaus gegen Sie verwendet und einen großen Schaden anrichten können.
2. Kalender ...
3. Google Drive ...
4. Google Fit ...
5. Fotos
Sollten Sie aus Versehen all Ihre Fotos gelöscht haben, keine Sorge, Google hat sie noch alle - einschließlich der Metadaten, wann, wo und mit welchem Gerät Sie die Fotos (und Videos) aufgenommen haben. Selbstverständlich gut geordnet nach Jahr und Datum.
6. E-Mails
Falls man Google-Mail oder Gmail nutzt, hat Google auch alle E-Mails, die Sie je gesendet oder bekommen haben. Das gleiche trifft auf alle E-Mails zu, die Sie gelöscht haben und auch die, die Sie nie erhalten haben (weil sie als Spam kategorisiert worden sind).
7. Aktivitätenprotokoll
Das Aktivitätenprotokoll umfasst wiederum Tausende Dateien und könnte Ihnen vermutlich auf Tag und Sekunde genau sagen, wie Sie sich gefühlt haben. Aufgrund der Fülle dieser Daten konnte Dylan Curran nur eine kurze Auswahl vorstellen:
Google speichert alle Werbeanzeigen, die Sie jemals gesehen oder angeklickt haben, jede App, die sie geöffnet, installiert oder gesucht haben und alle Webseiten, die sie je besucht haben.
Jedes Bild, das Sie gesucht oder gespeichert haben, jeden Ort, den Sie gesucht oder angeklickt haben, jede Nachricht und jeden Zeitungsartikel, jedes Video, das Sie angeklickt haben und jede einzelne Suchanfrage die Sie seit Ihrer ersten Google-Suche gemacht haben - egal ob Sie ein Google-Konto haben oder nicht!
Datensicherheit bei Facebook
Auch Facebook bietet die Option, seine privaten Daten herunterzuladen. Für Dylan Curran umfasste diese Datei "nur" 600 MB oder etwa 400.000 Seiten Text.
Darin befanden sich alle Nachrichten, die er je gesendet oder empfangen hat, alle Kontakte seines Telefons, und alle Sprachnachrichten.
Zusätzlich speichert Facebook all Ihre (möglichen) Interessen, basierend auf den Beiträgen, die sie geliket oder verborgen haben und - für den Datenschutzbeauftragten eher sinnlos - alle Sticker, die Sie je gesendet oder bekommen haben.
Logbuch
Darüber hinaus speichert Facebook - ähnlich wie Google - alle Daten Ihre Aktivitäten, wann Sie sich einloggen. Dazu gehört das von-wo und welches Gerät gerade genutzt wurde.
Außerdem speichert das Unternehmen ebenfalls Daten aus allen jemals mit Facebook verbunden Apps, sodass Facebook Ihre politische Einstellung und Interessen kennt. Facebook weiß vielleicht auch, dass Sie Single waren (denn Sie haben Tinder installiert/deinstalliert) und ab November ein neues Smartphone hatten.
Datensicherheit wird bei Windows groß geschrieben
Im Prinzip ja, denn wer Windows 10 nutzt, hat unzählige Möglichkeiten seine Privatsphäre "zu schützen". In der Tat sind es so viele, dass es unübersichtlich wird. Die wenigsten Menschen nehmen sich tatsächlich die Zeit, alle 16 (!) Menüpunkte und ihre jeweiligen Optionen und weiterführenden Einstellungen durchzulesen und individuell zu entscheiden. Kategorisch alle Schalter zu deaktivieren bringt weder den optimalen Schutz, noch das optimale Nutzungserlebnis.
Ganz ähnlich funktioniert auch das neue Sicherheitskonzept von Google, unter dem Motto: "Sie haben die Wahl" - nur dass Ihnen niemand erklärt, was Sie dort eigentlich auswählen können.
Fremdsteuerung von Webcam und Mikrofon
Die Daten, die Windows standardmäßig speichert, umfassen erneut die Standortdaten, welche Programme Sie installiert haben und wann und wofür Sie sie nutzen. Hinzu kommen: Kontakte, E-Mails, Kalender, Anrufliste, Kurznachrichten, Lieblingsrezepte, Spiele, Downloads, Fotos, Videos, Musik, on- und offline-Suchverlauf und sogar welchen Radiosender Sie hören. Außerdem hat Windows ständigen Zugriff auf Ihre Kameras und Mikrofone.
Dies stellt jedoch gleichzeitig eines der größten Paradoxen der modernen Gesellschaft dar. Wir würden nie im Leben der Regierung erlauben, Kameras oder Mikrofone in unseren Häusern oder Bewegungstracker in unserer Kleidung zu platzieren, stattdessen tun wir es freiwillig, denn - seien wir ehrlich - wir wollen unbedingt dieses süße Katzenvideo sehen. (ts)
Lesen Sie auch
Die dunkle Macht der neuen Medien: Wie soziale Medien unser Selbstwertgefühl beeinflussen, https://www.epochtimes.de/panorama/wissen-genial/die-dunkle-macht-der-neuen-medien-wie-soziale-medien-unser-selbstwertgefuehl-beeinflussen-a2885260.html
Apple und Co. sollen vollen Zugriff auf unsere Gesundheitsdaten bekommen, https://www.epochtimes.de/meinung/gastkommentar/
apple-und-co-sollen-vollen-zugriff-auf-unsere-gesundheitsdaten-bekommen-a2820016.html
https://www.epochtimes.de/panorama/tech/datensicherheit-das-wissen-
oogle-facebook-und-microsoft-wirklich-ueber-sie-a2885439.html
... Speed and security-level record already upon Intel ® Celeron ! Welcome to the online excursion of Gooken !
Mouseclick-fast, stable lifetime computer system with a kernel like the up to this time 195 times collective-patched 5.4 without any hacker and trojans, free from Viren and worms, no spyware and no adware, owner-, access-rights, integrity-rights and ACL, no cookies (session-cookies, if required), free from maintenance, advertisement, linfw3 upon iptables, ebtables, eventually arptables and always blocked net traffic for superuser root, port scan detector (psad), X/X11-Server with ---no-tcp, locking of all accounts except accounts for the superuser root and the user, locked login shells upon all accounts including root except surfuser (/sbin/nologin and/or firejail), Full System Encryption (FSE), secure end-to-ende-connections (TLS 1.3), few root-processes (X and kernel quit only), password-protection upon all passwords even if known (except the password for the LUKS-login for the encryption of the root-partition), noexec-home-partitions, updates up from 2010 to 2024 and longer, ..., without tracking scripts, scriptfilter, third-party-script- und image-Blocker and further on, sandbox firejail, Browser (within sandbox firejail): Konqueror and Pale Moon, Pale Moon security-extensions, anonymizing (Onion Router Tor), unrestricted internet, locale DNS-cache (local -> pdnsd > Tor-DNS), anonymized DNS-request, E-Mail-Client kmail with spam-filter (bogofilter, spamassassin, ...), ..., all upon mouseclick-fast, powersaving lifetime-hardware (quit for free), crash free and virus free (and at last exchangable) BIOS with own views and deep access rights, ..., all OpenSource.
Gooken is an online excursion to achieve real security with your computer. Just follow this excursion step by step (green hook by hook) !
But at first have a look upon some introducing links from NewsäLinks :
Technocrates lead the word into a dark age, uncut-news.ch, 07.16.2021
Population control and New World Order (NWO)
The promise of the technocrates for a brandew and better world are hollow as an empty balloon. Their politics forces into a scientific dictatorship and a new erea of neo-feudalism crushing the freedom. The time to avoid technocracy is now!
https://uncutnews.ch/technokraten-fuehren-die-welt-in-ein-neues-dunkles-zeitalter/
Our speak (Gooken):
Do not exchange real freedom into wrong security, uncut-news.ch, 06.02.2022
USA/DAS IMPERIUM
From Ron Paul. He is an US-american doctor and politicanr. He is member in the Libertarian Party and was during 1976 and 2013 (with pauses) a Republican representative in congress of the United States. Paul was during the US-president election 1988 candidate of the Libertarian Party and ran party-intern for the republican candidature of the US-president elections in 2008 and 2012.
https://uncutnews.ch/tauschen-sie-nicht-echte-freiheit-gegen-falsche-sicherheit/
 Lobby-revolving.-door: Google employs 65 government representatives from EU-staates, netzpolitik.org, 06.06.2016 Lobby-revolving.-door: Google employs 65 government representatives from EU-staates, netzpolitik.org, 06.06.2016
Das Google Transparency Project hat herausgefunden, dass in den letzten zehn Jahren 80 Personen sowohl bei EU-Regierungen wie auch bei Google angestellt waren. Google stellte im untersuchten Zeitraum 65 Regierungsvertreter ein, während 15 Google-Mitarbeiter in Regierungsdienste wechselten. Fünf Personen wechselten gar von der Regierung zu Google und dann zurück in Regierungsdienste,
https://netzpolitik.org/2016/lobby-drehtuer-google-stellt-in-zehn-jahren-65-eu-regierungsvertreter-ein/
Buyed Judges?
George Soros und Bill Gates sind zwei der größten Geldgeber des Europarats, epochtimes.de, 13.04.2021
https://www.epochtimes.de/politik/ausland/gekaufte-richter-am-egmr-george-soros-und-
bill-gates-sind-zwei-der-groessten-geldgeber-des-europarats-a3484703.html
Future of online advertisement: The new clothes of Ad-giants, netzpolitik.org, 02.25.2022
Die Ära der Tracking-Cookies neigt sich dem Ende und ein Kampf um die Vorherrschaft im digitalen Werbesystem ist entbrannt. Eine erstaunliche Partnerschaft zwischen Mozilla und Meta ist nur ein kleines Kapitel in dieser größeren Geschichte, analysiert unser Gastautor. Die nächste Phase der Online-Werbung könnte noch schlimmer werden als der Status Quo.
Werbetafeln leuchten im Dunkeln
Werbung verändert mal wieder ihre Form, doch es ist ungewiss, ob der Wandel Verbesserung bringt. - Gemeinfrei-ähnlich freigegeben durch unsplash.com Joe Yates
Michael Veale ist außerordentlicher Professor für Digital Rights und Regulierung am University College London in der Fakultät für Rechtswissenschaften. Er arbeitet an der Schnittstelle von Recht, neuen Technologien, Politik und Gesellschaft, mit einem aktuellen Schwerpunkt auf maschinellem Lernen und Technologien zur Verbesserung der Privatsphäre. Dieser Artikel erschien zunächst auf englisch.
Mozilla sorgte Anfang des Monats für einiges Erstaunen, als es eine Partnerschaft mit Meta ankündigte. Ausgerechnet mit dem Facebook-Mutterkonzern will die gemeinnützige Stiftung im Bereich neuer Werbetechnologien zusammenarbeiten. Dabei ist es noch nicht lange her, dass die Firefox-Entwickler:innen eine "Facebook-Container"-Funktion einführten, um die Cookies dieses einen spezifischen Konzerns unter Quarantäne zu stellen.
Es ist kein Geheimnis, dass der Firefox-Browser angesichts seines schwindenden Marktanteils eine Finanzspritze benötigt. Wahrscheinlich ist er auf der Suche nach mächtigen Freunden. Die Reputation von Mozilla ist jedoch nur der Nebenschauplatz einer viel größeren Geschichte: einer Geschichte über die Zukunft dessen, was wir unter Online-Privatsphäre verstehen. Denn das milliardenschwere System der Online-Werbung - im englischen spricht man von der Ad-Tech-Branche, kurz für Advertising Technologies - befindet sich in einem epochalen Wandel.
Apple und Google übernehmen die Kontrolle
Der Vorschlag von Mozilla und Meta betrifft die Ad Attribution, also die Zuordnung von Anzeigen.
https://netzpolitik.org/2022/zukunft-der-online-werbung-ad-tech-die-neuen-kleider-der-werbe-giganten-mozilla-meta-cookies/
 Don´t let your cookie steal your online-identity: Simple steps for more security, uncut-news.ch, 11.08.2024 Don´t let your cookie steal your online-identity: Simple steps for more security, uncut-news.ch, 11.08.2024
reclaimthenet
In einer Welt, in der alles, von Einkaufsliste bis zu persönlichen Gedanken, irgendwo im digitalen Raum gespeichert ist, sollten wir alle unsere Privatsphäre fest im Griff haben. Doch die Realität sieht anders aus: Viele von uns bewegen sich im Internet wie mit einer schutzlosen Hotelschlüsselkarte - wir zeigen sie herum, lassen sie in Cafés liegen, und wenn sie jemand stiehlt? Pech gehabt. Genau hier kommt das Cookie-Hijacking ins Spiel - ein Cyber-Angriff, bei dem ein unsichtbarer Dieb bereit ist, Ihre persönlichsten Daten zu entwenden und dem Meistbietenden zu verkaufen.
Was sind Cookies?
Cookies sind wie der diskrete, aber neugierige Butler des Internets, der uns von Seite zu Seite begleitet und dafür sorgt, dass wir eingeloggt bleiben, während wir Bankgeschäfte erledigen, shoppen oder surfen. Anders als die süßen Naschereien sind Cookies in der digitalen Welt kleine Textdateien - Informationspakete, die Webserver auf Ihrem Gerät speichern, damit Sie sich nicht bei jedem Klick neu anmelden müssen. Doch lassen Sie sich nicht täuschen. Wie jeder fleißige Butler sehen Cookies alles, merken sich alles und machen es manchmal sogar zu einfach.
Was sind Login-Cookies?
Login-Cookies sind quasi die Speicherkarten für Websites. Wenn Sie sich bei einem Konto anmelden, erhält Ihr Browser vom Server eine sogenannte "Sitzungs-ID" in Form eines Cookies. Von nun an ist dieses Cookie Ihr persönlicher VIP-Pass, der dafür sorgt, dass die Website Sie bei jedem Klick auf eine neue Seite erkennt. Stellen Sie sich das vor wie ein Festivalarmband: Wenn Sie es tragen, sind Sie drin - ohne sind Sie nur ein weiterer Besucher, der erneut nachweisen muss, dass er dazugehört.
Wie Login-Cookies funktionieren: Der Balanceakt der digitalen Identität
Wie läuft das also ab? Es ist ein komplexer Prozess:
Benutzeranmeldung: Sie geben Ihren Benutzernamen und Ihr Passwort ein. Der Server prüft und bestätigt, dass Sie es wirklich sind.
Cookie-Erstellung: Nach erfolgreicher Anmeldung erzeugt der Server eine Sitzungs-ID und speichert sie in einem Cookie, das er Ihrem Browser übermittelt.
Cookie-Aufbewahrung: Ihr Browser speichert das Cookie und präsentiert es jedes Mal, wenn Sie eine neue Seite der Website öffnen.
Sitzungsüberprüfung: Der Server überprüft bei jedem Klick die Sitzungs-ID. Passt alles, bleibt der Zugang bestehen, ohne dass Sie sich erneut anmelden müssen.
Sitzungsende: Die Sitzung endet, wenn Sie sich abmelden oder der Server das Cookie wegen Inaktivität löscht.
Cookie-Begegnungen in der realen Welt: Praktische Beispiele
Online-Banking: Wenn Sie sich in Ihr Bankkonto einloggen, übergibt der Server eine Sitzungs-ID in einem Login-Cookie an Ihren Browser. So können Sie ohne erneute Eingabe von Daten zwischen Seiten wechseln und Ihre Finanzen regeln. Melden Sie sich ab, wird das Cookie gelöscht und damit der Zugang zu Ihrem Konto gesperrt.
E-Commerce: Wenn Sie durch eine Shopping-Seite stöbern, sorgt das Login-Cookie dafür, dass Ihr Warenkorb bleibt, auch wenn Sie abgelenkt werden. Das Cookie stellt sicher, dass Ihre Sitzung beim erneuten Aufrufen der Seite noch aktiv ist.
Die Gefahr des Cookie-Hijackings: Wenn Hacker sich als Sie ausgeben
Beim Cookie-Hijacking - oder technisch "Session-Hijacking" - wird ein Session-Cookie gestohlen. Damit kann ein Angreifer in Ihre Konten eindringen, Ihre Identität übernehmen und auf Ihre Kosten shoppen oder Schaden anrichten. Um die simple Methode zu verstehen, wie eine digitale Identität zur Spielwiese für Hacker wird, betrachten wir die Schritte, die sie unternehmen.
Der Diebstahl: Den Schlüssel zum Königreich rauben
Um das Cookie zu entwenden, müssen Angreifer erst einmal Zugriff darauf bekommen. Beispielsweise über ungesicherte öffentliche WLANs, die Hackern Zugang zu Ihren Daten ermöglichen. Oder durch Cross-Site Scripting (XSS), bei dem Hacker bösartigen Code in vertrauenswürdige Webseiten einfügen, um Besucher-Cookies zu stehlen.
Zugriff auf Ihre Konten: Ein Einbruch ohne Passwort
Sobald der Hijacker Ihr Cookie hat, ist es ihm möglich, sich als Sie einzuloggen, ohne ein Passwort zu benötigen. Die Website wird den Hacker als Sie erkennen und ihm Zugang zu all Ihren Daten gewähren.
Ausbeutung: Ihr Leben als Spielwiese
Mit dem Cookie kann der Dieb nun auf Ihre persönlichen Daten zugreifen, Ihre Konten plündern und unbefugte Einkäufe tätigen. Inzwischen ist Cookie-Hijacking nicht mehr nur ein Problem für Einzelpersonen, sondern auch für Unternehmen, da Kundenvertrauen und Datenschutz auf dem Spiel stehen.
So schützen Sie sich
Um sich vor Cookie-Hijacking zu schützen, helfen einige grundlegende Sicherheitsvorkehrungen:
Verwenden Sie VPNs im öffentlichen WLAN,
Aktivieren Sie die Zwei-Faktor-Authentifizierung,
Seien Sie vorsichtig bei Links zu Angeboten von unbekannten Webseiten.
Unternehmen sollten zudem auf strenge Sicherheitsprotokolle setzen, Cookie-Schutzmaßnahmen in ihre Infrastruktur einbauen und Kundendaten mit größter Sorgfalt behandeln.
Fazit
In der digitalen Welt ist Vertrauen eine gefährliche Illusion. Solange unsere digitalen Identitäten auf so zerbrechlichen Daten wie einem Session-Cookie basieren, bleiben wir alle verwundbar. Denken Sie daran: Jemand könnte Sie online beobachten - und nicht nur wegen Ihres guten Geschmackes beim Online-Shopping.
Sichere Online-Interaktionen gewährleisten
1. Nutzen Sie sichere Netzwerkverbindungen
Öffentliches Wi-Fi ist verlockend, aber auch ein Einfallstor für Hacker. Cafés, Flughäfen und Hotels bieten oft ungesicherte Verbindungen, was Hacker anzieht, die auf Lauschangriffe spezialisiert sind. Bei sensiblen Online-Aktivitäten empfiehlt sich ein virtuelles privates Netzwerk (VPN), das Ihren Internetverkehr verschlüsselt und Sie vor neugierigen Blicken schützt. Stellen Sie sich ein VPN als unsichtbaren Schutzwall vor - eine smarte, diskrete Barriere gegen Cookie-schnappende Angreifer.
2. HTTPS-Protokolle durchsetzen
Websites, die noch das unsichere HTTP-Protokoll nutzen, machen sich zur leichten Beute. HTTPS hingegen umschließt Ihre Daten mit einer Schutzschicht, die es Angreifern erheblich erschwert, Informationen abzufangen. Wenn eine Website, die Sie verwenden, noch nicht auf HTTPS umgestiegen ist, sollten Sie deren Engagement für Ihre Sicherheit hinterfragen. Entwickler sollten sicherstellen, dass HTTPS ein Muss ist - so wie man beim Verlassen des Hauses die Tür abschließt.
3. Halten Sie die Software auf dem neuesten Stand
Veraltete Software lädt Hacker ein, da Sicherheitslücken oft erst durch Updates geschlossen werden. Ob Browser oder Plug-ins - bei Software-Updates geht es oft weniger um neue Funktionen als um die Beseitigung von Schwachstellen. Jedes Update hilft, potenzielle Einfallstore für Angreifer zu versperren. Da Hacker unerbittlich nach Schwachstellen suchen, ist es ratsam, stets die neuesten Sicherheits-Updates zu installieren.
4. Achten Sie auf ordnungsgemäße Sitzungsverwaltung
Das Abmelden nach einer Sitzung mag trivial erscheinen, ist jedoch ein wichtiger Schutzmechanismus. Durch das Abmelden wird das Sitzungs-Cookie ungültig und damit wertlos für Dritte. Besonders auf gemeinsam genutzten oder öffentlichen Computern ist das Abmelden unerlässlich - wie das Abschließen der Autotür beim Parken mit laufendem Motor.
5. Privates Surfen verwenden
Beim Surfen auf gemeinsam genutzten Computern ist der Inkognito- oder private Modus eine gute Option. Er schützt zwar nicht vollständig, verhindert jedoch die Speicherung von Sitzungscookies und des Browserverlaufs. Sobald das private Fenster geschlossen wird, verschwinden die meisten Spuren Ihrer Sitzung. Das Risiko, sensible Cookies zurückzulassen, die von anderen ausgenutzt werden könnten, lässt sich so deutlich minimieren.
6. Cookies regelmäßig verwalten
Cookies altern lassen ist wie Milch offen stehen zu lassen - sie können im falschen Moment verderben. Regelmäßiges Löschen oder das schnelle Auslaufenlassen von Cookies sorgt dafür, dass keine veralteten Cookies herumliegen, die zum Angriffsziel werden könnten. Browser-Erweiterungen zur Cookie-Verwaltung bieten eine zusätzliche Schutzebene. Betrachten Sie dies als digitalen Hausputz: Niemand möchte anfällige, alte Cookies herumliegen lassen.
7. Vorsicht bei Browser-Erweiterungen
Browser-Erweiterungen sind nützlich, verlangen jedoch oft umfassende Berechtigungen, die ihnen Zugriff auf Cookies und Browsing-Daten geben können. Installieren Sie daher nur Erweiterungen aus vertrauenswürdigen Quellen und überprüfen Sie die Berechtigungen. Denken Sie daran: Lassen Sie sie nur rein, wenn Sie sicher sind, dass sie Ihre Privatsphäre nicht missbrauchen.
8. Zwei-Faktor-Authentifizierung (2FA) verwenden
2FA fügt eine zusätzliche Sicherheitsebene hinzu, indem sie eine zweite Verifizierung verlangt, wie einen Code auf Ihr Telefon. Selbst wenn ein Angreifer Ihren Cookie abfangen sollte, fehlt ihm der zweite Authentifizierungsfaktor. So ist es, als bräuchte er nicht nur den Schlüssel, sondern auch den Zugangscode - Cookie-Hijacker schaffen es vielleicht bis zur Eingangstür, aber 2FA lässt sie nicht weiter.
Die entscheidende Rolle der Entwickler
Benutzer können viel tun, doch echter Schutz beginnt auf Code-Ebene. Entwickler sind in der Verantwortung, Anwendungen sicher zu gestalten und die Sitzungen der Nutzer abzusichern.
Sichere Kodierungspraktiken: Setzen Sie HttpOnly- und Secure-Flags bei Cookies, um sie vor JavaScript und ungesicherter Übertragung zu schützen.
Nutzeraufklärung: Viele Nutzer sind sich der digitalen Bedrohungen nicht bewusst. Entwickler können durch Erinnerungen und Warnungen in der Anwendung Aufklärung betreiben, z. B. für die Nutzung sicherer Geräte.
XSS-Schutz: XSS-Angriffe ermöglichen es Hackern, bösartigen Code einzuschleusen, um Daten abzufangen. Entwickler sollten XSS-Schutz einbauen und Cookies auf Code-Ebene absichern.
Da unser digitaler Fußabdruck wächst, muss auch unser Engagement für die Sicherheit zunehmen. Die Cookie-Sicherheit ist nur ein Teil des Puzzles, aber ohne sie bleibt der Schutz unvollständig. In einer Welt, in der Daten eine Währung sind und Privatsphäre wertvoll ist, geht es beim Cookie-Schutz um mehr als nur sicheres Surfen - es geht um den Schutz unserer digitalen Identität.
Quelle: Don´t Let a Cookie Steal Your Online Identity: Simple Steps to Stay Secure, https://reclaimthenet.org/dont-let-a-cookie-steal-your-online-identity-simple-steps-to-stay-secure
https://uncutnews.ch/lassen-sie-nicht-zu-dass-ein-cookie-ihre-online-identitaet-stiehlt-einfache-schritte-fuer-mehr-sicherheit/
Secret agencies/NSA/Surveillance/BigData
Edward Snowden: "If we weaken encryption, people will die", uncut-news.ch, 24.10.2021
https://uncutnews.ch/edward-snowden-wenn-sie-verschluesselungen-schwaechen-werden-menschen-sterben/
 Google and Microsoft are the biggest data collectors Google and Microsoft are the biggest data collectors
Data are spreaded out into the whole world
Online-advertisement: Companies collect data each minute, netzpolitik.org, 05.17.2022
Technologieunternehmen machen ihr Geld mit Online-Werbung. Ein neuer Bericht zeigt, in welchem Ausmaß sie dafür Daten abgreifen - und wo diese Daten landen.
Ein neuer Bericht zeigt, wie persönliche Daten dank Google und Co. bei Firmen in der ganzen Welt landen.
Eine Person, die in Deutschland im Internet unterwegs ist, wird im Schnitt jede Minute vermessen. Was schaut sie an? Wo geht sie hin? Auf das so geschnürte Datenpaket können Tausende Firmen zugreifen. Das geht aus einem neuen Bericht des Irish Council for Civil Liberties (ICCL) hervor. Firmen auf der ganzen Welt haben demnach Zugang zu teils sehr privaten Daten wie sexuellen Vorlieben oder politischer Haltung. Die Bürgerrechtsorganisation prangert die Aktivitäten der Tech-Giganten als "größtes Datenleck" an.
Anhand interner Dokumente aus der Werbeindustrie beleuchtet der Bericht das so genannte Real-Time-Bidding, ein Verfahren, mit dem in Echtzeit Anzeigenplätze auf Webseiten oder Apps versteigert werden. Dafür wird erhoben, welche Inhalte sich Nutzer:innen ansehen oder wo sie sich befinden, um ihnen zielgenau passende Werbeanzeigen zeigen zu können. Die Zahlen des Berichts beziehen sich auf Europa und die Vereinigten Staaten. Pro Tag würden in Europa demnach 197 Milliarden mal Daten abgegriffen.
"Google und Microsoft größte Datensammler"
Der größte Akteur ist dem Bericht zufolge Google. Doch auch Microsoft sei in die obere Liga aufgestiegen, seit es Ende 2021 die Real-Time-Bidding Firma Xandr kaufte. Zwei weitere Unternehmen, die ebenfalls im großen Stil mit Daten handeln - Facebook und Amazon - sind in den ausgewerteten Dokumenten nicht berücksichtigt, so der ICCL. Laut den recherchierten Zahlen ist Google in Deutschland und Europa der größte Händler. Pro Jahr beläuft sich der Wert des Real-Time-Bidding dem Bericht zufolge auf 117 Milliarden Dollar in den USA und Europa. In der EU sollen es 2019 23 Milliarden Euro gewesen sein. Aus den Dokumenten geht außerdem hervor, dass der Umfang des Datensammeln in Europa deutlich geringer ist als in den Vereinigten Staaten.
Technisch ist das Real-Time-Bidding leicht nachvollziehbar: Sobald man eine entsprechende Seiten öffnet, sammelt ein Dienst im Hintergrund Gebote für die Anzeigenplätze. Die Bietenden analysieren sämtliche Daten der Person, die die Anzeige sehen soll und entscheiden, ob und wie hoch geboten wird. Der höchstbietende Dienst bekommt anschließend den Anzeigenplatz. All das läuft in Echtzeit, also innerhalb weniger Millisekunden ab. Zu den Daten, die alle Dienste während des Prozesses abgreifen können, zählen nicht nur Standort oder Alter. Sie beinhalten oft auch persönliche Vorlieben oder religiöse Orientierung.
Daten enden auf der ganzen Welt
Die Daten, die gesammelt werden, sind nicht nur für die Bieterdienste zugänglich. Laut dem Bericht des ICCL teilt in Europa allein Google die gesammelten Daten mit 1.058 Unternehmen. Darunter seien auch Firmen aus China und Russland. Ein weiteres Dokument aus der Tracking-Industrie zeigt, welche privaten Informationen gesammelt werden, darunter zum Beispiel, ob eine Person Suchtprobleme oder Geschlechtskrankheiten hat. Welche Konsequenzen das haben kann, zeigte erst kürzlich ein Fall in den USA, bei dem ein katholischer Newsletter-Dienst mithilfe von kommerziell zugänglichen Daten aus der Dating-App Grindr einen Priester als homosexuell outete.
https://netzpolitik.org/2022/online-werbung-firmen-greifen-jede-minute-daten-ab/
 Testers in year 2016: Around 5500 connection buildup attempts of MS Windows 10 into the internet Testers in year 2016: Around 5500 connection buildup attempts of MS Windows 10 into the internet
Several hundrets of contacts to internet server within a few hours
Windows-Datenschutz auf BSI-Level - so gehts, PC-WELT.de, 04.17.2019
Seit der Einführung von Windows 10 wird das Betriebssystem für seinen mangelnden Datenschutz kritisiert: Es werden zu viele Daten ins Internet gesendet. Nun hat das BSI nachgemessen und aufgedeckt, wie Sie den Datenversand komplett abstellen können.
Kritik am Datenschutz von Windows 10 hagelt es von Sicherheitsexperten, Bloggern und Firmen. Ein PC mit Windows 10, der aktuell keine Aufgabe zu erledigen hat, nimmt dennoch laufend Verbindungen zu Servern im Internet auf. Die Kritik ist nicht neu. Schon Windows XP wurde für seine sogenannte "Call-Home"-Funktionen kritisiert. Damals im Jahr 2001 waren einige Programme, etwa der Windows Media Player, für den unangemeldeten Kontakt ins Internet verantwortlich.
Was sich mit Windows 10 im Jahr 2015 geändert hat, war die schiere Menge an Verbindungen.
Fortsetzung des Berichts und Maßnahmen: in Kürze!
 MacOS and Windows Apps are able to make films secretly, tagesschau.de, 07.13.2022 MacOS and Windows Apps are able to make films secretly, tagesschau.de, 07.13.2022
Computer operating systems do not protect enough against spying through Apps. An experiment of BR-Data journalists and PULS Reportage is showing this. This is a security risk especially in times for HomeOffice.
Report from Sebastian Bayerl, Maria Christoph, Rebecca Ciesielski, Pia Dangelmayer, Elisa Harlan, Robert Schöffel, BR
Die Corona-Pandemie hat die Kommunikation in der Arbeitswelt grundlegend verändert: Ob morgendliche Videokonferenz oder Meeting am Nachmittag, Videocalls mit aktivierter Kamera sind für viele Arbeitnehmerinnen und Arbeitnehmer Normalität. Dabei birgt das Arbeiten von zuhause in Bezug viele Risiken für die Datensicherheit.
https://www.tagesschau.de/investigativ/br-recherche/sicherheit-homeoffice-101.html
 Crass lack in security explored: How virus scanner decompose themselves, CHIP, 04.28.2020 Crass lack in security explored: How virus scanner decompose themselves, CHIP, 04.28.2020
Virenscanner sollen Windows eigentlich vor Gefahren schützen. Doch Forschern ist es gelungen, den Schutz zur Gefahr zu machen. Über symbolische Links zwischen Verzeichnissen konnten nicht nur 28 namhafte Virenscanner ausgetrickst werden, die Schutzsoftware ließ sich auch so manipulieren, dass sie sich selbst und Windows unbrauchbar machen konnte.
[...}] Virenscanner bergen auch Risiken. Der Grund ist einfach, die Tools arbeiten mit den umfassendsten Rechten auf dem System, die es gibt. Gelingt es Angreifern eine Schwachstelle zu finden, steht Windows mit runtergelassenen Hosen da.
Genau das ist Sicherheitsforschern gelungen.
[...] Das Tool der Wahl für den Angriff sind verknüpfte Verzeichnisse, wie man sie unter Windows mit dem Befehl "mklink /j" erstellen kann. Das kann jeder Nutzer unter Windows erledigen, Adminrechte braucht es dafür nicht.
Der Angriff nutzt dabei die grundlegende Arbeitsweise eines Virenscanners aus
https://www.chip.de/news/Sicherheitsluecke-Virenscanner-zerlegen-sich-selbst_182651458.html
Study
How bosses survey their employees, netzpolitik.org, 09.21.2021
Digitale Überwachung ist in vielen Arbeitsplätzen inzwischen Realität geworden. Eine umfassende Studie untersucht nun gängige Technologien und Systeme, die sich oft in einem rechtlichen Graubereich bewegen.
Viele Angestellte werden in ihrer Arbeit überwacht. Eine Studie untersucht nun gängige Technologien und Systeme. (Symbolbild) - Alle Rechte vorbehalten IMAGO / Panthermedia
Keine Frage, die Zeiterfassung am Arbeitsplatz ist digital viel praktischer als mit analoger Stechkarte. Doch beim Aufschreiben von Zeiten bleibt es oft nicht: Längst können solche Systeme etwa Daten über Arbeitstätigkeiten erfassen und festhalten, mit welchen Projekten oder Kund:innen sich Mitarbeitende wie lange beschäftigt haben. Später lassen sich diese Daten für Abrechnungen nutzen oder mit anderen Datenquellen vernetzen. Firmen wollen damit betriebliche Abläufe optimieren, während Arbeitnehmer:innen zunehmend gläsern werden.
"Unternehmen können digitale Überwachung und Kontrolle nutzen, um Arbeit zu beschleunigen und zu verdichten, Freiräume einzuengen oder Beschäftigte leichter ersetzbar zu machen", sagt Wolfie Christl. In einer 150 Seiten starken Studie hat der österreichische Datenschutz-Aktivist für die NGO Cracked Labs untersucht, wie weit die digitale Überwachung am Arbeitsplatz inzwischen fortgeschritten ist. Die Studie ist Teil des Projekts "Gläserne Belegschaft" und wurde mit Hilfe österreichischen Gewerkschaften und der Arbeiterkammer Wien erstellt.
https://netzpolitik.org/2021/studie-wie-chefs-ihre-angestellten-ueberwachen/
Screen recording in Windows 10: Get to know, how simple this can be done, CHIP, 01.27.2022
Möchten Sie Ihren Bildschirm unter Windows 10 abfilmen, können Sie die gleichen Screencast-Tools wie unter älteren Windows-Versionen anwenden. Wir erklären Ihnen, wie auch in der neuen Windows-Version ein Screencast gelingt. Mit der richtigen Tastenkombination geht es super einfach.
https://praxistipps.chip.de/windows-10-bildschirm-abfilmen-so-klappt-der-screencast_42476
 Visualized: With this 600 companyies Paypal shares your data, netzpolitik.org, 23.01.2018 Visualized: With this 600 companyies Paypal shares your data, netzpolitik.org, 23.01.2018
Seit dem 1. Januar 2018 gewährt der Online-Zahlungsdienst PayPal Einblick in die Liste der Firmen, mit denen er "möglicherweise" persönliche Informationen seiner Nutzer teilt. Rebecca Ricks hat die sage und schreibe 600 Firmen visualisiert.
https://netzpolitik.org/2018/visualisiert-mit-diesen-600-firmen-teilt-paypal-deine-daten/
 Facebook aks banks for user data, PC-WELT.de, 08.07.2018 Facebook aks banks for user data, PC-WELT.de, 08.07.2018
Facebook hat laut einem Medienbericht bei mehreren großen US-Banken angefragt, um von diesen Kundendaten zu bekommen.
https://www.pcwelt.de/a/facebook-fragte-banken-nach-nutzerdaten,3451879 ä
 It might already be risky to get an E-mail from Gmail (and other freemailer), because of its include getting stored and distributed. It might already be risky to get an E-mail from Gmail (and other freemailer), because of its include getting stored and distributed.
The best, one can do, is to resign from any E-mail-account. If you must have one, remove it after use. If you still have one, never tell more people about your E-mail-address than necessary.
 Google knows your online purchases from online shopping via Gmail-tracking, PC-WELT.de, 20.05.2019 Google knows your online purchases from online shopping via Gmail-tracking, PC-WELT.de, 20.05.2019
Google ist in der Lage, alle Online-Einkäufe der Nutzer zu tracken, auch wenn diese nicht via Google getätigt wurden.
https://www.pcwelt.de/news/Google-kennt-Ihre-Online-Einkaeufe-via-Gmail-Tracking-10594891.html
 Google tracks master card user Google tracks master card user
Bericht: Google verfolgt Nutzer offline mit Mastercard-Daten, PC-WELT.de, 08.31.2018
Laut einem Bloomberg-Bericht kauft Google Kunden-Daten von Mastercard, um Kunden auch offline zu tracken.
Wie die News-Plattform Bloomberg berichtet, ist Google wohl einen Deal mit Mastercard eingegangen, um Offline-Einkäufe von Kreditkarten mit Nutzerkonten zu verknüpfen. Für die Daten von 70 Prozent aller Mastercard-Inhaber der USA aus dem Jahr 2017 soll Google demnach mehrere Millionen US-Dollar gezahlt haben. Darin enthalten sind Transaktionsdaten, die für Google ausreichen, um Personen eindeutig zu identifizieren.
[...] Laut den Angaben von Bloomberg sind sich aber beide Unternehmen wohl darüber bewusst, dass hier jede Menge Datenschutz-Probleme auftauchen. Der Deal wurde daher nur zögerlich eingegangen. Vier Jahre wurde zwischen den zwei Unternehmen verhandelt, bevor der Deal abgeschlossen wurde. Mastercard-Inhaber wurden darüber hinaus nicht über das Tracking informiert. Zwar gäbe es in Googles Web-Console eine Möglichkeit das Tracking zu untersagen, jedoch ist dies für den Großteil der Nutzer nicht ersichtlich.
[...] Der Bloomberg-Bericht bezieht sich nur auf die USA. Ob Google in weiteren Ländern ähnlich vorgeht, geht aus dem Artikel nicht hervor. In den Vereinigten Staaten machen Umsätze mit Mastercard rund 25 Prozent des gesamten Umsatzes aus.
https://www.pcwelt.de/a/bericht-google-verfolgt-nutzer-offline-mit-mastercard-daten,3452190
Scoring and more
You must get active: The financial takeover of your bank account - BlackRock, Envestnet/Yodlee und die Federal Reserve, uncut-news.ch, 06.16.2021
Terror/Terrormanagement
coreysdigs.com: Have you ever heart of Yodlee? Ich auch nicht, bis ich entdeckte, dass das Unternehmen meine Daten in meinem Bankkonto sammelt und sie wahrscheinlich an Dritte verkauft. Dies wurde schnell zu einer persönlichen Recherche, bis ich erschütternde Zusammenhänge entdeckte, von denen ich erkannte, dass die Öffentlichkeit darauf aufmerksam gemacht werden muss. Bevor Sie beschließen, dass dies nichts mit Ihnen zu tun hätte, bitte ich Sie dringend, diesen Artikel in seiner Gesamtheit zu lesen und die zeitlichen Abläufe genau zu beachten, denn dies betrifft SIE ALLE, und es wird in mehreren Ländern eingeführt. Ich empfehle Ihnen, sich bei Ihrer Bank zu erkundigen und herauszufinden, welche Drittparteien in Ihre Konten verwickelt sind, und die Möglichkeit in Betracht zu ziehen, Ihre Gelder zu einer kleineren lokalen Bank zu transferieren. Hier geht es nicht nur um Spionage und Datenaggregation, sondern um einen strukturellen Aufbau, der uns in das System der Sozial- und Klimabilanz und noch darüber hinaus bringen soll. Und Biden schreibt die Anordnungen, um den Rahmen zu schaffen, den BlackRock ausgearbeitet hat.
Untersuchen Sie Ihre Bank, Finanzinstitute und Ihre Konten
Kurze Zusammenfassung
Mehr dazu: in Kürze u.a. auf News&Links#Bankenskandal
Apple
Privacy labels failMany ‚tracking-free‘ apps in iOS secretly track users, netzpolitik.org, 01.20.2022
Apple forces developers give clear privacy information to app users. But according to new research, four out of five tested apps that claim to not collect data from users actually do.
It reads like a fairly simple statement: "Data not collected". Apple introduced such clear privacy labels for apps on its mobile operating system iOS over a year ago. They are supposed to show whether and which data the app passes on to its operators or third parties.
A sizeable portion of apps claim not to collect any data from users. But many of these labels are clearly false, as a technical analysis shared exclusively with netzpolitik.org has shown. Computer scientist Konrad Kollnig from Oxford University examined 1,682 randomly selected apps from Apple´s App Store. 373 of the apps tested (22.2 percent) claim not to collect personal data. However, four out of five, 299 apps in total, contacted known tracking domains immediately after the first app launch and without gaining user consent. (Data to be published soon, more details on the method here.)
One prominent app from Kollnig´s dataset is "RT News" by the Russian state broadcaster. The app claims not to collect any data. To verify the accuracy of that claim, Kollnig loaded it onto a test device and navigated to a few random articles. In total, the RT app sent data to 19 domains. Not to Russia, but to tracking services of the tech giants Facebook and Google, the market research company ComScore and the advertising company Taboola.
Such data collection should be specified in the data protection label, says Kollnig, because it could contain sensitive information, including what news users have viewed in the app. "Unfortunately, it´s often unclear what data is really being collected and what happens to that data." He says that particular caution should be exercised with apps that have access to the GPS location. As research by the New York Times has shown, such location data often ends up in the hands of data companies that offer it for sale - a clear case of abuse.
Kollnig, a PhD student at Oxford University´s Department of Computer Science, and his colleagues have been studying just how much tracking is happening through apps. Most recently, they published an analysis of nearly two million Android apps in the Internet Policy Review. They found that little has changed since the EU´s General Data Protection Regulation took effect in May 2018. According to their findings, around 90 percent of the apps in Google´s Play Store may share tracking data with third parties.
For his analysis of iOS apps, Kollnig randomly selected apps that have been in Apple´s app store since January 2020 and have subsequently added a privacy label. He loaded the apps automatically on an iPhone 8 running on iOS 15.2, where each app was opened. No other interaction took place; crucially, no consent to tracking was given. Kollnig examined the data flowing from the phone through a so-called man-in-the-middle proxy. He also installed some apps manually for extra testing.
Privacy labels get bad reviews
In principle, Apple sets higher standards than other companies when it comes to data protection and privacy. The tech giant has used its privacy bona fides for marketing purposes, including speeches by CEO Tim Cook at major European data protection conferences.
In December 2020, Apple introduced privacy labels "to help you understand how apps handle your data". They faced criticism from the start. In January 2021, Washington Post columnist Geoffrey A. Fowler found more than a dozen false claims in privacy labels, including in a video app for children and a popular game. Fowler noted that the small print of the labels states that Apple does not always check the privacy information, but instead relies on occasional audits.
A year later, the situation is essentially the same. Kollnig found numerous popular apps in his analysis that collect more data than claimed. For example, the puzzle app of a large gaming company sends an ID number of users to numerous tracking services, contrary to its label. Tracking even happens within apps by government agencies. Kollnig found that the app of the Met Office, the UK´s national weather service, sends sensitive information such as GPS data to Google and Amazon and also - without any indication in the label - collects a user ID.
Apple declined to comment directly on Kollnig´s analysis. Contacted by netzpolitik.org, the tech giant only said that the information in the labels came from the developers, and that Apple focusses ongoing reviews on the most popular apps.
According to Kollnig, there is a practical reason why so much data from popular apps ends up with third parties. Tracking services are usually integrated into apps via so-called libraries. Libraries are subroutines that perform certain tasks in an app. Their use makes work easier for programmers, but means less control over the finished app. Many libraries come from companies like Google, and the tracking code is hidden in them. "App operators often have no way of verifying the program code of these libraries, because the tracking companies usually do not make their code public," says Kollnig.
Tracking offers app providers a way to make money through personalized advertising. "The need of app operators to earn money is understandable," says Kollnig. But the business comes at the expense of the users, who hardly know anything about the collected data. According to Kollnig, Big Tech companies deliberately make it difficult for app operators to use privacy-friendly alternatives. His thinks that in order for this to change, EU countries must start enforcing their privacy laws more vigorously.
Correction on Friday, January 21, 2022: The story initially misstated that one out of five apps, 299 in total, contacted known tracking domains immediately after the first app launch. We corrected that figure to four out of five.
.
https://netzpolitik.org/2022/apple-datenschutzlabels-grossteil-angeblich-trackingfreier-ios-apps-sammelt-heimlich-daten/
Digital-service-act
How the data industry prevented the prohibition of survey-advertisement, netzpolitik.org, 02.20.2022
Das EU-Parlament will verhaltensbasierte Werbung und invasives Tracking einschränken. Eine Initiative zum Verbot der umstrittenen Überwachungswerbung ist jedoch gescheitert. Ein Bericht des Corporate Europe Observatory zeigt, dass das auch am mächtigen Lobbyismus von Google, Facebook und Co. liegt.
https://netzpolitik.org/2022/digitale-dienste-gesetz-wie-die-datenindustrie-ein-verbot-von-ueberwachungswerbung-verhinderte/
Up to one billion internet connections daily
Foreign secret agencies
How the BND surveys the internet, tagesschau.de, 05.15.2020
Nach Informationen von BR und "Spiegel" kann der BND offenbar auf mehr als eine Billion Internetverbindungen täglich zugreifen. Nächste Woche wird in Karlsruhe entschieden, ob die Überwachung rechtens ist.
[...] Das hängt auch mit der Daten-Auswertung zusammen, die der BND betreibt. Die Daten werden ihm unbearbeitet von deutschen Internet-Austauschknoten übergeben, auf Anordnung des Kanzleramtes hin. 23 solcher Knoten gibt es hierzulande, mit dem DE-CIX in Frankfurt am Main steht dem BND auch der Knoten mit dem weltweit höchsten Datendurchsatz zur Verfügung.
Techniker des DE-CIX stellten im Oktober 2019 auf Nachfrage des Verfassungsgerichtes Berechnungen an, um die Größe der Datenmenge abzuschätzen. Derzeit werde "ein durchschnittliches Volumen von rund 47,5 Billionen IP-Verkehrsverbindungen täglich vermittelt". Der BND sei technisch in der Lage, jeden Tag auf 1,2 Billionen Internet-Verbindungen aus dieser Gesamtmenge zuzugreifen.
Bevor der BND die Daten auswertet, werden sie in einem ersten Schritt anhand von IP-Adressen gefiltert. In einem der Dokumente führt die Bundesregierung aus, dass IP-Adressen "in Bezug auf eine Verortung auf Länderebene zu 96 bis 98 Prozent genau" seien. Doch nimmt man die mehr als eine Billion Verbindungen, die der BND täglich ausleiten kann, würden 24 Milliarden Rohdaten nicht umgehend gelöscht, wie vorgesehen, sondern einer weiteren Filterstufe zugeführt.
Die Internet-Verbindungen werden in einem zweiten Schritt automatisiert nach Meta- und Inhaltsdaten untersucht, also konkret geführten Gesprächen. Metadaten zeigen zum Beispiel, wer mit wem telefoniert, wann und wie lang. Mehr als 100.000 Suchbegriffe werden verwendet: von Telefonnummern und E-Mail-Adressen bis hin zu Namen chemischer Stoffe, mit denen sich Massenvernichtungswaffen herstellen lassen.
[...] Snowden enthüllte globale Überwachung
In welchem Ausmaß der BND über Jahre Telekommunikationsdaten abgegriffen und an den US-Geheimdienst NSA weitergeleitet hat, wurde durch die Enthüllungen des Whistleblowers Edward Snowden im Juni 2013 und im daraufhin vom Deutschen Bundestag eingesetzten NSA-Untersuchungsausschusses deutlich. Das Gremium beschäftigte sich unter anderem mit dem Projekt "Eikonal". Dabei erfasste der BND mindestens von 2004 bis 2008 über einen Kabelknoten der Deutschen Telekom in Frankfurt am Main Daten und leitete sie an den US-Geheimdienst NSA weiter - offenbar ohne wirkliche rechtliche Grundlage.
Nach wie vor ist umstritten, ob sich darunter auch Daten deutscher Staatsbürger befunden haben. Ein Mitarbeiter der beim BND zuständigen Abteilung, den der NSA-Untersuchungsausschuss mehrfach als Zeugen vernommen hatte, wies entsprechende Medienberichte damals zurück: "Meines Wissens wurde aus diesem Ansatz kein Datum eines Deutschen abgeleitet." Grüne und Linke zogen am Schluss der Ausschussarbeit ein gegenteiliges Fazit: "Eikonal wuchs dem BND über den Kopf."
Unter anderem deswegen trat am 31. Dezember 2016 ein neues BND-Gesetz in Kraft. Für Armin Schuster - auch er wie von Notz Mitglied im PKGr - ist die Kontrolle des BND bereits jetzt streng: "Deutschland wirft im weltweiten Datenmeer nicht ein Schleppnetz aus, sondern arbeitet mit der Harpune und das wird intensiv kontrolliert."
In Berlin rechnet man aber damit, dass in Karlsruhe der Beschwerde zumindest in Teilen stattgeben wird.
https://www.tagesschau.de/investigativ/br-recherche/bnd-urteil-101.html
Dossier: eavesdropping by the state, netzpolitik.org, 2021
Von angezapften Unterseekabeln über die neueste Ausweitung von Staatstrojanern bis zum Datenmissbrauch durch Polizeibeamte - wir berichten seit Jahren über staatliche Überwachungsmaßnahmen und ihren Einsatz. Damit ihr keine tiefgreifenden Änderungen verpasst und den Überblick behaltet, sammeln wir in diesem Dossier alle unsere Artikel zum Thema staatlicher Überwachung. Wir bleiben für euch dran.
https://netzpolitik.org/staatliche-ueberwachung/
...
https://netzpolitik.org/2021/neues-dossier-zu-ueberwachung-auf-dem-laufenden-bleiben/
https://netzpolitik.org/2017/chronik-des-ueberwachungsstaates/
https://netzpolitik.org/2021/ueberwachungsgesamtrechnung-mehr-als-die-summe-der-einzelteile/
https://netzpolitik.org/2021/forschungsbericht-schockierendes-ausmass-von-biometrischer-ueberwachung-in-europa/
https://netzpolitik.org/2021/finfisher-wir-verklagen-das-bka-auf-den-staatstrojaner-vertrag/
https://netzpolitik.org/2021/staatstrojaner-pegasus-wir-muessen-die-gesamte-ueberwachungsindustrie-in-frage-stellen/
...
 How all began How all began
Five years lasting fight against End-to-End-encryption, netzpolitik.org, 02.12.2020
Die Regierungen der EU-Mitgliedstaaten wollen ihre Polizeien und Geheimdienste befähigen, Ende-zu-Ende-verschlüsselte Kommunikation zu umgehen oder mit technischen Werkzeugen auszuhebeln. Ein Rückblick.
https://netzpolitik.org/2020/wie-alles-anfing-fuenf-jahre-kampf-gegen-ende-zu-ende-verschluesselung/
Surveillance
36 Millionen Euro: ZITiS builds supercomputer for decryption, netzpolitik.org, 10.16.2018
https://netzpolitik.org/2018/36-millionen-euro-zitis-baut-supercomputer-zur-entschluesselung/
 MS Windows MS Windows
One, two, three, four state trojans, netzpolitik.org, 21.03.2019
[...] ZITiS ist nicht die einzige deutsche Hacker-Behörde. Das Bundeskriminalamt kann aktuell drei Staatstrojaner einsetzen, ein vierter wird zur Zeit programmiert.
Fortsetzung des Berichts: in Kürze, nach dem Listing von trojaner-board.de!
New analyzes-platform: check Windows-driver against trojans, trojaner-info.de, 12.27.2021
Microsoft bietet einen neuen Online-Service an, bei dem Entwickler und Sicherheitsforscher sich verdächtig verhaltende Treiber zur Analyse hochladen können.
Oft laufen Windows-Treiber mit Kernel-Rechten. Schafft es ein Angreifer an dieser Stelle manipulierend einzugreifen, könnte er Malware tief im System verankern. Um dem vorzubeugen, stellt Microsoft ab sofort eine Analyse-Plattform für Treiber bereit.
https://www.trojaner-info.de/daten-sichern-verschluesseln/aktuelles/
neue-analyse-plattform-windows-treiber-auf-trojaner-untersuchen.html
Warning, 2022: The war of the technocracy against humand kind will be proceeded, uncut-news.ch, 04.01.2022
Am letzten Tag des Jahres 2021 gibt es keinen besseren Zeitpunkt, um über die jüngsten Erfolge der Technokratie und ihre wahrscheinliche Entwicklung im Jahre 2022 nachzudenken.
Über Weihnachten habe ich meine "Zwölf Tage der Technokratie"-Artikel vorgestellt, die ursprünglich im Dezember 2019 geschrieben wurden. Obwohl diese unten auf der Startseite von Technocracy.news erscheinen, hatten viele Menschen sie nicht gelesen.
Die Absicht dieser Artikel war es, eine Einführung in die Technokratie zu geben, die verschiedene Themen wie Zentralbankwesen, Wissenschaft, Bildung und Politikwissenschaft umfasst. Es war eine passende Art und Weise, das Jahr 2019 abzuschließen.
Zu jedermanns Schock und Bestürzung begann die Große Panik von 2020 (mein Ausdruck) einen Monat später im Januar.
https://uncutnews.ch/warnung-2022-der-krieg-der-technokratie-gegen-die-menschheit-wird-fortgesetzt/
Zero by Gooken noticed "Universal Linux" errata since 2021
"Why Linux is better than Windows", leading expert Cosinus from trojaner-board.de, 2007 up to now (2021)
The quit endless Windows-failure-lists - All the problems of MS Windows users
https://www.trojaner-board.de/sitemap/f-16.html
https://www.trojaner-board.de/sitemap/f-16-p2.html
https://www.trojaner-board.de/sitemap/f-16-p3.html
...
...
https://www.trojaner-info.de
...
"The internet must get away!"
Schlecky Silberstein surfs in our filterbubble
Christian Brandes aka Schlecky Silberstein would like to forbid this medium, that feeds him. In "The internt must get away" the blogger describes, how we get misused and brainwashed by algorithms, trolls and tech-companies. But isn´t he a part of it too? A recension.
https://netzpolitik.org/2018/schlecky-silberstein-surft-in-unserer-filterbubble/
Reader opinion by Gooken
Many people share this opinion, so what´s wrong with it?.
Expert about privacy: "I always ask myself, why the people do still make this through", STERN.de, 06.09.2019
Marc Al-Hames knows all tricks about the advertisment industry. In an interview with the Stern he explained, why sudden confessions for data-protection of some companies can not be taken seriously and tells us about the defference between Apple and Google in the point data protection.
[...]."Facebook for example never understood privacy matters up to now."
[...] "Surveys showed the biggest amount of user not reading business conditions (AGB) and to follow the ones, who want."
https://www.stern.de/digital/online/datenschutz---die-
werbe-industrie-kann-uns-ueber-alle-geraete-hinweg-verfolgen--denen-entgeht-nichts--8723748.html
Hacker organize themselves more and more professionelly, trojaner-info.de, 12.22.2021
Im Laufe des Jahres 2021 haben Cyberkriminelle ihre Untergrund-Ökosysteme immer besser organisiert, sodass im neuen Jahr mit noch professionelleren Angriffsmustern gerechnet werden muss.
Insbesondere Ransomware-Gruppen suchen laut den Sicherheitsexperten von Radware zunehmend Verbündete unter erfahrenen Auftragshackern, die sich über die Gewinne aus großen Erpressungskampagnen freuen.
https://www.trojaner-info.de/daten-sichern-verschluesseln/
aktuelles/hacker-organisieren-sich-immer-professioneller.html
Scoring
You must get active! The financial takeover of your bank account- BlackRock, Envestnet/Yodlee and the Federal Reserve, uncut-news.ch, 08.16.2021
coreysdigs.com: Haben Sie schon einmal von Yodlee gehört? Ich auch nicht, bis ich entdeckte, dass das Unternehmen meine Daten in meinem Bankkonto sammelt und sie wahrscheinlich an Dritte verkauft. Dies wurde schnell zu einer persönlichen Recherche, bis ich erschütternde Zusammenhänge entdeckte, von denen ich erkannte, dass die Öffentlichkeit darauf aufmerksam gemacht werden muss. Bevor Sie beschließen, dass dies nichts mit Ihnen zu tun hätte, bitte ich Sie dringend, diesen Artikel in seiner Gesamtheit zu lesen und die zeitlichen Abläufe genau zu beachten, denn dies betrifft SIE ALLE, und es wird in mehreren Ländern eingeführt. Ich empfehle Ihnen, sich bei Ihrer Bank zu erkundigen und herauszufinden, welche Drittparteien in Ihre Konten verwickelt sind, und die Möglichkeit in Betracht zu ziehen, Ihre Gelder zu einer kleineren lokalen Bank zu transferieren. Hier geht es nicht nur um Spionage und Datenaggregation, sondern um einen strukturellen Aufbau, der uns in das System der Sozial- und Klimabilanz und noch darüber hinaus bringen soll. Und Biden schreibt die Anordnungen, um den Rahmen zu schaffen, den BlackRock ausgearbeitet hat.
Untersuchen Sie Ihre Bank, Finanzinstitute und Ihre Konten
Kurze Zusammenfassung
Um es kurz zusammenzufassen: Mir war aufgefallen, dass mein Bankkonto meine Ausgaben plötzlich in Gruppen wie Einkommen, Gesundheit &Fitness, Essen &Trinken, Reisen, Dienstleistungen für Unternehmen, Haustierbedarf usw. einteilte. Mir war sofort klar, wohin das führen würde, und ich ärgerte mich besonders über die Kategorie "Einkommen", in der Gelder falsch ausgewiesen wurden, die auf Drängen der Marionette Biden direkt an das Finanzamt weitergeleitet werden sollen. Um ein soziales Punktesystem dafür zu schaffen, wie und wo man sein Geld ausgeben kann oder Zugang zu Orten oder Dienstleistungen erhält, und damit die Regierung jeden ausgegebenen Cent ausspionieren kann, muss zunächst eine Struktur aufgebaut werden. Ich habe schnell nach dem Haftungsausschluss von Drittanbietern gesucht, um zu sehen, wer meine persönlichen Finanzdaten organisiert, und fand: "Kontoaggregationsdienste werden von Yodlee, unserem Drittanbieter, bereitgestellt. Die Daten werden von Yodlee bezogen oder manuell eingegeben". Ich ging dann zu dem Abschnitt, der es angeblich ermöglicht, die Weitergabe von Daten einzuschränken, aber die Einschränkung von Yodlee war keine Option. Ich rief meine Bank an und fragte, wann der Vertrag begann, und mir wurde gesagt, 2017. Ich fragte, was Yodlee außer dieser neuen Kategorie-Aggregation noch mit meinem Bankkonto zu tun hat, und mir wurde mitgeteilt, dass sie nichts finden konnten. Ich fragte, ob sie meine Daten verkaufen würden, und der Mann wusste es nicht. Ich bat darum, die Daten zu löschen, und mir wurde gesagt, dass sie das nicht tun können. Ich erklärte, dass ich meine Konten schließen werde, wenn sie das nicht tun können, und wollte mit einem Manager sprechen. Mir wurde gesagt, ich würde einen Anruf erhalten. Das geschah nie, und Sie können darauf wetten, dass ich meine Gelder verschoben habe.
Wie Sie in der Zeitleiste unten sehen werden, ist Yodlee einer der größten Finanzaggregatoren, der auch Ihre Daten verkauft und gegen den eine Sammelklage läuft, aber das wird diesen Zug nicht aufhalten. Das Unternehmen wurde 2015 von Envestnet übernommen. Zum Vergleich: Envestnet arbeitet mit 17 der 20 größten Banken sowie mit 5.200 weiteren Banken, Finanzinstituten und Unternehmen zusammen. Sie betreuen 4,8 Billionen US-Dollar an Vermögenswerten, verwalten 229 Milliarden US-Dollar an Vermögenswerten und betreiben mehr als 2 Millionen Finanzpläne pro Quartal. Envestnet betreut täglich 500 Millionen aggregierte Konten.
Drei Jahre später, im Jahr 2018, erwarb BlackRock, der weltweit größte Vermögensverwalter, eine Kapitalbeteiligung an Envestnet und ging eine Partnerschaft mit dem Unternehmen ein, um seine Technologie mit der von Envestnet zu integrieren. Im darauffolgenden Jahr kamen der CEO von Envestnet und seine Frau bei einem tödlichen Autounfall ums Leben, kurz nachdem der "Going Direct"-Reset unterzeichnet worden war. Nur wenige Monate später beantragten drei Demokraten eine FTC-Untersuchung gegen Envestnet/Yodlee wegen Bedenken hinsichtlich des Datenschutzes für die Verbraucher (das ist lustig), wodurch Envestnet im Wesentlichen unter Druck gesetzt wurde. Dies ist nur die Spitze des Eisbergs, aber es ergibt sich ein gutes Bild, wenn man die nachstehende Zeitleiste betrachtet. Diese Zeitleiste hätte weit über 30 Seiten lang sein können, um die Beteiligung von BlackRock zu erläutern, da sie die NWO-Finanzshow leiten - aber dies ist dazu gedacht, das Bewusstsein der Menschen zu schärfen, damit sie ihre eigenen Banken untersuchen und selbst Entscheidungen darüber treffen können, mit wem sie Bankgeschäfte tätigen und wie sie ihre Finanzdaten und Finanzen schützen wollen.
BlackRock hat drei hochrangige Positionen im Weißen Haus inne, verwaltet 7,8 Billionen Dollar an Vermögenswerten anderer Leute und ist damit der größte Vermögensverwalter der Welt. Der Konzern ist unter den drei größten Anteilseignern aller großen Unternehmen und Branchen (sehen Sie selbst nach), investiert in großem Umfang in den "Klimawandel", meidet fossile Brennstoffe und hat einen Großteil seiner Konkurrenz verschlungen. Die Spitzenreiter BlackRock und Vanguard werden bis 2027 voraussichtlich 20 Billionen Dollar verwalten. Es ist keine Überraschung, dass BlackRock und das Weiße Haus in den Regierungen Clinton, Obama und Biden eine Drehtür hatten und haben. Nicht nur das Personal wechselt zwischen den beiden Unternehmen, auch Vorstandsmitglieder von BlackRock wie Cheryl Mills, die während der Zeit der Clintons im Weißen Haus für beide tätig war, scheinen zu BlackRock überzulaufen. Sie sind die Entwickler des "Going Direct Reset" und helfen, den Weg zu ebnen.
Unter dem Deckmantel der "finanziellen Wellness" und des "klimabedingten Finanzrisikos" haben sie die Finanzindustrie dazu gebracht, die Finanzdaten aller Menschen zu rationalisieren und zu überwachen, so dass sie sie durch ein soziales Bewertungssystem kontrollieren, Ihnen sagen können, wie und wo Sie Ihr Geld ausgeben sollen, und das, was ihrer Meinung nach an das Finanzamt gehen sollte, abschöpfen können. Darüber hinaus werden Billionen von Dollar den Besitzer wechseln, von den älteren Menschen zu den Millennials - und diese Leute haben in all dem ihre Finger. Schauen Sie sich den kompletten Zeitplan an, um zu verstehen, wie sich all diese Maßnahmen auf alle auswirken.
Wie ich bereits letztes Jahr anmerkte - als die Stimulus-Schecks direkt eingezahlt wurden - geschah dies, um eine umfassendere Datenbank zu erstellen, als sie sie bereits über die Bankkonten der US-Bürger angelegt hatten. Das war nur ein weiterer Baustein in ihrem großen Plan. Es ging nie darum, Groschen auf Ihr Konto zu bekommen, um Ihnen zu "helfen". In diesem Zusammenhang gelang es den PPP-Kleinunternehmensdarlehen auch, Finanzdaten über Kleinunternehmen und Landwirte im ganzen Land zu erhalten.
Dies war der größte manipulierte Vermögenstransfer, den dieses Land je erlebt hat. Das Jahr 2020 wird kristallklar werden, wenn Sie diesen gesamten Bericht gelesen haben.
"Einblicke" = Überwachung und Kontrolle
Wenn Sie sich Ihr Bankkonto ansehen, suchen Sie nach "Drittanbietern" und "Aggregatoren". Vielleicht stoßen Sie auf eine Erklärung wie die meiner Bank, warum sie Ihre Daten sammelt. Sie verpacken das Ganze mit viel Schnickschnack und suggerieren, dass sie das für Sie tun … "Sie möchten vielleicht, dass wir Ihnen nützliche Einblicke in Ihre Finanzen liefern …, damit Sie klügere finanzielle Entscheidungen treffen können." Wieder einmal wird Ihnen versichert, dass Sie nicht intelligent genug wären, um Ihr eigenes Geld zu verwalten, so wie Sie ein intelligentes Haus, ein intelligentes Telefon und eine intelligente Stadt brauchen, um zu überleben.
DIES ist der Rahmen für das soziale Punktesystem. So wird es gemacht: Indem man Ihre Gelder auf Ihren Bankkonten kategorisiert und gleichzeitig ESG-Bewertungen (Umwelt, Soziales und Unternehmensführung), die von anderen Finanzinstituten vorgenommen werden, in Bezug auf Investitionen zuweist. Diese werden wahrscheinlich auch auf Ihre Bankkonten angewendet werden, insbesondere mit Bidens neuer Durchführungsverordnung.
Die Kategorie "Einkommen" wird zwar nicht in der Dropdown-Liste aufgeführt (zumindest bei meiner Bank), aber sie ordnet verschiedenen Einlagen "Einkommen" zu, auch wenn es sich nicht wirklich um Einkommen handelt, was unter den einzelnen Einlagen ersichtlich ist. Letztendlich werden sie auch eine "ESG"-Spalte für klimabezogenes Tracking einrichten.
Sehen Sie sich diese 6-1/2-minütige Videozusammenfassung an, die The Sharp Edge auf der Grundlage dieses Berichts produziert hat. Es enthält zwar nicht alle Details in der ausführlichen Zeitleiste unten, fasst aber vieles über diese finanzielle Übernahme zusammen.
Die Zeitleiste spiegelt die wichtigsten Aktionen von BlackRock, Envestnet/Yodlee, Biden, der Federal Reserve, dem US-Finanzministerium, den Banken und dem IRS wider.
Diese Zeitleiste zeigt Ihnen nicht nur, wie diese Aggregatoren Ihre Daten abgreifen, weitergeben und den Rahmen für ein Sozial- und Klimabewertungssystem schaffen, sondern auch, wer dahinter steckt, wie sie diese Show veranstalten und wohin sich dieses Spiel entwickelt.
Auf diese Weise zielen Envestnet und wahrscheinlich alle Finanzinstitute darauf ab, dass die Menschen "die digitale Revolution annehmen". Sie sehen Millennials als "gewöhnt an Technologie und soziale Medien, und sie wollen nichts anderes, wenn es um ihr Finanzleben geht."
1999
Envestnet wurde gegründet
Judson Bergman und Bill Crager gründeten Envestnet in Chicago, Illinois, und haben inzwischen Niederlassungen im ganzen Land. Sie verfügen über zahlreiche Marken, die alle von Faegre Drinker Biddle &Reath LLP, nur eine halbe Meile von ihrem Büro entfernt, eingetragen wurden. Envestnet hat im Laufe der Jahre eine ganze Reihe von Unternehmen übernommen, darunter FolioDynamix, FDX Advisors, PIEtech MoneyGuide, Yodlee und andere.
1999
...
https://uncutnews.ch/sie-muessen-jetzt-ativ-werden-die-finanzielle-uebernahme-ihr-
bankkonto-blackrock-envestnet-yodlee-und-die-federal-reserve/
George Orwell´s "1984" became to blueprint cyanotype for our dystopical reality, uncut-news.ch, 07.01.2021
Population control and the new world order (NWO)
Von John W. Whitehead & Nisha Whitehead
"If you want to get an image of our future, imagine yourself a boot treading upon a face - all the time.", George Orwell, 1984
28. Juni 2021, The Rutherford Institute
Read it with care: George Orwells (25. Juni 1903 - 21. Januar 1050) fiction became a manual for the modern, omnipresent surveillance state.
More than 70 years ago, Orwell, dying with fever and bloody fit of coughings - urged to warn in the roman 1984 against the arise of a society, the unhalted misuse of power and mass maniipulation, faschism and totalitarity as a result of the increasing use of technology.
https://uncutnews.ch/george-orwells-1984-wurde-zur-blaupause-fuer-unsere-dystopische-wirklichkeit/
 World Economic Forum / Cyber Polygon: Power off each device from the internet, uncut-news.ch, 06.29.2021 World Economic Forum / Cyber Polygon: Power off each device from the internet, uncut-news.ch, 06.29.2021
A little video intimating the solution for protection of the Cyber Poligon Simulation for each possible "cyber attack" as an aim for the event: The abolition of the internet.
https://uncutnews.ch/world-economic-forum-cyber-polygon-jedes-einzelne-geraet-vom-internet-trennen/
Increasing amount of cyberattacks
Clinics in the visor of hacker, tagesschau.de, 28.06.2021
https://www.tagesschau.de/wirtschaft/technologie/cybersicherheit-infrastruktur-hacker-kliniken-cybercrime-101.html
 Microsoft does not have to fear a class action lawsuit against Windows 10, PC-WELT.de, 11.30.2015 | 14:41 o´clock | Denise Bergert Microsoft does not have to fear a class action lawsuit against Windows 10, PC-WELT.de, 11.30.2015 | 14:41 o´clock | Denise Bergert
#WE#TOO: Computer - es geht (ging) kaum noch kaputter: Company smashing of Facebook, Googke, Amazon, Microsoft, Intel (Meltdown&Spectre), Apple and many more west-companies multi-times postulated by many organistations and persons
Details in future!
Betrayer&1#8;s getting serious hard to investigate
Hunderte Spendenmillionen versickern, tagesschau.de, 09.07.2019
Nach Recherchen von Report Mainz werden jedes Jahr Hunderte Millionen Euro an Spendengeldern nicht ordnungsgemäß verwendet. Die Rechtslage macht es Betrügern dabei leicht.
https://www.tagesschau.de/investigativ/report-mainz/spendenbetrug-101.html
"I have never been betrayed like that!"
#34c3: The eavesdropping programs of the secret services, netzpolitik.org, 29.01.2018
"Ich bin noch nie so belogen worden", sagte Hans-Christian Ströbele über seine Arbeit im NSA-BND-Untersuchungsausschuss. In einem Gespräch mit Constanze Kurz resümiert der grüne Politiker die Ergebnisse der parlamentarischen Untersuchung.
https://netzpolitik.org/2018/34c3-die-lauschprogramme-der-geheimdienste/
Expert about privacy: "I always ask myself, why the people do still make it through", STERN.de, 09.06.2019
Marc Al-Hames kennt alle Tricks der Werbeindustrie. Im Gespräch mit dem Stern erklärt er, warum die plötzlichen Datenschutz-Bekenntnisse einiger Konzerne nicht ernstzunehmen sind und was der größte Unterschied zwischen Apple und Google in puncto Datenschutz ist.
[...]."Facebook zum Beispiel hat Privatsphäre nie verstanden und versteht sie auch jetzt nicht."
[...] "Umfragen zufolge liest der Großteil der Nutzer keine Geschäftsbedingungen und stimmt allen Anfragen zu."
https://www.stern.de/digital/online/datenschutz---die-werbe-industrie-kann-
uns-ueber-alle-geraete-hinweg-verfolgen--denen-entgeht-nichts--8723748.html
 Unwanted agreements Unwanted agreements
Howto change your data settings for more privacy at Telekom, Vodafone and o2, netzpolitik.org, 05.08.2021
https://netzpolitik.org/2021/ungewollte-dsgvo-einwilligungen-
so-aenderst-du-deine-datenschutzeinstellungen-bei-telekom-vodafone-und-o2/
 Innvoation of Apple Innvoation of Apple
No tracking anymore - what does it mean?, tagesschau.de, 04.28.2021
What does come new with iOS 14.5?
https://www.tagesschau.de/wirtschaft/unternehmen/apple-tracking-faq-101.html
... might be simliar to the computer...:
 According to a study smartphones do share our data each four and a half minute, uncutnews, 31.03.2021 According to a study smartphones do share our data each four and a half minute, uncutnews, 31.03.2021
https://uncutnews.ch/laut-einer-studie-teilen-smartphones-unsere-daten-alle-viereinhalb-minuten/
 Android-Studie of Professor Leith: Google-Handies do send away twenty times more data than iPhones, CHIP, 04.04.2021 Android-Studie of Professor Leith: Google-Handies do send away twenty times more data than iPhones, CHIP, 04.04.2021
Android-malware: Howto protect users against fake-updates
https://www.chip.de/news/Brisante-Android-Studie-enthuellt-Google-Handys-geben-
20-Mal-mehr-Daten-weiter-als-iPhones_183434034.html
https://www.pcwelt.de/news/Android-sammelt-laut-Studie-20-mal-mehr-Daten-als-iOS-11004792.html
Except from non-profit organziation (that still should be viewed upon in News&Links critically) and some Raspberries, secure tor-relais (entry guards and exit nodes) are serious hard to find!
Digitalcourage e.V., digitalcourage.de
Since 1987 Digitalcourage e.V. is engaged in basic rights, data (privacy) protection and a livable world in the digital age. We are technique affine, but defend against our democracy getting "given away and sold out".
Since year 2000 we confer BigBrotherAwards. Digitalcourage is non-profit, financed by spends and is living from non-profit work. More about our work:
https://digitalcourage.de
https://digitalcourage.de/blog/2020/macht-der-digitalkonzerne#10
Get more to know about Digitalcourage from News&Links too!
 During my last updates few days ago I have noticed the following ... under system - securityt ... each steps one does, goes and went, each side, even outside of the www...., is stored in the background, by date, time and location !, Pia Berling @ krone.at, 24.11.2020 During my last updates few days ago I have noticed the following ... under system - securityt ... each steps one does, goes and went, each side, even outside of the www...., is stored in the background, by date, time and location !, Pia Berling @ krone.at, 24.11.2020
Go into the system settings (system control) and deactivate all ticks!
Then delete under the action history, that is part of a network with the Google account and others!
But there is still not any gurantee, that your activities won´t be prosecuted completely anymore... at least one has done something against it!
My opinion is, that it is a good thing to deactivate the total eavesdropping.. by deactivating Cortana ( Linux-aquivalent to krunner and akonadi -> includes of akonadi through akonaditray) ... (what I all have already made long ago), to put of the cameras too, to use them only, if really needed! ... and further on ...
https://www.krone.at/2282872
Software combine SAP
With data theft to the too of the world?, tagesschau.de, 11.12.2021
Nach Recherchen von Fakt und dem "Spiegel" könnte der Diebstahl von geistigem Eigentum durch SAP eine lange Tradition haben. Bereits von 1997 bis 2008 soll der Konzern in Kooperation mit Universitäten Entwicklungen von Mitbewerbern missbraucht haben.
Neu aufgetauchte interne Dokumente werfen einen düsteren Schatten auf den Softwarekonzern SAP, dessen Management und den Aufsichtsrat. Nach Recherchen des ARD-Magazins Fakt und des "Spiegel" drängt sich das Bild eines Unternehmens auf, das sich offenbar auch mit unlauteren Methoden, vor allem Diebstahl geistigen Eigentums, an die Weltspitze getrickst hat.
Die Vorgänge reichen bis zurück in die 1990er-Jahre und sind in einem Gutachten der Wirtschaftskanzlei Linklaters von 2010 festgehalten. In Auftrag gegeben hatte es SAP selbst.
Hintergrund war der damalige Rechtsstreit mit Oracle. Der US-Erzrivale hatte SAP 2007 verklagt, weil die Deutschen durch die Übernahme des Softwaredienstleisters TomorrowNow an urheberrechtlich geschützte Dateien von Oracle-Servern herangekommen waren. In einem Vergleich musste SAP später 357 Millionen Dollar Schadenersatz an Oracle zahlen.
Im Zentrum steht ein Hopp-Vertrauter
Das Linklaters-Gutachten sollte klären, ob Haftungsansprüche gegen den damaligen Vorstand Gerhard Oswald bestehen - Oswald war für die TomorrowNow-Übernahme zuständig. In dem Dokument finden sich zahlreiche Hinweise darauf, dass Oswald und einer seiner Mitarbeiter von Urheberrechtsverletzungen wussten. Zudem soll der damalige SAP-Vorstand unter CEO Henning Kagermann alles gebilligt haben.
Die Konzernspitze zog aus dem Gutachten indes keine Konsequenzen. Oswald wurde sogar befördert, obwohl die Linklaters-Juristen empfohlen hatten, sich von ihm "geräuschlos" zu trennen. Oswald, ein Vertrauter von SAP-Gründer und Großaktionär Dietmar Hopp, blieb bis 2016 im Vorstand und sitzt seit 2019 im Aufsichtsrat.
Dubiose Kooperation zwischen Uni Mannheim und SAP
Fakt und "Spiegel" berichten zudem über eine dubiose Kooperation von SAP mit der Universität Mannheim ab 1997, bei der abermals Oswald eine zentrale Rolle spielte. Auch sie ist Gegenstand des Gutachtens. Offiziell ging es bei der Kooperation darum, Konkurrenzsoftware durch ein unabhängiges Institut untersuchen zu lassen, in diesem Fall die Forschungsgruppe Wirtschaftsinformatik der Uni Mannheim. Tatsächlich hätten SAP-Mitarbeiter unter dem Deckmantel der Kooperation die Konkurrenz ausspioniert. Selbst Interventionen der Rechtsabteilung, des Compliance-Teams und der Revision seien weitgehend ignoriert worden.
Nach Informationen von Fakt und "Spiegel" zog SAP bis vor das Bundesverfassungsgericht, um die Staatsanwaltschaft Mannheim daran zu hindern, das Gutachten als Beweis in einem Ermittlungsverfahren gegen die SAP-Vorstände wegen Urheberrechtsverletzungen zu verwenden. Die Beamten waren auf das Dokument 2011 bei einer Razzia in der Konzernzentrale gestoßen.
Das höchste deutsche Gericht nahm die Verfassungsbeschwerde seinerzeit nicht an. Das Strafverfahren gegen die Vorstände wurde Ende 2017 eingestellt, SAP musste allerdings 250.000 Euro an die Staatskasse zahlen.
SAP teilte auf Anfrage mit, die Urheberrechtsverletzungen von TomorrowNow seien Gegenstand des Verfahrens mit Oracle gewesen, das einvernehmlich beigelegt wurde und abgeschlossen sei. Die Vorgänge rund um die Universität Mannheim seien intern umfassend aufbereitet worden. Der Schutz geistigen Eigentums bilde das Fundament aller SAP-Lösungen.
https://www.tagesschau.de/investigativ/mdr/sap-geistiges-eigentum-101.html
United Absurdistan - Judas Judäa - USA-81/82/1911/The Empire- US-republicans (quot;the farmer-party") & Co.
Do we all have to mutate now (since 1981/82) into his (labor-)rats or pigs, cows and battery chickens?
... in order to create and fead the growing big elefant in dizzier and dizzier heights?, someone once wanted to know.
Clever and Smart, NY83 (oh, by the way company foundation year of Microsoft...): "The next number without net!"
 Allicance: Five Eyes, Nine Eyes, ... Allicance: Five Eyes, Nine Eyes, ...
"We kill people on the base of meta-data"
Hacking and Eavesdropping, netzpolitik.org, 02.24.2020
https://netzpolitik.org/2020/ist-whatsapp-sicher-genug-fuer-die-diplomatie/
https://netzpolitik.org/2020/is-whatsapp-safe-for-diplomats/
Linux
"Üh, äh, böh: This is as stupid as Windows!", trojaner-board.de, Linux Forum
 "Thank you, Linux, you have made Microsoft rich!" "Thank you, Linux, you have made Microsoft rich!"
Hard to install Linux, hard to configure, hard to secure it really up, many updates, not all device drivers, discussable design, changing libraries, unsolved dependencies, missing software for special professional business work...
Debian based on the package-manager dpkg, syncatpic and just the for a long time based awful rare feautered, shaby aptitude, while Mandriva awaits with rpm, urpmi, yum and the user-friendly drakconf for administration ...
System crashed serious hard up to dbus-update from year 2019.
KDE caused system breakdowns. It got stable for the first time since a python-update in 2016.
A lot of lacks in security and weak points (exploits) had to be solved.
Welcome in the virtual world - Security and more in the internet, trojaner-info.de, 12.07.2021
The internet has changed the society inherently. Not just 50 years before, the telephone set in the own house was seldom.
Today billions of people are surfing each day in the internet, what has led into plenty of changes in many sectors. If advertisement, if criminality, all this happening in the real world became partially true within the net. But how can you protect against its criminality and what advantages does the web provide for companies?
[...] There are plenty of betraying methods and criminalse got more und more inventive. Indeed, meanwhile authorities found out the machination and police authorities have got more and more to do with the inverstigation in virtual crime. However wants to achieve a high security level must pay attention to many important factors.
https://www.trojaner-info.de/business-security/aktuell/
willkommen-in-der-virtuellen-welt-sicherheit-und-mehr-im-internet.html
Our LONGTERMED-kernel: kernel-5.4.269-pclos1 (pclos2024) from PCLinuxOS (pclos), kernel-lt-5.4.219-1.el7.elrepo.x86_64 with perf (el7.elrepo) from Yandex.ru, https://ftp.yandex.ru/elrepo/kernel/el7/x86_64/RPMS/
[ UNSOLVED: kernel-5.4.134 and actual kernel-5.4.151: unwanted root-processes got highly active causing many readwrites onto harddisc, whenever starting Pale Moon and tor (el7, rosa2016.1) each surrounded by firejail (OpenSuSE 15.2) ]
E-mail from Gooken to kernel-maintainer Greg Kroah-Hartmann gregkh@linuxfoundation.org and other Linux-kernel-experts
Date: 07.24.2021
Subject/Betreff: Unwanted hyperactive root-processes reading and writing out the whole SSD/harddrive ! / Kernel-5.4.134 (pclos) -> Apparmor / Tor (OpenSuSE) usw. etc.: Freigabe von Informationen, Ausführen von Code mit höheren Privilegien und beliebiger Kommandos in Linux, Erzeugung, Lesen und Überschreiben beliebiger Dateien
Hi, Greg, dear Linux experts and friends,
this is one of the most dangerous and worst things, Linux can happen!
Refering to the actual kernel 5.4.134 ( now up to the actual version 5.4.151 and higher, additional remark from 10.08.2021), there still is a problem with root-processes activated running highly active (making the tower-LED causing readwrites onto harddiscs and making the SSD/harddrive blink serious-madly hard during up to 20 minutes). The whole SSD/harddrive seems to get read out and overwritten!
The unwanted, highly by tor (pclos, mga7) resp. firejail activated kernel-root-processes are named
kworker/u2:1-kcryptd/253:2 (escpecially this one, CPU: gt; 10%, sometimes over 3600 % measured by ksysguard)
kworker/0:1H-kblockd
dmcrypt_write/2 and
jbd2/dm2--8
Now these processes (that might always get activated) make up the system (of the processes) through their unexpected high activity greater all other ones, even X11/X, making the LED for readwrites of my tower always blink !
This occurs since kernel around 5.4.134 (and again in 5.4.151), whenever I start browsing (with Pale Moon), activating firejail and tor (el7) too. Both, Pale Moon and tor are always started within firejail. The LED seems to blink (and processes work such active) until tor builds up the connection to a Guard node.
Please patch the kernel-5.4 to prevent it in future!
Please patch the kernel-5.4 to prevent it in future!
Regards
Gooken
Appendix
libapparmor.so.required by firejail (OpenSuSE 15.X) needed by tor (rosa2016.1, mga7) must be the cause for the activation as much as high activity of some root-processes!
I have got no other explanation.
Kernel security module apparmor itself got deactivated within the kernel by my boot-parameters "security=none" and "apparmor=none".
After tor and firejail version got changed from OpenSuSE 15.X to mga7 (firejail) resp. to CentOS el7 (Tor), so that libapparmor.so.1 is not required anymore, such root-processes did not get activated resp. active too much!
But they did appear unexectedly again in kernel-5.4.151 !
Restoring Linux with kernel-5.4.150 from my rescuing media (one more 128GB-SSD), this problem disappeared - no such root-processes started. But I do not believe it got really solved by this or generally!
So I still await your patches for kernel-5.4.
Regards
Gooken
Thanks a lot for your answer!
No, no malware, all is linux (rpm) checked well,
no, nothing can cause it - except, as you wrote, a browser-extension.
I do believe more in firejail as the reason.
Yes, Pale Moon starts within sandbox firejail and the start envokes tor too. An extension or firejail might be faulty, but why should kernel-root-processes react that way each time Pale Moon gets started?
The kernel should find out it itself, not making himself to such threatening jerk, whenever the user just wants to surf in the internet!
Regards
Gooken
10.27.2021
Hello, today it manages us (Gooken) to prevent the highly active kernel-processes from above after a look into the home-directory of tor (/home/surfuser).
There the size of a file increases all the times during the activation of tor surrounded by firejail (that causes the high activity of the kernel-processes), it is named:
cached-microdesc-consensus
and its size was incredible high (much over 100 MB)!
It prevents Tor from building up any connection, so I had to wait up to 20 minutes.
Deleting it did not help: This file occured and larges its size again.
So we set integrity on it (this file) by "chattr +i" and belonging firejail-rule. Now the problem described next indeed got solved, Tor immediately builds up connections, kernel-processes activity lowered to the current percentage far below 10 percent and the tower-LED for readwrites stopped blinking,
but nevertheless this is not really a good solution,
tor or firejail and kernel (here 5.4) of course still have to get patched ! ( !!! )
------------------------
[ UNSOLVED : Linux, all kernel, all LUKS (cryptsetup): Already the login for the mount of the LUKS-encrypted root-partition during the boot each trial fails !, Gooken, 06.06.2022 ]
This happens because of the wrong coding of special chars making up the password typed in from keyboard, so that the paragraph sign ("§" might be taken as a "#" and further more.
Even the further below mentioned assignments through setkey of such special chars to the meant ones (like paragraph sign for # and further more) in /boot/grub/menu.lst from below, does not help here anyhow!
The only thing to get logged into the system for the decryption of the LUKS-encrypted root-partition one can do is typing in the character following such assignments, so that the paragraph sign and further more is understood as they should. So make yourself confident with the character sets from keyboard how they got really get understood by Linux. We hope, this all gets patched one d
/boot/grub/menu.lst:
setkey y z
setkey z y
setkey Y Z
setkey Z Y
setkey equal parenright
setkey parenright parenleft
setkey parenleft asterisk
setkey doublequote at
setkey plus bracketright
setkey minus slash
setkey slash ampersand
setkey ampersand percent
setkey percent caret
setkey underscore question
setkey question underscore
setkey semicolon less
setkey less numbersign
setkey numbersign backslash
setkey colon greater
setkey greater bar
setkey asterisk braceright
timeout 10
password --md5 ...
default 0
title 008win1smp
password --md5 $.../
...
[ UNSOLVED: Kernel-5.10.52 (pclos, PCLinuxOS) causes restarts during the boot of KDE (4.3.4, 4.4.9 and 4.4.11-update-mix out of el6-mdv2010.2-OpenSuSE11.2-kukuk) right before the KDE-welcome-sound is played ] and udev-hotplug does not exist anymore
This problem remained unsolved: Using Kernel 5.4, this problem got not solved by us, Gooken.
Maybe this kernel gets patched by linuxfoundation in future.
IT-Security is the kind of "game"; to reach the highest IT security level as possible. Its aim is to escape from the sun-eating of the evil suneater ("computer"), by mutating him (the suneater resp. "computer") into a real computer - including its boundarires resp. connections within all his nets... ( do not ask us for all the people having already lost this "game" ...). We´d like to play it in the manner of the popular game "Mensch-ärger-Dich-nicht": hook by hook :
 Gooken provides 1000% IT-security: Just follow these green hooks! Gooken provides 1000% IT-security: Just follow these green hooks!
Lifetime-hardware from our data sheed: mouseclick-fast upon Celeron
 Tip from CHIP: Resign from MS Windows, CHIP, 18.09.2020 Tip from CHIP: Resign from MS Windows, CHIP, 18.09.2020
We do have a special security tipp for you. Whoever wants to protect effectively, says Windows good bye, in order to restrict hackers the room for attacks.
https://www.chip.de/artikel/Sicherheit-im-Internet-top-5-Tipps-der-NSA_182985028.html
But the enourmous advantage of the "reference-highschool-operating-system" UNIX/Linux: opensource, high support with updates, all kind of software of all rubriques and coleur, especially server (like httpd/Apache) and databasis (like MySQL): all inclusive. 1000% security can be achieved, as we are going to describe here!
 Notice: IP2Location C library enables the user to get the country, region, city, coordinates, ZIP code, time zone, ISP, domain name, connection type, area code, weather info, mobile carrier, elevation and usage type from any IP address or hostname. This library has been optimized for speed and memory utilization. The library contains API to query all IP2Location LITE and commercial binary databases. Users can download the latest LITE database from IP2Location web site using e.g. the included downloader. Notice: IP2Location C library enables the user to get the country, region, city, coordinates, ZIP code, time zone, ISP, domain name, connection type, area code, weather info, mobile carrier, elevation and usage type from any IP address or hostname. This library has been optimized for speed and memory utilization. The library contains API to query all IP2Location LITE and commercial binary databases. Users can download the latest LITE database from IP2Location web site using e.g. the included downloader.
https://fr2.rpmfind.net
 You are looking for good (secure anyonymizing) tor nodes, good entry-, middle- and good exit relais, of NGOs from secure countries? Then you are at the right place here and within our section News&Links! You are looking for good (secure anyonymizing) tor nodes, good entry-, middle- and good exit relais, of NGOs from secure countries? Then you are at the right place here and within our section News&Links!
 In contrast to the all in all quit compact, a registration requiring Debian Gooken presents a complete, especially a concrete solution for real security in concept on the base of UNIX-Linux-filesystems like ext4, btrfs and reiserfs. A lot of points and links refer to sources from Debian, while they got changed into more concrete methods - following the right security concepts. Also we did not like dpkg much in comparison with rpm same in design, structure and detail for the belonging packet-search-engines debian.org versus rpmfind.net with mirrors like r2.rpmfind.net. Too many clicks have to be made for Debian until a download of a package really starts. Methods sink down in very much hugh-large theory and all its possibilities in Debian. In contrast to the all in all quit compact, a registration requiring Debian Gooken presents a complete, especially a concrete solution for real security in concept on the base of UNIX-Linux-filesystems like ext4, btrfs and reiserfs. A lot of points and links refer to sources from Debian, while they got changed into more concrete methods - following the right security concepts. Also we did not like dpkg much in comparison with rpm same in design, structure and detail for the belonging packet-search-engines debian.org versus rpmfind.net with mirrors like r2.rpmfind.net. Too many clicks have to be made for Debian until a download of a package really starts. Methods sink down in very much hugh-large theory and all its possibilities in Debian.
Gooken&#s points origin in the cheap, economy and exemplary hardware listed in the data-sheed and by LUKS/dm-crypt/cryptsetup encrypted UNIX-/Linux-filesystems, those with useful owner-, group-, and access-rghts). At last an (at this time still not complete) online-(security-)check is possible to check out the browser.
UNIX/Linux is a "password-system". The main idea of UNIX/Linux is the creation of a password-protected account for each in the net communicating program (server or client), the isolation of each account from other ones resp. the setting of belonging access-rights, followed by the configuration of each of such programs (like /etc/httpd.conf for Apache, /etc/squid.conf for Squid and /etc/samba.conf for Samba (LAN) etc.) and the performance of further methods like for the pervention of chrooting by system-configurations and especially sandbox Firejail.
Beneath general system-wide configurations the rights for more or less all of the system-administrator root and similar user resp. accounts have to get restricted too, while normal user accounts can even get locked completely. An important restriction for even root (uid 0 and gid 0) is enpossibled especially by firewall Linfw3, that can completely prevent its net-access!
1000% IT-security: following Gooken always as concrete as possible - not only for Linux, but also for MS Windows and Smartphones (section Smartphones also from left menu) - for Android as much as iPhone!
( This all reminds us inourdays more or less of Trump in the role of the US-president. Many critics against the multiple previous convicted notorious liar have arised and actually do come up, all not feeding concrete enough in the for more then 150 years unchanged state constitution, so that Trump, past maneuvers as the exchange of the judges of the Supreme Court, still was able to beware his role us a legal president of the United States, details see Gooken in section News&Links#Trump ! )
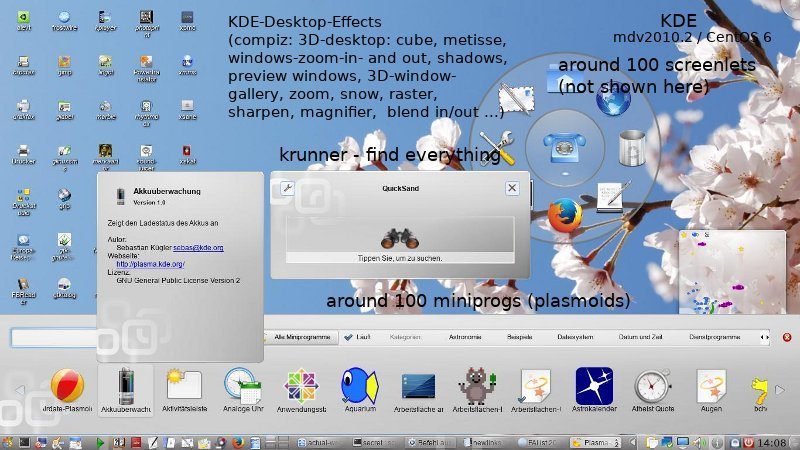
 DIN SPEC 3105 DIN SPEC 3105
Open DIN-norm for open hardware
https://netzpolitik.org/2020/offene-din-norm-fuer-offene-hardware/
Following our excurs, Linux will become a keyword-/password-system!
Get rid of all problems with your computer! You won´t have any troubles with your computer and computer-system anymore! This became really possible since 2010 Enterprise Linux resp. "Universal Linux" was released upon the TÜV Rheinland certified hardware listed in our section data sheed! Only the installation process will make its efforts. Of course you have to update the system with Enterprise Linux:
Gooken presents you "Universal Linux" especially on the base of the longer than 10 years updated Enterprise Linux 6, 7 and 8, CentOS C6, C7,. .. ( Fedora Core, RHEL6, CentOS 6 (same for CentOS 7) resp. Scientific Linux 6 resp. 7) and/or resp. additinally the Mandriva-derviates (Mandriva2010.2-2012, Mageia 1-7, Rosa2014.1, 2016.1, PC Linux OS (pclos)) and some Slackware (slack 14.2) and OpenSuSE (Thumbleweed, 15.2, 15.1, 15.0) including KDE-Desktop-Environment (KDE) and other Desktop Environments - the 1000% secure made computer operating system, full of surface covering, prototyped, almost rpm-based software, incl. emulators for many programs for other operating systems, together with the belonging everlasting lifetime-hardware running mouseclick-fast upon "Universal Linux" on low power consumption and lowest costs listed in data sheed from left menu - and all quit for free!
 gtk3 (el7): gtk3 (el7, rpm -i --force --nodeps), cairo ( el7, rpm -U --force, cairo-gobject (el7), glib2 (el7, beneath glib2 (el6) by rpm -i --force --nodeps), libepoxy (el6, el7), libxkbcommon (el7, rpm -i --force), fontconfig (el7), fribidi (el7), gdk-pixbuf2 (el7), glib2 (el7), harfbuzz (el7), jasper (el7), jasper-libs (el7), libblkid (el7), libexpoxy (el7), libjpeg-turbo (el7), libpng15 (el7), libmount (el7), uuid (el7), libuuid (el7), libwayland-client (el7), libwayland-curser (el7), libwayland-egl (el7), libxkbcommon (el7), libthai (el7), pango (el7), rest (el7) and zlib (el7). pango (el7) won´t let work drakconf (mdv2010.1), file-roller (el6) and palemoon for example. In this case, keep the old libpango (el6) by resigning from libpango out of pango (el7), same for libgio and libgobject of glib2 (e7) and libgdk_pixbuf of gdk_pixbuf2 (el7). If you have problems installing glib2 and gtk3, enpack the rpms and copy their includes (directories and files) manually into the pregiven directories by the command "cp -axf". gtk3 (el7): gtk3 (el7, rpm -i --force --nodeps), cairo ( el7, rpm -U --force, cairo-gobject (el7), glib2 (el7, beneath glib2 (el6) by rpm -i --force --nodeps), libepoxy (el6, el7), libxkbcommon (el7, rpm -i --force), fontconfig (el7), fribidi (el7), gdk-pixbuf2 (el7), glib2 (el7), harfbuzz (el7), jasper (el7), jasper-libs (el7), libblkid (el7), libexpoxy (el7), libjpeg-turbo (el7), libpng15 (el7), libmount (el7), uuid (el7), libuuid (el7), libwayland-client (el7), libwayland-curser (el7), libwayland-egl (el7), libxkbcommon (el7), libthai (el7), pango (el7), rest (el7) and zlib (el7). pango (el7) won´t let work drakconf (mdv2010.1), file-roller (el6) and palemoon for example. In this case, keep the old libpango (el6) by resigning from libpango out of pango (el7), same for libgio and libgobject of glib2 (e7) and libgdk_pixbuf of gdk_pixbuf2 (el7). If you have problems installing glib2 and gtk3, enpack the rpms and copy their includes (directories and files) manually into the pregiven directories by the command "cp -axf".
In order to approach CentOS 7 / SL 7 with CentOS 6 / SL6, you might want to install systemd (el7) too...
EU-finanzierte Cybersecurity-Firma die "anonymes" Schnüffeln und Fernsteuerung von Netzgeräten entwickelt, uncut-news.ch @ rt.com, 16.06.2021
[...] Die Erstellung und Verwendung des verschlüsselten Chats ANOM, der im Mittelpunkt der jüngsten behördenübergreifenden Operation gegen das organisierte Verbrechen stand, wurde als Beispiel angeführt. Die App enthielt einen geheimen Hauptschlüssel, der es den Strafverfolgungsbehörden ermöglichte, Nachrichten im laufenden Betrieb zu entschlüsseln und aufzuzeichnen.
"Wir machen uns Sorgen darüber, dass Geheimdienste Hintertüren haben… Die meisten Leute denken nicht darüber nach, dass Geheimdienste die App tatsächlich erstellen, um Leute zu fangen", sagte der CIA-Whistleblower John Kiriakou kürzlich in einem Interview mit RT über diese Operation.
"Ich denke, wir sollten alle einfach davon ausgehen, dass unsere Kommunikation, auch unsere verschlüsselte Kommunikation, überwacht wird," sagte Kiriakou, der sagte, die Episode war eine ernüchternde Erinnerung über die Grenzen der Online-Privatsphäre für diejenigen, die naiv zu glauben, digitale Nachrichten sind sicher vor Schnüffelei.
Anfang dieses Jahres aktualisierte die EU ihre Regeln für den Export von Technologien mit doppeltem Verwendungszweck, einschließlich Cyber-Überwachungsinstrumenten, um "Menschenrechtsverletzungen und -missbrauch zu verhindern". Die neuen Vorschriften wurden jedoch von Datenschutzorganisationen als zu schwach" eingestuft, um als Schutzmaßnahme zu dienen.
Weder das Unternehmen noch die europäischen Behörden haben auf den Bericht reagiert.
Quelle: EU-bankrolled cybersecurity firm develops intrusive tech that allows ´anonymous´ snooping &remote control of net devices - media
https://uncutnews.ch/eu-finanzierte-cybersecurity-firma-die-anonymes-
schnueffeln-und-fernsteuerung-von-netzgeraeten-entwickelt/
 (Planned in future) Vienna, net-communiciaiton: Free from eavesdropping with the help by quantum physics?, tagesschau.de, 16.12.2018 (Planned in future) Vienna, net-communiciaiton: Free from eavesdropping with the help by quantum physics?, tagesschau.de, 16.12.2018
Whoever communicats in the internet with eachother, he leaves tracks within the internet without fail. Research scientists from Vienna invented a new method making communication free from eavesdropping even in larger networks.
In future the quantum cryptography enables a eavesdrop-free communication in the internet. Researchers from Austria have - following their own descriptions - made the important step. It managed them to keep four members of a network communicate free from eavesdropping. Scientists around Rupert Ursin from the Institution for quantum optics and quantum information of the academia of sciences in Austria introduced their research in the british expert report "Nature".
https://www.tagesschau.de/ausland/quanten-101.html
Surveillance
36 millionen Euro: ZITiS builds supercomputer for encryption, netzpolitik.org, 16.10.2018
The hacker-authority ZITiS in Germany intends to buid a supercomputer for the deciphering of encrypted um data. This follows the 36 Millionen Euro lasting draft budget of the authority we ar publishing. ZITiS still searches for state-hacker, while actually only half of the places for this work are staffed.
German Federal Ministry of Internal State
Secure method
End-to-end-encryption is a method popular within application of daily communication technology. This technique has been used in messengers like Signal, WhatsApp or iMessage for years. End-to-ende means communication transfer without any breaks. Transferred contents can only be decrypted and read out at the end points of each communication partner.
Encryption technique is nothing to argue, it depends on mathematic, a science that is non-ambiguous. Wie die Kommunikationsanbieter ProtonMail, Threema, Tresorit und Tutanota in ihrem Gegenstatement auf den Punkt bringen: "Der aktuelle Entwurf der Resolution des EU-Ministerrates beruht auf einem eingeschränkten Verständnis der technischen Aspekte von Ende-zu-Ende-Verschlüsselung. Denn Ende-zu-Ende-Verschlüsselung ist absolut, Daten sind entweder verschlüsselt oder nicht.
[...] Obwohl bisher noch nichts entschieden ist, raten Datenschützer:innen und Expert:innen dazu aufmerksam zu bleiben. Es ist zwar noch kein Gesetz im Entwurf, die Annahme der Entschließung bereitet jedoch einen Weg für einen Entwurf der Kommission. Die zuständige EU-Innenkommissarin Ylva Johansson äußerte sich zuletzt ambivalent.
Zwar teilte sie in einem Schreiben EU-Abgeordneten Anfang Januar mit, dass es keine Pläne gebe, Verschlüsselung zu verbieten. Allerdings fügte die Kommissarin hinzu, "weiterhin gemeinsam mit den Mitgliedstaaten mögliche rechtliche, operative und technische Lösungen für den rechtmäßigen Zugang zu solchen Daten zu prüfen."
https://netzpolitik.org/2021/verschluesselung-sichere-kommunikationsanbieter-warnen-vor-hintertueren/
Survey of the internet node: DE-CIX sues BND, Tagesschau, 22.04.2015
The BND is taken into response before law for his surveys of the net-node DE-CIX in Frankfurt at Main. The holde of the node is going to sue. Criticizer do also sue the government for making tricks. Arond thre terabit data per second are passed and overworked, an amount of 600 CD-Rom. To the customers count all big internet companies like the Deutsche Telekom, Vodafone and Verizon, more details see Links, section "NSA, GHCQ & Co.".
... one more exception of our promise "Gooken 1000% - 1000% IT-security for your computer" grounds in webside code. Although tracking-scripts resp. JavaScript can (and should) be deactivated, information still are and can be stored in local as much as spreaded out into any PHP-MySQL coded databasis. Local isn´t the problem, but nevertheless, for this distribution of information into all kind of foreign databasis, an unusual release of the databasis-passwords is required,
but we really assume, they do!
But the exchange of DNS-information, canvas fingerprinting and the storing of the browser-user-agent-specification can be prevented as much as anonymizing proxies do, especially like TOR and/or maybe some VPN (Virtual Private Networking) at last for the anonymization of the IP !
An important part for the securty is taken by Linux-filesystems like btrfs and ext4 and our iptables- and ebtables-firewall linfw3 !
Beneath this we especially want to contribute on our websites to your choise of the right computer-hardware, the securing configuration of UNIX/Linux and the right choice of TOR--Nodes (so called EntryGuards and ExitNodes resp. Relais), in the last case even by the specializing sides News&Links! For more questions and questions of all kind of any matters our secure search engine Gooken wants to do its best.
Overwhelming, already everywhere published floods of information, reports over reports (material) out of the well-known best and very best sources within our section News&Links at last gives you one of the best opportunity ever to do something against responsible dangerous instances, more than endangering countries (like especially USA), companies, mandants, clients and persons by name - even by processing right before law against, what already has become deep, deep reality for decades!
What our party concerns, please do nothing but notice our general disclaimer!
So far our short description, the summary of Gooken!
 Transport encryption part 3, HTTPS with TLS 1.3 in practice, 06.11.18 | author / editorial staff: Filipe Pereira Martins und Anna Kobylinska / Peter Schmitz Transport encryption part 3, HTTPS with TLS 1.3 in practice, 06.11.18 | author / editorial staff: Filipe Pereira Martins und Anna Kobylinska / Peter Schmitz
TLS 1.3 promises more security for encrypted HTTPS-connections. Unfortunately the implementation is full of perfidies and suprises.
However wants to have a secure HTTPS-encryption, does the best to think once again about the TLS-configuration, as good intentions for data protection without modern transport encryption do not make any sense.
As the vulnerabilities for TLS-protocols up to version 1.2 got explored and known well (see the report "TLS 1.3 - much hot air or a big breakthrough?") it seems to be obvious, that snooping (eavesdropping on https-encrypted connections does happen much more often than one likes to accept. TLS 1.3 really helps.
All begins with the problem, that total resignment from TLS 1.2-fallback for clients with missing support for TLS 1.3 is no theme for the next time.
[...] A robust transport encryption has got its own shady sides: malware can get through without noticing.
During the use of TLS up to version 1.2 (especially by RSA-Ciphers) IT-experts are abled to examine malefic payloads of the data transfer right before passing through the company data center. The communication was read out by so-called middleboxes, it got deciphered, analyzed and forwarded. With TLS 1.3 this kind of monitoring belongs to the past, as each connection is build-up is by Diffie-Hellman-keys - no chance for the so called "deep-packet inspection", as the communication can not be deciphered in real-time as before.
https://www.security-insider.de/https-mit-tls-13-in-der-praxis-a-714096/
Mouseclick-fast: Secure surfing with TLS 1.3
Firefox 78.5.0 (el6, rpm.pbone.net, pachted with Firefox 78.9.0 (el7) except libxul.so) : >= Includes of lib64nss3 (mga7, pclos or nss (fc, ...) and libssl3.so.1.1.1d (well-patched openssl-1.1.1d (fc29) or libssl3.so.1.1.1a (certified openssl-1.1.1a, fc27) to /usr/lib64/firefox/libssl3.so (installation directory)
 We believe, all browser became out of date: Noone´t;s more secure and better! We believe, all browser became out of date: Noone´t;s more secure and better!
Orbot (Tor-Proxy) and PrivacyBrowser or Tor-Browser for Smartphones, desktop with Firefox (OpenSuSE, SL/CentOS) or especially Pale Moon (pclos, palemoon.org with exchange of nss (Pale Moon) with nss (el8) except libsoftokn()(64bit) ), both upon Tor?
https://www.pro-linux.de/news/1/27587/weitere-sicherheitsl%C3%BCcken-in-intel-prozessoren.html
 Gooken recommends the secure messanger Ginlo from the Deutschen Post AG for Android up from version 5 Gooken recommends the secure messanger Ginlo from the Deutschen Post AG for Android up from version 5
[ Next Signal messenger error got solved in version 5.34.10 ], Gooken, 04.11.2022
From: Gooken
To: Developer of messanger Signal (USA)
Permanent Signal Error Report all versions since October 2021 up to now, Gooken, 01.15.2022 - 03.25.2022
All actual Signal versions (up from October 2021) do not delete/remove and share any messages and further on upon our Android 4.4.2 - Smartphone armabiV7a anymore, belonging menu always leads into crash followed by a restart of Signal.
We mailed this several times to you and also delivered the error log with all the system information to youi as you postulated so much from us.
So why don´t you patch it to make it work again it already did before?
And why do elder versions only run just for some days giving the hint to download the actual version?
What the hell do you patch within the many, many updates you always provide?
As Signal should run up from Android 4.4+, as you published everywhere for it´s system requirements, do not force us all the time to buy a newer Smartphone with a more actual Android anymore.
And do not let us download all your so called patched newer versions with more than scrappy 40 MB full of suspicous code each apk!
Versions before end of October 2021 do indicate only working for some days (about one or two weeks) for considering themself as too old.
What I mean is, Signal does neither share, nor delete nor ... messages anymore upon Android 4.4.2 resp. 4.4.4. The menu crashes each election!
WhatsApp´s and a lot of Apps on my Smartphone and many Linux on my Computer is working fine - how can it happen?
Regards,
Gooken
We have sent several Signal-debug-protocols to the developers, but they still didn´r patch it.
 Deine persönlichen Nachrichten warten nur darauf, öffentlich zu werden, uncut-news.ch, 30.05.2025 Deine persönlichen Nachrichten warten nur darauf, öffentlich zu werden, uncut-news.ch, 30.05.2025
Christina Maas, reclaimthenet
Wenn eine Nachricht nicht Ende-zu-Ende verschlüsselt ist, solltest du davon ausgehen, dass sie irgendwann leakt.
Menschen behandeln Textnachrichten immer noch so, als würden sie Geheimnisse in einen Tresor flüstern. Sie verschicken Geständnisse, Beschwerden, Flirts und Wutausbrüche über Plattformen, die zu Billionen-Dollar-Schwergewichten der Überwachung gehören - und glauben offenbar, diese Daten verschwinden in einem wohlwollenden digitalen Schwarzen Loch.
In Wahrheit liegen diese Nachrichten auf Servern von Konzernen, deren Geschäftsmodell darauf beruht, mehr über dich zu wissen als deine eigene Familie.
Die Illusion der Privatsphäre
Quelle: reclaimthenet
https://uncutnews.ch/deine-persoenlichen-nachrichten-warten-nur-darauf-oeffentlich-zu-werden/
Weitere Berichte über datenschutzrechtliche Bedenken bei Signal und WhatsApp, hier spezielle Spionagesoftware im Umlauf und Metadaten: in Kürze!
Die Welt ausspionieren
Darum warnt der Iran vor WhatsApp: Ehemalige israelische Spione sitzen in Führungspositionen bei Google, Facebook und Amazon, uncut-news.ch, 20.06.2025
Alan MacLeod, mintpressnews
Eine MintPress-Studie hat ergeben, dass Hunderte ehemaliger Agenten der berüchtigten israelischen Spionageorganisation Einheit 8200 einflussreiche Positionen in vielen der weltweit größten Tech-Unternehmen, darunter Google, Facebook, Microsoft und Amazon, eingenommen haben.
Die Einheit 8200 der israelischen Verteidigungskräfte (IDF) ist berüchtigt für die Überwachung der einheimischen palästinensischen Bevölkerung und die Anhäufung von Informationen über Einzelpersonen zum Zwecke der Erpressung und Erpressung. Die Einheit 8200, die die Reichen und Berühmten der Welt ausspioniert, geriet letztes Jahr nach Bekanntwerden des Pegasus-Skandals in die Schlagzeilen. Ehemalige Beamte der Einheit 8200 entwickelten und implementierten eine Software, die Zehntausende von Politikern ausspionierte und wahrscheinlich zur Ermordung des saudischen Journalisten Jamal Khashoggi beitrug.
Google
Laut dem Stellenportal LinkedIn arbeiten derzeit mindestens 99 ehemalige Veteranen der Einheit 8200 für Google. Diese Zahl unterschätzt jedoch mit Sicherheit das Ausmaß der Zusammenarbeit zwischen den beiden Unternehmen. Zum einen werden hier keine ehemaligen Google-Mitarbeiter gezählt. Auch sind diejenigen nicht berücksichtigt, die kein öffentliches LinkedIn-Konto haben, oder diejenigen, die zwar ein Konto haben, aber ihre frühere Zugehörigkeit zu der israelischen Hightech-Überwachungseinheit nicht offengelegt haben. Dies dürfte eine beträchtliche Zahl sein, da es den Agenten ausdrücklich untersagt ist, ihre Zugehörigkeit zur Einheit 8200 jemals preiszugeben. Die Zahl 99 gibt also nur die Anzahl der derzeitigen (oder erst kürzlich eingestellten) Google-Mitarbeiter wieder, die sich dreist über israelische Militärgesetze hinwegsetzen, indem sie die Organisation in ihren Profilen angeben.
Zu diesen gehören: ...
Die Welt ausspionieren
Warum ist es ein Problem, dass ehemalige Offiziere der Einheit 8200 bei einigen der wichtigsten Kommunikationsunternehmen der Welt für Sicherheit, Entwicklung und Softwaredesign zuständig sind? Zunächst einmal besteht eine der Hauptaufgaben der Militäreinheit darin, ihr technisches Know-how für Spionageoperationen in der ganzen Welt einzusetzen. Wie die israelische Zeitung Haaretz in einer Untersuchung feststellte, ist Israel zu einem führenden Exporteur von Werkzeugen zum Ausspionieren von Zivilisten geworden" und verkauft invasive Überwachungssoftware an Dutzende von Regierungen, von denen viele zu den schlimmsten Menschenrechtsverletzern der Welt gehören. In Indonesien wurde die Software beispielsweise zur Erstellung einer Datenbank über Homosexuelle verwendet.
Die Einheit 8200 spioniert auch Amerikaner aus. Der Whistleblower Edward Snowden enthüllte, dass die NSA regelmäßig die Daten und die Kommunikation von US-Bürgern an die israelische Gruppe weitergibt. "Ich finde das erstaunlich… Das ist einer der größten Missbräuche, die wir gesehen haben", sagte Snowden.
Quelle: https://www.mintpressnews.com/revealed-former-israeli-spies-working-top-jobs-google-facebook-amazon/282413/
https://uncutnews.ch/darum-warnt-der-iran-vor-whatsapp-ehemalige-israelische-spione-sitzen-in-fuehrungspositionen-bei-google-facebook-und-amazon/
But at first we talk about:
 Via Browser for Smartphones, legendary (compared with Firefox or Chrome with more than 70 MB each browser): Via Browser for Smartphones, legendary (compared with Firefox or Chrome with more than 70 MB each browser):
-
Comfortable, secure smartphone-browser, just 0.86 MB sized apk, version > 4.3.3 from 12.2021
-
OpenSource,
-
also for elder Smartphones,
-
all needed functions,
-
tabs,
-
location release and blocking
-
user agent switcher,
-
pop-up-blocker,
-
adblocker,
-
internal filter ( one more adblocker ),
-
user definable filter ( ABP-filter-rules )
-
importable lists-filter: ABP-EasyList, ...
-
importable scripts
-
... as a general filter underlayed all filters abvoe for each webseite
-
script blocker (ABP: easy list, ...),
-
place for addons/extensions and scripts
-
incognito-mode (blocks history and cookies and further more.)
-
night mode (fine adjustable darkning)
-
More functions: favorites, share, tool box, show page source, ...
-
Quit Browser: Via Browser won´t push news and other things to you. No bother to your android devices
-
Mini Browser: Via Browser use much less memory usage on your android devices
-
less RAM-consumption
-
Version 4.3.0: well patched code (updated well)
-
...
-
Critics: Self-descriptions of this browser are in chinese language only.
It is still not possible to add any proxy. Thence for highest IT-security Tor-browser (torproject.org) Tor Smartphones still is our favorite browser!
-
...., comfortable and simple adjustments and easy handling
Download out of the internet or from a PlayStore.
https://m.apkkure.com/via-browser-fast-light-geek-best-choice/Mark.Via.GpP oder Huawei PlayStore
Dear reader, please inform the developer of Via Browser Tu Yafeng about the next issue!:
Email from Gooken to lakor@foxmail.com
Hello,
here´s Gooken.
Please forward this e-mail to the devoloper of VIA Browser Tu Yafeng!
Refering to Via Browser 4.3.0 for Android-Smartphone, following errors occur:
Errata Via Browser 4.3.0
1 Breakdown/crash: Via Browser breaks down / crashes completely on some websites: again and again. I´m sorry not noticing belonging website-URL.
2. Language: Language input into input-text-fields is not possible in some cases, until it is changed from system to english resp. from english to system and so on. This happened several times on https://metager.de for example.
3. In online shops like Ebay it is not possible to click onto the buttom for the selection of the payment-method (SEPA, PayPal etc.): no reaction at all! Same for the payment itself (bottom for buying the product). During this JavaScript was always turned on and incognito mode to off. But Via Browser does not react independent from its incognito mode and adblocking or any other option!
4. Missing parts: Via browser still does not offer an opportunity to enter any proxy. We use Tor for smartphones for example and like to enter the tor-proxy based on socks5 into Via Browser.
5. Whenever scrolling the bookmarks, the following error message occurs in Via Browser 4.3.0 up to 4.3.3: "Exception Happened. Thread [main,5,main] java.lang.AbstractMethodError abstract method not implemented."
6. We certainly do not agree with the terms of privacy! Via browser exchanges data and shares them with third companies, but in our eyes that must have to do with an internal account to a chinese or foreign cloud server within its settings part one must not create. We won´t use Via Browser resp. the account, until privacy is bewared!
Please tell the author of the browser Tu Yafeng about all this by sending him
this e-mail, so that the elsewhere very fine Via Browser gets patched and
upgraded soon!
Regards
Gooken
December, the 07 2021: One more errata:
All Signal messenger version since October 2021 do not enable user to mark out and delete messages anymore. Instead, signal quit crashes. This was found out upon Android 4.4.
What&s happened?
Dear reader, please contact this developer too!
BSI warns against Firefox &Thunderbird: Updates close several lacks in security, CHIP, 19.11.2020
Mozilla hat mit den aktuellen Updates für den Browser Firefox und den Mail-Client Thunderbird mehrere Sicherheitslücken geschlossen, vor denen das BSI warnt. Wir empfehlen Ihnen dringend, beide Programme möglichst bald auf die neueste Version upzudaten.
https://www.chip.de/news/BSI-warnt-vor-Firefox-und-Thunderbird-Updates-stopfen-gleich-mehrere-Sicherheitsluecken_104405834.html
Next in-between-update for Firefox 78: Firefox 78.0.2 is ready for downloading, CHIP, 09.07.2020
Erst letzte Woche hatte Mozilla planmäßig Firefox 78 zum Download bereitgestellt. Doch es trat eine Nebenwirkung im Zusammenhang mit Suchmaschinen auf, woraufhin die Verteilung gestoppt wurde. Firefox 78.0.1 hatte das Problem behoben. Jetzt steht mit Firefox 78.0.2 das nächste Zwischen-Update an, das unter anderem ein Problem mit Microsoft Teams behebt.
https://www.chip.de/news/Firefox-78-gestoppt-Mini-Update-Firefox-78.0.2-ist-da_182759007.html
Firefox 78.5.0 (el6, rpm.pbone.net, patched by Firefox-78.9.0 except libxul.so)
 Pale Moon extensions: secret agent and/or eclipsed moon, JavaScript-toggle-buttom, script-blocker, ABL (for AdblockPlus, ABP) resp. abprime, ehprime: hide elements (any visible webside contents self-pointed out for the election per mouse leading into one more filter-rule for ABL resp abprime, noscript, RequestPolicyBlockContinued, Block Content (msdy), PermissionsPlus (extends about:permissions and this by now for each website), Pure URL, signTextJS, n-Matrix, noscript (version 5.1.9 out of rpm seamonkey-noscript (el8, el7)), CanvasBlocker Legacy, JavaScript-Toggle-Buttom, Decentral Eyes, No Resource URI Leak usw.! Pale Moon extensions: secret agent and/or eclipsed moon, JavaScript-toggle-buttom, script-blocker, ABL (for AdblockPlus, ABP) resp. abprime, ehprime: hide elements (any visible webside contents self-pointed out for the election per mouse leading into one more filter-rule for ABL resp abprime, noscript, RequestPolicyBlockContinued, Block Content (msdy), PermissionsPlus (extends about:permissions and this by now for each website), Pure URL, signTextJS, n-Matrix, noscript (version 5.1.9 out of rpm seamonkey-noscript (el8, el7)), CanvasBlocker Legacy, JavaScript-Toggle-Buttom, Decentral Eyes, No Resource URI Leak usw.!
Gooken recommends Pale Moon, you can download from nluug.nl (PCLOS), palemoon.org or up from verison 33.3.0 without AVX support from https://ftp.palemoon.org/AVX/linux. The for more security firefox-code-reducing, but still comfortable Pale Moon is ready for tls-1.3 all upon minimal system requirements!
 Recommended installation order of Pale Moon extensions for security: 1 Block Content Download before 2 PermissionPlus, 3 ScriptBlocker, 4 ABL, 5 Request Policy Block Continued, 6 nMatrix, 7 noscript and goalkeeper 8 Privacy Badger. Recommended installation order of Pale Moon extensions for security: 1 Block Content Download before 2 PermissionPlus, 3 ScriptBlocker, 4 ABL, 5 Request Policy Block Continued, 6 nMatrix, 7 noscript and goalkeeper 8 Privacy Badger.
Pale Moon
Important nss-security-update end of November 2021:
nss: libnss3.so and libnssutils3.so can get exchanged with an actual nss (el8, el7) and nss-utils (el8, el7) easyly by the simple command "cp -fp" resp. link-command "ln"!
Can I run Firefox extensions in Pale Moon?
Yes, you can, for now. Since version 25 we´ve had the option to install (now called "legacy") XUL, bootstrapped and Jetpack type Firefox extensions on Pale Moon, despite Pale Moon being (and being identified as) a different browser. Please understand though that there is no guarantee that these extensions will work, and using extensions targeted at a different application is entirely at your own risk and you are pretty much on your own regarding support.
https://forum.palemoon.org/viewtopic.php?f=46&t=23697
PROBLEM: Pale Moon 30.0.0: Menüs can not be opened, and Pale Moon does not surf anymore ! So we still use Pale Moon 29.4.4 resp. 29.4.6 (recommended by us) by now
Pale Moon 31.0.0: Each mouse-click onto any menu item causes delays of about several seconds!
An answer followed few days later by Top news from Pale Moon Org, https://www.palemoon.org, 21 march 2022
"Pale Moon 30 rollout cancelled. Following severe issues with the unexpected exit of a core dev and considerable damage caused to our operations, the milestone 30 rollout has been cancelled.
Dabei geht der am Schluss installierte ("Torhüter, Torwart") Privacy Badger von der Bürgerrechtsorganisation EFF selbst nach vorgesehenen Blocken aller Trackingskripte mit dem Schieberegler von grün auf überalll rot, ausgenommen Facebook-Widgets, (hoffentlich) meist leer aus: Aufgelistete, vor ihm installierte Erweiterungen nehmen ihm diese Arbeit bereits ab.
privacybadger.org: [...] Although we like Disconnect, Adblock Plus, Ghostery and similar products, none of them are exactly what we were looking for. In our testing, all of them required some custom configuration to block non-consensual trackers. Several of these extensions have business models that we weren´t entirely comfortable with. And EFF hopes that by developing rigorous algorithmic and policy methods for detecting and preventing non-consensual tracking, we´ll produce a codebase that could in fact be adopted by those other extensions, or by mainstream browsers, to give users maximal control over who does and doesn´t get to know what they do online."
[ SOLVED by palemoon.org: Next problem "Pale Moon does´t start: XPCOM-error" got solved in Pale Moon > 29.4.1 ( and < 24.4.3, up from where it got solved now, rem., Gooken ) from 09.17.2021, but occured again in Pale Moon >= 29.4.2.1 ! ]
Dear reader, please inform the developer of Pale Moon about the next issue, as we might not reach him!:
Email sent by Gooken
to: moonchild.prod@palemoon.org, redaktion@chip.de
Date: 08.27.2021
Please forward this e-mail to the Pale Moon - forum and -developers !
Hello,
here´s Gooken, and we want to tell you, that Pale Moon greater or equal Version 29.4.0
does not start anymore!
Started in a terminal, belonging error-message occurs:
"XPCOMGlueLoad error for file /usr/lib64/palemoon/libxul.so:
/usr/lib64/palemoon/libxul.so: undefined symbol: g_bytes_unref
Couldn´t load XPCOM."
Our GTK version is 2.24 (gtk from Enterprise Linux 6).
All previous versions up to 29.3.0 did work fine.
It would be nice to patch it (of course we can try another GTK version, if not)!
Regards,
Palemoon up to now (24.4.4) still has got the sometimes arrow jumping toolbar icon during the load of some webpages.
It would be nice to patch it too.
Regards, Gooken
 Initialization of the most important Pale Moon extension "Block Content Download" (msdy) each new start: in about::config edit /home/user/.mozilla/userprofile/user.js,by changing values of all items like permissions.*.* to the value 3, 3 for images ( that can be webbugs, that means tracking scripts with returned images ), stylesheets, objects, scripts, subdocuments and so on, that at least means "No third party allowed". Initialization of the most important Pale Moon extension "Block Content Download" (msdy) each new start: in about::config edit /home/user/.mozilla/userprofile/user.js,by changing values of all items like permissions.*.* to the value 3, 3 for images ( that can be webbugs, that means tracking scripts with returned images ), stylesheets, objects, scripts, subdocuments and so on, that at least means "No third party allowed".
 Pale Moon extension: nMatrix Pale Moon extension: nMatrix
Point&click to forbid/allow any class of requests made by your browser. Use it to block scripts, iframes, ads, facebook etc.
nMatrix does also
Delete blocked cookies
Delete non-blocked session cookies minutes after the last time they have been used
Delete local storage content set by blocked hostnames
Clear browser cache every minutes
Spoof HTTP referrer string of third-party requests
Strict HTTPS: forbid mixed content
Block all hyperlink auditing attempts
Resolve CNAME records
 Pale Moon Extension: Pure URL 3.3.2 strips garbage referer tracking fields like ´utm_source´ from links and resolves short links Pale Moon Extension: Pure URL 3.3.2 strips garbage referer tracking fields like ´utm_source´ from links and resolves short links
Beware of these links!, uncut-news.ch, 10.27.2023
This article deals with certain link-parameters past the question mark tracking information and endangering privacy.
Quelle: https://reclaimthenet.org/beware-of-these-links
https://uncutnews.ch/vorsicht-bei-diesen-links/
 Pale Moon extension: Eclipsed Moon (please notive: On websites like https://slackware.pkgs.org/14.2/ Eclipsed moon still sets the original useragent of the Browser. To prevent this, prefer useragent-exchangers like SecretAgent !) Pale Moon extension: Eclipsed Moon (please notive: On websites like https://slackware.pkgs.org/14.2/ Eclipsed moon still sets the original useragent of the Browser. To prevent this, prefer useragent-exchangers like SecretAgent !)
By: Eurythrace Perseides
About this add-on
This add-on/extension is designed to work unobtrusively by using current, well known user agent strings and operating systems to "blend in" with the crowd. The preferred "smart" mode is designed to switch the user agent string only when no external tabs are open except for the home page, if it is an external page. The intent is to be quiet and NOT draw attention by changing the user agent string too frequently or using unique ones. It also offers an anonymity checklist for the browser settings, and has a "smart erase" feature to forget about a site when all open tabs to that site are closed. This is a COMPLETE erasure for that individual site, similar to the Delete History option when closing the browser. ALL PASSWORDS, COOKIES, HISTORY, ETC. WILL BE ERASED FOR THE SITE!
Test Package
A test package to verify the operation of the random User Agent generation may be downloaded from here:
https://addons.palemoon.org/datastore/addon/eclipsedmoon/eclipsedmoon-test.zip
Once unzipped, the XHTML file should be opened in a Pale Moon™ browser that already has the Eclipsed Moon add-on/extension installed. The operating mode of the add-on/extension should be set to "Page" before loading the test XHTML page. The test will then proceed to iterate a default value of 50 times and collect the statistics of the User Agents used for each iteration. Optionally, an iteration count may be passed to the XHTML file via adding a query string to the URI in the form of "?runs=100". The maximum number of iterations is set to 1000, although the JavaScript file associated with the XHTML file may be edited to change that number.
There is an optional PHP file that may be loaded on a server along with the supporting files so the test may be conducted over the internet rather than on the local computer. This will use a large amount of bandwidth to run the test since each iteration will need to completely reload files from the server. The difference is that using the PHP file collects the User Agent from the HTTP header rather than the window.navigator.userAgent DOM property.
https://addons.palemoon.org/addon/eclipsedmoon/
 Pale Moon extension: Certificate Patrol Pale Moon extension: Certificate Patrol
"Welcome to Certificate Patrol 2.0. We introduced some improvements, that we should first explain to you.
Before we even list the details of a certificate, we first show you the certification hierarchy. That is the most important clue for oyou to find out, if you´re being tricked. An intermediate authority can put any text in the certificate, that you would like to see, but it cannot falsify the certificate checksums and its position in the hierarchy. Dangerous certificates are likely to be generated by a long list of authorities belonging to different companies or governments. Genuine ones are likely to be signed directly by a root certificate in your browser or by an intermediate creaated by the same company. All the inbetween cases are likely to be legitimate, but you can´t be sure. We are still taking guesses hsere because we steill don´t know, which root certificates in our browsers are worthy of trust. By keeping your eyes open and observing the patterns, you are a lot likelier to notice, when you are being attacked. In case of doubt, compare (by telephone) the checksums with somebody, that could not possibly be affected.
Another important change is, that we now inspect certificates for all parts of webpage, so you may see server names and domains comping up, that you never thourght youwere visiting, just because they host some Javascript or media files.
It´s also new, that you can reject all new certificate, when you see them.
That doesn´t mean, that you will be protected from using them, because we don´t have that much control over your browser.
If you don´t trust a site, you still have to close the window yourself. But it maens, that, if you bump into the same certificate again, you will be asked again. You could use this to see, if a certain website always has the same certificate, when you change internet connection. (like open it from work, then from home). Then again, if you store the certificate, you´re even safer, that the certificate is the same.
Several websites hat the bad habit of using multiple certificates for the same hostname. We consider it a configuration error on their side, but since they insist, you now have a little option of the certificate change pop-up to accept any certificate for the host as long as the issuer, that is the next higher level authority, stays the same. This should help in most cases, although I bet there are some, which are more misconfigured than that."
 Initializing Palemoon-security-extension "Block Content Download" each new start: Type "about::config" into the address-line of your browser or edit /home/user/.mozilla/userprofile/user.js, by setting all items permissions.*.* to the value 3 for images, style sheets, objects, scripts, subdocuments (documents) and further on, that means at least onto this value for "no third parties" ! Initializing Palemoon-security-extension "Block Content Download" each new start: Type "about::config" into the address-line of your browser or edit /home/user/.mozilla/userprofile/user.js, by setting all items permissions.*.* to the value 3 for images, style sheets, objects, scripts, subdocuments (documents) and further on, that means at least onto this value for "no third parties" !
 Pale Moon security extension and tool resp. utility: Config Comments Pale Moon security extension and tool resp. utility: Config Comments
This security extension from Tools&Utilities instead of Security from palemoon.org explains many items within about:config in detail. As our excurs will make a lot of changes of items within about:config, we like to recommendthis browser extension very much too!
 Pale Moon mode gecko (Goanna) - start in below 15 instead of over 70 seconds - security extension and tool resp. utility called "Expire history by days" Pale Moon mode gecko (Goanna) - start in below 15 instead of over 70 seconds - security extension and tool resp. utility called "Expire history by days"
This security extension from Tools&Utilities instead of Security from palemoon.org empties the browser-history automatically. Set expire-in-days from value 0 to 1 and, following our observes, Pale Moon starts much, much faster...! The installation of this extension keeps Pale Moon from eavesdropping processes right at the beginning (Pale Moon start) too!
 Pale Moon extension: signTextJS Pale Moon extension: signTextJS
By: dkeeler@mozilla.com, rbarnes@mozilla.com, vbadev@gmail.com
About this add-on
window.crypto.signText is a digital signature technology, that has been available to Firefox users for 20 years. It is used by government and banking sites. It can be used to participate in plebiscites.
The window.crypto interfaces were removed from Firefox 35 and later releases. An add-on was developed as a stop-gap measure for users; that add-on is deprecated and does not work since Firefox 57, but still work with Pale Moon.
This fork based on the original signTextJS-0.7.7 add-on by mozkeeler.
https://addons.palemoon.org/addon/signtextjs/
 Pale Moon extension: Modify HTTP Response Pale Moon extension: Modify HTTP Response
By: Off JustOff
About this add-on
Modify HTTP Response is designed to rewrite http response body using search & replace patterns.
Warning:
This tool works on low level API and intended for advanced users.
Incorrect filters can cause browser freeze, hang or loose data.
Never use filters from untrusted sources or if you don´t understand them.
https://addons.palemoon.org/addon/modify-http-response/
 Pale Moon and Firefox extension: No Resource URI Leak Pale Moon and Firefox extension: No Resource URI Leak
Deny resource:// access to web content. We fill the hole to defend against fingerprinting. Very important Firefox privacy. A direct workaround for bugzilla.la/863246:
block access to resource:// URIs from web
block web-exposed subset of chrome:// URIs
uniformly filter disallowed redirects
restrict about: pages by default (for paranoids)
 Classic Add-ons Archive [External] Classic Add-ons Archive [External]
Catalog of classic Firefox add-ons created before WebExtensions apocalypse.
https://addons.palemoon.org/extensions/other/
[SOLVED by Gooken: Pale Moon always stops working (halts) for about 30 seconds after getting started ]
Enter about:config into the address-line and delete (quit) all values (URL/URI) containing "http://" and "https://"!
You don´t like the design of Pale Moon? Beneath an actual version of Pale, extensions, lookout for a theme you like from many ones from palemoon.org!
 Pale Moon Extensions: Eventually formulate exceptions for some of them within. Pale Moon Extensions: Eventually formulate exceptions for some of them within.
You can formulate them for extension Eclipsed Moon (OpenSource from palemoon.org) or SecretAgent (ClosedSource from manufaccturer out of UK) during the setting the browser-user-agent-specific, Noscript, RequestPolicy, n-Matrix as much as within the proxy-settings of Pale Moon. Please notice, that Eclipsed moon still isn´t able to formulate exceptions for single URI (URL).
 So nothing has to be done by the administrator as much as user manually in future - all gets automized - as generally possible with UNIX/Linux! So nothing has to be done by the administrator as much as user manually in future - all gets automized - as generally possible with UNIX/Linux!
Designs and styles: Many alternative designs and stylese for Pale Moon are provided by palemoon.org and other locations.
 Create one more profile by about:profiles without many or without all (too many restrictions causing) extensions, whenever some websites get too restricted and you don´t know, how to "reset" belonging extensions from above, in order to get the rights back, by restarting Pale Moon resp. Firefox or by launching a single window for this created alternative profile ( out of about:profiles ). Create one more profile by about:profiles without many or without all (too many restrictions causing) extensions, whenever some websites get too restricted and you don´t know, how to "reset" belonging extensions from above, in order to get the rights back, by restarting Pale Moon resp. Firefox or by launching a single window for this created alternative profile ( out of about:profiles ).
Block annoying cookie-banner (telling us to allow cookies): a browser-add-on cares for less frustration during the surfing online, CHIP, 10.09.2020
Download Firefox-Erweiterung: I don´t care about cookies für Firefox 3.2.2
CHIP tested it with: good
https://www.chip.de/news/Nervige-Cookie-Banner-blockieren-beim-Surfen-so-gehts_148087234.html
Virusses, trojans, worms, bots: 40 percent of all computers in Germany are "zombies", FOCUS Online, 03.02.2014
The amount is alarming: 40 Prozent of all PCs in Germany are infected and can be remoted by Cyber-gangster. Once installed, malware opens backdoors for the new one.
All Intel-CPU-generations since Celeron
"We can skim out (eavesdrop) everything", tagesschau.de, 04.01.2017
Following a newspaper report the detection of actual lacks in security within plenty of computer chips was also made by researchers from the Technical University Graz in Austria. "We were shocked by ourselves about the functioningt", said Michael Schwarz from the TU Graz to quot;Tagesspiegel".
By this leaks all data could be read out of the computer is getting about. "In principle we can read out everything typed into the computer." Attackers could gain online banking data or stored passwords
"Though for this purpose they have to get logged into or connected with the computer", restricted Mr. Schwarz.
https://www.tagesschau.de/ausland/intel-sicherheitsluecke-103.html
Warning against new infostealer, that is put about through Google-Ads, trojaner-info.de, 03.01.2023
Der Sicherheitsdienstanbieter Zscaler warnt vor einem erstmals im Dezember 2022 entdeckten Infostealer, der in der Lage ist, Anmeldeinformationen von Webbrowsern, VPN-Clients, E-Mail-Clients und Chat-Clients sowie von Kryptowährungswallets zu stehlen. Die in C++ geschriebene Malware bestehe aus einem Loader und dem Hauptmodul, erläutern die Sicherheitsexperten des Zscaler ThreatLabZ-Teams. Letzteres sei für das Exfiltrieren der gesammelten Anmeldedaten verantwortlich. Es handele sich um ein bösartiges Schadprogramm, dass sich vornehmlich über Google-Ads verbreitet.
https://www.trojaner-info.de/sicher-anonym-im-internet/aktuelles/warnung-vor-neuem-infostealer-der-sich-ueber-google-ads-verbreitet.html
 Huawei P40 Pro: Google does not exist anymore, CHIP, 02.04.2020 Huawei P40 Pro: Google does not exist anymore, CHIP, 02.04.2020
[...] ... is a salient smartphone with plenty of improvements...
https://www.chip.de/test/Huawei-P40-Pro-im-Test_182596289.html
From our data sheed ("... still functioning today!")
 Smartphone HUAWEI Y360 (Y360-U61) with accessory and magnetized black leather case and charging device from expert, year 2015, for 79 Euro (I got it from a friend for free...) Smartphone HUAWEI Y360 (Y360-U61) with accessory and magnetized black leather case and charging device from expert, year 2015, for 79 Euro (I got it from a friend for free...)
[...]
Detailed, precise check: spectre-meltdown-checker (el6) resp. meltdown-spectre-checker (el6)
 Solution: The solution is dependent from the security-concept (excurs). Microcode, kernel-version, device drivers and CPU themself might only help partially, that means not help at all and if they help, they only mitigate problems with Meltdown and Spectre: Solution: The solution is dependent from the security-concept (excurs). Microcode, kernel-version, device drivers and CPU themself might only help partially, that means not help at all and if they help, they only mitigate problems with Meltdown and Spectre:
Take the quit old Intel® Celeron into a fast RISC-processor "mutating" microcode_ctl ( take the fastest version you can: the faster, the more unrisk the CPU (!); enfastening (almost probably running most secure, as the fastest one: rosa2021.1, rosa2016.1): microcode_ctl-1.17-33.33.el6_10.x86_64.rpm, fc29: ver. 2.1-33, ), we might recommend the mouseclick-fast microcode_ctl (rosa2021.1, rosa2016.1, el9, el8) past (upon) microcode_ctl (el6) getting installed (overwritten el6) by rpm -i --force) or ucode_intel (OpenSuSE, newer rpm for 15.3, 15.2, 15.1) and an actualized kernel-5.4 (pclos) or kernel 4.19 (pclos) or >= 4.21 (kernel 5) (we installed kernel: 5.4.110-pclos past 4.20.13 (pclos1))
Our tip: Take the cpu fastest working version!
With this version from 05.22.2023 all (data-sheed. Celeron of Mini-ITX-220) seems to work faster than even mouseclick-fast, quit fast like the time before all these microcode_ctl-updates: microcode_ctl-20230214-1.el9.noarch.rpm !.
Or, pardon: Try Microcode Updates for Intel x86/x86-64 CPUs
OpenSuSE Tumbleweed for x86_64 ucode-intel-20240312-1.2.x86_64.rpm
Clean up your Linux-System, by making as many programs run as possible. Solve dependencies, look out for any missing library, clear up different versions of perl and python and so on.
Gorgeous! With this ucode-intel processors equal or higer Celeron run even faster than already mouseclick-fast right before!
Start microcode_ctl (for example in /etc/rc.local):
echo 1 > /sys/devices/system/cpu/microcode/reload
sh /usr/libexec/microcode_ctl/reload_microcode
... or by an used processor exploring udev-rule.
or: microcode_ctl -qu
and/or start it automatically each system boot.
For this, unlock the boot-partition by command "mount -o remount rw /boot", in order to integrate microcode ctl into the initramfs using dracut ("dracut -f /boot/initramfs-... kernel-module-version").
... and mouseclick-fast not only during the night ( 21.00 - 06.00 o´clock, a time, where some server got shutdown): microcode_ctl (el8, from July 2022).over microcode_ctl (el6).
Also, for such purposes, do not forget to actualize Linux as described in our section "Universal Linux"!
Firewall Linfw3 against Meltdown and Spectre: Set group "nobody" for the group of surfuser (with primary group nobody) and only allow surfuser with one more group of surfuser named surfgroup for example (instead of nobody) to go online. Linfw3 is able to block even root (UID: root, 0, GID: root, 0). So noone is allowed to go online through Linfw3 else surfuser with group surfgroup (instead of his primary group "nobody"), what prevents device drivers from exchaning data - as in this case caused by Meltdown and Spectre To go paranoid, to make it even more confusing for kernel and CPU, set all directories and files owned by surfuser to it´s primary group "nobody".
Emulators: virtualbox (MS Windows and other OS), qtemu, qemu (MS Windows, virtual emulators of many operating systems), mingw (the MSWindows-dll) and wine (MS Windows), dosemu-freedos (rosa2014.1, MSDOS, PC-DOS), basiliskII, basilisk (Macintosh), puae and uae (Amiga), hatari (ATARI ST), vice and micro64 (VC64), dosbox, dos2unix (text format converter), yabause (saturn emulator), xroar (dragon 32, 64, Tandy coco emulator), fbzx (Spectrum), caprice (Amstrad CPC), zboy (Nintendo Gameboy), ...
Howto use Windows within Linux through Virtualbox, PC-WELT.de, 08.05.2019
Per virtualization it is possible to use software and apps for Windows for Linux too. We show, howto.
https://www.pcwelt.de/ratgeber/Windows-als-virtuellen-PC-in-Linux-weiternutzen-9790033.html
Virtualbox (el6, all Linux): VirtualBox-5.2-5.2.28_130011_el6-1.x86_64.rpm 12-Apr-2019 20:25 78M, VirtualBox-6.0-6.0.6_130049_el6-1.x86_64.rpm 16-Apr-2019 15:58 118M ( or VirtualBox-5.2-5.2.28_130011_Linux_x86.run ) from https://download.virtualbox.org/virtualbox/5.2.28 resp. https://download.virtualbox.org/virtualbox/6.0.6
and Virtualbox: UserManual.pdf, https://download.virtualbox.org/virtualbox/6.0.6/Oracle_VM_VirtualBox_Extension_Pack-6.0.6-130049.vbox-extpack, https://download.virtualbox.org/virtualbox/6.0.6/VBoxGuestAdditions_6.0.6.iso
Actual version from March 2020: https://download.virtualbox.org/virtualbox/6.0.18/
... r und Ersteller von Technologien zu machen, die mit uns zusammenarbeiten."
Bereits letztes Jahr hatte sich Microsoft klar dazu bekannt, trotz Protesten der eigenen Mitarbeiter das US-Militär weiter mit seinen Technologien ausrüsten zu wollen. So bewarb sich der Konzern - genauso wie Amazon - um einen Großauftrag, der die Software des US-Militärs komplett überholen und auf Cloud-Basis bringen soll. Welcher Konzern den Auftrag erhält, ist noch offen. Im Sommer schloss Microsoft einen weiteren Milliarden-Deal ab, um die Büros des Pentagon mit seinen Office-Programmen auszustatten.
[...] Kritiker sehen die Kombination aus Edge-Computing und Militär als durchaus gefährlich an. So könnten Drohnen in Zukunft auf Basis ihrer KI-Algorithmen selbst die Entscheidung zum Angriff treffen. Google hatte sich wegen solcher Befürchtungen in seiner Belegschaft entschieden, die Zielerkennung von Drohnen nicht weiter zu unterstützen.
Nadella scheint diese Gefahr durchaus bewusst zu sein. In seiner Rede sprach er auch von der Verantwortung, die KI mit sich bringt. "Wir glauben an verantwortliche KI. Man muss auch die schweren Fragen stellen, nicht nur was ein Computer tun kann - sondern auch, was er tun sollte." Die Antwort nannte er nicht.
https://www.stern.de/digital/computer/microsoft-chef-erklaert--
warum-windows-und-co--kuenftig-kaum-eine-rolle-spielen-8945156.html
 Bastille: Full-automatic IT-security for UNIX / Linux per mouseclick?, fr2.rpmfind.net Bastille: Full-automatic IT-security for UNIX / Linux per mouseclick?, fr2.rpmfind.net
"Bastille is a system hardening / lockdown program which enhances the security of a Unix host. It configures daemons, system settings and firewalls to be more secure. It can shut off unneeded services and r-tools, like rcp and rlogin, and helps create "chroot jails", that help limit the vulnerability of common Internet services like Web services and DNS. This tool currently hardens Red Hat Enterprise Linux, Legacy, and Fedora Core, as well as Debian, SUSE, Gentoo, Mandriva, Ubuntu, Mac OS X, and HP-UX. If run in the preferred Interactive mode, it can teach you a good deal about Security while personalizing your system security state. If run in the quicker Automated mode, it can quickly tighten your machine, but not nearly as effectively (since user/sysadmin education is an important step!) Bastille can also assess the state of a system, which may serve as an aid to security administrators, auditors and system administrators, who wish to investigate the state of their system´s hardening without making changes to such. To run: -bastille [(-b|-c|-r|-x|--assess|--assessnobrowser)] -b : use a saved config file to apply changes directly to system -c : use the Curses (non-X11) GUI -r : revert Bastille changes to original file versions (pre-Bastille) -x : use the Perl/Tk (X11) GUI --assess : use the assessment functionality, viewing results in a browser --assessnobrowser: use the assessment functionality without a browser."
https://fr2.rpmfind.net/linux/rpm2html/search.php?query=Bastille&submit=Search+...
From this excurs
 Forbidden good? Forbidden good?
Firefox (64 Bit) 74.0 Final
Free download now from CHIP: the brand actual final version of Firefox 74.0.
CHIP test result: Very good
https://www.chip.de/news/Browser-im-Maerz-2020-Firefox-stuerzt-ab_169898532.html
Firefox-ESR-52.9.0-Extensions: quit complete filtering of tracking-scripts by ABP, RequestPolicy, noscript and our ff-ESR-security-settings through user.js (from Kai Raven.de and other authors resp. see further below)
 https://download.opensuse.org/repositories/home:/dliw:/ https://download.opensuse.org/repositories/home:/dliw:/
mozilla/openSUSE_Leap_15.1/x86_64/firefox-esr-52.9.0-lp151.3.18.x86_64.rpm (from 04.28.2020), requires (for el6): mozilla-nss (OpenSuSE Thumbleweed, libfreebl3 (OpenSuSE Thumbleweed), libsoftokn3 (OpenSuSE Thumbleweed)
 Respective the top-actual version of FirefoxESR-52.9.0 out of the directory: https://download.opensuse.org/repositories/home:/dliw:/mozilla/openSUSE_Leap_15.1/x86_64/ Respective the top-actual version of FirefoxESR-52.9.0 out of the directory: https://download.opensuse.org/repositories/home:/dliw:/mozilla/openSUSE_Leap_15.1/x86_64/
https://ftp.pbone.net/mirror/ftp5.gwdg.de/pub/opensuse/repositories/home:/linux4humans:/sle11_software:/
firefox/openSUSE_Evergreen_11.4/x86_64/MozillaFirefox-52.9.0-10.2.x86_64.rpm (from 02.15.2019)
 seamonkey (el6, this version 2.49 includes the actual patched firefox-52.9) seamonkey (el6, this version 2.49 includes the actual patched firefox-52.9)
https://rpm.pbone.net/index.php3/stat/4/idpl/54051369/dir/
opensuse_leap_15/com/MozillaFirefox-52.9.0-lp150.5.1.x86_64.rpm.html
https://rpm.pbone.net/index.php3/stat/4/idpl/55298083/dir/
opensuse/com/MozillaFirefox-52.9.0-4.5.x86_64.rpm.html
FirefoxESR-52.8.1 (el6, fr2.rpmfind.net)
Attention! The installation-order of some of the following Firefox-extensions is a not unimportant point: ABP (by the (*-wildcard-based) security-filter-rule "forbidden is, what is not (explicit) allowed", details in future from further below) and/or uBlock resp. ABL for Pale Moon) right before RequestPolicy before Noscript (or uMatrix) before PrivacyBadger before CanvasBlocker!
Notice: ( The last Firefox-extension we installed, "goalkeeper") Privacy Badger from the switzer civil rights organization EFF as the in our order last installed extension does not, as we hope - except facebook-widgets - block many tracking-scripts, even if single marked scripts turned from green (allow) to red (block): Listed previous installed script-blockers did already do their best.
privacybadger.org: [...] Although we like Disconnect, Adblock Plus, Ghostery and similar products, none of them are exactly what we were looking for. In our testing, all of them required some custom configuration to block non-consensual trackers. Several of these extensions have business models that we weren´t entirely comfortable with. And EFF hopes that by developing rigorous algorithmic and policy methods for detecting and preventing non-consensual tracking, we´ll produce a codebase that could in fact be adopted by those other extensions, or by mainstream browsers, to give users maximal control over who does and doesn´t get to know what they do online.
How does Privacy Badger work?
When you view a webpage, that page will often be made up of content from many different sources. (For example, a news webpage might load the actual article from the news company, ads from an ad company, and the comments section from a different company that´s been contracted out to provide that service.) Privacy Badger keeps track of all of this. If as you browse the web, the same source seems to be tracking your browser across different websites, then Privacy Badger springs into action, telling your browser not to load any more content from that source. And when your browser stops loading content from a source, that source can no longer track you.
Voila!
At a more technical level, Privacy Badger keeps note of the "third party" domains that embed images, scripts and advertising in the pages you visit. Privacy Badger looks for tracking techniques like uniquely identifying cookies, local storage "supercookies," first to third party cookie sharing via image pixels, and canvas fingerprinting. If it observes a single third-party host tracking you on three separate sites, Privacy Badger will automatically disallow content from that third-party tracker.
In some cases a third-party domain provides some important aspect of a page´s functionality, such as embedded maps, images, or stylesheets. In those cases Privacy Badger will allow connections to the third party but will screen out its tracking cookies and referrers (these hosts have their sliders set to the middle, "cookie block" position).
https://privacybadger.org/#What-is-Privacy-Badger
Electronic Frontier Foundation ( ff-extension Privacy Badger and other ones.) against mass surveillance and eavedropping trough NSA & Co.
USA: Erneut Klage gegen Massenüberwachung durch NSA abgewiesen, netzpolitik.org, 11.05.2019
Seit Jahren kämpft die Electronic Frontier Foundation vor Gerichten gegen die Massenüberwachung durch den US-Geheimdienst NSA. Nun hat ein Bundesrichter eine Klage aus dem Jahr 2008 abgewiesen: Um die nationale Sicherheit zu schützen, müsse ein mögliches Überwachungsprogramm geheim bleiben.
https://netzpolitik.org/2019/usa-erneut-klage-gegen-massenueberwachung-durch-nsa-abgewiesen/
 The failure: As it can be seen from the key-lock left beneath the addressline, the encryption with the new TLS 1.3 is not possible on our system (el6) for mentioned firefox (52.9), either just weak or even unencrypted! The failure: As it can be seen from the key-lock left beneath the addressline, the encryption with the new TLS 1.3 is not possible on our system (el6) for mentioned firefox (52.9), either just weak or even unencrypted!
What did happen to this firefox on OpenSuSE under all the patches? Actually we can only recommend the browser Pale Moon with quit the same extensions: secret agent and/or eclipsed moon, ABL (for AdblockPlus, ABP), noscript, RequestPolicyBlockContinued, Block Content Download, n-Matrix, CanvasBlocker, JavaScript-Toggle-Buttom, script-blocker, about:config-explainer, HTTPS enforcer, Decentral Eyes and further on, at last again the "goalkeeper" Privacy Badger made by the non-profit Electronic Fourier Foundation (EFF).
 Pale Moon extension: n-Matrix Pale Moon extension: n-Matrix
Add following rules from temporary to permanent into the dashboard of n-Matrix:
 Palemoon extension nMatrix Palemoon extension nMatrix
To go sure, add the follwoing rules from temporary to permanent within the Dashboard of n-Matrix:
https-strict: * true
https-strict: behind-the-scene false
matrix-off: about-scheme true
matrix-off: chrome-extension-scheme true
matrix-off: chrome-scheme true
matrix-off: moz-extension-scheme true
matrix-off: opera-scheme true
matrix-off: wyciwyg-scheme true
no-workers: * true
referrer-spoof: * true
referrer-spoof: behind-the-scene false
* * * block
* * css block
* * frame block
* * image block
* * script block
* * xhr block
* * media block
* * other block
* 1st-party css allow
* 1st-party image allow
afterdawn.dk www.afterdawn.dk script block
...
Alone the image block from above prevents from webbugs.
Notice, that all values can be set directly within the matrix by simple mouseclicks, even upon the describing border of the matrix!
 Pale Moon extension: Block Content Downloader Pale Moon extension: Block Content Downloader
Initialization Palemoon extension "Block Content Download" each newstart of Pale Moon: through typing in about::config into the address-bar or editing /home/user/.mozilla/userprofile/user.js to set all or quit all entries named permissions.*.* up or down to 3, where 3 at least stands for "Forbid third-parties" refering to images, objects, scripts, documents and so on !
 Pale Moon extension: signTextJS Pale Moon extension: signTextJS
By: dkeeler@mozilla.com, rbarnes@mozilla.com, vbadev@gmail.com
About this add-on
window.crypto.signText is a digital signature technology that has been available to Firefox users for 20 years. It is used by government and banking sites. It can be used to participate in plebiscites.
The window.crypto interfaces were removed from Firefox 35 and later releases. An add-on was developed as a stop-gap measure for users; that add-on is deprecated and does not work since Firefox 57, but still work with Pale Moon.
This fork based on the original signTextJS-0.7.7 add-on by mozkeeler.
https://addons.palemoon.org/addon/signtextjs/
 Pale Moon extension: Modify HTTP Response Pale Moon extension: Modify HTTP Response
By: Off JustOff
About this add-on
Modify HTTP Response is designed to rewrite http response body using search & replace patterns.
Warning:
This tool works on low level API and intended for advanced users.
Incorrect filters can cause browser freeze, hang or loose data.
Never use filters from untrusted sources or if you don´t understand them.
https://addons.palemoon.org/addon/modify-http-response/
 Classic Add-ons Archive [External] Classic Add-ons Archive [External]
Catalog of classic Firefox add-ons created before WebExtensions apocalypse.
https://addons.palemoon.org/extensions/other/
 uMatrix (uM, https://github.com/gorhill/uMatrix/releases/download/1.4.1b6/uMatrix_1.4.1b6.firefox.signed.xpi) or seamonkey-noscript (5.1.9 for ff52-ESR from February 2020, includes the xpi-install-file) or uMatrix (uM, https://github.com/gorhill/uMatrix/releases/download/1.4.1b6/uMatrix_1.4.1b6.firefox.signed.xpi) or seamonkey-noscript (5.1.9 for ff52-ESR from February 2020, includes the xpi-install-file) or
mozilla-noscript (5.1.8.6, 5.1.8.5, 5.1.7-1, fc, el7, el6, fr2.rpmfind.net or mozilla.org or http://ftp.pbone.net/mirror/archive.fedoraproject.org/fedora/linux/updates/25/armhfp/Packages/m/mozilla-noscript-5.1.7-1.fc25.noarch.rpm), https://rpm.pbone.net/index.php3/stat/4/idpl/54125427/dir/
rawhide/com/mozilla-noscript-2.6.8.36-1.171.noarch.rpm.html, vom 16.11.2018 (patched 171 times, therefore the recommended version)
 mozilla-adblockplus (-2.9.1-27 fc, el7, el6 or mozilla.org), https://fr2.rpmfind.net/linux/fedora-secondary/releases/29/ mozilla-adblockplus (-2.9.1-27 fc, el7, el6 or mozilla.org), https://fr2.rpmfind.net/linux/fedora-secondary/releases/29/
Everything/i386/os/Packages/m/mozilla-adblockplus-2.9.1-4.fc29.noarch.rpm, https://fr2.rpmfind.net/linux/epel/6/x86_64/Packages/m/mozilla-adblockplus-2.6.6-1.el6.noarch.rpm
 mozilla-requestpolicy (-1.0-0.22.20171019git633302 fc27 from 02.08.2020 / 08.02.2020, el6, rpmfind.net or mozilla.org, you still have to copy it from /usr/share/mozilla/extensions/ to /home/surfuser/.mozilla/extensions/), https://fr2.rpmfind.net/linux/fedora/linux/releases/29/Everything/x86_64/os/Packages/m/ mozilla-requestpolicy (-1.0-0.22.20171019git633302 fc27 from 02.08.2020 / 08.02.2020, el6, rpmfind.net or mozilla.org, you still have to copy it from /usr/share/mozilla/extensions/ to /home/surfuser/.mozilla/extensions/), https://fr2.rpmfind.net/linux/fedora/linux/releases/29/Everything/x86_64/os/Packages/m/
mozilla-requestpolicy-1.0-0.22.20171019git633302.fc29.noarch.rpm, https://fr2.rpmfind.net/linux/epel/6/x86_64/Packages/m/mozilla-requestpolicy-1.0-0.19.20171019git633302.el6.noarch.rpm
mozilla-https-everywhere (fc, el6 or mozilla.org), https://fr2.rpmfind.net/linux/fedora/linux/
updates/29/Everything/x86_64/Packages/m/mozilla-https-everywhere-2019.11.7-1.fc29.noarch.rpm, https://fr2.rpmfind.net/linux/epel/6/x86_64/Packages/m/mozilla-https-everywhere-2019.11.7-1.el6.noarch.rpm
firefox-ublock_origin (alt1, pkgs.org, mozilla.org)
 CanvasBlocker (mozilla.org, against Canvas Fingerprinting) CanvasBlocker (mozilla.org, against Canvas Fingerprinting)
 CookieController (mozilla.org, part of Jondofox) CookieController (mozilla.org, part of Jondofox)
Private Tab (mozilla.org)
 RefControl (mozilla.org, Referer Control) RefControl (mozilla.org, Referer Control)
 UserAgentSwitcher (mozilla.org) UserAgentSwitcher (mozilla.org)
 Link Redirect Fixer (mozilla.org) Link Redirect Fixer (mozilla.org)
Link_Cleaner (mozilla.org)
 secretagent (anonymizing useragents; extension from palemoon.org) secretagent (anonymizing useragents; extension from palemoon.org)
 CSS Exfil Protection by Mike Gualtieri ( xpi from mozilla.org, https://addons.cdn.mozilla.net/ CSS Exfil Protection by Mike Gualtieri ( xpi from mozilla.org, https://addons.cdn.mozilla.net/
user-media/addons/931864/css_exfil_protection-1.0.17-an+fx.xpi )
TrackMeNot (xpi), Firefox extension to protect web habits from tracking and profiling, protect against data profiling by search engines, "TrackMeNot is a lightweight browser extension that helps protect web searchers from surveillance and data-profiling by search engines. It does so not by means of concealment or encryption (i.e. covering one´s tracks), but instead by the opposite strategy: noise and obfuscation. With TrackMeNot actual web searches, lost in a cloud of false leads, are essentially hidden in plain view. User-installed TrackMeNot works with Firefox and Chrome browsers, integrates with all popular search engines and requires no 3rd-party servers or services. TrackMeNot runs as a low-priority background process, that periodically issues randomized search-queries to popular search engines, e.g., AOL, Yahoo!, Google, and Bing. It hides users´ actual search trails in a cloud of ´ghost´ queries, significantly increasing the difficulty of aggregating such data into accurate or identifying user profiles. TrackMeNot serves as a means of amplifying users´ discontent with advertising networks, that not only disregard privacy, but also facilitate the bulk surveillance agendas of corporate and government agencies, as documented recently in disclosures by Edward Snowden and others. To better simulate user behavior TrackMeNot uses a dynamic query mechanism to ´evolve´ each client (uniquely) over time, parsing the results of its searches for ´logical´ future query terms with which to replace those already used.
Public awareness of the vulnerability of searches to systematic surveillance and logging by search engine companies was initially raised in the wake of a case, initiated August 2005, in which the United States Department of Justice (DOJ) issued a subpoena to Google for one week´s worth of search query records (absent identifying information) and a random list of one million URLs from its Web index. This was cited as part of its defense of the constitutionality of the Child Online Protection Act (COPA). When Google refused, the DOJ filed a motion in a Federal District Court to force compliance. Google argued that the request imposed a burden, would compromise trade secrets, undermine customers´ trust in Google, and have a chilling effect on search activities. In March 2006, the Court granted a reduced version of the first motion, ordering Google to provide a random listing of 50,000 URLs, but denied the second motion, namely, the request for search queries.
While viewed from the perspective of user privacy this seems a good outcome, yet it does bring to light several disquieting points. First, from court documents we learn that AOL, Yahoo!, and Microsoft have complied with the government´s request, though details are not given. Second, we must face the reality that logs of our online searches are in the hands of search companies and can be quite easily linked to our identities. Thirdly, it is clear we have little idea of, or say in, what can be done with these logs. While, in this instance, Google withheld such records from the Government, it would be foolish to count on this outcome in the future. Public awareness of the vulnerability of searches to systematic surveillance and logging by search engine companies, was initially raised in the wake of a case, initiated August 2005, in which the United States Department of Justice (DOJ) issued a subpoena to Google for one week´s worth of search query records (absent identifying information) and a random list of one million URLs from its Web index. This was cited as part of its defense of the constitutionality of the Child Online Protection Act (COPA). When Google refused, the DOJ filed a motion in a Federal District Court to force compliance. Google argued that the request imposed a burden, would compromise trade secrets, undermine customers´ trust in Google, and have a chilling effect on search activities. In March 2006, the Court granted a reduced version of the first motion, ordering Google to provide a random listing of 50,000 URLs, but denied the second motion, namely, the request for search queries.
While viewed from the perspective of user privacy this seems a good outcome, yet it does bring to light several disquieting points. First, from court documents we learn that AOL, Yahoo!, and Microsoft have complied with the government´s request, though details are not given. Second, we must face the reality that logs of our online searches are in the hands of search companies and can be quite easily linked to our identities. Thirdly, it is clear we have little idea of, or say in, what can be done with these logs. While, in this instance, Google withheld such records from the Government, it would be foolish to count on this outcome in the future.
TrackMeNot is user-installed and user-managed, residing wholly on users´ system and functions without the need for 3rd-party servers or services. Placing users in full control is an essential feature of TrackMeNot, whose purpose is to protect against the unilateral policies set by search companies in their handling of our personal information. We have developed TrackMeNot as an immediate solution, implemented and controlled by users themselves. It fits within the class of strategies, described by Gary T. Marx, whereby individuals resist surveillance by taking advantage of blind spots inherent in large-scale systems1. TrackMeNot may not radically alter the privacy landscape but helps to place a particularly sensitive arena of contemporary life back in the hands of individuals, where it belongs in any free society.
Special thanks to the NYU Dept of Computer Science, the Media Research Lab, the Mozilla Foundation, Missing Pixel, the Portia Project, Babelzilla, Ernest Davis, Michael Zimmer, John Fanning, and Robb Bifano."
Details and installation from
https://www.cs.nyu.edu/trackmenot/, https://trackmenot.io
 Firefox Addons Firefox Addons
Firefox Multi-Account Containers Version 8.0.6, CHIP, 21.02.2022
Trennung von Privatem und Geschäftlichem
Mehr Privatsphäre beim Surfen
Umfangreiche Anpassungsmöglichkeiten
Mit dem kostenlosen Firefox Add-on "Multi-Account Containers" trennen Sie beim Surfen verschiedene Bereiche wie Online-Banking, Arbeit oder privates Surfen technisch voneinander, indem Sie Container festlegen und Webseiten passend einordnen.
In einem Tab checkt man die geschäftlichen E-Mails, in einem anderen ist der private Facebook-Account offen und im Dritten erledigt man Online-Banking: "Multi-Account Containers für Firefox" will diese verschiedenen Arbeitsbereiche innerhalb eines Browserfensters trennen und dadurch Ihre Privatsphäre stärker schützen.
Multi-Account Containers für Firefox: Ein Browserfenster, mehrere Accounts
[...] So können Sie beispielsweise Ihren Social-Media-Account geöffnet lassen, ohne das Facebook und Co. alles über Ihr restliches Surfverhalten mitbekommen.
https://www.chip.de/downloads/Firefox-Multi-Account-Containers_133326187.html
Privacy Badger - "Privacy Bader - How does Privacy Badger work?
When you view a webpage, that page will often be made up of content from many different sources. (For example, a news webpage might load the actual article from the news company, ads from an ad company, and the comments section from a different company that´s been contracted out to provide that service.) Privacy Badger keeps track of all of this. If as you browse the web, the same source seems to be tracking your browser across different websites, then Privacy Badger springs into action, telling your browser not to load any more content from that source. And when your browser stops loading content from a source, that source can no longer track you. Voila!
At a more technical level, Privacy Badger keeps note of the "third party" domains that embed images, scripts and advertising in the pages you visit. Privacy Badger looks for tracking techniques like uniquely identifying cookies, local storage "supercookies," first to third party cookie sharing via image pixels, and canvas fingerprinting. If it observes a single third-party host tracking you on three separate sites, Privacy Badger will automatically disallow content from that third-party tracker.
In some cases a third-party domain provides some important aspect of a page´s functionality, such as embedded maps, images, or stylesheets. In those cases Privacy Badger will allow connections to the third party but will screen out its tracking cookies and referrers (these hosts have their sliders set to the middle, "cookie block" position).
Does Privacy Badger account for a cookie that was used to track me even if I deleted it?
Yes. Privacy Badger keeps track of cookies that could be used to track you and where they came from, even if you frequently clear your browser´s cookies.
Does Privacy Badger still work when blocking third-party cookies in the browser?
When you tell your browser to deny third-party cookies, Privacy Badger still gets to learn from third parties trying to set cookies via HTTP headers (as well as from other tracking techniques such as pixel cookie sharing and canvas fingerprinting). Privacy Badger no longer gets to learn from cookies or HTML5 local storage being set via JavaScript, however. So, Privacy Badger still works, it´ll just learn to block fewer trackers. Clearing history or already-set cookies shouldn´t have any effect on Privacy Badger.
How does Privacy Badger handle social media widgets?
Social media widgets (such as the Facebook Like button, Twitter Tweet button, or Google +1 button) often track your reading habits. Even if you don´t click them, the social media companies often see exactly which pages you´re seeing the widget on. Privacy Badger includes a feature imported from the ShareMeNot project which is able to replace the widgets with a stand-in version, so that you can still see and click them. You will not be tracked by these replacements unless you explicitly choose to click them. Privacy Badger currently knows how to replace the following widgets if they are observed tracking you: AddThis, Facebook, Google, LinkedIn, Pinterest, Stumbleupon, and Twitter. (The source code for these replacements is here; pull requests are welcome.)
Note, that Privacy Badger will not replace social media widgets unless it has blocked the associated tracker. If you´re seeing real social media widgets, it generally means that Privacy Badger hasn´t detected tracking from that variant of the widget, or that the site you´re looking at has implemented its own version of the widget. To avoid confusion, the replacement widgets are marked with the Privacy Badger badge next to the button. To interact with a replacement widget, simply click on it. Depending on the widget, Privacy Badger will either send you directly to the appropriate sharing page (for example, to post a tweet) or it will enable and load the real social widget (for example, the Facebook Like button, with personalized information about how many of your friends have "liked" the page). In the second case, you will still need to interact with the real widget to "like" or share the page."
https://privacybadger.org/#How-does-Privacy-Badger-work
https://privacybadger.org/
https://www.eff.org/files/privacy-badger-latest.xpi
 Librefox: https://github.com/intika/Librefox/releases/download/ Librefox: https://github.com/intika/Librefox/releases/download/
Librefox-v2.1-v64.0.0/Librefox-2.1-Firefox-Linux-64.0.0.zip
 Update MozillaFirefox-52.9.0 (OpenSuSE: Februar 2019, gecko-engine / firefox-extensions ) with the at this time actual firefox-68.6.0 (el6, April 2020, quantum engine / webextensions): Update MozillaFirefox-52.9.0 (OpenSuSE: Februar 2019, gecko-engine / firefox-extensions ) with the at this time actual firefox-68.6.0 (el6, April 2020, quantum engine / webextensions):
As of February 2019
Enpack the following files out of rpm firefox-68.6.0 (el6, rpm, as of April 2020) into /usr/lib64/firefox/
gtk2 (directory)
fonts (directory)
run-mozilla.sh
libmozavcodec.so
libmozavutil.so
libmozsqlite3.so
libssl3.so (out of rpm openssl-1.1.1a up to openssl-1.1.1e)
Enpack the following files out of seamonkey (el6, rpm, as of: September 2019) into /usr/lib64/firefox/
liblgpllibs.so
libmozsandbox.so
plugin-container.so
Enpack the following files out of seamonkey (el6, rpm, as of: September 2019) into /usr/lib64/firefox/chrome/icons/default
en-US.aff
en-US.dic
Enpack the following files out of seamonkey (el6, rpm, Stand: September 2019) into /usr/lib64/firefox/browser/
blocklist.xml
Eventuelly remove IDs etc.
Edit /usr/lib64/firefox/application.ini and /usr/lib64/firefox/platform.ini and set the values as you like.
user.js
Firefox part within "about:config" gets autoconfigured each start of firefox. The configuration file named user.js making it possible can be found in the profil in /home/surfuser/.mozilla/firefox/profilename/.
Details of user.js are listed furhter below.
Still not updated: libxul.so (gecko, as of: February 2019). If this disturbs you, install seamonkey (el6) or
patch the firefox-source-code with patches from
https://hg.mozilla.org/releases/mozilla-esr60 (diff)
https://hg.mozilla.org/releases/mozilla-esr68 (diff)
 FirefoxESR-52-patches 2019- up to now: FirefoxESR-52-patches 2019- up to now:
2019-11-30 Updated package firefox-esr52 52.9.0-5 Muflone
2019-06-22 Updated package firefox-esr52 52.9.0-4 Muflone
2019-06-13 Updated package firefox-esr52 52.9.0-3 Muflone
2018-08-11 Updated package firefox-esr52 52.9.0-2 Muflone
https://aur.archlinux.org/cgit/aur.git/?h=firefox-esr52
Update Mozilla Firefox Javascript
mozjs (el6)
https://fr2.rpmfind.net
Alternatively Firefox-ESR >= 60 (el6), ff-60-ESR (el6), ff-68-ESR (el6), ... with engine Quantum and Webextensions does not enable most important extensions like RequestPolicy(BlockContinued).
 Anonymizing user-agents for extensions like secretagent: Anonymizing user-agents for extensions like secretagent:
"Privoxy/1.0"
"Mozilla/5.0 (compatible; Googlebot/2.1; +http://www.google.com/bot.html)"
"Mozilla/5.0 (compatible; bingbot/2.0; +http://www.bing.com/bingbot.htm)"
"Mozilla/5.0 (compatible; Yahoo! Slurp; http://help.yahoo.com/help/us/ysearch/slurp)"
"Mozilla/5.0 (compatible; Gooken; +http://www.gooken.de)"
Warning: This Firefox is without extensions like Request(Block)PolicyContinued !
 [SOLVED by Gooken, 15.03.2020] Firefox doesn´t show the actual extension version number for the extension installed by rpm within the item "Addons" from menu, so that Firefox is still working with the old, previous version installed before? [SOLVED by Gooken, 15.03.2020] Firefox doesn´t show the actual extension version number for the extension installed by rpm within the item "Addons" from menu, so that Firefox is still working with the old, previous version installed before?
This might happen for mozilla-adblockplus for example, as the xpi-file is missing within the package!
Copy all of this extenisons out of /usr/share/mozilla/extensions into /home/surfuser/.mozilla/extensions ("cp -axf"), set the owner- and acess-rights upon it and delete the belonging xpi-file (of the previous version) out of the subdirectory of the profile. Now the correct version number is shown in Addons, with wich Firefox will work in future.
 Does the Browser restrict websites (formulars and so on) although extension like ABP, noscript and RequestPolicyBlockContinuned and so on got reconfigured? Does the Browser restrict websites (formulars and so on) although extension like ABP, noscript and RequestPolicyBlockContinuned and so on got reconfigured?
If a reconfiguration of the extensions does not help at all, deactivate them in addons->extensions - extension by extension or, if nothing helps: all at once!
Now Firefox-52.9.0-ESR should really enable quit all functionality for websites.
After meant websites are left, do not forget to activate the extensions again!
 [ SOLVED : Websites with too much restrictions possible caused by extensions or security settings: No possible login etc. ] [ SOLVED : Websites with too much restrictions possible caused by extensions or security settings: No possible login etc. ]
If even the resetting of extensions does not help, create one more, new profile in about:profiles, set it temporary to the default profile and
restart firefox.
 Quit all files of ESR-52.9.0 except libxul.so, some libraries and the mask for settings omni.ja can be exchanged with those from newer Firefox like ESR-60.9.0 and ESR-68. Quit all files of ESR-52.9.0 except libxul.so, some libraries and the mask for settings omni.ja can be exchanged with those from newer Firefox like ESR-60.9.0 and ESR-68.
 Update kmozillahelper (zombie process): kmozillahelper (rosa2014.1) or deinstall it by "rpm -e --nodeps kmozillahelper" Update kmozillahelper (zombie process): kmozillahelper (rosa2014.1) or deinstall it by "rpm -e --nodeps kmozillahelper"
More about "security with firefox (Gecko)":
from this webside further below!
 Tails 4.2 improves automatic update Tails 4.2 improves automatic update
https://www.pro-linux.de/news/1/27707/tails-42-verbessert-das-automatische-update.html
Look for your Linux, if possible too.
 AppAmor - "o´zapft is?" AppAmor - "o´zapft is?"
AppArmor - broaching the computer system or kernel-security-module?, Gooken, 06.07.019
Profiles of AppArmor are: passwd, Browser, D-Bus, Netzwerk, Task-Manager (cron), dhclient, dhcp, DAPRA-portmap, tmpwatch, procmail, skype, wireshark, ftpd, mysqld, postfix, sendmail, squid, sshd, useradd, vsftpd, xinetd, fingerd, ntalkd, cupsd, xfs, ping, nvidia_modprobe, dovecot, apache2, dnsmasq, ntpd, identd, smbd, traceroute, winbindd, lessopen, klogd, avahi-daemon, ...
AppArmor works during the system boot by default for Linux like Debian Linux Tails. The boot time even more than doubles by this.
The module itself can be intergrated as a kernel security module as a kernel-boot-paramter. Pre-configured profiles can be envoked for example in /etc/rc.local.
The developer contracted with Microsoft years ago. Linus Tovalds recommends such securiy module, that can be integrated beneath Module SELinux developed by the NSA, discussed in another report we published in News&Links and japanese Tomoyo Linux (rosa, mdv).
Like all other MAC (Mandatory Access Control for the control of process interaction), AppArmor isn´t necessary to bound in "secure=none" in our kernel-bootline.
Original program description from rpmfind.net: "AppArmor is a security framework that proactively protects the operating system and applications. This package provides the libapparmor library, which contains the change_hat(2) symbol, used for sub-process confinement by AppArmor, as well as functions to parse AppArmor log messages.
Base profiles. AppArmor is a file and network mandatory access control mechanism. AppArmor confines processes to the resources allowed by the systems administrator and can constrain the scope of potential security
vulnerabilities. This package is part of a suite of tools that used to be named SubDomain."
"AppArmor is security Linux kernel module similar to the SELinux but it´s supposed to be easier to setup and maintain. There are many reasons for you to disable it, primary one is that its security features can get in the way of legitimate applications operation", https://www.techytalk.info/disable-and-remove-apparmor-on-ubuntu-based-linux-distributions/
Also see our report: serious hard News-Group-discussion about NSA´s SELinux.
Later on, the programming expert of AppArmor became a paid expert of Microsoft. We made the expirience, our computer system runs quit different fast, depending on night and daytime and the kind of information we handled. But without all the kernel-security-modules, AppArmor and so on, it always runs as fast as the mouseclick allows: mouseclick-fast.
AppArmor is a security module for Linux. It is a Mandatory Access Control (MAC) System controlling each application and program through profiles with access rights refining the common ones. Beneath the default profiles any profiles can be created. For each profile one of three modes has to be set.
https://wiki.ubuntuusers.en/AppArmor/
Howto use Windows within Linux through Virtualbox, PC-WELT.de, 08.05.2019
Per virtualization it is possible to use software and apps for Windows for Linux too. We show, howto.
https://www.pcwelt.de/ratgeber/Windows-als-virtuellen-PC-in-Linux-weiternutzen-9790033.html
Virtualbox (el6, all Linux): VirtualBox-6.0-6.0.6_130049_el6-1.x86_64.rpm from 16-Apr-2019 118M ( or VirtualBox-5.2-5.2.28_130011_Linux_x86.run ) and UserManual.pdf from
https://download.virtualbox.org/virtualbox/6.0.6
Alternatively: qemu (el6, all Linux), virt-manager (el6) and libvirt (el6), wine64 (el6, all Linux, 64-Bit-MS-Windows-Emulator) and wine (el6, all Linux, 32-Bit-MS-Windows-Emulator)
Wonderful Unix, wonderful OpenSource ("tick-tick-tick-..."), we are right (addition from 07.09.2013): Tagesschau reports about weak-points in many security software. The industry for software would have been built-in backdoors in their programs. It were possible to get information right before a user encrypts them and to send them over the internet. Super-computer were constructed to crack encrypted codes. NSA-program "Bullrun" belonged to the most kept secrets. The british agency GCHQ were very successfull in cracking code. Such analyses would have belonged to Google, Yahoo, Facebook und Microsoft.
From banking software up to election computer, if databases, data protection or data security: Only OpenSource-Software can be trusted!
Since 1981/82: Black monitors, tons of updates (terrabytes), Cyberwar, Suneater, missing driver, driver- and hardware failouts, glibc-patch, openssl-patch, system breakdowns ( a.o. python), defect kernel and glibc, Dirty Cow, Sambacry, Meltdown and Spectre, security access points in browser, hacker, trojans, viruses, unsolved packet-dependencies and so on and on
It must be the kind of (artificial-) bomb in each computer, because in any operating system and a lot of software and updates over updates, but through Gooken´s "Universal Linux 2010" it manges the first time past over 25 years to disarm it.
 New computer: Four things you should do right up from the beginning, PC-WELT.de, 02.03.2020 New computer: Four things you should do right up from the beginning, PC-WELT.de, 02.03.2020
It does not matter, how young or old you are: It is a beautiful feeling to start a new computer. Care yourself for the security right up from the beginning.
https://www.pcwelt.de/international/Neuer-Computer-Vier-Dinge-die-
Sie-gleich-zu-Beginn-machen-sollten-10763901.html
2009/2010: Year of the hardware, year of the software (CentOS el6, Mandriva2010) - ALL talk around the computer got passed! (!!!)
... almost surface-covering and security technically: just completion and updating (see the update-listing from our webside "Universal Linux 2010"! CentOS- and SL-updates (el6) are provided in the internet from year 2010 up to year 2026 and (mit el7) longer. Belonging power saving, mouseclick-fast and Linux-compatible lifetime-hardware (*) quit for free is listed in our -> data sheed device by devcie: all-in-one-mainboard, net adapter, all poor radiationed and supersilent, ultraslim-WLED-TFT, SSD, rom-drives (DVD-burner), multifunction-printer (printing- scanning - faxing and copying), mouse/keyboard, computer tower, ...
This all although the computer standed (and stands) for "nothings more "kaputter" (out of order)"... (following the excurs and see News&Links)! Lifetime-hardware (*): We are going to report about errorcs and defects of the mainboard under data sheed in future. There are none up to now.
 Avoid these 14 mistakes and errors during building up your PC ( hardware ) by yourself !, PC-WELT.de, 04.07.2020 Avoid these 14 mistakes and errors during building up your PC ( hardware ) by yourself !, PC-WELT.de, 04.07.2020
If you build up a PC for the first time by yourself, take notice of 14 important things. Otherwiese you might have a big bad suprise!
https://www.pcwelt.de/ratgeber/tipp-pc-selbst-bau-fehler-vermeiden-10834772.html
 Moving into a bad, bad world... Moving into a bad, bad world...
From Saturn-Service-Center: PC-build-up - Bios-Setup - partitonswise or complete mirroring (best done by the UNIX-/Linux-command dd) OR: partitionize - formatting (Linux-filesystem, almost ext4) - encryption (of most partitions) - installation - configuration - defragmentation (not required for Linux) - making updates:
Put your installation-DVD into the CD/DVD-drive to install the operating system, together with other belonging software. We assume the rpm-(packet-manager-) based Enterprise Linux (RHEL, Fedora, CentOS or Scientific Linux) or a Mandriva-Derivat (PC Linux OS, Rosa, Mageia, Mandriva), but refer to Debian Linux and so on and (indirectly) MS Windows too!
Follow the installation-steps from DVD (resp. other media like USB)!
Do all other steps by handbooks and guidelines from manufacturer, then follow this excurs!
For the partioning, under Linux at all formlized in the device-file fstab (/etc/fstab), we recommend already at this place at least 80 GB for the Root- and 20 GB for the home-partition, around 1 GB for the Boot-partition and the threefold of the RAM-size for the SWAP-partition (memory-swapping file).
Good to know, that encryption is possible already at this place for partitioning resp. right up after the formatting. We also refer to this namely later on in detail !
Installation und update sources Enterprise Linux CentOS resp. Scientific Linux (el6, el7):
http://mirror.eu.oneandone.net/linux/distributions/centos/6.10/isos/x86_64/
http://mirror.jgotteswinter.com/centos/6.10/isos/x86_64/
http://wftp.tu-chemnitz.de/pub/linux/centos/6.10/isos/x86_64/
http://ftp.halifax.rwth-aachen.de/centos/6.10/isos/x86_64/
http://ftp.rrzn.uni-hannover.de/centos/6.10/isos/x86_64/
http://mirror.de.leaseweb.net/centos/6.10/isos/x86_64/
http://mirror.softaculous.com/centos/6.10/isos/x86_64/
http://artfiles.org/centos.org/6.10/isos/x86_64/
http://mirror.cuegee.de/centos/6.10/isos/x86_64/
http://centos.bio.lmu.de/6.10/isos/x86_64/
http://ftp.hosteurope.de/mirror/centos.org/6.10/isos/x86_64/
http://mirror.daniel-jost.net/centos/6.10/isos/x86_64/
http://mirrors.cicku.me/centos/6.10/isos/x86_64/
http://mirror.yannic-bonenberger.com/centos/6.10/isos/x86_64/
http://centos.datente.com/media/6.10/isos/x86_64/
http://mirror.dataone.nl/centos/6.10/isos/x86_64/
http://centos.schlundtech.de/6.10/isos/x86_64/
http://ftp.plusline.de/centos/6.10/isos/x86_64/
http://ftp.fau.de/centos/6.10/isos/x86_64/
http://centos.mirrors.as250.net/6.10/isos/x86_64/
http://mirror2.hs-esslingen.de/centos/6.10/isos/x86_64/
http://mirror1.hs-esslingen.de/pub/Mirrors/centos/6.10/isos/x86_64/
http://mirror.rackspeed.de/centos.org//6.10/isos/x86_64/
http://mirror.ratiokontakt.de/mirror/centos/6.10/isos/x86_64/
http://mirror.netcologne.de/centos/6.10/isos/x86_64/
http://repo.de.bigstepcloud.com/centos/6.10/isos/x86_64/
http://mirror.euserv.net/linux/centos/6.10/isos/x86_64/
http://ftp.wrz.de/pub/CentOS/6.10/isos/x86_64/
http://centos.intergenia.de/6.10/isos/x86_64/
http://centos.mirror.net-d-sign.de/6.10/isos/x86_64/
http://mirror.imt-systems.com/centos/6.10/isos/x86_64/
http://mirror.23media.de/centos/6.10/isos/x86_64/
Nearby Countries
http://mirror.unix-solutions.be/centos/6.10/isos/x86_64/
http://centos.cu.be/6.10/isos/x86_64/
http://mirror.kinamo.be/centos/6.10/isos/x86_64/
http://centos.mirror.nucleus.be/6.10/isos/x86_64/
http://mirror.spreitzer.ch/centos/6.10/isos/x86_64/
http://linuxsoft.cern.ch/centos/6.10/isos/x86_64/
http://mirror.switch.ch/ftp/mirror/centos/6.10/isos/x86_64/
http://pkg.adfinis-sygroup.ch/centos/6.10/isos/x86_64/
http://mirror.plusserver.com/centos/6.10/isos/x86_64/
http://ftp.ciril.fr/pub/linux/centos/6.10/isos/x86_64/
http://mirror1.evolution-host.com/centos/6.10/isos/x86_64/
http://centos.crazyfrogs.org/6.10/isos/x86_64/
http://distrib-coffee.ipsl.jussieu.fr/pub/linux/centos/6.10/isos/x86_64/
http://centos.mirror.fr.planethoster.net/6.10/isos/x86_64/
http://ftp.rezopole.net/centos/6.10/isos/x86_64/
http://mirror.in2p3.fr/linux/CentOS/6.10/isos/x86_64/
http://mirrors.ircam.fr/pub/CentOS/6.10/isos/x86_64/
http://mir01.syntis.net/CentOS/6.10/isos/x86_64/
ftp://ftp.free.fr/mirrors/ftp.centos.org/6.10/isos/x86_64/
http://mirrors.standaloneinstaller.com/centos/6.10/isos/x86_64/
http://centos.mirrors.ovh.net/ftp.centos.org/6.10/isos/x86_64/
http://centos.mirror.ate.info/6.10/isos/x86_64/
http://fr.mirror.babylon.network/centos/6.10/isos/x86_64/
http://centos.quelquesmots.fr/6.10/isos/x86_64/
http://ftp.pasteur.fr/mirrors/CentOS/6.10/isos/x86_64/
http://mirrors.atosworldline.com/public/centos/6.10/isos/x86_64/
http://mirror.ibcp.fr/pub/Centos/6.10/isos/x86_64/
http://miroir.univ-paris13.fr/centos/6.10/isos/x86_64/
http://fr2.rpmfind.net/linux/centos/6.10/isos/x86_64/
http://centos.trisect.eu/6.10/isos/x86_64/
http://linux.cs.uu.nl/centos/6.10/isos/x86_64/
http://mirror.yourwebhoster.eu/centos/6.10/isos/x86_64/
http://mirror.colocenter.nl/pub/centos/6.10/isos/x86_64/
http://mirror.proserve.nl/centos/6.10/isos/x86_64/
http://mirror.i3d.net/pub/centos/6.10/isos/x86_64/
http://mirror.serverbeheren.nl/centos/6.10/isos/x86_64/
http://mirror.amsiohosting.net/centos.org/6.10/isos/x86_64/
http://mirror.1000mbps.com/centos/6.10/isos/x86_64/
http://mirror.widexs.nl/ftp/pub/os/Linux/distr/centos/6.10/isos/x86_64/
http://mirror.previder.nl/centos/6.10/isos/x86_64/
http://mirror.nl.leaseweb.net/centos/6.10/isos/x86_64/
http://mirror.denit.net/centos/6.10/isos/x86_64/
http://mirror.sitbv.nl/centos/6.10/isos/x86_64/
http://ftp.tudelft.nl/centos.org/6.10/isos/x86_64/
http://nl.mirror.babylon.network/centos/6.10/isos/x86_64/
http://mirror.cj2.nl/centos/6.10/isos/x86_64/
http://mirror.oxilion.nl/centos/6.10/isos/x86_64/
http://centos.ams.host-engine.com/6.10/isos/x86_64/
http://ftp.nluug.nl/ftp/pub/os/Linux/distr/CentOS/6.10/isos/x86_64/
http://mirror.netrouting.net/centos/6.10/isos/x86_64/
http://mirror.prolocation.net/centos/6.10/isos/x86_64/
http://centos.mirror1.spango.com/6.10/isos/x86_64/
http://mirror.schoemaker.systems/centos/6.10/isos/x86_64/
http://mirror.nforce.com/pub/linux/CentOS/6.10/isos/x86_64/
http://mirrors.supportex.net/centos/6.10/isos/x86_64/
http://mirrors.noction.com/centos/6.10/isos/x86_64/
http://centos.mirror.triple-it.nl/6.10/isos/x86_64/
http://centos.mirror.transip.nl/6.10/isos/x86_64/
http://mirror.fysik.dtu.dk/linux/centos/6.10/isos/x86_64/
http://ftp.klid.dk/ftp/centos/6.10/isos/x86_64/
http://mirrors.dk.telia.net/centos/6.10/isos/x86_64/
http://mirror.one.com/centos/6.10/isos/x86_64/
http://ftp.crc.dk/centos/6.10/isos/x86_64/
http://mirror.mhd.uk.as44574.net/mirror.centos.org/6.10/isos/x86_64/
http://centos.mirrors.nublue.co.uk/6.10/isos/x86_64/
http://mirrors.melbourne.co.uk/sites/ftp.centos.org/centos/6.10/isos/x86_64/
http://www.mirrorservice.org/sites/mirror.centos.org/6.10/isos/x86_64/
http://anorien.csc.warwick.ac.uk/mirrors/centos/6.10/isos/x86_64/
http://mirrors.clouvider.net/CentOS/6.10/isos/x86_64/
http://mirror.bytemark.co.uk/centos/6.10/isos/x86_64/
http://mirror.econdc.com/centos/6.10/isos/x86_64/
http://mirrors.vooservers.com/centos/6.10/isos/x86_64/
http://mirrors.ukfast.co.uk/sites/ftp.centos.org/6.10/isos/x86_64/
http://centos.serverspace.co.uk/centos/6.10/isos/x86_64/
http://centos.mirroring.pulsant.co.uk/6.10/isos/x86_64/
http://mirror.sov.uk.goscomb.net/centos/6.10/isos/x86_64/
http://mirror.vorboss.net/centos/6.10/isos/x86_64/
http://mirror.ox.ac.uk/sites/mirror.centos.org/6.10/isos/x86_64/
http://mirrors.coreix.net/centos/6.10/isos/x86_64/
http://mirror.sax.uk.as61049.net/centos/6.10/isos/x86_64/
http://mirror.cov.ukservers.com/centos/6.10/isos/x86_64/
http://repo.uk.bigstepcloud.com/centos/6.10/isos/x86_64/
http://mirror.as29550.net/mirror.centos.org/6.10/isos/x86_64/
...
...
Such listed "lifetime-hardware" from our data sheed ( like the low powered mainboard ASUS ITX-220, SSD, DVD-ROM-Burner and introduced AOC-TFT) does - within common outdoor temperature tolerances - not show any symptoms andtherefore - past "endless" powering on and offs and resets (new starts) of the computer system, even not those ones like the following:
 Software::Distributionen::Debian Software::Distributionen::Debian
Debian turns packet format from DEB to RPM, PRO-LINUX, 02.04.2019
https://www.pro-linux.de/news/1/26921/debian-stellt-auf-rpm-um.html
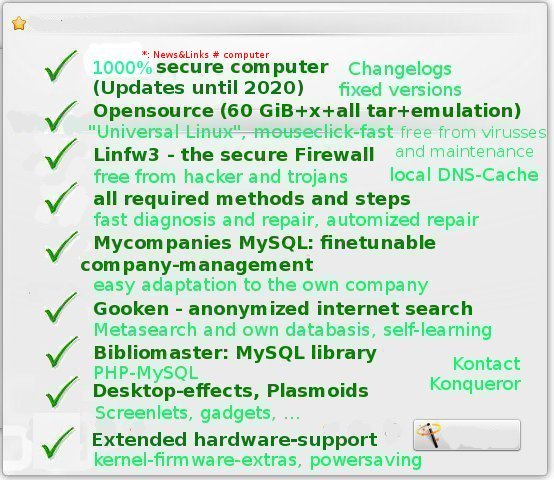
 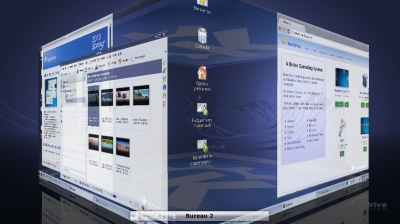 Year 2010: All for the computer is done (only updating remains essential)!
Year 2010: All for the computer is done (only updating remains essential)!
Computing without any risks: Power-saving, mouseclick-fast all-in-one lifetime-hardware (quit)
-
(quit) for free
-
breathtaking mouseclick-fast already upon listed hardware from see under "data sheed" (immediately appearing graphics per mouseclick, fast graphics (* some intensive memory programs like browser and dolphin depending on the kernel version and RAM still might need a few seconds)). This is also a good indication for a tuned, fine working system with freeness from hacker and trojans and so on.
-
"Universal Linux 2010": of at least 8 MB RAM: We tested "Universal Linux 2010" out of kernel-4.19 (pclos, highly recommended, but our choice: 5.4.110 (pclos1) past 4.20.13 (pclos1), alternatively: kernel-4.18 (el8), kernel-4.9 (el6), kernel-2.32 (el6)); tls1.3 requires kernel >= 4.13, see https://www.security-insider.de/https-mit-tls-13-in-der-praxis-a-714096/), if functioning, mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)), glibc (el8: 2.28, pclos: the actual 2.31, mga6: 2.22, fc, for printers with 32-bit driver only like Brother install glibc (2.22, el6) too and relink and delete adequately in /lib), qt4 (el6) and KDE 4 as a mix out of kde (mdv2010.2, November 2011), kde (el6, actual patched, year 2018) and kde (4.4.4, OpenSuSE, 2013), glibc like glibc (pclos: 2.31),
kernel-firmware (around 250 MB, OpenSuSE, slack 14.2, el6,...), kernel-firmware-extra
If glibc (mga6, 2.22, pclos) is kept, el8, pclos (at this time 2.31), el7, el6 and ROSA (see our section Update "Universal Linux 2010") provide quit good alternatives to such high versioned Fedora Core (fc >= 29).
If a 32-bit-printer-driver is used, keep the previous glibc for i586, just install glibc (pclos: 2.31 x86_64, el6, x86_64)!
In order to avoid error-messages of glibc (el8) during system-boot, just remove the line LC_TIME=de_DE.UTF-8 in /etc/sysconfig/i18n ! Eventually install locales (pclos, mga7, mga6), locales-en, locales-de, ... too.
After the installation of kernel-4.19 (pclos), lookout for the requirements and install missing ones like kmod (pclos): "rpm -qi --requires kernel-4.19....".
-
without any breakdowns (stable hard- and software)
-
shock-proofed ( SSD )
-
break-in-protection (chassis intrusion detection, baby phone etc.)
-
standardized, scientific Open Source (code from project groups and software practica of universities)
-
self-repairing
-
surface covering software (client, server, all rubriques including 3D- und 2D-games, ...) and all already installed on harddisc
-
free from licence fees
-
free from all maintenance
-
free from virusses, worms, hacker, trojans, malware, adware, spyware, Meltdown and Spectre, pharming, spam, phishing, bots, tracking-scripts, cryptominers, driver-problems, ...
-
without need of playing doctor (without essential harddisc-scans and self-checks)
-
free from any password-hacks and -cracks by locked system and user accounts upon /sbin/nologin for the login-shell, by using (access-protected) key-files from harddisc for the
-
LUKS-encrypted partitions (except the LUKS-encrypted root-partition), common read/write/executable/suid/sgid/sticky-access-rights and ACL together with owner rights upon processes directories and files ( especially /usr/bin/su and /bin/su )
-
through special kernel-, boot- and mount options, pamd-Login
-
Start of X (X11, X-Windows) through options -nolisten tcp and -xauth, special "xhost-"-locks for other user
-
Kernel-Securty-Modules (grub-boot-option security): MAC (what is not needed anymore to achieve promised total security, it´s just for lovers): Mandatory Access Control (restricatable process interaction): AppArmor, Tomoyo (graphical support), SELinux, ...
-
All root owned processes except X (and mgetty/mingetty, if installed) are started by kthreadd and belong to the kernel
-
Hardened kernel (not essentially needed, it origins from Kernel-Security-Module secumod): grsecurity-patches, paxctld
-
communication and surfing without any tracks in the world wide web and internet (prconfigured through prefs.js resp. user.js, through firejail sandbox-protected
-
Firefox-ESR (Extended Security Release bzw. Pale Moon) with special extensions in private mode), with
-
Tor (Tor-Browser) even anonymized within one more own sandbox without the origin IP (anonymized computer-identifying number out of the ipv4-address-namespace) and even
-
DNS-Traffic is kept anonymous by TorDNS as the remote-host-DNS, while the most frequent DNS-queries get resolved local within /etc/hosts and persistently pdnsd within the harddisc-cache (/var/lib/cache/pdnsd/pdnsd.cache).
-
With Firejail many browser are running firejail´s suid-sandbox, processed under user "surfuser" of the group "surfgroup" resp. "toruser" and "torgroup" by
-
https/SSL/TLS (TLS2.0, TLS3.0) not hackable end-to-end-encrypted net-connections
-
free from Man-In-The-Middle-Attacks etc. and therefore (through Firewall Linfw3) without ICMP-, UDP- and IGMP-traffic and other communications (communication protocols): iptraf for example always shows an empty second field below the field with the TCP-connections) and so on
-
quit upgrade and update-free past year 2026 ( nahezu )
-
all partitons including the root-partition and USB-memory-sticks, temporary directories and SWAP-filei are encrypted (FSE: Full System Encryption by LUKS, OpenPGP forr E-mail and single directories and files)
-
Because of common read/write/executalbe-access-rights and ACL, directories and files remain free from read, write and execution for all user (except root), especially for the surfuser except oneself as the active user:
paranoid security without too many restrictions for the user!
With this system, be welcomed live on the daily update-channel https://www.pro-linux.de from year 2010 up to year 2026 and longer!
Described "Universal-Linux" also includes emulators for other operating systems (beneath boot manager grub for the multi-boot):
-
MS Windows 3.1, 95, 98, SE, ME, NT 4.0, NT 3.5, XP, 2003, Vista, Windows 2008, Windows 7, alles sowohl i686 (32 Bit) als auch x86_64 (64 Bit): Emulator wine (hauptsächlich), qemu oder xen), Virtualisierung: KVM (Kernel-Modul kvm-amd, kvm-intel mit libvirt, qemu-kvm, libvirt-client, libvirt-daemonsystem, bridge-utils, Virt-Manager, von Red Hat entwickelten und von Microsoft signierten Gerätetreiber ( Virt-IO-Driver )), Virtualbox, Vmware ( Einzelheiten zur Virtualisierung siehe z.B. https://www.pcwelt.de/ratgeber/Virtualisierung_unter_Linux-9988750.html )
-
MS DOS (dosemu)
-
Apple Macintosh (basiliskII), PowerMAC (SheepShaver)
-
Cisco 7200 and 3600 and Freescale Coldfire 5206 Emulator (dynamips)
-
Amiga (uae, fs-uae, e-uae, uade)
-
Atari ST, Atari 8 Bit Computer (hatari)
-
Commodore VC 64 (vice, micro64), Amstrad CPC (caprice32),
-
ZX Spectrum (fbzx), MSX (fmsx, openmsx), NeoGeo (gngeo), Dragon32, Dragon64 und Tandy CoCo (xroar), Minitel (xtel), Nintendo Gameboy (zboy), TI89(Ti)/92(+)/V200 emulator (tiemu3)
-
Multi-System-Emulator (simh)
-
and many other computer operating systems.
Gooken internet search engine shows you on this website step by step (hook by hook), what has to be done for reaching this total IT-security for the computer!
You can enjoy hardened Linux booting from DVD, alternatively from USB-Stick:
"Tails Linux: The Anti-NSA-PC, 04.23.2014
Can NSA crack everything, even hardest encryption? Only a UNIX/Linux based System can achieve security, means one of the authors below. Edward Snowden knows more about this than other ones. In order to make communication really secure, he decided to install the Linux-Distribution Tails. CHIP shows the Anti-NSA-PC for free [...]. Fast and simple: Tails runs as hardened Debian Linux", http://www.chip.de/artikel/Tails-Linux-installieren-Der-Anti-NSA-PC_63845971.html
Edward Snowden also recommends a in his eyes secure Linux/UNIX-derivate on News&Links#Computer and News&Links#Alternatives and secure apps.
But if the well-known referencial Computer-system resp. "Universal-Linux" we are going to introduce should ever not be such secure as it ought to be, the setting of the ro-option standing for read-only for the root-partition in /etc/fstab resp. /boot/grub/menu.lst (grub1, analogous grub2) past all the installing and updating can create a shoot-steadfast Linux even on harddrives doing its best.
Darknet-Browser Tor is ready for Android: You can surf complete anonymously with your handy, CHIP, 27.05.2019
The Tor-Browser is rated as a symbol for anonymes surfing in the internet and the easiest way into the Darknet. Now a ready version of the browser was provided in the Google Play Store. We show you, howto surf with this browser by upon your Android smartphone over the Tor-network.
https://www.chip.de/news/Darknet-Browser-Tor-fuer-Android-fertig-
Am-Handy-komplett-anonym-surfen_148414180.html
Year 2016: Incredible high rubbish-hills of packages for not actual Linux-distributions are still provided by contributors like fr2.rpmfind.net and pbone.net. Most distribution versions can not be kept up-to-date, while the update-list from pro-linux.de is increasing day by day. Linux, comment from newsgroup alt.linux.suse, year 2003:
"I am so happy, that my linux run stable for the last 12 hours!".
More today:
Red Hat Enterprise Linux 7.1 receives extended security certifications, Pro-Linux, 14.12.2017
Without modification, Red Hat Enterprise Linux got certified for the "General-Purpose Operating System Protection Profile" (OSPP) 3.9. Now Red Hat Enterprise Linux can be used and applied in security-critical environments.
.
https://www.pro-linux.de/news/1/25437/red-hat-enterprise-linux-71-erhält-erweiterte-sicherheitszertifikation.html
Date: 30.03.2011, thanks, we got it: [espeak -v en "] Secure,  mouseclick-fast upon MS Windows 7 and Linux and all belonging Linux-games: (bohemian) 19 W power consumpting computer ASUS (mini) ITX-220 from year 2009/2010 with a socked, crasfree bios, onboard Intel-soundchip, onboard Atheros-LAN-Chip and -ROM and onboard INTEL graphics, AOC WLED-TFT less 18 Watt with more than one million working hours, all for about 200 €. Looking upon technical revisions and software-rpm-packet-changelogs one notices, the world gave its best: 2010 - (quit) everything has been made for computers - magic year of fast, ergonomic, powersaving hardware, year of Mandriva 2010, year of CentOS 6 ( DVD CentOS 6 (actual tenth-revision, with many updates and patches by Jonny Hughes, NY) for 4,95 € or for free out of the internet ) and the for the more than 50.000 next ten years (until year 2026) fixed and patched packet-versions of Fedora Project resp. the in a careful way resulting and ( Fedora Core (fc) - ) backported Enterprise Linux (el) resp. CentOS 6, where its IT-security raised up quit to maxium by concept with methods, configurations and updates we want to present here on this webside, so that computer-technique got solved (after a long, long time ...): error-free (total: since python-stablity-patch from year 2016), free from trojans, hacker, viruses, spyware, adware, everything. Day after day the amount of still missing software declined and you still have to keep the computer up to date sometimes by installing some updates. Up to that year, the paid prices for different Linux distributions can exceed even those of other operating systems. But now you won´t have any difficulties. Text to the illustration from the top, Build your final mouseclick-fast upon MS Windows 7 and Linux and all belonging Linux-games: (bohemian) 19 W power consumpting computer ASUS (mini) ITX-220 from year 2009/2010 with a socked, crasfree bios, onboard Intel-soundchip, onboard Atheros-LAN-Chip and -ROM and onboard INTEL graphics, AOC WLED-TFT less 18 Watt with more than one million working hours, all for about 200 €. Looking upon technical revisions and software-rpm-packet-changelogs one notices, the world gave its best: 2010 - (quit) everything has been made for computers - magic year of fast, ergonomic, powersaving hardware, year of Mandriva 2010, year of CentOS 6 ( DVD CentOS 6 (actual tenth-revision, with many updates and patches by Jonny Hughes, NY) for 4,95 € or for free out of the internet ) and the for the more than 50.000 next ten years (until year 2026) fixed and patched packet-versions of Fedora Project resp. the in a careful way resulting and ( Fedora Core (fc) - ) backported Enterprise Linux (el) resp. CentOS 6, where its IT-security raised up quit to maxium by concept with methods, configurations and updates we want to present here on this webside, so that computer-technique got solved (after a long, long time ...): error-free (total: since python-stablity-patch from year 2016), free from trojans, hacker, viruses, spyware, adware, everything. Day after day the amount of still missing software declined and you still have to keep the computer up to date sometimes by installing some updates. Up to that year, the paid prices for different Linux distributions can exceed even those of other operating systems. But now you won´t have any difficulties. Text to the illustration from the top, Build your final
 "UNIVERSAL COMPUTER with UNIVERSAL-LINUX"
"UNIVERSAL COMPUTER with UNIVERSAL-LINUX"
consisting of up to 100 DVD a 4,4 GB full of rpm- and deb-packages (Debian) and many Tarballs from anywhere ON THE DAILY UPDATE-PATCH-CHANNEL (fc, el6/sl6) http://www.pro-linux.de/sicherheit/1/1/1.html) and belonging more Packages from pkgs.org, fr2.rpmfind.net and pbone.net. All kind of Linux-games run fine too.
Similar to Scientific Linux, "CentOS" stands for "Community Enterprise Operating System". It is based to 100% upon the source code of Red Hat Enterprise Linux. The only difference is, that commercial support is missing. Typical CentOS-user are organizations and private people aiming for a stable Enterprise-operating-system without the need of commercial support. The stable versions of CentOS are supported with (RPM-) acutualizations for ten years.
CentOS is a Linux-Distribution from Red Hat with the same source code like Red Hat Enterprise Linux. Since January 2014 CentOS belongs to Red Hat as a costly free alternative to Red Hat Enterprise Linux for all those, that do not need commercial support for Red Hat Enterprise Linux. Even no one guarantees, CentOS in fact is almost compatible with Red Hat Enterprise Linux.
https://www.pro-linux.de/news/1/27054/centos-8-benötigt-noch-etwas-zeit.html
What we are going to describe in the following:
No hacker, no virusses, no trojans, no malware, no ad- and no spyware, no ransomware, no dangerous scripts, rare resp. no left traces in the net, ..., nothing of it, and no kernel up from 2.6.39 (if stable) and not much root owned processes, that can affect the computer system anymore: use
-
command dd for secure working with the partitionwise restores and backups started from an encrypted rescue partition, usb-memory-stick or DVD like Knoppix together with cryptsetup (LUKS) installed,
-
ipables-based firewall linfw3,
-
port scan detection (psad, psd),
-
intrusion detection sysems (IDS)
-
the local dns-cache dnsmasq
-
and adblocker like our listing importing konqueror-adblocker and free useragent-settings and other extensions for your browser together with
-
sandbox firejail (pclos),
-
configure /etc/fstab for the declaration of the partitions and file systems, in our case ext4 under security aspects,
-
configure /etc/passwd for the blocking shells,
-
set owner- and access-rights,
-
ACL (setfacl/getfacl),
-
use MAC (apparmor, tomoyo) and
-
chattr upon UNIX/Linux-filesystems and follow the
-
configurations and methods introduced here on this webside to make security really possible! Profit from
-
end-to-end-encrypting TLS/SSL used by browser like Konqueror, Firefox, Firefox ESR resp. Tor-Browser (Firefox ESR) and
-
pgp/gpg- and TLS-based e-mail-clients like Thunderbird and/or Kmail, claws-mail with claws-mail-plugins, ...
-
all this upon a Luks/dm-crypt and dracut full encrypted computer-system (FSE), going sure also with a read-only set (and by dracut LUKS-encrypted) root-partition.
HOWTO: Either you install the version of an actual (new) Linux-distribution after the expiration of the updates for your installed one, we recommend Debian Linux resp. Ubuntu, SuSE Linux, Fedora, the in a careful way from Fedora resulting and backported CentOS (resp. RedHat), Rosa and Openmandriva, PCWelt: Ubuntu and Mint, or you install the covering and approved (and many, many TOP-games on the base of OpenGL and SDL including) el6, mdv2010.0 resp. mdv2011, mga1 up to mga3 or any rpm-distribution of the last decades from fr2.rpmfind.net and care for its updates. For mdv2010.0 you think of updating with the secure running autumn- and spring- updatening version mdv2010.1 and mdv2010.2 to mdv2010.2 (65 GB, around 15 DVD).
 How does this work? It´s easy (or it sound so): All you need for the next time in principle is "any" Linux-distribution from DVD/CD, USB-memory-stick or per download out of the internet etc., one that is named by PRO-Linux (http://www.pro-linux.de/1/1/sicherheit.html) withiin the hugh update-listing of the last ten, twenty years. Install this distribution following the self activating installation instructions onto an installation media (we recommend an at least 120 GB Solid State Disk (SSD with an at least 65 GB sized main- resp. root-partition and at least 2 GB SWAP-partition)) and eventually more single programms resp. packages with the help of an as much expressive packagemanger as possible. We recommend Debian Linux or a ( Fedora Core - ) backported and long-update-support guaranteeing Linux-Distribution (like RedHat resp. CentOS and Scientific Linux el6 and el7). Regardless from the amount of software resp. packages, this Linux-Distribution can be considered as a gear to the big UNIX/Linux- and its emulation-world of even more, we recommend actual UNIX-/Linux-distributions, actual updates and all kind of software and games. Emulation means, that with the help of emulators (like Wine for MS Windows) and virtual machines like Xen and Qemu software running upon other operating systems can be used too. Notice, that it is possible to install all software on the installation media at once without risking too much. The important thing is, that it is possisble to upgrade the Standard-GNU-C-library (glibc) of this distribution, so that the kernel of the LONGTERM-series out of kernel-3 and -4 can be upgraded too.. How does this work? It´s easy (or it sound so): All you need for the next time in principle is "any" Linux-distribution from DVD/CD, USB-memory-stick or per download out of the internet etc., one that is named by PRO-Linux (http://www.pro-linux.de/1/1/sicherheit.html) withiin the hugh update-listing of the last ten, twenty years. Install this distribution following the self activating installation instructions onto an installation media (we recommend an at least 120 GB Solid State Disk (SSD with an at least 65 GB sized main- resp. root-partition and at least 2 GB SWAP-partition)) and eventually more single programms resp. packages with the help of an as much expressive packagemanger as possible. We recommend Debian Linux or a ( Fedora Core - ) backported and long-update-support guaranteeing Linux-Distribution (like RedHat resp. CentOS and Scientific Linux el6 and el7). Regardless from the amount of software resp. packages, this Linux-Distribution can be considered as a gear to the big UNIX/Linux- and its emulation-world of even more, we recommend actual UNIX-/Linux-distributions, actual updates and all kind of software and games. Emulation means, that with the help of emulators (like Wine for MS Windows) and virtual machines like Xen and Qemu software running upon other operating systems can be used too. Notice, that it is possible to install all software on the installation media at once without risking too much. The important thing is, that it is possisble to upgrade the Standard-GNU-C-library (glibc) of this distribution, so that the kernel of the LONGTERM-series out of kernel-3 and -4 can be upgraded too..
A securing 1:1 partioned media should not miss! Perform all security methods introduced in future point by point as soon as possible, as the installation is endangered extremely (by hacker and so on) with the very first built-up connection to the net!
quot;There is not much diffrence between the Linux-Distributions / Der Unterschied zwischen den Linux-Distributionen ist nicht sehr groß mit Ausnahme der Basisinstallation und der Paketverwaltung. Die meisten Distributionen beinhalten zum Großteil die gleichen Anwendungen. Der Hauptunterschied besteht in den Versionen dieser Programme, die mit der stabilen Veröffentlichung der Distribution ausgeliefert werden. Zum Beispiel sind der Kernel, Bind, Apache, OpenSSH, Xorg, gcc, zlib, etc. in allen Linux-Distributionen vorhanden."
https://www.debian.org/doc/manuals/securing-debian-howto/ch12.de.html
 Avoid Legacy Communication Services Avoid Legacy Communication Services
A large number of legacy Unix programs do not provide essential security during data transmission. These include FTP, Telnet, rlogin, and rsh. No matter whether you´re securing your Linux server or personal system, stop using these services for good.
You can use other alternatives for this type of data transfer tasks. For example, services like OpenSSH, SFTP, or FTPS makes sure that data transmission happens over a secure channel. Some of them employ SSL or TLS encryptions to harden your data communication. You may use the below commands to remove legacy services like NIS, telnet, and rsh from your system.
# yum erase xinetd ypserv tftp-server telnet-server rsh-server
# apt-get --purge remove xinetd nis yp-tools tftpd atftpd tftpd-hpa telnetd rsh-server rsh-redone-server
Use the first command for RPM-based distributions like RHEL and Centos or any system that uses the yum package manager. The second command works on Debian/Ubuntu-based systems.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Enable SELinux Enable SELinux
SELinux or Security Enhanced Linux is a security mechanism that implements various methods for access control at the kernel level. SELinux is developed by Red Hat and has been added to many modern Linux distributions. You can think of it as a set of kernel modifications and user-space tools. You can check out whether SELinux is enabled in your system or not by using the below command.
# getenforce
If it returns enforcing that means your system is protected by SELinux. If the result says permissive that means your system has SELinux but it´s not enforced. It will return disabled for systems where SELinux is completely disabled. You can enforce SELinux by using the below command.
# setenforce 1
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Lock Login Attempts after Failure Lock Login Attempts after Failure
Admins should make sure that users can´t log into their server after a certain number of failed attempts. This increases the overall security of the system by mitigating password attacks. You can use the Linux faillog command to see the failed login attempts.
# faillog
# faillog -m 3
# faillog -l 1800
The first command will display the failed login attempts for users from the /var/log/faillog database. The second command sets the maximum number of allowed failed login attempts to 3. The third one sets a lock of 1800 seconds or 30 minutes after the allowed number of failed login attempts.
# faillog -r -u <username>,
Use this command to unlock a user once they´re prohibited from login. The max number of failed login attempts for the root user should be high or else brute force attacks may leave you locked.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Check for Empty Passwords Check for Empty Passwords
Users are the weakest link in a system´s overall security. Admins need to make sure that no user on the system has empty passphrases. This is a mandatory step for proper Linux hardening. Use the following awk command in Linux to verify this.
# awk -F: ´($2 == "") {print}´ /etc/shadow
It will display if there´re any user accounts that have an empty password in your server. To increase Linux server hardening, lock any user that uses empty passphrases. You can use the below command to do this from your Linux terminal.
# passwd -l <username>
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Validate the UID of Non-Root Users Validate the UID of Non-Root Users
A UID or User-ID is a non-negative number assigned to the users of a system by the kernel. The UID 0 is the UID of the superuser or root. It is important to make sure that no user other than root has this UID value. Else, they can masquerade the whole system as root.
# awk -F: ´($3 == "0") {print}´ /etc/passwd
You can find out which users have this UID value by running this awk program. The output should contain only a single entry, which corresponds to root.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Remove the X Window Systems (x11) Remove the X Window Systems (x11)
The X Window Systems or x11 is the de-facto graphical interface for Linux systems. If you´re using Linux for powering your server instead of your personal system, you can delete this entirely. It will help to increase your server security by removing a lot of unnecessary packages.
# yum groupremove "X Window System"
This yum command will delete x11 from RHEL or Centos systems. If you´re using Debian/Ubuntu instead, use the following command.
# apt-get remove xserver-xorg-core
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Disable the X Window Systems (x11) Disable the X Window Systems (x11)
If you don´t want to delete x11 permanently, you may disable this service instead. This way, your system will boot into text mode instead of the GUI. Edit the /etc/default/grub file using your favorite Linux text editor.
# nano /etc/default/grub
Find the below line -
GRUB_CMDLINE_LINUX_DEFAULT="quiet splash"
Now, change it to -
GRUB_CMDLINE_LINUX_DEFAULT="text"
Finally, update the GRUB file by using -
# update-grub
The last step is to tell systemd to not load the GUI system. You can do this by running the below commands.
# systemctl enable multi-user.target --force
# systemctl set-default multi-user.target
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Investigate IP Addresses Investigate IP Addresses
If you find any suspicious IP in your network, you can investigate it using standard Linux commands. The below command uses netstat and awk to display a summary of running protocols.
# netstat -nat | awk ´{print $6}´ | sort | uniq -c | sort -n
Use the below command to find more information about a specific IP.
# netstat -nat |grep <IP_ADDR>, | awk ´{print $6}´ | sort | uniq -c | sort -n
To see all unique IP addresses, use the following command.
# netstat -nat | awk ´{ print $5}´ | cut -d: -f1 | sed -e ´/^$/d´ | uniq
Feed the above command to wc for getting the number total of unique IP addresses.
# netstat -nat | awk ´{ print $5}´ | cut -d: -f1 | sed -e ´/^$/d´ | uniq | wc -l
Visit our guide on various Linux network commands if you want to dive deeper into network security.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Disable SUID and SGID Permission Disable SUID and SGID Permission
SUID and SGID are special types of file permission in the Linux file system. Having the SUID permission allows users other to run executable files like they are the owner of those files. Likewise, the SGID permission gives directory rights similar to the owner but also gives ownership of all child files in a directory.
These are bad since you don´t want any users other than you to have those permissions on a secure server. You should find any file that has SUID and SGID enabled and disable those. The following commands will respectively list all files that have SUID and SGID permission enabled.
# find / -perm /4000
# find / -perm /2000
Investigate these files upon /etc/permissions* (permissions, OpenSuSE) properly and see if these permissions are mandatory or not. If not, remove SUID/SGID privileges. The below commands will remove SUID/SGID respectively.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Enable Disk Quotas Enable Disk Quotas
Disk Quotas are simply limits set by the system administrator which restrict usage of the Linux filesystem for other users. If you are hardening your Linux security, implementing disk quotas is mandatory for your server.
# nano /etc/fstab
LABEL=/home /home ext2 defaults,usrquota,grpquota 1 2
Add the above line to /etc/fstab for enabling disk quota for the /home filesystem. If you have already a line /home, modify that accordingly.
# quotacheck -avug
This command will display all quota information and create the files aquota.user and aquota.group in /home.
# edquota <user>,
This command will open the quota settings of <user>, in an editor where you can assign the quota limits. You can set both soft and hard limits for the disk quota size as well as the number of inodes. Use the below command to view a report on the disk quota usage.
# repquota /home
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Maintain Word-Writable Files Maintain Word-Writable Files
Word-writable files are fils that anyone can write to. This can be very dangerous since it effectively allows users to run executables. Plus, your Linux hardening is not foolproof unless you´ve set the appropriate sticky bits. A sticky bit is a single bit that, when set, prevents users from deleting someone else´s directories.
Thus, if you´ve got world-writable files that have sticky bits set, anyone can delete these files, even if they´re not owned by them. This is another serious issue and will often cause havoc on server security. Luckily, you can find all such files by using the below command.
# find /path/to/dir -xdev -type d \( -perm -0002 -a ! -perm -1000 \) -print
Replace the path argument with directories that may contain such files. You can also start from the root ‘/´ of your filesystem but it´ll take a long time to execute. Once listed, investigate the files thoroughly and change their permissions as required.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Maintain Noowner Files Maintain Noowner Files
Noowner files are files that do not have any owner or group associated with them. These can pose a number of unwanted security threats. So, admins should take the necessary measures required to identify these. They can either assign them to the appropriate users or may delete them entirely.
You can use the following find command to list the noowner files present in a directory. Check out this guide to learn more about the find command in Linux.
# find /path/to/dir -xdev -type d \( -perm -0002 -a ! -perm -1000 \) -print
Inspect the results thoroughly to make sure there aren´t any unwanted noowner files in your server.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Install Logwatch / Logcheck Install Logwatch / Logcheck
Log analyzer
 Secure Web Server Secure Web Server
Linux servers are widely used for powering web applications. If you´re using your server for this purpose, you need to harden your server components appropriately. Some of these the PHP runtime, Apache HTTP server, and the Nginx reverse proxy server. Secure your Apache server by adding the below lines in the configuration file.
# nano /etc/httpd/conf/httpd.conf
ServerTokens Prod
ServerSignature Off
TraceEnable Off
Options all -Indexes
Header always unset X-Powered-By
# systemctl restart httpd.service
We´ve prepared a standalone guide on the Nginx server a while ago. Follow the suggestions in that guide to secure your Nginx server. Head over to this documentation for learning the best PHP security practices.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Configure TCP Wrappers Configure TCP Wrappers
TCP wrappers are a host-based network filtering system that allows or denies access to your host services based on pre-set policies. However, for it to work, your host service must be compiled against the libwrap.a library. Some common TCP wrapperd Unix daemons include sshd, vsftpd, and xinetd.
# ldd /sbin/sshd | grep libwrap
This command will notify if a service is supported by TCP wrappers or not. The TCP wrappers system enforces access control using two configuration files, the /etc/hosts.allow and /etc/hosts.deny. For example, add the following lines to /etc/hosts.allow for allowing all incoming requests to the ssh daemon.
# nano /etc/hosts.allow
sshd : ALL
Add the following to /etc/hosts.deny for rejecting all incoming requests to the FTP daemon.
# nano /etc/hosts.deny
vsftpd : ALL
To see more information about the configuration options, consult the tcpd man page, or visit this documentation from FreeBSD.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Maintain Cron Access Maintain Cron Access
Linux provides robust automation support by means of cron jobs. In short, you can specify routine tasks using the cron scheduler. Visit our earlier guide on cron and crontab to learn how cron works. Nevertheless, admins must make sure that ordinary users are unable to access or put entries in the crontab. Simply put their usernames in the /etc/cron.deny file to do this.
# echo ALL >,>,/etc/cron.deny
This command will disable cron for all users in your server except root. To allow access for a specific user, add his username.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Disable Ctrl+Alt+Delete Disable Ctrl+Alt+Delete
The Ctrl+Alt+Delete key combinations allow users to force reboot many Linux distributions. This can be particularly problematic if you´re managing a secure server. Admins should disable this hotkey in order to maintain proper Linux hardening. You can run the following command to disable this in systemd-based systems.
# systemctl mask ctrl-alt-del.target
If you´re on legacy systems that use init V instead of systemd, edit the /etc/inittab file and comment out the following line by appending a hash before it.
# nano /etc/inittab
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Restrict Core Dumps Restrict Core Dumps
Core dumps are memory snapshots (core-files) that contain crash information of executables. These are created when binaries stop working or crash in simple terms. They contain too much sensitive information about the host system and may threaten your Linux security if fallen into the wrong hands. Thus, it is always a good idea to restrict core dumps on production servers.
# echo ´hard core 0´ >,>, /etc/security/limits.conf
# echo ´fs.suid_dumpable = 0´ >,>, /etc/sysctl.conf
# sysctl -p
# echo ´ulimit -S -c 0 >, /dev/null 2>,&1´ >,>, /etc/profile
Run the above commands to restrict cor dumps on your server and increase Linux hardening.
https://www.ubuntupit.com/best-linux-hardening-security-tips-a-comprehensive-checklist/
 Right up from the very beginning - installing an OS like UNIX/Linux Right up from the very beginning - installing an OS like UNIX/Linux
... most already through installation media:
format -" partitioning -> format -> encryption (full system encryption, FSE) -> format -> installation (from extern media) -> configuration -> defragmentation (not essential for many UNIX/Linux file systems) -> encryption (full system encryption, FSE) -> (backup with dd and) actualization -> configuration -> (backup with dd and) actualization ( ... notice total time needed: ? )
Alternatively: Some nice "guy" or so does many things for you by mirroring almost completed system from his onto your own media (SSD (sdx), harddisc (S-ATA: sdx, IDE: hdx, CD-/DVD, USB-memory stick, ...). This can save plenty of time (look out for the right processor architecture (x86_64, i686, ...) and set /etc/X11/xorg.conf for the next time to vesa or fb)! Do this mirroring with a command like: "dd if=/dev/sda of=/dev/sdb"
Use sdd instead of dd to see a progress bar.
Used editor in the following: nano
First this webside introduces some configurations, followed by actualization, partitioning, encryption during the introduction of basic shell-commands.
 Mounting partitions the right way Mounting partitions the right way
When mounting an Ext file system (ext2, ext3 or ext4), there are several additional options you can apply to the mount call or to /etc/fstab. For instance, this is my fstab entry for the /tmp partition:
/dev/hda7 /tmp ext2 defaults,nosuid,noexec,nodev 0 2
You see the difference in the options sections. The option nosuid ignores the setuid and setgid bits completely, while noexec forbids execution of any program on that mount point, and nodev ignores device files. This sounds great, but it:
only applies to ext2 or ext3 file systems
can be circumvented easily
The noexec option prevents binaries from being executed directly, but was easily circumvented in earlier versions of the kernel:
alex@joker:/tmp# mount | grep tmp
/dev/hda7 on /tmp type ext2 (rw,noexec,nosuid,nodev)
alex@joker:/tmp# ./date
bash: ./date: Permission denied
alex@joker:/tmp# /lib/ld-linux.so.2 ./date
Sun Dec 3 17:49:23 CET 2000
Newer versions of the kernel do however handle the noexec flag properly:
angrist:/tmp# mount | grep /tmp
/dev/hda3 on /tmp type ext3 (rw,noexec,nosuid,nodev)
angrist:/tmp# ./date
bash: ./tmp: Permission denied
angrist:/tmp# /lib/ld-linux.so.2 ./date
./date: error while loading shared libraries: ./date: failed to map segment
from shared object: Operation not permitted
However, many script kiddies have exploits which try to create and execute files in /tmp. If they do not have a clue, they will fall into this pit. In other words, a user cannot be tricked into executing a trojanized binary in /tmp e.g. when /tmp is accidentally added into the local PATH.
Also be forewarned, some script might depend on /tmp being executable. Most notably, Debconf has (had?) some issues regarding this, for more information see Bug 116448.
 Decisive advantage of option noexec, especially for the home partition: Potential virus host cells (executable files, that may be virus infected hosts) remain absolutely ineffective! Viruses can not infect files on the home partition and temporary partitions, if the option noexec is set (while the root-partition got already resistant against viruses in usermode by normal access-rights below or equal chmod <=755 for owners like root !) Decisive advantage of option noexec, especially for the home partition: Potential virus host cells (executable files, that may be virus infected hosts) remain absolutely ineffective! Viruses can not infect files on the home partition and temporary partitions, if the option noexec is set (while the root-partition got already resistant against viruses in usermode by normal access-rights below or equal chmod <=755 for owners like root !)
The following is a more thorough example. A note, though: /var could be set noexec, but some software [21] keeps its programs under in /var. The same applies to the nosuid option.
/dev/sda6 /usr ext3 defaults,ro,nodev 0 2
/dev/sda12 /usr/share ext3 defaults,ro,nodev,nosuid 0 2
/dev/sda7 /var ext3 defaults,nodev,usrquota,grpquota 0 2
/dev/sda8 /tmp ext3 defaults,nodev,nosuid,noexec,usrquota,grpquota 0 2
/dev/sda9 /var/tmp ext3 defaults,nodev,nosuid,noexec,usrquota,grpquota 0 2
/dev/sda10 /var/log ext3 defaults,nodev,nosuid,noexec 0 2
/dev/sda11 /var/account ext3 defaults,nodev,nosuid,noexec 0 2
/dev/sda13 /home ext3 rw,nosuid,nodev,exec,auto,nouser,async,usrquota,grpquota 0 2
/dev/fd0 /mnt/fd0 ext3 defaults,users,nodev,nosuid,noexec 0 0
/dev/fd0 /mnt/floppy vfat defaults,users,nodev,nosuid,noexec 0 0
/dev/hda /mnt/cdrom iso9660 ro,users,nodev,nosuid,noexec 0 0
https://www.debian.org/doc/manuals/securing-debian-howto/ch4.en.html
 Postfix - shorten information Postfix - shorten information
/etc/postifx/main.cf
smtpd_banner = $myhostname ESMTP $mail_name (FreeBSD/GNU)
... that means without version number and eventually with a new operating system name.
https://www.debian.org/doc/manuals/securing-debian-howto/ch12.de.html
 dbus (messagebus): Secure up single service-files dbus (messagebus): Secure up single service-files
dbus of many versions does make mistakes from time to time, by removing single service-files out of /usr/share/dbus-1/services and /usr/share/dbus-1/system-services from time to time without being allowed.
Therefore all service-files should be backuped in any backup-directory.
Exchange "Exec=kded" into "Exec=kded4"
nano /usr/share/dbus-1/services/org.kde.kded.service
[D-BUS Service]
Name=org.kde.kded
Exec=/usr/bin/kded4
 Just update by the kernel-binary (kernel-...rpm) or configure, patch and compile the kernel-source (kernel-...rpm.src) Just update by the kernel-binary (kernel-...rpm) or configure, patch and compile the kernel-source (kernel-...rpm.src)
We assume, that any rpm-based Linux-Distribution is already installed on a storage media like harddisc. Our section for updates refers to RedHat, Almalinux, CentOS oder Scientific Linux, Fedora Core, PCLinuxOS, ROSA, Mageia oder Mandriva.
How to configure, patch and compile kernel-sources: Download and install all binary rpm required for the kernel. Then download, install or enpack the kernel-source-rpm into /usr/src either by "tar -xvjf kernel-source-package", rpm on the kernel-source-rpm or file-roller. A new directory named "linux-kernelversion-xxx" or "kernel-source-xxx" is created within /usr/src.
Link this new directory to a linking file named linux: "ln -sf linux-xxx linux" resp. "ln -sf kernel-source-xxx linux".
Change into this directory linux resp. linux-xxx resp. kernel-source-xxxx and call "menu oldconfig".. A file .config is created to configure the kernel.
Type "menu xconfig" or "menu gconfig" or "make menuconfig" and configure the kernel-drivers and so on needed (CC), needed as modules (CC MM) and such to resign from.
For FSE (full system encryption) by dracut, two options have to be enabled, what is already done in kernel (pclos, rosa2016.1, el8, el7) and kernel-desktop (mdv2011) but not kernel (el6):
Generally, the security level of software is not only presented by stability, but also by the freeness of errors and warnings during the compilation of their source codes listed by the compiler. Kernel-2.6.32 (el6) consists of many of them and some of them are caused by kmem.h, while the quit restless error-free (only a few small patches 2012-2016 inclusive dirty-cow are known!) kernel-2.6.39.4-5.1 (mdv2011) runs error-free on our system without any warnings during the compilation time of around four hours! This is the best sign for good and secure running code. The only thing remaining is to patch with the dirty-cow-patch in mm.h and memory.c.
http://repository.timesys.com/buildsources/k/kernel/kernel-2.6.39/
Kernel: We recommend kernel 4 (we chose 5.4.110 (pclos) past 4.20.13 (pclos) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: Version 008)) and glibc (el8, pclos)), but do describe 2.6.39.4-5 now (also running on some playstations and so on) patched up to date by sources (containing the dirty-cow-patch in main), consisting of less compilation warning and no errors than 2.6.32 (el6). This mdv-kernel is described from patch-sources like http://repository.timesys.com/buildsources/k/kernel/kernel-2.6.39/, kernel itself from http://fr2.rpmfind.net/linux/kernel/v2.6/linux-2.6.39.4.tar.xz: kernel-desktop (mdv2011): glibc (pclos, mga6), module-init-tools (we recommend mdv2011, but you can also use el6, up to 3.16; append ".conf" to all files in /etc/modules.d; module-init-tools (mdv2011) never makes trouble with it), coreutils (el6), initscripts (mdv2011, pclos and el6 as depecited below), util-linux (mdv2011 or el6 except /bin/mount, /bin/mount and /lib64/libmount* you have to delete after enpacking the rpm (not installing!) and copying its include), kernel-firmware (pclos, slack14.2 with more than 250 MB unpacked, mga6, el6), if you want plus kernel-firmware (OpenSuSE 42.1, 32 MB) plus kernel-firmware (OpenSuSE 13.2) plus linux-firmware (fc27, 35 MB) plus kernel-firmware-extra (pclos, rosa2014.1), kernel-headers (el6), kernel-doc (el6), ksymoops (OpenSuSE 12.2, mdv2011), coreutils (el6), coreutils-libs (el6), binutils (fc25, el6), nss (el7, el6, fc30), nss-softokn (el7, el6, fc30), nss-sysinit (el7, el6, fc30) und nss-softokn-freebl (el7, el6, fc30), nss-util (el7, el6, fc30), nss-tools (el7, el6, fc30) .
glibc (el8: 2.28, pclos: the actual 2.31, mga6: 2.22, fc, for printers with 32-bit driver only like Brother install glibc (2.22, el6) too and relink and delete adequately in /lib),
In order to avoid error-messages of glibc (el8) during system-boot, just remove the line LC_TIME=de_DE.UTF-8 in /etc/sysconfig/i18n ! Eventually install locales (pclos, mga7, mga6), locales-en, locales-de, ... too.
All patches for 2.6.39.4-5.1 until now are available in the internet from http://repository.timesys.com/buildsources/k/kernel/kernel-2.6.39/.
compiler-gcc5, add-timesys-bootlogo, dirty-cow, lantronix-ts1, no-setlocalversion, no-unused-but-set-variable, revert-nfsroot, timeconst.pl-eliminate-perl-warning, ltrx-image-rom and yaffs2.
Patch: patch (el6, fc27, mdv2010.1) has to be installed. Then type "patch -p1 < ../patchname.patch "
But at first do the following:
Actual Kernel: how to install a patched kernel-source: A lot of freed partition (memory) is required, maybe plenty of Gigabyte. Download and install all binary rpm required for the kernel. Then download and enpack the kernel-source-rpm into /usr/src either by "tar -xvjf kernel-source-package" or file-roller.
Two possibilites:
1) building a kernel-rpm out of the sources after applying the patches: Configure the spec-file of the installed source-rpm by adding or commenting in and out the patches to build a new binary kernel-rpm to install or update: https://www.howtoforge.de/anleitung/wie-man-einen-kernel-kompiliert-auf-fedora/. For CentOS and mdv depending on the package manager use command "rpm -ba" instead of "rpmbuild -ba" kernel-xxx.spec to create the binary..
2) Configure the sources and compile them:
A new directory named "linux-kernelversion" or "kernel-source-kernelversion" is created within /usr/src.
Link this new directory to a linking file named linux: "ln -sf linux-kernelversion linux" resp. "ln -sf kernel-source-kernelversion linux".
Change into this directory linux resp. linux-kernelversion resp. kernel-source-xxxx and call "menu oldconfig". A file .config is created to configure the kernel. Copy .config to include/config/auto.conf
If you do not know, what to enable or not, choose MM
(M) or (CC) to load as a module wherever possible,
(A) or (CC MM) auto-load the module or
(-): resign from the module.
Example (module extraction of kernel-2.6.39-40.src.rpm)
General Preparation of Linux, kernel-2.6.39-40.src.rpm
In order to take a firewall in use, kernel support for iptables and modules should be enabled.
Open a konsole and enter one of the statements
make menuconfig for the Dialog-GUI,
male xconfig for tk-GUI or
make gconfig with GTK or
make config
Choose kernel options within
Networking options --->
[*] Network packet filtering (replaces ipchains)
IP: Netfilter Configuration --->
.
(M) Userspace queueing via NETLINK (EXPERIMENTAL)
(M) IP tables support (required for filtering/masq/NAT)
(M) limit match support
(M) MAC address match support
(M) netfilter MARK match support
(M) Multiple port match support
(M) TOS match support
(M) Connection state match support
(M) Unclean match support (EXPERIMENTAL)
(M) Owner match support (EXPERIMENTAL)
(M) Packet filtering
(M) REJECT target support
(M) MIRROR target support (EXPERIMENTAL)
.
(M) Packet mangling
(M) TOS target support
(M) MARK target support
(M) LOG target support
(M) ipchains (2.2-style) support
(M) ipfwadm (2.0-style) support
think of other options (modules), store this configuration.
Before iptables can be used, the kernel module netfilter for the support of iptables has to be loaded e.g. by the statement modprobe:
# modprobe ip_tables
kernel-firmware (binary blobs within /lib/firmware, rpm kernel-firmware (around 250 MB) and/or kernel-firmware-extra ):
For kernels before 4.18:
KERNEL Enable support for Linux firmware
Device Drivers --->
Generic Driver Options --->
-*- Userspace firmware loading support
[*] Include in-kernel firmware blobs in kernel binary
(/lib/firmware) Firmware blobs root directory
For kernels beginning with 4.18:
KERNEL Enable support for Linux firmware
Device Drivers --->
Generic Driver Options --->
Firmware loader --->
-*- Firmware loading facility
() Build named firmware blobs into the kernel binary
(/lib/firmware) Firmware blobs root directory
Type "make dep && make clean && make mrproper" .
Type "menu xconfig" or "menu gconfig" or "make menuconfig" and configure the kernel-drivers and so on needed (CC), needed as modules (CC MM) and such to resign from, or for a pregiven configuration type "make oldconfig".
For FSE (full system encryption) by dracut, two options have to be enabled, what is already done in kernel-desktop (mdv2011) but not kernel (el6):
within the first item "General Setup"enable "Initial-RAM-filesystem and RAM-disk-support"and in "general drivers" enable the option "Maintain a devtmpfs at /dev/ with subitem "automount devtmpfs at /dev, after the kernel mounted the rootfs".
If you do not know, what to enable or not, choose MM to load as a module wherever possible.
Save the new .config.
Set the Kernel-Version at the top of the makefile.
Three possibilites, after the patching of the source-code like the dirty-cow-patch:
patch -p1 < ../any_patch.patch
apply all other patches in this way
make -i rpm (to create the binary kernel-rpm package, what endures on our system for around four hours)
make all # or
make dep (dependency properties to establish the relationship)
make clean (to remove the old data)
make bzImage (to create its core vmlinuz for /boot only after renaming the created file bzImage: time needed: around 30 minutes) or
make bzImage &,& make modules && make modules_install for the installation of the kernel-modules too.
Copy the bzImage to /boot, rename it to vmlinuz-kernelversion.
Use mkinitrd resp. in the case of FSE (Full Disk Encryption resp. encrypted root-partition) dracut to create the initrd resp. initramfs within directory /boot. If dracut does not work anymore ex. as a cause of updates, rename the new-kernel-version to the old-kernel-version in Makefile and make bzImage once again.
If you use grub as the bootloader and not grub2 and the configufile is still not configured for the new kernel, do this by editing /boot/grub/menu.lst and exchanging the vmlinuz-kernel-versions. If a new initramfs or initrd is created, enter them in the line for initrd.
done.
 Installation guide and for tuning Linux secure: https://wiki.kairaven.de/open/os/linux/tuxsectune and https://wiki.centos.org/HowTos/OS_Protection ( in our example related to mdv2010.2 or CentOS 6 el6 with many patches/updates by Jonny Hughes, NY ). Be careful, for example with the exchange of the password-encryption from md5 to sha256 or sha512 and the /etc/system-auth. Make backup or copies! Installation guide and for tuning Linux secure: https://wiki.kairaven.de/open/os/linux/tuxsectune and https://wiki.centos.org/HowTos/OS_Protection ( in our example related to mdv2010.2 or CentOS 6 el6 with many patches/updates by Jonny Hughes, NY ). Be careful, for example with the exchange of the password-encryption from md5 to sha256 or sha512 and the /etc/system-auth. Make backup or copies!
Through "about:config" many URL can be removed out of the listing after typing in "http".
 Using Compile-time-Hardening-Options Using Compile-time-Hardening-Options
Several compile-time options (detailed below) can be used to help harden a resulting binary against memory corruption attacks or provide additional warning messages during compiles. Using "dpkg-buildflags" is the recommended way to incorporate the build flags in Debian.
See ReleaseGoals/SecurityHardeningBuildFlags for additional information, https://wiki.debian.org/ReleaseGoals/SecurityHardeningBuildFlags.
For a step-by-step guide, see the HardeningWalkthrough, https://wiki.debian.org/HardeningWalkthrough.
Source: https://wiki.debian.org/Hardening
Fedora/CentOS etc: https://fedoraproject.org/wiki/Changes/Harden_All_Packages
 Listing: Linux-Security-Updates up from year 2000, PRO-LINUX.de Listing: Linux-Security-Updates up from year 2000, PRO-LINUX.de
... of the most important distributions with naming the closed error, bug resp. exploit
https://www.pro-linux.de/sicherheit/1/1/1.html
 Recent LWN.net security pages Recent LWN.net security pages
Here are the most recent LWN.net security pages, with a comprehensive roundup of a week´s worth security-related information.
Date Contents
Apr 12, 2017 Network security in the microservice environment; Two Project Zero reports; ..
.
Apr 05, 2017 ARM pointer authentication; Quotes; Exploiting Broadcom WiFi; ...
Mar 29, 2017 refcount_t meets the network stack; Quotes; ...
Mar 22, 2017 Inline encryption support for block devices; Shim review; ..
.
Mar 15, 2017 A kernel TEE party; Quotes; Struts 2 vulnerability; ...
Mar 08, 2017 A new process for CVE assignment; Smart TV bugging quotes; Threat modeling ...
Mar 01, 2017 The case of the prematurely freed SKB; SHA-1 collision and fallout; ...
Feb 22, 2017 The case against password hashers; New vulnerabilities in dropbear, kernel, nagios-core, qemu, ...
Feb 15, 2017 A look at password managers; New vulnerabilities in kernel, libevent, mysql, php, ...
Feb 08, 2017 Reliably generating good passwords; New vulnerabilities in epiphany, graphicsmagick, gstreamer (and plugins), spice, ...
Feb 01, 2017 The Internet of scary things; New vulnerabilities in ansible, chromium, kernel, mozilla, ...
Jan 25, 2017 Security training for everyone; New vulnerabilities in fedmsg, firejail, java, systemd, ...
Jan 18, 2017 Ansible and CVE-2016-9587; New vulnerabilities in bind, docker, qemu, webkit2gtk, ...
Jan 11, 2017 SipHash in the kernel; New vulnerabilities in kernel, kopete, syncthing, webkit2gtk, ...
Jan 04, 2017 Fuzzing open source; New vulnerabilities in bash, httpd, kernel, openssh, ...
Dec 22, 2016 OWASP ModSecurity Core Rule Set 3.0; New vulnerabilities in apport, kernel, libupnp, samba, ...
Dec 14, 2016 ModSecurity for web-application firewalls; New vulnerabilities in jasper, kernel, mozilla, roundcube, ...
Dec 07, 2016 Locking down module parameters; New vulnerabilities in chromium, firefox, kernel, xen, ...
Nov 30, 2016 Django debates user tracking; New vulnerabilities in drupal, firefox, kernel, ntp, ...
Nov 16, 2016 Reference-count protection in the kernel; New vulnerabilities in chromium, firefox, kernel, sudo, ...
https://lwn.net/Security/
 Setting /usr read-only for the separate usr-partition Setting /usr read-only for the separate usr-partition
If you set /usr read-only (in /etc/fstab), you will not be able to install new packages on your Debian GNU/Linux system. You will have to first remount it read-write, install the packages and then remount it read-only. apt can be configured to run commands before and after installing packages, so you might want to configure it properly.
To do this modify /etc/apt/apt.conf and add:
DPkg
{
Pre-Invoke { "mount /usr -o remount,rw" };
Post-Invoke { "mount /usr -o remount,ro" };
};
Note that the Post-Invoke may fail with a "/usr busy" error message. This happens mainly when you are using files during the update that got updated. You can find these programs by running
# lsof +L1
Stop or restart these programs and run the Post-Invoke manually. Beware! This means you´ll likely need to restart your X session (if you´re running one) every time you do a major upgrade of your system. You might want to reconsider whether a read-only /usr is suitable for your system ( and please notice, that this might not be recommended, if there is an encrypted root-partition), see also this discussion on debian-devel about read-only /usr.
We are going to encrypt even more the complete system (FSE) by reliable LUKS, including the complete root- and home-partition (and USB-media) to set partitions unwriteable to read-only. Notice, that this does not exclude the same for a separate usr-partition.
 /etc/pam.d/system-auth ( tested just on our platform and system ): /etc/pam.d/system-auth ( tested just on our platform and system ):
#%PAM-1.0
auth required pam_env.so
auth sufficient pam_unix.so try_first_pass likeauth
auth required pam_deny.so
auth requisite pam_succeed_if.so uid >= 500 quiet
auth required pam_tally2.so deny=3 onerr=fail unlock_time=60
account sufficient pam_tcb.so shadow
account required pam_deny.so
account sufficient pam_succeed_if.so uid < 500 quiet
account required pam_tally2.so per_user
password required pam_cracklib.so try_first_pass retry=3 minlen=6 dcredit=1 ucredit=0
password sufficient pam_unix.so try_first_pass use_authtok sha512 shadow remember=2
password required pam_deny.so
session optional pam_keyinit.so revoke
session required pam_limits.so
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_unix.so
More about pam-modules:
http://www.linuxdevcenter.com/pub/a/linux/2001/09/27/pamintro.html?page=2
https://linux.die.net/man/5/pam.d
 One more things with PAM: One more things with PAM:
Use encryption other than DES for your passwords (making them harder to brute-force decode).
Set resource limits on all your users so they can´t perform denial-of-service attacks (number of processes, amount of memory, etc).
Enable shadow passwords (see below) on the fly.
Allow specific users to login only at specific times from specific places.
Within a few hours of installing and configuring your system, you can prevent many attacks before they even occur. For example, use PAM to disable the system-wide usage of .rhosts files in user´s home directories by adding these lines to /etc/pam.d/rlogin:
#
# Disable rsh / rlogin / rexec for users
#
login auth required pam_rhosts_auth.so no_rhosts
Quelle: http://www.tldp.org/HOWTO/Security-HOWTO/password-security.html#AEN698
 Account locking Account locking
While having strong passwords in place for user accounts can help thwart brute force attacks as mentioned previously in point 18 - Enforce strong passwords, this is only one way of slowing down this type of attack. A good indication of brute force attack is a user account that has failed to log in successfully multiple times within a short period of time, these sorts of actions should be blocked and reported. We can block these attacks by automatically locking out the account, either at the directory if in use or locally.
The pam_tally2.so PAM module can be used to lock out local accounts after a set number of failures. To get this working I have added the below line to the /etc/pam.d/password-auth file.
auth required pam_tally2.so file=/var/log/tallylog deny=3 even_deny_root unlock_time=1200
This will log all failures to the /var/log/tallylog file and lock out an account after 3 consecutive failures. By default it will not deny the root account however we can also lock out root by specifying even_deny_root (though this may not be required if you have disabled root access as per point 3 - Disable remote root access and point 4 - Disable root console access). The unlock time is the amount of seconds after a failed login attempt that an account will automatically unlock and become available again.
Failed logins can be viewed as below, to view all failures simply remove the --user flag.
[[email protected] ~]# pam_tally2 --user=bob
Login Failures Latest failure From
bob 4 08/21/15 19:38:23 localhost
The failure count can be manually reset by appending -reset onto this command.
pam_tally2 --user=bob --reset
If a login is successful before the limit has been reached the failure count will reset to 0. For more details see the pam_tally2 manual page by typing ´man pam_tally2´.
It´s worth noting that the manual page advises to configure this with the /etc/pam.d/login file, however I found that under CentOS 7 this did not work and needed to use the /etc/pam.d/password-auth file instead. I also tried using /etc/pam.d/system-auth which I found documented elsewhere but this also failed, so this may differ based on your operating system.
You can also manually lock and unlock local user accounts rather than waiting for the failure limit to be reached.
Lock the user account ‘bob´.https://www.rootusers.com/23-hardening-tips-to-secure-your-linux-server/#4
Quelle: https://www.rootusers.com/23-hardening-tips-to-secure-your-linux-server/
 pam_tcb.so: Migrating from shadow passwords to tcb in Linux pam_tcb.so: Migrating from shadow passwords to tcb in Linux
For a more secure Linux password system, a migration from shadow passwords to tcb is worth a little extra work. Vincent Danen tells you what you need to recompile and patch.Wechsel von shadow-Passwörtern nach tcb in Linux.
"Shadow passwords have been a de facto standard with Linux distributions for years, and as well as the use of md5 passwords. However, there are drawbacks to using the traditional shadow password method, and even md5 is not as secure as it used to be. One drawback to the shadow password file is that any application that requires looking up a single shadow password (i.e., your password) also can look at everyone else´s shadow passwords, which means that any compromised tool that can read the shadow file will be able to obtain everyone´s shadow password."
Install pam_tcb (like pam_tcb(pclos) and other pam-module-rpm). If the encryption should be blowfish, install the package bcrypt.
Source and howto: https://www.techrepublic.com/article/migrating-from-shadow-passwords-to-tcb-in-linux/
alternatively: Migrating to tcb, http://www.opennet.ru/man.shtml?topic=tcb_convert&category=8&russian=2
After performing the howto (but still resigning from blowfish and the deletion of the shadow-files), our modified /etc/pam.d/system-auth has got the include:
#%PAM-1.0
auth optional pam-mount.so try_first_pass
auth required pam_env.so
auth sufficient pam_tcb.so
auth required pam_deny.so
auth requisite pam_succeed_if.so uid >= 500 quiet
auth required pam_tally2.so deny=3 onerr=fail unlock_time=1200
account sufficient pam_tcb.so
account required pam_deny.so
account sufficient pam_succeed_if.so uid < 500 quiet
account required pam_tally2.so per_user
password required pam_cracklib.so try_first_pass retry=3 minlen=6 dcredit=1 ucredit=1
password sufficient pam_tcb.so use_authtok tcb write_to=tcb
password required pam_deny.so
session optional pam_mount.so
session optional pam_keyinit.so revoke
session required pam_limits.so
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_tcb.so
and /etc/pam.d/password-auth:
#%PAM-1.0
# This file is auto-generated.
# User changes will be destroyed the next time authconfig is run.
auth required pam_env.so
auth required pam_tally2.so file=/var/log/tallylog deny=3 even_deny_root unlock_time=1200
auth sufficient pam_tcb.so shadow fork prefix=$2a$ count=8
auth required pam_deny.so
account required pam_tcb.so
password requisite pam_cracklib.so try_first_pass retry=3 type=
password sufficient pam_tcb.so try_first_pass use_authtok sha512 shadow
password required pam_deny.so
session optional pam_keyinit.so revoke
session required pam_limits.so
session [success=1 default=ignore] pam_succeed_if.so service in crond quiet use_uid
session required pam_tcb.so
/etc/nsswitch.conf:
#
# /etc/nsswitch.conf
#
# An example Name Service Switch config file. This file should be
# sorted with the most-used services at the beginning.
#
# The entry ´[NOTFOUND=return]´ means that the search for an
# entry should stop if the search in the previous entry turned
# up nothing. Note that if the search failed due to some other reason
# (like no NIS server responding) then the search continues with the
# next entry.
#
# Legal entries are:
#
# compat Use compatibility setup
# nisplus or nis+ Use NIS+ (NIS version 3)
# nis or yp Use NIS (NIS version 2), also called YP
# dns Use DNS (Domain Name Service)
# files Use the local files
# db Use the local database (.db) files
# [NOTFOUND=return] Stop searching if not found so far
#
# For more information, please read the nsswitch.conf.5 manual page.
#
passwd: files -root -ALL
shadow: files -root -ALL
group: files
hosts: files [success=return] localhost [success=return] [notfound=return]
networks: files
services: -ALL
protocols: -ALL
rpc: -root -ALL
ethers: -ALL
netmasks: files
netgroup: files
publickey: files
bootparams: files
ipnodes: -ALL
sendmailvars: -ALL
automount: -root -ALL
aliases: files
hosts with localhost for pdnsd and TOR resp. tordns: we care about this in future here!
Installation of software can lead to other settings, so check out this file from time to time !
More details about /etc/nsswitch.conf: https://docs.oracle.com/cd/E24841_01/html/820-2980/ipconfig-42.html
You should try the originally meant "shadow: tcb nisplus nis" instead and set hosts to "hosts: files ... dns ..." into this recommended order.
and with pam_tcb.so for all pam_unix.so in /etc/pam.d/*
This all makes the computer once more mouseclick-fast and secure.
 Disable Root Console Access Disable Root Console Access
The previous step disables remote access for the root account, however it will still be possible for root to log in through any console device. Depending on the security of your console access you may wish to leave root access in place, otherwise it can be removed by clearing the /etc/securetty file as shown below.
echo > /etc/securetty
This file lists all devices that root is allowed to login to, the file must exist otherwise root will be allowed access through any communication device available whether that be console or other.
With no devices listed in this file root access has been disabled. It is important to note that this does not prevent root from logging in remotely with SSH for instance, that must be disabled as outlined in point 3 - Disable remote root access above.
Access to the console itself should also be secured, a physical console can be protected by the information covered in point 13 - Physical security.
https://www.rootusers.com/23-hardening-tips-to-secure-your-linux-server/
 Limited amount of processes, source. Arch Linux Limited amount of processes, source. Arch Linux
On systems with many or untrusted users, it is important to limit the number of processes each can run at once, therefore preventing fork bombs and other denial of service attacks. /etc/security/limits.conf determines how many processes each user, or group can have open, and is empty (except for useful comments) by default. adding the following lines to this file will limit all users to 100 active processes, unless they use the prlimit command to explicitly raise their maximum to 200 for that session. These values can be changed according to the appropriate number of processes a user should have running, or the hardware of the box you are administrating. Do not set the limit too low. System can malfunction.
* soft nproc 300
* hard nporc 320
# user soft nproc 200
# user hard nproc 250
# surfuser soft nproc 60
# surfuser hard nporc 80
toruser soft nproc 80
toruser hard nporc 100
 librepository (el6), libsafec-check (fc30, fc29): Finds unsafe APIs
This once more makes computer mouseclick-fast! librepository (el6), libsafec-check (fc30, fc29): Finds unsafe APIs
This once more makes computer mouseclick-fast!
 Virus scanner ClamAV, Admin 03/20 (clamav (el6)) Virus scanner ClamAV, Admin 03/20 (clamav (el6))
In order to protect Windows-Clients against the malicious internet, there are some solutions. This article introduces the best Linux-programs for it.
The secure storage of large and larger data masses is a challenge for each IT-infrastructure.
ADMIN-Magazin reported, how administrators can configure the Squid-proxy, so that he scans for viruses with ClamAV and Dansguardian. The same functions for Samba-Fileserver. You should not forget, that the scan of webtraffic and incoming E-Mail only does not care for complete security. Therefore it is still essential to run local virus scanner upon Windows-Clients.
It is not the big problem to install ClamAV, because most Linux-distributions do provide already made packages in their repositories.
https://www.admin-magazin.de/Das-Heft/2010/03/ClamAV
Reader opinion by Gooken: For a well-configured Linux, a virus scanner is only needed for Samba and especially E-Mail-clients resp. a virus scanner, even ClamAV, of course, isn´t really needed at all!
 Bastille, msec, rkhunter, chkrootkit, clamav (clamscan, klamav), maldetect, checksec, seccheck, xsysinfo, smartd, nessus, tkcvs and cervisia, ... Bastille, msec, rkhunter, chkrootkit, clamav (clamscan, klamav), maldetect, checksec, seccheck, xsysinfo, smartd, nessus, tkcvs and cervisia, ...
At this place think of programs like bastille and msec (rosa2016.1, rosa2014.1) to check out lacks in system security, before going on with the manual configuration hook by hook. Such programs with own graphical frontends resp. wizards protocol lacks in security and are able to automatically reconfigure the system even more secure.
 Two-Factor-Authentification Two-Factor-Authentification
Two factor authentication can be implemented for SSH access or other application login, it will improve login security by adding a second factor of authentication, that is the password is typically known as something you know, while the second factor may be a physical security token or mobile device which acts as something you have. The combination of something you know and something you have ensures that you are more likely who you say you are.
There are custom applications available for this such as Duo Securityand Google Authenticator as well as many others. These typically involve installing an application on a smart phone and then entering the generated code alongside your username and password when you authenticate.
Google Authenticator can be used for many other applications than just SSH, such as for WordPress login with third party plugin support.
https://www.rootusers.com/23-hardening-tips-to-secure-your-linux-server/
... can´t believe it, remark by Gooken:
As executed programs (processes), think of text processing and terminal, do already exist in the RAM...
All INTEL-CPU-generations since Celeron
"We can read out everything!", tagesschau.de, 04.01.2017
As a consequence of a newspaper-report scientific researches from the Technical University Graz exposed the newest security-exploit in many computer processors. "We were shocked ourself, that this functions", said Michael Schwarz from TU Graz to "Tagesspiegel".
By this exploit all data could be read out, that are in actual process by the computer. "In Principle we could read out all actually entered by the keyboard." Attackers could also get data from Onlinebanking or stored passwords. "Therefore they must intrude into the computer", Schwarz restricted.
Serious hard lack in security in all Intel-CPUs, PC-WELT, 03.01.2018
A serious hard lack was found in Intel-processors of the last 10 years (excpet the one introduced by us in our data-sheed, rem., Gooken). Its closure costs performance.
https://www.pcwelt.de/a/schwere-luecke-in-allen-intel-cpus-entdeckt,3449263
 What to do: What to do:
Data sheed: Plattform: ITX-220: is not listed in the table for exploited mainboards by Intel (1) and an exploit remaind undetected as the helping-tool for belonging system-analyzes from Intel indicated (intel-sa00086.zip for Linux) (2). Result: Modul MEI (2) can not be found (this module can be integrated by the command "modprobe mei" manually or within /etc/modules each boot or dracut right up from the system-start).
Is there a workaround/fix?
- There are patches against Meltdown for Linux ( KPTI (formerly KAISER)), Windows, and OS X. There is also work to harden software against future exploitation of Spectre, respectively to patch software after exploitation through Spectre, https://meltdownattack.com/
- iucode-tool (pclos2018)
 - CPU: mouseclick-fast and secure: microcode_ctl ( do not get irritated by any other versions, install fast working (microcode_ctl-1.17-33.23.el6_10.x86_64.rpm, fc29: 2.1-34, rosa2016.1) upon el6 ) or ucode-intel ( OpenSuSE, >= 20190618-lp151.2.3.1.x86_64.rpm ), against ZombieLoad too (in order to get activated by console), we recommend the mouseclick-fast microcode_ctl (rosa2016.1), upon microcode_ctl (el6, rpm -i --force). Take the fastest actual microcode_ctl like microcode_ctl-1.17-33.23.el6_10.x86_64.rpm, fc29, rosa2016.1. In order to use microcode_ctl, flash the CPU by executing the command "microcode_ctl -Qu" each boot after entering it in /etc/rc.local or out of /usr/share/autostart. If it is not booted, the CPU will work upon its initial (default) microcode again. - CPU: mouseclick-fast and secure: microcode_ctl ( do not get irritated by any other versions, install fast working (microcode_ctl-1.17-33.23.el6_10.x86_64.rpm, fc29: 2.1-34, rosa2016.1) upon el6 ) or ucode-intel ( OpenSuSE, >= 20190618-lp151.2.3.1.x86_64.rpm ), against ZombieLoad too (in order to get activated by console), we recommend the mouseclick-fast microcode_ctl (rosa2016.1), upon microcode_ctl (el6, rpm -i --force). Take the fastest actual microcode_ctl like microcode_ctl-1.17-33.23.el6_10.x86_64.rpm, fc29, rosa2016.1. In order to use microcode_ctl, flash the CPU by executing the command "microcode_ctl -Qu" each boot after entering it in /etc/rc.local or out of /usr/share/autostart. If it is not booted, the CPU will work upon its initial (default) microcode again.
Howto start microcode_ctl, for example add into /etc/rc.local:
echo 1 > /sys/devices/system/cpu/microcode/reload
# microcode_ctl -Qu
sh /usr/libexec/microcode_ctl/reload_microcode
or
start microcode_ctl automatically each boot by belonging udev-rule (number 83).
Changelog microcode_ctl
* Fr Dez 15 2017 Petr Oros poros@redhat.com - 1:1.17-25.2
- Update Intel CPU microde for 06-3f-02, 06-4f-01 and 06-55-04
- Add amd microcode_amd_fam17h.bin data file
- Resolves: #1527357
- Intel: Tools for ME-security-exploits, 24.11.2017, https://www.pro-linux.de/news/1/25369/intel-werkzeug-f%C3%BCr-me-sicherheitsl%C3%BCcken-vorgestellt.html
- kernel-5.4.249 (pclos2023) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) and the reintegrated KPTI-/KAISER-patch
- "modprobe mei" or start or stop the load of module mei in /etc/modules by entering resp. removing the line "mei" MEI in this matter was mentionded in Intel-security-checks as one part of the main risk.
After the installation of kernel-4.19 (pclos), lookout for the requirements and install missing ones like kmod (pclos): "rpm -qi --requires kernel-4.19....".
- Update Firefox to 57.0.4 resp. 52.5.3-ESR (OpenSuSE) - Security fixes to address the Meltdown and Spectre timing attacks - https://blog.mozilla.org/security/2018/01/03/mitigations-landing-new-class-timing-attack/ - Require new nss 3.34 (fixed rhbz#1531031) - Disabled ARM on all Fedoras due to rhbz#1523912
- Nvidia vs. Spectre: New Nvidia-drivers protect against Spectre-CPU-attacks, https://www.pcwelt.de/a/neue-nvidia-treiber-schuetzen-vor-spectre-cpu-attacken,3449339
NVIDIA graphics drivers (USN-3521-1, https://wiki.ubuntu.com/SecurityTeam/KnowledgeBase/SpectreAndMeltdown?_ga=
2.181440484.2145149635.1515760095-1741249263.1499327986)
- Webkitgtk+ (USN-3530-1)
- QEMU (USN-3560-1)
- libvirt (USN-3561-1)
- Cloud Images: Cloud images which address CVE-2017-5753 and CVE-2017-5715 (aka Spectre) and CVE-2017-5754 (aka Meltdown) are available for https://cloud-images.ubuntu.com from for the following releases: ...
 Beneath microcode_ctl (rosa2016.1, el6) look out for actual kernel-firmware (el6) and kernel-headers (el6) too. Take those from year2020, making it all mouseclick-fast ! Beneath microcode_ctl (rosa2016.1, el6) look out for actual kernel-firmware (el6) and kernel-headers (el6) too. Take those from year2020, making it all mouseclick-fast !
 Firewall Linfw3 against Meltdown and Spectre: Set group "nobody" for the group of surfuser (with primary group nobody) and only allow surfuser with one more group of surfuser named surfgroup for example (instead of nobody) to go online. Linfw3 is able to block even root (UID: root, 0, GID: root, 0). So noone is allowed to go online through Linfw3 else surfuser with group surfgroup (instead of his primary group "nobody"), what prevents device drivers from exchaning data - as in this case caused by Meltdown and Spectre To go paranoid, to make it even more confusing for kernel and CPU, set all directories and files owned by surfuser to it´s primary group "nobody". Firewall Linfw3 against Meltdown and Spectre: Set group "nobody" for the group of surfuser (with primary group nobody) and only allow surfuser with one more group of surfuser named surfgroup for example (instead of nobody) to go online. Linfw3 is able to block even root (UID: root, 0, GID: root, 0). So noone is allowed to go online through Linfw3 else surfuser with group surfgroup (instead of his primary group "nobody"), what prevents device drivers from exchaning data - as in this case caused by Meltdown and Spectre To go paranoid, to make it even more confusing for kernel and CPU, set all directories and files owned by surfuser to it´s primary group "nobody".
Test, if the system is secure now, protected well against Meltdown and Spectre, type into terminal the command:
head /sys/devices/system/cpu/vulnerabilities/*
You can update the kernel, if not.
https://www.pcwelt.de/tipps/CPU-Sicher-vor-Meltdown-Spectre-und-Co-10593390.html
 Integrate sensors and chips from mainboard: Integrate sensors and chips from mainboard:
Paket lm_sensors (pclos)
sensors-detect
modprobe for found modules: enter them into /etc/modules ( for ITX-220: it87, coretemp, i2c-dev, mei)
Notice: It might be mouseclick-fast and more seucre not to enter them into /etc/modules.
LAN-Chip: eventually activate it through CMOS-BIOS-Setup (default: inactive)
 Logging off idle users Logging off idle users
Idle users are usually a security problem, a user might be idle maybe because he´s out to lunch or because a remote connection hung and was not re-established. For whatever the reason, idle users might lead to a compromise:
because the user´s console might be unlocked and can be accessed by an intruder.
because an attacker might be able to re-attach to a closed network connection and send commands to the remote shell (this is fairly easy if the remote shell is not encrypted as in the case of telnet).
Some remote systems have even been compromised through an idle (and detached) screen.
Automatic disconnection of idle users is usually a part of the local security policy that must be enforced. There are several ways to do this:
If bash is the user shell, a system administrator can set a default TMOUT value (see bash(1)) which will make the shell automatically log off remote idle users. Note that it must be set with the -o option or users will be able to change (or unset) it.
Install timeoutd and configure /etc/timeouts according to your local security policy. The daemon will watch for idle users and time out their shells accordingly.
Install autolog and configure it to remove idle users.
The timeoutd or autolog daemons are the preferred method since, after all, users can change their default shell or can, after running their default shell, switch to another (uncontrolled) shell.
Linux: TMOUT To Automatically Log Users Out
last updated May 18, 2011 in Categories BASH Shell, Linux
How do I auto Logout my shell user in Linux after certain minutes of inactivity?
Linux bash shell allows you to define the TMOUT environment variable. Set TMOUT to automatically log users out after a period of inactivity. The value is defined in seconds. For example,
export TMOUT=120
The above command will implement a 2 minute idle time-out for the default /bin/bash shell. You can edit your ~/.bash_profile or /etc/profile file as follows to define a 5 minute idle time out:
# set a 5 min timeout policy for bash shell
TMOUT=300
readonly TMOUT
export TMOUT
Save and close the file. The readonly command is used to make variables and functions readonly i.e. you user cannot change the value of variable called TMOUT.
How Do I Disable TMOUT?
To disable auto-logout, just set the TMOUT to zero or unset it as follows:
$ export TMOUT=0
or
$ unset TMOUT
Please note that readonly variable can only be disabled by root in /etc/profile or ~/.bash_profile
https://www.cyberciti.biz/faq/linux-tmout-shell-autologout-variable/
Or assign a value for SHELL_TIMEOUT (TMOUT) in /etc/security/msec/level.secure
SHELL_TIMEOUT=300
 Restricting access to kernel pointers in the proc filesystem, source: Arch Linux Restricting access to kernel pointers in the proc filesystem, source: Arch Linux
Note: linux-hardened sets kptr_restrict=2 by default rather than 0.
Enabling kernel.kptr_restrict will hide kernel symbol addresses in /proc/kallsyms from regular users without CAP_SYSLOG, making it more difficult for kernel exploits to resolve addresses/symbols dynamically. This will not help that much on a pre-compiled Arch Linux kernel, since a determined attacker could just download the kernel package and get the symbols manually from there, but if you´re compiling your own kernel, this can help mitigating local root exploits. This will break some perf commands when used by non-root users (but many perf features require root access anyway). See FS#34323 for more information.
/etc/sysctl.d/50-kptr-restrict.conf
kernel.kptr_restrict = 1
 Next point fstab-Option hidepid for proc from source Arch Linux should be applied once more at your own risk: Next point fstab-Option hidepid for proc from source Arch Linux should be applied once more at your own risk:
hidepid
"Warning: This may cause issues for certain applications like an application running in a sandbox and Xorg.
.
The kernel has the ability to hide other user-processes, normally accessible via /proc, from unprivileged users by mounting the proc filesystem with the hidepid= and gid= options documented here.
This greatly complicates an intruder´s task of gathering information about running processes, whether some daemon runs with elevated privileges, whether other user runs some sensitive program, whether other users run any program at all, makes it impossible to learn whether any user runs a specific program (given the program doesn´t reveal itself by its behaviour), and, as an additional bonus, poorly written programs passing sensitive information via program arguments are now protected against local eavesdroppers.
The proc group, provided by the filesystem package, acts as a whitelist of users authorized to learn other users´ process information. If users or services need access to /proc/<pid> directories beyond their own, add them to the group.
For example, to hide process information from other users except those in the proc group:
/etc/fstab
proc /proc proc nosuid,nodev,noexec,hidepid=2,gid=proc 0 0 "
In the following and therefore just for our paranoid view, only some more security-points, now from debian.org, https://www.debian.org/doc/manuals/securing-debian-howto/ch1.en.html up to https://www.debian.org/doc/manuals/securing-debian-howto/ch12.en.html, might interest like:
 Choose a BIOS password Choose a BIOS password
Before you install any operating system on your computer, set up a BIOS password. After installation (once you have enabled bootup from the hard disk) you should go back to the BIOS and change the boot sequence to disable booting from floppy, CD-ROM and other devices that shouldn´t boot. Otherwise a cracker only needs physical access and a boot disk to access your entire system.
Disabling booting unless a password is supplied is even better. This can be very effective if you run a server, because it is not rebooted very often. The downside to this tactic is that rebooting requires human intervention which can cause problems if the machine is not easily accessible.
Note: many BIOSes have well known default master passwords, and applications also exist to retrieve the passwords from the BIOS. Corollary: don´t depend on this measure to secure console access to system.
Set
- Supervisor Password
- User Access Level from Full Access, View Only or Limited to No Access - this prevents user acsess onto the BIOS-Setup-Utility, so that no changes of the settings are possible anymore. Now the BIOS is protected.
- User Password
- Password Check from (only for BIOS-)Setup to Always
 Turn Off IPv6 Turn Off IPv6
If you´re not using a IPv6 protocol, then you should disable it because most of the applications or policies not required IPv6 protocol and currently it doesn´t required on the server. Go to network configuration file and add followings lines to disable it.
nano /etc/sysconfig/network
NETWORKING_IPV6=no
USERCTL=no # prvents normal user from dialing in
IPV6INIT=no
https://www.tecmint.com/linux-server-hardening-security-tips/
Boot-process: If the message "Can not stat ( a named ) initscript" occurs during system boot, delete this initscript through all six runlevel and in directory init.d by
rm -df /etc/rc0.d/initscript-name
rm -df /etc/rc1.d/initscript-name
...
rm -df /etc/rc6.d/initscript-name
rm -df /etc/init.d/initscript-name
 Activate resp. deactivate kernel-moduls Activate resp. deactivate kernel-moduls
Get a listing of the kernel-modules by the terminal command lsmod.
In order to make the computer mouseclick-fast, all kernel modules without essential use have to be removed from /etc/rc.modules, while this file enpossibles to integrate modules by the command &quto;modprobe Modulname" added to the last line.
.
Following our example-hardware from datasheed, the control-modules it87 und i2c-dev can be disabled and the service envoking them named lm_sensors deactivated.
######################################
# xorg.conf mit automatischer Hardware-Erkennung
# WARNUNG: VERSUCHE, DICH ANFANGS AUF NUR EINIGE WENIGE EINSTELLUNGEN ZU KONZENTRIEREN, WENN DER X-SERVER NICHT STARTET und vor dem Start immer noch nach einer Konfiguration fragt:
# Imfalle eines Fehlstarts konsultiere /var/log/Xog.0.log und suche dort nach Error- (EE)- und Warnungen- (WW)-Einträgen!
#####################################
#
# Einzelheiten: "man xorg.conf"
# File generated by XFdrake (rev )
# *************************************************
# Refer to the xorg.conf man page for details about the format of
# this file.
# ******
# ************************************************
Section "ServerLayout"
Identifier "XFree86 Configured"
Screen 0 "Screen0" 0 0
# InputDevice "Keyboard0" "CoreKeyboard" # commented in: hotplug
# InputDevice "Mymouse1" "CorePointer"# commented in: hotplug
Option "AIGLX" "true"
EndSection
Section "ServerFlags"
Option "DontVTSwitch" "true"
Option "DontZap" "true" # disable <Ctrl><Alt><BS> (server abort)
Option "AllowMouseOpenFail" "true" # allows the server to start up even if the mouse does not work
DontZoom # disable <Ctrl><Alt><KP_+>/<KP_-> (resolution switching)
Option "DPMS" "true"
Option "Xinerama" "true"
Option "DRI2" "true"
# Option "DRI3" "true"
Option "UseDefaultFontPath" "true"
Option "Pixmap" "32"
Option "IgnoreABI" "true" # X-Server-Version
Option "AutoAddDevices" "true"
Option "AutoEnableDevices" "true"
EndSection
Section "Module"
Load "dbe" # Double-Buffering Extension
Load "v4l" # Video for Linux
Load "type1"
Load "freetype"
Load "glx" # 3D layer
Load "dri2" # direct rendering
# Load "dri3" # direct rendering
Load "glamoregl" # glamor
Load "record" # Developer extension, usually not needed ( ... but this is speeding up KI !)
Load "extmod"
# Load "speedo" # Speedo fonts, this module doesn´t exist in Xorg 7.0.17
# The following are deprecated/unstable/unneeded in Xorg 7.0
# Load "ddc" # ddc probing of monitor, this should be never present, as it gets automatically loaded.
# Load "GLcore" # This should be never present, as it gets automatically loaded.
# Load "bitmap" # Should be never present, as it gets automatically loaded. This is a font module, and loading it in xorg.conf makes X try to load it twice.
SubSection "extmod"
Option "omit xfree86-dga"
EndSubSection
EndSection
Section "Extensions"
# compiz needs Composite, but it can cause bad (end even softreset-resistant)
# effects in some graphics cards, especially nv.
Option "Composite" "Enable"
EndSection
Section "Monitor"
Identifier "Monitor0"
ModelName "Generic Monitor"
# HorizSync 47.7
# VertRefresh 59.8
Option "PreferredMode" "1366x768"
# DisplaySize 361 203
# Beware having to wear glasses! Vesa values! You can comment in following Modeline for Monitor AOC e943FwS preferred modeline (59.8 Hz vsync, 47.7 kHz hsync, ratio 16/9, 84 dpi)
# ModeLine "1366×768" 85.5 1366 1436 1579 1792 768 771 774 798 +hsync +vsync
# ModeLine "1368×768_120" 185.67 1368 1472 1624 1880 768 769 772 823 -hSync +vsync
# ModeLine "1368×768_100" 151.73 1368 1464 1616 1864 768 769 772 814 -hSync +vsync
# ModeLine "1368×768_85" 125.67 1368 1456 1600 1832 768 769 772 807 -hSync +vsync
# ModeLine "1368×768_75" 110.19 1368 1456 1600 1832 768 769 772 802 -hSync +vsync
# ModeLine "1368×768_60" 85.86 1368 1440 1584 1800 768 769 772 795 -hSync +vsync
# ModeLine "1368×768" 85.86 1368 1440 1584 1800 768 769 772 795 -hSync +vsync
# ModeLine "1368×768_50" 69.92 1368 1424 1568 1768 768 769 772 791 -hSync +vsync
# Option "MonitorLayout" "LVDS,AUTO"
EndSection
Section "Device"
Identifier "Card0"
# Driver (chipset) autodetect
VendorName "All"
BoardName "All"
# BusID "PCI:1:0:0"
# VendorName "Intel Corporation"
# BoardName "Intel 810 and later"
# Driver "intel" # alternativ: fbdev (framebuffer device), vesa (Standard), vga, vga16, uncommon, void, dummy, ati, catalyst, nv, nvidia, nouveau, amdgpu, rendition, radeon, radeonhd, fglrx, tdfx, trident, virge, s3virge, siliconmotion, aiptek, apm, ast, fpit, glint, mutouch, qxl, r128, synaptics, v4l, wacom, xgi, ark, virtualbox, vmware, vmmouse, matrox, cirrus, aty, i810, i128, i740, ark, kyropfb, matrox, i2c-matrox, hga, riva, sst, neo, s3, openchrome (incl. unichrome), savage, sis, tseng, ...
Screen 0
# BusID "PCI:0:2:0"
Option "DPMS"
Option "AccelMethod" "uxa"
# Option "AccelMethod" "sna"
# Option "AccelMethod" "EXA"
# Option "AccelMethod" "glamor"
Option "AddARGBGLXVisuals" "true"
Option "fbdev" "true" # this speeds up too
Option "DRI" "true"
Option "DRI" "2"
# Option "DRI" "3"
### More available Driver options, X11 for Intel 945GM configures the options for you automatically, so you might comment in most of them
# sw_cursor is needed for some ati and radeon cards
# Option "sw_cursor"
# Option "hw_cursor"
# Option "NoAccel"
# Option "ShowCache"
Option "ShadowFB"
Option "UseFBDev"
# Option "Rotate"
# Option "VideoKey"
# Option "Linear Framebuffer <bool>
# Option "SwapbuffersWait" <bool>
# Option "XvPreferOverlay" "true"
# Option "Backlight" <string>
# Option "ColorKey" <i>
Option "HotPlug" "true" # mouse and keyboard in section device don´nt need to be declared in future (although we do)
Option "XvMC" "true"
# Option "BufferCache" "true"
# Option "DisableGLXRootClipping" "true"
# Option "EnablePageFlip" "true"
# Option "ColorTiling2D" "true"
# Option "TripleBuffer" "true"
# Option "MigrationHeuristic" "greedy"
# Option "ColorTiling" "true"
Option "TearFree" "true"
Option "ZaphodHeads" "VGA1"
# Tweaks for the xorg 7.4 (otherwise broken) "intel" driver
# Option "Tiling" "true"
Option "Legacy3D" "true"# compiz, beryl 3D-Support with DRI &Composite
Option "XAANoOffscreenPixmaps"
Option "AllowGLXWithComposite" "true"
# These two lines are (presumably) needed to prevent fonts from being scrambled
Option "XaaNoScanlineImageWriteRect" "true"
Option "XaaNoScanlineCPUToScreenColorExpandFill" "true"
# Option "RelaxedFencing" <bool>
# Option "RelaxedFencing" # [<bool>]
# Option "Throttle" # [<bool>]
# Option "DelayedFlush" # [<bool>]
# Option "PerCrtcPixmaps" # [<bool>]
# Option "FallbackDebug" # [<bool>]
# Option "DebugFlushBatches" # [<bool>]
# Option "DebugFlushCaches" # [<bool>]
# Option "DebugWait" # [<bool>]
EndSection
Section "Screen"
Identifier "Screen0"
Device "Card0"
Monitor "Monitor0"
DefaultColorDepth 24
Option "AddARGBGLXVisuals" "true"
# Option "DisableGLXRootClipping" "true"
SubSection "Display"
Depth 32
Modes "1366×768 1360×765 1280×720 1024×768 860×640" # up to 4096 possible for Intel 945G of ITX-220
EndSubSection
SubSection "Display"
Depth 24
Modes "1366×768 1360×765 1280×720 1024×768"
EndSubSection
SubSection "Display"
Depth 16
Modes "1366×768 1360×765 1280×720 1024×768" 860×640"
EndSubSection
SubSection "Display"
Depth 15
Modes "1366×768 1360×765 1280×720 1024×768"
EndSubSection
SubSection "Display"
Depth 8
Modes "1366×768 1360×765 1280×720 1024×768"
EndSubSection
EndSection
Section "DRI"
Mode 0666
EndSection
Section "InputDevice" # not needed, if hotplugged
Identifier "Mymouse1"
Driver "mouse" # man mousedrv
# Option "Device" "/dev/ttyS0"
# Option "Protocol" "ImPS/2"
Option "Protocol" "usb"
# Option "Protocol" "auto"
# Option "Protocol" "Auto"
# Option "Protocol" "ExplorerPS/2"
# Option "Protocol" "auto"
# Option "Device" "/dev/psaux"
# Option "Device" "/dev/ttyS0"
Option "Device" "/dev/input/mice"
Option "Emulate3Buttons" "true"
Option "CorePointer"
# Option "ZAxisMapping" "4 5" # wheel mouse, not needed, if hotplugged
# Option "ZAxisMapping" "4 5 6 7"
EndSection
Section "InputDevice"
# generated from default
Identifier "Keyboard0"
Driver "kbd"
Option "XkbModel" "pc105"
Option "XkbLayout" "de"
Option "CoreKeyboard"
Option "XkbRules" "xorg"
Option "AccelerationProfile" "0"
EndSection
Used driver: xorg-x11-drv-intel (el6, 2010-2020, here 2020 not from CentOS 6 in year 2016, but 2020 from https://download.copr.fedorainfracloud.org/results/scx/xorg-x11-drv-intel/epel-6-x86_64/01523747-xorg-x11-drv-intel/) for Intel 945MG from mainboard ITX-220
Details see man "xorg.conf" and "man mousedrv"
X11-error-log: /var/log/Xorg.0.log
Try this X11 even without any /etc/xorg.conf ! Secure up /etc/X11/xorg.conf before it.
 Do not plug to the Internet until ready Do not plug to the Internet until ready
The system should not be immediately connected to the Internet during installation. This could sound stupid but network installation is a common method. Since the system will install and activate services immediately, if the system is connected to the Internet and the services are not properly configured you are opening it to attack.
 Run the minimum number of services required Run the minimum number of services required
Services are programs such as ftp servers and web servers. Since they have to be listening for incoming connections that request the service, external computers can connect to yours. Services are sometimes vulnerable (i.e. can be compromised under a given attack) and hence present a security risk. Unwanted servces might be: telnet, ftp, smbd and nmbd (Samba), portmap (NFS), automount (NFS, network file system), rexec, named (DNS), lpd (printer), inetd, ...
https://www.tecmint.com/remove-unwanted-services-from-linux/
 Set a LILO or GRUB password Set a LILO or GRUB password
What matters for updates, should almost be not the version of the rpm but the new release of one and the same version (backport-concept).
 umask (see man umask): recommended values: umask (see man umask): recommended values:
/etc/fstab: option umask 077 at least for the root- and home-Partition
~/.bashrc: umask 077 # for all user
~/.bashrc-profile: umask 077 # for all user
/etc/profile: umask 022 # to keep most of all accessible for a user
 Disable root prompt on the initramfs Disable root prompt on the initramfs
Note: This applies to the default kernels provided for releases after Debian 3.1
Linux 2.6 kernels provide a way to access a root shell while booting which will be presented during loading the initramfs on error. This is helpful to permit the administrator to enter a rescue shell with root permissions. This shell can be used to manually load modules when autodetection fails. This behavior is the default for initramfs-tools generated initramfs. The following message will appear:
"ALERT! /dev/sda1 does not exist. Dropping to a shell!"
In order to remove this behavior you need to set the following boot argument:panic=0. Add this to the variable GRUB_CMDLINE_LINUX in /etc/default/grub and issue update-grub or to the append section of /etc/lilo.conf.
 Remove root prompt on the kernel Remove root prompt on the kernel
Note: This does not apply to the kernels provided for Debian 3.1 as the timeout for the kernel delay has been changed to 0.
Linux 2.4 kernels provide a way to access a root shell while booting which will be presented just after loading the cramfs file system. A message will appear to permit the administrator to enter an executable shell with root permissions, this shell can be used to manually load modules wheX11-Servern autodetection fails. This behavior is the default for initrd´s linuxrc. The following message will appear:
Press ENTER to obtain a shell (waits 5 seconds)
In order to remove this behavior you need to change /etc/mkinitrd/mkinitrd.conf and set:
# DELAY The number of seconds the linuxrc script should wait to
# allow the user to interrupt it before the system is brought up
DELAY=0
Then regenerate your ramdisk image. You can do this for example with:
# cd /boot
# mkinitrd -o initrd.img-2.4.18-k7 /lib/modules/2.4.18-k7
or (preferred):
# dpkg-reconfigure -plow kernel-image-2.4.x-yz
 Restricting console login access Restricting console login access
Some security policies might force administrators to log in to the system through the console with their user/password and then become superuser (with su or sudo). This policy is implemented in Debian by editing the /etc/pam.d/login and the /etc/securetty when using PAM (make a backup, before doing this!):
/etc/pam.d/login enables the pam_securetty.so module. This module, when properly configured will not ask for a password when the root user tries to login on an insecure console, rejecting access as this user.
securetty by adding/removing the terminals to which root access will be allowed. If you wish to allow only local console access then you need console, ttyX and vc/X (if using devfs devices), you might want to add also ttySX, if you are using a serial console for local access (where X is an integer, you might want to have multiple instances. The default configuration for Wheezy includes many tty devices, serial ports, vc consoles as well as the X server and the console device. You can safely adjust this if you are not using that many consoles. You can confirm the virtual consoles and the tty devices you have by reviewing /etc/inittab . For more information on terminal devices read the Text-Terminal-HOWTO.
When using PAM, other changes to the login process, which might include restrictions to users and groups at given times, can be configured in /etc/pam.d/login. An interesting feature, that can be disabled, is the possibility to login with null (blank) passwords. This feature can be limited by removing nullok from the line:
auth required pam_unix.so nullok
Our /etc/pam.d/login:
%PAM-1.0
auth required pam-securetty.so
auth required pam_tally2.so deny=3 even_deny_root unlock_time=2400
auth include system-auth
account required pam_nologin.so
account include system-auth
password include system-auth
# pam_selinux.so close should be the first session rule
session required pam_selinux.so close
session required pam_loginuid.so
session optional pam_console.so
# pam_selinux.so open should only be followed by sessions to be executed in the user context
session required pam_selinux.so open
session required pam_namespace.so
session optional pam_keyinit.so force revoke
session include system-auth
-session optional pam_ck_connector.so
 securetty securetty
is the file, where to add or delete terminals for the login of root. If a local access by console should be allowed only, then add console, ttyX and vc/X ( if devfs-interface is used, where X is an integer ).
https://www.debian.org/doc/manuals/securing-debian-howto/ch4.de.html
The primary entry types and their affects are as follows:
If /etc/securetty doesn´t exist, root is allowed to login from any tty
If /etc/securetty exist and is empty, root access will be restricted to single user mode or programs, that are not restricted by pam_securetty (i.e. su, sudo, ssh, scp, sftp)
if you are using devfs (a deprecated filesystem for handling /dev), adding entries of the form vc/[0-9]* will permit root login from the given virtual console number
if you are using udev (for dynamic device management and replacement for devfs), adding entries of the form tty[0-9]* will permit root login from the given virtual console number
listing console in securetty, normally has no effect since /dev/console points to the current console and is normally only used as the tty filename in single user mode, which is unaffected by /etc/securetty
adding entries like pts/[0-9]* will allow programs that use pseudo-terminals (pty) and pam_securetty to login into root assuming the allocated pty is one of the ones listed; it´s normally a good idea not to include these entries because it´s a security risk; it would allow, for instance, someone to login into root via telenet, which sends passwords in plaintext (note that pts/[0-9]* is the format for udev which is used in RHEL 5.5; it will be different if using devfs or some other form of device management)
For single user mode, /etc/securetty is not consulted because the sulogin is used instead of login. See the sulogin man page for more info. Also you can change the login program used in /etc/inittab for each runlevel.
https://unix.stackexchange.com/questions/41840/effect-of-entries-in-etc-securetty
 Restricting system reboots through the console Restricting system reboots through the console
If your system has a keyboard attached to it anyone (yes anyone) with physical access to the system can reboot the system through it without login in just pressing the Ctrl+Alt+Delete keyboard combination, also known as the three finger salute. This might, or might not, adhere to your security policy.
This is aggravated in environments in which the operating system is running virtualised. In these environments, the possibility extends to users that have access to the virtual console (which might be accessed over the network). Also note that, in these environments, this keyboard combination is used constantly (to open a login shell in some GUI operating systems) and an administrator might virtually send it and force a system reboot.
There are two ways to restrict this:
configure it so that only allowed users can reboot the system, disable this feature completely.
If you want to restrict this, you must check the /etc/inittab so that the line that includes ctrlaltdel calls shutdown with the -a switch.
The default in Debian includes this switch:
ca:12345:ctrlaltdel:/sbin/shutdown -t1 -a -r now
The -a switch, as the shutdown(8) manpage describes,makes it possible to allow some users to shutdown the system. For this the file /etc/shutdown.allow must be created and the administrator has to include there the name of users which can boot the system. When the three finger salute combination is pressed in a console the program will check if any of the users listed in the file are logged in. If none of them is, shutdown will not reboot the system.
If you want to disable the Ctrl+Alt+Del combination you just need to comment the line with the ctrlaltdel definition in the /etc/inittab.
Remember to run init q after making any changes to the /etc/inittab file for the changes to take effect.
 Restricting the use of the Magic SysRq key Restricting the use of the Magic SysRq key
The Magic SysRq key is a key combination that allows users connected to the system console of a Linux kernel to perform some low-level commands. These low-level commands are sent by pressing simultaneously Alt+SysRq and a command key. The SysRq key in many keyboards is labeled as the Print Screen key.
Since the Etch release, the Magic SysRq key feature is enabled in the Linux kernel to allow console users certain privileges. You can confirm this by checking if the /proc/sys/kernel/sysrq exists and reviewing its value:
$ cat /proc/sys/kernel/sysrq
438
The default value shown above allows all of the SysRq functions except for the possibility of sending signals to processes. For example, it allow users connected to the console to remount all systems read-only, reboot the system or cause a kernel panic. In all the features are enabled, or in older kernels (earlier than 2.6.12) the value will be just 1.
You should disable this functionality ifaccess to the console is not restricted to authorised users: the console is connected to a modem line, there is easy physical access to the system or it is running in a virtualised environment and other users access the console. To do this edit the /etc/sysctl.conf and add the following lines:
# Disables the magic SysRq key
kernel.sysrq = 0
 User authentication: PAM User authentication: PAM
PAM (Pluggable Authentication Modules) allows system administrators to choose how applications authenticate users. Note that PAM can do nothing unless an application is compiled with support for PAM. Most of the applications that are shipped with Debian have this support built in (Debian did not have PAM support before 2.2). The current default configuration for any PAM-enabled service is to emulate UNIX authentication (read /usr/share/doc/libpam0g/Debian-PAM-MiniPolicy.gz for more information on how PAM services should work in Debian).
Each application with PAM support provides a configuration file in /etc/pam.d/ which can be used to modify its behavior:
what backend is used for authentication.
what backend is used for sessions.
how do password checks behave.
The following description is far from complete, for more information you might want to read the Linux-PAM Guides as a reference. This documentation is available in the system if you install the libpam-doc at /usr/share/doc/libpam-doc/html/.
PAM offers you the possibility to go through several authentication steps at once, without the user´s knowledge. You could authenticate against a Berkeley database and against the normal passwd file, and the user only logs in if the authentication succeeds in both. You can restrict a lot with PAM, just as you can open your system doors very wide. So be careful. A typical configuration line has a control field as its second element. Generally it should be set to requisite, which returns a login failure if one module fails.
More about PAM: https://www.debian.org/doc/manuals/securing-debian-howto/ch4.en.html, chapter 4.11
 User login actions: edit /etc/login.defs (make a backup, before doing this!) User login actions: edit /etc/login.defs (make a backup, before doing this!)
The next step is to edit the basic configuration and action upon user login. Note that this file is not part of the PAM configuration, it´s a configuration file honored by login and su programs, so it doesn´t make sense tuning it for cases where neither of the two programs are at least indirectly called (the getty program which sits on the consoles and offers the initial login prompt does invoke login).
FAILLOG_ENAB yes
If you enable this variable, failed logins will be logged. It is important to keep track of them to catch someone who tries a brute force attack.
LOG_UNKFAIL_ENAB no
If you set this variable to ´yes´ it will record unknown usernames if the login failed. It is best if you use ´no´ (the default) since, otherwise, user passwords might be inadvertenly logged here (if a user mistypes and they enter their password as the username). If you set it to ´yes´, make sure the logs have the proper permissions (640 for example, with an appropriate group setting such as adm).
SYSLOG_SU_ENAB yes
This one enables logging of su attempts to syslog. Quite important on serious machines but note that this can create privacy issues as well.
SYSLOG_SG_ENAB yes
The same as SYSLOG_SU_ENAB but applies to the sg program.
ENCRYPT_METHOD SHA512
As stated above, encrypted passwords greatly reduce the problem of dictionary attacks, since you can use longer passwords. This definition has to be consistent with the value defined in /etc/pam.d/common-password.
 User login actions: edit /etc/pam.d/login (make a backup, before doing this!) User login actions: edit /etc/pam.d/login (make a backup, before doing this!)
You can adjust the login configuration file to implement an stricter policy. For example, you can change the default configuration and increase the delay time between login prompts. The default configuration sets a 3 seconds delay:
auth optional pam_faildelay.so delay=3000000
Increasing the delay value to a higher value to make it harder to use the terminal to log in using brute force. If a wrong password is typed in, the possible attacker (or normal user!) has to wait longer seconds to get a new login prompt, which is quite time consuming when you test passwords. For example, if you set delay=10000000, users will have to wait 10 seconds if they type a wrong password.
In this file you can also set the system to present a message to users before a user logs in. The default is disabled, as shown below:
# auth required pam_issue.so issue=/etc/issue
If required by your security policy, this file can be used to show a standard message indicating that access to the system is restricted and user acess is logged. This kind of disclaimer might be required in some environments and jurisdictions. To enable it, just include the relevant information in the /etc/issue [24] file and uncomment the line enabling the pam_issue.so module in /etc/pam.d/login. In this file you can also enable additional features which might be relevant to apply local security policies such as:
setting rules for which users can access at which times, by enabling the pam_time.so module and configuring /etc/security/time.conf accordingly (disabled by default),
setup login sessions to use user limits as defined in /etc/security/limits.conf (enabled by default),
present the user with the information of previous login information (enabled by default),
print a message (/etc/motd and /run/motd.dynamic) to users after login in (enabled by default),
 Restricting ftp: editing /etc/ftpusers (make a backup, before doing this!) Restricting ftp: editing /etc/ftpusers (make a backup, before doing this!)
The /etc/ftpusers file contains a list of users who are not allowed to log into the host using ftp. Only use this file if you really want to allow ftp (which is not recommended in general, because it uses clear-text passwords). If your daemon supports PAM, you can also use that to allow and deny users for certain services.
A convenient way to add all system accounts to the /etc/ftpusers is to run
$ awk -F : ´{if ($3<1000) print $1}´ /etc/passwd > /etc/ftpusers
 Disallow remote administrative access Disallow remote administrative access
You should also modify /etc/security/access.conf to disallow remote logins to administrative accounts. This way users need to invoke su (or sudo) to use any administrative powers and the appropriate audit trace will always be generated.
You need to add the following line to /etc/security/access.conf, the default Debian configuration file has a sample line commented out (making your system mouseclick-fast; do not forget to make a backup of this file, before doing this!).
As already described commented in in /etc/security/access.conf, for root and system user and user:
:
# User "root" should be denied to get access from all other sources.
- : root : ALL
- : user : ALL
- : surfuser : 127.0.0.0/24
- : toruser : 127.0.0.0/24
- : uuidd : ALL
- . messagebus: ALL
- : wheel:ALL EXCEPT LOCAL
- : ftp : ALL
- : mail : ALL
- : pop3ad : ALL
- : bin : ALL
- : daemon : ALL
- : adm : ALL
- : sync : ALL
- : halt : ALL
- : news : ALL
# All other users should be denied to get access from all sources.
: ALL : ALL
Look out for other important options in this file too. Remember to enable the pam_access module for every service (or default configuration) in /etc/pam.d/ if you want your changes to /etc/security/access.conf honored.
 Configuring syncookies Configuring syncookies
This option is a double-edged sword. On the one hand it protects your system against syn packet flooding; on the other hand it violates defined standards (RFCs).
net/ipv4/tcp_syncookies = 1
If you want to change this option each time the kernel is working you need to change it in /etc/network/options by setting syncookies=yes. This will take effect when ever /etc/init.d/networking is run (which is typically done at boot time) while the following will have a one-time effect until the reboot:
echo 1 > /proc/sys/net/ipv4/tcp_syncookies # e.g. within /etc/rc.local
This option will only be available if the kernel is compiled with the CONFIG_SYNCOOKIES. All Debian kernels are compiled with this option builtin but you can verify it running:
$ sysctl -A |grep syncookies
net/ipv4/tcp_syncookies = 1
For more information on TCP syncookies read http://cr.yp.to/syncookies.html.
Disabling weak-end hosts issues
Systems with more than one interface on different networks can have services configured so that they will bind only to a given IP address. This usually prevents access to services when requested through any other address. However, this does not mean (although it is a common misconception) that the service is bound to a given hardware address (interface card).
This is not an ARP issue and it´s not an RFC violation (it´s called weak end host in RFC1122, section 3.3.4.2). Remember, IP addresses have nothing to do with physical interfaces.
On 2.2 (and previous) kernels this can be fixed with:
# echo 1 > /proc/sys/net/ipv4/conf/all/hidden
# echo 1 > /proc/sys/net/ipv4/conf/eth0/hidden
# echo 1 > /proc/sys/net/ipv4/conf/eth1/hidden
.....
On later kernels this can be fixed either with:
iptables rules.
properly configured routing.
kernel patching.
Along this text there will be many occasions in which it is shown how to configure some services (sshd server, apache, printer service...) in order to have them listening on any given address, the reader should take into account that, without the fixes given here, the fix would not prevent accesses from within the same (local) network.
https://www.debian.org/doc/manuals/securing-debian-howto/ch4.en.html
 Using tcpwrappers Using tcpwrappers
TCP wrappers were developed when there were no real packet filters available and access control was needed. Nevertheless, they´re still very interesting and useful. The TCP wrappers allow you to allow or deny a service for a host or a domain and define a default allow or deny rule (all performed on the application level). If you want more information take a look at hosts_access(5).
Many services installed in Debian are either:
launched through the tcpwrapper service (tcpd)
compiled with libwrapper support built-in.
On the one hand, for services configured in /etc/inetd.conf (this includes telnet, ftp, netbios, swat and finger) you will see that the configuration file executes /usr/sbin/tcpd first. On the other hand, even if a service is not launched by the inetd superdaemon, support for the tcp wrappers rules can be compiled into it. Services compiled with tcp wrappers in Debian include ssh, portmap, in.talk, rpc.statd, rpc.mountd, gdm, oaf (the GNOME activator daemon), nessus and many others.
To see which packages use tcpwrappers [31] try:
$ apt-cache rdepends libwrap0
Take this into account when running tcpdchk (a very useful TCP wrappers config file rule and syntax checker). When you add stand-alone services (that are directly linked with the wrapper library) into the hosts.deny and hosts.allow files, tcpdchk will warn you that it is not able to find the mentioned services since it only looks for them in /etc/inetd.conf (the manpage is not totally accurate here).
Now, here comes a small trick, and probably the smallest intrusion detection system available. In general, you should have a decent firewall policy as a first line, and tcp wrappers as the second line of defense. One little trick is to set up a SPAWN command in /etc/hosts.deny that sends mail to root whenever a denied service triggers wrappers:
ALL: ALL: SPAWN (
echo -e "n
TCP Wrappers: Connection refusedn
By: $(uname -n)n
Process: %d (pid %p)n
User: %un
Host: %cn
Date: $(date)n
" | /usr/bin/mail -s "Connection to %d blocked" root) &
Beware: The above printed example is open to a DoS attack by making many connections in a short period of time. Many emails mean a lot of file I/O by sending only a few packets.
https://www.debian.org/doc/manuals/securing-debian-howto/ch4.en.html
 Protecting against ARP attacks Protecting against ARP attacks
When you don´t trust the other boxes on your LAN (which should always be the case, because it´s the safest attitude) you should protect yourself from the various existing ARP attacks.
As you know the ARP protocol is used to link IP addresses to MAC addresses (see RFC826 for all the details). Every time you send a packet to an IP address an ARP resolution is done (first by looking into the local ARP cache then if the IP isn´t present in the cache by broadcasting an ARP query) to find the target´s hardware address. All the ARP attacks aim to fool your box into thinking that box B´s IP address is associated to the intruder´s box´s MAC address; Then every packet that you want to send to the IP associated to box B will be send to the intruder´s box...
Those attacks (ARP cache poisoning, ARP spoofing...) allow the attacker to sniff the traffic even on switched networks, to easily hijack connections, to disconnect any host from the network... ARP attacks are powerful and simple to implement, and several tools exists, such as arpspoof from the dsniff package or arpoison.
However, there is always a solution:
Use a static ARP cache. You can set up "static" entries in your ARP cache with:
arp -s host_name hdwr_addr
By setting static entries for each important host in your network you ensure that nobody will create/modify a (fake) entry for these hosts (static entries don´t expire and can´t be modified) and spoofed ARP replies will be ignored.
Detect suspicious ARP traffic. You can use arpwatch, karpski or more general IDS that can also detect suspicious ARP traffic (snort, prelude...).
Implement IP traffic filtering validating the MAC address.
https://www.debian.org/doc/manuals/securing-debian-howto/ch4.de.html
 Securing FTP Securing FTP
If you really have to use FTP (without wrapping it with sslwrap or inside a SSL or SSH tunnel), you should chroot ftp into the ftp users´ home directory, so that the user is unable to see anything else than their own directory. Otherwise they could traverse your root file system just like if they had a shell in it. You can add the following line in your proftpd.conf in your global section to enable this chroot feature:
DefaultRoot ~
Restart ProFTPd by /etc/init.d/proftpd restart and check whether you can escape from your homedir now.
To prevent ProFTPd DoS attacks using ../../.., add the following line in /etc/proftpd.conf: DenyFilter *.*/
Always remember that FTP sends login and authentication passwords in clear text (this is not an issue if you are providing an anonymous public service) and there are better alternatives in Debian for this. For example, sftp (provided by ssh). There are also free implementations of SSH for other operating systems: putty and cygwin for example.
However, if you still maintain the FTP server while making users access through SSH you might encounter a typical problem. Users accessing anonymous FTP servers inside SSH-secured systems might try to log in the FTP server. While the access will be refused, the password will nevertheless be sent through the net in clear form. To avoid that, ProFTPd developer TJ Saunders has created a patch that prevents users feeding the anonymous FTP server with valid SSH accounts. More information and patch available at: ProFTPD Patches. This patch has been reported to Debian too, see Bug #145669.
https://www.debian.org/doc/manuals/securing-debian-howto/ch-sec-services.en.html
 Boot-break kernel or haldaemon (hal, hald)? Boot-break kernel or haldaemon (hal, hald)?
The kernel (in our case 5.4.110 resp. 4.20.13) or haldaemon resp. hal from Mandriva-derivates as much as CentOS 6 is an enormous system-boot- and -shutdown-break "making more or less a pause" of around 30 up to 45 seconds during the system boot resp. -shutdown.
Configuration of hal:
/etc/hal.conf
<!-- This configuration file controls the Hardware Abstraction Layer
daemon - it is meant that OS vendors customize this file to reflect
their desired policy.
-->
<haldconfig>
<!-- If true, then the device list is saved to disk such that
properties are kept between invocations of hald.
-->
<persistent_device_list>false</persistent_device_list>
<!-- Default value for storage.media_check_enabled for devices of
capability storage - this can be overridden by .fdi files.
Setting this to false results a whitelist policy, e.g. media
check is only enabled for storage devices with a .fdi file
saying so.
Conversely, setting it to true results in a blacklist policy
where media check is enabled by default but may be overridden
by a .fdi for devices causing trouble.
-->
<storage_media_check_enabled>true</storage_media_check_enabled>
<!-- Default value for storage.automount_enabled_hint for devices of
capability storage - this can be overridden by .fdi files.
Setting this to false results a whitelist policy, e.g. policy
agents should only automount storage devices with a .fdi file
saying so.
Conversely, setting it to true results in a blacklist policy
where policy agents should always automount unless this is
explicitly overridden by .fdi for devices causing trouble.
-->
<storage_automount_enabled_hint>true</storage_automount_enabled_hint>
https://www.thegeekdiary.com/linux-os-service-haldaemon/
Deprecated
As of 2011, Linux distributions such as Ubuntu,[5] Debian,[6] and Fedora and on FreeBSD,[7] and projects such as KDE,[8] GNOME and X.org are in the process of deprecating HAL as it has "become a large monolithic unmaintainable mess".[5] The process is largely complete, but some use of HAL remains - Debian squeeze (Feb 2011) and Ubuntu version 10.04 remove HAL from the basic system and boot process.[9] In Linux, it is in the process of being merged into udev (main udev, libudev, and udev-extras) and existing udev and kernel functionality. The replacement for non-Linux systems such as FreeBSD is devd.
Initially a new daemon DeviceKit was planned to replace certain aspects of HAL, but in March 2009, DeviceKit was deprecated in favor of adding the same code to udev as a package: udev-extras, and some functions have now moved to udev proper.
https://en.wikipedia.org/wiki/HAL_(software)
Disabling useless daemons in RHEL/Centos/Oracle 6 servers
HAL provides valuable attack surfaces to attackers as an intermediary to privileged operations and should be disabled unless necessary: # chkconfig haldaemon off.
The hald - Hardware Access Layer Daemon - runs several processes in order to keep track of what hardware is installed on your system. This includes polling USB Drives and ´hot-swap´ devices to check for changes along with a host of other tasks.
You might see it running on your system as follows:
2474 ? S 0:00 \_ hald-runner
2481 ? S 0:00 \_ hald-addon-acpi: listening on acpid socket /var/run/acpid.socket
2487 ? S 0:00 \_ hald-addon-keyboard: listening on /dev/input/event0
2495 ? S 41:47 \_ hald-addon-storage: polling /dev/hdc
If your system is static and the devices do not change, you can actually disable this service using a policy entry.
Create a file in your policy directory, for example /etc/hal/fdi/policy/99-custom.fdi. Add the text:
hald-addon-storage
Save and reload the hald using /etc/init.d/haldaemon restart.
And you will find that service no longer is polling your hardware.
Of course to turn it back on, remove that policy entry and restart the haldaemon again, it will be back in service.
Solution Credit: Linuxforums User cn77
www.softpanorama.org/Commercial_linuxes/RHEL/Daemons/removing_daemons_in_rhel6.shtml
udev-Regel für PS/2-mouse (optical mouse from Logitech®)
... results from &quto;udevadm info -a -p /devices/platform/i8042/serio1/input/input12"
/etc/udev/rules.d/10-ps2mouse.rules
KERNEL=="input12" SUBSYSTEM=="input" DRIVER=="" ATTR{uniq}=="" ATTR{properties}=="1" ATTR{phys}=="isa0060/serio1/input0" ATTR{name}=="ImExPS/2 Logitech Wheel Mouse" ATTR{modalias}=="input:b0011v0002p0006e0063-e0,1,2,k110,111,112,113,114,r0,1,6,8,amlsfw"
KERNELS=="serio1" SUBSYSTEMS=="serio" DRIVERS=="psmouse" ATTRS{resetafter}=="5" ATTRS{resolution}=="200" ATTRS{description}=="i8042 AUX port" ATTRS{firmware_id}=="PNP: PNP0f03 PNP0f13" ATTRS{protocol}=="ImExPS/2" ATTRS{rate}=="100" ATTRS{bind_mode}=="auto" ATTRS{resync_time}=="0" ATTRS{modalias}=="serio:ty01pr00id00ex00"
 Secure up RPC-services Secure up RPC-services
Deactivate RPC abschalten (or deinstall it), if not needed.
https://www.debian.org/doc/manuals/securing-debian-howto/ch-sec-services.de.html
 haveged haveged
The haveged project is an attempt to provide an easy-to-use, unpredictable random number generator based upon an adaptation of the HAVEGE algorithm. Haveged was created to remedy low-entropy conditions in the Linux random device that can occur under some workloads, especially on headless servers.
 tcp_wrapper for server tcp_wrapper for server
With this package you can monitor and filter incoming requests for the SYSTAT, FINGER, FTP, TELNET, RLOGIN, RSH, EXEC, TFTP, TALK, and other network services.
It supports both 4.3BSD-style sockets and System V.4-style TLI. Praise yourself lucky if you don´t know what that means.
The package provides tiny daemon wrapper programs that can be installed without any changes to existing software or to existing configuration files. The wrappers report the name of the client host and of the requested service; the wrappers do not exchange information with the client or server applications, and impose no overhead on the actual conversation between the client and server applications.
Optional features are: access control to restrict what systems can connect to what network daemons; client user name lookups with the RFC 931 etc. protocol; additional protection against hosts that pretend to have someone elses host name; additional protection against hosts that pretend to have someone elses host address.
 Securing Squid Securing Squid
Squid is one of the most popular proxy/cache server, and there are some security issues that should be taken into account. Squid´s default configuration file denies all users requests. However the Debian package allows access from ´localhost´, you just need to configure your browser properly. You should configure Squid to allow access to trusted users, hosts or networks defining an Access Control List on /etc/squid/squid.conf, see the Squid User´s Guide for more information about defining ACLs rules. Notice that Debian provides a minimum configuration for Squid that will prevent anything, except from localhost to connect to your proxy server (which will run in the default port 3128). You will need to customize your /etc/squid/squid.conf as needed. The recommended minimum configuration (provided with the package) is shown below:
acl all src 0.0.0.0/0.0.0.0
acl manager proto cache_object
acl localhost src 127.0.0.1/255.255.255.255
acl SSL_ports port 443 563
acl Safe_ports port 80 # http
acl Safe_ports port 21 # ftp
acl Safe_ports port 443 563 # https, snews
acl Safe_ports port 70 # gopher
acl Safe_ports port 210 # wais
acl Safe_ports port 1025-65535 # unregistered ports
acl Safe_ports port 280 # http-mgmt
X11-Server
acl Safe_ports port 488 # gss-http
acl Safe_ports port 591 # filemaker
acl Safe_ports port 777 # multiling http
acl Safe_ports port 901 # SWAT
acl purge method PURGE
acl CONNECT method CONNECT
(...)
# Only allow cachemgr access from localhost
http_access allow manager localhost
http_access deny manager
# Only allow purge requests from localhost
http_access allow purge localhost
http_access deny purge
# Deny requests to unknown ports
http_access deny !Safe_ports
# Deny CONNECT to other than SSL ports
http_access deny CONNECT !SSL_ports
#
# INSERT YOUR OWN RULE(S) HERE TO ALLOW ACCESS FROM YOUR CLIENTS
#
http_access allow localhost
# And finally deny all other access to this proxy
http_access deny all
#Default:
# icp_access deny all
#
#Allow ICP queries from everyone
icp_access allow all
You should also configure Squid based on your system resources, including cache memory (option cache_mem), location of the cached files and the amount of space they will take up on disk (option cache_dir).
Notice that, if not properly configured, someone may relay a mail message through Squid, since the HTTP and SMTP protocols are designed similarly. Squid´s default configuration file denies access to port 25. If you wish to allow connections to port 25 just add it to Safe_ports lists. However, this is NOT recommended.
Setting and configuring the proxy/cache server properly is only part of keeping your site secure. Another necessary task is to analyze Squid´s logs to assure that all things are working as they should be working. There are some packages in Debian GNU/Linux that can help an administrator to do this. The following packages are available in Debian 3.0 and Debian 3.1 (sarge):
calamaris - Log analyzer for Squid or Oops proxy log files.
modlogan - A modular logfile analyzer.
sarg - Squid Analysis Report Generator.
squidtaild - Squid log monitoring program.
When using Squid in Accelerator Mode it acts as a web server too. Turning on this option increases code complexity, making it less reliable. By default Squid is not configured to act as a web server, so you don´t need to worry about this. Note that if you want to use this feature be sure that it is really necessary. To find more information about Accelerator Mode on Squid see the Squid User´s Guide - Accelerator Mode
 Securing printing access (the lpd and lprng issue) Securing printing access (the lpd and lprng issue)
Imagine, you arrive at work, and the printer is spitting out endless amounts of paper because someone is DoSing your line printer daemon. Nasty, isn´t it?
In any UNIX printing architecture, there has to be a way to get the client´s data to the host´s print server. In traditional lpr and lp, the client command copies or symlinks the data into the spool directory (which is why these programs are usually SUID or SGID).
In order to avoid any issues you should keep your printer servers especially secure. This means you need to configure your printer service so it will only allow connections from a set of trusted servers. In order to do this, add the servers you want to allow printing to your /etc/hosts.lpd.
However, even if you do this, the lpr daemon accepts incoming connections on port 515 of any interface. You should consider firewalling connections from networks/hosts which are not allowed printing (the lpr daemon cannot be limited to listen only on a given IP address).
Lprng should be preferred over lpr since it can be configured to do IP access control. And you can specify which interface to bind to (although somewhat weirdly).
If you are using a printer in your system, but only locally, you will not want to share this service over a network. You can consider using other printing systems, like the one provided by cups or PDQ which is based on user permissions of the /dev/lp0 device.
In cups, the print data is transferred to the server via the HTTP protocol. This means the client program doesn´t need any special privileges, but does require that the server is listening on a port somewhere.
However, if you want to use cups, but only locally, you can configure it to bind to the loopback interface by changing /etc/cups/cupsd.conf:
Listen 127.0.0.1:631 # This might not work! To go sure: Port 631 and Listen /var/run/cups/cups.sock
There are many other security options like allowing or denying networks and hosts in this config file. However, if you do not need them you might be better off just limiting the listening port. Cups also serves documentation through the HTTP port, if you do not want to disclose potential useful information to outside attackers (and the port is open) add also:
>Location /<
Order Deny,Allow
Deny From All
Allow From 127.0.0.1 # or try "Allow @LOCAL"
</Location>
This configuration file can be modified to add some more features including SSL/TLS certificates and crypto. The manuals are available at http://localhost:631/ or at cups.org.
FIXME: Add more content (the article on Amateur Fortress Building provides some very interesting views).
FIXME: Check if PDG is available in Debian, and if so, suggest this as the preferred printing system.
FIXME: Check if Farmer/Wietse has a replacement for printer daemon and if it´s available in Debian.
https://www.debian.org/doc/manuals/securing-debian-howto/ch-sec-services.en.html
 Securing SSH, mail-service, BIND, Apache, Finger and deactivate NIS Securing SSH, mail-service, BIND, Apache, Finger and deactivate NIS
https://www.debian.org/doc/manuals/securing-debian-howto/ch-sec-services.de.html
 Administrate the services with systemd since year 2013 or by chkconfig Administrate the services with systemd since year 2013 or by chkconfig
/etc/rc.local for each boot still is not registrated, so it still might not be executed, maybe the same for ip6tables and iptables. For this purpose create rc.local in /etc/init.d (by overwriting it with /etc/init.d/linfw3 for example) to change the include of previous daemon linfw3, now rc.local in /etc/init.d up to the following: start() "sh /etc/init.d/rc.local", unneeded variables removed and without stop() and restart(). Set a new chkconfig-number in the commented in line at the beginning.
To be careful, registrate the service: "chkconfig --add rc.local".
Generally, using this command, all services get visible in MCC -> service administration.
Set the hooks to activate the needed ones only or set the runlevel 0 up to 6 for each new service manually, almost like 0-OFF 1-OFF 2-OFF 3-ON 4-ON 5-ON 6-OFF.
Notice, that all runlevel-init-scripts out of /etc/init.d/ and /etc/rcX.d can also get started (start), restarted (restart) and stopped (stop) for MDV and el6 and many other distributions manually by a command like:
"sh /etc/init.d/linfw3 start".
Start of the database server mysqld (el6.remi): like rc.local above, but the bind-address has to be commented in /etc/my.cnf.
Reverse-Proxy daemon (init-script) nginx (el6): like rc.local above too, but before you do this, copy "cp -axf /usr/lib/perl5/strict.pm /usr/local/share/perl5&quto; and "cp -axf /usr/lib/perl5/warnings* /usr/local/share/perl5/".
Apache webserver daemon httpd (el6): like rc.local above, but modules have to be configured well, eventually remove them.
Print server daemon: cups (pclos)
LAN-server resp. - clients: samba-... (el6); samba is not required for single pc-workstations connected with a DSL-router
...
But before these init-scripts get started, configure the server in their own configuration-files in /etc !
...
Detailed includes of /etc/rc.local and one more script in /usr/sbin for ACL-access-rights are listed further below. Both will be started as runlevel-init-scripts (daemons) each boot out of /etc/init.d .
 Important access-rights each system-boot, meaning of UNIX/Linux-groups Important access-rights each system-boot, meaning of UNIX/Linux-groups
Files and directories with unrestricted access-rights can be found out, even without root-rights:
The command
find / -path /proc -prune -o -type f -perm 666
finds all files within the complete file-system except within "/proc", that can be read and overwritten (write). The next one,
find / -path /proc -prune -o -type f -perm 777
lists all such files, that are executable too.
find / -path /proc -prune -o -type d -perm 777
finds directores, that are ready for read and write.
Instead of giving directorese and files the full access rights (chmod 777), it is the better to use groups for the common used files by the command
chgrp [-R] [group] [file/Directory]
https://www.pcwelt.de/ratgeber/Sechs-wichtige-Sicherheitstipps-Linux-Server-9940087.html#6
777 ->, 770, 775 -> 770, 755 ->, 750, 641 ->, 640 usw.
For this, at least following user should belong to the group of root: standard group root, uuid, lp, lpadmin, tty, user and toruser.
Be a little bit careful with this! We almost resign from this assignment of users to the group of root in main in future, but whoever wants can try to restrict even more the access rights this way...
 chgrp changes the group of directories and files. For the full access by different user and groups only the access-right 770 for directories and 660 for files have to be set only.. chgrp changes the group of directories and files. For the full access by different user and groups only the access-right 770 for directories and 660 for files have to be set only..
 Important access-rights set each system boot Important access-rights set each system boot
/etc/rc.local
chown root:root / # Notice: It would be much better to enter all chown and chmod here in /etc/permissions.secure and in the adequate form there only!
chown root:root /* # -> /etc/permissions.secure
chmod 700 -R /etc/init.d
chmod 700 -R /etc/rc0.d
chmod 700 -R /etc/rc1.d
chmod 700 -R /etc/rc2.d
chmod 700 -R /etc/rc3.d
chmod 700 -R /etc/rc4.d
chmod 700 -R /etc/rc5.d
chmod 700 -R /etc/rc6.d
chmod 400 /etc/shadow*
chmod 400 path_to_encrypted_key_file_for_LUKS_encrypted_partitions
...
Also set in /etc/permissions.local "/usr/sbin/suexec root:root 0755" (instead of 4755) ! In order to gain a first, short overview for more access-rights within /etc/rc.local set each boot ( for a second we are going to list them more in detail soon ). They do not make the system working only secure, they also do let work it mouseclick-fast :
chmod 111 /# Notice: It would be much better to enter all chown and chmod here in /etc/permissions.secure and in the adequate form there only!
chmod 755 /usr # 755 needed for caffeine only, else 751
chmod 751 /bin
chmod 751 /var # resp. 750, if user belongs to the group of root
chmod 751 /sbin
chmod 751 /lib64
chmod 751 /usr/lib64
# chmod 751 -R /usr/lib64/python2.6
# chmod 751 -R /usr/lib/python2.6 # shall have got the same include as /usr/lib64/python2.6
chmod 751 /usr/lib64/kde4
chmod 751 /etc # resp. chmod 750, if the groups listed above belong to root, same for /opt and /var, but we won&#t follow this in future.
chmod 755 /etc/* # resp.chmod 750, if the groups listed above belong to root, same for /opt and /var, but we won&#t follow this in future.
chmod 755 /etc/bashrc
chmod 755 -R /etc/font*
chmod 755 /etc/group
chmod 755 /etc/nsswitch.conf
chmod 755 /etc/ld.so.preload
chmod 755 -R /etc/pango*
chmod 755 /etc/sysconfig/network
chmod 755 /etc/sysconfig/network-scripts
chmod 700 -R /etc/init.d
chmod 700 -R /etc/rc0.d
chmod 700 -R /etc/rc1.d
chmod 700 -R /etc/rc2.d
chmod 700 -R /etc/rc3.d
chmod 700 -R /etc/rc4.d
chmod 700 -R /etc/rc5.d
chmod 700 -R /etc/rc6.d
chown root:shadow /etc/shadow*
chmod 400 /etc/shadow*
chown root:root /etc/passwd*
chmod 644 /etc/passwd*
chown root:root /etc/fstab*
chmod 400 /etc/fstab*
chown root:root /etc/crypttab*
chmod 700 /etc/crypttab*
chown root:root /etc/mtab*
chmod 700 /etc/mtab*
chown root:root /etc/hosts
chmod 644 /etc/hosts
chown root:root /etc/mtab*
chmod 644 /etc/mtab* # chmod 700: kdf arbeitet nicht
chown root:root /etc/login.defs
chmod 755 /etc/login.defs
chmod 755 -R /etc/firejail
chmod 755 -R /etc/xdg*
chmod 755 -R /etc/resolv.conf
chown root:root -R /etc/modprobe*
chmod 700 -R /etc/modprobe*
chmod 751 /opt # resp. 750, if user belongs to the group of root
chmod 751 /lib
chmod 700 /root
chmod 700 -R /etc/init.d
chmod 751 /initrd
chmod 751 /misc
chmod 700 -R /boot-save
chown root:root /usr/bin
chown root:root /usr/sbin
chown root:root /usr/lib64
chown root:root /usr/lib
chown root:root /usr/libexec
chown root:root /usr/share
chown root:root /root
chmod 700 /usr/bin/xterm # terminals (except your favorite one)
chmod 700 /usr/bin/aterm
chmod 700 /usr/bin/byobu*
chmod 700 /usr/bin/terminator*
chmod 700 /usr/bin/quadkonsole*
chmod 700 /usr/bin/lxterminal*
chmod 700 /usr/bin/yakuake*
chmod 700 /usr/bin/aterm
chmod 700 /usr/bin/multi-aterm
chmod 700 /usr/bin/tcsh*
chmod 700 /usr/bin/rxvt*
chown root:firejail /usr/bin/firejail
chmod 04750 /usr/bin/firejail # For this, surfuser must be a member of the primary group named firejail of firejail !
chmod 644 /etc/passwd
chmod 644 /etc/security/msec/*.secure
chmod 711 /home
chmod 700 /home/user
chmod 700 /home/surfuser
chmod 700 /home/uuidd
chmod 700 /home/toruser
chmod 700 -R /home/user/Dokumente
#
 # from permissions (OpenSuSE, chkstat), level: secure with some changes # from permissions (OpenSuSE, chkstat), level: secure with some changes
/ root:root 111
/root/ root:root 700
/tmp/ root:root 1777
/tmp/.X11-unix/ root:root 1777
/tmp/.ICE-unix/ root:root 1777
/dev/ root:root 755
/bin/ root:root 751
/sbin/ root:root 751
/lib/ root:root 751
/etc/ root:root 751
/home/ root:root 711
/boot/ root:root 755
/opt/ root:root 751
/usr/ root:root 755
/usr/local root:root 755
#
# /var:
#
/var/tmp/ root:root 1777
/var/log/ root:root 755
/var/spool/ root:root 755
/var/spool/mqueue/ root:root 700
/var/spool/news/ news:news 775
/var/spool/voice/ root:root 755
/var/spool/mail/ root:root 1777
/var/adm/ root:root 755
/var/adm/backup/ root:root 700
/var/cache/ root:root 755
/var/cache/man/ man:root 755
/var/run/nscd/socket root:root 666
/run/nscd/socket root:root 666
/var/run/sudo/ root:root 700
/run/sudo/ root:root 700
#
# login tracking
#
/var/log/lastlog root:root 644
/var/log/faillog root:root 600
/var/log/wtmp root:utmp 664
/var/log/btmp root:utmp 600
/var/run/utmp root:utmp 664
/run/utmp root:utmp 664
#
# some device files
#
/dev/zero root:root 666
/dev/null root:root 666
/dev/full root:root 666
/dev/ip root:root 660
/dev/initrd root:disk 660
/dev/kmem root:kmem 640
#
# /etc
#
/etc/lilo.conf root:root 600
/etc/passwd root:root 644
/etc/shadow root:shadow 400
/etc/init.d/ root:root 755
/etc/hosts root:root 644
# Changing the hosts_access(5) files causes trouble with services
# that do not run as root!
/etc/hosts.allow root:root 644
/etc/hosts.deny root:root 644
/etc/hosts.equiv root:root 644
/etc/hosts.lpd root:root 644
/etc/ld.so.conf root:root 644
/etc/ld.so.cache root:root 644
/etc/opiekeys root:root 600
/etc/ppp/ root:root 750
/etc/ppp/chap-secrets root:root 600
/etc/ppp/pap-secrets root:root 600
# sysconfig files:
/etc/sysconfig/network/providers/ root:root 700
# utempter
/usr/lib/utempter/utempter root:utmp 2755
# ensure correct permissions on ssh files to avoid sshd refusing
# logins (bnc#398250)
/etc/ssh/ssh_host_key root:root 600
/etc/ssh/ssh_host_key.pub root:root 644
/etc/ssh/ssh_host_dsa_key root:root 600
/etc/ssh/ssh_host_dsa_key.pub root:root 644
/etc/ssh/ssh_host_rsa_key root:root 600
/etc/ssh/ssh_host_rsa_key.pub root:root 644
/etc/ssh/ssh_config root:root 644
/etc/ssh/sshd_config root:root 640
#
# legacy
#
# new traceroute program by Olaf Kirch does not need setuid root any more.
/usr/sbin/traceroute root:root 755
# games:games 775 safe as long as we don´t change files below it (#103186)
# still people do it (#429882) so root:root 755 is the consequence.
/var/games/ root:root 0755
# No longer common. Set setuid bit yourself if you need it
# (#66191)
#/usr/bin/ziptool root:trusted 0755
#
# udev static devices (#438039)
#
/lib/udev/devices/net/tun root:root 0666
/lib/udev/devices/null root:root 0666
/lib/udev/devices/ptmx root:tty 0666
/lib/udev/devices/tty root:tty 0666
/lib/udev/devices/zero root:root 0666
#
# named chroot (#438045)
#
/var/lib/named/dev/null root:root 0666
/var/lib/named/dev/random root:root 0666
# opiesu is not allowed setuid root as code quality is bad (bnc#882035)
/usr/bin/opiesu root:root 0755
# we no longer make rpm build dirs 1777
/usr/src/packages/SOURCES/ root:root 0755
/usr/src/packages/BUILD/ root:root 0755
/usr/src/packages/BUILDROOT/ root:root 0755
/usr/src/packages/RPMS/ root:root 0755
/usr/src/packages/RPMS/alphaev56/ root:root 0755
/usr/src/packages/RPMS/alphaev67/ root:root 0755
/usr/src/packages/RPMS/alphaev6/ root:root 0755
/usr/src/packages/RPMS/alpha/ root:root 0755
/usr/src/packages/RPMS/amd64/ root:root 0755
/usr/src/packages/RPMS/arm4l/ root:root 0755
/usr/src/packages/RPMS/armv4l/ root:root 0755
/usr/src/packages/RPMS/armv5tejl/ root:root 0755
/usr/src/packages/RPMS/armv5tejvl/ root:root 0755
/usr/src/packages/RPMS/armv5tel/ root:root 0755
/usr/src/packages/RPMS/armv5tevl/ root:root 0755
/usr/src/packages/RPMS/armv6l/ root:root 0755
/usr/src/packages/RPMS/armv6vl/ root:root 0755
/usr/src/packages/RPMS/armv7l/ root:root 0755
/usr/src/packages/RPMS/athlon/ root:root 0755
/usr/src/packages/RPMS/geode/ root:root 0755
/usr/src/packages/RPMS/hppa2.0/ root:root 0755
/usr/src/packages/RPMS/hppa/ root:root 0755
/usr/src/packages/RPMS/i386/ root:root 0755
/usr/src/packages/RPMS/i486/ root:root 0755
/usr/src/packages/RPMS/i586/ root:root 0755
/usr/src/packages/RPMS/i686/ root:root 0755
/usr/src/packages/RPMS/ia32e/ root:root 0755
/usr/src/packages/RPMS/ia64/ root:root 0755
/usr/src/packages/RPMS/mips/ root:root 0755
/usr/src/packages/RPMS/noarch/ root:root 0755
/usr/src/packages/RPMS/pentium3/ root:root 0755
/usr/src/packages/RPMS/pentium4/ root:root 0755
/usr/src/packages/RPMS/powerpc64/ root:root 0755
/usr/src/packages/RPMS/powerpc/ root:root 0755
/usr/src/packages/RPMS/ppc64/ root:root 0755
/usr/src/packages/RPMS/ppc/ root:root 0755
/usr/src/packages/RPMS/s390/ root:root 0755
/usr/src/packages/RPMS/s390x/ root:root 0755
/usr/src/packages/RPMS/sparc64/ root:root 0755
/usr/src/packages/RPMS/sparc/ root:root 0755
/usr/src/packages/RPMS/sparcv9/ root:root 0755
/usr/src/packages/RPMS/x86_64/ root:root 0755
/usr/src/packages/SPECS/ root:root 0755
/usr/src/packages/SRPMS/ root:root 0755
#
# /etc
#
/etc/crontab root:root 600
/etc/exports root:root 644
/etc/fstab root:root 400
/etc/ftpusers root:root 644
/var/lib/nfs/rmtab root:root 644
/etc/syslog.conf root:root 600
/etc/ssh/sshd_config root:root 600
# we might want to tighten that up in the future in this profile (remove the
# ability for others to read/enter)
/etc/cron.d root:root 755
/etc/cron.daily root:root 755
/etc/cron.hourly root:root 755
/etc/cron.monthly root:root 755
/etc/cron.weekly root:root 755
#
# suid system programs that need the suid bit to work:
#
/bin/su root:root 4755
# disable at and cron for users that do not belnong to the group "trusted"
/usr/bin/at root:trusted 0750
/usr/bin/crontab root:trusted 0750
/usr/bin/gpasswd root:shadow 4755
/usr/bin/newgrp root:root 0755
/usr/bin/passwd root:shadow 4755
/usr/bin/chfn root:shadow 4755
/usr/bin/chage root:shadow 0755
/usr/bin/chsh root:shadow 0755
/usr/bin/expiry root:shadow 0755
/usr/bin/sudo root:root 4755
/usr/sbin/su-wrapper root:root 0755
# opie password system
#
/usr/bin/opiepasswd root:root 0755
#
/sbin/mount.nfs root:root 0755
#
#
/usr/bin/fusermount root:trusted 4750
# needs setuid root when using shadow via NIS:
#
/sbin/unix_chkpwd root:shadow 0755
/sbin/unix2_chkpwd root:shadow 0755
# squid changes
/var/cache/squid/ squid:root 0750
/var/log/squid/ squid:root 0750
/usr/sbin/pinger squid:root 0750
+capabilities cap_net_raw=ep
/usr/sbin/basic_pam_auth root:shadow 2750
# still to be converted to utempter
/usr/lib/gnome-pty-helper root:utmp 2755
#
# mixed section: most of it is disabled in this permissions.secure:
#
# video
/usr/bin/v4l-conf root:video 0750
# turned off write and wall by disabling sgid tty:
/usr/bin/wall root:tty 0755
/usr/bin/write root:tty 0755
# thttpd: sgid + executeable only for group www. Useless...
/usr/bin/makeweb root:www 2750
# pcmcia:
# Needs setuid to eject cards (#100120)
/sbin/pccardctl root:trusted 4750
# gnokii nokia cellphone software
# #66209
/usr/sbin/mgnokiidev root:uucp 755
# mailman mailing list software
# #66315
/usr/lib/mailman/cgi-bin/admin root:mailman 2755
/usr/lib/mailman/cgi-bin/admindb root:mailman 2755
/usr/lib/mailman/cgi-bin/edithtml root:mailman 2755
/usr/lib/mailman/cgi-bin/listinfo root:mailman 2755
/usr/lib/mailman/cgi-bin/options root:mailman 2755
/usr/lib/mailman/cgi-bin/private root:mailman 2755
/usr/lib/mailman/cgi-bin/roster root:mailman 2755
/usr/lib/mailman/cgi-bin/subscribe root:mailman 2755
/usr/lib/mailman/cgi-bin/confirm root:mailman 2755
/usr/lib/mailman/cgi-bin/create root:mailman 2755
/usr/lib/mailman/cgi-bin/editarch root:mailman 2755
/usr/lib/mailman/cgi-bin/rmlist root:mailman 2755
/usr/lib/mailman/mail/mailman root:mailman 2755
# libgnomesu (#75823, #175616)
/usr/lib/libgnomesu/gnomesu-pam-backend root:root 4755
#
# networking (need root for the privileged socket)
#
/usr/bin/ping root:root 0755
+capabilities cap_net_raw=ep
/usr/bin/ping6 root:root 0755
+capabilities cap_net_raw=ep
# mtr is linked against ncurses. no suid bit, for root only:
/usr/sbin/mtr root:dialout 0750
/usr/bin/rcp root:root 0000
/usr/bin/rlogin root:root 0000
/usr/bin/rsh root:root 0000
# exim
/usr/sbin/exim root:root 0755
#
# dialup networking programs
#
/usr/sbin/pppoe-wrapper root:dialout 4750
# i4l package (#100750):
/sbin/isdnctrl root:dialout 4750
# #66111
/usr/bin/vboxbeep root:trusted 0755
#
# linux text console utilities
#
# setuid needed on the text console to set the terminal content on ctrl-o
# #66112
/usr/lib/mc/cons.saver root:root 0755
#
# terminal emulators
# This and future SUSE products have support for the utempter, a small helper
# program that does the utmp/wtmp update work with the necessary rights.
# The use of utempter obsoletes the need for sgid bits on terminal emulator
# binaries. We mention screen here, but all other terminal emulators have
# moved to /etc/permissions, with modes set to 0755.
# needs setuid to access /dev/console
# framebuffer terminal emulator (japanese)
/usr/bin/jfbterm root:tty 0755
#
# kde
# (all of them are disabled in permissions.secure except for
# the helper programs)
#
# needs setuid root when using shadow via NIS:
# #66218
/usr/lib/kde4/libexec/kcheckpass root:shadow 4755
/usr/lib64/kde4/libexec/kcheckpass root:shadow 4755
/usr/lib/kde4/libexec/kdesud root:nogroup 2755
/usr/lib64/kde4/libexec/kdesud root:nogroup 2755
/usr/lib/libexec/kf5/kdesud root:nogroup 2755
/usr/lib64/libexec/kf5/kdesud root:nogroup 2755
# bnc#523833
/usr/lib/kde4/libexec/start_kdeinit root:root 4755
/usr/lib64/kde4/libexec/start_kdeinit root:root 4755
#
# amanda
#
/usr/sbin/amcheck root:amanda 0750
/usr/lib/amanda/calcsize root:amanda 0750
/usr/lib/amanda/rundump root:amanda 0750
/usr/lib/amanda/planner root:amanda 0750
/usr/lib/amanda/runtar root:amanda 0750
/usr/lib/amanda/dumper root:amanda 0750
/usr/lib/amanda/killpgrp root:amanda 0750
#
# gnats
#
/usr/lib/gnats/gen-index gnats:root 4555
/usr/lib/gnats/pr-edit gnats:root 4555
/usr/lib/gnats/queue-pr gnats:root 4555
#
# news (inn)
#
# the inn start script changes it´s uid to news:news. Later innbind
# is called by this user. Those programs do not need to be called by
# anyone else, therefore the strange permissions 4554 are required
# for operation. (#67032, #594393)
#
/usr/lib/news/bin/rnews news:uucp 4550
/usr/lib/news/bin/inews news:news 2555
/usr/lib/news/bin/innbind root:news 4550
#
# sendfax
#
# restrictive, only for "trusted" group users:
/usr/lib/mgetty+sendfax/faxq-helper fax:root 4755
/var/spool/fax/outgoing/ fax:root 0755
/var/spool/fax/outgoing/locks fax:root 0755
#
# uucp
#
/var/spool/uucppublic/ root:uucp 1770
/usr/bin/uucp uucp:uucp 6555
/usr/bin/uuname uucp:uucp 6555
/usr/bin/uustat uucp:uucp 6555
/usr/bin/uux uucp:uucp 6555
/usr/lib/uucp/uucico uucp:uucp 6555
/usr/lib/uucp/uuxqt uucp:uucp 6555
# pcp (bnc#782967)
/var/lib/pcp/tmp/ root:root 0755
/var/lib/pcp/tmp/pmdabash/ root:root 0755
/var/lib/pcp/tmp/mmv/ root:root 0755
/var/lib/pcp/tmp/pmlogger/ root:root 0755
/var/lib/pcp/tmp/pmie/ root:root 0755
# PolicyKit (#295341)
/usr/lib/PolicyKit/polkit-set-default-helper polkituser:root 4755
/usr/lib/PolicyKit/polkit-read-auth-helper root:polkituser 2755
/usr/lib/PolicyKit/polkit-revoke-helper root:polkituser 2755
/usr/lib/PolicyKit/polkit-explicit-grant-helper root:polkituser 2755
/usr/lib/PolicyKit/polkit-grant-helper root:polkituser 2755
/usr/lib/PolicyKit/polkit-grant-helper-pam root:polkituser 4750
# polkit new (bnc#523377)
/usr/lib/polkit-1/polkit-agent-helper-1 root:root 4755
/usr/bin/pkexec root:root 4755
# dbus-1 (#333361)
/lib/dbus-1/dbus-daemon-launch-helper root:messagebus 4750
/lib64/dbus-1/dbus-daemon-launch-helper root:messagebus 4750
# dbus-1 in /usr #1056764)
/usr/lib/dbus-1/dbus-daemon-launch-helper root:messagebus 4750
/usr/lib64/dbus-1/dbus-daemon-launch-helper root:messagebus 4750
# policycoreutils (#440596)
/usr/bin/newrole root:root 0755
# VirtualBox (#429725)
/usr/lib/virtualbox/VirtualBox root:vboxusers 0755
# bsc#1120650
/usr/lib/virtualbox/VirtualBoxVM root:vboxusers 0750
/usr/lib/virtualbox/VBoxHeadless root:vboxusers 0755
/usr/lib/virtualbox/VBoxSDL root:vboxusers 0755
# (bnc#533550)
/usr/lib/virtualbox/VBoxNetAdpCtl root:vboxusers 0755
# bnc#669055
/usr/lib/virtualbox/VBoxNetDHCP root:vboxusers 0755
# bsc#1033425
/usr/lib/virtualbox/VBoxNetNAT root:vboxusers 0755
# open-vm-tools (bnc#474285)
/usr/bin/vmware-user-suid-wrapper root:root 0755
# lockdev (bnc#588325)
/usr/sbin/lockdev root:lock 2755
# hawk (bnc#665045)
/usr/sbin/hawk_chkpwd root:haclient 4750
/usr/sbin/hawk_invoke root:haclient 4750
# chromium (bnc#718016)
/usr/lib/chrome_sandbox root:root 4755
# ecryptfs-utils (bnc#740110)
/sbin/mount.ecryptfs_private root:root 0755
# wireshark (bsc#957624)
/usr/bin/dumpcap root:wireshark 0750
+capabilities cap_net_raw,cap_net_admin=ep
# singularity (bsc#1028304)
# these have been dropped in version 2.4 (see bsc#1111411, comment 4)
#/usr/lib/singularity/bin/expand-suid root:singularity 4750
#/usr/lib/singularity/bin/create-suid root:singularity 4750
#/usr/lib/singularity/bin/export-suid root:singularity 4750
#/usr/lib/singularity/bin/import-suid root:singularity 4750
/usr/lib/singularity/bin/action-suid root:singularity 4750
/usr/lib/singularity/bin/mount-suid root:singularity 4750
/usr/lib/singularity/bin/start-suid root:singularity 4750
/usr/bin/su root:root 4755
/usr/bin/mount root:root 4755
/usr/bin/umount root:root 4755
# cdrecord of cdrtools from Joerg Schilling (bnc#550021)
# in secure mode, no provisions are made for reliable cd burning, as admins
# will have very likely prohibited that anyway.
/usr/bin/cdrecord root:root 755
/usr/bin/readcd root:root 755
/usr/bin/cdda2wav root:root 755
# qemu-bridge-helper (bnc#765948, bsc#988279)
/usr/lib/qemu-bridge-helper root:kvm 04750
# systemd-journal (bnc#888151)
/var/log/journal/ root:systemd-journal 2755
#iouyap (bnc#904060)
/usr/lib/iouyap root:iouyap 0750
# radosgw (bsc#943471)
/usr/bin/radosgw root:www 0750
+capabilities cap_net_bind_service=ep
# gstreamer ptp (bsc#960173)
/usr/lib/gstreamer-1.0/gst-ptp-helper root:root 0755
+capabilities cap_net_bind_service=ep
#
# suexec is only secure if the document root doesn´t contain files
# writeable by wwwrun. Make sure you have a safe server setup
# before setting the setuid bit! See also
# https://bugzilla.novell.com/show_bug.cgi?id=263789
# http://httpd.apache.org/docs/trunk/suexec.html
# You need to override this in permissions.local.
# suexec2 is a symlink for now, leave as-is
#
/usr/sbin/suexec root:root 0755
# newgidmap / newuidmap (bsc#979282, bsc#1048645)
/usr/bin/newgidmap root:shadow 4755
/usr/bin/newuidmap root:shadow 4755
# kwayland (bsc#1062182)
/usr/bin/kwin_wayland root:root 0755
+capabilities cap_sys_nice=ep
# gvfs (bsc#1065864)
/usr/lib/gvfs/gvfsd-nfs root:root 0755
# icinga2 (bsc#1069410)
/run/icinga2/cmd icinga:icingagmd 2750
# fping (bsc#1047921)
/usr/sbin/fping root:root 0755
+capabilities cap_net_raw=ep
# usbauth (bsc#1066877)
/usr/bin/usbauth-npriv root:usbauth 04750
/usr/lib/usbauth-notifier root:usbauth-notifier 0750
/usr/lib/usbauth-notifier/usbauth-notifier root:usbauth 02755
# spice-gtk (bsc#1101420)
/usr/bin/spice-client-glib-usb-acl-helper root:kvm 04750
# smc-tools (bsc#1102956)
/usr/lib/libsmc-preload.so root:root 04755
/usr/lib64/libsmc-preload.so root:root 04755
# lxc (bsc#988348)
/usr/lib/lxc/lxc-user-nic root:kvm 04750
# firejail (bsc#1059013)
/usr/bin/firejail root:firejail 04750 # For this, surfuser must be member of the primary group named firejail of firejail !
# authbind (bsc#1111251)
/usr/lib/authbind/helper root:root 04755
# fuse3 (bsc#1111230)
/usr/bin/fusermount3 root:trusted 04750
# 389-ds (bsc#1111564)
/usr/sbin/ns-slapd root:dirsrv 0750
/ root:root 111
/home root:root 711
/home/user user:user 700
/home/surfuser surfuser:surfuser 700
/home/toranonym toruser:torgroup 700
/usr/src root:root 700
/usr/lib64 root:root 751
/usr/lib64/kde4 root:root 751
/usr root:root 755
/bin root:root 751
/sbin root:root 751
/lib64 root:root 751
/lib root:root 751
/root root:root 700
/initrd root:root 751
/misc root:root 751
/boot-save root:root 000
/usr/games root:root 751
/net root:root 751
/secoff root:root 710
/sid-root root:root 700
/srv root:root 751
/sys root:root 751
/var root:root 751
/mnt root:root 755
/media root:root 711
/initrd root:root 751
/etc/security/msec/*.secure root:root 751
/usr/local root:root 755
/usr/local/Brother root:root 755
/GenuineIntel.bin root:root 710
/Module.symvers root:root 751
/usr/lib/cups root:sys 755
/usr/share/cups root:sys 755
/etc/cups root:sys 755
/smack root:root 700
/usr/share root:root 755
/usr/share/* root:root 755
/usr/libexec root:root 751
/usr/libexec/* root:root 755
/usr/lib64/kde4 root:root 751
/home/user/Dokumente user:user 700
/home/user/Dokumente/* user:user 700
/home/user/.kde4 user:user 700
/home/user/.kde4/* user:user 700
/home/user/.kde4/share/apps/kmail/mail user:user 700
/home/user/.kde4/share/apps/kmail/mail/*/*/* user:user 700
/home/surfuser/.mozilla surfuser:surfuser 100
/var/cache root:root 755
/var/cache/cups root:sys 775
/var/cache/cups/ppds.dat lp:sys 755
/var/cache/cups/job.cache root:sys 755
/var/cache/cups/help.index lp:sys 755
/var/cache/pdnsd pdnsd:pdnsd 755
/var/cache/pdnsd/pdnsd.cache pdnsd:pdnsd 755
/var/cache/coolkey root:root 755
/var/cache/urpmi root:root 755
/var/cache/apparmor root:root 755
/home/uuidd uuidd:uuidd 700
/usr/libexec root:root 755
/usr/lib/cups/filter root:sys 755 # Gruppe sys, abhängig von /etc/cups/cupsd.conf
/usr/lib/cups/filter/* root:sys 755
/usr/lib/cups/driver root:sys 755
/usr/lib/cups/driver/* root:sys 755
/usr/share/cups/ root:sys 755
/usr/share/cups/* root:sys 755
/usr/share/cups/model/ root:sys 755
/var/spool root:root 755
/var/spool/MailScanner root:root 755
/usr/lib/cups/filter/* root:sys 755
/usr/lib/cups/driver/* root:sys 755
/usr/share/cups/* root:sys 755
/etc/cups root:sys 755
/etc/cups/* root:sys 755
/var/cache/cups root:sys 775
/var/cache/cups/rss root:sys 775
/lib64/ld*.so root:root 755
/lib64/libc-*.so root:root 755
/usr/lib64/kde4 root:root 751
/usr/lib64/kde4/* root:root 755
/usr/share root:root 755
/usr/games root:root 751
/etc/security/msec/*.secure root:root 751
/usr/local root:root 755
/usr/share/* root:root 755
/usr/bin/rsh root:root 0000
/usr/bin/rlogin root:root 0000
/usr/bin/rcp root:root 0000
/usr/bin/telnet* root:root 0000
/usr/bin/scp root:root 0000
/kerberos/bin/rsh root:root 0000
/kerberos/bin/rlogin root:root 0000
/kerberos/bin/rcp root:root 0000
/kerberos/bin/telnet* root:root 0000
/home/user/.kde4/share/config root:root 755
/home/user/.kde4/share/apps root:root 755
/home/user/.kde4/share/icons root:root 755
Start permissions for example in /etc/rc.local: chkstat --set --no-fscaps /etc/permissions # rpm "permissions" from OpenSuSE (even possible for CentOS 6)
chkstat --set --no-fscaps /etc/permissions.secure # configuration from right above
chkstat --set --no-fscaps /etc/permissions.local # ... but configure it at first!
... oh, where does it belong to (this line went out)?: +capabilities cap_net_bind_service=ep
 CAPABILITIES CAPABILITIES
capsh, getcap, setcap, ...
linux - Using capsh to drop all capabilities - Stack Overflow
root: All caps are assigned to root by default !
pub enum Capability { CAP_CHOWN, CAP_DAC_OVERRIDE, CAP_DAC_READ_SEARCH, CAP_FOWNER, CAP_FSETID, CAP_KILL, CAP_SETGID, CAP_SETUID, CAP_SETPCAP Drops the capability for the current process via a call to cap_drop_bound.0x0000003fffffffff=cap_chown,cap_dac_override,cap_dac_read_search,cap_fowner,cap_fsetid,cap_kill,cap_setgid,cap_setuid,cap_setpcap,cap_linux_immutable,cap_net_bind_service,cap_net_broadcast,cap_net_admin,cap_net_raw,cap_ipc_lock,cap_ipc_owner,cap_sys_module,cap_sys_rawio,cap_sys_chroot,cap_sys_ptrace,cap_sys_pacct,cap_sys_admin,cap_sys_boot,cap_sys_nice,cap_sys_resource,cap_sys_time,cap_sys_tty_config,cap_mknod,cap_lease,cap_audit_write,cap_audit_control,cap_setfcap,cap_mac_override,cap_mac_admin,cap_syslog,cap_wake_alarm,cap_block_suspend,37...
Capabilities:
capsh --print Current: = Bounding set = Securebits: 00/0x0/1´b0 secure-noroot: no (unlocked) secure-no-suid-fixup: no (unlocked) secure-keep-caps: no (unlocked) uid=10101(u0_a101) gid=10101...
/etc/permissions.secure :
...
/usr/sbin/pinger squid:root 0750
+capabilities cap_net_raw=ep
...
/usr/bin/ping root:root 0755
+capabilities cap_net_raw=ep
...
stackoverflow.com/questions/28811823/using-capsh-to-drop-all-capabilities
 /etc/rc.local (complete, vollständig) /etc/rc.local (complete, vollständig)
#!/bin/sh
#
### BEGIN INIT INFO
# Provides: rc.local
# X-Mandriva-Compat-Mode
# Default-Start: 2 3 4 5
# Short-Description: Local initialization script
# Description: This script will be executed *after* all the other init scripts.
# You can put your own initialization stuff in here if you don´t
# want to do the full Sys V style init stuff.
### END INIT INFO
sysctl -p /etc/sysctl.conf
auditctl -e0
echo 1 > /sys/devices/system/cpu/microcode/reload
# microcode_ctl -Qu
sh /usr/libexec/microcode_ctl/reload_microcode
hdparm -W1a0A0 /dev/sda # mausklick-schnelle SSD am S-ATA-Port, beachte die Anschlussnummer (1: sda, 2: sdb, ...)
echo deadline > /sys/block/sdb/queue/scheduler
echo 500 > /proc/sys/vm/dirty_writeback_centisecs
echo 20 > /proc/sys/vm/dirty_ratio
echo 5 > /proc/sys/vm/dirty_background_ratio
echo 1 > /proc/sys/net/ipv6/conf/all/disable_ipv6
echo 1 > /proc/sys/net/ipv4/tcp_syncookies
echo "" > /etc/securetty
# https://en.wikipedia.org/wiki/TCP_congestion-avoidance_algorithm
# cat /proc/sys/net/ipv4/tcp_congestion_control
# modprobe tcp_htcp
modprobe sch_fq_codel
modprobe tcp_cubic
# modprobe tcp_bbr
# echo sch_fq_codel > /proc/sys/net/core/default_qdisc
echo cubic > /proc/sys/net/ipv4/tcp_congestion_control
macchanger --mac=ac:22:ca:00:00:c1 eth0
echo sch_fq_codel > /proc/sys/net/core/default_qdisc
xhost -
xhost +si:localuser:user
xhost -inet6:user@
xhost -nis:user@
xhost - 192.168.178.1
xhost - 192.168.178.40
# echo 1 > /proc/sys/net/ipv4/conf/all/hidden # or net.ipv4.conf.all.hidden=1 within /etc/sysctl.conf
# echo 1 > /proc/sys/net/ipv4/conf/eth0/hidden
# echo 1 > /proc/sys/net/ipv4/conf/all/secure_redirects
# echo 0 > /proc/sys/net/ipv4/conf/all/shared_media
# echo 1 > /proc/sys/net/ipv4/conf/eth0/secure_redirects
# echo 0 > /proc/sys/net/ipv4/conf/eth0/shared_media
touch /var/lock/subsys/local
modprobe usblp
modprobe usb_storage
ifconfig eth0 -multicast
ifconfig lo -multicast
ifconfig lo -broadcast
ip link set eth0 multicast off
ip link set lo multicast off
sh /etc/init.d/ip6tables restart # wenn iptables-ipv6 (el6) neben iptables (el6) installiert worden ist; Der gesamte Traffic innerhalb des neuen Adressraums IPv6 wird auf INPUT, OUTPUT und FORWARD mit Linfw3 geblockt, siehe Regeln innerhalb /etc/sysconfig/ip6tables. Anstelle dieses totalen Blocks können alle IPv4-Regeln von Linfw3 in /usr/local/LINFW3.sh nach /etc/sysconfig/ip6tables übernommen werden, indem ipt="iptables" mit ipt="ip6tables" ausgestauscht wird. Überprüfe außerdem, ob /sbin/ip6tables* richtig mit /sbin/ip6tables-multi verlinkt ist.
mount -t securityfs -o rw,noatime /sys/kernel/security /mnt2
#sh /etc/init.d/syslog start
sh /etc/init.d/rsyslog start
cp -fp /etc/hosts.savenew /etc/hosts
cp -fp /etc/pdnsd-savenew.conf /etc/pdnsd.conf
# cp -fp /boot-save/ifcfg-eth0* /etc/sysconfig/network-scripts/
cp -fp /boot-save/70-persistent-net.rules /etc/udev/rules.d/
export RESOLV_HOST_CONF="/etc/hosts"
# sh /etc/init.d/incrond start
# sh /etc/init.d/noflushd start
# gpg-agent --daemon --use-standard-socket
# atieventsd
# dhclient -4 -cf /etc/dhcp/dhclient.conf eth0 &
# NetworkManager --log-level=ERR
# preload
# ifup eth0
# acpid&
# dnssec-triggerd
# unbound -dv -c /etc/unbound/unbound.conf
# tcpd &
# sh /etc/init.d/xfs start
# sh /etc/init.d/psad start
# paxctld -c /etc/paxctld.conf -d -p /var/run/paxctld
# dnscrypt-proxy --daemonize --user=pdnsd --local-address 127.0.0.2:53 -r 192.168.178.1 -l --tcp-port 443 /dev/null
# dnscrypt-proxy --daemonize --user=pdnsd --local-address 127.0.0.2:53 -r 208.67.222.222 --tcp-port 443 -l /dev/null
# dnscrypt-proxy --daemonize --user=pdnsd --local-address 127.0.0.2:53 -r 213.73.91.35 --tcp-port 443 -l /dev/null
# cp -fp /var/cache/pdnsd.cache /var/cache/pdnsd-savenew.cache
# speechd
# artsd&
# killall plymouthdxhost -
# sh /etc/init.d/lpd start
# redshift -l 60:10 -t 6500K:6200K&
sh /etc/init.d/modules-disabled start# kernel.modules_disabled=1, here after 45 seconds
chkstat --set --no-fscaps /etc/permissions # rpm permissions form OpenSuSE
chkstat --set --no-fscaps /etc/permissions.secure
#apparmor_parser -af /etc/apparmor/profiles/extras/usr.lib.firefox.firefox &
#apparmor_parser -af /etc/apparmor/profiles/sbin.dhclient &
#apparmor_parser -af /etc/apparmor/profiles/usr.bin.man &
#apparmor_parser -af /etc/apparmor/profiles/usr.bin/passwd &
#apparmor_parser -af /etc/apparmor/profiles/extras/usr.lib.firefox.sh &
# /usr/lib64/apparmorapplet&
unshare apparmor-dbus &
echo "ALLOW_REBOOT=yes" >> /etc/security/msec/security.conf
echo "BASE_LEVEL=secure" > /etc/security/msec/security.conf
echo "ENABLE_STARTUP_MSEC=yes" > /etc/security/msec/security.conf
echo "ENABLE_STARTUP_PERMS=enforce" > /etc/security/msec/security.conf
msec -f secure # msec: rpm from Mandriva Linux and Rosalabs
# chmod 666 /dev/usb/lp0 # besser: Sämtliche chown und chmod in /etc/permissions.secure in der vorgesehenen Form eintragen!
chown pdnsd:pdnsd -R /var/cache/pdnsd
chmod 755 /var/cache/pdnsd/pdnsd.cache
chown root:root /etc/hosts
chmod 400 /usr/local/key
chmod 644 /etc/hosts
chmod 111 /
chmod 751 /etc
chmod 755 /etc/sysconfig/network
chmod 755 /etc/sysconfig/network-scripts
chmod 400 /etc/shadow*
chmod 400 /etc/fstab*
chmod 700 /etc/crypttab*
chmod 700 /etc/mtab*
chmod 711 /home
chmod 700 /home/user
chmod 700 /home/surfuser
chmod 700 -R /home/surfuser/.mozilla
chown root:root /home/surfuser/.mozilla/firefox/profile.default/user.js
chmod 755 /home/surfuser/.mozilla/firefox/profile.default/user.js
chown root:root /home/surfuser/.mozilla/firefox/prefs.js
chmod 755 /home/surfuser/.mozilla/firefox/prefs.js
chmod 700 -R /home/surfuser/.moon*
chmod 700 -R /usr/src
chmod 751 /etc/X11
chmod 751 /usr/lib64
chmod 751 /usr/lib64/kde4
chmod 700 /home/toruser
chmod 700 -R /home/user/Dokumente
chmod 700 /home/uuidd
chmod 400 /usr/local/ke*
chmod 755 /usr
chmod 751 /bin
chmod 751 /sbin
chmod 751 /lib64
chmod 751 /opt
chmod 751 /lib
chmod 700 /root
chmod 700 -R /etc/init.d
chmod 751 /initrd
chmod 751 /misc
chmod 700 -R /boot-save
chmod 644 /etc/passwd
chmod 751 /usr/games
chmod 751 /net
chmod 710 /secoff
chmod 700 /sid-root
chmod 700 /smack
chmod 751 /srv
chmod 751 /sys
chmod 700 /typo3i*
chmod 751 /var
chmod 700 /lost*found
chmod 710 /intel-ucode*
chmod 751 /initrd
chmod 710 /GenuineIntel.bin
chmod 751 /etc/security/msec/*.secure
chmod 751 /Module.symvers
rm -df /home/surfuser/.Xauth*.*
rm -df /home/surfuser/.xauth*
rm -df /home/toruser/.xauth*
rm -df /home/toruser/.Xauth*.*
rm -df /home/user/.kde4/share/apps/kmail/mail/Spam/cur/*
rm -df /var/spool/cups/a*
rm -df /var/spool/cups/b*
rm -df /var/spool/cups/c*
rm -df /var/spool/cups/d*
rm -df /var/spool/cups/e*
rm -df /var/spool/cups/f*
rm -df /var/spool/cups/g*
rm -df /var/spool/cups/h*
rm -df /var/spool/cups/i*
rm -df /var/spool/cups/j*
rm -df /var/spool/cups/k*
rm -df /var/spool/cups/l*
rm -df /var/spool/cups/m*
rm -df /var/spool/cups/o*
rm -df /var/spool/cups/p*
rm -df /var/spool/cups/q*
rm -df /var/spool/cups/r*
rm -df /var/spool/cups/s*
rm -df /var/spool/cups/u*
rm -df /var/spool/cups/v*
rm -df /var/spool/cups/w*
rm -df /var/spool/cups/x*
rm -df /var/spool/cups/y*
rm -df /var/spool/cups/z*
echo ´V´ > /dev/watchdog
sh /etc/init.d/dosetfacls start# Script dosetfacls right up in the following
exit
 Also create file (runlevel-init-script) Also create file (runlevel-init-script)
/etc/init.d/dosetfacls
 Erzeuge noch Erzeuge noch
/etc/init.d/dosetfacls
#!/bin/sh
#
# This is file /etc/rc.d/init.d/linfw3 and was put here
# by the linfw3 rpm
#
# chkconfig: 2345 92 36
#
# description: secure iptables based firewall against all hacker and trojans \
# evtl. change chkconfig Number!
#
# ********************************************************************
#
# File : $Source: /cvsroot/ijbswa/current/linfw3.init,v $
#
# Purpose : This shell script takes care of starting and stopping
# linfw3.
#
# Copyright : Written by Gooken
# http://www.gooken.de
#
#
#
# ********************************************************************/
# Source function library.
. /etc/rc.d/init.d/functions
start () {
# start daemon
setfacl -m u:-1:- /* # There is an unnamed (!) process starting from time to time by user so called "-1, root".... listed on the buttom of the listing from ps -aux (gamin, FAM?)
setfacl -m u:-1:- /mnt
setfacl -m u:-1:- /media
setfacl -m u:apache:- /home/user
setfacl -m u:apache:- /home/surfuser
setfacl -m u:apache:- /home/toranonym
setfacl -m u:apache:- /mnt
setfacl -m u:apache:- /media
setfacl -m u:surfuser:- /etc/shadow*
setfacl -m u:toranonym:- /etc/shadow*
setfacl -m u:surfuser:- /etc/fstab*
setfacl -m u:surfuser:- /etc/mtab*
setfacl -m u:surfuser:- /etc/crypttab*
setfacl -m u:toranonym:- /etc/fstab*
setfacl -m u:toranonym:- /etc/mtab*
setfacl -m u:toranonym:- /etc/crypttab*
setfacl -m u:surfuser:- /etc/init.d
setfacl -m u:surfuser:- /etc/init.d/*
setfacl -m u:toranonym:- /etc/init.d
setfacl -m u:toranonym:- /etc/init.d/*
setfacl -m u:surfuser:- /etc/rc0.d
setfacl -m u:surfuser:- /etc/rc1.d
setfacl -m u:surfuser:- /etc/rc2.d
setfacl -m u:surfuser:- /etc/rc3.d
setfacl -m u:surfuser:- /etc/rc4.d
setfacl -m u:surfuser:- /etc/rc5.d
setfacl -m u:surfuser:- /etc/rc6.d
setfacl -m u:surfuser:- /etc/rc.local
setfacl -m u:toranonym:- /etc/rc0.d
setfacl -m u:toranonym:- /etc/rc1.d
setfacl -m u:toranonym:- /etc/rc2.d
setfacl -m u:toranonym:- /etc/rc3.d
setfacl -m u:toranonym:- /etc/rc4.d
setfacl -m u:toranonym:- /etc/rc.local
setfacl -m u:surfuser:- /etc/security/msec
setfacl -m u:surfuser:- /etc/security
setfacl -m u:toranonym:- /etc/security
setfacl -m u:toranonym:- /etc/security/msec
setfacl -m u:surfuser:- /etc/crypttab*
setfacl -m u:surfuser:- /usr/bin/*
setfacl -x surfuser /usr/bin/bash*
setfacl -x surfuser /usr/bin/unshare
setfacl -x surfuser /usr/bin/firejail*
setfacl -x surfuser /usr/bin/firefox*
setfacl -x surfuser /usr/bin/gftp*
setfacl -x surfuser /usr/bin/tor*
setfacl -x surfuser /usr/bin/xauth*
setfacl -x surfuser /usr/bin/xargs*
setfacl -x surfuser /usr/bin/sg*
setfacl -x surfuser /usr/bin/palemoon*
setfacl -x surfuser /usr/bin/export
setfacl -x surfuser /usr/bin/thunderbird*
setfacl -x surfuser /usr/bin/gpg-agent*
setfacl -m u:surfuser:- /usr/libexec
setfacl -m u:surfuser:- /usr/sbin
setfacl -m u:surfuser:--x /bin
setfacl -m u:surfuser:- /bin/*
setfacl -m u:surfuser:- /sbin
setfacl -x surfuser /bin/bash*
setfacl -x surfuser /bin/certtool
setfacl -x surfuser /bin/certutil
setfacl -x surfuser /bin/basename
setfacl -x surfuser /bin/bash.old
setfacl -x surfuser /bin/p11tool
setfacl -x surfuser /bin/pk12util
setfacl -x surfuser /bin/smime
setfacl -x surfuser /bin/shlibsign
setfacl -x surfuser /bin/sign*
setfacl -x surfuser /bin/ssltap*
setfacl -m u:surfuser:--x /home/surfuser
setfacl -m u:toranonym:- /home/surfuser
setfacl -m u:surfuser:- /usr/local
setfacl -m u:surfuser:- /opt
setfacl -m u:surfuser:--x /lib64
setfacl -m u:surfuser:--x /usr/lib64
setfacl -m u:surfuser:--x /lib
setfacl -m u:surfuser:--x /usr/lib
setfacl -m u:surfuser:- /misc
setfacl -m u:surfuser:- /net
setfacl -m u:surfuser:- /sid-root
setfacl -m u:surfuser:--x /etc
setfacl -m u:surfuser:- /intel-ucode
setfacl -m u:surfuser:--x /secoff
setfacl -m u:surfuser:- /smack
setfacl -m u:surfuser:- /srv
setfacl -m u:surfuser:- /--tcp-port
setfacl -m u:surfuser:- /initrd
setfacl -m u:surfuser:- /ttf
setfacl -m u:surfuser:- /none
setfacl -m u:surfuser:- /doc
setfacl -m u:surfuser:- /firejail
setfacl -m u:surfuser:- /root
setfacl -m u:surfuser:- /usr/lib64/kde4/*
setfacl -x surfuser /usr/lib64/kde4/libexec
setfacl -m u:surfuser:- /usr/lib64/kde4/libexec/*
setfacl -x surfuser /usr/lib64/kde4/libexec/kdesu*
return
}
case "$1" in
start)
start
;;
*)
gprintf "Usage: %s {start|stop|restart|status}
" "$LINFW3_PRG"
exit 1
esac
exit $RETVAL
Notice: toranonym is our elder account for tor. Now it´s surfuser too - as general for browsing, but can be used for more privilidges, for many, many processes like for chats or global mapping like marble. surfuser only is enough - just reset belonging setfacl process by process to allow by option -x
Exchange $ again with the dollar-character... and start it each boot within /etc/rc.local by the command "sh /etc/init.d/dosetfacls start" !
 Change File Attributes (chattr) for example for data integrity ( option -i ) Change File Attributes (chattr) for example for data integrity ( option -i )
man chattr
User-Extended-Attributes must be set for the belonging partitions!
Also notice the many configuration files in the home-directory, that might get changed by you or automatically. We would resign from "chattr +i" upon them.
chattr +i -R /boot
chattr +i /etc/hosts* # Neben Root-Eigentumsrechten wichtiger Schutz vor Server-Pharming
chattr +i /etc/fstab
chattr +i /home/surfuser/.mozilla
chattr +i /home/surfuser/.mozilla/firefox/*.js
chattr +i /home/surfuser/.mozilla/firefox/profile.default/user.js
chattr +i /home/surfuser/torrc
chattr +i /home/surfuser/geoip*
chattr +i -R /home/user/.*
chattr +i -R /home/user/*
chattr -i -R /home/user/.dbus
chattr -i /home/user/.cache
chattr -i -R /home/user/.gnupg
chattr -i -R /home/user/.pulse*
chattr -i /home/user/.screenrc*
chattr -i /home/user/.esd_auth*
chattr -i /home/user/.Xauthority*
chattr -i /home/user/.Xdefaults*
chattr -i /home/user/.xsession*
chattr -i -R /home/user/.gconf*
chattr -i -R /home/user/.local*
chattr -i -R /home/user/.mcop*
chattr -i -R /home/user/.qt*
chattr -i -R /home/user/.kde*
chattr -i -R /home/user/.wine*
chattr -i -R /home/.MANY_GAMES_CONFIGS
chattr -i -R /home/user/.config*
... und create as described further above the belonging two runlevel-init-scripts (daemons) in /etc/init.d namens rc.local and dosetfacl.
Register those two scripts and active them by default in higher runlevels:
chkconfig --add rc.local && chkconfig --add dosetfacl
Advantage: regardless from packet-installations, significant ACL-access-rights were set each system boot. This keeps the system secure and makes it mouse-click-fast.
Additionally, the grsecurity-patches for the kernel (resp. root-kernel-processes), login-lock /sbin/nologin and password-protection and locking of all system- and user-accounts excecpt surfuser (and maybe a separate toruser), Sandbox Firejail (especially for the lock of the shells/terminals) and Firewall Linfw3 get in use too, beneath Tor resp. the tor-browser with firefox-extensions for script-filtering like ABP, noscript and RequestPolicyBlockContinued and more get in use too.
Set setfacl -m u:surfuser:- /usr/bin/* except for /usr/bin/bash, /usr/bin/firefox, /usr/bin/firejail, /usr/bin/sg, /usr/bin/proftp*, /usr/bin/tor*, /usr/bin/export, /usr/bin/xauth*, /usr/bin/xarg* and all communication programs, surfuser should be able to use.
 rsyslog anstelle syslogd rsyslog anstelle syslogd
Rsyslog is an enhanced multi-threaded syslogd supporting, among others, MySQL, PostgreSQL, syslog/tcp, RFC 3195, permitted sender lists, filtering on any message part, and fine grain output format control. It is quite compatible to stock sysklogd and can be used as a drop-in replacement. Its advanced features make it suitable for enterprise-class, encryption protected syslog relay chains while at the same time being very easy to setup for the novice user. o lmnet.so - Implementation of network related stuff. o lmregexp.so - Implementation of regexp related stuff. o lmtcpclt.so - This is the implementation of TCP-based syslog clients. o lmtcpsrv.so - Common code for plain TCP based servers. o imtcp.so - This is the implementation of the TCP input module. o imudp.so - This is the implementation of the UDP input module. o imuxsock.so - This is the implementation of the Unix sockets input module. o imklog.so - The kernel log input module for Linux. o immark.so - This is the implementation of the build-in mark message input module. o imfile.so - This is the input module for reading text file data.
You have to delete all *syslog*-init-script-files out of /etc/rc*.d/ and /etc/init.d/ .
/etc/rsyslog.conf
# rsyslog v5 configuration file
# For more information see /usr/share/doc/rsyslog-*/rsyslog_conf.html
# If you experience problems, see http://www.rsyslog.com/doc/troubleshoot.html
#### MODULES ####
DollarsignModLoad imuxsock # provides support for local system logging (e.g. via logger command)
Dollarsignimklog # provides kernel logging support (previously done by rklogd)
#DollarsignModLoad immark # provides --MARK-- message capability
# Provides UDP syslog reception
#$ModLoad imudp
#$UDPServerRun 514
# Provides TCP syslog reception
#$ModLoad imtcp
#$InputTCPServerRun 514
#### GLOBAL DIRECTIVES ####
# Use default timestamp format
$ActionFileDefaultTemplate RSYSLOG_TraditionalFileFormat
# File syncing capability is disabled by default. This feature is usually not required,
# not useful and an extreme performance hit
#$ActionFileEnableSync on
# Include all config files in /etc/rsyslog.d/
$IncludeConfig /etc/rsyslog.d/*.conf
#### RULES ####
# Log all kernel messages to the console.
# Logging much else clutters up the screen.
#kern.* /dev/console
# Log anything (except mail) of level info or higher.
# Don´t log private authentication messages!
*.warn;mail.none;news.none;authpriv.none;cron.none /tmp/messages
# The authpriv file has restricted access.
authpriv.* /tmp/secure
# Log all the mail messages in one place.
mail.* -/tmp/maillog
# Log cron stuff
cron.* /tmp/cron
# Everybody gets emergency messages
*.emerg *
# Save news errors of level crit and higher in a special file.
uucp,news.crit /tmp/spooler
# Save boot messages also to boot.log
local7.* /tmp/boot.log
# ### begin forwarding rule ###
# The statement between the begin ... end define a SINGLE forwarding
# rule. They belong together, do NOT split them. If you create multiple
# forwarding rules, duplicate the whole block!
# Remote Logging (we use TCP for reliable delivery)
#
# An on-disk queue is created for this action. If the remote host is
# down, messages are spooled to disk and sent when it is up again.
#$WorkDirectory /var/lib/rsyslog # where to place spool files
#$ActionQueueFileName fwdRule1 # unique name prefix for spool files
#$ActionQueueMaxDiskSpace 1g # 1gb space limit (use as much as possible)
#$ActionQueueSaveOnShutdown on # save messages to disk on shutdown
#$ActionQueueType LinkedList # run asynchronously
#$ActionResumeRetryCount -1 # infinite retries if host is down
# remote host is: name/ip:port, e.g. 192.168.0.1:514, port optional
#*.* @@remote-host:514
# ### end of the forwarding rule ###
#
# INN
#
news.=crit /tmp/news/news.crit
news.=err /tmp/news/news.err
news.notice /tmp/news/news.notice
news.=debug /tmp/news/news.debug
 /proc/sys/* - Kernel-flags &Co.: detailed configuration /proc/sys/* - Kernel-flags &Co.: detailed configuration
sysctl.conf - variables are files out of /proc/sys
check settings by "sysctl -a"
# Kernel sysctl configuration file
# /etc/sysctl.conf
# sysctl settings are defined through files in
# /usr/lib/sysctl.d/, /run/sysctl.d/, and /etc/sysctl.d/.
#
# Vendors settings live in /usr/lib/sysctl.d/.
# To override a whole file, create a new file with the same in
# /etc/sysctl.d/ and put new settings there. To override
# only specific settings, add a file with a lexically later
# name in /etc/sysctl.d/ and put new settings there.
#
# For more information, see sysctl.conf(5) and sysctl.d(5).
# Kernel sysctl configuration file for CentOS and Mandriva Linux
#
# For binary values, 0 is disabled, 1 is enabled. See sysctl(8) and
# sysctl.conf(5) for more details.
# /etc/sysctl.conf
# additionally from http://joshrendek.com/2013/01/securing-ubuntu/ resp. http://www.nsa.gov/ia/_files/os/redhat/rhel5-guide-i731.pdf
# Turn on execshild
# kernel.exec-shield = 1
# Controls the System Request debugging functionality of the kernel
kernel.sysrq =0
net.ipv6.conf.lo.use_tempaddr = 0
# Disables IP dynaddr
net.ipv4.ip_dynaddr = 1
# Disable ECN
net.ipv4.tcp_ecn = 1
# Controls source route verification
net.ipv4.conf.all.rp_filter =1
net.ipv4.conf.default.rp_filter = 1
net.ipv4.tcp_congestion_control=cubic
# Do not accept source routing
net.ipv4.conf.default.accept_source_route = 0
# Controls the System Request debugging functionality of the kernel
kernel.sysrq =0
# kernel.modules_disabled=0
# kernel.exec-shield=1
# Controls whether core dumps will append the PID to the core filename.
# Useful for debugging multi-threaded applications.
kernel.core_uses_pid = 0
# If the kptr_restrict value is 0, kernel addresses are provided without limitations (recommended).
# If the kptr_restict value is 1, addresses are provided if the current user has a CAP_SYSLOG
# capability.
# If the kptr_restrict value is 2, the kernel addresses are hidden regardless of privileges the
# current user has.
kernel.kptr_restrict=2
kernel.dmesg_restrict = 1
# kernel.yama.ptrace_scope=3
# If you set this variable to 1 then cd tray will close automatically when the
# cd drive is being accessed.
# Setting this to 1 is not advised when supermount is enabled
# (as it has been known to cause problems)
dev.cdrom.autoclose=1
dev.cdrom.autoeject=1
# removed to fix some digital extraction problems
# dev.cdrom.check_media=1
# to be able to eject via the device eject button (magicdev)
dev.cdrom.lock=0
# Disable netfilter on bridges.
#net.bridge.bridge-nf-call-ip6tables = 0
#net.bridge.bridge-nf-call-iptables = 0
#net.bridge.bridge-nf-call-arptables = 0
net.ipv4.ip_forward =0
# Do not send ICMP redirects (we are not a router)
net.ipv4.conf.all.send_redirects = 0
net.ipv4.conf.default.send_redirects = 0
net.ipv4.tcp_max_syn_backlog =512
# Do not accept IP source route packets (we are not a router)
net.ipv4.conf.all.accept_source_route = 0
net.ipv4.conf.all.accept_redirects = 0
net.ipv4.conf.default.accept_redirects = 0
net.ipv4.conf.all.secure_redirects = 1
net.ipv4.conf.default.accept_source_route = 0
net.ipv4.conf.default.accept_redirects = 0
net.ipv4.conf.default.secure_redirects = 0
net.ipv4.tcp_syncookies = 1
net.ipv4.conf.all.log_martians = 1
net.ipv4.conf.all.shared_media = 0
net.ipv4.conf.eth0.secure_redirects=1
net.ipv4.conf.eth0.shared_media=0
# Increase system IP port limits
net.ipv4.ip_local_port_range = 2000 65000
# Increase TCP max buffer size setable using setsockopt()
net.ipv4.tcp_rmem = 4096 87380 8388608
net.ipv4.tcp_wmem = 4096 87380 8388608
net.ipv6.conf.eth0.disable_ipv6=1
net.ipv6.conf.all.disable_ipv6 = 1
net.ipv6.conf.default.router_solicitations=0
net.ipv4.tcp_syncookies = 1
net.ipv6.conf.default.accept_ra_rtr_pref=0
net.ipv6.conf.default.accept_ra_pinfo=0
net.ipv6.conf.default.accept_ra_defrtr=0
net.ipv6.conf.default.autoconf=0
net.ipv6.conf.default.dad_transmits=0
net.ipv6.conf.default.max_addresses=0
#
# ls /lib/modules/´uname -r´/kernel/net/ipv4/
# modprobe tcp_htcp
# modprobe tcp_cubic
# modprobe tcp_bbr
# net.core.default_qdisc=sch_fq_codel
net.ipv4.tcp_congestion_control=cubic
# BBR
# net.core.default_qdisc=fq
# net.ipv4.tcp_congestion_control=bbr
# Increase Linux auto tuning TCP buffer limits
# min, default, and max number of bytes to use
# set max to at least 4MB, or higher if you use very high BDP paths
net.core.somaxconn=65535
net.core.optmem_max=25165824
net.core.rmem_max =212992
net.core.wmem_max =212992
net.core.rmem_default =212992
net.core.wmem_default =212992
net.core.netdev_max_backlog = 1000
#
kernel.sysrq = 0
kernel.core_uses_pid = 1
# Optimization for port usefor LBs
# Increase system file descriptor limit
fs.file-max=65535
fs.protected_hardlinks=1
fs.protected_symlinks=1
fs.protected_regular=1
# fs.protected_fifos=1 # this might cause overflow of processes akonadi_maildir: system runs out of capacities
# fs.dir-notify-enable=0
# fs.mount-max=20
fs.suid_dumpable=0
# The kernel allocates aio memory on demand, and this number limits the
# number of parallel aio requests; the only drawback of a larger limit is
# that a malicious guest could issue parallel requests to cause the kernel
# to set aside memory. Set this number at least as large as
# 128 * (number of virtual disks on the host)
# Libvirt uses a default of 1M requests to allow 8k disks, with at most
# 64M of kernel memory if all disks hit an aio request at the same time.
# fs.aio-max-nr = 1048576
# Allow for more PIDs (to reduce rollover problems); may break some programs 32768
kernel.pid_max=65536
net.ipv4.tcp_syncookies = 1
kernel.msgmnb = 65536
kernel.msgmax = 65536
kernel.shmmax = 3294967295
kernel.shmall = 3294967295
kernel.randomize_va_space = 2
net.ipv4.tcp_fin_timeout =3600
net.ipv4.tcp_keepalive_time =7200
net.ipv4.tcp_keepalive_probes =7
net.ipv4.tcp_syn_retries =6
net.ipv4.tcp_retries1 =1
net.ipv4.tcp_retries2 =3
net.ipv4.tcp_retrans_collapse =1
net.ipv4.tcp_sack =1
net.ipv4.ip_default_ttl =64
net.ipv4.ipfrag_time =30
net.ipv4.ip_no_pmtu_disc =0
net.unix.max_dgram_qlen =10
vm.overcommit_memory =2
vm.overcommit_ratio=200
# or: vm.overcommit_kbytes=
vm.page-cluster =3
vm.oom_dump_tasks =0
vm.dirty_ratio=20
vm.dirty_writeback_centisecs=500
vm.dirty_background_ratio=5
kernel.ctrl-alt-del =1
kernel.panic =0
kernel.acct =4 2 30
# Uncomment the following to stop low-level messages on console
#kernel.printk = 3 4 1 3
kernel.printk =0 6 1 3
kernel.printk_ratelimit = 5 # period to wait in seconds
kernel.printk_ratelimit_burst = 60 # max. amount same time
kernel.shmall =-1
# If the kptr_restrict value is 0, kernel addresses are provided without limitations (recommended).
# If the kptr_restict value is 1, addresses are provided if the current user has a CAP_SYSLOG capability.
# If the kptr_restrict value is 2, the kernel addresses are hidden regardless of privileges the current user has.
kernel.kptr_restrict=2
# ptrace: process tracing
# kernel.yama.ptrace_scope=3
dev.raid.speed_limit_min =1000
dev.raid.speed_limit_max =200000
net.ipv4.conf.all.rp_filter=1
net.ipv4.tcp_window_scaling=1
net.ipv4.tcp_timestamps=0
net.ipv4.conf.all.log_martians=1
net.ipv4.icmp_echo_ignore_all=1
net.ipv4.icmp_echo_ignore_broadcasts=1
net.ipv4.icmp_ignore_bogus_error_responses=1
net.ipv4.tcp_congestion_control=cubic
net.ipv4.conf.all.secure_redirects=1
net.ipv4.conf.all.shared_media=0
net.ipv4.conf.eth0.secure_redirects=1
net.ipv4.conf.eth0.shared_media=0
# The kernel allocates aio memory on demand, and this number limits the
# number of parallel aio requests; the only drawback of a larger limit is
# that a malicious guest could issue parallel requests to cause the kernel
# to set aside memory. Set this number at least as large as
# 128 * (number of virtual disks on the host)
# Libvirt uses a default of 1M requests to allow 8k disks, with at most
# 64M of kernel memory if all disks hit an aio request at the same time.
# fs.aio-max-nr = 1048576
http://www.linux-admins.net/2010/09/all-you-need-to-know-about-procsys.html
Example for ulimit, ulimit -a and sysctl -a, https://forum.altlinux.org/index.php?topic=4786.0
Link
ln -sf /usr/sbin/sysctl /sbin/sysctl
Test sysctl.conf: sysctl -p /etc/sysctl.conf and activate an error-free sysctl by daemon or in /etc/rc.local
sysctl -p /etc/sysctl.config
 Disable Unwanted SUID- and SGID-Binaries Disable Unwanted SUID- and SGID-Binaries
All SUID/SGID bits enabled file can be misused when the SUID/SGID executable has a security problem or bug. All local or remote user can use such file. It is a good idea to find all such files. Use the find command as follows:
#See all set user id files:
find / -perm +4000
# See all group id files
find / -perm +2000
# Or combine both in a single command
find / ( -perm -4000 -o -perm -2000 ) -print
find / -path -prune -o -type f -perm +6000 -ls
You need to investigate each reported file. See reported file man page for further details.
https://www.cyberciti.biz/tips/linux-security.html
 How to Remove (Delete) Symbolic Links in Linux, linuxize.com, 09.05.2019 How to Remove (Delete) Symbolic Links in Linux, linuxize.com, 09.05.2019
A symbolic link, also known as a symlink, is a special type of file that points to another file or directory. It is something like a shortcut in Windows. A symlink can point to a file or a directory on the same or a different filesystem or partition.
In this guide, we will show you how to remove (delete) symbolic links in Linux/UNIX systems using the rm, unlink, and find commands.
...
find /path/to/directory -maxdepth 1 -xtype l
https://linuxize.com/post/how-to-remove-symbolic-links-in-linux/
 Safe-Linking: Making Linux exploitation harder, itweb.co.za, 05.22.2020 Safe-Linking: Making Linux exploitation harder, itweb.co.za, 05.22.2020
Businesses and users alike are constantly on the lookout for easier ways to do things, and shortcuts that help us work faster and with less effort. Unfortunately, bad actors are no different, and are always hunting for existing vulnerabilities or weaknesses, that can be exploited.
[...] A good example of this would be memory corruption attacks, which are often employed to exploit programs written in Linux, the most widely-used open source operating system in the world.
With this in mind, Check Point has created Safe-Linking, a security mechanism to protect the internal structure of the heap - or the portion of memory that is not set to a constant size before compilation and can be controlled dynamically by a programmer - from being tampered with.
[...] Simply put, Safe-Linking removes the address data for the program, so the bad actor can no longer be sure where in the system´s memory it will be loaded - making it much harder for them to launch an exploit against the program," the company adds.
https://www.itweb.co.za/content/Kjlyrvw1ejVMk6am
https://reportcybercrime.com/safe-linking-making-linux-exploitation-harder/
Check Point schließt 20 Jahre alte Sicherheitslücke in Linux, trojaner-info.de, 26.05.2020
Das Check Point Research Team führt eine neue Schutzmaßnahme für das Betriebssystem ein, die sich Safe-Linking nennt. Uralte Schwachstelle endlich geschlossen.
Das Check Point Research Team führt eine neue Sicherheitsmethode ein, um Linux-Systeme um einiges sicherer zu machen. Den Sicherheitsforschern gelang es, eine 20 Jahre alte und bestens bekannte Sicherheitslücke endlich zu schließen.
https://www.trojaner-info.de/sicher-anonym-im-internet/
aktuelles/check-point-schliesst-20-jahre-alte-sicherheitsluecke-in-linux.html
[...] In our latest research, we created a security mechanism, called "Safe-Linking", to protect malloc()´s single-linked lists from tampering by an attacker. We successfully pitched our approach to maintainers of core open-source libraries, and it is now integrated into the most common standard library implementation: glibc (Linux) and its popular embedded counterpart: uClibc-NG.
https://www.terabitweb.com/2020/05/21/safe-linking-eliminating-a-20-year-old-malloc-exploit-primitive/
 User auditing - The Big Brother is watching you User auditing - The Big Brother is watching you
If you are really paranoid you might want to add a system-wide configuration to audit, what the users are doing in your system. This sections presents some tips using diverse utilities you can use.
- Input and output audit with script, 4.11.10.1
- Using the shell history file, 4.11.10.2
- Complete user audit with accounting utilities, 4.11.10.3
- Other user auditing methods, 4.11.10.4
- Reviewing user profiles, 4.11.11
- Limiting what users can see/access, 4.11.13
- Limiting access to other user´s information, 4.11.13.1
- Generating user passwords, 4.11.14
- Checking user passwords
 kauditd and auditd: Linux Audit Kernel Subsystem and Linux Audit System kauditd and auditd: Linux Audit Kernel Subsystem and Linux Audit System
Who does audit the code?
kauditd: internal kernel-auditing, for example of windows-titles out of Firefox online.
Kernel-interner audit-Daemon kauditd: URL, Webseiten-Inhalte: Fentstertitel, ... (online mit Browsern wie Firefox)
"00:00:12 [kauditd] dbadmin 4182 1 4182 0 1 May18 00:02:19 /opt/vertica/spread/sbin/spread -c /home/dbadmin/DatabaseName/v_DatabaseName_node0001_catalog/spread.conf..."
https://forum.vertica.com/discussion/236239/vertica-service-not-starting-after-server-reboot
kauditd is a kernel process, which is a part of the Linux kernel responsible for the kernel audit events (and communicates with the auditd process). The special brackets surrounding it are telling you that this is not a regular (userland) process (launched through a command), but a kernel process (started/managed by the Linux kernel itself)
https://wiki.gentoo.org/wiki/SELinux/Tutorials/The_security_context_of_a_process
The auditd is provided for system auditing. It is responsible for writing audit records to the disk. During startup, the rules in /etc/audit.rules are read by this daemon. You can open /etc/audit.rules file and make changes such as setup audit file log location and other option. With auditd you can answers the following questions:
System startup and shutdown events (reboot / halt).
Date and time of the event.
User respoisble for the event (suh as trying to access /path/to/topsecret.dat file).
Type of event (edit, access, delete, write, update file &commands).
Success or failure of the event.
Records events that modify date and time.
Find out who made changes to modify the system´s network settings.
Record events that modify user/group information.
See who made changes to a file etc.
See our quick tutorial which explains enabling and using the auditd service.
https://www.cyberciti.biz/tips/linux-security.html
 kauditd und auditd: Kernel- und Linux Audit System kauditd und auditd: Kernel- und Linux Audit System
Who does audit the audit code?
How to use Auditing System in Linux - Configure, Audit Logs and ...
Well, the Linux Auditing system is the answer for all the above questions. The Linux Auditing system allows an administrator to configure audit rules to monitor the system calls, network access, files etc…and generate a summary report - which can be later analyzed and investigated for suspicious activity.
https://techglimpse.com/how-to-use-auditing-system-in-linux-configure-audit-logs-and-generate-reports/
See our quick tutorial which explains enabling and using the auditd service.
https://www.cyberciti.biz/tips/linux-security.html
 Router: Howto detect instrusive attempts within the Fritzbox-menu, PC-WELT.de, 04.19.2021 Router: Howto detect instrusive attempts within the Fritzbox-menu, PC-WELT.de, 04.19.2021
https://www.pcwelt.de/tipps/Einbruchsversuche-in-Fritzbox-Menue-aufdecken-11007603.html
The Linux audit subsystem is not one of the best-loved parts of the kernel. It allows the creation of a log stream documenting specific system events — system calls, modifications to specific files, actions by processes with certain user IDs, etc. For some, it is an ideal way to get a handle on what is being done on the system and, in particular, to satisfy various requirements for security certifications (Common Criteria, for example). For others, it is an ugly and invasive addition to the kernel that adds maintenance and runtime overhead without adding useful functionality. More recently, though, it seems that audit adds some security holes of its own. But the real problem, perhaps, is that almost nobody actually looks at this code, so bugs can lurk for a long time.
The system call auditing mechanism creates audit log entries in response to system calls; the system administrator can load rules specifying which system calls are to be logged. These rules can include various tests on system call parameters, but there is also a simple bitmask, indexed by system call number, specifying which calls might be of interest. One of the first things done by the audit code is to check the appropriate bit for the current system call to see if it is set; if it is not, there is no auditing work to be done.
[...] In summary, the code is a giant mess. The way it works is nearly incomprehensible. It contains at least one severe bug. I´d love to see it fixed, but for now, distributions seem to think that enabling CONFIG_AUDITSYSCALL is a reasonable thing to do, and I´d argue that it´s actually a terrible choice for anyone who doesn´t actually need syscall audit rules. And I don´t know who needs these things.
It is telling, though, that this particular vulnerability has existed in the audit subsystem almost since its inception. The audit code receives little in the way of review; most kernel developers simply turn it off for their own kernels and look the other way. But this subsystem is just the sort of thing that distributors are almost required to enable in their kernels; some users will want it, so they have to turn it on for everybody. As a result, almost all systems out there have audit enabled (look for a running kauditd thread), even though few of them are using it. These systems take a performance penalty just for having audit enabled, and they are vulnerable to any issues that may be found in the audit code.
If audit were to be implemented today, the developer involved would have to give some serious thought, at least, to using the tracing mechanism. It already has hooks applied in all of the right places, but those hooks have (almost) zero overhead when they are not enabled. Tracing has its own filtering mechanism built in; the addition of BPF-based filters will make that feature more capable and faster as well. In a sense, the audit subsystem contains yet another kernel-based virtual machine that makes decisions about which events to log; using the tracing infrastructure would allow the removal of that code and a consolidation to a single virtual machine that is more widely maintained and reviewed.
The audit system we have, though, predates the tracing subsystem, so it could not have been based on tracing. Replacing it without breaking users would not be a trivial job, even in the absence of snags that have been glossed over in the above paragraph (and such snags certainly exist). So we are likely stuck with the current audit subsystem (which will certainly not be marked "broken" in the mainline kernel) for the foreseeable future. Hopefully it will receive some auditing of its own just in case there are more old surprises lurking therein.
Posted May 30, 2014 6:50 UTC (Fri) by bnorris (subscriber, #92090) [Link]
&g; As a result, almost all systems out there have audit enabled
$ grep CONFIG_AUDIT /boot/config-´uname -r´
CONFIG_AUDIT_ARCH=y
CONFIG_AUDIT=y
CONFIG_AUDITSYSCALL=y
CONFIG_AUDIT_WATCH=y
CONFIG_AUDIT_TREE=y
( You might want to comment them in ... )
> (look for a running kauditd thread)
None here.
&g; even though few of them are using it. These systems take a performance penalty just for having audit enabled, and they are vulnerable to any issues that may be found in the audit code.
I´m not an expert on the kaudit subsystem (in fact, I just learned of it), but it looks like kauditd is only spawned in response to a user-space request for it (e.g. from SELinux auditd). See kernel/audit.c:...
https://lwn.net/Articles/600568/
man auditd
man auditd.conf
Disable auditd temporarily (this will disable logging instantly but will not survive a reboot):
 auditctl -e0 # for example within /etc/rc.local auditctl -e0 # for example within /etc/rc.local
Disable auditd permanently (this will require a reboot):
systemctl disable auditd
http://kb.ictbanking.net/article.php?id=632
 kauditd - CentOS | Forum kauditd - CentOS | Forum
kauditd. General support questions including new installations. How to disable kauditd? I tried to put audit=0 to the kernel line in grub, but no luck....
www.centos.org/forums/viewtopic.php?t=10899
kauditd might care for connection even with SELinux from NSA. So why did he had no luck with it? Boot-parameter "audit=0" (for grub: within /boot/grub/menu.lst) does prevent from kernel audit named kauditd ever starting: no auditing like firefox by the kernel anymore!
 Disable the OOM Killer (process oom_reaper), The Ubuntu Forum Community, Ubuntu Specialised Support, January 2nd, 2014 Disable the OOM Killer (process oom_reaper), The Ubuntu Forum Community, Ubuntu Specialised Support, January 2nd, 2014
As the title suggests, regardless of the repercussions, how do you disable this "feature".
Please do not provide alternate suggestions such as "get more ram" or "tell the program to use less memory".
I´m running a Minecraft server that has its heap space and permgen configured to use nearly all of the available memory on the vps where it resides. I have a highly specific reason for doing this and no, it has never caused me any problems in the past.
Yes the OOM Killer is killing the process see: OOM killed process 659 (java) vm:4973220kB, rss:2066504kB, swap:0kB
Who ever thought killing processes that are consuming beyond a specific amount of memory was a good idea, you have caused me and, the users of my server immeasurable levels of frustration. I am no Linux guru, so any help would be appreciated so long as that help reads "To disable the oom-killer do X".
Thank you in advance.
Re: Disable the OOM Killer
http://thetechnick.blogspot.com/2010...-on-linux.html
http://www.oracle.com/technetwork/ar...r-1911807.html
The OOM killer can be completely disabled with the following command. This is not recommended for production environments, because if an out-of-memory condition does present itself, there could be unexpected behavior depending on the available system resources and configuration. This unexpected behavior could be anything from a kernel panic to a hang depending on the resources available to the kernel at the time of the OOM condition.
sysctl vm.overcommit_memory=2 # mouseclick-fast
echo "vm.overcommit_memory=2" >> /etc/sysctl.conf
[...] Re: Disable the OOM Killer
Hi, Psionic,
I was having the same difficulties. You report that the oom-killer is still killing your process, I suggest either properly fully disabling the oom-killer or lowering the overcommit ratio, as follows:
Disabling OOM Killer
According to: https://www.kernel.org/doc/Documenta...ups/memory.txt
Code:
You can disable the OOM-killer by writing "1" to memory.oom_control file, as:
# echo 1 > memory.oom_control # (unknown variable by sysctl, remark, Gooken)
Reducing Overcommit Ratio
According to https://www.kernel.org/doc/Documenta...mit-accounting
Code:
2 - Don´t overcommit. The total address space commit for the system is not permitted to exceed swap + a configurable amount (default is 50%) of physical RAM.
Depending on the amount you use, in most situations this means a process will not be killed while accessing pages but will receive errors on memory allocation as appropriate.
Useful for applications that want to guarantee their memory allocations will be available in the future without having to initialize every page.
The overcommit policy is set via the sysctl ´vm.overcommit_memory´.
The overcommit amount can be set via ´vm.overcommit_ratio´ (percentage) or ´vm.overcommit_kbytes´ (absolute value).
There´s a rather good article on this topic http://www.linuxdevcenter.com/pub/a/...ry.html?page=1
Of course, in general if you´re getting processes killed it means there´s a problem with using more memory than the system can cope with, and the symptoms are very likely to come out somewhere else. In my case the oom-killer was definitely picking the right process, even though it was the primary purpose of the whole computer: the program had a data-dependent bug and was allocating memory out of control.
I hope that helps.
Kind regards,
...
https://serverfault.com/questions/606185/how-does-vm-overcommit-memory-work
More about oom_reaper
ttps://stackoverflow.com/questions/35791416/how-to-disable-the-oom-killer-in-linux
https://lwn.net/Articles/666024/
https://lwn.net/Articles/668126/
https://code.woboq.org/linux/linux/mm/oom_kill.c.html
https://www.oracle.com/technical-resources/articles/it-infrastructure/dev-oom-killer.html
https://superuser.com/q/1150215
https://ubuntuforums.org/showthread.php?t=2197016
https://askubuntu.com/q/1188024
https://unix.stackexchange.com/q/432171
https://blog.csdn.net/s_lisheng/article/details/82192613
 rtkit-daemon (rpm rtkit) rtkit-daemon (rpm rtkit)
Description: "RealtimeKit is a D-Bus system service that changes the scheduling policy of user processes/threads to SCHED_RR (i.e. realtime scheduling mode) on request. It is intended to be used as a secure mechanism to allow real-time scheduling to be used by normal user processes.".
https://fr2.rpmfind.net/
"I´s...a management daemon so to say. Instead of applications asking the kernel directly (and needing proper permissions for this, usually root) they ask the daemon. The daemon can hand out the realtime permissions then according it its configuration (/etc/dbus-1/system.d/org.freedesktop.RealtimeKit1.conf). It´s simply a helper process that allows applications to ask for realtime permissions through dbus...not really much more. But having such a helper process makes the whole procedure much more secure (no suid root needed for some programs), cleaner (dbus interface) and more flexible (one daemon to configure, not each program with an own configuration..if at all)."
For rtkit isn´t almost needed, as we got told in the internet above, and there are no real dependencies from it, it´ might not be a bad idea to deinstall it:
"rpm -e --nodeps rtkit"
... same eventually with Packagekit (el6), gvfsd (gvfs (el6) and so on: just deinstall them! The less (not really needed daemons do run under root, the more secure the system might behave...
 netns, migration/0, kintgerityd, oom_reaper, ... ( one of them lists the actual website-title!) netns, migration/0, kintgerityd, oom_reaper, ... ( one of them lists the actual website-title!)
Kernel-daemons almost can´t get deactivated manually! This might be possible by removing some (not needed) kernel-modules by rmmod, delmod or kernel-configuration only (within file .config).
 netns netns
Running strongSwan in Network Namespaces (netns) on Linux
Normally, the network stack (interfaces, routing tables, firewall rules etc.) is shared by all processes running on an operating system. With Linux network namespaces (netns) it´s possible to have multiple separate instances of the network stack.
Note: While basic support for network namespaces was added to the Linux kernel a long time ago, some features (e.g. CLUSTERIP support) might require a recent kernel.
The easiest way to work with network namespaces is to use the ip command of the iproute2 package. These commands will have to be executed as root (i.e. with sudo on most distros).
Network Namespace Basics
To create a new netns use the following command:
# ip netns add <network namespace name>
A list of all currently defined netns is provided by ip netns list.
Interfaces can be assigned to a netns with the ip link command:
# ip link set <interface name netns <netns name>
If you run ip link list afterwards such an interface won´t be seen as it is only available in the configured netns.
So to actually list the interface in a specific netns it´s required to be able to run commands in a specific netns. This can be done with the ip netns exec command. So to get a list of interfaces defined in a specific netns use:
# ip netns exec <netns name> ip link list
If only one physical interface is available, or if you don´t want to assign physical interfaces to the netns for other reasons, it´s possible to create virtual Ethernet interface pairs (veth, provided via CONFIG_VETH). These are like a bi-directional pipe (i.e. what´s written to one end comes out the other and vice-versa) of which one end is placed inside the netns and the other stays outside in the "default" or "global" namespace.
To create such a pair use:
# ip link add <interface name 1> type veth peer name <interface name 2>
This creates two connected Enthernet interfaces with the given names. One is assigned to a netns (via ip link) the other is not (it doesn´t matter which one and it´s also possible to assign both interfaces to two different netns to connect them). How the outer interface is used depends on the use case, it may be put inside a bridge, or used in routing rules to route traffic to and from a netns.
Since interfaces assigned to a netns are disabled they have to be enabled first, and they will probably also require an IP address, which can be done with:
# ip netns exec <netns name> ip addr add x.x.x.x/x dev <iface name>
# ip netns exec <netns name> ip link set dev <iface name> up
Similar to these commands routes or firewall rules may be added by running ip route or iptables inside a specific netns via ip netns exec <command.
Running a single instance of strongSwan inside a netns is straight-forward. Simply run ipsec commands via ip netns exec ipsec <command>.
But more interesting is probably running multiple instances of strongSwan in separate namespaces. Because all netns share the same file system this is a bit tricky.
Luckily, the ip netns exec command provides a helpful feature: Every file found in /etc/netns/<name>/ for a given netns is bind mounted over its corresponding counterpart in /etc (so it has to exist there). This can be used to provide different config files for each instance, but may also be used to redirect the so called piddir, where the charon and starter daemons create their PID files and UNIX sockets (the default is to use /var/run, which would conflict if multiple instances would use it).
To do so make sure strongSwan is configured with --sysconfdir=/etc and e.g. --with-piddir=/etc/ipsec.d/run. Then after building and installing strongSwan the piddirs can be created as follows:
# mkdir -p /etc/ipsec.d/run
# mkdir -p /etc/netns/<netns name 1>/ipsec.d/run
# mkdir -p /etc/netns/<netns name 2>/ipsec.d/run
https://wiki.strongswan.org/projects/strongswan/wiki/Netns
 StrongSwan is an OpenSource IPsec-based VPN Solution for Linux * runs both on Linux 2.4 (KLIPS IPsec) and Linux 2.6 (NETKEY IPsec) kernels * implements both the IKEv1 and IKEv2 (RFC 4306) key exchange protocols * Fully tested support of IPv6 IPsec tunnel and transport connections * Dynamical IP address and interface update with IKEv2 MOBIKE (RFC 4555) * Automatic insertion and deletion of IPsec-policy-based firewall rules * Strong 128/192/256 bit AES or Camellia encryption, 3DES support * NAT-Traversal via UDP encapsulation and port floating (RFC 3947) * Dead Peer Detection (DPD, RFC 3706) takes care of dangling tunnels * Static virtual IPs and IKEv1 ModeConfig pull and push modes * XAUTH server and client functionality on top of IKEv1 Main Mode authentication * Virtual IP address pool managed by IKE daemon or SQL database * Secure IKEv2 EAP user authentication (EAP-SIM, EAP-AKA, EAP-MSCHAPv2, etc.) * Optional relaying of EAP messages to AAA server via EAP-RADIUS plugin * Support of IKEv2 Multiple Authentication Exchanges (RFC 4739) * Authentication based on X.509 certificates or preshared keys * Generation of a default self-signed certificate during first strongSwan startup * Retrieval and local caching of Certificate Revocation Lists via HTTP or LDAP * Full support of the Online Certificate Status Protocol (OCSP, RCF 2560). * CA management (OCSP and CRL URIs, default LDAP server) * Powerful IPsec policies based on wildcards or intermediate CAs * Group policies based on X.509 attribute certificates (RFC 3281) * Storage of RSA private keys and certificates on a smartcard (PKCS #11 interface) * Modular plugins for crypto algorithms and relational database interfaces * Support of elliptic curve DH groups and ECDSA certificates (Suite B, RFC 4869) * Optional built-in integrity and crypto tests for plugins and libraries * Smooth Linux desktop integration via the strongSwan NetworkManager applet This package triggers the installation of both, IKEv1 and IKEv2 daemons. StrongSwan is an OpenSource IPsec-based VPN Solution for Linux * runs both on Linux 2.4 (KLIPS IPsec) and Linux 2.6 (NETKEY IPsec) kernels * implements both the IKEv1 and IKEv2 (RFC 4306) key exchange protocols * Fully tested support of IPv6 IPsec tunnel and transport connections * Dynamical IP address and interface update with IKEv2 MOBIKE (RFC 4555) * Automatic insertion and deletion of IPsec-policy-based firewall rules * Strong 128/192/256 bit AES or Camellia encryption, 3DES support * NAT-Traversal via UDP encapsulation and port floating (RFC 3947) * Dead Peer Detection (DPD, RFC 3706) takes care of dangling tunnels * Static virtual IPs and IKEv1 ModeConfig pull and push modes * XAUTH server and client functionality on top of IKEv1 Main Mode authentication * Virtual IP address pool managed by IKE daemon or SQL database * Secure IKEv2 EAP user authentication (EAP-SIM, EAP-AKA, EAP-MSCHAPv2, etc.) * Optional relaying of EAP messages to AAA server via EAP-RADIUS plugin * Support of IKEv2 Multiple Authentication Exchanges (RFC 4739) * Authentication based on X.509 certificates or preshared keys * Generation of a default self-signed certificate during first strongSwan startup * Retrieval and local caching of Certificate Revocation Lists via HTTP or LDAP * Full support of the Online Certificate Status Protocol (OCSP, RCF 2560). * CA management (OCSP and CRL URIs, default LDAP server) * Powerful IPsec policies based on wildcards or intermediate CAs * Group policies based on X.509 attribute certificates (RFC 3281) * Storage of RSA private keys and certificates on a smartcard (PKCS #11 interface) * Modular plugins for crypto algorithms and relational database interfaces * Support of elliptic curve DH groups and ECDSA certificates (Suite B, RFC 4869) * Optional built-in integrity and crypto tests for plugins and libraries * Smooth Linux desktop integration via the strongSwan NetworkManager applet This package triggers the installation of both, IKEv1 and IKEv2 daemons.
https://fr2.rpmfind.net
Block network access of a process, unix.stackexchange.com
It is possible to block the (outgoing) network access of a single process in different ways: by unshare / nsenter, ip-netns, iptables, apparmor and firejail.
https://unix.stackexchange.com/questions/68956/block-network-access-of-a-process
 Notice: We use right above mentioned command "unshare" for starting firejail (for sandboxing firefox (including for example libtrace.so of different file-sizes the versions) by the command "unshare firejail..." etc)., psad (/etc/init.d/psad: prog="unshare psad"), uuidd (/etc/init.d/uuidd with prog="unshare uuidd" and "daemon.... unshare $DAEMON" within the start-function, apparmor-dbus out of /etc/rc.local, messagebus (/etc/init.d/messagebus with processname="unshare dbus-daemon", dbus), gpm (/etc/init.d/gpm with "daemon "unshare /usr/sbin/gpm" -m ... ), cups (/etc/init.d/cups with "daemon "unshare cups" ...), dm (again in /etc/init.d/dm) and Notice: We use right above mentioned command "unshare" for starting firejail (for sandboxing firefox (including for example libtrace.so of different file-sizes the versions) by the command "unshare firejail..." etc)., psad (/etc/init.d/psad: prog="unshare psad"), uuidd (/etc/init.d/uuidd with prog="unshare uuidd" and "daemon.... unshare $DAEMON" within the start-function, apparmor-dbus out of /etc/rc.local, messagebus (/etc/init.d/messagebus with processname="unshare dbus-daemon", dbus), gpm (/etc/init.d/gpm with "daemon "unshare /usr/sbin/gpm" -m ... ), cups (/etc/init.d/cups with "daemon "unshare cups" ...), dm (again in /etc/init.d/dm) and
one of the best things you can do ever, the securing with we hope by option --tcp nolisten configured X-server (root-process X):
X (X11, ServerCmd=/usr/bin/unshare /usr/bin/X within (resp., to be more concrete, follow the linking of) /usr/share/config/kdm/kdmrc: enhance the command for execution of X with unshare: "ServerCmd=/usr/bin/unshare /usr/bin/X" and "Willing=/usr/bin/unshare /usr/share/X11/xdm/Xwilling"), kdm (/usr/share/config/kdm/kdmrc with "Preloader=/usr/bin/unshare /usr/bin/preloadkde", haldaemon (/etc/init.d/haldaemon), udevd (in /sbin/start_udev with "else /usr/bin/unshare /sbin/udevd -d ..."), polkitd (/etc/xdg/polkit-gnome-authentification-agent-1.desktop: "exec=unshare /usr/libexec/polkit-gnome-authentication-agent-1" and /etc/xdg-polkit-kde-authentification-agent-1.desktop: "exec=unshare /usr/libexec/polkit-kde-authentification-agent-1 ), konsole and xterm, dolphin, drakconf.real resp. drakconf (MCC), network-ready-games like gl-117, trackballs, extremetuxracer, marsshooter, freedroidrpg, orbital, xonotic etc. in future (do them all just to be careful)! Some kernel-modules like for usblp for USB-printer by unshare (for example in /etc/rc.loca): unshare COMMA-ABOVE-FOR-EXECUTIONmodprobe usblpCOMMA-ABOVE-FOR-EXECUTION,
graphic-card (just experimentel): unshare COMMA-ABOVE-FOR-EXECUTIONi915COMMA-ABOVE-FOR-EXECUTION, mainboard (just experimentel!): unshare COMMA-ABOVE-FOR-EXECUTIONlpc_ichCOMMA-ABOVE-FOR-EXECUTION, (less experimentel): unshare COMMA...modprobe videoCOMMA..., but still NOT functioning are those "unshared" ones for internal kernel-processs like kernel-daemon netns (/etc/rc.local): "unshare --net --mount -p pidof netns", oom_reaper (/etc/rc.local): "unshare --net --mount -p pidof oom_reaper", migration/0 (/etc/rc.local): "unshare --net --mount -p pidof migration/0". Also try firejail for a sandboxed network namespace by option net, netfilter, join-network=name|pid and netns, see man firejai, section join-network for good examples also doing fine with Linfw3 (through iptables-restore and iptables-save) or try slirp4netns (OpenSuSE 15.2).
rsyslog (runlevel-init-script /etc/init.d/rsyslog, line with daemon: .daemon --pidfile="$PIDFILE" unshare $exec -i "$PIDFILE&uqot; $SYSLOGD_OPTIONS
... eventually try the same with unshare within /etc/init.d/cups!
Especially hardening the root- and suid-processes by unshare makes the computer secure (as quit all remaining riscs do depend from kernel-processes now) and, as we, believe it or not, really meant having recognized, very mouseclick-fast too!
It couldn´t be easier and more simple to contribute to the highest security level ever: You just have to type "unshare" right before quit each program´t;s and daemon´s (scripts out of /etc/init.d) start, regardless from starting by terminal, out of the menu or by any runlevel-init-script and script !
 Always open resp. start programs resp. applications not allowed to communicate in any net with unshare or with adequate options of firejail, even within the terminal, k-menu, context-menu (service-menu), directory desktop, quick starter and quick launcher! Use unshare even for firejail itself, especially whenever firejail got a sandbox for the a browser like firefox: we show the complete resulting command for this case further below! Always open resp. start programs resp. applications not allowed to communicate in any net with unshare or with adequate options of firejail, even within the terminal, k-menu, context-menu (service-menu), directory desktop, quick starter and quick launcher! Use unshare even for firejail itself, especially whenever firejail got a sandbox for the a browser like firefox: we show the complete resulting command for this case further below!
OK, we show the meant command to start Tor and Firefox by Firejail through unshare ( unexplaineds ) from further below already right at this place:
 sg surfgroup "unshare firejail --nice=19 --profile=/etc/firejail/firefox.profile /usr/lib64/firefox/firefox --no-remote &" && sg surfgroup "unshare firejail --nice=19 --profile=/etc/firejail/palemoon.profile tor -f /home/surfuser/torrc" && export RESOLV_HOST_CONF="/etc/hosts" sg surfgroup "unshare firejail --nice=19 --profile=/etc/firejail/firefox.profile /usr/lib64/firefox/firefox --no-remote &" && sg surfgroup "unshare firejail --nice=19 --profile=/etc/firejail/palemoon.profile tor -f /home/surfuser/torrc" && export RESOLV_HOST_CONF="/etc/hosts"
 watchdogd: How can I disable a watchdog, once it has been enabled? watchdogd: How can I disable a watchdog, once it has been enabled?
Normally to shut down the watchdog driver you have to write a ´V´ character to /dev/watchdog which you could do from a root bash prompt just with:
echo ´V´ > /dev/watchdog
However, before you try to create your own watchdog driver take a look at the existing Linux watchdog daemon to see, if it can do the job. A good start is my page here: http://www.sat.dundee.ac.uk/~psc/watchdog/Linux-Watchdog.html
https://unix.stackexchange.com/questions/144588/how-can-i-disable-a-watchdog-once-it-has-been-enabled
 Increase kernel integrity with disabled Linux kernel modules loading Increase kernel integrity with disabled Linux kernel modules loading
Increasing Linux kernel integrity
Disable loading kernel module on Linux systems, linux-audit.com
The Linux kernel can be configured to disallow loading new kernel modules. This feature is especially useful for high secure systems, or if you care about securing your system to the fullest. In this article, we will have a look at the configuration of this option. At the same time allowing legitimate kernel modules to be loaded.
Disable kernel modules
Newer kernel modules have a sysctl variable named kernel.modules_disabled.
Sysctl is the tool which allows you to see and change kernel settings of a running system. The related /etc/sysctl.conf file is used to ensure that your settings are also used at the next boot of the system.
The sysctl key kernel.modules_disabled is very straightforward. If it contains a "1" it will disable loading new modules, where a"0" will still allow loading them.
Using this option will be a great protection against loading malicious kernel modules. For example, it may help to counter rootkits. Needless to say, but when someone was already been able to gain root access, you have a serious problem. Still, setting this security measure can be useful to achieve maximum hardening of your Linux system. An altered script or program has no chance of loading things you didn´t specifically approve.
[...] By default, the sysctl key is set to"0", which means new modules can be loaded. This is a safe default for systems but also allows malicious modules to be loaded.
# sysctl -a | grep modules
kernel.modules_disabled = 0
Now we disable loading new modules, by using the sysctl key and set it to"1". There are two ways of doing it, using sysctl directly or echo the value to a file on the pseudo file system /proc, which holds the kernel settings.
# echo 1 > /proc/sys/kernel/modules_disabled
Protection against re-enabling
You might think that loading a kernel module is as simple as re-enabling the option and then still load your kernel module. The kernel has a built-in protection, to avoid this from happening. Trying to set the value back to"0" will result in an"invalid argument" message.
Sysctl showing invalid argument when trying to set value
As can be seen, sysctl will say the value is set to"0". However, the value isn´t applied, as this key is read-only. Slightly confusing, and therefore always good to check the value again.
# sysctl kernel.modules_disabled
kernel.modules_disabled = 1
As expected, the value is still set to"1".
Disable module loading after boot time
By configuring the /etc/sysctl.conf file we can disallow the loading of kernel modules at boot time. Simply add the related line, with the value"1" as shown in the example.
Caveat: Things might break
Depending on your environment, you might be careful with using this option. It may be working very well on servers, but not on desktop systems. The reason is the type of usage is different, especially when it comes with loading new kernel modules. For example inserting a USB drive, mouse or network functionality might break. So before deploying the option, make sure you test these common use cases.
Hybrid option
Instead of enabling the option directly via /etc/sysctl.conf, it might be better to activate this setting after booting and loading required modules.
Your startup script could be looking like
#!/bin/sh/ # code by Gooken
sleep 45 # original text: 300; decrease this time, if usb and all modules are working fine, if not, test checkout lsmod and increase it
# insmod <module>
# insmod <module>
modprobe usb_storage
modprobe dm_zero
modprobe vfat
modprobe fat
modprobe isofs # DVD/CD/...
modprobe udf # DVD/CD/...
modprobe nls_iso8859_1
modprobe nls_cp437
modprobe glue_helper
modprobe dax
modprobe uinput
modprobe ahci
modprobe libahci
modprobe ecb
modprobe af_alg
modprobe algif_skcipher
modprobe lrw
modprobe cbc
modprobe aes_x86_64 # for USB, that might be LUKS-encrypted
modprobe twofish_common
modprobe twofish_x86_64_3way
modprobe twofish_x86_64
modprobe twofish_generic
echo 1 > /proc/sys/kernel/modules_disabled
Usually to get iptables working, these are the related modules: iptables, x_tables, iptable_filter.
Depending on your Linux distribution, the startup should be loaded as late as possible. If you have /etc/rc.local available, that is usually a safe bet.
Do you use this option already? Or found some other caveats? Like to hear your feedback in the comments.
https://linux-audit.com/increase-kernel-integrity-with-disabled-linux-kernel-modules-loading/
In other words: write the small routine from above into a runlevel-init-script (for example this of /etc/init.d/linfw3 renamed to /etc/init.d/modules-disabled) right into the start function, where it is executed by the command start & (and not just the command "start") in the background. Before this is done, remove all code not needed anymore from this script. Now the script itself is executed not as usual by chkconfig, ntsysv7, the MCC (drakconf) or systemd, but only out of /etc/rc.local by the command "sh /etc/init.d/modules-disabled start".
 kernel.printk.* in /etc/sysctl.conf kernel.printk.* in /etc/sysctl.conf
kernel.printk =0 6 7 0 # The four values in printk denote: console_loglevel, default_message_loglevel, minimum_console_loglevel and default_console_loglevel respectively.
0=emerg, 1=alert, 2=crit, ...
kernel.printk_ratelimit = 5 # period to wait in seconds
kernel.printk_ratelimit_burst = 60 # max. amount same time
https://unix.stackexchange.com/questions/13019/description-of-kernel-printk-values
 Regelmäßig Logs analysieren Regelmäßig Logs analysieren
Speichere logs in vorgesehene Log-Server. Damit wird verhindert, dass Eindringlinge auf einfache Art Modifikationen an Log-Dateien vornehmen. Hier noch einmal namentlich die in Linux üblichen Log-Dateien und ihre Verwendung:
/var/log/message - Hier protokolliert mehr oder weniger das gesamte System
/var/log/auth.log - Authentifizierung
/var/log/kern.log - Kernel-Logs.
/var/log/cron.log - Crond-Logs (cron job).
/var/log/maillog - Mailserver-Logs
/var/log/boot.log - System-boot-Log
/var/log/mysqld.log - Logdatei des MySQL-Datenbankservers
/var/log/secure - Authentifizierung
/var/log/utmp oder /var/log/wtmp : Protokolliert die records-Dateien
/var/log/yum.log: Yum-Logdatei
https://www.tecmint.com/linux-server-hardening-security-tips/
 Prevent too informative system information in logfiles Prevent too informative system information in logfiles
The system-log-level reach from debug over info, warning up to emerg. A detailed protocolling is something to think about, they can be read out by users as much as processes. For outputs of dmesg log-level "warning" might restrict delivered protocol-information:
/etc/init.d/rklogd
RKLOGD_OPTIONS="-c 4"
 Using and customizing logcheck Using and customizing logcheck
The logcheck package in Debian is divided into the three packages logcheck (the main program), logcheck-database (a database of regular expressions for the program) and logtail (prints loglines that have not yet been read). The Debian default (in /etc/cron.d/logcheck) is that logcheck is run every hour and after reboots.
This tool can be quite useful if properly customized to alert the administrator of unusual system events. Logcheck can be fully customized so that it sends mails based on events found in the logs and worthy of attention. The default installation includes profiles for ignored events and policy violations for three different setups (workstation, server and paranoid). The Debian package includes a configuration file /etc/logcheck/logcheck.conf, sourced by the program, that defines which user the checks are sent to. It also provides a way for packages that provide services to implement new policies in the directories: /etc/logcheck/cracking.d/_packagename_, /etc/logcheck/violations.d/_packagename_, /etc/logcheck/violations.ignore.d/_packagename_, /etc/logcheck/ignore.d.paranoid/_packagename_, /etc/logcheck/ignore.d.server/_packagename_, and /etc/logcheck/ignore.d.workstation/_packagename_. However, not many packages currently do so. If you have a policy that can be useful for other users, please send it as a bug report for the appropriate package (as a wishlist bug). For more information read /usr/share/doc/logcheck/README.Debian.
The best way to configure logcheck is to edit its main configuration file /etc/logcheck/logcheck.conf after installation. Change the default user (root) to whom reports should be mailed. You should set the reportlevel in there, too. logcheck-database has three report levels of increasing verbosity: workstation, server, paranoid. "server" being the default level, paranoid is only recommended for high-security machines running as few services as possible and workstation for relatively sheltered, non-critical machines. If you wish to add new log files just add them to /etc/logcheck/logcheck.logfiles. It is tuned for default syslog install.
Once this is done you might want to check the mails that are sent, for the first few days/weeks/months. If you find you are sent messages you do not wish to receive, just add the regular expressions (see regex(7) and egrep(1)) that correspond to these messages to the /etc/logcheck/ignore.d.reportlevel/local. Try to match the whole logline. Details on howto write rules are explained in /usr/share/doc/logcheck-database/README.logcheck-database.gz. It´s an ongoing tuning process; once the messages that are sent are always relevant you can consider the tuning finished. Note that if logcheck does not find anything relevant in your system it will not mail you even if it does run (so you might get a mail only once a week, if you are lucky).
 Configure, where alerts are sent Configure, where alerts are sent
Debian comes with a standard syslog configuration (in /etc/syslog.conf) that logs messages to the appropriate files depending on the system facility. You should be familiar with this; have a look at the syslog.conf file and the documentation if not. If you intend to maintain a secure system you should be aware of where log messages are sent so they do not go unnoticed.
For example, sending messages to the console also is an interesting setup useful for many production-level systems. But for many such systems it is also important to add a new machine that will serve as loghost (i.e. it receives logs from all other systems).
Root´s mail should be considered also, many security controls (like snort) send alerts to root´s mailbox. This mailbox usually points to the first user created in the system (check /etc/aliases). Take care to send root´s mail to some place where it will be read (either locally or remotely).
There are other role accounts and aliases on your system. On a small system, it´s probably simplest to make sure that all such aliases point to the root account, and that mail to root is forwarded to the system administrator´s personal mailbox.
 Firefox: Copy the secure libssl*, libnss* and libnspr4* of tor-Browser (ESR) or out of an actual Firefox like 63 to Firefox (ESR, same version as tor-browser) into /usr/lib64/firefox/ followed by chown root:root and chmod 755 upon them. Firefox: Copy the secure libssl*, libnss* and libnspr4* of tor-Browser (ESR) or out of an actual Firefox like 63 to Firefox (ESR, same version as tor-browser) into /usr/lib64/firefox/ followed by chown root:root and chmod 755 upon them.
 Protecting against ARP-attacks Protecting against ARP-attacks
When you don´t trust the other boxes on your LAN (which should always be the case, because it´s the safest attitude) you should protect yourself from the various existing ARP attacks.
As you know the ARP protocol is used to link IP addresses to MAC addresses (see RFC826 for all the details). Every time you send a packet to an IP address an ARP resolution is done (first by looking into the local ARP cache then, if the IP isn´t present, in the cache by broadcasting an ARP query) to find the target´s hardware address. All the ARP attacks aim to fool your box into thinking, that box B´s IP address is associated to the intruder´s box´s MAC address; Then every packet that you want to send to the IP associated to box B will be send to the intruder´s box...
Those attacks (ARP cache poisoning, ARP spoofing...) allow the attacker to sniff the traffic even on switched networks, to easily hijack connections, to disconnect any host from the network... ARP attacks are powerful and simple to implement, and several tools exists, such as arpspoof from the dsniff package or arpoison.
However, there is always a solution:
Use a static ARP cache. You can set up "static" entries in your ARP cache with:
arp -s host_name hdwr_addr
By setting static entries for each important host in your network you ensure that nobody will create/modify a (fake) entry for these hosts (static entries don´t expire and can´t be modified) and spoofed ARP replies will be ignored.
Detect suspicious ARP traffic. You can use arpwatch, karpski or more general IDS that can also detect suspicious ARP traffic (snort, prelude...).
Implement IP traffic filtering validating the MAC address.
 Secure up services running on your system Secure up services running on your system
SSH, Squid, FTP, X-Window-System, Display-Manager, Druckerzugriff, Mail-Dienst, BIND, Apache, Finger, chroot- and suid-paranoia, Cleartext-passwort-paranoia, deactivating NIS, deactivating RPC-services:
https://www.debian.org/doc/manuals/securing-debian-howto/ch-sec-services.de.html
 Package signing Package signing
https://www.debian.org/doc/manuals/securing-debian-howto/ch7.de.html
 Remote vulnerability assessment tools Remote vulnerability assessment tools
The tools provided by Debian to perform remote vulnerability assessment are:
nessus, raccess, nikto (whisker´s replacement)
By far, the most complete and up-to-date tools is nessus which is composed of a client (nessus) used as a GUI and a server (nessusd) which launches the programmed attacks. Nessus includes remote vulnerabilities for quite a number of systems including network appliances, ftp servers, www servers, etc. The latest security plugins are able even to parse a web site and try to discover which interactive pages are available which could be attacked. There are also Java and Win32 clients (not included in Debian) which can be used to contact the management server.
 Make these changes within your router, in order to close lacks in security and to increase the internet trafffic speed, uncut-news.ch, 01.26.2024 Make these changes within your router, in order to close lacks in security and to increase the internet trafffic speed, uncut-news.ch, 01.26.2024
Text in english: https://reclaimthenet.org/make-these-changes-to-your-router-to-patch-security-holes-and-increase-internet-speed
Lassen Sie Ihren Router niemals in der Standardeinstellung.
Unser Leben ist immer mehr mit dem Internet verknüpft, und die Sicherheit und der Schutz der Privatsphäre bei unseren Online-Aktivitäten sind von größter Bedeutung. Vor diesem Hintergrund gibt es eine wichtige, aber oft übersehene Komponente in unserem Zuhause, die eine entscheidende Rolle für unsere digitale Sicherheit spielt: der Heimrouter. Dieses unscheinbare Gerät ist das Tor, durch das unsere gesamte Online-Kommunikation läuft. Es ist ein Stück Technik, das in Haushalten auf der ganzen Welt allgegenwärtig ist, aber seine Bedeutung für den Schutz unserer digitalen Privatsphäre und Sicherheit wird oft unterschätzt.
Ihr Router regelt den Internetverkehr für alle Geräte, die an Ihr Heimnetzwerk angeschlossen sind, wie Telefone, Laptops, Tablets, Konsolen und Smart-TVs. Ihr Router hat nicht nur Einfluss auf die Internetgeschwindigkeit aller angeschlossenen Geräte, sondern kann, wenn er nicht richtig konfiguriert ist, auch Sicherheitslücken aufweisen, die böswillige Akteure ausnutzen können, um Ihren Internetverkehr auszuspionieren. Glücklicherweise können Sie Ihren Router mit ein paar einfachen Schritten absichern und für die beste Geschwindigkeit und Verbindung optimieren.
Zugang zu den Einstellungen Ihres Routers
Um mit der Sicherung und Optimierung Ihres Routers zu beginnen, müssen Sie sich über Ihren Browser bei Ihrem Router anmelden.
Geben Sie zunächst die Standardnetzwerkadresse Ihres Routers in die Adresszeile Ihres Browsers ein.
Die häufigsten Router-Netzwerkadressen sind 192.168.1.1 und 192.168.0.1.
Einige weniger gebräuchliche Router-Adressen sind
192.168.15.1
192.168.100.1
192.168.1.254
10.0.1.1
Wenn keine dieser Adressen funktioniert, überprüfen Sie, ob die Standardnetzwerkadresse auf Ihrem Router aufgedruckt oder in der offiziellen Dokumentation Ihres Routers angegeben ist.
Die meisten Router stellen ihre offizielle Dokumentation auf ihren Support-Websites zur Verfügung. Hier finden Sie die Links zu den offiziellen Support-Websites für einige der gängigsten Router-Marken:
ASUS
Linksys
Netgear
Synology
TP-Link
Wenn Sie einen Router eines anderen Herstellers verwenden, suchen Sie nach "[Router-Hersteller] Support", "[Router-Hersteller] Dokumentation" oder "[Router-Hersteller] Login", um die entsprechende Dokumentation zu finden.
Nachdem Sie die Standardnetzwerkadresse Ihres Routers gefunden und in die Adressleiste Ihres Browsers eingegeben haben, müssen Sie die Anmeldedaten Ihres Routers eingeben.
Wenn Sie Ihre Zugangsdaten nicht kennen, versuchen Sie es mit dem Benutzernamen "admin" und dem Passwort "password".
Sollte dies nicht funktionieren, überprüfen Sie, ob die Anmeldedaten auf Ihrem Router aufgedruckt sind oder in der offiziellen Dokumentation Ihres Routers stehen.
Nachdem Sie sich erfolgreich angemeldet haben, können Sie mit der Sicherung und Optimierung Ihres Routers beginnen, indem Sie den Schritten in dieser Anleitung folgen. Jeder Schritt enthält eine allgemeine Anleitung zur Durchführung, aber der spezifische Prozess kann je nach Router variieren. Wenn Sie spezifische Anweisungen benötigen, lesen Sie die offizielle Dokumentation Ihres Routers oder besuchen Sie die Support-Website.
Ändern Sie das Standardpasswort Ihres Routers.
Da die meisten Router ein schwaches Standardpasswort verwenden, sollten Sie als erstes dieses schwache Standardpasswort in ein sicheres, eindeutiges Passwort ändern, um Ihren Router zu schützen.
Die Option zum Ändern des Passworts finden Sie normalerweise in den Router-Einstellungen unter "Verwaltung", "Allgemein" oder "Drahtlos".
Bei einigen Routern müssen Sie nur das neue Passwort eingeben, um Ihr Passwort zu ändern. Bei anderen Routern müssen Sie das alte und das neue Kennwort eingeben und das Kennwort bestätigen. Bei einigen Routern müssen Sie auch Sicherheitsfragen und -antworten eingeben.
Wenn Sie aufgefordert werden, Sicherheitsfragen und -antworten einzugeben, ist es am besten, die Antworten als zufällige Passwörter festzulegen und sie in einem Passwortmanager zu speichern, um zu verhindern, dass sie durch Social-Engineering-Angriffe aufgedeckt werden.
Ändern Sie den voreingestellten öffentlichen Namen (SSID) Ihres Routers.
Der voreingestellte öffentliche Name oder Service Set Identifier (SSID) Ihres Routers enthält oft verräterische Informationen wie die Marke und Modellnummer Ihres Routers oder den Namen Ihres Internet Service Providers (ISP). Wenn Sie den öffentlichen Namen Ihres Routers in einen weniger aufschlussreichen Namen ändern, z. B. in ein zufälliges Wort oder eine Phrase, können Sie es böswilligen Angreifern oder Netzwerk-Schnüfflern erschweren, das Modell Ihres Routers herauszufinden.
Die Option zum Ändern des Routernamens befindet sich in der Regel im Abschnitt "Erweitert" oder "Drahtlos" in den Einstellungen Ihres Routers.
WPA3-AES-Verschlüsselung verwenden
Wireless Protected Access 3-Advanced Encryption Standard 3 (WPA3-AES) ist einer der sichersten drahtlosen Verschlüsselungsstandards, und Sie sollten sicherstellen, dass Ihr Router diesen Standard verwendet, sofern er unterstützt wird. Falls Ihr Router WPA3-AES nicht unterstützt, verwenden Sie WPA2-AES.
Die Option zum Überprüfen und Ändern des drahtlosen Verschlüsselungsstandards Ihres Routers befindet sich normalerweise im Abschnitt "Erweitert", "Drahtlos" oder "Drahtlose Sicherheit" der Router-Einstellungen.
Deaktivieren Sie UPnP
Universal Plug and Play (UPnP) ermöglicht es jedem Programm in Ihrem lokalen Netzwerk, Ports auf der Firewall Ihres Routers zu öffnen und Verbindungen zu Geräten außerhalb des Netzwerks herzustellen. In der Regel ist UPnP bei Routern standardmäßig aktiviert, da es neuen Geräten ermöglicht, sich automatisch dem Netzwerk anzuschließen und mit anderen Geräten zu verbinden. Milliarden von Geräten sind jedoch von den UPnP-Schwachstellen betroffen, und durch Deaktivieren von UPnP können Sie Ihr Netzwerk vor diesen Schwachstellen schützen.
Die Option zum Deaktivieren von UPnP finden Sie in der Regel in den Einstellungen Ihres Routers unter "Erweitert", "Drahtlos" oder "Drahtlose Sicherheit".
In den meisten Fällen wird die Deaktivierung von UPnP keine Probleme verursachen. Sollten jedoch Probleme mit bestimmten Anwendungen, Geräten oder Diensten auftreten, können Sie manuell Ports für diese Anwendungen, Geräte oder Dienste öffnen und an diese weiterleiten.
Die Option zum manuellen Öffnen von Ports befindet sich in der Regel in den Abschnitten "Erweitert", "Anwendungen und Spiele", "Netzwerk", "Netzwerkcenter", "Portweiterleitung", "Port-Triggering", "Virtuelle Server", "WAN" oder "Sicherheit" in den Einstellungen Ihres Routers.
Sobald Sie die Option zum manuellen Öffnen von Ports auf Ihrem Router gefunden haben, müssen Sie die TCP- und UDP-Ports finden, auf die die spezifische Anwendung, das Gerät oder der Dienst weitergeleitet werden soll, und diese Portdetails beim Öffnen des Ports auf Ihrem Router eingeben.
Sie können diese Portdetails finden, indem Sie nach [Name der Anwendung/des Geräts/des Dienstes] Portweiterleitung suchen.
Ändern Sie Ihren Standard-DNS
Jedes Mal, wenn Sie eine Verbindung zu einer Website oder einem Online-Dienst herstellen, ruft Ihr Gerät einen Domain Name Server (DNS) auf, um den Domainnamen in die für die Verbindung erforderliche Internetprotokolladresse (IP) zu übersetzen. Standardmäßig verwendet Ihr Router den DNS, der von Ihrem Internetdienstanbieter bereitgestellt wird. Diese vom ISP bereitgestellten Server sind jedoch oft langsamer als Alternativen und ermöglichen dem ISP, den Zugriff auf Websites auf DNS-Ebene zu blockieren. Durch die Wahl eines schnellen, datenschutzfreundlichen DNS, z. B. 1.1.1.1 von Cloudflare, können Sie die DNS-Blockierung durch Ihren Internetanbieter vermeiden und von einer höheren Surfgeschwindigkeit profitieren.
Um Ihren Standard-DNS zu ändern, erhalten Sie die DNS-Serverdetails von Ihrem bevorzugten DNS-Anbieter. Die DNS-Server-Details für Cloudflare 1.1.1.1 finden Sie hier.
Ändern Sie dann den Standard-DNS-Server in den Einstellungen Ihres Routers. Die Option zum Ändern des DNS befindet sich in der Regel unter "Erweitert", "Konnektivität", "Lokales Netzwerk", "Internet", "IPv6", "Netzwerk", "Netzwerkcenter" oder "WAN" in den Einstellungen Ihres Routers.
Wi-Fi-Kanalbreite einstellen
Wi-Fi arbeitet auf zwei Frequenzen - 2,4 Gigahertz (GHz) und 5 GHz. Jede dieser Frequenzen ist in mehrere Kanäle aufgeteilt. Durch Einstellen der Wi-Fi-Kanalbreite können Sie die Verbindungsgeschwindigkeit verbessern oder Störungen reduzieren.
Die Option zum Überprüfen und Ändern der aktuellen Wi-Fi-Frequenz und Kanalbreite finden Sie in der Regel im Abschnitt "Erweitert", "Wi-Fi-Verbindung" oder "Drahtlos" in den Einstellungen Ihres Routers.
Wenn Sie in einem Bereich wohnen, in dem viel Platz zwischen Ihnen und anderen Wi-Fi-Netzwerken ist (z. B. in einem Haus mit viel Platz zwischen den Nachbarn), versuchen Sie, die Kanalbreite (einige Router nennen dies "Bandbreite") auf 40 MHz zu ändern, wenn Ihre Wi-Fi-Frequenz 2,4 GHz beträgt, oder auf 80 MHz, wenn Ihre Frequenz 5 GHz beträgt, und sehen Sie, ob sich Ihre Wi-Fi-Geschwindigkeit dadurch verbessert.
Wenn es in Ihrer Nähe viele Wi-Fi-Netzwerke gibt (z. B. in einem Mehrfamilienhaus) und Sie Probleme mit Interferenzen haben, versuchen Sie, die Kanalbreite auf 20 MHz zu ändern, wenn Ihre Wi-Fi-Frequenz 2,4 GHz beträgt, oder auf 40 MHz, wenn Ihre Wi-Fi-Frequenz 5 GHz beträgt.
Wi-Fi 6 aktivieren
Wenn Sie Wi-Fi 6, den neuesten Wi-Fi-Standard, auf Ihrem Router aktivieren, können Sie Ihre Internetgeschwindigkeit erhöhen, eine bessere Verbindung herstellen und mehr Geräte anschließen.
Viele Router verwenden automatisch den neuesten Wi-Fi-Standard. Wenn Ihr Router jedoch ermöglicht, den Wi-Fi-Standard zu ändern, finden Sie diese Option in der Regel im Abschnitt "Drahtlos" der Router-Einstellungen. Bei einigen Routern wird Wi-Fi 6 als "802.11ax" bezeichnet.
Wenn Ihr Router Wi-Fi 6 nicht unterstützt, aktivieren Sie den neuesten verfügbaren Standard. Wi-Fi 5 kann als "802.11ac" und Wi-Fi 4 als "802.11n" aufgeführt sein.
WPS deaktivieren
Wi-Fi Protected Setup (WPS) ist ein Netzwerksicherheitsstandard, der bei vielen Routern standardmäßig aktiviert ist, aber erhebliche Sicherheitslücken aufweist.
Sie können überprüfen, ob Ihr Router WPS unterstützt, indem Sie nach einem physischen WPS-Knopf am Router suchen, die offizielle Dokumentation lesen oder nach "[Routername] wps" suchen.
Die Option zum Deaktivieren von WPS befindet sich in der Regel unter "Erweitert", "Erweiterte Einstellungen", "Schnittstelleneinstellungen", "Netzwerkcenter", "Drahtlos" oder "Drahtloseinstellungen" in den Einstellungen Ihres Routers.
Fernverwaltung deaktivieren
Fernverwaltung, Fernzugriff oder Fernverwaltung ist eine Funktion, die es Personen außerhalb Ihres lokalen Netzwerks ermöglicht, sich bei Ihrem Router anzumelden. Die meisten Router haben diese Funktion standardmäßig deaktiviert, aber Sie sollten immer die Einstellungen Ihres Routers überprüfen und sicherstellen, dass die Fernverwaltung deaktiviert ist.
Die Option zum Überprüfen und Deaktivieren der Fernverwaltung befindet sich in der Regel im Abschnitt "Erweiterte Einstellungen", "Zugriffsverwaltung", "Verwaltung", "Fernzugriff", "Fernverwaltung" oder "Webdienstverwaltung" in den Einstellungen Ihres Routers.
HTTPS-Authentifizierung aktivieren
Viele Router stellen die Verbindung zu ihren Einstellungen über das standardmäßige Hypertext Transfer Protocol (HTTP) her. Sie können diese Verbindung sicherer machen, indem Sie sie auf Hypertext Transfer Protocol Secure (HTTPS) umstellen.
Die Option zum Überprüfen und Aktivieren von HTTPS befindet sich in der Regel im Abschnitt "Verwaltung", "Systemsteuerung", "Netzwerk", "Sicherheit" oder "System" der Router-Einstellungen.
11. Aktivieren Sie die Firewall Ihres Routers.
Die Firewall Ihres Routers schützt Ihr Heimnetzwerk, indem sie die meisten Verbindungen aus dem Internet blockiert. Bei den meisten Routern ist die Firewall bereits aktiviert, aber es ist ratsam, die Einstellungen Ihres Routers zu überprüfen und sicherzustellen, dass die Firewall aktiviert ist.
Die Option zum Überprüfen und Aktivieren der Firewall Ihres Routers finden Sie in der Regel unter "Erweiterte Einstellungen", "Inhaltsfilterung", "Firewall" oder "Sicherheit" in den Einstellungen Ihres Routers.
Nachdem Sie die Firewall aktiviert haben, überprüfen Sie, ob Sie damit anonyme Internetanfragen und Port 113 filtern oder blockieren können. Wenn dies möglich ist, filtern oder blockieren Sie diesen Datenverkehr, um einige der potenziellen Wege zu schließen, die Eindringlinge nutzen könnten, um Ihren Router anzugreifen.
Einrichtung eines Gast-Wi-Fi-Netzwerks
Wenn Sie ein Gast-Wi-Fi-Netzwerk einrichten, können sich Besucher mit Ihrem Wi-Fi-Netzwerk verbinden, ohne Zugriff auf die Dateien und Computer in Ihrem Heimnetzwerk zu erhalten.
Die Option zum Einrichten eines Wi-Fi-Gastnetzwerks finden Sie in der Regel in den Einstellungen Ihres Routers unter "Erweitert", "Gastzugang", "Gastnetzwerk", "Einstellungen" oder "Wi-Fi-Verbindung".
Halten Sie die Firmware ihres Routers auf dem neuesten Stand
Die neueste Firmware auf Ihrem Router ist wichtig, um sich vor den neuesten Sicherheitsbedrohungen zu schützen, und kann auch die Leistung Ihres Routers verbessern.
Einige Router benachrichtigen Sie, wenn eine neue Firmware verfügbar ist, sobald Sie sich bei den Einstellungen Ihres Routers anmelden. Wenn Ihr Router Sie nicht automatisch benachrichtigt, finden Sie die Option zum Überprüfen und Aktualisieren der Router-Firmware in der Regel unter "Verwaltung", "Erweitert", "Firmware-Update" oder "Router-Update" in den Einstellungen Ihres Routers.
Einige Router bieten auch automatische Firmware-Updates an. Dies kann eine echte Möglichkeit sein, um über Firmware-Updates auf dem Laufenden zu bleiben. Bevor Sie jedoch automatische Firmware-Updates aktivieren, sollten Sie sich genau darüber informieren, wie diese auf Ihrem Router durchgeführt werden, um sicherzustellen, dass die Updates Ihre Verbindung nicht beeinträchtigen.
Einrichtung eines VPN auf Ihrem Router in Betracht ziehen
Wenn Sie bereits ein virtuelles privates Netzwerk (VPN) verwenden, können Sie es auf Ihrem Router einrichten, um Ihr gesamtes Heimnetzwerk und alle Geräte, die daran angeschlossen sind, zu schützen. Auf diese Weise können Sie nicht nur die Verschlüsselung des VPN-Verkehrs auf Geräte ausweiten, für die es keine VPN-Anwendungen gibt (z. B. Videospielkonsolen), sondern auch mehrere Geräte über eine einzige VPN-Verbindung betreiben (was nützlich sein kann, wenn Ihr VPN-Anbieter die Anzahl der Verbindungen begrenzt).
Die Option zur Installation eines VPN finden Sie in der Regel in den Einstellungen Ihres Routers unter "Erweitert", "VPN", "VPN-Client" oder "VPN-Server".
Unsere empfohlenen VPN-Anbieter finden Sie hier.
15) Installation einer angepassten Router-Firmware in Betracht ziehen
Die meisten Router-Firmware-Programme sind Closed-Source-Programme, d.h. es gibt keinen öffentlich zugänglichen Quellcode, der überprüft werden kann, und die Funktionen werden vom Anbieter der Firmware festgelegt. Wenn Sie mehr Einblick in den Quellcode Ihres Routers haben und die Funktionen anpassen möchten, sollten Sie die Installation einer benutzerdefinierten Router-Firmware in Erwägung ziehen.
Zwei der beliebtesten Open-Source-Lösungen für angepasste Router-Firmware sind OpenWrt und PfSense.
OpenWrt bietet mehr als 3.000 Pakete, die installiert werden können, um Ihrem Router zusätzliche Funktionen hinzuzufügen. Mit diesen Paketen können Sie Werbung auf Routerebene blockieren (was bedeutet, dass sie auf allen Geräten blockiert wird), Download- und Bandbreitenbeschränkungen festlegen, Ihren Router zu einem zentralen Knotenpunkt für die Heimautomatisierung machen und vieles mehr.
PfSense verfügt über mehr als 60 Pakete, die installiert werden können, um die Funktionalität des Routers zu erweitern. Ferner bietet PfSense integrierte Backup-Konfigurationen (mit denen Sie Ihre Router-Einstellungen einfach sichern können), spezifisches Traffic-Routing (mit dem Sie festlegen können, wie die einzelnen Geräte ihren Datenverkehr leiten sollen, z.B. können Sie festlegen, dass einige Geräte ihren Datenverkehr über Ihr VPN leiten und andere Geräte Ihr VPN nicht verwenden), einfache Konfigurationen von Firewall-Regeln und vieles mehr.
Einige Router sind nicht mit benutzerdefinierter Firmware kompatibel, daher müssen Sie prüfen, ob Sie OpenWrt oder PfSense auf Ihrem Router installieren können. Sie können in der offiziellen Dokumentation Ihres Routers nachsehen oder nach "[Routername] openwrt" oder "[Routername] pfsense" suchen, um herauszufinden, ob Ihr Router benutzerdefinierte Firmware unterstützt.
Wenn Ihr Router benutzerdefinierte Firmware unterstützt, suchen Sie in den Suchergebnissen nach Installationsanweisungen und folgen Sie diesen, um OpenWrt oder PfSense auf Ihrem Router zu installieren.
Schränken Sie die physische Sichtbarkeit Ihres Routers ein.
Ihr Router enthält viele physikalische Informationen, die von Angreifern ausgenutzt werden könnten. Zum Beispiel könnte die Form oder der Text auf Ihrem Router die Marke und Modellnummer verraten. Sie sollten daher Maßnahmen ergreifen, um die Sichtbarkeit Ihres Routers zu verbergen.
Im Idealfall sollte er an einem vollkommen unzugänglichen Ort aufgestellt werden, z. B. in einem Schrank oder in einem separaten Raum. Zumindest sollte er in einem Bereich stehen, der nicht durch Fenster eingesehen werden kann.
Helfen Sie anderen, ihren Router sicherer und schneller zu machen
Wenn Sie diese Tipps befolgen, können Sie schneller und sicherer im Internet surfen. Geben Sie diese Tipps auch an Freunde, Verwandte und andere Personen weiter, die ihre Router-Einstellungen aktualisieren müssen.
Quelle: Make These Changes To Your Router to Patch Security Holes and Increase Internet Speed, https://reclaimthenet.org/make-these-changes-to-your-router-to-
patch-security-holes-and-increase-internet-speed
https://uncutnews.ch/nehmen-sie-diese-aenderungen-an-ihrem-router-vor-um-
sicherheitsluecken-zu-schliessen-und-die-internetgeschwindigkeit-zu-erhoehen/
Lesermeinung Gooken
Unter vielem anderen zusätzlich zu beachten:
Welche Server sind mit dem Router verbunden? Dritte? Gastserver? Gäste? Sperrung/Austragung/Deaktivierung
Ist der Adressraum IPv6 zugelassen (statische Adressen)? Wir emfehlen nur IPv4.
Neben UPnP: Mediaserver, NAS-Server, ...: aktiveren oder deaktivieren.
FTP-/FTPs-Zugang?
Ist eine WPA3-Verschlüsselung möglich?
Aktivierte Router-Firewall (Verhinderung der Nutzung verbundener Geräte als Server, geräteweise Einstellung)?
Individuelle Benutzereinstellungen?
Automatische Updates für den Router: aktivieren/deaktiveren
Automatische Verbindungsaufnahme zum ISP (Internet Service Provider, Internet-Zugang-Anbieter)? deaktivieren
Wartung/Reparatur des Routers durch Dritte? deaktivieren
... (!)
Gehen Sie sorgsam alle möglichen Router-Einstellungen durch und halten Sie eventuell Rücksprache mit ihrem ISP!
 Network scanner tools Network scanner tools
Debian does provide some tools used for remote scanning of hosts (but not vulnerability assessment). These tools are, in some cases, used by vulnerability assessment scanners as the first type of "attack" run against remote hosts in an attempt to determine remote services available. Currently Debian provides:
nmap, xprobe, p0f, knocker, isic, hping2, icmpush, nbtscan (for SMB /NetBIOS audits), fragrouter, strobe (in the netdiag package), irpas
While xprobe provide only remote operating system detection (using TCP/IP fingerprinting, nmap and knocker do both operating system detection and port scanning of the remote hosts. On the other hand, hping2 and icmpush can be used for remote ICMP attack techniques.
Designed specifically for SMB networks, nbtscan can be used to scan IP networks and retrieve name information from SMB-enabled servers, including: usernames, network names, MAC addresses...
On the other hand, fragrouter can be used to test network intrusion detection systems and see if the NIDS can be eluded by fragmentation attacks.
 Virtual Private Networks Virtual Private Networks
A virtual private network (VPN) is a group of two or more computer systems, typically connected to a private network with limited public network access, that communicate securely over a public network. VPNs may connect a single computer to a private network (client-server), or a remote LAN to a private network (server-server). VPNs often include the use of encryption, strong authentication of remote users or hosts, and methods for hiding the private network´s topology.
Debian provides quite a few packages to set up encrypted virtual private networks:
vtun, tunnelv (non-US section), cipe-source, cipe-common, tinc, secvpn, pptpd, openvpn, openswan (http://www.openswan.org/)
The OpenSWAN package is probably the best choice overall, since it promises to interoperate with almost anything that uses the IP security protocol, IPsec (RFC 2411). However, the other packages listed above can also help you get a secure tunnel up in a hurry. The point to point tunneling protocol (PPTP) is a proprietary Microsoft protocol for VPN. It is supported under Linux, but is known to have serious security issues.
For more information see the VPN-Masquerade HOWTO (covers IPsec and PPTP), VPN HOWTO (covers PPP over SSH), Cipe mini-HOWTO, and PPP and SSH mini-HOWTO.
Also worth checking out is Yavipin, but no Debian packages seem to be available yet.
 Reaction in the case of user-idle-state, https://wiki.centos.org/HowTos/OS_Protection Reaction in the case of user-idle-state, https://wiki.centos.org/HowTos/OS_Protection
Now that we´ve restricted the login options for the server, lets kick off all the idle folks. To do this, we´re going to use a bash variable in /etc/profile. There are some reasonably trivial ways around this of course, but it´s all about layering the security.
echo "Idle users will be removed after 15 minutes"
echo "readonly TMOUT=900" >> /etc/profile.d/os-security.sh
echo "readonly HISTFILE" >> /etc/profile.d/os-security.sh
chmod +x /etc/profile.d/os-security.sh
 Restrictions for cron and at, https://wiki.centos.org/HowTos/OS_Protection Restrictions for cron and at, https://wiki.centos.org/HowTos/OS_Protection
In some cases, administrators may want the root user or other trusted users to be able to run cronjobs or timed scripts with at. In order to lock these down, you will need to create a cron.deny and at.deny file inside /etc with the names of all blocked users. An easy way to do this is to parse /etc/passwd. The script below will do this for you.
echo "Locking down Cron"
touch /etc/cron.allow
chmod 600 /etc/cron.allow
awk -F: ´{print $1}´ /etc/passwd | grep -v root > /etc/cron.deny
echo "Locking down AT"
touch /etc/at.allow
chmod 600 /etc/at.allow
awk -F: ´{print $1}´ /etc/passwd | grep -v root > /etc/at.deny
 Lockdown Cronjobs Lockdown Cronjobs
Cron has it´s own built in feature, where it allows to specify who may, and who may not want to run jobs. This is controlled by the use of files called /etc/cron.allow and /etc/cron.deny. To lock a user using cron, simply add user names in cron.deny and to allow a user to run cron add in cron.allow file. If you would like to disable all users from using cron, add the ´ALL´ line to cron.deny file.
# echo ALL >>/etc/cron.deny
Cron Scheduling Examples in Linux: https://www.tecmint.com/11-cron-scheduling-task-examples-in-linux/
https://www.tecmint.com/linux-server-hardening-security-tips/
 Sysctl Security, https://wiki.centos.org/HowTos/OS_Protection Sysctl Security, https://wiki.centos.org/HowTos/OS_Protection
Next we need to have a look inside /etc/sysctl.conf and make some basic changes. If these lines exist, modify them to match below. If they don´t exist, simply add them in. If you have multiple network interfaces on the server, some of these may cause issues. Test these before you put them into production. If you want to know more about any of these options, install the kernel-doc package, and look in Documentation/networking/ip-sysctl.txt
# Kernel sysctl configuration file
# /etc/sysctl.conf
# test with sysctl -p /etc/sysctl.conf
# additionally from http://joshrendek.com/2013/01/securing-ubuntu/ resp. http://www.nsa.gov/ia/_files/os/redhat/rhel5-guide-i731.pdf
# Turn on execshild
# kernel.exec-shield = 1
# Controls the System Request debugging functionality of the kernel
kernel.sysrq =0
# Controls whether core dumps will append the PID to the core filename.
# Useful for debugging multi-threaded applications.
kernel.core_uses_pid = 0
kernel.dmesg_restrict = 1
kernel.randomize_va_space = 1
kernel.ctrl-alt-del =1
kernel.panic =0
kernel.acct =4 2 30
kernel.printk =4
kernel.shmall =-1
kernel.shmmax =134217728
# Allow for more PIDs (to reduce rollover problems); may break some programs 32768
kernel.pid_max = 65536
kernel.printk_ratelimit = 5 # period to wait in seconds
kernel.printk_ratelimit_burst = 60 # max. amount same time
vm.overcommit_memory=2 # mouseclick-fast
vm.overcommit_ratio=150 # 4 GB RAM + 2 GB SWAP, mouseclick-fast
# or: vm.overcommit_kbytes=
vm.page-cluster =3
vm.oom_dump_tasks =0
dev.raid.speed_limit_min =1000
dev.raid.speed_limit_max =200000
# Optimization for port usefor LBs
# Increase system file descriptor limit
fs.file-max = 65535
#
# For binary values, 0 is disabled, 1 is enabled. See sysctl(8) and
net.ipv4.ip_forward = 0
net.ipv4.conf.all.send_redirects = 0
net.ipv4.conf.default.send_redirects = 0
net.ipv4.tcp_max_syn_backlog = 1280
net.ipv4.icmp_echo_ignore_broadcasts = 1
net.ipv4.conf.all.accept_source_route = 0
net.ipv4.conf.all.accept_redirects = 0
net.ipv4.conf.all.secure_redirects = 0
net.ipv4.conf.all.log_martians = 1
net.ipv4.conf.default.accept_source_route = 0
net.ipv4.conf.default.accept_redirects = 0
net.ipv4.conf.default.secure_redirects = 0
net.ipv4.icmp_echo_ignore_broadcasts = 1
net.ipv4.icmp_ignore_bogus_error_responses = 1
net.ipv4.tcp_syncookies = 1
net.ipv4.conf.all.rp_filter = 1
net.ipv4.conf.default.rp_filter = 1
net.ipv4.tcp_timestamps = 0
net.ipv4.tcp_window_scaling = 1
net.ipv4.tcp_fin_timeout =3600
net.ipv4.tcp_keepalive_time =7200
net.ipv4.tcp_keepalive_probes =7
net.ipv4.tcp_syn_retries =6
net.ipv4.tcp_retries1 =1
net.ipv4.tcp_retries2 =3
net.ipv4.tcp_retrans_collapse =1
net.ipv4.tcp_sack =1
net.ipv4.ip_default_ttl =64
net.ipv4.ipfrag_time =30
net.ipv4.ip_no_pmtu_disc =0
net.unix.max_dgram_qlen =10
# Increase system IP port limits
net.ipv4.ip_local_port_range = 2000 65000
# Increase TCP max buffer size setable using setsockopt()
net.ipv4.tcp_rmem = 4096 87380 8388608
net.ipv4.tcp_wmem = 4096 87380 8388608
net.ipv6.conf.eth0.disable_ipv6=1
# Tune IPv6
net.ipv6.conf.default.router_solicitations = 0
net.ipv6.conf.default.accept_ra_rtr_pref = 0
net.ipv6.conf.default.accept_ra_pinfo = 0
net.ipv6.conf.default.accept_ra_defrtr = 0
net.ipv6.conf.default.autoconf = 0
net.ipv6.conf.default.dad_transmits = 0
net.ipv6.conf.default.max_addresses = 0
# Increase Linux auto tuning TCP buffer limits
# min, default, and max number of bytes to use
# set max to at least 4MB, or higher if you use very high BDP paths
net.core.rmem_max = 8388608
net.core.wmem_max = 8388608
net.core.netdev_max_backlog = 5000
# net.core.default_qdisc=sch_fq_codel
net.ipv4.tcp_congestion_control=cubic
# BBR
# net.core.default_qdisc=fq
# net.ipv4.tcp_congestion_control=bbr
# If you set this variable to 1 then cd tray will close automatically when the
# cd drive is being accessed.
# Setting this to 1 is not advised when supermount is enabled
# (as it has been known to cause problems)
dev.cdrom.autoclose=1
# removed to fix some digital extraction problems
# dev.cdrom.check_media=1
# to be able to eject via the device eject button (magicdev)
dev.cdrom.lock=0
#
# BBR - Netwerkturbo für Linux
# Die neue Flusskontrolle erscheint aber auch ideal für Server im lokalen Netzwerk, die hin und wieder die Netzwerkbandbreite voll ausschöpfen sollen, etwa bei der Übertragung großer Dateien bei NAS-Geräten, Nextcloud- oder
# Streamingservern.
# https://www.pcwelt.de/ratgeber/BBR-Netzwerkturbo-fuer-Linux-im-Ueberblick-10612165.html
# net.core.default_qdisc=fq
net.ipv4.tcp_congestion_control=bbr
# Increase Linux auto tuning TCP buffer limits
# min, default, and max number of bytes to use
# set max to at least 4MB, or higher if you use very high BDP paths
net.core.rmem_max =212992
net.core.wmem_max =212992
net.core.netdev_max_backlog = 5000
#
kernel.sysrq = 0
kernel.core_uses_pid = 1
fs.file-max=65535
kernel.pid_max=65536
net.ipv4.tcp_syncookies = 1
kernel.msgmnb = 65536
kernel.msgmax = 65536
kernel.shmmax = 134217728
kernel.shmall = 4294967296
kernel.randomize_va_space = 2
net.ipv4.tcp_window_scaling=1
net.ipv4.tcp_timestamps=0
net.ipv4.conf.all.log_martians=1# sysctl.conf(5) for more details.
net.ipv6.conf.lo.use_tempaddr = 0
# Disables IP dynaddr
net.ipv4.ip_dynaddr = 1
# Disable ECN
net.ipv4.tcp_ecn = 1
# Controls source route verification
net.ipv4.conf.all.rp_filter =1
net.ipv4.conf.default.rp_filter = 1
# Do not accept source routing
net.ipv4.conf.default.accept_source_route = 0
# Controls the System Request debugging functionality of the kernel
kernel.sysrq =0
# Controls whether core dumps will append the PID to the core filename.
# Useful for debugging multi-threaded applications.
kernel.core_uses_pid = 0
kernel.dmesg_restrict = 1
# If you set this variable to 1 then cd tray will close automatically when the
# cd drive is being accessed.
# Setting this to 1 is not advised when supermount is enabled
# (as it has been known to cause problems)
dev.cdrom.autoclose=1
# removed to fix some digital extraction problems
# dev.cdrom.check_media=1
# to be able to eject via the device eject button (magicdev)
dev.cdrom.lock=0
# Disable netfilter on bridges.
#net.bridge.bridge-nf-call-ip6tables = 0
#net.bridge.bridge-nf-call-iptables = 0
#net.bridge.bridge-nf-call-arptables = 0
net.ipv4.ip_forward =0
net.ipv4.conf.all.send_redirects = 0
net.ipv4.conf.default.send_redirects = 0
net.ipv4.tcp_max_syn_backlog =512
net.ipv4.conf.all.accept_source_route = 0
net.ipv4.conf.all.accept_redirects = 0
net.ipv4.conf.default.accept_redirects = 0
net.ipv4.conf.all.secure_redirects = 0
net.ipv4.conf.default.accept_source_route = 0
net.ipv4.conf.default.accept_redirects = 0
net.ipv4.conf.default.secure_redirects = 0
net.ipv4.tcp_syncookies = 1
net.ipv4.ip_local_port_range = 2000 65000
# Increase TCP max buffer size setable using setsockopt()
net.ipv4.tcp_rmem = 4096 87380 8388608
net.ipv4.tcp_wmem = 4096 87380 8388608
net.ipv6.conf.default.router_solicitations=0
net.ipv6.conf.default.accept_ra_rtr_pref=0
net.ipv6.conf.default.accept_ra_pinfo=0
net.ipv6.conf.default.accept_ra_defrtr=0
net.ipv6.conf.default.autoconf=0
net.ipv6.conf.default.dad_transmits=0
net.ipv6.conf.default.max_addresses=0
net.ipv4.icmp_echo_ignore_all=1
net.ipv4.icmp_echo_ignore_broadcasts=1
net.ipv4.icmp_ignore_bogus_error_responses=1
net.core.rmem_default =212992
net.core.wmem_default =212992
net.ipv4.tcp_fin_timeout =3600
net.ipv4.tcp_keepalive_time =7200
net.ipv4.tcp_keepalive_probes =7
net.ipv4.tcp_syn_retries =6
net.ipv4.tcp_retries1 =1
net.ipv4.tcp_retries2 =3
net.ipv4.tcp_retrans_collapse =1
net.ipv4.tcp_sack =1
net.ipv4.ip_default_ttl =64
net.ipv4.ipfrag_time =30
net.ipv4.ip_no_pmtu_disc =0
net.unix.max_dgram_qlen =10
vm.overcommit_memory =2
vm.overcommit_ratio=150 # 4 GB RAM + 2 GB SWAP, mausklick-schnell
# or: vm.overcommit_kbytes=
vm.page-cluster =3
kernel.ctrl-alt-del =1
kernel.panic =0
kernel.acct =4 2 30
kernel.printk =4
kernel.shmall =-1
kernel.shmmax =134217728
dev.raid.speed_limit_min =1000
dev.raid.speed_limit_max =200000
net.ipv4.conf.all.rp_filter=1
 Gooken´s excellent DNS-security-concept, details from much further below: "DNS-surf-mask" local (etc/hosts/) for fundamental domain-IP including some blocks, followed by pdnsd (the local DNS-proxy/DNS-server with adjustable long-time storage) and finally tordns (the anonymizing DNS-Server of Tor (the Onion Router), tor-resolve) Gooken´s excellent DNS-security-concept, details from much further below: "DNS-surf-mask" local (etc/hosts/) for fundamental domain-IP including some blocks, followed by pdnsd (the local DNS-proxy/DNS-server with adjustable long-time storage) and finally tordns (the anonymizing DNS-Server of Tor (the Onion Router), tor-resolve)
 Deactivate IPv6, https://help.ubuntu.com/community/StricterDefaults Deactivate IPv6, https://help.ubuntu.com/community/StricterDefaults
IPv6 is part of a Linux-kernel since 2.6.28. Such addresses do never change. If IPv6 is configured wrong, it can cause troubles within a network and for DNS-queries.
IPv6 is enabled on Ubuntu by default. Most firewalls (like LINFW3) only apply to IPv4, and completely ignore IPv6. If you don´t use IPv6 at all, you can prevent it loading at boot time by changing alias net-pf-10 ipv6 to alias net-pf-10 off in /etc/modprobe.d/aliases resp. /etc/modprobe.conf and scheduling a reboot.
RedHat Enterprise Linux / CentOS / Fedora Core:
/etc/modprobe.conf, change line:
alias net-pf-10 ipv6
into:
alias net-pf-10 off
alias ipv6 off
and restart the computer.
RedHat Enterprise Linux / CentOS / Fedora Core / Mandriva:
Add the following entry to /etc/sysconfig/network:
NETWORKING_IPV6="no"
... and restart the system.
 ktune: Kernel-Tuning resp. by boot-options ( /etc/init.d/ktune, if not already done in /boot/grub/menu.lst)), so make it mouseclick-fast ktune: Kernel-Tuning resp. by boot-options ( /etc/init.d/ktune, if not already done in /boot/grub/menu.lst)), so make it mouseclick-fast
/etc/sysctl.d/*
nano /etc/sysctl.d/01-disable-ipv6.conf
net.ipv6.conf.all.disable_ipv6 = 1
nano /etc/sysctl.d/10-ptrace.conf
kernel.yama.ptrace.scope=3
nano /etc/sysctl.d/50-kptr-restrict.conf
kernel.kptr_restrict=1
nano /etc/sysctl.d/armci.conf
# Controls the maximum shared segment size, in bytes, siehe auch /etc/sysctl.conf
kernel.shmmax = 134217728
nano /etc/sysctl.d/libvirtd
The kernel allocates aio memory on demand, and this number limits the
# number of parallel aio requests; the only drawback of a larger limit is
# that a malicious guest could issue parallel requests to cause the kernel
# to set aside memory. Set this number at least as large as
# 128 * (number of virtual disks on the host)
# Libvirt uses a default of 1M requests to allow 8k disks, with at most
# 64M of kernel memory if all disks hit an aio request at the same time.
# fs.aio-max-nr = 1048576
Start ktune
sh /etc/init.d/ktune start
 Deactivate IPv6 Deactivate IPv6
This article describes, howto deactivate the IPv6 support for Linux and Windows. Dies kann aus Sicherheitsgründen sinnvoll sein, solange man IPv6 noch nicht produktiv einsetzt. Damit kann verhindert werden, dass man eine IPv6 Adresse erhält, sobald ein IPv6 Router Advertisement Daemon in einem Netz verfügbar ist. Außerdem sind bestehende Firewall Rules oft nicht für IPv6 gültig. In diesem Fall hätte man dann unter Umständen Dienste per IPv6 zugänglich die man eigentlich mit einer IPv4 Regel unterbunden hat. Unter Linux gibt es das eigene Kommando "ip6tables" zur Verwaltung der IPv6 Firewall Rules.
1 Ubuntu
2 RHEL / CentOS
Ubuntu
In Ubuntu 10.04, 12.04, 14.04 und 16.04 ist IPv6 direkt in den Kernel kompiliert und wird nicht als Modul geladen. Die einfachste Methode um IPv6 zu deaktivieren ist den passenden sysctl Parameter zu setzen. Temporär kann dies mit folgendem Kommando erfolgen:
echo 1 > /proc/sys/net/ipv6/conf/all/disable_ipv6
Um diese Einstellung dauerhaft vorzunehmen bietet es sich an auf die sysctl Funktionalitäten zurückzugreifen. Dafür einfach eine Datei namens /etc/sysctl.d/01-disable-ipv6.conf anlegen mit folgendem Inhalt:
net.ipv6.conf.all.disable_ipv6 = 1
Nach dem nächsten Reboot ist IPv6 dann deaktiviert.
Am besten kann dies mit dem Kommando "ip addr show" überprüft werden. Es darf dann keine Einträge mit dem Text "inet6" mehr geben.
ip addr show | grep inet6
RHEL / CentOS
Unter RHEL 6 / CentOS 6 (with many patches/updates by Jonny Hughes, NY, kann die Deaktivierung von IPv6 ident wie unter Ubuntu via sysctl erfolgen (siehe oben).
In RHEL 4 / CentOS 4 ist IPv6 als Modul integriert. Um dieses zu deaktiveren einfach folgende Zeile in der Datei /etc/modprobe.conf hinzufügen:
install ipv6 /bin/true
Die Überprüfung, ob es geklappt hat, kann mit dem Kommando "ip addr show | grep inet6" oder alternativ mit dem Kommando
lsmod | grep -i ipv6
 TCP Wrapper, https://wiki.centos.org/HowTos/OS_Protection TCP Wrapper, https://wiki.centos.org/HowTos/OS_Protection
Next we need to have a look inside /etc/sysctl.conf and make some basic changes. The TCP wrappers can provide a quick and easy method for controlling access to applications linked to them. Examples of TCP Wrapper aware applications are sshd, and portmap. A restrictive example is below. This example blocks everything but ssh:
echo "ALL:ALL" >> /etc/hosts.deny
echo "sshd:ALL" >> /etc/hosts.allow
echo "ALL:ALL:DENY" >> /etc/hosts.allow
 Turn on SELinux Turn on SELinux
Security-Enhanced Linux (SELinux) is a compulsory access control security mechanism provided in the kernel. Disabling SELinux means removing security mechanism from the system. Think twice carefully before removing, if your system is attached to internet and accessed by the public, then think some more on it.
SELinux provides three basic modes of operation and they are.
Enforcing: This is default mode which enable and enforce the SELinux security policy on the machine.
Permissive: In this mode, SELinux will not enforce the security policy on the system, only warn and log actions. This mode is very useful in term of troubleshooting SELinux related issues.
Disabled: SELinux is turned off.
You can view current status of SELinux mode from the command line using ´system-config-selinux´, ´getenforce´ or ´sestatus´ commands.
# sestatus
If it is disabled, enable SELinux using the following command.
setenforce enforcing
It also can be managed from ´/etc/selinux/config´ file, where you can enable or disable it.
https://www.tecmint.com/linux-server-hardening-security-tips/. Bootparameter in /boot/grub/menu:lst: "selinux=1"
AppArmor or SELinux?, forum.ubuntuusers.de
Why does Ubuntu not use SELinux, ... I see it so too.... I have no trust anymore. . Tom-L. Beiträge form year 2007 ( five years before Snowden´s publications...): 1181.
@glasen
Many thanks, I am going to reed it having time next morning..
@timmy11
Soso, NSA aso. Hmm, I would for myself wouldn´t bother about ... I mean, ok, of it would be our government Bundesregierung... Bundes-trojan :lol:
No, but to be serious: Security against third parties may be higher, if institutes like NSA are involved, but I feel the shabby smell with it too.
timmy11
Maybe someone can convince us from the opposite.
For me America means (... the governmental organizations): I like everything to know and to snoop upon.
Murdoc
Avatar von Murdoc
I also see this....I simple do not have any trust anymore:(
Tom L.: I mean having read, that SELinux is an official part of the kernel. Therefore I believe, that Kernel developer ( and more than only the same one) has studied the source code carefully.
glasen: Sorry, but I can not stand your paranoia.
Obviously NSA become a member to develope SELinux, but as Linux is open-source free software, it is impossible for NSA to keep any backdoors secretly open.
If there were one line code, that could not stand Peer-Review, SELinux would never be a part of the kernel-sources!
Murdoc: I believe this too, but they have studied everything, but there are also kernel-exploits :-/
If secret services would do this, intergrating backdoors within the kernel ..., then certainly not by a project like SELinux, but through other parts of the kernel.
comm_a_nder: Hey, boys, think about it.
Mosurft: Generally I do not feel well connecting SELinux made by NSA, even for - I do believe - noone can study and analyze each part of the source-code. Anyoune does always not notice anything, otherwise there would be no lacks in security and even a secret service has got the most interest in getting and checking a PC with the click on the buttom, in order to check out PCs...
I´d like to know, who runs SELinux on a computer with Ubuntu and how it functions! And if someone does not like SELinux, what about Grsecurity? Did anyone check it out?
Greetings, Mo.
comm_a_nder: If i said it in the wrong way and you feel attacked in person, it makes me sorry.
Back to the theme: Especially the parts of software added by NSA, have been checked out well. But as I told you, there were surely much more effective ways for the boys from "Crypto City" to migrate code into kernel-source.
Murdoc. As we are going on paranoidal, I ask for the BIOS.
Now, as ASUS offers a Minimal Linux to browse, the question is posed, what the BIOS is all enabled to do?
Mosurft: If I do not trust the BIOS, then I better do not use any computer...! ;)
...
https://forum.ubuntuusers.de/topic/apparmor-oder-selinux
Introduced mainboard ITX-220 comes with in- and deactivable BIOS-LAN-Chip and Coretemp for the regulation of the temperature... Next point: SELinux. As our excurs shows, it is suspicously not needed. So we´d prefer to deactivate it right within the boot-paramters.
 Review Logs Regularly Review Logs Regularly
Move logs in dedicated log server, this may prevents intruders to easily modify local logs. Below are the Common Linux default log files name and their usage:
/var/log/message - Where whole system logs or current activity logs are available.
/var/log/auth.log - Authentication logs.
/var/log/kern.log - Kernel logs.
/var/log/cron.log - Crond logs (cron job).
/var/log/maillog - Mail server logs.
/var/log/boot.log - System boot log.
/var/log/mysqld.log - MySQL database server log file.
/var/log/secure - Authentication log.
/var/log/utmp or /var/log/wtmp : Login records file.
/var/log/yum.log: Yum log files.
https://www.tecmint.com/linux-server-hardening-security-tips/
 Shared Memory (shm und tmpfs, siehe unsere /etc/fstab im noch Folgenden), https://help.ubuntu.com/community/StricterDefaults Shared Memory (shm und tmpfs, siehe unsere /etc/fstab im noch Folgenden), https://help.ubuntu.com/community/StricterDefaults
By default, /run/shm is mounted read/write, with permission to execute programs. In recent years, many security mailing lists have noted many exploits where /run/shm is used in an attack against a running service, such as httpd. Most of these exploits, however, rely on an insecure web application rather than a vulnerability in Apache or Ubuntu. There are a few reasons for it to be mounted read/write in specific configurations, such as real-time configuration of a Synaptics touchpad for laptops, but for servers and desktop installations there is no benefit to mounting /run/shm read/write. To change this setting, edit the /etc/fstab file to include the following line:
none /run/shm tmpfs defaults,ro 0 0
resp. http://joshrendek.com/2013/01/securing-ubuntu/ :
A common exploit vector is going through shared memory (which can let you change the UID of running programs and other malicious actions). It can also be used as a place to drop files once an initial breakin has been made. An example of one such exploit is available here.
Open /etc/fstab/:
tmpfs /dev/shm tmpfs defaults,ro 0 0
This will mount /run/shm in read-only mode. Note: MANY programs will not work if you make /run/shm read-only (e.g. Google Chrome).If you have a good reason to keep it writable, put this line in /etc/fstab instead:
none /run/shm tmpfs rw,noexec,nosuid,nodev 0 0
This will mount /run/shm writable, but without permission to execute programs, without permission to change the UID of running programs, or to create block or character devices in the namespace.
The changes will take effect the next time you reboot, unless you remount /run/shm with the command sudo mount -o remount /run/shm.
 SSH Settings, https://help.ubuntu.com/community/StricterDefaults SSH Settings, https://help.ubuntu.com/community/StricterDefaults
While the SSH daemon is secure enough for most people, some may wish to further enhance their security by changing certain sshd settings. Some settings which could be changed to enhance security are given here. All changes, unless otherwise stated, are made in the /etc/ssh/sshd_config file. Lines with a pound sign (#) are commented and not read. To edit this file from a terminal:
sudoedit /etc/ssh/sshd_config
For a Gnome editor, press Alt+F2 and use:
gksudo gedit /etc/ssh/sshd_config
For a KDE editor, press Alt+F2 and use:
kdesu kate /etc/ssh/sshd_config
Please remember, after making any changes, sshd must be restarted, which can be done from the terminal with this command:
service ssh restart (CentOS: sh /etc/init.d/sshd restart)
..., https://help.ubuntu.com/community/StricterDefaults .
 Configuring bastille, http://joshrendek.com/2013/01/securing-ubuntu/ Configuring bastille, http://joshrendek.com/2013/01/securing-ubuntu/
The Bastille Hardening program "locks down" an operating system, proactively configuring the system for increased security and decreasing its susceptibility to compromise. Bastille can also assess a system´s current state of hardening, granularly reporting on each of the security settings with which it works.
File permissions module: Yes (suid)
Disable SUID for mount/umount: Yes
Disable SUID on ping: Yes
Disable clear-text r-protocols that use IP-based authentication? Yes
Enforce password aging? No (situation dependent, I have no users accessing my machines except me, and I only allow ssh keys)
Default umask: Yes
Umask: 077
Disable root login on tty 1-6: Yes
Password protect GRUB prompt: No (situation dependent, I´m on a VPS and would like to get support in case I need it)
Password protect su mode: Yes
default-deny on tcp-wrappers and xinetd? No
Ensure telnet doesn´t run? Yes
Ensure FTP does not run? Yes
display authorized use message? No (situation dependent, if you had other users, Yes)
Put limits on system resource usage? Yes
Restrict console access to group of users? Yes (then choose root)
Add additional logging? Yes
Setup remote logging, if you have a remote log host, I don´t so I answered No
Setup process accounting? Yes
Disable acpid? Yes
Deactivate nfs + samba? Yes (situation dependent)
Stop sendmail from running in daemon mode? No (I have this firewalled off, so I´m not concerned)
Deactivate apache? Yes
Disable printing? Yes
TMPDIR/TMP scripts? No (if a multi-user system, yes)
Packet filtering script? Yes
Finished? YES! & reboot
 Link the dns resolver nslookup to the anonymizing tor-resolve Link the dns resolver nslookup to the anonymizing tor-resolve
We are going to write about Tor (The Onion Router) at the end of our excurs. If you already use Tor, secure up your system by linking nslookup with the DNS-anonymizing resolver tor-resolve:
make a copy of nslookup: cp -f /usr/bin/nslookup /usr/bin/nslookup-save
links nslookup with tor-resolve: ln -sf /usr/bin/tor-resolve /usr/bin/nslookup.
You can do the same for dns-resolving host and dig too.
Notice, that the output of those programs is not the same (but in all cases they do contain the IP for the domain requested).
For programs that do not work past this linking, enter the ip-domain-pairs in /etc/hosts and adjust /etc/nsswitch.conf. Read more about /etc/hosts at the end of our excurs.
At last, think about setting ACL-rights upon these files, see our section for setfacl.
 For our "Universal-Linux" (backported sytem) an actual kernel and actual kernel-firmware can be downloaded from PCLinuxOS, a backport of Fedora Core, Almalinux, ROSA, Mageia and Mandriva, http://ftp.pbone.net/mirror/www.pclinuxos.com/pclinuxos/ For our "Universal-Linux" (backported sytem) an actual kernel and actual kernel-firmware can be downloaded from PCLinuxOS, a backport of Fedora Core, Almalinux, ROSA, Mageia and Mandriva, http://ftp.pbone.net/mirror/www.pclinuxos.com/pclinuxos/
apt/pclinuxos/64bit/RPMS.x86_64/ or https://ftp.nluug.nl/ftp/pub/os/
Linux/distr/pclinuxos/pclinuxos/ or https://linux.palemoon.org and other URL. We strongly recommend LONGTERMED kernel-5.4.249 (pclos2023) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: Version 008)), glibc (el8, pclos) and kernel-firmware (pclos) and kernel-firmware-extra (pclos) and Konqueror (el6) with the intergrated adbocker resp. actual Firefox (ESR, the backported company edition) from http://ftp.scientificlinux.org/linux/scientific/6.9/x86_64/updates/security/ or http://mirror.centos.org/centos/6/updates/x86_64/Packages/ with extensions named on this webside in the following.
After the installation of kernel-4.19 (pclos), lookout for the requirements and install missing ones like kmod (pclos): "rpm -qi --requires kernel-4.19....".
 Deinstallation of programs (also see section "Updating/Updates"): If sudo, rpcbind, portmapper, sshd SSH-Daemon, rsh, telnet, avahi-daemon or cups-browsed daemon of the CUPS-system is not needed for example, it is possible to deactivate or deinstall them: "dpkg ..." , "rpm -e [nodeps]" source: https://wiki.kairaven.de/open/os/linux/tuxsectune Deinstallation of programs (also see section "Updating/Updates"): If sudo, rpcbind, portmapper, sshd SSH-Daemon, rsh, telnet, avahi-daemon or cups-browsed daemon of the CUPS-system is not needed for example, it is possible to deactivate or deinstall them: "dpkg ..." , "rpm -e [nodeps]" source: https://wiki.kairaven.de/open/os/linux/tuxsectune
 Quota Quota
Quota limits the memory consumption for a single user and/or group, so that an "overflow" of a volume resp. partition is prevented. For quota the kernal must be configured. If CONFIG_QFMT_V2 is set as modul, kernel modul quota_v2.ko is added to /etc/modules:
sudo echo quota_v2 >>, /etc/modules
For quota following packages have to be installed:
sudo aptitude install quota quotatool
If there is not any quota upon NFS-mounted file systems resp. RPC-quota-server, the service RPC-Remote-Quota-Server can be deactivated:
sudo systemctl disable quotarpc.service # sh /etc/init.d/quota... stop # and disable
In /etc/fstab the mount-options of the /fs file system are added with the options for the usage of journaling quota:
/etc/fstab
/fs /mountpoint ext4 optionen,usrjquota=aquota.usr/grpjquota=aquota.group,jqfmt=vfsv0|1
Use usrjquota for quota of user and/or grpjquota for groups. Volumes with a size of 4TB use quota-format vfsv1.
Finally restart the system, if the file system can not be mounted by the following command:
sudo mount -o remount /mountpoint
More details and source: https://wiki.kairaven.de/open/os/linux/tuxsectune
 Kernel-configuration Kernel-configuration
Deactivate as much as possible, that means all modules, that are not needed. The preconfiguration for single user is already set for the everyday life. This might differ from special requirements and development and a backup-kernel should be installed parallely too, if the configuration and the boot fails.
More details and source: https://wiki.kairaven.de/open/os/linux/tuxsectune
We are describing, how to configure and compile the kernel-source in our section for updates.
 Blocking of modules Blocking of modules
https://wiki.kairaven.de/open/os/linux/tuxsectune (resp. by "blacklist modul-name" within /etc/modules.d).
 Dienste mit systemd Dienste mit systemd
Removal and deactivation
Deactive all services, that are not needed. Either deinstall complete packages or, if a deinstallation is not wanted, use systemctl (alternatively: ntsysv, chkconfig or MCC#system-services (mdv2010) for deactivation).
More about security-settings for services by systemd and source: https://wiki.kairaven.de/open/os/linux/tuxsectune .
 at & cron at & cron
Resrict the users, that are enable to create and modify at (batch) and cron jobs, enable them within /etc/at.allow and /etc/cron.allow by entering them with their login-name line-by-line (only for users, that are enabled).
 Hardend compilation Hardend compilation
Flags, that can be set for the configure-Script.
Executable
´CFLAGS= -g -O2 -fPIE -fstack-protector-strong -Wformat -Wformat-security -Werror=format-security´
´CPPFLAGS= -D_FORTIFY_SOURCE=2´
´CXXFLAGS= -g -O2 -fPIE -fstack-protector-strong -Wformat -Wformat-security -Werror=format-security´
´LDFLAGS= -fPIE -pie -Wl,-z,relro -Wl,-z,now´
Shared Library
´CFLAGS= -g -O2 -fpic -fstack-protector-strong -Wformat -Wformat-security -Werror=format-security´
´CPPFLAGS= -D_FORTIFY_SOURCE=2´
´CXXFLAGS= -g -O2 -fpic -fstack-protector-strong -Wformat -Wformat-security -Werror=format-security´
´LDFLAGS= -fpic -Wl,-z,relro -Wl,-z,now´
If option "-fpic" does not work, use "-fPIC".
 Evtl. deinstall ( rpm -e packagename or rpm -e --nodeps packagename ) Evtl. deinstall ( rpm -e packagename or rpm -e --nodeps packagename )
ConsoleKit (el6, except /usr/libexec/ck*session-info*)
rpcbind (el6, mdv2010.2), sudo (el6, mdv2010.2), portmap (el6, mdv2010.2), dayplanner, mmc-agent (mdv2010.2), tracker (mdv2010), codeina (mdv2010), xguest (mdv2010), wu-ftpd (mdv2010), anonftp (mdv), mdkonline (mdv2010), f-spot (does not work on the base of updated mono (rosa2014.1), abrt (el6), funguloids (mdv2010.2), banshee (rosa,mdv) and amarok (rosa,mdv): unavailable for el6, both ones do not work, qmmp (el6, mdv) does not work, lxde (mdv2010, lxpanel tries to get inpredictable root-access).
 Start only the processes needed. Use net_applet from NetworkManager and not nm-applet. There might be an error in the skript for NetworkManager. Replace everything except last line in start() with "/usr/bin/NetworkManager --login-level=INFO". Start only the processes needed. Use net_applet from NetworkManager and not nm-applet. There might be an error in the skript for NetworkManager. Replace everything except last line in start() with "/usr/bin/NetworkManager --login-level=INFO".
Commercial modules: Linux and the NSA
tgruene, 16.10.2013
Bei dem letzten Newslink über Oracles Versuch, dem DOD den Vorteil kommerzieller Software zu erkläeren, kam mir der Gedanke, dass auf einem.typischen Linuxrechner eine ganze Reihe Module laufen, fuer die kein Quellcode zur Verfuegung steht (die dafür von US-amerikanischen Firmen zur Verfügung gestellt werden und somit vermutlich auch gesetzestreue (aka NSA-freundliche) Hintertüren enthalten), seien es Nvidia/ATI-Treiber, Virtualbox oder unter Debian vermutlich fast der gesamte Inhalt von firmware-linux-nonfree.
Mich interessiert, wie gut der Kernel und die Module voneinander abgeschottet sind - wie leicht ist es, solch einem Modul z.B. einen Keylogger einzubauen, der meine Passwörter beim Tippen abfängt und übers Internet irgendwohin schickt? Dass die NSA meine Emails liest, ist unverschämt, stört mich aber an sich nicht weiter, sonst würde ich ja keine Emails an Leute schreiben, deren Schlüssel ich nicht kenne, doch meinen GPG-Schlüssel und die Passwörter abzuhören - dagegen habe ich ganz ordentlich etwas.
 Terminal -> lsmod Terminal -> lsmod
/etc/modprobe.d/blacklist*
blacklist mei
blacklist it87 # disabled for Mainboard ASUS ITX-220
blacklist i2c_dev # ITX-220
blacklist coretemp # ITX-220
blacklist snd-usb-audio
blacklist snd_pcm_oss
blacklist snd_mixer_oss
blacklist snd_seq_oss
blacklist pata_acpi
blacklist rivatv
blacklist i82875p_edac
# do not use "Boot Protocol" drivers, we prefer usbhid
# and they cause problems when loaded together with usbhid (#37726, #40861)
blacklist usbkbd
blacklist usbmouse
# disable PC speaker by default
# pcspkr is the standard driver, while snd-pcsp is the ALSA driver
blacklist pcspkr
blacklist snd-pcsp
blacklist pcspkr
blacklist snd-pcsp
blacklist vhost
blacklist vhost_net
blacklist tpm_infineon
blacklist tmp_tis
blacklist tmp_tis_core
blacklist i82875p_edac
blacklist pcspkr
blacklist snd-pcsp
blacklist rivatv
blacklist i82875p_edac
blacklist pcspkr
blacklist it87
blacklist i2c_dev
blacklist coretemp
blacklist vhost_net
blacklist tpm_infineon
blacklist tmp_tis
blacklist tmp_tis_core
blacklist i82875p_edac
blacklist pcspkr
blacklist snd-pcsp
blacklist rivatv
blacklist i82875p_edac
blacklist pcspkr
# watchdog drivers
blacklist i8xx_tco
# framebuffer drivers
blacklist aty128fb
blacklist atyfb
blacklist radeonfb
blacklist i810fb
blacklist cirrusfb
blacklist intelfb
blacklist kyrofb
blacklist i2c-matroxfb
blacklist hgafb
blacklist nvidiafb
blacklist rivafb
blacklist savagefb
blacklist sstfb
blacklist neofb
blacklist tridentfb
blacklist tdfxfb
blacklist virgefb
blacklist vga16fb
blacklist matroxfb_base
# ISDN - see bugs 154799, 159068
blacklist hisax
blacklist hisax_fcpcipnp
 Partition-check during each system boot) Partition-check during each system boot)
This is described later on, but it might be such important, to tell it alrady at this place.
We assume, that the partitions got already encrypted with LUKS/dm-crypt (we are describing later on, how this can be made, if not). But the check will work upon unencrypted ones too. To be careful, we are going to check out partitions with file systems like ext4 each system boot, especially thinking of all the updating with rpm-packages in future.
| tune2fs -c 1 /dev/mapper/cryptedhomepartition |
resp.

| reiserfstune -m 1 /dev/mapper/cryptedroot_resp_home_resp_bootpartition |
resp.

| tune2fs -d 7 /dev/mapper/cryptedroot_resp_home_resp_bootpartition |
For unencrypted and not internal kernel-partitions replace the container-file "/dev/mapper/cryptedhomepartiton" with a device file like /dev/sda1.
Also activate in the device configuration file /etc/fstab the check each boot. Do this line (partition) by line (partition) more or less regarding "priorities&uot; of the check, by setting a positive interger not equal to zero behind the number (zero) for the (deactivated) dump at the end of the line: "0 1" for the root-partition, "0 1" or "0 2" for the home-partition and so on.
An example of the content of /etc/fstab as a whole is given further below.
 Apache-Webserver (httpd.conf) (analogous: LAN/Samba (samba.conf, database server/MySQL (my.cnf and mysld.conf) and other server, print-server (CUPS) see end of this website ) Apache-Webserver (httpd.conf) (analogous: LAN/Samba (samba.conf, database server/MySQL (my.cnf and mysld.conf) and other server, print-server (CUPS) see end of this website )
Now it is the turn for the webserver, almost Apache httpd 1.3 or 2.0. Basic functions are enriched by many loadable modules.
To see, which modules are really needed, have a look into /etc/apache/httpd.conf (CentOS 6 and CentOS 7: /etc/httpd/httpd.conf):
LoadModule autoindex_module /usr/lib/apache/1.3/mod_autoindex.so
LoadModule dir_module /usr/lib/apache/1.3/mod_dir.so
LoadModule cgi_module /usr/lib/apache/1.3/mod_cgi.so
LoadModule userdir_module /usr/lib/apache/1.3/mod_userdir.so
LoadModule proxy_module /usr/lib/apache/1.3/libproxy.so
Superfluos modules can be commented in by "#" plus blank at the very beginning of each line. Apache will work faster and will consumpt less memory the less modules are needed..
Only those modules should be loaded, that are really needed. The kind of server determines, which ones. Nevertheless there are modules, a standard webserver does not need:
* lib_status (presents a server-internal status)
* libproxy (an enormous security risk, as the webserver realizes a proxy for the accesses of other server)
* mod_cgi (to start so-called cgi-scripts. Such scripts are rarely used today as they are one more security risk)
* mod_userdir (generates a web-directory for each user)
In Debian, Apache 2.0 uses the file /etc/apache2/apache2.conf for configuration. All modules symbolically linked in /etc/apache2/mods-enabled are loaded by default. To deactivate such modules, the link has to be deleted.
After the config-files were changed,
apache -t
shows, if the configuration-syntax still is OK.
/etc/init.d/apache restart
oder
/etc/init.d/apache2 restart # C6 (el6): sh /etc/init.d/httpd restart
restarts the server, therewith the changes can take into effect.
Notice, that SuSE makes it the other way. Apache-modules are loaded within the file /etc/sysconfig/apache2. Look out in this file for the line with "APACHE_MODULES" and delete the entries not needed. After this,
SuSEconfig
has to be started out of the shell. Restart Apache by
rcapache2 restart
Get more infos about the task for each module, have a look at
http://httpd.apache.org/docs/1.3/mod/index-bytype.html und
http://httpd.apache.org/docs/2.0/mod/
More reports
Apache: Howto stop unwanted referer, https://www.strassenprogrammierer.de/apache-unerwuenschte-referer-stoppen_tipp_441.html
source. https://www.strassenprogrammierer.de/webserver-absichern-hacker_tipp_479.html
 Secure Apache/PHP/Nginx server Secure Apache/PHP/Nginx server
Edit httpd.conf file (CentOS: /etc/httpd/conf/httpd.conf) and add the following:
ServerTokens Prod
ServerSignature Off
TraceEnable Off
Options all -Indexes
Header always unset X-Powered-By
Restart the httpd/apache2 server on Linux
You must install and enable mod_security on RHEL/CentOS server. It is recommended that you edit php.ini and secure it too.
https://www.cyberciti.biz/tips/linux-security.html
 DDoS-Schutzdienst: DDoS-Schutzdienst:
Der DDoS-Schutzdienst ist in der Lage, selbst die komplexesten DDoS-Angriffe abzuwehren.
https://en.wikipedia.org/wiki/Denial-of-service_attack#Distributed_attack
https://www.cloudflare.com/learning/ddos/what-is-a-ddos-attack/
https://us.norton.com/internetsecurity-emerging-threats-what-is-a-ddos-attack-30sectech-by-norton.html
https://www.digitalattackmap.com/understanding-ddos/
 Lastverteilung: Lastverteilung:
Der Lastenausgleich geht häufig mit Ausfallsicherheitsmechanismen einher: Indem Sie einen Cluster mit der entsprechenden Kapazität aufbauen und die Anforderungen auf einzelne Systeme verteilen, können Sie die Ausfallsicherheit erhöhen Ausfallsicherheit, wenn der Ausfall eines Systems erkannt wird und die Anforderungen automatisch an ein anderes System gesendet werden.
https://de.wikipedia.org/wiki/Lastverteilung_(Informatik)
https://www.nginx.com/resources/glossary/load-balancing/
 HMAC authentication HMAC authentication
HMAC stands for keyed-hash message authentication code. A message authentication code protects against the modification of transmitted data by an attacker, who can read the data in real time. TLS use hash values (hence the H in HMAC) out of the numerous possibilities for the reliable authentication of messages.
https://en.wikipedia.org/wiki/HMAC
HMAC Authentication in Web API - Dot Net Tutorials
Understanding the Keys used in HMAC Authentication. Uses of HMAC Authentication in Web API. How does the HMAC Authentication work?
https://dotnettutorials.net/lesson/hmac-authentication-web-api/
What is HMAC authentication and how does it make VPN safer?
HMAC stands for hashed message authentication code and is an important factor in VPN security. Learn why strong HMAC auth matters for VPN security.
https://protonvpn.com/blog/hmac-authentication/
 Station-to-Station (STS) protocol, Cipher Block Chaining: Station-to-Station (STS) protocol, Cipher Block Chaining:
CBC stands for Cipher Block Chaining, which is every message depending on the previous passes. So can yourself short interruptions of the channel can be quickly noticed. Diffie-Hellman key exchange:
https://en.wikipedia.org/wiki/Diffie-Hellman_key_exchange A symmetric encryption scheme is used, the key of which is the negotiation of Diffie-Hellman key exchanges with elliptic curves. The server and the app use intelligent math to negotiate and verify the secret key, which is then used to encrypt the data for the entire session. Station-to-Station (STS) protocol: https://en.wikipedia.org/wiki/Station-to-Station_protocol In public-key cryptography, the Station-to-Station (STS) protocol is a cryptographic key agreement scheme. The protocol is based on classic Diffie-Hellman, and provides mutual key and entity authentication. Unlike the classic Diffie-Hellman, which is not secure against a man-in-the-middle attack, this protocol assumes that the partie s have signature keys, which are used to sign messages, thereby providing security against man-in-the-middle attacks. In addition to protecting the established key from an attacker, the STS protocol uses no timestamps and provides perfect forward secrecy. It also entails two-way explicit key confirmation, making it an authenticated key agreement with key confirmation (AKC) protocol. s have signature keys, which are used to sign messages, thereby providing security against man-in-the-middle attacks. In addition to protecting the established key from an attacker, the STS protocol uses no timestamps and provides perfect forward secrecy. It also entails two-way explicit key confirmation, making it an authenticated key agreement with key confirmation (AKC) protocol.
https://en.wikipedia.org/wiki/Block_cipher_mode_of_operation#CBC
 Pretty Good Privacy Pretty Good Privacy
PGP encryption uses a serial combination of hashing, data compression, symmetric-key cryptography, and finally public-key cryptography; each step uses one of several supported algorithms. Each public key is bound to a username or an e-mail address. The first version of this system was generally known as a web of trust to contrast with the X.509 system, which uses a hierarchical approach based on certificate authority and which was added
to PGP implementations later. Current versions of PGP encryption include both options through an automated key management server.
https://en.wikipedia.org/wiki/Pretty_Good_Privacy
 Perfect Forward Secrecy Perfect Forward Secrecy
With Perfect Forward Secrecy, even if a dedicated opponent is somehow able to attack the computer or server during a session, they will not be able to decrypt traffic from past sessions. The provider uses namely with each connection a new secret key. Even if you remain connected to the Server for a long period of time, the provider automatically changes the key every 60 minutes. This key renewal process every 60 minutes guarantees "Forward Secrecy". So if an attacker succeeds in compromising the key, in the worst case scenario, he could track the data for up to 60 minutes. Then everything is secret again.
https://en.wikipedia.org/wiki/Forward_secrecy
 Shadowsocks SOCKS5 proxy (all servers) Shadowsocks Proxy can be used by the provider through the application (Mac OS X, Windows, Linux, iOS, Android, Windows 10 Mobile). In addition, there is an advantage that "shadow socks" can not even be blocked in highly restrictive networks. Shadowsocks SOCKS5 proxy (all servers) Shadowsocks Proxy can be used by the provider through the application (Mac OS X, Windows, Linux, iOS, Android, Windows 10 Mobile). In addition, there is an advantage that "shadow socks" can not even be blocked in highly restrictive networks.
https://shadowsocks.org/en/index.html
 Smart DNS Proxy (all servers) Smart DNS Proxy (all servers)
There are currently two common ways to circumvent geo-blocks of foreign video-on-demand services such as Hulu, Netflix or Vudu. The first way is to use SmartDNS services. The term SmartDNS hides on innovative technology that has been specifically designed to bypass the geo-blocking barrier. To configure the SmartDNS service, there is only a minimal change to the TCP/IP properties of the network connection. Then, the user can freely use many suspended streaming services regardless of their current whereabouts.
http://www.unblock.ch/smart-dns-anbieter/
 DNS-Leak: DNS-Leak:
Eigene DNS-Server ohne Festplatten (RAM-Disk). Zusätzlich werden OpenDNS-Server (IPv6) verwendet (Auswahlmöglichkeit in den Einstellungen). Der Dienst schützt zuverlässig vor dem bekannten DNS-Leck.
https://www.hongkiat.com/blog/creating-ram-drives/
https://www.tomshardware.com/news/what-we-know-ddr5-ram,39079.html
https://www.opendns.com/about/innovations/ipv6/
 IP-Leak: IP-Leak:
Eine eigene Software verhindert zuverlässig Angriffe bekannter DNS-Leak-Methoden.
 WebRTC-Leak: WebRTC-Leak:
Der Service schützt zuverlässig vor dem bekannten WebRTC-Leak-Problem.
 Speicherschutz-Funktion (Schutz vor Serverausfällen): Speicherschutz-Funktion (Schutz vor Serverausfällen):
Diese Funktion ist in der Lage, den verfügbaren Arbeitsspeicher so aufzuteilen und laufende Programme so voneinander zu trennen, dass ein Programmierfehler oder Absturz eines einzelnen Programms nicht die Stabilität anderer Programme oder des Gesamtsystems beeinträchtigt (Speicherschutz-Mechanismus).
Serverausfall (Schutzmöglichkeiten):
Unterspannungsschutz (UVP)
Überspannungsschutz (OVP)
Kurzschlusssicherung (SCP)
Überlastschutz (OPP)
Überstromschutz (OCP)
Überhitzungsschutz (OTP)
Japanische 105°C Kondensatoren (Lebensdauer vom Netzteil)
Brandmelder (im Serverraum eingebaut)
Diese Schutzfunktionen (Netzteil) können die meisten Serverausfälle verhindern.
 Login methods, Two-Factor-Authentification (TOTP) Login methods, Two-Factor-Authentification (TOTP)
Two factor authentication can be implemented for SSH access or other application login, it will improve login security by adding a second factor of authentication, that is the password is typically known as something you know, while the second factor may be a physical security token or mobile device which acts as something you have. The combination of something you know and something you have ensures that you are more likely who you say you are.
There are custom applications available for this such as Duo Securityand Google Authenticator as well as many others. These typically involve installing an application on a smart phone and then entering the generated code alongside your username and password when you authenticate.
Google Authenticator can be used for many other applications than just SSH, such as for WordPress login with third party plugin support.
https://www.rootusers.com/23-hardening-tips-to-secure-your-linux-server/
4096 bit encryption/Eliptic-cuves-cryptography/
Two-Factor-Authentfication/connection (SSL/TLS encryption)/full IPv6
Support/HMAC-Authentifizierung/Cipher Block Chaining/Diffie-Hellman-Schlüsselaustausch/STS-Protokoll (Station-to-Station)/Pretty Good Privacy/Perfect Forward
Secrecy/encryption tool (Cloud Storage/Backup)/Failure Backup-solution/NAT-Firewall/
DDoS-protection/Lastverteilung/DNS-Leak/IP Leak/WebRTC Leak/WebRTC Leak/
Windows Login Leak/Arttifical Intelligence (NeuroRouting™)/Zero-Knowledge-Beweis/
Fiat-Shamir-Protokoll/Schnorr-Identification/SecureCore-function (security kernel)/
4096 bit encryption:
https://www.pcwelt.de/ratgeber/Verschluesselung_-_Was_ist_noch_unknackbar_-Sicherheits-Check-8845011.html
https://www.heise.de/security/artikel/Kryptographie-in-der-IT-Empfehlungen-zu-Verschluesselung-und-Verfahren-3221002.html?seite=all
https://de.wikipedia.org/wiki/Elliptic_Curve_Cryptography
https://www.heise.de/select/ix/2017/3/1487529933065685
https://www.computerweekly.com/de/definition/Elliptische-Kurven-Kryptografie-Elliptic-Curve-Cryptography-ECC
https://www.globalsign.com/de-de/blog/ecc-101/
https://www.ssl247.de/certificats-ssl/rsa-dsa-ecc
Two-Factor-Authetification(TOTP):
https://de.wikipedia.org/wiki/Zwei-Faktor-Authentisierung
https://www.pcwelt.de/ratgeber/Wichtige_Dienste_per_Zwei-Faktor-Authentifizierung_schuetzen-Sicherheit-8679969.html
https://www.security-insider.de/flexiblere-zwei-faktor-authentifizierung-an-vpns-a-700259/
https://www.security-insider.de/remote-access-vpn-mit-zwei-faktor-authentifizierung-a-389000/
http://www.itseccity.de/produkte-services/it-security/vpn-loesungen/ncp-engineering090315.html
Authenticator-App:
a) FreeOTP Authenticator
b) Authy
c) Microsoft Authenticator
d) LastPass Authenticator
e) Google Authenticator
 Kill hack-attempts against the Secure Shell Kill hack-attempts against the Secure Shell
In order to prevent hundrets of sshd-tasks starting at the same by a hacking attempt, add the line
MaxStartups 3:30:10
into the configuratio file /etc/ssh/sshd_config. This restriction is effective but complicated. The values in the example mean, that 2 (= 1. value minus 1) unauthenticated (and therefore in the Login-state assembled) sshd-connections are always allowed.
A third connection (= 1. value) is blocked by a probability of 30% (second value).
The probaliity of ending a connection is increasing linear, until up from 10 opened (built-up) connections (third value) each attempt to build up a connection is blocked at all at the rate of 100 in percent.
Notice, that useres already logged in do not refer to these values! The values in the example from above should suffer the need for each small and middle-sized server. If there are plenty of SSH-user, higher values might be recommended, for example:
MaxStartups 10:30:50 6
Source: https://www.strassenprogrammierer.de/sicherheit-ssh-hacker_tipp_480.html
 Forbid root-access for SSH Forbid root-access for SSH
Change the ssh-configuration:
nano /etc/ssh/sshd_config
and set
PermitRootLogin no
And to make it most secure, we add the following lines:
# Only permit user admin.
AllowUsers admin
# Generally block root or user of group root:
DenyUsers root
DenyGroups root
This lines can be added at the beginning of the file. Enhance the entry AllowUser, if further on more user are permitted for the SSH-login. New user are separated by a blank and not colon,. for example:
AllowUsers admin user1 user2 user3
Now the ssh-daemon gets started:
service ssh restart
Debian:
/etc/init.d/ssh reload
CentOS: sh /etc/init.d/sshd restart
Now we open a new session and try to login as root. By using the correct password, we get the message:
Access denied
Quelle: https://www.rechenkraft.net/wiki/Root_Server_absichern_(Ubuntu_14.04)
https://linux-scout.de/sicherheit/debian-server-absichern-so-machen-sie-es-richtig/
 Secure Linux Server Secure Linux Server
From Qloc Wiki
Here you find significant basics to secure a Debian/Ubuntu System. Except the tips listed here there are a lot of security precautions to make attacks more difficult.
Generally for all public systems essential services should only be accessible from the outside. Unused services like webserver or MySQL Server should eiteher be inaccessible with the help of iptables-rules or be deactivated.
Summary
1 Secure keywords (passwords)
2 SSH Port: secure up by change
3 Creating SSH-keys
4 Opening of required ports only
5 Prevention of Brute Force Attacks
6 Installing security updates
https://wiki.qloc.de/index.php/Absichern_eines_Linux_Servers
Right here we´d like to mention the server configuration files for many more security settings (like access/login, ACL-access-rights, log, bandwidth and server-ports (now "client"-ports) to open). Also search for adequate modules resp. securing server-extensions.
- Apache: mod_evasive against DDoS, mod_cband as traffic-Cop
- Fail2Ban for the https-vHosts- resp. htaccess authentification
- 24/7 monitoring with SMS alerting through an SMS Gateway via monit
- encrypted backups in two different computer centers
- instead of unencrypted ftp: SFTP. Transfer gets encrypted through sshd.
Configure an ftp-server working with ssl-encryption, it es similar to POP3 and IMAP. Then the transfers get secure, noone can read data.
Forbid anonymous accounts and run the ftp server in a chroot environment. This keeps away most annoynances.
Use ssh instead of ftpd just relying on ssh too.
Normalerweise ist das Verbinden mit einem FTP-Server mit SSL nicht schwieriger als mit einem ohne.
Just configure the ftp-client for the SSL-ecnryption and he will connect. The everyting works like connecting with a ftp-server without SSL. One will be just asked, if the certificate is accespted.
SSH use port 22. It is possible to upload files too, but the user once logged in has the possibility to access the system- except the account is chrooted.
...
https://serversupportforum.de/forum/security/28079-abschottung-wie-geht-es-nun-weiter-2.html
 Memory-protection-function (protection against server-breakdowns): Memory-protection-function (protection against server-breakdowns):
This function is be abled to separate the RAM into areas and distinguish processes the way, that programmers or breakdowns do not affect the stability of other processes or impairs the whole system (RAM-protection).
Server-breakdown-protection:
Low-Voltage-protection (UVP)
Overvoltage-protection (OVP)
Short circuit protection: (SCP)
Overload-protection (OPP)
Over current stream protection (OCP)
Over heat protection (OTP)
Japanese 105 degree condensators (lifetime of the netadapter)
Fire detectors (server room)
Chroot ( Befehl chroot ): is part of commands resp. communication-protocols like mount, ssh, stfp and effects one of the most serious hard threats! Help is given by sandboxes and/or/including the locking of the shells of the user (unfortunately a sandbox only, if a program works upon sandboxes, for example tor-browser does not (but migh have its own one). We are going to talk about this problem!
Chroot and Chroot-Jail (Chroot-Enviroment, Chroot-Sandbox)
https://wiki.debian.org/chroot
Step by step: https://www.linuxwiki.de/chroot
Chroot and Chroot-Jail, debian.org, wikipedia.org
A chroot on Unix operating systems is an operation, that changes the apparent root directory for the current running process and its children. A program that is run in such a modified environment cannot name (and therefore normally cannot access) files outside the designated directory tree. The term "chroot" may refer to the chroot system call or the chroot wrapper program. The modified environment is called a chroot jail.
https://wiki.debian.org/chroot
https://en.wikipedia.org/wiki/Chroot
Linux - Keeping users inside their home directory - Super User
If you use chroot like this, everything the user needs (executables, libraries, etc.) has to be within the chrooted directory. I´ve seen ftp-servers set up that way, with static executables copied into a bin directory.
https://superuser.com/questions/396282/keeping-users-inside-their-home-directory
How to configure ProFTPD to chroot users to /home directory or any ...
If you´re using ProFTPD user on a Linux server, you most certainly have wondered, how you can configure the FTP server to chroot (or jail) it´s users to a particular ...
https://www.pc-freak.net/blog/how-to-configure-proftpd-to-chroot-users-to-
home-directory-or-any-other-selected-directory-2
Furthermore past the configuration the server can run in a lower, but even more safer runlevel like runlevel 3 (command: "init 3") than common runlevel 5 or 6. mgetty resp. mingetty: terminal-switch ( ALT + CTRL + F1 up to F7), server configuration file (if it is possible there), systemd (sysctl) or chkconfig (to set the runlevel for the server during system boot)
 Coreboot - flashing the BIOS: Manufacturer BIOS-replacement by the Linux-System, https://www.kuketz-blog.de/sicheres-desktop-system-linux-haerten-teil1/ Coreboot - flashing the BIOS: Manufacturer BIOS-replacement by the Linux-System, https://www.kuketz-blog.de/sicheres-desktop-system-linux-haerten-teil1/
"System security already defines upon the hardware-level. Even today it might be difficult to find out WLAN-chipsets open source driver are provided. Exceptions like for AR9170 chipset are provided, same for the BIOS.
Idally Coreboot can replace the actual BIOS for a open-source, free BIOS. Otherwise hidden backdoors are risked usable by secret services.
We can be only really "secure", if open-source is used by hard- and software. [...].
Therefore I am urged for the project "hardened Linux" to make an exception and like to repeat, that this project does not protect against directed secret services.
I...] As I wrote with the first article, a secure operating system can only be obtained using Linux resp. Unix."
https://www.coreboot.org/Supported_Motherboards # u.a.
Many BIOS-variants are associated with software failures. Getting rid of them often implies updates from manufacturer. Beneath these unintended restrictions basic approaches exist to implement more functions in proprietary firmware (BIOS resp. UEFI) in future, that make afraid of more conscious restrictions of functionality.
Quelle: https://www.kuketz-blog.de/sicheres-desktop-system-linux-haerten-teil1/
https://www.kuketz-blog.de/sicheres-desktop-system-linux-haerten-teil2/
https://de.wikipedia.org/wiki/Coreboot
https://www.golem.de/0912/72132.html
With Coreboot the system-startup-time can also be declined.
 Copy the Bios-flashing file (.ROM) from manufacturer-DVD into the boot-partition too, in order to get loaded after pressing the function-key or the Bios-setup to flash, if required! Copy the Bios-flashing file (.ROM) from manufacturer-DVD into the boot-partition too, in order to get loaded after pressing the function-key or the Bios-setup to flash, if required!
 Shorten the boot-time for your Linux rapidly: For grub, exchange the value for the automized election to five or three seconds only. Shorten the boot-time for your Linux rapidly: For grub, exchange the value for the automized election to five or three seconds only.
Initscripts: use systemd or care for a short list through chkconfig by deleting as many scripts out of the list you can find in /etc/init.d as possible, therefore use chkconfig --del. Also repair listed loop-errors of such scripts in that way warned agains during the system-boot.
If you put order into the list of init-scripts, Linux like C6 (CentOS 6) will boot in less than one minute (upon Intel Celeron in less than 20 seconds) even faster than Debian!
Of course more boot time for the typing in of the password for the decryption of the LUKS-encrypted root-partition, the partition-checks and for the boot (startup) of the Desktop Environment at the end of the boot has still to be considered (added)!
Disable any network-connection-build-up, until the system got booted!
 hal resp. haldaemon extends the boot-startup-time for C6 (Centos 6) resp. "previous" mdv (2010-2012) until the KDE-login (kdm) without regarding the LUKS-passwort-login and harddisc-check by fsck (we thought of each boot) serious hard from around 20 seconds up to more than one minute ! hal resp. hald (haldaemon) might work faster by creating the file haldaemon within /etc/sysconfig with the follwoing include: hal resp. haldaemon extends the boot-startup-time for C6 (Centos 6) resp. "previous" mdv (2010-2012) until the KDE-login (kdm) without regarding the LUKS-passwort-login and harddisc-check by fsck (we thought of each boot) serious hard from around 20 seconds up to more than one minute ! hal resp. hald (haldaemon) might work faster by creating the file haldaemon within /etc/sysconfig with the follwoing include:
--child-timeout=15 # Begrenzung der Kindprozesse
--daemon=no
In /etc/dbus-1/system.d/hal.conf forbid some up to now allowed methods and devices, eventually like LightSensor and WakeOnLan, and in another subdirectorys haldaemon referring files like *dell-computer* eventually can just be deleted (removed)..
 Configuration of the CD/DVD-Rom-devices Configuration of the CD/DVD-Rom-devices
/etc/udev/rules.de/70-local.rules
SUBSYSTEM=="block", KERNEL=="sr0", SYMLINK+="cdrom", GROUP="cdrom", MODE:="0777"
 Konfiguration der Netzwerkschnittstelle
/etc/udev/rules.d/70-persistent-net.rules for mainboard ASUS ITX-220 Konfiguration der Netzwerkschnittstelle
/etc/udev/rules.d/70-persistent-net.rules for mainboard ASUS ITX-220
# This file was automatically generated by the /lib/udev/write_net_rules
# program, run by the persistent-net-generator.rules rules file.
#
# You can modify it, as long as you keep each rule on a single
# line, and change only the value of the NAME= key.
# Drakx-net rule for eth0 (cb:ad:b3:81:1a:53)
SUBSYSTEM=="net", ACTION=="add", DRIVERS=="?*", ATTR{address}=="cb:ad:b3:81:1a:53",ATTR{type}=="1", KERNEL=="eth*", NAME="eth0"
# PCI device 0x10ec:0x8168 (r8169)
SUBSYSTEM=="net", ACTION=="add", DRIVERS=="?*", ATTR{address}=="0b:01:ab:ba:3b:15", ATTR{type}=="1", KERNEL=="eth*", NAME="eth1"
First entry configures the interface as we hope NAME="eth0" for udev for the original mac-address in ATTR..., this is not the mac-address renewed by macchanger within /etc/rc.local later on, else set this exchanged one (renewed by macchanger already at this place), the second entry configures the PCI-interface of ITX-220 for, as we hope, NAME="eth1". This PCI-entry, or both entries, might be automatically generated by udev. Lookout, that belonging NAME is always eth0 is always the NAME in the first case (first entry) and eth1 in the last case (second entry) (and never eth0).
 ifcfg-eth0 ifcfg-eth0
/etc/sysconfig/network-scripts/ifcfg-eth0
DEVICE=eth0
BOOTPROTO=dhcp
ONBOOT=no
METRIC=5
MII_NOT_SUPPORTED=yes
USERCTL=no
DNS1=127.0.0.1
RESOLV_MODS=yes
LINK_DETECTION_DELAY=6
IPV6INIT=no
IPV6TO4INIT=no
ACCOUNTING=yes
DHCP_CLIENT=dhclient -4 -cf /etc/dhcp/dhclient.conf eth0
NEEDHOSTNAME=no
PEERDNS=no
PEERYP=no
PEERNTPD=no
TYPE=Ethernet
IPADDR=0.0.0.0
MACADDR=e1:a0:b0:cd:a1:b8 # original OR "black masked" hardware address (ethernet-card): Try /etc/rc.local. "macchanger --mac e1:a0:b0:cd:a1:b8 eth0" and set in Linfw3 "your IP" to the by this mac-address new resp. origin pregiven one (local IP) next (or past) the connection-build-up. The computer (system) might break down after all these changes, but after some newstarts, the system will gain its old´n good stability right back.
More network troubleshooting:
https://www.pcwelt.de/a/wlan-probleme-so-loesen-sie-typische-aergernisse,3389115
https://www.pcwelt.de/ratgeber/Fehlersuche-im-Netzwerk-LAN-WLAN-1953158.html
 Intall the actual netprofile (rpm: omv2015, pclos, rosa2014.1) only; never choose other (elder) buggish versions! Intall the actual netprofile (rpm: omv2015, pclos, rosa2014.1) only; never choose other (elder) buggish versions!
 If the interface is eth0 only, delete the following files: If the interface is eth0 only, delete the following files:
rm -df /etc/netprofile/profiles/default/network/var/lib/dhcp/dhclient-eth1.leases
rm -df /etc/netprofile/profiles/default/network/var/lib/dhcp/dhclient-eth1.leases
...
 Remove all other interfaces except eth0 from drbl.conf, choose eth0 only, if eth0 is the net-interface Remove all other interfaces except eth0 from drbl.conf, choose eth0 only, if eth0 is the net-interface
drbl.conf
nano cd /etc/drbl/drbl.conf
There should be only one interface named eth0 be configured, even shown in MCC. If the net-adapter does not build up the connection, look out for all passages in files with eth not valued zero like eth1, eth2 and so on! Use grep -R to find such files and remove them (such passages)! Update dhclient (el6) and netprofile including all netprofile-plugins to netprofile (rosa2016.1, omv4)! If there are still problems, have a hort time to plug out the net adapter of the DSL-Modem to plug it in again for a new connection build-up with the DSL-provider. Now the net adapter should work fine and, as we hope forever!
 Netz-Aliase Netz-Aliase
/etc/networks
default 0.0.0.0
loopback 127.0.0.0
link-local 169.254.0.0 # link-local 169.254.0.0 # In a computer network, a link-local address is a network address that is valid only for communications within the network segment (link) or the broadcast domain that the host is connected to. Link-local addresses are most often assigned automatically through a process known as stateless address autoconfiguration or link-local address autoconfiguration. Link-local addresses are not guaranteed to be unique beyond a single network segment. Routers therefore do not forward packets with link-local addresses.
For protocols that have only link-local addresses, such as Ethernet,[dubious - discuss] hardware addresses assigned by manufacturers in networking elements are unique, consisting of a vendor identification and a serial identifier.
Link-local addresses for IPv4 are defined in the address block 169.254.0.0/16 in CIDR notation. In IPv6, they are assigned the address block fe80::/10, https://en.wikipedia.org/wiki/Link-local_address.
 Preload-acceleration Preload-acceleration
The Tool Preload accelerates not the boot time, but program starts or autostarts (under "Start programs"), that are used often or regulary awaiting past each system login. This simple service protcols the program favorites and loads them into the RAM right before. The program start accelerates by this. Preload is obtainable as rpm and deb packet.
A manual configuration is not essential, but possible ("/etc/preload.conf") (start preload for example within /etc/rc.local)
https://www.pcwelt.de/ratgeber/Schneller_Linux-Start_ueber_Systemd_-_so_geht_s-Dienste_optimieren-8259105.html
 rkhunter, chkrootkit, Lynis - security check rkhunter, chkrootkit, Lynis - security check
With lynis an audit can simply be made:
su
lynis audit system --quick
After the first run one gets confronted with the total result named "Hardening index". "Warnings" and "Suggestions" howto secure resp. harden the system are shown during the scrolling.
https://www.kuketz-blog.de/linux-systemhaertung-basis-linux-haerten-teil2/
 Optimized usage of graphic cards and monitors in Linux, PC-WELT.de, 30.04.2021 Optimized usage of graphic cards and monitors in Linux, PC-WELT.de, 30.04.2021
[...] The standard installed Open-Source-graphic-card-driver are sufficient for the most user, for more optimized performance the proprietary driver from manufacturer migh be recommended.
https://www.pcwelt.de/ratgeber/Grafikkarten-Monitore-in-Linux-optimal-nutzen-11020222.html
 Delete X Windows on server Delete X Windows on server
X Windows on server is not required. There is no reason to run X Windows on your dedicated mail and Apache web server. You can disable and remove X Windows to improve server security and performance. Edit /etc/inittab and set run level to 3. Finally, remove X Windows system, enter:
# yum groupremove "X Window System"
On CentOS 7/RHEL 7 server use the following commands:
# yum group remove "GNOME Desktop"
# yum group remove "KDE Plasma Workspaces"
# yum group remove "Server with GUI"
# yum group remove "MATE Desktop"
https://www.cyberciti.biz/tips/linux-security.html
 X-Server: Howto secure up: Host- and cookie-based access X-Server: Howto secure up: Host- and cookie-based access
he number 1 rated high risk system vulnerability noted by the recent ISS audit of BNL was the use of "xhost +" or an open X display. Using "xhost +" allows anyone the ability to watch your keystrokes, capture windows and insert command strings into your windows. This situation is particularly bad when you have root access to a machine. There is no legitimate reason to run "xhost +". Most people will be using ssh to make their connections to other machines than their desktop and ssh tunnels X11 traffic, eliminating any need for "xhost +". To use turn on X11 forwarding with ssh call it like:
ssh -X host.domain
This can be turned on by default by adding the following to $HOME/.ssh/config:
Host *.bnl.gov
ForwardX11 yes
Make sure of the following things:
You should not set your DISPLAY variable, ssh will do it for you. It will look something like:
echo $DISPLAY
localhost:12.0
X11 forwarding must be allowed by the SSH server. Check /etc/ssh/sshd_config for a line saying "X11Forwarding yes".
On Linux/UNIX machines, the "xhost +" command can be issued at many locations, so you will have to remember, where you did it or find the location to turn it off (I believe that all recent version of the Linux X server have "xhost -" as the default). If you cannot find where the "xhost +" command is issued, adding a call to "xhost -" somewhere will turn it off.
Some of the most common files where you can find the "xhost +" command are in the X11 startup files. These file are
$HOME/.Xclients
$HOME/.Xclients.gnome
$HOME/.Xclients.kde
$HOME/.xinitrc
$HOMN/.xsession
/etc/X11/xinit/xinitrc
/usr/X11R6/bin/startx
/usr/X11R6/lib/X11/xdm/Xsession
Also, doing a man xinit will give you more information on startup files which are executed when one starts up X11.
If you want to test to see whether you have fixed the "xhost +" problem on your systems, log into another unix computer, disable the ssh X11 encryption channel by resetting the $DISPLAY environment variable back to the server port 0 of your desktop, and then try starting up an xclock. For example, type the following commands
ssh youraccount@yourfavoritunixserver.phy.bnl.gov
setenv DISPLAY yourdesktop.phy.bnl.gov:0
xclock
If an xclock pops up on your screen, you still have not properly enabled X11 access control. You should contact your computer liaison for further assistance.
Xterminals
To enable access control (set xhost -) on Tektronix Xterminals bring up the "Setup" menu (F3 key). In the "Configuration Summaries" pull down menu select "X Environment". On the X Environment page toggle "Enable Access Control" to "Yes". Return to the Main Menu and then "Save Settings to NVRAM". The terminal will now reject all X connections except those coming from the machine you connect to via XDM and those coming through tunnels to you XDM host created when you ssh to another machine. If you run "xhost +" on the XDM host, then you will again disable access control, so you should make sure that you do not do this in any of the X setup files (see the UNIX discussion above).
The following is an e-mail from Ofer Rind, who tells us how to enable X11 authentication on NCD Xterminals. Thanks Ofer for you post.
-----------
-
Disabling Xhost+ on an Xterminal
(NB: This was tried on both NCD and Textronix Xterminals and seemed to work; however, your mileage may vary. The description is for an NCD.)
Press Alt-F3 to pull up the Xterminal control bar. Select "Change Setup Parameters" from the "Setup" menu. When the setup parameters window pops up, select "Access Control." This will expand the menu, revealing an option called "Enable Access Control." Turn this on by pressing the adjacent square. Then, at the bottom of setup window, press the "Apply"
button to effect the change. This sometimes takes several seconds, be patient. When the arrow cursor returns, close the setup window and return to your previously scheduled program. X access control should now (hopefully) be enabled. NOTE that this access control can be superseded by a user who logs in on the Xterm and sets "xhost +".
Quelle: http://www.phy.bnl.gov/cybersecurity/old/xhost_plus.html
So our settings typed in terminal and /etc/rc.local after login to superuser by command "su" are (reset by "xhost +" on problems past the login):
xhost -
xhost +si:localuser:local-username
xhost +si:localuser:lokaler-Benutzername# lokaler-Benutzername: nur user, d.h. alle anderen Benutzer sind gesperrt, darunter Benutzer root, surfuser und toruser
xhost -si:localuser:root # bereits mit "xhost -"
xhost -si:localuser:toruser # bereits mit "xhost -"
xhost -si:localuser:surfuser # bereits mit "xhost -"
xhost -inet6:user@ # Das @-Zeichen muss bei inet6 (IPv6) im Unterschied zu si hinter dem Benutzernamen user stehen.
xhost -nis:user@ # nis: Secure RPC network
Output of command xhost:
access control enabled, only authorized clients can connect
SI:localuser:local-username
Do not set it for any other user, even NOT root! These simple two rules (for example in /etc/rc.local) make the system once more mouseclick-fast..
 X-Server, cookie-based access: MIT-MAGIC-COOKIE-1 X-Server, cookie-based access: MIT-MAGIC-COOKIE-1
When using xdm (X Display Manager) to log in, you get a much better access method: MIT-MAGIC-COOKIE-1.
A 128-bit "cookie" is generated and stored in your .Xauthority file. If you need to allow a remote machine access to your display, you can use the xauth command and the information in your .Xauthority file to provide access to only that connection. See the Remote-X-Apps mini-howto, available at
http://metalab.unc.edu/LDP/HOWTO/mini/Remote-X-Apps.html.
Cookie-based access
The cookie-based authorization methods are based on choosing a magic cookie (an arbitrary piece of data) and passing it to the X display server when it is started; every client that can prove having knowledge of this cookie is then authorized connection to the server.
These cookies are created by a separate program and stored in the file .Xauthority in the user´s home directory, by default. As a result, every program run by the client on the local computer can access this file and therefore the cookie that is necessary for being authorized by the server. If the user wants to run a program from another computer on the network, the cookie has to be copied to that other computer. How the cookie is copied is a system-dependent issue: for example, on Unix-like platforms, scp can be used to copy the cookie.
The two systems using this method are MIT-MAGIC-COOKIE-1 and XDM-AUTHORIZATION-1. In the first method, the client simply sends the cookie when requested to authenticate. In the second method, a secret key is also stored in the .Xauthority file. The client creates a string by concatenating the current time, a transport-dependent identifier, and the cookie, encrypts the resulting string, and sends it to the server.
The xauth application is a utility for accessing the .Xauthority file. The environment variable XAUTHORITY can be defined to override the name and location of that cookie file.
The Inter-Client Exchange (ICE) Protocol implemented by the Inter-Client Exchange Library for direct communication between X11 clients uses the same MIT-MAGIC-COOKIE-1 authentication method, but has its own iceauth utility for accessing its own .ICEauthority file, the location of which can be overridden with the environment variable ICEAUTHORITY. ICE is used, for example, by DCOP and the X Session Management protocol (XSMP).
https://en.wikipedia.org/wiki/X_Window_authorization
Fetch the magic cookie entry relevant to your local display:
[garth@server1 ~]$ echo xauth add xauth list ${DISPLAY#localhost}
xauth add server1.localdomain/unix:12 MIT-MAGIC-COOKIE-1 2928a6e16b7d6d57041dcee632764b72
Switch user to "oracle" and add the entry into your /home/oracle/.Xauthority file (by copying the ‘xauth add…´ line from above:
[garth@server1 ~]$ sudo su - oracle
[oracle@server1 garth]$ echo $DISPLAY
localhost:12.0
[oracle@server1 garth]$ xauth add server1.localdomain/unix:12 MIT-MAGIC-COOKIE-1 2928a6e16b7d6d57041dcee632764b72
xauth: creating new authority file /home/oracle/.Xauthority
After this your X-session should work…try something like "xcalc" or "firefox" to test it first and you should be ready to go!
http://www.snapdba.com/2013/02/ssh-x-11-forwarding-and-magic-cookies/
 Also use ssh to allow secure X connections. This has the advantage of also being transparent to the end user, and means that no unencrypted data flows across the network. Also use ssh to allow secure X connections. This has the advantage of also being transparent to the end user, and means that no unencrypted data flows across the network.
 Also disable any remote connections to your X server by using the ´-nolisten tcp´ option to your X server. This will prevent any network connections to your server over tcp sockets. Also disable any remote connections to your X server by using the ´-nolisten tcp´ option to your X server. This will prevent any network connections to your server over tcp sockets.
Take a look at the Xsecurity man page for more information on X security. The safe bet is to use xdm to login to your console and then use ssh to go to remote sites on which you wish to run X programs.
http://www.tldp.org/HOWTO/Security-HOWTO/password-security.html#AEN698
kdm: /usr/share/config/kdm/kdmrc
...
AllowNullPasswd=false
AllowRootLogin=false
AllowShutdown=None
AutoReLogin=false
...
ServerArgsLocal=-deferglyphs 16 -nolisten tcp
...
 X11: Graphic card adjustments, especially for opengl- and SDL-games X11: Graphic card adjustments, especially for opengl- and SDL-games
Adjustment influences system and graphic card.
BIOS-Setup: Northbridge -> COMBO-mode
Start driconf (hardware see data sheed)
Activate:
1) performance
+ synchronisation follows the verticale frequency rate, so that programs choose the minimal one
+ buffer object reuse: Enable reuse of all size of buffered objects
2 ) display (screen) quality
+ activate S3TC texture compression, even if unsupported by software
3) on failures
+ activate the immediate emptyting of the batch buffer each call for char
+ activate the immediate empying of the GPU-buffer
+ disable throttling on first batch after flush
+ force GLSL extension default behavior to "warn"
+ disable backslash-based line continuation in GLSL-source
+ disable dual source blending
+ perform code generation at shader link time
 Deny administrative remote access Deny administrative remote access
/etc/security/access.conf should be changed the way, that a remote access into an administrative account becomes impossible. By this user have to start the program su (or sudo) for administrative rights, so that there is always a track to check.
Add the following line into /etc/security/access.conf:
-:wheel:ALL EXCEPT LOCAL
Do not forget to activate pam-module each service (or the standard configuration), if you want changings within /etc/security/access.conf get noticed.
https://www.debian.org/doc/manuals/securing-debian-howto/ch4.de.html
 How to Check Password Expiration of User How to Check Password Expiration of User
In Linux, user´s passwords are stored in ´/etc/shadow´ file in encrypted format. To check password expiration of user´s, you need to use ´chage´ command. It displays information of password expiration details along with last password change date. These details are used by system to decide when a user must change his/her password.
To view any existing user´s aging information such as expiry date and time, use the following command.
 ftp-Sicherheitseinstellungen vornehmen: ftp-Sicherheitseinstellungen vornehmen:
Always care to set binar file transfer in your ftp-client (like gftp).
/etc/ftpusers
surfuser # user surfuser only
/etc/ftp-sites
/etc/ftpaccess
mail root@localhost
loginfails 1
readme README&asterisk; login
readme README&asterisk; cwd=&asterisk;
message /welcome.msg login
message .message cwd=*
compress yes all
tar no all
chmod no none
delete no none
overwrite no none
rename no none
log transfers anonymous,real inbound,outbound
shutdown /etc/shutmsg
passwd-check rfc822 warn
 Ablauf der Passwort-Gültigkeit überüfen Ablauf der Passwort-Gültigkeit überüfen
In Linux werden die Passwörter zu den Benutzerkonten in der Datei ´/etc/shadow´ in verschlüsselter Form abgespeichert. Um den Ablauf der Gültigkeit zu überprüfen, verwende man das Kommando ´chage´.
#chage -l username
To change password aging of any user, use the following command.
#chage -M 60 username
#chage -M 60 -m 7 -W 7 userName
Parameters
-M Set maximum number of days
-m Set minimum number of days
Quelle: https://www.tecmint.com/linux-server-hardening-security-tips/
 Checking Accounts for Empty Passwords Checking Accounts for Empty Passwords
Any account having an empty password means its opened for unauthorized access to anyone on the web and it´s a part of security within a Linux server. So, you must make sure all accounts have strong passwords and no one has any authorized access. Empty password accounts are security risks and that can be easily hackable. To check if there were any accounts with empty password, use the following command.
cat /etc/shadow | awk -F: ´($2==""){print $1}´
https://www.tecmint.com/linux-server-hardening-security-tips/
 Keep a (daily) watch onlog-files (for example with logwatch) as much as the last logins in /var/log/lastlog Keep a (daily) watch onlog-files (for example with logwatch) as much as the last logins in /var/log/lastlog
With the help of the command lastlog the content from /var/log/lastlog can be transferred into a readable format.
https://www.stefanux.de/wiki/doku.php/linux/hardening
 Services should not run as root-processes Services should not run as root-processes
deactivate services not needed (smalling the place for attacks): check out opened ports
netstat -lnptu
Internetsuperserver
veralteter inetd noch nötig?
xinetd sicher konfigurieren
(gefährdete) Dienste absichern:
nur auf einer bestimmten IP lauschen, auf andere Ports wechseln
evtl. Port-knocking einsetzen (Beispiel SSH)
Bind mit chroot
sicheren FTP-Server einsetzen: vsftp oder pure-ftpd
unsichere Dienste nicht für kritische Aufgaben (Login) zulassen:
FTP
Telnet
veraltete r-Dienste (rsh, rlogin, …)
nur notwendige Benutzerkonten einrichten
regelmäßig die Passwörter der Benutzer auf unsichere Passwörter überprüfen
leere Passwörter nicht erlauben
Kernel absichern
eigenen (minimalen) Kernel bauen
Integritätschecker, z.B. tripwire als cronjob laufen lassen. Die Signaturen sollten auf einem sicheren Drittsystem gelagert werden bzw. read-only gemountet sein (z. B. auf einer CD oder Diskette mit Schreibschutz)
Die Benutzung von Shadow ist meist schon aktiviert (shadowconfig on)
Protokolle (Logfiles) sichern:
Loghost einrichten oder
Logfiles absichern: Mit Secure Logging von Core-Wisdom können Sie Logfiles auch in mySQL-Datenbanken ablegen oder per Fingerabdruck gegen Veränderung sichern.
msyslogd oder
logrotate → Log per mail
regelmäßig nach suid-Programme suchen:
automatisch mit Programmen:
sxid schickt eine tägliche Report über dazugekommene suid/sgid per mail zu
manuell:
root-suids:
find / -perm -4000 2>/dev/null
allgemein suids:
find / -perm +6000
sgid-programme:
find / -perm -2000 2>/dev/null
volle Ausgabe mit allen Rechten bekommt man mit:
ls -lad --full-time ´find / -perm +6000´
Banner (Versionsnummern etc.) von Diensten abschalten
in /etc/motd die Kernelversion nicht anzeigen lassen, stattdessen Warnungen für Angreifer
SSH: Im Sourcecode
Webserver:
Logfiles studieren
Monitoring betreiben
Source: https://www.stefanux.de/wiki/doku.php/linux/hardening
 SVGA SVGA
SVGAlib programs are typically SUID-root in order to access all your Linux machine´s video hardware. This makes them very dangerous. If they crash, you typically need to reboot your machine to get a usable console back. Make sure any SVGA programs you are running are authentic and can at least be somewhat trusted. Even better, don´t run them at all.
Quelle: http://www.tldp.org/HOWTO/Security-HOWTO/password-security.html#AEN698
 GGI (Generic Graphics Interface project) GGI (Generic Graphics Interface project)
The Linux GGI project is trying to solve several of the problems with video interfaces on Linux. GGI will move a small piece of the video code into the Linux kernel, and then control access to the video system. This means GGI will be able to restore your console at any time to a known good state. They will also allow a secure attention key, so you can be sure that there is no Trojan horse login program running on your console.
http://synergy.caltech.edu/~ggi/
Source: http://www.tldp.org/HOWTO/Security-HOWTO/password-security.html#AEN698
 Disable USB stick to detect (recommended for companies etc.) Disable USB stick to detect (recommended for companies etc.)
Many times it happens that we want to restrict users from using USB stick in systems to protect and secure data from stealing. Create a file ´/etc/modprobe.d/no-usb´ and adding below line will not detect USB
storage.
install usb-storage /bin/true
https://www.tecmint.com/linux-server-hardening-security-tips/
Disbale USB/firewire/thunderbolt-devices
echo ";install usb-storage /bin/true" >> /etc/modprobe.d/disable-usb-storage.conf
echo "blacklist firewire-core" >> /etc/modprobe.d/firewire.conf
echo ";blacklist thunderbolt" >> /etc/modprobe.d/thunderbolt.conf
Once done, users can not quickly copy sensitive data to USB devices or install malware/viruses or backdoor on your Linux based system.
https://www.cyberciti.biz/tips/linux-security.html
 System-Banner System-Banner
Formulate any "welcome"-text after the login into the server on the system in /usr/lib/issue.net to make unwanted users really think, if to proceed or if it would be better to log out or get away..
 How to Spoof a MAC Address (identifying hardware address of the ethernet card) permanently
[...] A 48-bit MAC address (e.g., 08:4f:b5:05:56:a0) is a globally unique identifier associated with a physical network interface, which is assigned by a manufacturer of the corresponding network interface card. Higher 24 bits in a MAC address (also known as OUI or "Organizationally Unique Identifier") uniquely identify the organization which has issued the MAC address, so that there is no conflict among all existing MAC addresses. How to Spoof a MAC Address (identifying hardware address of the ethernet card) permanently
[...] A 48-bit MAC address (e.g., 08:4f:b5:05:56:a0) is a globally unique identifier associated with a physical network interface, which is assigned by a manufacturer of the corresponding network interface card. Higher 24 bits in a MAC address (also known as OUI or "Organizationally Unique Identifier") uniquely identify the organization which has issued the MAC address, so that there is no conflict among all existing MAC addresses.
While a MAC address is a manufacturer-assigned hardware address, it can actually be modified by a user. This practice is often called "MAC address spoofing." In this tutorial, I am going to show how to spoof the MAC address of a network interface on Linux.
Why Spoof a MAC Address?
There could be several technical reasons you may want to change a MAC address. Some ISPs authenticate a subscriber´s Internet connection via the MAC address of their home router. Suppose your router is just broken in such a scenario. While your ISP re-establishes your Internet access with a new router, you could temporarily restore the Internet access by changing the MAC address of your computer to that of the broken router.
Many DHCP servers lease IP addresses based on MAC addresses. Suppose for any reason you need to get a different IP address via DHCP than the current one you have. Then you could spoof your MAC address to get a new IP address via DHCP, instead of waiting for the current DHCP lease to expire who knows when.
Technical reasons aside, there are also legitimate privacy and security reasons why you wish to hide your real MAC address. Unlike your layer-3 IP address which can change depending on the networks you are connected to, your MAC address can uniquely identify you wherever you go. Call me a paranoid, but you know what this means to your privacy. There is also an exploit known as piggybacking, where a hacker snoops on your MAC address on a public WiFi network, and attempts to impersonate you using your MAC address while you are away.
[...] If you want to spoof your MAC address permanently across reboots, you can specify the spoofed MAC address in interface configuration files. For example, if you want to change the MAC address of eth0, do the following.
macchanger: Some things have to be done: "macchanger -r eth0" suggests a random MAC-address to add into /etc/rc.local (by "macchanger --mac new-MAC-address eth0"), same in /etc/sysconfig/network-scripts/ifcfg-eth0 and change the by this new obtained, local IP in LINFW3 (Dialog -> NONYESNO -> own IP), eventually restart the system.
On Fedora, CentOS or RHEL:
nano /etc/sysconfig/network-scripts/ifcfg-eth0
DEVICE=eth0
MACADDR=00:00:00:00:00:01
Alternatively, you can create a custom startup script in /etc/NetworkManager/dispatcher.d as follows, especially if you are using Network Manager. I assume that you already installed macchanger.
nano /etc/NetworkManager/dispatcher.d/000-changemac
#!/bin/bash
case "$2" in
up)
macchanger --mac=00:00:00:00:00:01 "$1"
;;
esac
... or macchanger -r "$1"
Quelle: https://xmodulo.com/spoof-mac-address-network-interface-linux.html
This might depend on the hardware. "macchanger -r eth0" can be started at the end of a dialin-script like /usr/sbin/ifup or ifup-eth too for example. The same is possible by ifconfig.
If all this does not function, try same or similar command manually by terminal after the dialin.
Find out the actual set MAC- resp. MAC-Fake-Adresse by
macchanger -s eth0 or
ifconfig
 Adjustments within /etc/sysctl/network-scripts/ifcfg-eth0 Adjustments within /etc/sysctl/network-scripts/ifcfg-eth0
DEVICE=eth0
# MACADRESS=....
BOOTPROTO=dhcp
ONBOOT=no # automized dialin each boot
METRIC=5
MII_NOT_SUPPORTED=yes
USERCTL=yes # user are allowed to configure the dialin and to dial in itself
DNS1=127.0.0.1
DNS2=203.13.81.14
RESOLV_MODS=yes
LINK_DETECTION_DELAY=6
IPV6INIT=no # perfer IPv4 with dynamic (changing) IP
IPV6TO4INIT=no
ACCOUNTING=no
DHCP_CLIENT=dhclient
NEEDHOSTNAME=no
PEERDNS=no
PEERYP=no
PEERNTPD=no
 Resolver configuration file Resolver configuration file
File /etc/host.conf contains special information, how to configure the resolver library with a configuration keyword each line, followed by belonging configuration information.
/etc/host.conf
order hosts,bind
multi on
reorder on
nospoof on
spoofalert on
Quelle: man host.conf
 NetworkManager-Configuration by /etc/NetworkManager/NetworkManager.conf: NetworkManager-Configuration by /etc/NetworkManager/NetworkManager.conf:
[main]
dns=none
plugins=keyfile
dhcp=dhclient
rc-manager=unmanaged
[ifupdown]
managed=false
[logging]
level=error
domains=none
More (secure) configurations of he NetworkManager by NetworkManager.conf see https://developer.gnome.org/NetworkManager/1.11/NetworkManager.conf.html
 Deactivate NIS Deactivate NIS
... in order to avoid password-sharing. For this, LDAP is recommended.
 Sicheres finger Sicheres finger
Es gibt viele finger-Daemon, als besonders sicher gilt ffingerd. Hier kann die Anzahl der zur selben Zeit laufenden Prozesse und die Anzahl der darauf zugreifenden Hosts limitiert und das verfügbare Interface eingegrenzt werden.
 Sichere Nutzung von PCs unter Ubuntu (und andere, Anm., Gooken)- für kleine Unternehmen und Selbstständige v2.0 (PDF, 189KB, Datei ist barrierefrei⁄barrierearm), BSI, 01.08.2018 Sichere Nutzung von PCs unter Ubuntu (und andere, Anm., Gooken)- für kleine Unternehmen und Selbstständige v2.0 (PDF, 189KB, Datei ist barrierefrei⁄barrierearm), BSI, 01.08.2018
https://www.allianz-fuer-cybersicherheit.de/ACS/DE/_/downloads/BSI-CS_009.html
 Guidance Guidance
EUD Security Guidance: Ubuntu 18.04 LTS
Created: 24 Jul 2018
Updated: 24 Jul 2018
https://www.ncsc.gov.uk/guidance/eud-security-guidance-ubuntu-1804-lts
 paxctld von grsecurity.net (Aufruf paxctld in /etc/rc.local mit "paxctld -c /etc/paxctld.conf -d -p /var/run/paxctld" paxctld von grsecurity.net (Aufruf paxctld in /etc/rc.local mit "paxctld -c /etc/paxctld.conf -d -p /var/run/paxctld"
https://wiki.gentoo.org/wiki/Project:Hardened/PaX_Quickstart
/etc/paxctld.conf (allowed is s,r,p,m and E)
e,E - https://pax.grsecurity.net/docs/emutramp.txt
m,M - http://pax.grsecurity.net/docs/mprotect.txt
p,P - http://pax.grsecurity.net/docs/pageexec.txt
r,R - http://pax.grsecurity.net/docs/randmmap.txt
s,S - http://pax.grsecurity.net/docs/segmexec.txt
https://en.wikibooks.org/wiki/Grsecurity/Additional_Utilities
#gdb
# /usr/bin/gdb srpm
# steam
# /usr/lib32/ld-linux.so.2 m
# /usr/lib64/ld-linux.so.2 m
# node
# /usr/bin/node m
# /usr/bin/perf m
# firefox
# /usr/lib64/firefox/firefox m
# /usr/lib64/palemoon/palemoon m
# tor-browser
# /home/toruser/tor*/Browser/firefox m
# /usr/lib64/thunderbird/thunderbird m
# oxide
/usr/lib/x86_64-linux-gnu/oxide-qt/oxide-renderer m
# valgrind
/usr/bin/valgrind m
# python
/usr/bin/python E
/usr/bin/python2.6 E
/usr/bin/python2.7 E
/usr/bin/python3.2mu E
# java
# /usr/lib/jvm/java-6-sun-1.6.0.10/jre/bin/java m
# /usr/lib/jvm/java-6-sun-1.6.0.10/jre/bin/javaws m
# /usr/lib/jvm/java-6-openjdk/jre/bin/java m
# /usr/lib/jvm/java-6-openjdk/jre/bin/java m
# /usr/lib/jvm/java-8-openjdk/jre/bin/java m
# /usr/lib/jvm/oracle-jdk-bin-1.8/bin/java m
# /usr/lib/jvm/oracle-jdk-bin-1.8/jre/bin/java m
# /usr/lib/jvm/zulu-8-amd64/bin/java m
# openrc
/lib/rc/bin/lsb2rcconf E
# tuned
# /usr/sbin/tuned m
# libreoffice
# Ubuntu doesn´t seem to carry this patch:
# https://bz.apache.org/ooo/show_bug.cgi?id=80816
# libreoffice will still run fine without the below line,
# but it will report an RWX mprotect attempt
# /usr/lib/libreoffice/program/soffice.bin m
 Lock virtual consoles except tty7 by default Lock virtual consoles except tty7 by default
/etc/inittab, comment in:
...
# Run gettys in standard runlevels
#1:2345:respawn:/sbin/mingetty tty1
#2:2345:respawn:/sbin/mingetty tty2
#3:2345:respawn:/sbin/mingetty tty3
#4:2345:respawn:/sbin/mingetty tty4
#5:2345:respawn:/sbin/mingetty tty5
#6:2345:respawn:/sbin/mingetty tty6
...
Start as few root-processes as possible!
 Remaining essential root-processes except those started by kernel (kthreadd): Remaining essential root-processes except those started by kernel (kthreadd):
init
X # xhost-access-control or run in usermode, see https://wiki.gentoo.org/wiki/Non_root_Xorg, and X with option "--nolisten tcp" (by default, check it out by pressing keys ESC + STRL and moving mouse over process X; configuration for X: /etc/X11/xorg.conf section "ServerLayout")
hald # makes acpid superfluosly
console-kit-daemon # needed only for the login, timeout possible
wpa-supplicant # part of NetworkManager
psad # or iptables: psd, port-scan-detection; start only with securing options like --no-rdns, --no-whois and --no-snort-sids
udevd # devices and interfaces
kdm
syslogd
klogd
gpm
cupsd
dhclient # or dhcpd etc.
pam_timestamp_c
master
spamd # alternatively try bogofilter for example always running in usermode
 Lost or forgotten password, no access onto the system? Lost or forgotten password, no access onto the system?
The steps you need to take in order to recover from this depend on whether or not you have applied the suggested procedure for limiting access to lilo and your system´s BIOS.
If you have limited both, you need to disable the BIOS setting that only allows booting from the hard disk before proceeding. If you have also forgotten your BIOS password, you will have to reset your BIOS by opening the system and manually removing the BIOS battery.
Once you have enabled booting from a CD-ROM or diskette enable, try the following:
Boot-up from a rescue disk and start the kernel
Go to the virtual console (Alt+F2)
Mount the hard disk where your /root is
Edit (Debian 2.2 rescue disk comes with the editor ae, and Debian 3.0 comes with nano-tiny which is similar to vi) /etc/shadow and change the line:
root:asdfjl290341274075:XXXX:X:XXXX:X::: (X=any number)
to:
root::XXXX:X:XXXX:X:::
This will remove the forgotten root password, contained in the first colon separated field after the user name. Save the file, reboot the system and login with root using an empty password. Remember to reset the password. This will work unless you have configured the system more tightly, i.e. if you have not allowed users to have null passwords or not allowed root to login from the console.
https://www.debian.org/doc/manuals/securing-debian-howto/ch12.de.html
 Checking file system integrity Checking file system integrity
Are you sure /bin/login on your hard drive is still the binary you installed there some months ago? What if it is a hacked version, which stores the entered password in a hidden file or mails it in clear-text version all over the Internet?
The only method to have some kind of protection is to check your files every hour/day/month (I prefer daily) by comparing the actual and the old md5sum of this file. Two files cannot have the same md5sum (the MD5 digest is 128 bits, so the chance that two different files will have the same md5sum is roughly one in 3.4e3803), so you´re on the safe site here, unless someone has also hacked the algorithm that creates md5sums on that machine. This is, well, extremely difficult and very unlikely. You really should consider this auditing of your binaries as very important, since it is an easy way to recognize changes at your binaries.
Common tools used for this are sxid, aide (Advanced Intrusion Detection Environment), tripwire, integrit and samhain. Installing debsums will also help you to check the file system integrity, by comparing the md5sums of every file against the md5sums used in the Debian package archive. But beware: those files can easily be changed by an attacker and not all packages provide md5sums listings for the binaries they provided. For more information please read Do periodic integrity checks, Section 10.2 and Taking a snapshot of the system, Section 4.19.
You might want to use locate to index the whole filesystem, if so, consider the implications of that. The Debian findutils package contains locate which runs as user nobody, and so it only indexes files which are visible to everybody. However, if you change its behaviour you will make all file locations visible to all users. If you want to index all the filesystem (not the bits that the user nobody can see) you can replace locate with the package slocate. slocate is labeled as a security enhanced version of GNU locate, but it actually provides additional file-locating functionality. When using slocate, the user only sees the actually accessible files and you can exclude any files or directories on the system. The slocate package runs its update process with higher privledges than locate, and indexes every file. Users are then able to quickly search for every file which they are able to see. slocate doesn´t let them see new files; it filters the output based on your UID.
You might want to use bsign or elfsign. elfsign provides an utility to add a digital signature to an ELF binary and a second utility to verify that signature. The current implementation uses PKI to sign the checksum of the binary. The benefits of doing this are that it enables one to determine if a binary has been modified and who created it. bsign uses GPG, elfsign uses PKI (X.509) certificates (OpenSSL).
https://www.debian.org/doc/manuals/securing-debian-howto/ch4.en.html
Solution: encryption of the root-partition, see Full System Encryption (FSE)
 Lifetime hardware, conductor pathes: secured contacts on graphic cards, boards and platines Lifetime hardware, conductor pathes: secured contacts on graphic cards, boards and platines
Sounds like it is our last advice (but of course it isn´t), not to forget to put some chalk into the computer tower inside. The trick is to keep contacts on mainboard including graphic-chip resp. graphic card and other electronic devices always rust-proof and save from moisture!
 Remove online accounts of internet service provider Remove online accounts of internet service provider
Phishing, profiling, spam, data handling, investigations by law, organized criminality, secret agencies, ad networks, large server farms, artificial intelligence, social bots, hacks, doxxing, honeypots, man-in-the-middle-attacks, ...: Before starting with the installation of "Universal Linux 2010" resp. before going to update programs and system, try to remove as much online-accounts as possible, that means as making sense for you: social media, Google, paypal, online banking, online shopping, ... This might become quit difficult: So read out belonging manuals and follow the instructions. For still existing accounts security settings should be made serious hard after the logins into the online portals.
 Allround-protection through iptables-firewall Linfw3 Allround-protection through iptables-firewall Linfw3
Linfw3 can be downloaded during further below. With Linfw3 all hacker and all trojans can be blocked, if only the user like surfuser within a group like surfgroup are allowed the password protected start of processes going online into the net. Even superuser root resp. uid 0 belongs to all the user, who are not allowed going online, only processes started by (surfuser) of group (surfgroup). By this, programs can go online in a very easy way, after belonging ports once got opened in Linfw3. This is the main advantage. The next advantage: All passwords except the ones for the LUKS-encrypted root partition get irrelevant - even if others know them! The access rights for files should be set local for each user only onto <=700 ( what can be done automatically per "umask 077" within /etc/fstab, manually by chmod or graphically through the context menu). The last risk remains in the Chrooting, settings by msec like "Forbid root-access", "Forbid extern access for root/forbid chrooting" and/or Sandbox firejail prevent by locking the consoles of the user accounts (including root (uid 0, gid 0), but except surfuser). Even the shell-login of all system- and user-accounts except surfuser can be restricted to /sbin/nologin too - no login possible. This can be done with msec_gui or by a special UNIX/Linux-(bash-)command). ACL-access-control (request by getfacl, settings by setfacl) can restrict processes owned (started) by surfuser access on all kind of (exectuable) files too. Scripts over once opened (established) net-connections can be blocked by Firefox-Extensions ABP, noscript and RequestPolicyBlockedContinued resp. Firefox >= 64 with mechanisms against Cross-Site-Tracking/-Scripting and all other kind of tracking. Beneath this, the Port-Scan-Detektor psad or psd of iptables activated by Linfw3 does its best too! And do not forget FSE (Full System Encryption by LUKS/dm-crypt) thinking of the command mount and therefore also cryptsetup (LUKS) including such chroot... All in all the remaining risk is given only by the started root-processes from kernel from the house Linus Tovalds, although they get blocked by Linfw3 too as long as owned by root by the way already depicted. Especially one root-process envokes some distrust - X (the X-Server, including the graphic card driver), but X can be restricted by own ACl through the command xhost as described in some points from above. There it is described, howto start X with option "-nolisten tcp" and that X can also be started in normal usermode. To get total paranoid, MAC (control resp. restriction of process interaction) might interest too - but that really mustn´t.
This excurs specifies Linfw3, firejail, ACL-Access Control Lists, MAC, Intrusion Detection Systems (IDS, if needed), important Firefox-Extensions upon opened connections and further methods later on, past the section for updating.
 Regardless from all Linux-distributions, one and the same Linux gets installed package by package, although this might not possible for each distribution as a fault of their specific architectures (library-structure and so on).
Regardless from all Linux-distributions, one and the same Linux gets installed package by package, although this might not possible for each distribution as a fault of their specific architectures (library-structure and so on).
 We would prefer the most complete Linux by electing certain distributions getting mixed to call it slackware either by installing a brandnew distribution to mix it up after getting updated or by the backport concept we are going to describe here. We would prefer the most complete Linux by electing certain distributions getting mixed to call it slackware either by installing a brandnew distribution to mix it up after getting updated or by the backport concept we are going to describe here.
Linux resp. (backported) "Universal-Linux" can origin in mdv2010.1 for example. It is updated long-termed and consequently with Fedora Project (fc), especially CentOS 6 (el6) and CentOS 7 (el7) resp. Scientific Linux (sl6/el6, sl7/el7) and fc -> EPEL (el6, el7) and other el6/sl6 and el7/sl7, where each source package is listed directly under the binary one on pkgs.org. It finally managed to stop leaving rubbish over rubbish of packages from all the outworn over outworn distribution behind. The speciality for the backport-concept is, that almost one and the same version with its own releases get patched over patched in many cases for the same version by new releases, what is marked in the rpm-package name behind the point at the end of the package name, until the intern code does its work stable and secure. So one and the same package-version of the same release got fixed resp. picked out and overworked and overworked until security and functionality (as amost the best sign for security) are given, leading to new releases to one and the same versions. Nevertheless the version might differ resp. change in some, quit seldom cases too.
 Secure Programming HOWTO, David A. Wheeler, 2015-09-19 Secure Programming HOWTO, David A. Wheeler, 2015-09-19
This book provides a set of design and implementation guidelines for writing secure programs. Such programs include application programs used as viewers of remote data, web applications (including CGI scripts), network servers, and setuid/setgid programs. Specific guidelines for C, C++, Java, Perl, PHP, Python, Tcl, and Ada95 are included. It especially covers Linux and Unix based systems, but much of its material applies to any system. For a current version of the book, see http://www.dwheeler.com/secure-programs
https://dwheeler.com/secure-programs/Secure-Programs-HOWTO/index.html
SuSE:
Suse Doc: Deployment Guide - Backporting Source Code
SUSE uses backports extensively. The information in this section helps you understand, why it can be deceptive to compare version numbers in order to judge ...
www.suse.com/documentation/sled11/book_sle_deployment/data/sec_update_backports.html
Debian:
Debian richtet neues Backports-Repositorium ein - Pro-Linux
Mit dem neuen Repositorium "lenny-backports-sloppy" stehen Debian-Anwendern künftig aktualisierte Programme ohne große Risiken und Mühen zur Verfügung.
www.pro-linux.de/news/1/16241/debian-richtet-neues-backports-repositorium-ein.html
This backporting is provided for CentOS for more than 10 years (CentOS 6: from year 2010 until year 2026), accompanied by CentOS 7 (until 2027).
Installed Linux can be completed to talk about this one and only Linux by installing packages from many other distributions too.
You can read more about CentOS and this fact in our section for Updates.
Alternatively you can order this complete mdv2010 already in an FSE-encrypted form (full system encryption by dracut and LUKS) preinstalled on SSD, where all updates past the update expiration time of mdv2010 including those from CentOS el7 and el6 are already installed. Now, just unpack the tarball of an actual Firefox (actual or actual ESR, extended security release from CentOS or Rosalabs) and Thunderbird (actual ESR (el6, el7)) into a directory like /usr/lib64/firefox-any-name and /usr/lib64/thunderbird-any-name and link the executable files /usr/bin/firefox by the command "ln -sf /usr/lib64/firefox-any-name/firefox-bin /usr/bin/firefox" to update firefox in future following the firefox-INFO-menu. We are going to describe the update of Firefox (and Konqueror) explicitly further below. At last you care for a more or less actual GNU C standard library (glibc(pclos)), for this purpose we tested mga6, ver. 2.22-29 form 17. June 2018. Of course all already installed glibc-packages can be upgraded to mga6 (2.22-29) or higher) or main glibc-package (mga6) with all other glibc-packages coming from el6.
 We decided us for kernel 5.4.110 (pclos) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) on the base of the GNU C Standard Library glibc-2.31 (pclos), glibc-2.22 (mga6) out of:
We decided us for kernel 5.4.110 (pclos) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) on the base of the GNU C Standard Library glibc-2.31 (pclos), glibc-2.22 (mga6) out of:
glibc (el8, pclos, mga6), glibc-headers (el8), glibc-common (el8), glibc-utils (el8), glibc-all-langpacks (el8), libc6 (rosa2016.1, rosa2014.1), compat-glibc (el6), glib2.0-common (pclos, el6), glibc-i18ndata (pclos, mga6), glibc-headers (pclos, el6), glibc-static (el6), glibc-utils (pclos, mga6), glibc-profile (pclos, mga6), glibc-glibc_lsb (rosa2016.1, rosa2014.1), locales (pclos, mga6), glib2 (el6), prelink (mga6, mga7, mga5, pclos, rosa2016.1, rosa2014.1), lib64stdc++ (pclos, mga6) or (and this is our tested-well choice:) glibc complete mga6 or: glibc (pclos, mga6 main glibc, rest-rpm: el6), libstdc++ (mga6), libsigc++ (mga6)
In order to avoid error-messages of glibc (el8) during system-boot, just remove the line LC_TIME=de_DE.UTF-8 in /etc/sysconfig/i18n ! Eventually install locales (pclos, mga7, mga6), locales-en, locales-de, ... too.
additionally, but be careful, miroplayer (el6) and the MCC-printer-administration might not work anymore: lib64glib2 (rosa2014.1), lib64gio2 (rosa2014.1), lib64gobjet2 (rosa2014.1), lib64gmodule2 (rosa2014.1). If they do not, reinstall glib2 (el6) and glib2.0-common (el6).
You can get all such glibc-packages from pkgs.org and rpmfind.net without any problems, but the new filesystem of glibc for mga3 since version 2.17 consists of new linked directories in directory root named /bin, /sbin, /lib and /lib64, so that all of their files have to be copied into equal named directories of /usr: /usr/bin, /usr/sbin, /usr/lib and /usr/lib64. This can cause programs like terminal "konsole" not working anymore, so that the cursor remains in the upper left corner of the started terminal, to think about other terminals like the recommended xterm and the very secure rated but no unicode supporting aterm and the next step to do like installing package (rpm) shadow-utils. Konsole is still functioning only, after devpts is mounted in the device-configuration-file /etc/fstab. This can be done by the following entry:
none /dev/pts devpts mode=620,gid=5
with gid for tty and in the user-administration of MCC set user to a member of group tty,wheel,lp. Now it is possible to install many packages from more actual distributions like not only mdv2011 and mdv2012, but also Mageia Cauldron 1 up to 4 and especially Fedora Project resp. CentOS 6.8 el6 (release: 2010, modificiaton release date (rpm) CentOS- resp. SL-release: 03.08.2015) and el7 (in the last two cases with update-guarantees until year 2026).Now software-packages are provided by rpmfind.net and pkgs.org for CentOS (resp. el6, el7, Scientificlinux (sl6, el6), ALT Linux, Repoforge (el6.rf), CERT Forensics Tools, PUIAS Computational, KBS Extras Testing, P.N., Nux Dextop (el6.nux), Rpmforge (el6.rf), Epel (el6), Atomix, Russian Fedora (el6.ru), NauLinux School (el6.nau), Nau Linux Extras, LinuxTECH und Ghettoforge (el6.gf)), Mandriva mdv2010, mdv2011, mdv2012, Mageia5 down to Mageia 1, Rosa2014.1, Rosa2012.1, newest Fedora, OpenSuSE and Tarballs and programs for any other OS to emulate from everywhere. With el6 and el6 you can follow the Gentoo-GLSA (https://security.gentoo.org/glsa/ ) update security list. We list each package in our section for updates. This all can also be made for other distributions, annoying, if not. Folllowing our steps, this OpenSource-System full of device-driver can be made incomparible secure, while the iptables-firewall Linfw3 bewares the central meaning. For more details, please follow the details from our excurs as follows, especially in the section for updates. For this please notice, that one should not be forgotten: to make 1:1-backups during the installation process on at least one extern storage media, especially by command dd.
report from 21.10.2004, last update: 06.23.2017. If you can not see a menu on the left side, please click here.
Time for the system boot < 1 second
It was long ago, year 2010, my computer satisfied my needs, even in future. Soon you will agree. You can not make more secure what is secure, same by versatile and who really follows this report by an everlasting, 100% secure computer-system including a ultraslim 18W-WLED-Monitor (TÜV certified) for about 200€ power-consumption 20 up to 40W only, all for about 200 &euro. Many other models might interest too. On our linksites section for "News&Links" ( we even found out Rasperry Pi 3 and especally C.H.I.P., a 3-W-computer for 9€, a model with much memory and as powerful as the smartphone. Further on we are going to present an independent from defragmentation and (included) virus-scanner and so on most secure Mandriva-Linux-computer-sytem from kiosks for only some Euro in year 2010, that is able to manage quit all one can imagine, because of its covering software seized in about more than 65 GB (15 DVD) quit for free. Not only the suspend-mode is working on our hardware, where the complete monitor gets "suspended", whenever you choose the resting mode resp. state (similar to the poweroff-state by hardware), Gooken of the computer tower blinks and Mandriva (2010) turns off all devices except RAM, in order to
"boot" the complete system in less than one second after pressing the powerbutton of your computer tower!
If this does not function, update acpid to at least 2.0.4 or el6. For these two suspend modes including hibernate of all in all four modes make yourself sure, that ACPI_2.0 is activated in the BIOS, that the SWAP-partition is sized by around 2 GB and that all USB-devices like usb-memory-stick are plugged out (umounted, umount and unplugged). Now the green LED of the computer-tower is blinking for mainboards like ITX-220 (details see data-sheed). Envoke the system again by pressing the power-buttom of the computer tower. Now a password request out of the OpenGL-screensaver (also used for the case of screen-locking) is made, but only if activated within power-management of systemsettings.
Here once again all energy saving modes (suspend modes) under "Universal Linux 2010" (backported system) in detail:
- blanked screen, readiness (passive) - dark blanked screen. Some power is already saved by this.
- locked screen - OpenGL-screensaver with user-password request - protection during all the (almost short kept) time, a user abandons the computer. Power is still consumpted, until power saving modes might get into effect.
- abandoned / suspended - The monitor is powered off (almost automatically after a some time set), but awakes again with the user activity like mouse-move, mouseclick or any keystroke. Saved power: 18 Watt monitor-power- consumption
- hibernation - the actual state gets saved into the SWAP-file, the computer seems to be "powered off completely" , while the BIOS blinks the green LED at the computer tower, but an awake resp. the backup of the state right before is possible by pressing the power-on/off-buttom of the computer-tower. After the awake, the user-password is requested to go on working with the computer in the state right before, if determined by the power-management of systemsettings; saved power: quit all 37 Watt.
- deep sleep - another kind of hibernation or similar to it, but the data is written onto the hard-drive resp. SSD. All internet connections (network manager) got closed after the awake in both last hibernation modes, so they have to build up again.
The following terminal-command
sudo rtcwake -m off -s 60
is well to test, if the hardware does support the "fast boot" (x86-hardware almost does, ARM-Rechner does it not always). Der Schalter "-m" bestimmt den ACPI-Modus. Mögliche Werte sind "standby", "mem", "disk" oder "off" (komplettes Ausschalten). Als zweiter Parameter ist hier "-s" ("seconds") mit einer nachfolgenden Zeitangabe in Sekunden angegeben. Der obige Testbefehl wird also das System herunterfahren und nach einer Minute neu starten (60 Sekunden). Obwohl mit Schalter "-t" ("time) auch exakte Zeitangaben möglich ist, empfehlen wir, den geplanten Neustart immer mit Parameter "-s" anzugeben. Es ist wenig Mühe, etwa zehn Stunden in Sekunden umzurechnen (10*3600=36 000).
Um Shutdown und Start zu automatisieren, kommt der Zeitplaner Cron ins Spiel: Nach dem Aufruf der Crontab-Editors mit
sudo crontab -e
schaltet folgender Eintrag
0 22 * * * /usr/sbin/rtcwake -m off -s 36000
den Rechner täglich um 22:00 Uhr ab und startet ihn nach 36 000 Sekunden (zehn Stunden) wieder - exakt um 8:00 Uhr.
https://www.pcwelt.de/ratgeber/Linux-Systemstart-beschleunigen-so-geht-s-8259105.html
And... much happened: incredible 38 Gigabyte Traffic with our websites last month April without making ads: Computer age without aging, no platform without fundamental IT security, so be welcome on the excurs for IT-security from Gooken on Gooken.de as a significant contribute to the successful interplay of informatics and society!
Now you can resign from things, that the world does not need! So everything is already authorized on DVD mdk2004 - except some special software like Nasa-moon-watch perhaps. After waiting quit the same long time, hardware fulfills important criteria too.
Starting Situation
Whoever posseses a "(mirolike) suneater" (a computer), one theme can interest: security. "Earlier so-called cybercriminals immobilized foreign calculators by computer-viruses, today the data thieves strip of whole bank accounts (by credit-card-betrayal, cracking of chips, debit entries, emails like scams, skumming, hacking and phishing");, wrote the press even after the millennium change. Eyes Since George Orwell we discuss the phenomenon of the Big Brother as someone trying to find out our habits, in order to achieve the aims for his few interests groups. Can´t enumerate all this: Spied offices and toilettes, cams in banks, in railway-stations and airports, right in front of petrol stations and bank automats: The eyes and ears of the big brother seem to be everywhere. Worlds get handicraft and abused (by censoring not fitting facts, opinions and views) .Trains were getting late, delrailed, while planes, cars and ships crashed or sank. Power supply systems had their blackouts, user konterminated by elements from platines and therefore got irrediated by the normal use of hardware, see postings form newsgroups cited and linked on our linkside. Significant preparations against thunder-storms were not made. Prices for power supply drifted. Votings were not encountered right. Opinions got suppressed and manipulated by positionings within search engines and legitimating rules, in some cases their listings took more into effect than prepunishment registers of criminal courts, unmanned airoplanes threatened with shooting us, corruption escalated.
Once, in year 2003, SuSE Linux 7.3 appears including four printed out manuals: one reference, one for the programs, one for networks, but still the market share for Linux except for server reached less than 10 percent. Linux has got the right intellectual touch, many people do not like. The handbooks interest a lot, but did not explain, how to create and manage a really secure computer system. Upon the base of a software surface covering distirbution like mdv-Linux from year 2010 we dare to say it managed us to do so by this excurs resp. report. This mdv also makes it possibles to emulate other popular operating systems on the platform of powersaving but ergonomic fast working hardware. Even diversified games for this distribution understand to convice us very much, many of them are running upon OpenGL and SDL. Nice to notice, and what is interesting most: They and all Software of this distribution do really, really run! See how risky other operating systems had been constituted, for not many people did believe us before it all happened with them:
Focus:de, February 2015: "Also unreal e-mails from betrayer and cyber-criminals are well known, it is a matter of a few seconds we click on such emails to make it happen. As soon as such email do open, we forbode this email not to be sent only to us. Dangerous viruses can take into effect (prevention: UNIX-Linux filesystems, spam-filter with a first virus-scanner like spamassassin and clamav prevent the propagation of viruses). The second next mistake is to open the atteachments and links too. Cyper-Criminals can rob millons of email-addresses by data-robbery. Inourdays plenty of time is spent online to be reachable so that we can get abused. The problem to protect the increasing amount of data becomes day by day more difficult Fingerprints are left in emails, by online-shopping (registrations, tracking-scripts), whats-app-news and more."
 Viruses, trojans, worms, bots: 40 percent of the computers are "zombies", Focus, 02.03.2014
Viruses, trojans, worms, bots: 40 percent of the computers are "zombies", Focus, 02.03.2014
The amout is alarming: 40 percent of all PC in Germany are infectedt and can be remoted by cybercriminals. Once set free, malware opens the backdoorr for more abuse. How to protect: The amount of infected computer increased last year up to 40 percent, confirmed the Anti-Botnet-Support-Center of the internet community Eco. More than 220.000 computer with old browser-versions have been scanned. This forwards to trojans and viruses. In many cases, the first varmint opens the door for more infecitons, describes the community. "Zombie-computers" could be remoted. Infected so colled "zombie-computers" could be remoted by cybercriminals. "Their systems are engaged as part of networks, that are abused by criminals for abuse like spam-transfer or denial-of-service-attacks, leading to die immense harms", described Markus Schaffrin, the ECO security expert. The result is alarming, said Eco. For more security, a well configured firewall and anti-virus-scanner remained essential. Focus explains, how you can find the best virus-scanner (we, Gooken, think it´s clamav. This open sourced scanner is always checked well, as he can be installed on all popular operating systems).
Linux does not work? How you can solve every driver-problem, PC-WELT.de, 04.07.2017
Linux runs on quit all PC and notebooks, but not each hardware periphery is recognized automatically. For new devices some problems are possible.
[...] Linux-distributions provide a wide hardware support and run on quit all PC. With SATA, ethernet, graphic-card and monitor as much as mouse and keyboard there are no problems at all awaiting. Those basic functions should be warranted each case.
Elder printer, scanner or tv-cards without driver for Windows 7, 8 or 10 can often be reused for Linux, but for very new or seldom devices sometimes there is no support pregiven. Before the installation tests for hardware-compatibility should be made.
Report in german language onle: https://www.pcwelt.de/ratgeber/So-bringen-Sie-Linux-trotz-Probleme-zum-Laufen-9789269.html
New nvidia-driver cause system-breakdowns, PCWelt.de, 10.03.2016
Nvidia´s new graphic card driver 364.47 cause serious hard problems for some PC-user. Concered user can do the following: http://www.pcwelt.de/news/Neue-Nvidia-Treiber-364.47-sorgen-fuer-Abstuerze-9943889.html .
Even a supergau in Fukoshima took place! Even have a look onto the section for "News&Links" from our left menu! If we follow such reports, we remind of emergancies, catastrophes and incalculatable payments. Since computer-technique seems to be part in almost everything (Na/ST), it and the companies behind seem to be quit liable for all, in person also see our linkside....! One question seems to be central:
Do we reign computers, or do computer reign us?
Computing begins, where it ends
Green LED vs. red LED: "Yes, I think I´am OK vs. yes, I think I am (the) stupid idiot (while our own system signs: "..." with one very short blinking point more or less periodically after the other one in around two up to ten seconds, asking the user back for "any complaints?", reminding him for "more activity, please..." and saying "I tell you...(heartbeats)"), what shall not confound with the three LED at the top of the num-block the keyboard saying to the user "Hi!" and "bye" resp. "out of order" (kernel-panic). All or something, that of course is not essential anymore in the case of touch-screens, and that´s the naked truth. The own computer should be no disadvantage and not stand for riscs (red LED) without loosing his advantages and opportunites (green LED). Computer systems should not think about themselves, that they are stupid for all, by making themselves work with capacities reducing and control wresting self-checks for virus-scans, bot-processes, bugs (program-errors), processes of trojans and self-maintenances as the cause of their technical unjustifiance. This is almost self-signaled by the blinking orange or red LED of the computer-tower. A solution far from MS Windows is found since year 2004 resp. 2010: Gooken does present even more a (classical, quit everlasting) computer-system on lowest costs with quit all software almost in top-graphic running as secure and stable without much blinking of the red LED as computer can! In spite of red marked text and our linksite you become a witness of the eight wonder of the world named "the almost 100% security bewaring computer running on lowest cost, where there is quit no software of rubriques of all kind missing", even not of games and TOP-games! Please do not forget to read our linksites from the left menu section "News&Links" These linksites contribute to the right understanding of the work with the computer and, although we are going to provide the promised security by this excurs, many remaining threatenings from the outside are still awaiting! For security studies for MS Windows, please have a look upon News&Links too.
Very past installation phase, a system almost free from security-leaks, maintenance and administration will be provided. The only thing one has to do from time to time is, to install some actual updates.
MS Windows "Replacement": Windows-Emulation by virtualbox, VM, qemu, xen, mingw and wine (mdv2010), same for MAC-OSX by BasiliskII and Amiga by uae and so on
Through wine, winecfg and at last playonlinux of mdv2010 emulation of software running on MS Windows (98, XP, 7, ... ) including MSOffice and Internet Explorer 6 up to actually 8 is not the problem anymore (although in our opinion with the well-equipped mdv2010 we need much or anything of it...). More than 100 Top-Games: see our data sheed.
Frontend playonlinux presents software, that can be installed groupwise like accessories, development, education, games, graphics, internet, entertainment, office and others and offers the following software in detail beneath many other one to install:
MS Office, MS Word Viewer, Intenet Explorer, 6 up to (actually) 8, Google Picasa, WowApp, 7-Zip, Ultimateencoder, Amazon Kindle, Azuon, Cadstd Lite, PDU Spy, Photofiltre Studio X, Dreamweaver, Codeblocks, Flashplayer, Flash 8, Flash MX, Notepad++, Graph, Teach2000, Simultit, Rocket Reader, Huckel 95, Adobe Photoshop, Fireworks8, Microsoft Paint and more, more than hundred games see our data sheed!
playonlinux installs different Wine32 and Wine64 depending on the programms chosen.
It also offers installation of any setup.exe regardless from the download out of the internet, that means from harddrive or CD/DVD too.
Installation
Wine: How to use the Windows-Replacement in Linux, PCWelt.de, 08.11.2015
Wine is a a clone of the Windows-API with many windows-programs to run under Linux too. Whenever functioning, it is in opposite to virtualization (virtualbox, Xen, qemu, ... ) the more direct way: http://www.pcwelt.de/ratgeber/Wine-So-nutzen-Sie-Wine-als-Windows-Ersatz-9790018.html, zahlreiche Top-Games aus playonlinux siehe unter Datenblatt.
PCWelt also presents security tipps for the user, PCWelt.de, 03.08.2015 and 22.08.2015
Create your VPN (private internet tunnel)
Most public WLAN-net are - as already told by name - public. Hacker, equipped even with only a few programs, can "catch" the traffiic from the next area. Although it is useful to provide more security by calling websites per https in the address-line of a browser, it is not the best solution. A private network (VPN) should be used, in order to provide an encrypted data-tunnel between your device and the internet. There do exist versions of such programs for free like "Hide My Ass", "Hotspot Shield" and "Tunnel Bear"- a payed VPN belongs to the better alternatives (or use the real secure freeswan, strongswan, openvpn or openswan). The versions to pay like Hide My Ass cost 40 € the year for example and protectis not only your PCs but also your mobile devices.
libreswan (rpm): "Libreswan is a free implementation of IPsec & IKE for Linux. IPsec is the Internet Protocol Security and uses strong cryptography to provide both authentication and encryption services. These services allow you to build secure tunnels through untrusted networks. Everything passing through the untrusted net is encrypted by the ipsec gateway machine and decrypted by the gateway at the other end of the tunnel. The resulting tunnel is a virtual private network or VPN.
This package contains the daemons and userland tools for setting up Libreswan. To build KLIPS, see the kmod-libreswan.spec file. Libreswan also supports IKEv2 (RFC4309) and Secure Labeling. Libreswan is based on Openswan-2.6.38 which in turn is based on FreeS/WAN-2.04"
 You can use a virtual private network-client for free like OpenVPN (or Freeswan, Anm., die Red.), in order to connect to a VPN-service, where you have an account, so that you can visit the internet through an encrypted access. This is a good reason for VPN, but not the only one. Maybe you do not want, that your internet provider surveys all your online-activities at home. Normally, if you go online, the provider can survey all of your activities. By VPN your internet service provider can only see the connection to the VPN. Besides from this VPN help you to bypass regional restrictions for websides like Amazon, Hulu, Netflix and BBC iPlayer. One example for a VPN-provider is the company IPredator from Schweden offering VPN-services for eight Dollar the month, keeping its connection to the famous torrent-tracking-site "The Pirate Bay". IPredator promises not store any traffic data of their user. You can also use PGP-encryption, if you contact IPredator-support per mail. One more popular VPN-provider is Private Internet Access, that promises not to protocol traffice data too. PIA costs 7 Dollar per month or 40 Dollar the whole year. PIA also helps to bypass reginal blocks in the USA, Canada, Great Britain and several countdries in continental europe. Although VPN protects your privacy, provider of websites like Facebook and Google can protocol your internet-activites. The use of your anonymous-private-mode of your browser is not caring for complete anonymity, but it keeps websites from reading out your cookies and the histroy of your browser, in order to get more to know about you. We are going to see, what we can do, comment by Gooken.
You can use a virtual private network-client for free like OpenVPN (or Freeswan, Anm., die Red.), in order to connect to a VPN-service, where you have an account, so that you can visit the internet through an encrypted access. This is a good reason for VPN, but not the only one. Maybe you do not want, that your internet provider surveys all your online-activities at home. Normally, if you go online, the provider can survey all of your activities. By VPN your internet service provider can only see the connection to the VPN. Besides from this VPN help you to bypass regional restrictions for websides like Amazon, Hulu, Netflix and BBC iPlayer. One example for a VPN-provider is the company IPredator from Schweden offering VPN-services for eight Dollar the month, keeping its connection to the famous torrent-tracking-site "The Pirate Bay". IPredator promises not store any traffic data of their user. You can also use PGP-encryption, if you contact IPredator-support per mail. One more popular VPN-provider is Private Internet Access, that promises not to protocol traffice data too. PIA costs 7 Dollar per month or 40 Dollar the whole year. PIA also helps to bypass reginal blocks in the USA, Canada, Great Britain and several countdries in continental europe. Although VPN protects your privacy, provider of websites like Facebook and Google can protocol your internet-activites. The use of your anonymous-private-mode of your browser is not caring for complete anonymity, but it keeps websites from reading out your cookies and the histroy of your browser, in order to get more to know about you. We are going to see, what we can do, comment by Gooken.
Howto configure and establish VPN-connections can be read here (in german language): http://pdf.zeit.de/digital/datenschutz/2013-01/serie-mein-digitaler-schutzschild-vpn-ipredator.pdf .
The risk remains by the VPN-provider, as he knows the IP-address - so you have to convice him. This is the central disadvantage in opposite to Tor.
I2P is a decentral network connecting users, in order to make an point-to-point- (end to end-) encryption possible. It is still under development and provides an experimental additon to other methods for encryption or anonymization.
Tor is a connection-based low-latency anonymous communication system. This package provides the "tor" program, which serves as both a client and a relay node. Scripts will automatically create a "toruser" user and group, and set tor up to run as a daemon when the system is rebooted. Applications connect to the local Tor proxy using the SOCKS protocol. The local proxy chooses a path through a set of relays, in which each relay knows its predecessor and successor, but no others. Traffic flowing down the circuit is unwrapped by a symmetric key at each relay, which reveals the downstream relay. Warnings: Tor does no protocol cleaning. That means there is a danger that application protocols and associated programs can be induced to reveal information about the initiator. Tor depends on Privoxy and similar protocol cleaners to solve this problem. This is alpha code, and is even more likely than released code to have anonymity-spoiling bugs. The present network is very small -- this further reduces the strength of the anonymity provided. Tor is not presently suitable for high-stakes anonymity., rpmfind.net about tor, 18.01.2016
Another example, why to resign from TOR is named by PCWelt.de:
"In November last year the anonymizing-network Tor started his first spend campaign. With overwhelming success. Exact 205.874 US-Dollar (around 190.262 Euro) from 5265 different givers are taken by the project Tor during six weeks. With this amount of money, the Tor project is going to reduce the dependencies from the US-government, financing Tor of about 80 up to 90 percent. As the US security agencies try to infiltrate the tor-network, it makes sense Tor making more independent from USA. Alleged the US-policei FBI spent one million dollar to an explorer of the Carnegie Mellon University, in order to help the FBI, to intrude into the anonymizing-network. The NSA is going to crack TOR too.", http://www.pcwelt.de/news/Erfolgreiche-Spendenkampagne-fuer-Anonymisierungs-Tool-Tor-9916676.html
Tor - no absolute security, heise.de, 30.08.2016
The anonymizing network like Tor left security leaks and access points: if many Tor-nodes gets observed, conclusions to the location as much as identity of a user can be drawn - and not only by institutes by law than NSA. There are some tor-based virusses and malware on their way - probably seldom, but really existant, http://www.heise.de/download/product/tor-browser-40042 .
 Protect the router
Protect the router
The most important connection to the internet for the everyday life is your router at home for the use of online banking and so on, where sensible data is transferred. So do not use ever the same passwords, especially not that of the router. For most secure home connection always use WPA2-encryption and random generated login-passwords out of at least 30 characters, that should be kept within a password-manager. One more report about router is following below at the end of step 1 of this excurs.
 Security updates: Critical leaks in root-security in SD-WAN-routern of Cisco, CHIP, 01.30.2021 Security updates: Critical leaks in root-security in SD-WAN-routern of Cisco, CHIP, 01.30.2021
Admins of Cisco-hard- and -Software should install the actual security patches. Otherwise attackers can attack the networks and execute malicious code, in oder to win the control over them.
https://www.trojaner-info.de/business-security/aktuell/sicherheitsupdates-kritische-root-luecken-in-sd-wan-routern-von-cisco.html
 Resign from Java (whenever possible)
Resign from Java (whenever possible)
Oracle´s Java does not belong to the required software for PC-user for our relief. Java is full of lacks in security. Security experts postulate from Oracle the complete overworking of Java. January 2013 they advised all PC-user to deactivate Java as possible, that means except the cases where Java is needed. One should wholehearted attempt to delete Java from system completely and at once! This can be done for MS Windows by the system control. Nevertheless, if a webside requires Java, the recommend of installing actual Java software is not missing.
 Be careful with the password-recovery of mail accounts
Be careful with the password-recovery of mail accounts
Make hacker the life as hard as possible. Use different mail-accounts with different passwords kept in a password manager with hard to hack address names like "myrec0v3ry_ZMf43yQKGA@outlook.com". Then hacker can not hack in an easy way and especially not all passwords at once.
 Do not use only antivirus-software but also anti-malware-scanner
Do not use only antivirus-software but also anti-malware-scanner
Virus scanner alone do not cover and remove all malware. It is a good idea to use malware-scanner too.
 Screen the webcam
Times were known, malware sended word-documents all over to email-contacts. This can get even more and more worse, if computers are suited with webcams and microphones. Put adhensive tapes, maybe with paper between, over the lense of the webcam. Whenever the webcam is needed by the user, he just has to deduct it.
Screen the webcam
Times were known, malware sended word-documents all over to email-contacts. This can get even more and more worse, if computers are suited with webcams and microphones. Put adhensive tapes, maybe with paper between, over the lense of the webcam. Whenever the webcam is needed by the user, he just has to deduct it.
Databasis (SQL)
 Password-protection for MySQL after the login into MySQL by starting the daemon mysqld and entering "mysql -h -localhost -u username -p" in order to type into beloginging terminal:
Password-protection for MySQL after the login into MySQL by starting the daemon mysqld and entering "mysql -h -localhost -u username -p" in order to type into beloginging terminal:
| grant usage on *.* to ´username´ identified by ´password-to-set´; |
This method is advised as secure. Alternatively, but for some protocollings not such secure:
| SET PASSWORD FOR ´username´ = PASSWORD(´password-to-set´); |
The (own) computer should escape from the dark empire, here named by Miro´s "Suneater", but how?
Technical failures cause from human ones. "The way is the target", means their leader Konfuzius. Gooken itself is a meeting place for the scientific based IT-Security since computer might run secure. Its excursion is introducing the security-concept without the accumulation of any costs for consultation, training, conversion and licenses. It does so by realizing a secure and standard company management database and an everlasting as possible, standard IT-Security-concept for your computer-system through all of companies (fields, mandators, master, departments, standard-processes, editor, printouts, diagrams, security) intergrating Mycompanies company management in PHP-MySQL standard with intergratable PHP-FCKEditor for text-fields, also all ready for WEB-2.0-and 3.0-technology, the determination of security levels, computer-manual, (security-)commands, checklist and prototypes in order to resign from scans from hard-disks as much as from the amount of essential updates and upgrades to none (!) at all as much as possible, a deep look into the work resp. code of search-engines like Gooken, "News&Links" especially for the friends of MS Windows to carry on and more. In comparison with other projects, those of Gooken do not only consist of an everlasting character, but also find an end to the very beginning!

Theory
All this direct help online is offered to beware stable positions right before law and opposite fellow men. It is is realized by adjustments and downloads consisting of SQL through company.
management, pdf like the computer-manual with checklist and surface covering security-software for prevention, diagnosis and repair to solve the survival-request of computer-age with its central rating for computers completely concretisizing the book "Security in Information Technology" second edition by Prof. Dr. Kersten, Oldenbourg-Hochschulverlag from 1995. Therefore Gooken tries to contribute to the calm, troublefree enterprise! Quit all needs and security problems of the computer can be solved! Gooken offers
Introduction-"basics" to reach the highes IT-security-level" as possible, and a pdf containing also next step 2 to reach an enhanced IT-security-level, pdf system-(security-)commands and pdf checklist,
Anonymizing Proxyserver
surfing with the anonymizing base64-, rotate-13 URL- and SSL-encrypting Proxy and den base64, rotate13, nonssl Proxy for free (with restricted capacity for dowloads) programmed by Abdullah Arif. In both cases, for payment as much as for free, IP are not only exchanged, but also all kind of scripts including tracking-scripts beneath cookies get blocked, by choosing the option "remove scripts". This is important to avoid methods like Canvas Fingerprinting, details see our "online check". If there is no access for our free proxy, try https://www.vtunnel.com.
Webdesign- and programming in HTML, JavaScript, PHP, PHP-MySQL and MySQL
Search engines
 Many search-engines tell us, that we can search secure, because they resign from storing the IP of their user. But since Edward Snowden june 2013 the fact is,
that many search engines host on server within the USA, even those recommended by so called privacy protectors. Such search-engines have to refer to the Patriot Act and US-law and therefore have to serve the full access of US-authorities. So they can not offer protected privacy (even not, if they try. source: metager, year 2014).
Many search-engines tell us, that we can search secure, because they resign from storing the IP of their user. But since Edward Snowden june 2013 the fact is,
that many search engines host on server within the USA, even those recommended by so called privacy protectors. Such search-engines have to refer to the Patriot Act and US-law and therefore have to serve the full access of US-authorities. So they can not offer protected privacy (even not, if they try. source: metager, year 2014).
German government and the EU-commission, Tagesschau, 21.05.2014: Mundt supports the demands of Bundeswirtschaftsminister Sigmar Gabriel postulating a hard reglementation and the annihilation of the Google concern. Paris also postulates for harder rules. The minister and his french administration colleague Arnaud Montebourg postulted in a letter to sharpen the suggested conditions for Google. Indeed the ministre from Berlin and Paris do not find the sympathy of the EU-competition commissioner Joaquin Almunia signed by scepsis against the annihilation of Google. But all with Google is by far not obivious. It can not be exclude the commission following all the compaints against Google in further processes by law, explained Almunia at the same time.
 Instead the platform independent Gooken is a self-learning search-engine with SSL-support. Gooken was developed for answering still unanswered questions in conjunction with IT-security past our excurs with downloads as much as for any purpose. You are searching completely anonymously, no click-registration by meta queried searchengines! Actually, no data are stored, neither your IP nor the user-agent-specification of your browser! Gooken resigns from tracking-scripts, participating in a web-advertisement net as much as from server-farms! You can open all websites anonymously.
Instead the platform independent Gooken is a self-learning search-engine with SSL-support. Gooken was developed for answering still unanswered questions in conjunction with IT-security past our excurs with downloads as much as for any purpose. You are searching completely anonymously, no click-registration by meta queried searchengines! Actually, no data are stored, neither your IP nor the user-agent-specification of your browser! Gooken resigns from tracking-scripts, participating in a web-advertisement net as much as from server-farms! You can open all websites anonymously.
Open Website Reputation: Gooken 100/100
downloads making Linux, what it proclaims to be: free from any intrusions, without any hacker and any trojan and therefore secure independent from most distribution and version: Linfw3 - the unbeatable fortress with protection against insecure browser-plugins - the comfortable end of all hacker and trojan (for single user, client, server) - besides Klean, Rename-Manager, the (LAN-supporting, platform-independent) PHP-MySQL-library Bibliomaster, platform-independent PHP-MySQL company-management-database Mycompanies and
a filterlist for the adblocker of the konqueror and other adblocker from the Easylist and during the time collected entries
Trials against small money for the attempt to improve your online-reputation within the internet on price at agreement
Fedora and CentOS (resp. ALT Linux) Updates, Linux for Security, and Top Seven by Susan Linton - Jan. 17, 2014, Comments (0)
Related Blog Posts
Microsoft Linux, Fedora 23 Beta a GO
Magical Mageia Review, Mint 17.3 Named Rosa
LinuxToday was another interesting day in the newfeeds, so much so I can܌t pick just one. There were several headlines focusing on Fedora or CentOS (resp. ALT Linux) today. Linux.com has posted a top seven distro list for 2014 and Jack Wallen says CESG recommends Linux for security. Tha´´s not all either. First up today, Jack Wallen over at TechRepublic.com published an article discussing the results of the United Kingdom´s Communications-Electronics Security Group (CESG) operating system security tests. The tests consisted of 12 categories of security focus such as Disk Encryption, Authentication, and Platform Integrity and Sandboxing. As if there was any question, Linux proved the most secure of all the desktop and mobile systems tested. So, be sure to check out Wallen´s article for more detail and relevant links.
Operating Systems and covering well designed Software ready to start: after all those computer systems really one to work and game with (stable)!
mdv on USB-memory-stick: Opensource from (bootable) DVD, (bootable) USB (-memory-stick and memory-cards), from DVD onto SSD and HDD, so take the - as we think - one time chance to avoid in future not only computer-techique but also all operating systems. This can be performed by the shell-script mandriva-seed, unetbootin and other programs.:
mdv on DVD: from mdv-final for quit all devices - comuter-final, computing has right begun, where it ended: Opensource-2010-FINAL, secure, easy to handle, but most comfortable Linux fullfillingFSH 2.3 (Filesystem Hierarchy Standard) and ISO-standard-LSB 4.0, with 65 GB (15 DVD) + Fedore rpm + unlimited software from see our data-sheed (left menu) also recommended by prism.break.org, stable and secure from DVD onto your SSD (and/or harddrive) with lifetime installation-support, fc-SuSE-mdv: We also offer complex as much as the mdv2010 already updated, stable and secure Linux-distribution powerpack+final version mdv2010.0 from year 2010 (x86_64, 64-bit, optionally MAC based ("NSA-")Tomoyo-Linux by NTT DATA Corporation, Japan) with driver-comfortable kernel 2.6.31 (2.6-final resp. Knoppix 2010 like mdv-2010-Kernel 2.6.33-7-2, 2.6.39 (with allow-discards-support for FSE and FDE and patches up to actual date from see in our section for updates) or kernel-5.4.249 (pclos/PCLinuxOS) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) and glibc (el8, pclos), kernel-rsbac (hardened), RFC-rules bewaring methods for encryption, Firefox 3.6.17 you can update to an actual version like Firefox ESR, patched bash, LUKS/dm-crypt (cryptsetup) with most driver for desktop-computer, all postscript-based printer, PPD from manufacturer or diver-CD, alternatively see compatibilty-list and foomatic-, PPD- and cups-filter-driver and cupsddk (cups driver development kit) from these DVD or Linuxfoundation, openprinting.org and powerpack+ from year 2007 (i586, 32-bit), many graphic-card-drivers including IPG-driver intel, IGP-openchrome and IGP-unichrome3D, ati-, nvidia- and the universal VESA-standard-graphiccard-driver and other ones; each version out of one installation-DVD (1) for the binary-packages (rpm), one DVD for more mdv-2010-software-packages, most already known from mdk10.1 (2004) (2) including Debian Linux paket-manager (apt, dpkg, alien), debbuild (el6), debmirror (el6) more drivers and software listed in the data sheed below and one DVD for the belonging (updated) sourcecode-packages (3): 3 DVD Linux total, stable and secure mdv2010.0-final (x86_64) or mdv2007-powerpack+(i586), 3 × 4,4 GB comfortable, most stable and secure Linux total, free from shipping costs, for 20 € 24h-livetime-support from fr2.rpmfind.net and sources or installation-DVD mdv2010.0 from http://linuxisos.de for 8 € (2013), or
mdv from SSD: 65 GB mdv-software (15 DVD for mdv2010 out of mdv2010.0, updates, mdv2010.1, mdv2010.2 including all GLSA-updates except KDE and 2014 patched bash and openSSL 1.0.2, Firefox ESR ) extract see data sheed plus source-rpm from your sent-in at least 120GB sized SSD, FSE (FDE) of all partitions: root (around 65 GB) , (by keyfile from the root-partition automounted) home (around 25 GB), SWAP (around 3GB) and one more partition (around 30GB), 24h-livetime-support from fr2.rpmfind.net or
After the installation of kernel-4.19 (pclos), lookout for the requirements and install missing ones like kmod (pclos): "rpm -qi --requires kernel-4.19....".
mdv out of the internet: mdv2010-packages for free from: http://fr2.rpmfind.net/linux/RPM/mandriva/2010.0/x86_64/index.html, http://fr2.rpmfind.net/linux/RPM/mandriva/2010.1/x86_64/index.html and, http://fr2.rpmfind.net/linux/RPM/mandriva/2010.2/x86_64/index.html 24h-livetime-support from fr2.rpmfind.net and sources, plus quit all Linux-tarballs,
kernel-5.4.249 (PC-LinuxOS) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6, version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) and glibc (el8, pclos) resp. kernel-desktop-2.6.39 (mdv-2011-standard-kernel), kernel-server-2.6.39 (standard-kernel with patches up to now, year 2016, from see our section for updates), kernel-linus-2.6.31 (original kernel from Linus Tovalds), kernel-rsbac (hardened kernel), kernel-uml (protected usermode-kernel), xen-Kernel (XEN-virtual machines), lirc-kernel (infrared-driver), kernel-tmb (laptop), kqemu-kernel (kquemu-driver for the standard-kernel), vpnclient-kernel (vpnc-driver), fglrx-kernel (nvidia-driver), em8300-kernel, broadcom-wl-kernel, hfsmodem-kernel, madwifi-kernel (WLAN-driver), libafs-kernel, lzma-kernel, kernel-rt (SMP-onboard-Realttek/Atheros-LAN-BIOS-Chip with an activatable LAN-ROM), fusion-kernel (fusion-driver), kernel-netbook, kernel-openvz (SMP: multiprocessor-kernel), libafs-kernel, kernel-kerrighed (kerrighed-Support), obencbm-kernel, psb-kernel, actuator-kernel (actuator-driver), lzma-kernel (lzma-driver), m560x-kernel, broadcom-wl-kernel, nvidia-current-kernel, nvidia96xx-kernel, nvidia173-kernel, netfilter-rtsp-kernel, fortune-kernel, vhba-kernel (vhba-driver), em8300-kernel, r5u870-kernel, r5u870-kernel-laptop, squashfs-lzma-kernel, vboxadditions-kernel, virtualbox-kernel, actual Kernel-3.X.X (from fr2.rpmfind.net or kernel.org), ...
Notice, that in order to keep transparency and other aspects, the system boot does not in main follow the kernel with its many firmware, but the runlevel-init-scripts out of /etc/rc.runlevel0-6 out of tarball resp. rpm named initscripts and util-linux, almost steered by the script named init.
uml-kernel: User-Mode-Linux is a safe, secure way of running Linux versions and Linux processes. Run buggy software, experiment with new Linux kernels or distributions and poke around in the internals of Linux, all without risking your main Linux setup. User-Mode Linux gives you a virtual machine that may have more hardware and software virtual resources than your actual, physical computer. Disk storage for the virtual machine is entirely contained inside a single file on your physical machine. You can assign your virtual machine only the hardware access you want it to have. With properly limited access, nothing you do on the virtual machine can change or damage your real computer, or its software; you need an uml-kernel and an adequate root-fs-filesystem of about 1GB from http://uml.devloop.org.uk/; start: #./smb-kernel-name ubda=name-of-root_fs rw mem=256m; stop: #halt.
The Filesystem Hierarchy Standard (FHS) defines the directory structure and directory contents in Unix and Unix-like operating systems, maintained by the Linux Foundation. The current version is 2.3, announced on 29 January 2004.[1]
Only some Linux-distributions fullfill the Filesystem Hierarchy Standard and LSB standard. The Linux Standard Base (LSB) itself is a joint project by several Linux distributions under the organizational structure of the Linux Foundation to standardize the software system structure, including the filesystem hierarchy used in the GNU/Linux operating system. The LSB is based on the POSIX specification, the Single UNIX Specification, and several other open standards, but extends them in certain areas. According to the LSB, the goal of the LSB is to develop and promote a set of open standards that will increase compatibility among Linux distributions and enable software applications to run on any compliant system even in binary form. In addition, the LSB will help coordinate efforts to recruit software vendors to port and write products for Linux Operating Systems. The LSB is registered as an official ISO standard. Linux Standard Base aims to make binaries portable.
mdv2010.0, LSB-version by after typing in the command
LSB Version: lsb-4.0-64...
Distributor ID: MandrivaLinux
Description: Mandriva Linux 2010.2
Release: 2010.2
Codename: Adelie (Napoleon, annotation by the red.)
With mdv2010 software is not only covering, it also can be displayed advantageous and interesting:
Window-administration (die hält, was sie verspricht): always-in-foreground, always-in-background, remember, force of positioning and seizing function and so on, fringes, work surface assignment, window-heaver, menü for behaviors, screen-edges, window-effects, changes of windows, actions, activation, spezific settings, ...
Effects for the desktop: kiba-dock, 3D-window-galery, 3D-windows-stack, fade in and out for the system-login and -logout, cube, preview (of minimized windows), showcase with miniaturized images for opened windows, translucency, transparency, dimming, zoom, auto-reticle for centering, gliding, magnifier, shadow, wonderlamp (during the maximizment of minimized windows), wave, ... on the base of composite: spotlighter (justable desktop-spotlight), ardesia (desktop-sketching), curtain (curtain to move on the desktop from one side to the other)...; like plasmoids without markable loss of performance for active processes of mdv2010.

Key-strokes for KDE-desktop-effects: STRG+F9 or mouse pointer into upper left corner: preview with mini-pictures of opened windows, ALT+TAB: window change, STRG+ALT+Scrollrad: window-transparency, STRG+Arrows: cube-rotation of the workplaces
Plasmoids resp. plasma (applets) for the desktop and the controlbar (please notice, that in differnence to mdv2010-rpm-packages actually not all of them do function, so we have to wait, and that some of them get their information
Desktop right upper corner with halfmoon-plasmoid: toolbox out of add control-line, configuraiton of key shortcuts, adjustment for the active-directory-perspective, enlargement/declinement of fonts and symbols and unlocking of the (plasmoid-)miniprograms

to present out of the internet): Daisy (free program choice within rings or bars), Lancelot (desktop-menu), timezones and weather, birthday-reminder, calculator, widget-dashboard, system-monitoring, multiple rowed fast-loader (more-rowed compressing collector for icons with optional mini-pull-down-(up-)menu), unit-conversion, LCD-weather-station, weather forecast, wordclock with timezones, accu-check, image frame, comic, egg-clock, jumping ball, colorchoosing stick, calculator, moon phases, zoom, social desktop, ToDo-lists, remember the milk, system-monitor, guitar-tuner, image-preview, widget-dashboard, birthday-reminder, flickr, language-translator, sun-system, fishtank, DVB-signal-meter, newsticker, Mountoid, Bundesliga, Facebook, Flickr, bsun (wandernde Sonne), FrustML resp. (Mensch-Ärger-Dich-Nicht), Fancy Tasks (quickstarter similar to cairo-dock), Koala (similar to Tamagocchi), Astrocalendar, Plasmio (SMS), daisy (desktop-icons in a cricle), 15 stones,Tomatoid, egg-clock, spell verification, blackboard, WorkContext (nepomuk) and much more ...
Gadgets, Apps-Installer, ...
                        
Gai, The General Applet Interface Library von http://fr2.rpmfind.net oder http://gai.sourceforge.net : gai-pal, gai-album, gai-bgswitcher, gai-blobs, gai-clock, gai-mailcounter, gai-nebulus, gai-sun, gai-othello, gai-pager, gai-terrain, gai-visual-audio, gi8k, gwlan, vpn, bluecombo, FishTime, shermans-aquarium, TV in a box (tvib), usermon, ...
 Cairo-Dock from http://fr2.rpmfind.net or http://www.glx-dock.org/
Cairo-Dock from http://fr2.rpmfind.net or http://www.glx-dock.org/
 krunner: KDE Semantic desktop search per singe mouseclick on the base of gingko resp. akonadi and nepomuk and so on (all upon MySQL) by direct text-search like Cortana for MS Windows, ideal per mouseclick from the taskline or out of the KDE-start-menu, in order to search for names, database entries of all kind, textfiles, audios, images, videos, e-mail, news (Usenet), command execution, date and time, desktop-sessions (user exchange), kopete-contacts, contacts from kontact, webbrowser-history, konqueror-sessions, bookmarks (to find and envoke), units-converter, media playing, nepomuk (semantic search), locations (open files and addresses, ginkgo resp. semantic view during the saving of documents and other files), (opened and closed) windows and work areas (and their includes), plasma-desktop (interaction with the plasma-shell), TechBase (search within the KDE-TechBase), Wikipedia (searching in Wikipedia), Wikitravel (searching in Wikitravel), dictionary, recent documents, devices, kate-sessions, kget (links to download-manager kget), konsole-sessions, language translator, special chars (creates special chars) and so on: krunner (el6, ..., mdv) (or press ALT+F2) krunner: KDE Semantic desktop search per singe mouseclick on the base of gingko resp. akonadi and nepomuk and so on (all upon MySQL) by direct text-search like Cortana for MS Windows, ideal per mouseclick from the taskline or out of the KDE-start-menu, in order to search for names, database entries of all kind, textfiles, audios, images, videos, e-mail, news (Usenet), command execution, date and time, desktop-sessions (user exchange), kopete-contacts, contacts from kontact, webbrowser-history, konqueror-sessions, bookmarks (to find and envoke), units-converter, media playing, nepomuk (semantic search), locations (open files and addresses, ginkgo resp. semantic view during the saving of documents and other files), (opened and closed) windows and work areas (and their includes), plasma-desktop (interaction with the plasma-shell), TechBase (search within the KDE-TechBase), Wikipedia (searching in Wikipedia), Wikitravel (searching in Wikitravel), dictionary, recent documents, devices, kate-sessions, kget (links to download-manager kget), konsole-sessions, language translator, special chars (creates special chars) and so on: krunner (el6, ..., mdv) (or press ALT+F2)
rpm-description: "Ginkgo (KDE (mdv2010.2, mga, rosa) is a graphical front-end for managing data semantically. Ginkgo lets you create and explore links between your personal data such as e-mails, contacts, files, Web pages. It harnesses the Nepomuk framework."
Start ginkgo (KDE (mdv, mga)): Click upon a directory or file ->, context menu -> "Annotate" (context menu of KDE (mdv2010.2) -> Ginkgo: data record with different text fields
For KDE (el6, OpenSuSE-11.2 4.4.4, 4.4.11) ginkgo does not function, but clicking upon "semantic view" during the saving of documents and files is a good alternative, as it opens the same text-input-fields like ginkgo.
Now you might want to click onto the pliers symbol (settings) and modules, in order to deactivate Wikipedia, Wikitravel and the Google language translator.
[SOLVED by Gooken, 21.10.2016: drkonqi: One or more akonadi_resource do not work or cannot be found]
At first, lookout for akonadi (el6) installed (rpm -qi akonadi).
There are three rpm-packages full of akonadi_resources like ical, birthdays, kcal, knut, kolabproxy, localbookmarks, mbox, microblog, nntp, notes, vcard, vcarddir, nepomuktag, strigi, kabc, kcal and imap: akonadi-kde (mdv2010.2) and kdepim-runtime (el6) with kdepim-runtime-libs (el6).
Now enpack akonadi-kde (mdv2010.2) and copy the not working akonadi-resources, that can be found in rpm´s usr/bin/ to /usr/bin.
The other direction from kdepim-runtime (el6) to akonadi-kde (mdv2010.2) might be the correct one in some cases too.
If you want to start nepomuk-semantic-desktop-search (krunner):
1 eventually start the strigidaemon: /usr/bin/strigidaemon&
2 start desktopsearch-KDE-control-modul ( systemsettings or krunner:enter "nepomuk", in order to select it ) -> 3 select files to index / Dateiindizierung (Verzeichnisse auswählen) -> 4 activate both, nepomuk and strigi / Nepomuk-Semantik-Dienste und Strigi-Datei-Indexer zugleich aktivieren.
3 If the error message ( like "akonadi_ical_resource can not be executed successfully" ) still appears, start akonaditray and remove the belonging resource out of the resource-listing. Many resource can be removed, but maildis, maildir and mailtrans are always needed for kmail.
 Desktop-Screenlets, image: GUI-Screenlet-administration with more than 100 screenlets additionaly downloadable ones and screenlet-daemon, screenlet in the fore- and background, scalable size, widget-attribute, more attributes like: growing flower ( to give some water from time to time), slideshow, pager, control (to add more screenlets), radio, meter, stocks, speech, sensors, ringssensors, ruler, convert, example of howto create a screenlet, copystack, clear weather von weather.com, ...
Desktop-Screenlets, image: GUI-Screenlet-administration with more than 100 screenlets additionaly downloadable ones and screenlet-daemon, screenlet in the fore- and background, scalable size, widget-attribute, more attributes like: growing flower ( to give some water from time to time), slideshow, pager, control (to add more screenlets), radio, meter, stocks, speech, sensors, ringssensors, ruler, convert, example of howto create a screenlet, copystack, clear weather von weather.com, ...
For more details see the data sheed from left menu.
"4.65 from 5 stars are the results of the average voting of a test from year 2014 for Mandriva based upon 204 meanings of customers from Erfahrungen.com investigates regulary such votings from all sources out of the internet, that are carefully read out by hand and stochastic methods."
 Mandriva Metisse takes 3D to a New Level, http://cybernetnews.com/mandriva-metisse-linux-takes-3d-to-a-new-level/
Mandriva Metisse takes 3D to a New Level, http://cybernetnews.com/mandriva-metisse-linux-takes-3d-to-a-new-level/
This morning I´ve been watching videos of the Mandriva Metisse Linux that, in my opinion, puts some amazing 3D features at your fingertips. All of this XGL and 3D stuff is often shrugged off as merely being eye candy, but there are four video demonstrations that really show the usability that these features can really offer. I always thought that openSUSE Linux was always the furthest advanced version of Linux since they often implement the latest technology. However, Mandriva seems to be taking that crown away, and I have really considered switching to it as my primary version of Linux that I use. I like the look and feel of their operating system, and it is obvious that they are exploring new ways to make it the best it can be.
Download Mandriva Metisse
Thanks for the tip Chris!
Convince yourself: The quit short and many years overworked errata-list of the comfortable mdv2010.0 can be directly obtained from Mandriva Errata 2010.0. Not all of the mentioned problems there have to be solved. With mdv2007 and mdv2010 the time has come to install many, if not all, packages of this distribution and maybe more tarballs at once on the same SSD resp. harddisc instead of, to go sure, a few ones only as generally recommended by institutes like BIS.
The address of Mandriva is not missing on mandriva´s homepage.
Mandriva S.A. (prev. Mandrake), Paris, St. Etienne, Frankreich, Tel...., email-addresses... ( founder: Gael Duval, 70 persons employed )
"Mandriva Linux the brainchild of Gael Duval, who wanted to focus on ease of use for new users. Duval became the co-founder of Mandrakesoft". Most packages origin in Fedora (but I knew a distribution of Fedora on DVD from the same year 2010 remaining quit scanty in comparison).
 Abb.: System tray (plasmoid) out of Krandr (screen resolution), kmix, Klipper, parcellite (additional configuration of klipper), NetworkManager, Stardict, USB-connections and encrypted partitions, kgpg, korganizer (calender and. dating planner with reminder function), printer-applet (printer jobs), nepomuk (semantic search), i - information for system messages by kwrited (actually not started, that means still without: knotes or tomboy, tvbrowser, ...), clock with date and calendar and the fast screenlock- and poweron-off-plasmoid; enfastened load of the tray after the deinstallation of interfering draksnapshot Abb.: System tray (plasmoid) out of Krandr (screen resolution), kmix, Klipper, parcellite (additional configuration of klipper), NetworkManager, Stardict, USB-connections and encrypted partitions, kgpg, korganizer (calender and. dating planner with reminder function), printer-applet (printer jobs), nepomuk (semantic search), i - information for system messages by kwrited (actually not started, that means still without: knotes or tomboy, tvbrowser, ...), clock with date and calendar and the fast screenlock- and poweron-off-plasmoid; enfastened load of the tray after the deinstallation of interfering draksnapshot
"Mandriva Linux 2010 - perhaps The Best Linux Release All Year - Mandriva Linux 2010 was recently released and brings lots of nice improvements to an already nice system. Mandriva has a long and distinguished history in the Linux distribution arena. They began over a decade ago using Red Hat as their base and quickly became the preferred choice of the new Linux user. This release hopes to offer some amenities to appeal to users of newer trends in technology such as semantic desktop and netbook support. The Mandriva Linux installer sets the standard in user-friendly Linux installers. For those familiar with Mandriva this release brings some great improvements. The best two so far have been the increased stability and performance. Mandriva may have had a reputation for being a bit crashy in the past, but it appears those days are gone. In the several days since a fresh install only one application crash has occurred here, and this application is known to be unstable across distributions. This new-found stability comes with even better speed as well. Not only does Mandriva boot quicker (speedboot: kernel-parameter that can be set in /boot/grub/menu.lst or /etc/lilo.conf, speedboot=yes), but desktop performance has improved noticeably. Applications open and function faster, including the two heavyweights OpenOffice.org and Firefox. There is virtually no graphic artifacting and redraws are immediate. In addition, the 2010 graphics are just beautiful (source: http://www.makeuseof.com/tag/mandriva-linux-2010-perhaps-the-best-linux-release-all-year/).
mdv2010 enpossibles to choose any design and style out of desktop, appearance and desktop-design-details from systemsettings and gnome-control-center - self mades as much as pregiven ones. A screen covering bootsplash can appear right up at the beginning when powered on using grub or escpecially grub2. Color-schemes can be imported like the one from the CD of the monitor-manufacturer and there are a lot of emojis. Addtionally plasmoids and many ressources-saving 3D-deskop-effects can enrich the desktop. With compiz, the deskop-workplaces are ordered cube or metisse, while the desktop-background can be any wallpaper, slide-show, global map, weather map, mandelbrot and so on as much an image on the fly. Especially OpenGL, fast direct-rendering, SDL and pulseaudio guarant the video- and audio-processing. Mandriva´s center of gravity lies together with the up to year 2060 actualizing Scientifclinux (sl6, el6) alias CentOS 6.7 (el6) and 6.7 (el7) in the extended hardware-support of our days as much as in future.
Nevertheless keep an actual mirrored 1:1-backup on another media during the installation! After all the installation, mdv2010 is running fine.
Mandriva for free: Mandriva Lx 2014 1,6GB free download. Notice, that we would like to keep mdv2010. Therefore we did not test this Mandriva-distribution!
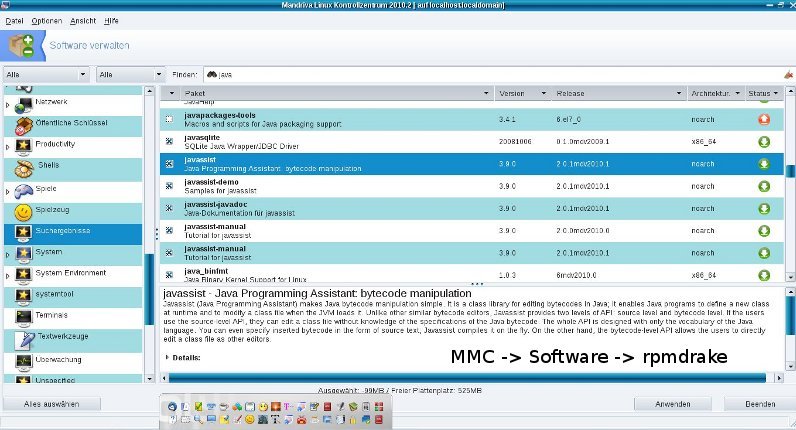
Bootstrap of mdv2010 (creates) a basic Debian system: debootstrap is used to create a Debian base system from scratch without requiring the availability of alien, dpkg with debbuild and debmirror and/or apt. Notice, that in comparison with package manager of mdv2010, those off Debian 2010 like aptitude and synapitic do consist of errors, error-messages, breakdowns and bad overviews. It does this by downloading .deb files from a mirror site, and carefully unpacking them into a directory which can eventually be chrooted into (although we recommended to forbid this command). Debian is also supported by dpkg, apt, dselect, dash, ..., but with mdv2010 there seems to be not much Debian software missed, see http://fr2.rpmfind.net/linux/RPM/mandriva/2010.0/x86_64/. The coloured out listings of Mageia Cauldron - and Mandriva-rpm to select is most satisfying on http://fr2.rpmfind.net.
Mandriva-One (mdv2010.2-final, i586) direct bootable from your USB-memory-stick, USB 2.0 and higher. Harddrive and SSD do remain not only unused, but can also be used for installation.
Linux on your USB-memory-stick:
with a free partition of at least 2 GB or unformatted for 64- and 32-Bit-CPU, mdv-fundament, optional installation onto your harddrive resp. SSD, kernel 2.6.33, grub (with a optional md5-encrypted password-protection for each bootable dracut resp. kernel and memory check by memtest) and lilo (boot-manager, especially for kernel < 2.6.39), Firefox 3.6.13 including the security-addons we recommend and privoxy, KDE 4.4.5, Dolphin 4.4.5, Konqueror 4.4.5, Kontact with kmail and bogofilter, clamav, Korganizer, OpenOffice, packet-manager drakrpm, rpm, gurpmi and urpmi, drakconf, gparted/parted (for changing the partition-size even on USB-stick), software for repair, mplayer (i chose video: X11 (XImage/Shm) and audio: sdl SDLib audio output), mplayer-codecs, mplayer-codecs-extra, mplayerplugin, amarok, image viewer, gimp, gcc, gcc-c++, kwrite, fsck, rkhunter and chkrootkit, xskat, pysol, gnuchess and eboard with crafty (chess), shell-shock resident bash, bash-completion, konsole, xterm, many repair-functions and so on, mdv-i586-rpm-packages OR
of at least 6 GB free partition or unformatted 5.5GB more mdv2010-software from installation-DVD out of all rubrics like gparted, system-monitors, system-tools and more programs for repair, wine and qemu (emulation), k3b and brasero, xscanimage, xsane, tesseract, gocr, cups, xine, totem, flphoto, gtkam, tvtime, zapping, dvbtune, jikes, kino, audacity, supertux, toppler, rocksndiamonds, ....
both free from porto the way back to you. Therefore you just have to put your USB-stick and 10€ protection-fee into an envelope to send it to our address, see impressum. Before your order this, please test your BIOS, if it supports the booting with USB-storage-media (BIOS-boot-sequence and/or keys to determine the boot-sequence like F8), username: user and root, password: mandrivaone.
Reader discussion on netzpolitik.org, Opensource disconnect vs. proprietary Ghostery
chromax 29. JUN 2015 @ 20:42
Where do you know, if OpenSource-code refers to the compiled one? Still missing security…
Antworten
CrX 29. JUN 2015 @ 22:06
This question is of academic nature. Practitioner interest in the verficiation (indentically) of executable files and source code.
Therefore oneself compiles the Open-Source, if confident with it.
Antworten
skoam 24. SEP 2015 @ 10:09
This is immer the right question and an answer does already exist: Open Source can be compiled, in order to compare the build with the receipt executbale binary code. If the hash-sums (md5sum/shasum/file sizes) do not agree (that means differing), the executable code deals with code not listed by its source.
Why UNIX/Linux? Because I know it is opensource and the kind of its (almost german) programmers behind (book from Prof. Kersten and books from some other authors).
It always must be caviar? Tell us about any more secure distribution ever!
Gentoo Linux 12.1 2012 Live-DVD (x86_64 for 32 and 64 bit- and AMD64 forr 64 Bit-CPU) from Gentoo.org, burnt 3,3 GiB ISO. The so called meta-operating-system Gentoo is recommended by prism-break.org. It is bootable from DVD as much as installabe onto SSD/HDD by open-source-packages to compile in. You can also order already DVD-burnt Gentoo 12.1 AMD64 from us free from postage-fees for 10 €
Smartphones
In comparison with IPhone 6: This smartphone can something like no other one, Focus, 01.11.2014
For 12 US-Dollar only, it rivals with Apple or Samsung - with uncommon features. "Smartphone-the drug is real like everywhere. This handy does not pig up your dates, does not irritate you during concerts, does not disturb you in the cinema and cleans up the passways. The solutiion is found. With this promise, a user names quot;The NoPhone Team" of the Crowdfunding-platform Kickstarter his project. It is a handy like no other one and can do like no smartphone can. Namely... nothing. Perfect for the pockets of the trousers: its wireless design made of flexible plastic feels cool and real. "Just pull it out and hold it." The most signifcatn features are named by the manufacturers: no accu, no nerved updates, splinter-free, water-proofed. This project has it success: the No-Phone-Team wanted to collect 5.000 Dollar but accounted 18.000. With this phone, that can neither phone nor write SMS nor surf in the internet, should cost twelf Dollar. There is another "NoPhone"-version with selfie-function. This model has a mirror in its display and is distributed in the words: "Show your friends your newest selfie, if they stand directly behind you."
We do not believe much in honesty of the other ones in all matters: In regard to SAR-values, cases like Macolini and the feel of the "slap in the face" (probably metastasis) on the side of the handy taken from our section for News&Links and other cases, where magnetic influence was felt by second persons in the circumcirlce of more than three meters from the handy phoning, Gooken dissuades from all kind of wireless (mobile) phones except emergencies!
Two cameras, several microphones, a GPS-modulel and oodles private user data: smartphones are the perfect supervisory devices
Security export leaks out: Your smartphone can spy out - although you powered off everytjhing, STERN.de, 08.02.2018
Über GPS und Co. können uns Smartphones permanent überwachen. Zum Glück kann man die Funktionen aber abschalten. Ein Forscher erklärt nun, wie man diese Sicherheitsmaßnahmen trotzdem aushebelt - und warum das kaum zu verhindern ist.
Zwei Kameras, mehrere Mikrofone, ein GPS-Modul und Unmengen private Daten der Nutzer: Smartphones sind die perfekten Überwachungsgeräte.
https://www.stern.de/digital/smartphones/so-kann-ihr-smartphone-sie-ausspionieren---obwohl-sie-alles-abgeschaltet-haben-7855612.html
https://www.stern.de/digital/computer/erpressungs-trojanern--so-schuetzen-sie-sich-vor-ransomware-6725356.html
https://www.stern.de/digital/online/datenraub--mit-diesen-7-tipps-schuetzen-sie-sich-davor-8521708.html
https://www.stern.de/tv/datenhack--warum-wurde-es-dem-taeter-so-leicht-gemacht-und-wie-kann-man-sich-schuetzen--8521650.html
https://www.stern.de/digital/smartphones/so-kann-ihr-smartphone-sie-ausspionieren---obwohl-sie-alles-abgeschaltet-haben-7855612.html
https://www.stern.de/digital/online/der-mann--der-uns-schwierige-passwoerter-einbrockte--bereut-seine-entscheidung-7577534.html
https://www.stern.de/digital/computer/erpressungs-trojanern--so-schuetzen-sie-sich-vor-ransomware-6725356.html
https://www.stern.de/digital/online/iphone-privatsphaere--mit-diesen-einstellungen-schuetzen-sie-ihre-daten-8522116.html
https://www.stern.de/tv/datenhack--warum-wurde-es-dem-taeter-so-leicht-gemacht-und-wie-kann-man-sich-schuetzen--8521650.html
https://www.stern.de/tv/gute-passwoerter-und-co---so-schuetzen-sie-sich-bestmoeglich-vor-hackerangriffen-8524324.html
How to make mobile end-devices secure: http://www.pcwelt.de/ratgeber/So-sichert-man-mobile-Endgeraete-im-Unternehmen-ab-FAQ-9582121.html.
This links origins from our section News&Links#computer#smartphones, CHIP, 26.12.2016: Android-security is one thing to take care of with fitting apps. With such apps you do not need to fear NSA, data robbery, viruses and Co. anymore. CHIP presents the apps protecting your android-handy in a perfect way.
Data-backup for Smartphones: Here are the best solutions for data-backup for Android, iOS and Windows.
ifixit: It is easy to repair smartphones - FOCUS Online.
10.000 mAh powerful monster-akku from Smartphone-Manufacturer OUKITEL, Focus Online 02.07.2015
Four times more powerful than Galaxy S6: This Smartphone has a akku-load durability of one week
The days of empty smartphone-akkus might be gone. The manufaturer OUKITEL plans the first smartphone with an akku-load of one week ...
See reports from our linkside: They are manufactured by perverts (Apple; see a report from our linkside), tiny displays bother the eyes, they radiate and cause serious hard accidents, while one can not care enough for IT security even around them: smartphones. Gooken primarily cares for the Desktop-PC. Therefore, before the (similar) use of smartphones and handies it is strongly recommended to have a look upon our linkside by clicking onto links or here, but remark, that the use of so called-crypto-smartphones and crypto-mobil-phones can provide the needed protection up to the already endangering point of crypto- resp. supercomputers.
ZDNet / Mobile: Why Open-Source-Handies are the better smartphones, from Jack Wallen, 24. september 2009
Open Source provides the mobil market plenty of advantages beginning with the reducing of costs, more security up to many adoptable settings and a more productive development of applications. Do you agree, that Open-Source-devices are the better smartphones? Or does Apple, even Microsoft with Windows Mobile 7 win the fight for the market share? You can write a comment.
Hardware-Support: device-drivers, hardware-databasis
Kernel-5.4.110 (PCLinuxOS) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) and glibc (el8, pclos, mga6) resp. kernel 2.6.39 (mdv2010) with actual patches up to now from see our section for updates provides extended hardware support. But sometimes you just have to wait. So called "old" hardware must not be bad, the drivers are almost provided. Popular driver are already wtihin the kernel or kernel-modules. If missing in kernel-modules, belonging packages (rpm, deb) can be taken over into such modules. CPUs of mainboards consist of standard machine command sets that are already regarded in the package name like x86_64, i686, ia64, ppc, ppc64, ppc64le, aarch64, s390, s390x, arm, armhfp, sparc and so on, while the BIOS (BIOS-chip) on the mainboard should be socked, so that it can ordered, if malfunctioning. For the graphiccard you can use the UNIX/Linux-standard-driver fbdev or vesa. And the plugin of TFT-monitors is as simple as it can be in the case of postscript-printers by naming the belonging PPD-file out of (rpm) openprinting-packages, manufacturers or manufacturer-driver-CD. Start MCC, go to section "add a printer" and link to such PPD-file. Good to know, that USB is downward compatible. If the (W)LAN-chip does not work, a standard-PCIe- or PCI-ethernet-card helps out, until the packages or Tarballs for the driver are released in the internet, same for graphiccard and the onboard-soundchip.
Hardware for Linux, PC-WELT.de, 11.06.2019
Question: Is it guranteed, that hardware can be used for Linux for my PC, netbook and peripherals unrestrictedly?
Answer: To say it shortly: No. Here´s the long version of the answer: It takes a leap of faith. Hardware manufacturer seldom offer support for Linux. Basic components like graphik-, SATA- or Ethernet-chipset do not provide problems. But for printer, scanner, USB-TV- or WLAN-Stick, in many cases the driver CD does not include drivers for Linux. And even if, they just fit seldomely into the installed system. Notebooks are often restricted too. In some cases the brightness of the monitor screen can not be adjusted by key combinations or the power modes do not function like in Windows.
Therefore it only helps to get informed through the internet or by the salesman about notebooks and peripherals. There are salesman specialized for Linux like Tuxedo.
https://www.pcwelt.de/ratgeber/5-Fragen-und-Antworten-fuer-Linux-Anfaenger-10589209.html
 PC-WELT.de, 01.09.2015: "Find out compatible hardware before you order it
PC-WELT.de, 01.09.2015: "Find out compatible hardware before you order it
Whoever does not want to care for Linux-driver, one should check out the compability of the hardware before it is ordered. In most cases it is sufficient to start a search by searchengines with the name of the hardare device in combination with "Linux". One can also search in hardware-databasis. It es also useful to get informed by websites like http://wiki.ubuntuusers.de/Hardware with lists of hardware, that functions and tipps for their installation. Informationen about TV-cards and Sticks are also providid by Linux TV.
Of Linux should be installed on a notebook, http://tuxmobil.org or Ubuntu Wiki provide userful information. There are some manufacturer specialized for notebooks with preinstalled Linux like Tuxedo Computers, although such devices might be a little bit more expensive than Windows-notebooks."
After an upgrade of the glibc from mdv2010 to rosa2014.1 or mga3 a hugh repertoire of driver-packages and -tarballs are provided for even actual hardware.
Such companies do provide drivers for Linux:
Graphic cards: Intel, Nvidia, AMD
Printer and scanner: Epson, HP, Intel, Samsung, Brother and Canon
Hardware databasis and hardware support:
http://openprinting.org for Ghostscript- and the PPD-files of postscript-printer
https://de.opensuse.org/Portal:Hardware
http://wiki.ubuntuusers.de/Hardware
http://linuxtv.org/wiki/index.php/Hardware_Device_Information
http://community.linuxmint.com/hardware
http://tuxmobil.org/
https://wiki.ubuntu.com/HardwareSupport/Machines/Laptops
http://www.tuxedocomputers.com
http://wiki.ubuntuusers.de/Drucker
http://www.pcwelt.de/ratgeber/Uefi-statt-Bios-Das-muss-man-beim-Linux-Boot-beachten-Von-USB-und-DVD-9715238.html
http://wiki.ubuntuusers.de/Scanner
A detailed report about the hardware-support of drivers is provided by the following article: http://www.pcwelt.de/ratgeber/So-bringen-Sie-Linux-trotz-Probleme-zum-Laufen-9789269.html.
If a driver is still missing, he can be buid (constructed) by any user. Several howtos can be found in the internet. For the printer packages lke cups-ddk are released for cups.
X11-server-troubleshooting (graphic card): see our section for "updates"
Printer-Troubleshooting: see our data sheet, section printer
Lacks in security
"The way is the target" are the well-known words from our precedent security-manager Konfuzius (...), that made us write here so much. Our main aim is to drag him out of the computer-scene for IT security and, who is awake enough, even forever! Together with the checklist it is proofed, that computer technology must not be nonsens, even if it is meant so and even if there is nothing really secure in this world, because of the race of the safeendangering with the secure and the certain kind of human behind this scene. Computer-history of nowadays with the typical constitution of software in intransparent „pirate-black“ binary machine-code, unlucid amounts of versions and distributions have shown some more (responsible) difficulties in satisfying claims for achieving real protection for the jack of all trade. Smartphones, notebooks and so on are only mentioned on our linkside. MG Chip: "The combination of raster-electron-, raster-Auger- and raster-plammet-microscope is cracking any kind of chips, however signed secure from manipulation". Serious hard cases of system-self-destructs can not be excluded. But resignation does not help. Nevertheless the aim in general of this excursion is to provide computer-systems with almost no lacks in security at all, and therefore (quit) without any scans from hard-disks by any scan-software. By following the excursion, your UNIX-computer will be freed from all (!) problems with the computer quit at once like (... ever seen so much red in your documents?)
 proprietary software (opensource against liablity, more clearance of question about liablity), cost-traps (here: billing by handies and SMS, overread of additional parts of contracts and the conditions), blackmail for unlocking suddenly locked computers (see our report under links), abuse of copyrights and patents, cult for criminals, billions hard investment into spying software and techniques, missing, confusing or the fluctuating IT-security-concept, hard-disk-scans, defragmentation (unnecessary for many UNIX-file-systems), harddrives (instead of MC-SSD, cite: "A magentic harddrive is much to risky to intrust data. Although a lot of improvements took place, who has not heart or - in worst cases - made the experience of lost data. Therefore enough reasons are relevant." (source: poshtar@datensicherx.com, 13.05.2014)), the demand for a registry, registry-errors (UNIX-systems have no registry), degeneracy of the registry, suddenly or inpredictable lost files, explosion (of net-adapter), fire (net-adapter, porous PC-lautspeaker-cable, ...), your own ununderstandable blackened company (enlighted by our PHP-MySQL-company management Mycompanies), virtual blackmail by encrypting harddrives against ransom, shooting through unmanned flying objects as a technical response to stored data, kontermination (through chipsets, preventable by IGP and all-in-one-mainboards) and radiation, WLAN-radiation (see our linkside), CRT-radiation, CD-burner-radiation, netadapter-radiation, warning high SAR-value (handies), zero-emission (reflectable monitor emissionf or example by special PCMCIA-cards prevented by special editors like the zero emission pad), hardware-recognigtion (standarized driver, Kernel ver. greater 2.6.30), infiltration of social networks, handy-hunts through nets, inconsistency (vs. everlasting science), need for upgrades (new tarballs, zip-archives, functionality), updates, patches and bugfixes (vs. functionality), browser with outdated ssl3.0 (modern usage is provided by TLS), changeovers to different security software, missing changelogs, software-overload on harddisc (Opensource, independency-checks, other introduced methods), hacker (STATE-NEW lined iptables-blocking), large holes in firewalls (iptables block-rate), intrusion and valdalism, viruses (access-rights of UNIX-filesystems), freak (patch or prefer browsers like Firefox or Konqueor instead), abuse by virus scanner (standard opensource clamav), worms, rootkits (rkhunter) resp. botnets and trojans (no botnets and no trojans by correct usage of the OWNER-concept of iptables), manipulation by system-administrators upon software, files and configurations, ddos-attacks (almost on the base of bots and trojans), inactual alarms, false-alarms, forgotten or coded warnings and error-messages, ad- and spyware as much as Trackingscripts (firefox-addons), Driveby-Downloads, Canvas Fingerprinting (see under online check), forced acquisition because of truncated customer support for old operating systems (lifetime installation-support for all mdv/mdk over "pointed 1-" to "pointed 0" versions), product-manufacturing fault right on the surface of installation-CD/-DVD, aggressive marketing, need of updates and upgrades instead of functionality, unknown authors behind the named, burn-errors, problems with the BIOS and during the system-startup resp. boot, flush and reset, intransparent boot-processes, hard undestandable process-names (partial standarizement by UNIX/Linux), unmushed nets (failsafed mushed nets), video- and voice-recording, judge-microphons, observing satellite technique (see under links), spanish flies, night viewers, evaluation of such recordings (audit, protocolling files), text- and image-manipulation, manipulation of websits by webhoster, instability, system-breakdowns, broken USB-Sticks (secure umount and never before, fsck), usage of USB-hubs instead of prolonging USB-cables only, manipulated electric meter and cables (UPS: unbreakablel power supply), ineffective encryption through non scientific based cryptograhic methods from highschools, the search for important function-keys,iweak point human, insufficient set of (security-) system-commands, hangons and newstarts, anomal login attempts (LADS - login anomally detection system), inactual alarms and warnings, installation of malware by the opening of e-mail-attachements, unsigned installation from anywhere, installation by everyone, inportability, defect peripherals and hardware, restricted presentation of websides, keylogger and other malware, wiretrapping bedbugs (from USB-cards and other devices), hack of sensible data from USB-sticks through their microcontroller, crack of WLAN-encryption-keys, spy-nets, false email-sender-addresses (disabled browser-cache, header of email-source-text, digital signatures by public signature-keys, de-Mail), DoS-attacks, root-rights providing buffer-overflows (bugs),
proprietary software (opensource against liablity, more clearance of question about liablity), cost-traps (here: billing by handies and SMS, overread of additional parts of contracts and the conditions), blackmail for unlocking suddenly locked computers (see our report under links), abuse of copyrights and patents, cult for criminals, billions hard investment into spying software and techniques, missing, confusing or the fluctuating IT-security-concept, hard-disk-scans, defragmentation (unnecessary for many UNIX-file-systems), harddrives (instead of MC-SSD, cite: "A magentic harddrive is much to risky to intrust data. Although a lot of improvements took place, who has not heart or - in worst cases - made the experience of lost data. Therefore enough reasons are relevant." (source: poshtar@datensicherx.com, 13.05.2014)), the demand for a registry, registry-errors (UNIX-systems have no registry), degeneracy of the registry, suddenly or inpredictable lost files, explosion (of net-adapter), fire (net-adapter, porous PC-lautspeaker-cable, ...), your own ununderstandable blackened company (enlighted by our PHP-MySQL-company management Mycompanies), virtual blackmail by encrypting harddrives against ransom, shooting through unmanned flying objects as a technical response to stored data, kontermination (through chipsets, preventable by IGP and all-in-one-mainboards) and radiation, WLAN-radiation (see our linkside), CRT-radiation, CD-burner-radiation, netadapter-radiation, warning high SAR-value (handies), zero-emission (reflectable monitor emissionf or example by special PCMCIA-cards prevented by special editors like the zero emission pad), hardware-recognigtion (standarized driver, Kernel ver. greater 2.6.30), infiltration of social networks, handy-hunts through nets, inconsistency (vs. everlasting science), need for upgrades (new tarballs, zip-archives, functionality), updates, patches and bugfixes (vs. functionality), browser with outdated ssl3.0 (modern usage is provided by TLS), changeovers to different security software, missing changelogs, software-overload on harddisc (Opensource, independency-checks, other introduced methods), hacker (STATE-NEW lined iptables-blocking), large holes in firewalls (iptables block-rate), intrusion and valdalism, viruses (access-rights of UNIX-filesystems), freak (patch or prefer browsers like Firefox or Konqueor instead), abuse by virus scanner (standard opensource clamav), worms, rootkits (rkhunter) resp. botnets and trojans (no botnets and no trojans by correct usage of the OWNER-concept of iptables), manipulation by system-administrators upon software, files and configurations, ddos-attacks (almost on the base of bots and trojans), inactual alarms, false-alarms, forgotten or coded warnings and error-messages, ad- and spyware as much as Trackingscripts (firefox-addons), Driveby-Downloads, Canvas Fingerprinting (see under online check), forced acquisition because of truncated customer support for old operating systems (lifetime installation-support for all mdv/mdk over "pointed 1-" to "pointed 0" versions), product-manufacturing fault right on the surface of installation-CD/-DVD, aggressive marketing, need of updates and upgrades instead of functionality, unknown authors behind the named, burn-errors, problems with the BIOS and during the system-startup resp. boot, flush and reset, intransparent boot-processes, hard undestandable process-names (partial standarizement by UNIX/Linux), unmushed nets (failsafed mushed nets), video- and voice-recording, judge-microphons, observing satellite technique (see under links), spanish flies, night viewers, evaluation of such recordings (audit, protocolling files), text- and image-manipulation, manipulation of websits by webhoster, instability, system-breakdowns, broken USB-Sticks (secure umount and never before, fsck), usage of USB-hubs instead of prolonging USB-cables only, manipulated electric meter and cables (UPS: unbreakablel power supply), ineffective encryption through non scientific based cryptograhic methods from highschools, the search for important function-keys,iweak point human, insufficient set of (security-) system-commands, hangons and newstarts, anomal login attempts (LADS - login anomally detection system), inactual alarms and warnings, installation of malware by the opening of e-mail-attachements, unsigned installation from anywhere, installation by everyone, inportability, defect peripherals and hardware, restricted presentation of websides, keylogger and other malware, wiretrapping bedbugs (from USB-cards and other devices), hack of sensible data from USB-sticks through their microcontroller, crack of WLAN-encryption-keys, spy-nets, false email-sender-addresses (disabled browser-cache, header of email-source-text, digital signatures by public signature-keys, de-Mail), DoS-attacks, root-rights providing buffer-overflows (bugs),
aggressive marketing, missing warnings of the BIOS during overheatings of the CPU and from the inside, malfunction of USB-memory-sticks, intransparent boot-procedures without detailed information, long boot-times, weak-point-human (as a title of a contribution from a newsgroup), hard to understandable files and processes by name, side-manipulation and censorship by webhosters, need for additional software for example for ftp-transfer, use of harddiscs instead of durable and less power-consumpting (MLC-) Solid State Disks (SSD), installation of malicious software by opening attachments from e-mail, need for external graphic- and sound-cards (IGP, onboard integrated graphic- and sound-chips), software from unspecified sources (integrity checks, checksum), installation by any users instead by users with special access rights only, cloud computing (by avoiding storage onto foreign media, extern harddrive, USB-memory-stick), bad cable connection, listenings in to WLAN, cracks of WLAN encrypting keys, illegal access into WLAN-access-points, broadcasting bedbugs from USB-cards or other devices), lack of test reports and exchange of experiences (datasheed and test-forums), low duration of batteries and akkus, unknown details of OS-kernel bad or low encryption, encryption by elsewheres cryptographic methods instead of those checked resp. developed by high-schools, bad or low encrpted instant messaging (OTR, ...), manipulation of files like out of /etc/security/msec (FDE, FSE for full disc and full system encryption), file-encryption), vandalism "you can power off your computer now!", insecure passwords, inpredictable exhaust of passwords, amount of passwords (kwallet and relevation), visiblity of files storing passwords (steghide), bad adhere to deadlines, intimelineness, forget of the sourrounding (dating planner, countdown clocking, scheduler, task scheduler, ntp-daemon), burn error on CD/DVD (noflushd), inportability, unmashed nets (failsafe mashed), security endangering security software, missing software, incomplete set of (security-)system-commands, instabilty (breakdowns, blackouts and hang-ons, Alpha-Beta-software-developement stages, ...), release of authorizing root-rights, hacker, smashed wholes into firewalls, viruses, worms, rootkits (rkhunter) resp. trojans, dialer, hoax (watching out for the sender), false alarms, anomal attempts to login (Login Anomaly Detection System like LADS, delays after false-logins, commands to list logins and login-times, risks of WLAN (many single security operations have to be performed), security lacking file-systems, restricted file-systems (capacity of copied files, sytem dependencies, looking out for important function keys (BIOS, security modes...), inpredictibale deletion of files from anywhere, inpredictable remote maintenances, changing of fundamental configurations and settings, need for a registry, registry-errors, Entarten and Verwaisen der Registryeinträge, capacity restricting zombies, adware, popups, tracking scripts, ad- and spyware, online registrations for the release of software, spy-nets, intransparent connecitions over foreign net-nodes ( traceroute-command tcptraceroute see News&Links#Computer ), DoS-attacks, click-ping-tracing, cookies and Third-Party-cookies, supercookies, informing browser-chronicle, ABE, cross-side-scripting, operating time with akku/batteries, suspicious plugins, encryption cracking supercomputers, restricted presentation of websides, censorship depending of the true aims behind, spam (Spamassassin), spam-entries (Captcha), scam, missing option resp. missing command for even foreign notes through the net registrating traceroute (comannd tcptraceroute), read and writes from harddiscs by other parties, phishing, dialer, dissuasiveness, need of upgrades, errors and mistakes, missing software, registration, forwardings and therefore profiling by search-engines and depreciation, pass of hugh server-farms and advertising-networks, personalized advertisment, profiling, identifying ua-browser-answerback (see our online check) resp. IP, static new IP-adress-room ipv6, identity theft, pre-punishment-registration (cybermobbing), bad support, maintenance, bad sectors and file-systems with errors resp. the long time for their repair, capacity-resctriction of file-systems during file-transfer, bad encryption, online speed-blocker, editors (programming) without syntax-highlighting, missing log-files for protocolling, wait-states, needs for many drivers, more than hard to understand names for system-files, processes and errors, hard to understand names for processes and files, support for children and disabled (input-support and other programs like dasher, mouse-tweaks, speech, squid-guard, window-manager like LXDE and XFCE, ...), problems typing in by the ten-finger-system (missing keyboard), manufacturing faults on CD-surfaces (MS 98/SE), insufficient or bad tuned software-components and the risk of their dependencies, need for additional software like for ftp-transfer, old concept of magnetic hard-drives instead of long-durationed, specific natural durabilities for the storage, fast working and powersaving Sold Sate Drives (SSD), need of repair, (extern) graphic-, sound- and ethernet-cards (all-in-one boards, ideally with CPU, cooler and RAM) as a contribute to the enburdening of net-adapter to prevent open fire and explosions, 1000-Watt-PC, 65-Watt-CPU, techical reconstruction of direct debit mandates, missing delivery of online-ordered goods, especially from foreign countries and in cases of a too low amount in controversy, different device-interfaces (well known solved by downward-compatible USB), the disperse resp. page of the security-concept, waste of ressources, waste disposal problems, intern self-destructs, write-offs, science pocketing software-companies, costs for acquistion, licences, training, additional costs, difficulties or bad handlings, ...
... "in West Nix Niue (not new)" ...
with alternatives from our data sheed now all at low cost on the ground of power-consumption like energy saving lamps!
Data Protection
Windows 10: Deactivated funtions do send data to Microsoft, http://www.pcwelt.de/news/Windows-10-Deaktivierte-Funktionen-senden-Daten-an-Microsoft-Datenschutz-9781744.html
Other person do in the best case thinkable even not know, if you possess a computer at all, neither by IP nor DNS nor they know about your installed operating system resp. operating systems, installed software and files!
Although only human failures can cause errors during the installaton of mdv2010, some errors can happen. There is an amount of error-messages of mdv2010, that do not help troubleshooting, some are missing. Therefore we recommend a second SSD for the backup of every important installation-state of the first one. Then as many packages can be installed on the SSD as the user likes and ever needs without lacking in system-security, if you are installing operating-systems like mdv2010 with packages totally sized over 65 GB!
Survey of the internet node: DE-CIX sues BND, Tagesschau, 22.04.2015
The BND is taken into response before law for his surveys of the net-node DE-CIX in Frankfurt at Main. The holde of the node is going to sue. Criticizer do also sue the government for making tricks. Arond thre terabit data per second are passed and overworked, an amount of 600 CD-Rom. To the customers count all big internet companies like the Deutsche Telekom, Vodafone and Verizon, more details see Links, section "NSA, GHCQ & Co.".
Prism.break is right to recommend both alternatives (addition from 07.09.2013): Tagesschau reports about weak-points in many security software. The industry for software would have been built-in backdoors in their programs. It were possible to get information right before a user encrypts them and to send them over the internet. Super-computer were constructed to crack encrypted codes. NSA-program "Bullrun" belonged to the most kept secrets.
The british agency GCHQ were very successfull in cracking code.
prism-break.org: "With proprietary software, you need to have 100% trust in the vendor because there´s nothing except for their morality in the way of them leaking your personal information. Even if you can vouch for their integrity, proprietary software invariably has more uncaught security bugs and exploits because there are fewer eyes examining the source code."
prism-break.org, 2014: "Apple, Google and Microsoft are probable part of PRISM. You can not trust their proprietary operating systems in the matter of keeping sensible data safe from NSA.
Two alternatives do remain: GNU/Linux and BSD.
GNU/Linux has a much hugh community than BSD in order to help us for the change. It is recommended to search for a proper GNU/Linux-distribution fulfilling the requirerments."
PCWelt.de, 19.10.2015: "BitBox BitBox is a browser-in-the-box - a virtual environment, in order to secure the internet to make it more comfortable during the surfing. This virtual machine with a separated webbrowser protects in front of dangers, for example the rebuild resp. modified browser Dragon from the antivirus expert Comodo. His appearence reminds of Google Chrome, but Dragon is constituted to be more stable and thanks the privacy mode this browser is able to stop serious hard cookies. The inspection of SSL-certificates is more precise. Whoever wants to keep his browser save before the rest of the PC, likes to prefer BitBox - a browser-in-the-box. The developers of BitBox, the Bundesamt for Information Security (BSI), has put their browser into a fitting virtual Linux-environment. Linux has got some advantages in comparison to Windows - there are only a few "varmints", known for this operating system offered for free. So you use a virtual Ubuntu for a surf-system resp. for online-banking. A virus scanner is not required anymore. Tip: Alternatively use Wubi.exe, in order to install Ubuntu beneath Windows. This small file installs Ubuntu beneath Windows on the harddrive. When the system starts, the system is chosen. In this case, a virtual box is not needed anymore."
On Tuesday, March 3, 2015, researchers announced a new SSL/TLS vulnerability called the FREAK attack. It allows an attacker to intercept HTTPS connections between vulnerable clients and servers and force them to use weakened encryption, which the attacker can break to steal or manipulate sensitive data. This site is dedicated to tracking the impact of the attack and helping users test whether they´´re vulnerable. In addition to browsers, many mobile apps, embedded systems and other software products also use TLS. These are also potentially vulnerable if they rely on unpatched libraries or offer RSA_EXPORT cipher suites.
Vulnerable Browsers are Internet Explorer,. Chrome on Mac OS, Chrome on Android, Safari on Mac OS, Safari on iOS, Stock Android Browser, Blackberry Browser and, Opera on Mac OS.
Firefox (Windows, MAX, Linux) and Konqueror (Linux) are not affected, see freakattack.com for more details.
Tagesschau, 07.31.2014: Actually scientific experts found out, that sensible data can be read out through microcontrollers (processors) from USB-sticks, see the report from our linkside under the point links! Therefore a new USB-standard is devoloped. By this, all data of computers can be read out, even passwords and email-contents as much as devices be steered like webcams. The operating sytem does not notice all of this, as it believes in key-strokes and not software attacks.
prism-break.org: "We recommend MC-based SSD instead of magnetic harddrives, "A magentic harddrive is much to risky to intrust data. Although a lot of improvements took place, who has not heart or - in worst cases - made the experience of lost data. Therefore enough reasons are relevant" (source: poshtar@datensicherx.com, 13.05.2014)) (similar to magnetic hard-drives, in order to keep the very fast access-times of a SSD, at least 4 GB memory should be kept free, comment, the Red.)
Legend end: Microsoft ends up with Internet Explorer, Focus, 18.03.2015
New browser past 20 years
After two decades a legend of the internet died: Microsoft actually develops a new browser, in order to exchange the Internet Explorer. For the next time, his name is "Spartan" - and he shall have nothing to do with his precedor.
Tagesschau, 28.04.2014: Vulnerabilities of the microsoft-browser
USA dissuade from Internet Explorer
In Microsofts Internet Explorer, market share more than 50% (2012, studie web-analyzators from Net Applications), vulnerabilities past the date for support fof XP (08.04.2014) were found, that do still exist. The US-government advises to use other browsers for the next time. There would be so much difficutlies in the Explorer-version six to eleven, that hacker can cause enormous harm, warned the ministry of home country protection. Problems are known since the weekend. Microsoft told, to do something against them. The vulnerabiltity would cause in wrong programmed memory-accesses.
Prepared websites, that user of the internet-explorer call, could provide access for attackers to the computer, in order to execute mailicous code and take control upon the computer. The vulnerabilty already is effectively in use. It is the first serious one, since the support for Windows XP ended. Therefore it could still exist for PCs with the 13 years old operationg system regardless from Microsoft having solved the problem.
In News&Links we describe, howto make an Internet Browser of MS Windows upon the base of a Debian-sandbox secure, downloadable for free.
Internet-Gang robbs one billion dollar from banks, Focus, 15.02.2015
A bank robbery in the internet-century were made in that way: A Gang broke into in computer-systems of credit institutes and manipulated even account balances. They would have get any amounts of money from cash automates they liked.
Focus 2015: Antivirus-scanner promise allround-protection for the computer and to make the surfing online more secure. But in the half of all cases, they can not defend cyber-attacks.
Tagesschau.de 11/2013: Appelbaum from Wikileaks sees opportunities for effective encryption. Therefore free and open source were needed. Not all encryption were the same, not all companies have been confidential or can be trusted.
Tagessschau, 11/2013: Wikileaks sees opportunities for functioning encryption. One needs free and open sourced software. Not each encryption were secure, not all companies were trustable. Wikileaks hops for concete methods against. For expample, if an attorney were proclaiming trust on telephone, although he did not use an encrypted telephone, one should call careless.
Tagesschau, 10.03.2014, cite Snowden: "If you encrypt your hardware and connections within nets it is much more difficult to collect your data by mass-wise-controlling software. Of course, such data can be cracked resp. hacked for special surveillance, but remain more secure. The best proof would have been delivered by his encrypted kept own documents sent per email." ( two encryption can be made for e-mail-transfers: one of the text-includes of e-mails by pgp-gpg, one by pop3s and smtps (TLS) for the belonging connection to the pop3- and smtp-server).
 WLAN-Router WLAN-Router
Router-Sicherheitstest 2020: AVM, Asus & Co. im Vergleich, PC-Magazin.de, 16.6.2020
Welchen Anteil haben verbreitete WLAN-Router am Schutz des heimischen Netzwerks und seiner Nutzer? PC Magazin und das Sicherheitslabor AV-Comparatives sind dieser Frage in einem umfangreichen Test nachgegangen.
https://www.pc-magazin.de/vergleich/router-sicherheitstest-2020-3201633.html
 Viele WLAN-Router von Sicherheitslücke bedroht: Nutzer sollten bestimmte Funktion besser abschalten, CHIP, 28.05.2020 Viele WLAN-Router von Sicherheitslücke bedroht: Nutzer sollten bestimmte Funktion besser abschalten, CHIP, 28.05.2020
IT-Spezialisten haben eine schwerwiegende Router-Sicherheitslücke entdeckt, die offenbar eine ganze Reihe von Netgear-Geräten betrofft. Über die Lücke können sich Angreifer unbemerkt Kontrolle über die Router verschaffen und dem Nutzer so manipulierte Updates unterjubeln. Wie Sie sich davor schützen können, lesen Sie hier. Worauf es beim Kauf eines neuen Routers ankommt, erklären wir Ihnen im Video.
Die Sicherheitsforscher des IoT-Labs der FH Oberösterreich sind auf eine eklatante Sicherheitslücke beim Netgear-Router Nighthawk R7000 gestoßen; offenbar sind auch viele weitere Modelle gefährdet. Das Problem: Der Router bezieht Firmware-Updates zwar verschlüsselt - dabei wird von den Geräten offenbar jedoch nicht das jeweilige Serverzertifikat geprüft. Dadurch ist es Angreifern grundsätzlich möglich, manipulierte Updates der Firmware auf dem Router zu installieren. So können sich die Cyber-Kriminellen potentiell Kontrolle über die Router der Nutzer verschaffen.
Sind einzelne Dateien beziehungsweise der Update-Server selbst gerade nicht verfügbar, kann es sogar dazu kommen, dass die Router bei der Installation gänzlich unverschlüsselte Protokolle nutzen, um die Updates zu installieren, was Angreifer ihre Attacken noch leichter durchführen lässt. Hinzu kommt, dass digitale Signaturen vor dem Update-Prozess nicht überprüft werden. Das führt dazu, dass die Router auch manipulierte Updates installieren, ohne dass dies vom Gerät erkannt wird. Sowohl der automatische Update-Prozess als auch das Update via Assistent im Web Interface sind offenbar von der Schwachstelle betroffen.
Eine offizielle Lösung seitens des Herstellers gibt es bisher nicht: Wie die Forscher der FH Oberösterreich schreiben, habe sich Netgear seit Ende Januar nicht mehr zu dem Problem geäußert, geschweige denn einen Work-Around via Update ausgerollt.
https://www.chip.de/news/Viele-WLAN-Router-von-Sicherheitsluecke-bedroht-Nutzer-sollten-bestimmte-Funktion-besser-abschalten_182735284.html
 Router-Sicherheit: Virenforscher warnt vor Angriffen über den Browser, Spiegel Online, 26.05.2015 Router-Sicherheit: Virenforscher warnt vor Angriffen über den Browser, Spiegel Online, 26.05.2015
Über manipulierte Websites lässt sich die Konfiguration diverser Router ändern, warnt ein Virenforscher. Weil die Geräte fortan Anfragen auf gefälschte Internetangebote umleiten, haben Kriminelle die Chance, Passwörter mitzuschneiden. Einmal falsch geklickt, schon macht der Router Ärger: Eine raffinierte neue Attacke nutzt die Schwachstellen gängiger Modelle aus, Unbekannte stellen dafür mit Schadsoftware verseuchte Webseiten ins Netz. Der unter dem Pseudonym Kafeine bekannte Sicherheitsexperte beschreibt auf seinem Blog das Problem, das mindestens 40 Modelle bekannter Hersteller gefährdet, darunter Geräte von Asus, Belkin, D-Link, Linksys, Netgear und Zyxel. Fritzbox-Router tauchen nicht auf der Liste auf. Die Angriffe, die Kafeine beobachtet hat, verlaufen nach folgendem Muster: Nutzer von Googles Chrome-Browser werden zu einem Server umgeleitet, der Schadcode enthält. Dieser versucht, das Router-Modell des Nutzers zu bestimmen, um dann die DNS-Einstellungen des Geräts zu ändern. Das Domain Name System, kurz DNS, wird oft als Adressbuch des Internet bezeichnet, denn es funktioniert ganz ähnlich: Gibt der Nutzer im Browser eine bestimmte Web-Adresse ein, geht die Anfrage an den Router, der dann mithilfe eines DNS-Servers die passende IP-Adresse nachschlägt. Gelingt es einem Angreifer, sich mithilfe eines manipulierten Adressbuchs in diese Kette zu schalten, kann er dem Router andere IP-Adressen unterjubeln und den Nutzer so auf gefälschte Websites lotsen. Kriminelle könnten etwa die Startseite einer Bank nachahmen, um die Log-in-Daten abzugreifen, die auf der gefälschten Seite eingetippt werden.Fast eine Millionen Zugriffe an einem Tag: Unbekannten Angreifern ist kürzlich offenbar eine solche Umleitung von Seitenaufrufen gelungen - und das massenhaft: Ein von Kafeine beobachteter DNS-Server konnte in diesem Monat bisher täglich rund 250.000 Zugriffe verzeichnen. An einem Tag - dem 9. Mai - waren es sogar fast eine Million Zugriffe, schreibt der Virenforscher. Die Angreifer gehen clever vor: Als sekundären DNS-Server nutzen sie Googles öffentlichen DNS-Dienst, was bedeutet, dass die Betroffenen auch dann Seiten erreichen, wenn der Server der Angreifer einmal den Dienst verweigert. Bemerkenswert ist, dass offenbar nicht nur Router gefährdet sind, deren Fernwartungsfunktion aktiviert ist. Der beschriebene Angriff erfolgt Kafeine zufolge durch eine sogenannte Cross-Site-Request-Forgery (CSRF), mit der ein Browser gezwungen werden kann, Aktionen auf fremden Webseiten auszuführen. Ziel des Angriffs ist die Administrations-Oberfläche des Routers. Auch wenn sie von der Fernwartung abgekoppelt und eigentlich nur im lokalen Netzwerk verfügbar ist, lässt sie sich attackieren, da Router im Gegensatz zu Internetseiten oft nicht gegen CSRF-Attacken geschützt sind, schreibt "Computerworld".
Wie kann man sich schützen?
Die von Kafeine veröffentlichte Liste betroffener Geräte ist vermutlich nicht vollständig. Nutzer sollten daher - unabhängig davon, ob ihr Router zu den genannten gehört - prüfen, ob die Firmware Ihres Routers auf dem neuesten Stand ist und sie gegebenenfalls aktualisieren. Die Cyberkriminellen machen sich mit diesem Angriff nämlich vor allem die Bequemlichkeit der User zunutze: Einen Router konfigurieren viele Nutzer nur einmal, danach kümmern sie sich nicht mehr darum. Wie wichtig regelmäßige Firmware-Updates gerade für diese Schnittstelle ins Internet sind, hat erst vor einigen Tagen die NetUSB-Lücke gezeigt.
 Passwörter von 500.000 WLAN-Routern geleakt: Das sollten Nutzer jetzt unbedingt beachten, CHIP, 21.01.2020 Passwörter von 500.000 WLAN-Routern geleakt: Das sollten Nutzer jetzt unbedingt beachten, CHIP, 21.01.2020
FritzBox Firmware Update: So einfach geht die Aktualisierung
Hacker nutzen WLAN-Router und Server, um Botnets aufzubauen. Nun wurden die IP-Adressen und Passwörter von über einer halben Million Geräten frei zugänglich im Netz veröffentlicht. Doch es gibt Maßnahmen, die jeder Nutzer jetzt ergreifen kann. Zum Beispiel ein Update. Wie Sie Ihre Fritzbox am besten updaten, erklären wir Ihnen im Video.
https://www.chip.de/news/Passwoerter-von-500.000-WLAN-Routern-geleakt-Das-sollten-Nutzer-jetzt-unbedingt-beachten_179776444.html
 Router updaten: Bundesamt warnt vor Sicherheitslücken, PC-WELT.de, 07.01.2020 Router updaten: Bundesamt warnt vor Sicherheitslücken, PC-WELT.de, 07.01.2020
Das Bundesamt für Sicherheit in der Informationstechnik (BSI) warnt Besitzer von D-Link-Routern vor einer Schwachstelle.
Das Bundesamt für Sicherheit in der Informationstechnik (BSI) warnt aktuell die Bürger mit zwei technischen Sicherheitshinweisen der Risikostufe 3 und Risikostufe 4 vor Schwachstellen in WLAN-Routern des Herstellers D-Link. Die erste Schwachstelle ermögliche die Offenlegung von Informationen. Die zweite Lücke ermögliche das Ausführen von beliebigem Programmcode.
https://www.pcwelt.de/news/Router-updaten-Bundesamt-warnt-vor-Sicherheitsluecken-10732250.html
Typische Probleme am Router lösen, PC-WELT.de, 10.09.2019
Wenn selbst bei schnellem DSL Streams stocken oder Internettelefonate abbrechen, helfen die richtigen Einstellungen am Router.
https://www.pcwelt.de/a/typische-probleme-am-router-loesen,3449919
Kein Zugriff auf 192.168.1.1? So klappt das Router-Login, PC-WELT.de, 18.03.2019
Trotz Eingabe der IP-Adresse 192.168.1.1 oder 192.168.2.1 im Browser klappt das Router-Login nicht? Wir bringen Sie in 7 Schritten ins Router-Menü.
https://www.pcwelt.de/ratgeber/192-168-1-1-so-klappt-das-Router-Login-9638280.html
 Browse: Therefore always try to turn http:// -> https:// (ssl) in the address-line of your browser manually, before the URL of the webside is entered! Favorites should contain only such URL too. Notice, that a ssl-certificate of the webserver resp. webhoster is not present in all cases!
Browse: Therefore always try to turn http:// -> https:// (ssl) in the address-line of your browser manually, before the URL of the webside is entered! Favorites should contain only such URL too. Notice, that a ssl-certificate of the webserver resp. webhoster is not present in all cases!
JonDoBrowser: Anonymous Firefox-replacement, still beta, CHIP, 14.09.2012
The JonDos GmbH (University Leipzig) accused Firefox for having built-in functions, that are harmful for data protection. Therefore their developers released the (together with Jondo) anonymizing JonDoBrowser Beta for free, http://www.chip.de/news/JonDoBrowser-Anonymer-Firefox-Ersatz-mit-Macken_57527151.html.
Jondofox - Firefox with condom
Download Jondofox: http://www.heise.de/download/product/jondofox-58547/download
We, Gooken, introduce a list of security browser on News&Links#Alternatives#The-Green-LED#BrowserCharts For installing Jondobrowser, set the path to the firefox-profile in the installation script of Jondofox manually to /home/surfuser/.mozilla/firefox. The inegration follows right past the start of firefox. Never install addons not basing on Open Source. Jondobrowser´s integration of Add-ons like https-everywhere should, as described, also be seen critically.
Freak: "Freak"-Sicherheitslücke: Auch Windows betroffen, 06.03.2015,
Mit einem sogenannten "Freak"-Angriff wird es Dritten möglich, eigentlich geschützten Datenverkehr zu entschlüsseln und womöglich persönliche Daten mitzulesen. Diese Betriebssysteme und Browser sind betroffen.
Am vergangenen Dienstag wurden Informationen über die sogenannte "Freak"-Sicherheitslücke öffentlich gemacht. Durch diese können Dritte Daten aus eigentlich geschützten SSL-/TLS-Verbindungen abgreifen. Damit dies aber tatsächlich möglich wird, müssen bestimmte Kombinationen aus benutztem Webbrowser und verwendetem Betriebssystem gegeben sein. Grundsätzlich sind Android-, iOS-, Windows-Phone-, Windows-, Mac- und Linux-Nutzer gefährdet. Zum Ausnutzen der Lücke müssen zudem Webseiten mit einer geschwächten Verschlüsselung angesurft werden, wie auf.
During a normal browsing with MS Windows and MAC, focus 31.08.2014
Danger in the internet: the unvisible drive-by-download
Infections by drive-by-downloads are very perfide. During the surfing in the internet, malware of infected websites can be loaded onto the computer without the possibility to notify it - article by FOCUS-Online-expert Marco Preuss
Stern.de reports in April 2014 about adobe-flash-player with security-lacks that can lead into trojans finding out password and credit-card-information. Updating this software is strongly recommended, same for Java. With UNIX-Systems updates, patches and bugfixes can be be performed from their original sources and that means immediately with the date of their release as much as in the following example:
Checksum helps to prevent the download of trojans out of the internet.
Inceasing amount of data theft, Tagesschau, 07.04.2014
As IT-security-experts tell among other things in conjunction with lacks in security of OpenSSL, In year 2013 data of more than half billions internet-users have been stolen as a result of online-attacks. 552 million identities are involved, as told by a security-company about six × more than 2012.
Sueddeutsche.de, 21.12.2014 tells in a report, that you still can not trust cloud computing and the own data on other far-away-server. We believe not only in security risks of cloud computing, but also in data receiving consulting companies from there. Inspite of our excurs, on the base of some other operating systems there still were a need for security experts in 2014!
Tageschau, 28.04.2014 reports about actually found out one more serios hard security lack in Internet Explorer 6 up to 11 (market share value more than 50 %, 2012, .netApplications), so that XP, no further updates available since 04.08.2014, still has to be updated and even USA advised to use other browser by so called country-protecting organizations. The troubles caused by such Internet Explorer versions would have been such big, that hacker could do harm a lot. Since the last weekend, Microsoft is looking for solutions. The security-whole conisted of a buggish memory-access that enabled users using the IE to gain access to computers to execute mailicious code and to gain control over the computer. This security-lack would have been already taken in use.
AOL email-accounts including security-requests also would have been hackened.
Yesterday Apple Apple warned against data theft due to a lack in security in OS-X. If an attacker is provided access to the same network as other users - for example the usage of abad protected WLAN-connection of a restaurant - he could be able to access data from email-transfer and other communication procedures (protocols), that should have been encrypted instead as already mentioned by Edward Snowden, his former organization would already have taken advantage upon it..
Not much can be done against fake accounts in the name of identity theft of oneself in the internet except by law. One should register oneself in the most popular social networks like facebook to make a contribute to avoid it. Such account should be suited with as few sensible data as possible and be visited regulary in this sense of maintenance.
We, Gooken, also notice, that norisbank (Deutsche Bank) gots certified many times for online banking by german certifiers like "Stitung Warentest", although, as Tagesschau reported, states do invest billons more or less against such this security of encryption! In such cases UNIX-commands like "tcptraceroute" can provide users some important facts about such online-connections (as00.estara.com). Instead OpenSSL should strongly be updated from openssl.org at least to version >= 1.0.2d past 07.04.2014 ... as part of our DVD-2 mdv2010.0-updates!
Such red marked text does not come to an end on our webside "News&Links", if it were not enough red... . Please click here!
 The essential Idea: "PC-refrigerator" through airodynamic The essential Idea: "PC-refrigerator" through airodynamic
might origin not from us, but is to do everything right at the beginning. Not software, but the exemplary, power-saving and therefore the net-adapter enburdening hardware depicted in our data sheed stands in the middle of interest here. To be more concrete, we talk about the computer tower itself, where everything should prepared for best air-cirulation. This cooling box (hardware-refrigerator) makes it possible to cool down warm air 3 up to 10 degree;C. All you need are one or better two cooler, one for the incoming air right up at the bottom of the front of the tower and one more for at the top of its back for the leaving of the air in a quit fast way. Therefore do not forget to seal the rest of the tower using plastic foils and adhensive tapes. Not only the circulating air but also the metal of the walls of the tower do also have the specifiation to increase the cooling of the inside. If possible, also follow the tip from fr2.rpmfind.net, where the tower of the server system consists of half-cylindered metal plate between the two coolers upon the mainboard. Screen resolution and screen repition rate should be set to "auto" following an almost large rate between 59 up to 95 Hz and higher. Now, the eye-friendly graphic chip can show what is performance especially during extrem burdening play of opengl- and sdl- based computer-games-scenes, while the stable hardware might do its work forever too.
Mandriva Linux 2010 - The Calming
Therefore you almost need:
2 SSD at least a 128 GB or 1 SSD or 1 (external) harddrive of thecapacity of at least the installation-SSD or -harddrive for the restauration and the backup
1 USB-memory stick with a command dd and the partitionmanager gparted providing rescure system, Mindi, Mondo or a DVD with Knoppix (that you can download out of the internet), best, following the manual howto install on harddrive, such Knoppix on a separte, small, greater or equal 250 MB partition on the installation-SSD or harddrive and
1 directory for all the already installed packages.

See, how Linux is prepared for the endurable mouseclick-fast work with SSD:
Linux tips & tricks
Linux ready and optimized for SSD: http://www.pcwelt.de/ratgeber/Linux-Special-SSDs-unter-Linux-6593528.html. The text of this webside is in german language, so we summarize, that we recommend the full-installation of Linux on SSD. Important seems to be the ability to trim the SSD, what can be checked out by the command "hdparm -I /dev/sda | grep -i TRIM". In /etc/fstab noatime,nodiratime,data=writeback and eventually option discard should be set for the root-, home- and the temporary partition, for SWAP use commit=0,data=writeback,discard. commit stands for the period, data are written out of the cache onto SSD. Do not set it too high, not above 600. The last thing for the SSD to make work mouseclick-fast is the installation of the rpm-packages hdparm and sdparm for el7. Following an instruction for Debian, also set in /etc/crypttab the option "allow-discards" for dm-crypt and in /etc/lvm/lvm.conf the option "allow-discards" for LVM (we resigned from LVM), for Btrfs-filesystems also set the mount-option "ssd" in /etc/fstab.
The read-access-time in MB/s can be find out by "hdparm -t /dev/sda" and
one more test still uses both options -t and -T, but also option --direct ("Use O_DIRECT to bypass page cache for timings"), what leads to direct read without page cacheing. This test is almost used, as the pure data flow to the SSD within two resp. three seconds is measured: "hdparm -tT --direct /dev/sda"
Check, if the started kernel does already recognize the SSD: cat /sys/block/sda/queue/rotational
If zero resp. 0, he does! If not, please follow reports like https://wiki.ubuntuusers.de/SSD/Scheduler/
 Following this report, the IO-Scheduler can be chosen: noops, deadline or CFQ. cat /sys/block/sda/queue/scheduler shows the activated one in edged brackets. After performing tests like above, choose the right one, that is almost noops, especially deadline by Grub (analogous Grub2) entering in /boot/grub/menu.lst the option "elevator=deadline" past the kernel-options beginning with kernel=... and past ro resp. rw .
The Firmware-version is named by "hdparm -iv /dev/sda"
Following this report, the IO-Scheduler can be chosen: noops, deadline or CFQ. cat /sys/block/sda/queue/scheduler shows the activated one in edged brackets. After performing tests like above, choose the right one, that is almost noops, especially deadline by Grub (analogous Grub2) entering in /boot/grub/menu.lst the option "elevator=deadline" past the kernel-options beginning with kernel=... and past ro resp. rw .
The Firmware-version is named by "hdparm -iv /dev/sda"
For TRIM-supporting SSD "discard" can be set not only in /etc/fstab and allow-discards not only in crypttab, but for ext4 also by command tune2fs:

| tune2fs /dev/device-filename resp. ( in the case of LUKS-encryption) tune2fs -o discard /dev/mapper/container_filename |
This command makes the "durable" activation of the SSD-TRIM by option "discard" without blockings much more possible
Universal-Linux BULLET-PROOF: Root-partition read only
For the Root- and Home-Partition depending on conditons, we also can set the ro-Option for read-only, if we do not want to install and update anyhting anymore, do this by following the conditions of the arcticle from http://xpt.sourceforge.net/techdocs/nix/sysmng/sm08-ReadOnlyRootFileSystem/, https://wiki.debian.org/ReadonlyRoot, http://www.linuxfromscratch.org/hints/downloads/files/readonly_rootfs.txt and http://www.logicsupply.com/explore/io-hub/how-to-build-a-read-only-linux-system/ . Even think about the deactivation of the journalling of reiserfs by option "nolog", that keeps the SSD from writing journals (that means logs of the last stable (error-free) state before errors occured, in order to restore in error-cases). More or less, setting root-partition read-only can be considered as useful, but a little bit "paranoid":
 "Read-only rootfs: Theory and Practice - Chris Simmonds, 2net
"Read-only rootfs: Theory and Practice - Chris Simmonds, 2net
Configuring the rootfs to be read-only makes embedded systems more robust and reduces the wear on flash storage. In addition, by removing all state from the rootfs it becomes easier to implement system image updates and factory reset.
In this presentation, I show how to identify components that need to store some state, and to split it into volatile state that is needed only until the device shuts down and non-volatile state that is required permanently. I give examples and show various techniques of mapping writes onto volatile or non-volatile storage. To show how this works in practice, I use a standard Yocto Project build and show what changes you have to make to achieve a real-world embedded system with read-only rootfs. In the last section I consider the implications for software image update. Expect a live demonstration"
https://www.youtube.com/watch?v=Nocs3etLs9
https://wiki.debian.org/ReadonlyRoot # (usage at your own risk!)
Preconditions
The FHS allows mounting all underneath /bin, /lib, /sbin and /usr read-only. But you can extend this much more by using different filesystems for some trees and take care for special files.
Locations that must be writable are /etc, /home, /srv, /tmp, /var. The hierarchies below /dev, /proc, /selinux and /sys are already handled by special filesystems.
For /tmp you can use a tmpfs filesystem or its own filesystem. For /var it´s prefered to use its own filesystem. An example can look like this:
Device file Filesystem Mount point RO/RW
/dev/sda1 ext2 / ro
/dev/sda2 ext3
/var rw
—
tmpfs /tmp rw
/var/local/home bind mount /home rw
/var/local/srv bind mount /srv rw
You can use a filesystem without a journal for /, because you don´t write there and you don´t need the journal. This can be an ext4, too, hence you can take advantage of the improvements of ext4. Create the filesystem with mke2fs -t ext4 -O ^has_journal /dev/sda1 or remove the journal with tune2fs -O ^has_journal /dev/sda1.
Special files in /etc
You have to take care for some files in /etc. These are
adjtime
because it´s modified on boot up; see bug 156489
Solution for mdv and el6,el7: Change the hwclock-command in /etc/init.d/reboot and /etc/init.d/halt from "hwclock --systohc" to "hwclock --systohc --adjfile=/var/local/adjtime".
Solution for Debian Wheezy:
(1) add the option --noadjfile to HWCLOCKPARS in /etc/init.d/hwclockfirst.sh and /etc/init.d/hwclock.sh
or
(2) fix /etc/init.d/hwclockfirst.sh by replacing -f by -L in "if [ -w /etc ] && [ ! -f /etc/adjtime ] && [ ! -e /etc/adjtime ]; then"; see 520606.
alsa: init.d/alsa-utils
All versions before alsa-utils/1.0.27.2-1 (@2013-10-25 concerns wheezy version) of alsa-utils package startup script creates /.pulse files, leading to multiple error messages "Failed to create secure directory" when pulseaudio is installed.
Relevant bug: 712980
blkid.tab
because it´s modified at runtime by libblkid1
Solution:You can´t create a symlink from /etc/blkid.tab to /var/local/blkid.tab because, unfortunately, libblkid1 will not honor this symlink. It will replace it on every write by a file, if the filesystem is mounted for writing (e.g. while doing an apt-get install). To work around this you must set the environement variable BLKID_FILE to /var/local/blkid.tab. You should do this in /etc/environment to set the variable for everybody, who might do mounting.
courier imap
Courier IMAP uses a text file (/etc/courier/shared/index) for fast user lookups, if running as a mail server for virtual mailboxes (the default configuration of authenticating against pam is unaffected by this).
If using virtual mailboxes with shared accounts the file will need to be moved elsewhere, the directory /var/cache/courier/shared/ would be suitable but will need to be manually created.
Once that is done update /etc/courier/imapd and change IMAP_SHAREDINDEXFILE to IMAP_SHAREDINDEXFILE=/etc/courier/shared/index .
See http://www.courier-mta.org/imap/README.sharedfolders.html for information upstream provide about this setting.
cups
CUPS stores any kind of state files under /etc (classes.conf, cupsd.conf, printers.conf subscriptions.conf) and upstream is against any modification.
Relevant bug: 549673
lvm
Lvm stores a backup of current and archives of previous metadata in /etc/lvm/{backup,archive}. That causes any operation altering the metadata (vgreduce, vgextend, lvcreate, lvremove, lvresize, ...) to fail if / is not remounted read-write during the operation.
Solution: The location of the backup and archives is specified in /etc/lvm/lvm.conf. Set backup_dir = "/var/backups/lvm/backup" and archive_dir = "/var/backups/lvm/archive", create /var/backups/lvm and move /etc/lvm/backup and /etc/lvm/archive there.
Note: Lvm normally creates a backup during boot. This no longer happens as it is smart enough to see that /var is not yet mounted (or still read-only). But unless you use cluster lvm you will always already have a current backup from the last time you changed the metadata. So no harm done.
Relevant bugs: 372207 562234 (for etckeeper behavior WRT LVM files see 462355)
mtab
used by mount
Solution: Create a symlink from /etc/mtab to /proc/self/mounts
mount.cifs (before smbfs 2:3.4.3-1) doesn´t honour this symlink and replace it with a real file; see 408394
mtab is in /etc for historical reasons as per FHS 2.3.
network/run
Used by ifupdown up to Squeeze
Solution: ifupdown links /etc/network/run to /run/network in postinst if /etc/network/run is not a directory.
rm -rf /etc/network/run
dpkg-reconfigure ifupdown
Alternatively: Create a symlink from /etc/network/run to /lib/init/rw/etc-network-run (network/run is accessed by ifupdown init scripts before /var might be mounted, therefore, the abuse of /lib/init/rw)
Systems running Wheezy will be automatically moved to using /run/network no matter what their existing configuration was.
Relevant bug: 389996
nologin
modified on boot up by the initscripts bootmisc.sh and rmnologin
This should already be a symlink to /var/lib/initscripts/nologin
In wheezy the init scripts directly modify /var/lib/initscripts/nologin
resolv.conf
If you have only a static nameserver configuration, then there´s no problem. Otherwise you should use the package resolvconf.
passwd, shadow
These files might be modified by the user with the tools chfn, chsh and passwd. If you are the only user of you system, you can remount the filesystem read/write, before using these tools. Otherwise you might think about using NIS or LDAP.
samba/dhcp.conf
If the dhcp3-client (AKA isc-dhcp-client) package is installed, every time a DHCP connection is established, /etc/dhcp3/dhclient-enter-hooks.d/samba creates /etc/samba/dhcp.conf, no matter if it is used or not in /etc/samba/smb.conf.
Relevant bug: 629406
suck
suck puts files in /etc/suck which are modified by suck at runtime; see 206631 To work around this problem, you have to move /etc/suck/sucknewsrc* to a new directory /var/local/suck, create a symlink /etc/suck/suckkillfile to /var/local/suck/suckkillfile and set etcdir in get-news.conf to /var/local/suck (this sets the -dd option of suck)
udev
If the udev rules 75-cd-aliases-generator.rules and 75-persistent-net-generator.rules are enabled, udev will try to update the files 70-persistent-cd.rules and 70-persistent-net.rules in /etc/udev/rules.d/ if needed. It is recommended to create the files once with all the rules needed and then disable the /etc/init.d/udev-mtab init script. While the root is readonly new rules are added to /dev/.udev/rules.d/.
Copy /var/lock or /var/lock/* to the mini-partition for /var. Do this also for kernel-partition /tmp or set /tmp to read-write. Copy /var/log/* to it too and link it to /tmp: "ln -sf /tmp /var/log/*".
Link the konqueror-browser-cache to /tmp: This means linking some cache-files of /home/user/.kde4 resp. /home/surfuser/.kde4 with the temporary /tmp one.
Enable readonly root
To make your root filesystem mounted readonly, you must edit your /etc/fstab and set the mount option ro.
# /etc/fstab: static file system information.
#
# file system mount point fs-type options dump pass
/dev/hda1 / ext2 defaults,noatime,ro,errors=remount-ro 0 0
/dev/hda4 /var ext3 defaults 0 2
The option noatime is useful while the disk is mounted read/write while updates.
https://wiki.debian.org/ReadonlyRoot, http://xpt.sourceforge.net/techdocs/nix/sysmng/
sm08-ReadOnlyRootFileSystem/, http://www.linuxfromscratch.org/hints/downloads/files/readonly_rootfs.txt und http://www.logicsupply.com/explore/io-hub/how-to-build-a-read-only-linux-system/.
ext4 partition READ ONLY mounten - forum.ubuntuusers.de
forum.ubuntuusers.de/topic/ext4-partition-read-only-mounten
Next step: Deactivate journalling-feature of file systems like ext4 and reiserfs (reiserfs: nolog-option) and
disable filesystem-checks by tune2fs (ext4) resp. reiserfstune and by setting the fs-check-parameter for the root-partition to 0.
Now a correcture within /etc/rc.sysinit shall be done:
"if remount_needed ; then
action "Remounting root filesystem in read-write mode: " mount -n -o remount,rw /
fi"
nach
"if remount_needed ; then
action "Remounting root filesystem in read-write mode: " mount -n -o remount /
fi"
see https://bbs.archlinux.org/viewtopic.php?id=135943
At last the kernel-option "ro" should be entered in /boot/grub/menu.lst for grub, for example behind "root=UUID...".
Never mind or nevertheless, If these steps for setting the root-partition read-only do not help, try the following article: http://xpt.sourceforge.net/techdocs/nix/sysmng/sm08-ReadOnlyRootFileSystem/single/
Generally, the security level of software is not only presented by stability, but also by the freeness of errors and warnings during the compilation of their source codes listed by the compiler. Kernel-2.6.32 (el6) consits of many of them and most of them are caused by kmem.h, while kernel-5.4.249 (PCLinuxOS) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) and glibc (el8, pclos, mga6) resp. kernel-2.6.39.4-5.1 (mdv2011) runs error-free on our system without any warnings during the compilation time of around four hours! The only thing remaining is to patch with the dirty-cow-patch in mm.h and memory.c (listed in the internet). You can get acutal patches for this kernel from see our section for updates.
After the installation of kernel-4.19 (pclos), lookout for the requirements and install missing ones like kmod (pclos): "rpm -qi --requires kernel-4.19....".
New Kernel: Configuration and Installation out of its source
How to install a new kernel: Download and install all binary packages (rpm resp. deb) required for the kernel. Then download and enpack the kernel-source-rpm into /usr/src either by "tar -xvjf kernel-source-package" or file-roller. A new directory named "linux-kernelversion-xxx" or "kernel-source-xxx" is created within /usr/src.
Link this new directory to a linking file named linux: "ln -sf linux-xxx linux" resp. "ln -sf kernel-source-xxx linux".
Change into this directory linux resp. linux-xxx resp. kernel-source-xxxx and call "menu oldconfig". A file .config is created to configure the kernel.
Set the Kernel-Version at the top of the makefile.
Type "menu xconfig" or "menu gconfig" or "make menuconfig" and configure the kernel-drivers and so on needed (CC), needed as modules (CC MM) and such to resign from.
FSE (full system encryption) prevents from chroots, mounts (see "man mount") and bootups especially through systems on USB-sticks and from CD/DVD in order to read all kind of data from storage media like harddrives and memory (RAM) and data theft and so on.
For FSE (full system encryption) by dracut, two options have to be enabled, what is already done in kernel-desktop (mdv2011) but not kernel (el6):
within the first item "General Setup"enable "Initial-RAM-filesystem and RAM-disk-support"and in "general drivers" enable the option "Maintain a devtmpfs at /dev/ with subitem "automount devtmpfs at /dev, after the kernel mounted the rootfs".
If you do not know, what to enable or not, choose MM to load as a module wherever possible.
Linus Tovald called the grsecurity-patches rubbish (PRO-LINUX, 2017, 2018):
http://rpmfind.rediris.es/rpm2html/suse-8.2/secumod-1.6e-91.x86_64.html
Nice description, but as far, as I know this kernelmodule does following.
The system is been protected by disallowing several things
- ´texec´ : TPE protection (Trusted Path Execution, more on this later)
- ´procfs´ : procfs protection
- ´hardlink´ : hardlink create protection
- ´symlink´ : symlink follow protection
- ´rawdisk´ : rawdisk protection
- ´pipe´ : Pipe (FIFO) protection
- ´trace´ : process trace protection
- ´systable´ : syscall table checking
- ´logging´ : if you want logging, turn this on
- ´persist´ : by default this is set to 0, so the module can be unloaded,
but you may set it to 1 to make it unremovable
- ´capbits´ : set the capbits value. You have to supply a certain mode for
the capbits variable.
Hardlink/symlinkprotection protects the system from making this links for
users.
Persist sets a capability that the module cannot be unloaded.
Capbits are kernelbits, that define certain rights even for root - in normal
case root could do allmost anything.
Like in all cases you have to know, what you do, because with that module
loaded some processes will not have the full rights they need.
For example I tried a /proc protection module and hotplug freezed after that
(not funny).
There is no real desription of anything reguarding that module and I don´t
know, which bits to set and which not!
Another thing is the opensource thing within that modules, because you can
only use them on SuSE (with some disadvantages you can use the
firewallscript on Debian and Red Hat).
It is allways a nice thing to make more a secret of a thing, than
describing, how it works.
Philippe
https://archive.cert.uni-stuttgart.de/suse-security/2003/09/msg00202.html
 grsecurity-patch - Components (similar to secumod), en.wikipedia.org grsecurity-patch - Components (similar to secumod), en.wikipedia.org
kernel source: subdirecotry of /usr/src/kernel-version/, "patch -p1 < ../grsecurity.patch"
PaX
A major component bundled with grsecurity is PaX. Among other features, the patch flags data memory, the stack, for example, as non-executable and program memory as non-writable. The aim is to prevent memory from being overwritten, which can help to prevent many types of security vulnerabilities, such as buffer overflows. PaX also provides address space layout randomization (ASLR), which randomizes important memory addresses to reduce the probability of attacks that rely on easily predicted memory addresses.
Role-based access control
Another notable component of grsecurity is that it provides a full role-based access control (RBAC) system. RBAC is intended to restrict access to the system further than what is normally provided by Unix access control lists, with the aim of creating a fully least-privilege system, where users and processes have the absolute minimum privileges to work correctly and nothing more. This way, if the system is compromised, the ability of the attacker to damage or gain sensitive information on the system can be drastically reduced. RBAC works through a collection of roles. Each role can have individual restrictions on what it can or cannot do, and these roles and restrictions form an access policy which can be amended as needed.
A list of RBAC features
:
Domain support for users and groups
Role transition tables
IP-based roles
Non-root access to special roles
Special roles that require no authentication
Nested subjects
Support for variables in the configuration
And, or, and difference set operations on variables in configuration
Object mode that controls the creation of setuid and setgid files
Create and delete object modes
Kernel interpretation of inheritance
Real-time regular expression resolution
Ability to deny ptraces to specific processes
User and group transition checking and enforcement on an inclusive or exclusive basis
/dev/grsec entry for kernel authentication and learning logs
Next-generation code that produces least-privilege policies for the entire system with no configuration
Policy statistics for gradm
Inheritance-based learning
Learning configuration file that allows the administrator to enable inheritance-based learning or disable learning on specific paths
Full path names for offending process and parent process
RBAC status function for gradm
/proc/<pid>/ipaddr gives the remote address of the person who started a given process
Secure policy enforcement
Supports read, write, append, execute, view, and read-only ptrace object permissions
Supports hide, protect, and override subject flags
Supports the PaX flags
Shared memory protection feature
Integrated local attack response on all alerts
Subject flag that ensures a process can never execute trojaned code
Full-featured, fine-grained auditing
Resource, socket, and capability support
Protection against exploit bruteforcing
/proc/pid filedescriptor/memory protection
Rules can be placed on non-existent files/processes
Policy regeneration on subjects and objects
Configurable log suppression
Configurable process accounting
Human-readable configuration
Not filesystem or architecture dependent
Scales well: supports as many policies as memory can handle with the same performance hit
No run-time memory allocation
SMP safe
O(1) time efficiency for most operations
Include directive for specifying additional policies
Enable, disable, reload capabilities
Option to hide kernel processes
Chroot restrictions
grsecurity restricts chroot in a variety of ways to prevent various vulnerabilities and privilege escalation attacks, as well as to add additional checks:
No attaching shared memory outside chroot
No kill, ptrace (architecture-independent), capget, setpgid, getpgid and getsid outside chroot
No sending of signals by fcntl outside chroot
No viewing of any process outside chroot, even if /proc is mounted
No mounting or remounting
No pivot_root
No double chroot
No fchdir out of chroot
Enforced chdir("/") upon chroot
No (f)chmod +s
No mknod
No sysctl writes
No raising of scheduler priority
No connecting to abstract unix domain sockets outside chroot
Removal of harmful privileges via cap
Miscellaneous features
Among other things, it can be configured to audit a specific group of users, mounting/unmounting of devices, changes to the system time and date, and chdir logging. Some of the other audit types allow the administrator to also log denied resource attempts, failed fork attempts, IPC creation and removal, and exec logging together with its arguments.
Trusted path execution is another optional feature that can be used to prevent users from executing binaries not owned by the root user, or world-writable binaries. This is useful to prevent users from executing their own malicious
binaries or accidentally executing world-writable system binaries that could have been modified by a malicious user.
grsecurity also hardens the way chroot "jails" work. A chroot jail can be used to isolate a particular process from the rest of the system, which can be used to minimise the potential for damage should the service be compromised. There are ways to "break out" of a chroot jail, which grsecurity attempts to prevent.
There are also other features that increase security and prevent users from gaining unnecessary knowledge about the system, such as restricting the dmesg and netstat commands to the root user.[13]
List of additional features and security improvements:
/proc restrictions that do not leak information about process owners
Symlink/hardlink restrictions to prevent /tmp races
FIFO restrictions
dmesg restriction
Enhanced implementation of trusted path execution
GID-based socket restrictions
Nearly all options are sysctl-tunable, with a locking mechanism
All alerts and audits support a feature that logs the IP address of the attacker with the log
Stream connections across Unix domain sockets carry the attacker´s IP address with them (on 2.4 only)
Detection of local connections: copies attacker´s IP address to the other task
Automatic deterrence of exploit brute-forcing
Low, medium, high, and custom security levels
Tunable flood-time and burst for logging
https://en.wikipedia.org/wiki/Grsecurity
Activate only those options, that will not lead into serious hard malfunctionings of the kernel!
 Install paxctld (rpm or tarball from http://www.grsecurity.net) Install paxctld (rpm or tarball from http://www.grsecurity.net)
Save the new .config.
Three possibilites, after the patching of the source-code (in our case the dirty-cow-patch):
make -i rpm (to create the binary kernel-rpm package, what endures on our system for around four hours)
make bzImage (to create its core vmlinuz for /boot only after renaming the created file bzImage: time needed: around 30 minutes) or
make bzImage &&make modules &&make modules_install for the installation of the kernel-modules too.
Copy the bzImage to /boot, rename it to vmlinuz-kernelversion.
Use mkinitrd resp. in the case of FSE (Full Disk Encryption resp. encrypted root-partition) dracut to create the initrd resp. initramfs within directory /boot.
If you use grub as the bootloader and not grub2 and the configufile is still not configured for the new kernel, do this by editing /boot/grub/menu.lst and exchanging the vmlinuz-kernel-versions. If a new initramfs or initrd is created, enter them in the line for initrd.
done.
In our /grub/menu.lst, quit the same for grub2, the resulting entry for FSE (Full System Encryption) performed according to by gentoo-Schnatterente is:
title dracut-mdv-008-Linux
password --md5 $103Axa2112...
kernel (hd0,7)/vmlinuz BOOT_IMAGE=dracut-mdv-008-Linux root=UUID=2193ab... resume=UUID=2193ab... rootfstype=ext4 elevator=deadline nosmp security=none panic=0 apparmor=0 selinux=0 disable=IPV6 audit=0 hibernate=protect_image iomem=strict nosmp iomem=relaxed speedboot=yes KEYMAP=de LANG=de_DE.UTF-8 intel.audio=1 intel.modeset=1 intel.dpm=1 rd.luks=1 rd.lvm=0 rd.md=0 rd.luks.allow-discards rd.luks.uuid=ab1....vga=795 video=VGA-1:1366×768 tz=Europe/Berlin
initrd (hd0,7)/initramfs
0 of (hd0,7) stands for sda, 1 for sdb usw. and 7 for the boot-partition sda8, deadline for the SSD optimizing elevator resp. scheduler to choose, what is introduced soon through the configuraiton by special echo-commands.
Set resume=UUID=... from above to the UUID from root=UUID=... from above (UUID of the Luks-encrypted root-partition) ! Also eventually set the boot-parameter noinitrd.
 kernel.yama.ptrace_scope=3
kernel.yama.ptrace_scope=3
# 0 - Default attach security permissions.
# 1 - Restricted attach. Only child processes plus normal permissions.
# 2 - Admin-only attach. Only executables with CAP_SYS_PTRACE.
3 - No attach. No process may call ptrace at all. Irrevocable.
echo "kernel.yama.ptrace_scope=3" > /etc/sysctl.d/10-ptrace.conf
Boot-paramter-list:
http://redsymbol.net/linux-kernel-boot-parameters/2.6.39/
The rescue-system Knoppix (Debian Linux, in our case Wheezy ol´ stable i386 (32 bit) from year 2010 with partition-manager gparted and dd, browser iceweazel and many tools and software) copied from DVD to an extra partition of at least 250 MB is listed in /boot/grub/menu.lst of the bootmanager Grub as follows:
title Rescue
password....
root(hd0,4)
kernel /boot/isolinux/linux knoppix keyboard=de lang=de_DE.UTF-8 desktop=kde tz=Europe/Berlin
initrd /boot/isolinux/minirt.gz
boot
It boots within few seconds and makes password-request to make it run and to get decrypted from its partition. After the login, in order to decrypt all the other LUKS-encrypted partitions, LUKS/dm-crypt should be installed, so at first packet cryptsetup has to be downloaded from the Debian-pool (debian.org). Update glibc too. If you want, you can update and/or increase this system up to a more comfortablel Debian Linux on an enlarged partition.
Information about the availability of TRIM of a SSD for the TRIM with discard-option on the base of ext4 out of /etc/fstab:
| hdparm -I /dev/sda | grep -i trim |
Our partition-concept for MCC-" partition manager (local harddrives) or gparted upon parted,
our partiitions on SanDisk SSD 120 GB:
 LUKS-(cryptsetup)-encrypted extra partition (for sensible data and so on, with a key-file, that means for automatic encryption and decryption): 29 GB
LUKS-(cryptsetup)-encrypted extra partition (for sensible data and so on, with a key-file, that means for automatic encryption and decryption): 29 GB
 LUKS-(cryptsetup)-encrypted root-partition ("schnatterschnatter - but no ente"quot;): 50 GB
LUKS-(cryptsetup)-encrypted root-partition ("schnatterschnatter - but no ente"quot;): 50 GB
 LUKS-(cryptsetup)-encrypted (urandomed self de- and encrypting) SWAP-partition: 1,9 GB (2 GB RAM)
LUKS-(cryptsetup)-encrypted (urandomed self de- and encrypting) SWAP-partition: 1,9 GB (2 GB RAM)
 Boot-partition (unencrypted, so that this partition should be backuped to compare files like kernel named vmlinuz with md5sum or sha1sum) : 203 MB
Boot-partition (unencrypted, so that this partition should be backuped to compare files like kernel named vmlinuz with md5sum or sha1sum) : 203 MB
 KNOPPIX-encrypted-partition Knoppix (rescue system from DVD, a up to year 2016 actualized Debian Ol´ Wheezy from year 2010 with gparted, dd and much more. LUKS (cryptsetup) should be installed additionally too for editing above listed other partitions): 894 MB
KNOPPIX-encrypted-partition Knoppix (rescue system from DVD, a up to year 2016 actualized Debian Ol´ Wheezy from year 2010 with gparted, dd and much more. LUKS (cryptsetup) should be installed additionally too for editing above listed other partitions): 894 MB
 LUKS-(cryptsetup)-encrypted home partition (encrypted and decrypted automatically during boot by a once generated belonging key-file from the root-partition): 34 GB
LUKS-(cryptsetup)-encrypted home partition (encrypted and decrypted automatically during boot by a once generated belonging key-file from the root-partition): 34 GB
Advantage: easy handling, without Logical Volume Management (LVM) !
This all 1:1 upon another securing media, in our case the same one and therefore one more SanDisk 120 GB.
 /etc/crypttab
/etc/crypttab
# <target name> <source device> <key file> <options>
cryptohome UUID=.... /somewhere/keyfile luks,data=ordered,allow-discards
cryptswap /dev/sda_certain_number /dev/urandom swap,check=/bin/true,data=ordered,allow-discards
/boot/grub/menu.lst:
setkey y z
setkey z y
setkey Y Z
setkey Z Y
setkey equal parenright
setkey parenright parenleft
setkey parenleft asterisk
setkey doublequote at
setkey plus bracketright
setkey minus slash
setkey slash ampersand
setkey ampersand percent
setkey percent caret
setkey underscore question
setkey question underscore
setkey semicolon less
setkey less numbersign
setkey numbersign backslash
setkey colon greater
setkey greater bar
setkey asterisk braceright
timeout 10
password --md5 ...
default 0
kernel (hd0,7)/vmlinuz BOOT_IMAGE=linux root=UUID=c1... rd.luks.allow-discards rootfstype=ext4 nosmp elevator=deadline security=none nosmp speedboot=yes panic=0 apparmor=0 iomem=strict hibernate=protect_image disable=IPV6 selinux=0 audit=0 KEYMAP=de LANG=de_DE.UTF-8 intel.audio=1 intel.modeset=1 intel.dpm=1 rd.luks=1 rd.multipath=0 rd.dm=0 rd.lvm=0 rd.md=0 rd.shell=0 rd.luks.uuid=3... video=VGA-1:1366×768 vga=795 tz=Europe/Berlin desktop=kde
initrd (hd0,7)/initramfs-4.9.49
The root-partition seems to be sized quit small, so choose 60 GB instead of 50, we suggest to the disadvantage of the extra partition.
Order each entry in the device-configuration-file /etc/fstab: 1 device-file (partition or disc))/device/UUID/kernel-partition 2 mountpoint 3 filesystem 4 mount-options 5 Dump 6 fsck (self-check during the system start resp. boot), details:
 So in /etc/fstab we can set for ext4 (discard supported), ext3 (withoud discard), reiserfs (without discard), reiser4fs (discard), btrfs (discard), vfat (without discard):
So in /etc/fstab we can set for ext4 (discard supported), ext3 (withoud discard), reiserfs (without discard), reiser4fs (discard), btrfs (discard), vfat (without discard):
 root-partition: UUID=... / ext4 notail,noatime,nodiratime,barrier=flush,data=writeback,nouser,user_xattr,mode=500,async,commit=0,umask=077,iocharset=utf-8,acl 0 root-partition: UUID=... / ext4 notail,noatime,nodiratime,barrier=flush,data=writeback,nouser,user_xattr,mode=500,async,commit=0,umask=077,iocharset=utf-8,acl 0
 Bootpartition (hier wegen dracut): UUID=... /boot ext4 noatime,nodiratime,ro,nouser,nouser,noexec,async,nosuid,mode=500,umask=077,user_xattr,data=writeback,commit=0,iocharset=utf-8,acl 0 3 Bootpartition (hier wegen dracut): UUID=... /boot ext4 noatime,nodiratime,ro,nouser,nouser,noexec,async,nosuid,mode=500,umask=077,user_xattr,data=writeback,commit=0,iocharset=utf-8,acl 0 3
 Home-Partition: /dev/mapper/cryptohome /home ext4 rw,suid,nodev,noexec,nosuid,auto,async,noatime,nodiratime,discard,data=writeback,commit=0,nouser_xattr,barrier=1,journal_checksum,mode=700,umask=077,errors=remount-ro,iocharset=utf-8 0 # automatic cryptsetup is recommended (cryptsetup-option --key-file): Only access over the root-partion with the stored key-file will be possible. Acess-rights for the key-file: chown root:root path_to_key_file/key.asc && chmod 400 /patch_to_key_file/key.asc Home-Partition: /dev/mapper/cryptohome /home ext4 rw,suid,nodev,noexec,nosuid,auto,async,noatime,nodiratime,discard,data=writeback,commit=0,nouser_xattr,barrier=1,journal_checksum,mode=700,umask=077,errors=remount-ro,iocharset=utf-8 0 # automatic cryptsetup is recommended (cryptsetup-option --key-file): Only access over the root-partion with the stored key-file will be possible. Acess-rights for the key-file: chown root:root path_to_key_file/key.asc && chmod 400 /patch_to_key_file/key.asc
# exec or noexec
 /dev/cdrom /media/cdrom auto umask=0,users,noauto,iocharset=utf8,ro,noexec 0 0 /dev/cdrom /media/cdrom auto umask=0,users,noauto,iocharset=utf8,ro,noexec 0 0
 proc /sid-root/proc proc notail,noatime,nodiratime,noexec,rw,nodev,nosuid,nouser,data=writeback,mode=555,hidepid=2,gid=user,surfgroup,torgroup 0 0 # mouseclick-fast proc /sid-root/proc proc notail,noatime,nodiratime,noexec,rw,nodev,nosuid,nouser,data=writeback,mode=555,hidepid=2,gid=user,surfgroup,torgroup 0 0 # mouseclick-fast
none /proc proc notail,noatime,nodiratime,noexec,rw,nodev,nosuid,nouser,data=writeback,mode=555 0 0
 # usbfs /proc/bus/usb usbfs rw,relatime,devgid=43,devmode=664,noexec 0 0 # if not already mounted during system boot; notice: MCC-Partiton-Manager and so on will miss /proc/bus/usb # usbfs /proc/bus/usb usbfs rw,relatime,devgid=43,devmode=664,noexec 0 0 # if not already mounted during system boot; notice: MCC-Partiton-Manager and so on will miss /proc/bus/usb
 sysfs /sid-root/sys sysfs notail,noatime,nosuid,nodiratime,rw,noexec,nouser,nosuid,nodev,data=writeback,mode=555 0 0 sysfs /sid-root/sys sysfs notail,noatime,nosuid,nodiratime,rw,noexec,nouser,nosuid,nodev,data=writeback,mode=555 0 0
 Temporary, tmp ins RAM:: Temporary, tmp ins RAM::
 tmpfs /tmp tmpfs noatime,nodiratime,noexec,ro,nodev,nouser,nosuid,mode=1777,size=8M 0 0 # original tmp, that was made hidden by firejail using option "private-tmp" within any /etc/firejail/config-files tmpfs /tmp tmpfs noatime,nodiratime,noexec,ro,nodev,nouser,nosuid,mode=1777,size=8M 0 0 # original tmp, that was made hidden by firejail using option "private-tmp" within any /etc/firejail/config-files
 shm /tmp tmpfs noatime,nodiratime,noexec,rw,nodev,nosuid,nouser,mode=1777 0 0 shm /tmp tmpfs noatime,nodiratime,noexec,rw,nodev,nosuid,nouser,mode=1777 0 0
 tmpfs /tmp2 tmpfs noatime,nodiratime,noexec,ro,nodev,nouser,nosuid,mode=1777,size=128M 0 0 # one more tmp for the down- and uploads tmpfs /tmp2 tmpfs noatime,nodiratime,noexec,ro,nodev,nouser,nosuid,mode=1777,size=128M 0 0 # one more tmp for the down- and uploads
 shm /tmp2 tmpfs noatime,nodiratime,noexec,rw,nodev,nosuid,nouser,mode=1777 0 0 shm /tmp2 tmpfs noatime,nodiratime,noexec,rw,nodev,nosuid,nouser,mode=1777 0 0
#SWAP:
 /dev/mapper/cryptswap swap swap defaults,discard,rw,data=writeback 0 0 /dev/mapper/cryptswap swap swap defaults,discard,rw,data=writeback 0 0
 none /dev/pts devpts mode=620,gid=5,rw none /dev/pts devpts mode=620,gid=5,rw
 UUID=... /var/local ext4 rw,noatime,nodiratime,nosuid,aync,nodev,noexec,user_xattr,acl,barrier=1,data=writeback,mode=755,umask=077,commit=0,iocharset=utf8 # needed in small size of around 1 GB in order to mount the root-partition read-only UUID=... /var/local ext4 rw,noatime,nodiratime,nosuid,aync,nodev,noexec,user_xattr,acl,barrier=1,data=writeback,mode=755,umask=077,commit=0,iocharset=utf8 # needed in small size of around 1 GB in order to mount the root-partition read-only
 binfmt /proc/sys/fs/binfmt_misc binfmt_misc rw,noatime 0 0 # binfmt_misc is a capability of the Linux kernel which allows arbitrary executable file formats to be recognized and passed to certain user space applications, such as s emulators and virtual machines. The executable formats are registered through a special purpose file system interface (similar to /proc). Debian-based distributions provide the functionality through an extra binfmt-support package.[1]...see https://en.wikipedia.org/wiki/Binfmt_misc binfmt /proc/sys/fs/binfmt_misc binfmt_misc rw,noatime 0 0 # binfmt_misc is a capability of the Linux kernel which allows arbitrary executable file formats to be recognized and passed to certain user space applications, such as s emulators and virtual machines. The executable formats are registered through a special purpose file system interface (similar to /proc). Debian-based distributions provide the functionality through an extra binfmt-support package.[1]...see https://en.wikipedia.org/wiki/Binfmt_misc
securityfs /sys/kernel/security /mnt/any_mountpoint securityfs rw,noatime 0 0 # lsm, secure fs for kernel-security-modules ... or mount it within /etc/rc.local by "mount -t securityfs -o rw,noatime /sys/kernel/security /mnt2"
# and /etc/fstab of our USB-stick:
/dev/sda1 / unionfs 0 1
/dev/mapper/usbstick1 /media/mnt_usb1 vfat rw,nosuid,nodev,uhelper=hal,users,noexec,uid=10001,utf8,shortname=mixed,flush,umask=077 0 1 # An entry in /etc/crypttab only instead of both files fstab and crypttab is sufficient. LUKS-encrypted USB-memory-stick with UUID (you can find out by mount -l ) and name usbstick1 within /etc/crypttab. Also think about mounting this encrypted USB-stick without having to enterthe password for encryption manually each system boot by creating a key-file or using the already present one from cryptohome, adding this key-file to /etc/crypttab and assocating it with the USB-stick by the command "cryptsetup luksAddKey /dev/sdc1 /path_to_keyfile/keyfile". Notice, that it might not be necessary to add this entry for an USB-memory stick in /etc/fstab here. Do this only in the case of problems with their hotplug!
 /etc/fstab: Set the UUIDs instead of the named device-partitions
Find out the UUIDs with the console-command "blkid" (this is not possible for the internal kernel-partitions). /etc/fstab: Set the UUIDs instead of the named device-partitions
Find out the UUIDs with the console-command "blkid" (this is not possible for the internal kernel-partitions).
 AHCI-Mode: BIOS-setup for SSD AHCI-Mode: BIOS-setup for SSD
Start the Bios- / Firmware-setup and look, if the AHCI-Modus (Advanced Host Controller Interface) for the SATA-adapter is active. Alternatively "RAID" is possible too.
You can almost find the option in the menu under "Advanced -> Integrated Peripherals", "SATA Configuration" or "PCH Storage Configuration". Elder mainboard-platines do also have the option "IDE", in order to increase the throughput of the harddrives, if not chosen. If there is provided only "IDE", you must resign from the SATA-optimization.
On a side for overview ("System Status" or similar side) you almost find infomation about the SATA-Port the harddrives get connected. New motherboards only do have SATA-ports with fast 6 GBit/s (SATA III) and any port can be used. SATA II as much as SATA I fullfill our criteria to make all running mouseclick-fast.
 And in /etc/rc.local (started by adding "sh /etc/rc.local" from any activated bootscript of /etc/init.d/, followed by a system-restart) for optimized SSD (in our example on the first S-ATA-port named sda) we choose the following parameters after a check with "hdparm -I /dev/sda": and "man hdparm":
And in /etc/rc.local (started by adding "sh /etc/rc.local" from any activated bootscript of /etc/init.d/, followed by a system-restart) for optimized SSD (in our example on the first S-ATA-port named sda) we choose the following parameters after a check with "hdparm -I /dev/sda": and "man hdparm":
hdparm -W1a0A0 /dev/sda (also try other optimizing parameters of hdparm)
echo deadline > /sys/block/sda/queue/scheduler
echo 500 > /proc/sys/vm/dirty_writeback_centisecs
echo 20 > /proc/sys/vm/dirty_ratio
echo 5 > /proc/sys/vm/dirty_background_ratio
touch /var/lock/subsys/local
SSD: commit=0: mouseclick-fast
Option defaults consists of the for security significant async,nouser,rw,suid,dev,exec,auto.
man mount: "All I/O to the filesystem should be done synchronously. In case of media with limited number of write cycles (e.g. some flash drives) "sync" may cause life-cycle shortening." In other words, for SSD prefer option async!
The namely security advised option "W0" instead of elected W1 deactivates the write-cache of the SSD, what protects data even more in the case of system hangons and breakdowns. More parameters of hdparm are explained by "hdparm -h" and manpages, see "man hdparm".Notice, that for more performcance "W1" for write-cacheing is generally recommended.
The pair of number from above like "0 1" stands for dump equal to no and fsck equal to yes, while the number itself stands for 0 none (no check), 1 recommended for the root-partition, 2 for all other partitionss and 3 for all less important partitions. With these setting, named filesystem can not be damaged anymore, otherwise, if ever thinkable, use manually "reiserfsck --no-tree device_file" to do its best for reiserfs.
umask: generally sets the access-rights as a subtrahend: Set umask 022 standing for less or equal 755 resp. umask 077 for less or equal 700 for the root- and home-partition in /etc/fstab and also in: /etc/profile, /etc/login.defs, /home/user/.bash_profile, /home/surfuser/.bash_profile, /root/.bash_profile, ROOT_UMASK=077 in /etc/security/msec/level.secure and USER_UMASK=077; acl: enable POSIX Access Control Lists.
Keep everything as SSD-friendly and mouseclick-fast you can, link the browser-cbache of Konqueror to the temporary directory /tmp being part of shm (shared memory, RAM) from fstab above:
 rm -df /home/surfuser/.kde4/cache-localhos and ln -sf /tmp /home/surfuser/.kde4/cache-localhost, /home/surfuser/tmp, /home/user/.kde4/cache-localhost, /home/user/.kde4/socket-localhost, /home/user/.kde4/tmp, /home/user/.kde4/tmp-localhost and rm -df /home/surfuser/.kde4/cache-localhos and ln -sf /tmp /home/surfuser/.kde4/cache-localhost, /home/surfuser/tmp, /home/user/.kde4/cache-localhost, /home/user/.kde4/socket-localhost, /home/user/.kde4/tmp, /home/user/.kde4/tmp-localhost and
ln -sf /tmp/kde-user /home/user/.kde4/tmp-localhost.localdomain, ln -sf /tmp/kde-surfuser/.kde4/tmp-localhost.localdomain . In the long run this spares plenty of cleaning. Do not link cache-localhost.localdomain and socket-localhost.localdomain, as this might cause some problems starting KDE.
 ln -sf /tmp /home/alluser/.cache2 && rm -dfr /home/alluser/.cache &&rename /home/alluser/.cache2 /home/alluser/.cache /home/alluser/.cache2 ln -sf /tmp /home/alluser/.cache2 && rm -dfr /home/alluser/.cache &&rename /home/alluser/.cache2 /home/alluser/.cache /home/alluser/.cache2
bleachbit (el6, cleaner): This program can cause serious hard damage!
We go on for SSD: Option discard is not functioning each kernel and SSD. commit sets the interval or frequency for write-operations, what is 5s per default. It is not recommended to change this value. barrier is one more feature of ext4 and ext3 caring for writing (coherent) data right in front of a barrier before such coherent data are writtten behind it. barriers=1 effects more securirty, while barriers=0 contributes to more perfmormance. ro for read-only still should not be set for the root-partition. This would have caused "skipping journal replay". data=writeback means "Data ordering (data=ordered) is not preserved, data may be written into the main file system after its metadata has been committed to the journal.", options see http://www.mjmwired.net/kernel/Documentation/filesystems/ext4.txt#169 . Most options are accepted by ext3 too, but not reiserfs. Notice, that reiserfs does not accept all of the listed options like barrier, errors and discard, inspite of this option nolog is accepted. Test options by "mount -o options devicefile mountpoint", before they are set in /etc/fstab!
rpm-description cmospwd (el6): "CmosPwd decrypts password stored in cmos used to access BIOS SETUP. Works with the following BIOSes * ACER/IBM BIOS * AMI BIOS * AMI WinBIOS 2.5 * Award 4.5x/4.6x/6.0 * Compaq (1992) * Compaq (New version) * IBM (PS/2, Activa, Thinkpad) * Packard Bell * Phoenix 1.00.09.AC0 (1994), a486 1.03, 1.04, 1.10 A03, 4.05 rev 1.02.943, 4.06 rev 1.13.1107 * Phoenix 4 release 6 (User) * Gateway Solo - Phoenix 4.0 release 6 * Toshiba * Zenith AMI With CmosPwd, you can also backup, restore and erase/kill cmos."
So at first, generally the best thing one can do, is to abrogate the complete internet-access (what we do not suppose...) and to get a spare-parted backup-SSD or harddrive for the case of all the on mdv2010 remaining unsolved dependencies of packages your are going to install, that means in order to
Browser-Cache into RAM
about:config ->, to add a new entry type string
with the value /shm
After a newstart, firefox is cached into RAM. Go quit the same way for other browsers, source: http://wiki.siduction.de/index.php?title=Solid_State_Disks_(SSDs)_unter_Linux_optimal_nutzen&printable=yes. For Konqueror just link directory /home/username/.kde4/localhost-cache to /shm.
Convince yourself to get gnutls (el7) with libtasn1 (el7) installed. Otherwise gnutls might not work correctly for firefox.
| backup partitionwise 1:1 by command dd (details see below) |
 Flashrom, Coreboot Flashrom, Coreboot
Have a second BIOS-chip. Save the actual BIOS-firmware of the used BIOS-chip into a bin(ary) resp. rom-file. This can be done by an utility from the disc with drivers for the mainboard, out of the internet or by the UNIX-(Linux)-program called flashrom. flashrom is a utility for detecting, reading, writing, verifying and erasing flash chips. It´s often used to flash BIOS/EFI/coreboot/firmware images in-system using a supported mainboard, but it also supports flashing of network cards (NICs), SATA controller cards and other external devices, which can program flash chips. On malfunction especially after the powering on of the computer, you can flush the BIOS through the backup up right from the desktop, if not, you have to exchange the chip or the net-adapter, same for the RAM, that can be checked by progs of UNIX (Linux) like memtest. For the protection against wiretapping bedbugs care for "chassis intrusion detection", for the usage of as few USB-cards as possible, if the BIOS is resetted and if there are any hearable feedbacks from hardware inspite of FCC. Compare constructions and notice any specifications direct from the platines like the manufacturer-types or -ID . With some luck, a radio tunes their frequencies.
"Welcome to coreboot!
coreboot is an Open Source project aimed at replacing the proprietary BIOS (firmware) found in most computers. coreboot performs a little bit of hardware initialization and then executes additional boot logic, called a payload.
With the separation of hardware initialization and later boot logic, coreboot can scale from specialized applications that run directly from firmware, run operating systems in flash, load custom bootloaders, or implement firmware standards, like PC BIOS services or UEFI. This allows for systems to only include the features necessary in the target application, reducing the amount of code and flash space required.
coreboot currently supports over 230 different mainboards. Check the Support page to see if your system is supported."
https://www.coreboot.org/Welcome_to_coreboot
https://www.coreboot.org/Supported_Motherboards
 Password-protection
Password-protection
If Linfw3 is used, so that root and all other user except a special surfuser get blocked, and if all other methods introduced here on this webside are performed, no password hacking and cracking is ever possible anymore, even not after the password got known by other ones and independent from its name or constitution or who and whatever, neither from the outside (net), inside (software) nor direct at office or home or anywhere. Keys for the LUKS-encrypted partitions must be stored on a portable USB-memory-stick, better memory-/chip-card or fingerprint-scanner
Password-protection on our introduced exemplary system:
BIOS-password
Grub-md5-Password for all bootable partitions and memory-check within /boot/grub/menu.lst
Special (own) inportable password for always LUKS-encrypted partitions on the base of FSE (Full System Encryption) with keys (passwords) for the dracut-enbound root-Partition on a LUKS-password encrypted USB-memory-stick, rest (see
exemplary listed /etc/fstab) as sha2-key-file for user:group root:root and chmod 400 within any directory of the root-partition
Secured LUKS-root-partition with manual password-login onto a separate storage media for the cass of data loss from USB-memory-stick etc.
ACL-locked su-login for "surfuser"
Keys (passwords) for the additional encryption of e-mail and single directories and files with gnupg (kgpg) within the for "surfuser" by ACL inaccessible made directory .gnupg
desktop-manager: user-password for kdm and other desktop manager (or simplefying automized login free from password-entry)
Passwörds for LUKS-encrypted USB-memory-sticks
Password-manager for the twice password-encrypted access storage for all other passwords: revelation (el6, el7, rosa2014.1, rosa2016.1, fc 2X)
/etc/shadow (password-)file: chown root:root and chmod 400
 inacccessible shell-bash-login in /etc/passwd and eventually usage of sandbox firejail with option "shell none" inacccessible shell-bash-login in /etc/passwd and eventually usage of sandbox firejail with option "shell none"
Password protection, Focus, 11.04.2015
Snowden meant, hacker could hack a primitive password within one second. But the whistleblower gives tipps, how to keep passwords safe, so that they can not be hacked: by passphrases. Most passwords are simple variants like "12345678", "password" or the forename of the user. Edward Snowden thinks, passwords with the length of eight characters still do remain very insecure. They could be hacked by supercomputers in less than one second. Passphrases are passwords consisting of more than one word. Long, one time appearing sentences like
are easy to remember and combine different characters. They could not be decrypted by hacking programs.
A similar uncrackable method for password generation is described by PCWelt.de on http://www.pcwelt.de/ratgeber/So-erstellen-und-merken-Sie-sich-wirklich-sichere-Passwoerter-ohne-Zusatz-Tools-9940466.html .
Expert explains: The perfect password would be cracked by hackers in 227 millionen years, FOCUS Online, 09.05.2018
https://www.focus.de/digital/videos/geheimnis-liegt-in-drei-worten-experte-erklaert-hacker-wuerden-227-millionen-jahre-fuer-dieses-passwort-brauchen_id_7744168.html
Passwords are stored in the, as we hope, only root-accessible /etc/shadow for Linux. This file is handled over /etc/passwd listing usernames, belonging groups, "x" as a replacement for the password to read-in and so on.
All sensible data should never be stored on the onboard resp. plugged-in storage-media, SSD and harddrives and only onto those unplugged ones containing the backups and onto well-encrypted USB-memory-sticks!
More Internet Security
pam_shield (el6): pam_shield is a PAM module that uses iptables to lock out script kiddies that probe your computer for open logins and/or easy guessable passwords. pam_shield is meant as an aid to protect public computers on the open internet. An IP can also be entered manually by the command shield-trigger add 122.22.1.2 into the belonging database, same through "del" for deletion..pam_shield should get configured in /etc/security/shield.conf.
fail2ban (el6): Fail2ban scans log files like /var/log/pwdfail or /var/log/apache/error_log and bans IP that makes too many password failures. It updates firewall rules to reject the IP address.
DenyHosts is a Python script that analyzes the sshd server log messages to determine which hosts are attempting to hack into your system. It also determines what user accounts are being targeted. It keeps track of the frequency of attempts from each host and, upon discovering a repeated attack host, updates the /etc/hosts.deny file to prevent future break-in attempts from that host. Email reports can be sent to a system admin.
If you beware this principle, the computer generally provides the promised security for you.
Of course we tested and possess MS Windows. As we all know, it is not sufficient just to install an operating system and security-software to call the computer-system really secure, while finding out, that effective solutions may cost time! Installation should be done by users with the rights of the system-administrator only. During installation the signatur helps to be aware of the origin of software. Before the installation itself, packet-manager check out dublications and dependencies. If a packet is ever missing, packet-manager like urpmi can download and install all needed packages from different sources and the internet. to solve them. After that, version-control by CVS (Version Controlling Systems) can also do their best. The packet-database seems to be similar to the MS-Win-registry, but it is not such complex. If the packet-database should ever be damaged, it can be repaired in a simple way by the commands rm -f /var/lib/rpm/__* and rpm --rebuilddb. If this should not help, start the MCC packet-manager rpmdrake, in order to install any packet. rpmdrake is almost able to solve such conflicts. Notice, that MCC´s downloaded files are at least temporary in directory /var/cache/urpmi/rpms. Not all of the infinite amount of packet-dependencies are solved, even not in mdv2010!
 How to Rebuild Corrupted RPM Database in CentOS, Aaron KiliJune 1, 2018 Categories CentOS 3 Comments How to Rebuild Corrupted RPM Database in CentOS, Aaron KiliJune 1, 2018 Categories CentOS 3 Comments
The RPM database is made up of files under the /var/lib/rpm/ directory in CentOS and other enterprise Linux distributions such as RHEL, openSUSE, Oracle Linux and more.
If the RPM database is corrupted, RPM will not work correctly, thus updates cannot be applied to your system, you encounter errors while updating packages on your system via YUM package manager. The worst case scenario is being unable to run any rpm and yum commands successfully.
There are a number of factors that can lead to the RPM database corruption, such as incomplete previous transactions, installation of certain third-party software, removing specific packages, and many others.
In this article, we will show how to rebuild a corrupted RPM database; this way you can recover from an RPM database corruption in CentOS. This requires root user privileges, otherwise, use the sudo command to gain those privileges.
First start by backing up your current RPM database before proceeding (you might need it in the future), using the following commands.
# mkdir /backups/
# tar -zcvf /backups/rpmdb-$(date +"%d%m%Y").tar.gz /var/lib/rpm
Next, verify the integrity of the master package metadata file /var/lib/rpm/Packages; this is the file that needs rebuilding, but first remove /var/lib/rpm/__db* files to prevent stale locks using following commands.
# rm -f /var/lib/rpm/__db*
# /usr/lib/rpm/rpmdb_verify /var/lib/rpm/Packages
In case the above operation fails, meaning you still encounter errors, then you should dump and load a new database. Also verify the integrity of the freshly loaded Packages file as follows.
# cd /var/lib/rpm/
# mv Packages Packages.back
# /usr/lib/rpm/rpmdb_dump Packages.back | /usr/lib/rpm/rpmdb_load Packages
# /usr/lib/rpm/rpmdb_verify Packages
Now to check the database headers, query all installed packages using the -q and -a flags, and try to carefully observe any error(s) sent to the stderror.
# rpm -qa >/dev/null #output is discarded to enable printing of errors only
Last but not least, rebuild the RPM database using the following command, the -vv option allows for displaying lots of debugging information.
# rpm -vv --rebuilddb
Now to check the database headers, query all installed packages using the -q and -a flags, and try to carefully observe any error(s) sent to the stderror.
# rpm -qa >/dev/null #output is discarded to enable printing of errors only
https://www.tecmint.com/rebuild-corrupted-rpm-database-in-centos/
Read Also: 20 Practical Examples of RPM Command in Linux: https://www.tecmint.com/20-practical-examples-of-rpm-commands-in-linux/
Indeed: Our experience in mdv2010 tells us, that the only weak point grounds still in the overwhelming amount of existing packet-dependencies during an intensive installation of packages online (with a high amount of packages) by rpmdrake from MCC (drakconf) quit "at once" of a complexity much higher than from installation-DVD. Therefore we recommend not to download too many packets, not more than 50 "at once" and to have a look into the directory /var/lib/urmpi/rpms, where the not installed packages are still stored, if MCC is set to "do not empty the packet-cache after download" before. Then error-messages of the reinstallation by packet-manager like rpm, urpmi and yum almost tell what to do next - if there is inspite of checks of rpmdrake within the packet still any rpm, especially library-rpm, missing or if one rpm conflicts with another one to delete it before reinstallation is possible.
We repeat: agesschau, 07.31.2014: Actually scientific experts found out, that sensible data can be read out through microcontrollers (processors) from USB-sticks, see the report from our linkside under the point links! Therefore a new USB-standard is devoloped. By this, all data of computers can be read out, even passwords and email-contents as much as devices be steered like webcams. The operating sytem does not notice all of this, as it believes in key-strokes and not software attacks.
mouseclick-fast
Mouseclick-fast: We almost have just the following services activated through MCC: NetworkManager, acpid, alsa, cups, dnsmasq, gpm, ip6tables, iptables, jexec, linfw3, lm_sensors, partmon, postfix, sound, sysstat, udev-post, uuidd, wine and sometimes ntpd and httpd.
That´s all. So service network got deactivated too by command "chkconfig --level 2345 network off".
Increase the surf-speed with the browser, press STRG and ESC, choose the process for the browser by right clicking onto him and pull the appearing shift register for the process-priority at least one quarter length right. Alternatively use the terminal-commands nice and renice for a priority between -20 and 19 incl., default is 0 (source. Focus Onine, 07.11.2015);
Gooken recommends extrem high priorities for Dolphin, Kmail, Kontact, Kopete, Office, some OpenGL- and SDL-games (if useful) and Konqueror and/or any other browser,
Brake block and espionage: "root,-1", ( dangerous, speed lowering ) (system-)process named unknown (for login under uid:0) of owner "root,-1" with changing PID and unknown dimesioned CPU-enburdening "kept secret"
In advance, this might really help: setfacl -m u:root:- /usr/libexec/gam_server
. Also exchange gamin (mdv2010) with gamin (pclos2017).
http://stackoverflow.com/questions/13655110/how-to-kill-a-process-whose-pid-keeps-changing:
Such a process is called a "comet" by systems administrators.
The process group ID (PGID) doesn´t change on fork, so you can kill it (or SIGSTOP it) by sending a signal to the process group (you pass a negated PGID instead of a PID to kill).
answered Dec 1 ´12 at 1:18
caf
161k18208340
What if it calls setpgid/setsid each time too? :-) - R.. Dec 1 ´12 at 2:28
The only reason, I can see, why you wouldn´t see it is, that the forked child has not been created yet but the parent has progressed far enough in it´s death that it is no longer listed.
Unfortunately I don´t think it´s possible to kill this kind of process without some guessing. To do so would require knowing the next pid in advance. You can guess the next pid but not be certain that no other pid gets it assigned.
We generally want to get rid of such processes: Wait for our new experiences at this place! Mouseclick-fast and secure: the ultimative speed boost beneath SSD-technology from see data-sheed: At first, update the gam_server (gamin (fc25) and gamin-server (OpenSuSE13.2) with gam_server into /usr/libexec) or remove it (like in OpenSuSE, where gamin is not offered), that might has to do with it and never connect to the ISP (Internet Service Provider) using the NetworkManager (el6) together with networkmanager-applet (mdv2010.2), but through "ifup eth0" by surfuser (but without naming surfgroup) instead, maybe out of the K-Menu, in the case of Konqueror for example set:
| renice -n 18 ´pidof konqueror´ |
that means for surfuser joining surfgroup in order to start konqueror after the login to surfuser:
| "knemo && sg surfgroup konqueror && renice -n 18 ´pidof konqueror´ && kded4" |
rpm-description: "Run command in restricted environment. Chrootuid makes it easy to run a network service at low privilege level and with restricted file system access. At Eindhoven University, they use this program to run the gopher and www (world-wide web) network daemons in a minimal environment: The daemons have access only to their own directory tree, and run under a low-privileged userid. The arrangement greatly reduces the impact of possible loopholes in daemon software."
 Or additionally on the base of the suid-sandboxfirejail (ram80: 0.9.44.8-1, rosa2014.1, rosa2016.1, pclos2017 or https://sourceforge.net/projects/firejail/) for all programs online and untrusted (following the includes, that might be some, we chose firejail for quit all), one more program for mdv2010.2 or el6 from rosa2014.1, that you also can download from here:
Or additionally on the base of the suid-sandboxfirejail (ram80: 0.9.44.8-1, rosa2014.1, rosa2016.1, pclos2017 or https://sourceforge.net/projects/firejail/) for all programs online and untrusted (following the includes, that might be some, we chose firejail for quit all), one more program for mdv2010.2 or el6 from rosa2014.1, that you also can download from here:
firejail-0.9.52-1pclos2017.x86_64.rpm (from December 2017, vendor:none, pbone.net)
or download firejail pclos2017 preconfigured by us for firefox, Konqueror and kmail and so on from our update-section preconfigured by us for firejail-0.9.52-1.
| "knemo && sg surfgroup "firejail --private=/home/surfuser konqueror" && renice -n 18 ´pidof konqueror´ && kded4" |
or, enhanced with option --profile:
| "knemo && sg surfgroup "unshare firejail --nice=18 --profile=/etc/firejail/konqueror.profile --private=/home/surfuser konqueror" && kded4" |
This call seems to get quit long, so for a start with priority 18 from -20 up to 20 by a single (or double) mouseclick do not forget to add an this command into the belonging entry for konqueror within the k-menu, on the desktop or in the quick-starter of the taskline. For shell-scripts this can be done by "xterm -e /path_to/shellscript.sh" resp. "konsole -e /path_to/shellscript.sh"
Linux namespaces sandbox program firejail, https://sourceforge.net/projects/firejail/
"Firejail is a SUID program that reduces the risk of security breaches by restricting the running environment of untrusted applications using Linux namespaces and seccomp-bpf. It allows a process and all its descendants to have their own private view of the globally shared kernel resources, such as the network stack, process table, mount table.
Written in C with virtually no dependencies, the software runs on any Linux computer with a 3.x (and 5.4.110 with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) and glibc (el8, pclos, mga6) resp. 2.6.39.4-5.1, com., Gooken) kernel version or newer. The sandbox is lightweight, the overhead is low. There are no complicated configuration files to edit, no socket connections open, no daemons running in the background. All security features are implemented directly in Linux kernel and available on any Linux computer.
Firejail can sandbox any type of processes: servers, graphical applications, and even user login sessions. The software includes security profiles for a large number of Linux programs: Mozilla Firefox, Chromium, VLC, Transmission etc."
 Firejail is a SUID sandbox program, that reduces the risk of security breaches by restricting the running environment of untrusted applications using Linux namespaces.
Firejail is a SUID sandbox program, that reduces the risk of security breaches by restricting the running environment of untrusted applications using Linux namespaces.
firejail - version 0.9.48
Options:
-- - signal the end of options and disables further option processing.
--allow-debuggers - allow tools such as strace and gdb inside the sandbox.
 --allow-private-blacklist - allow blacklisting files in private --allow-private-blacklist - allow blacklisting files in private
home directories.
--allusers - all user home directories are visible inside the sandbox.
--apparmor - enable AppArmor confinement.
--appimage - sandbox an AppImage application.
--audit[=test-program] - audit the sandbox.
--bandwidth=name|pid - set bandwidth limits.
--bind=dirname1,dirname2 - mount-bind dirname1 on top of dirname2.
--bind=filename1,filename2 - mount-bind filename1 on top of filename2.
--blacklist=filename - blacklist directory or file.
-c - execute command and exit.
--caps - enable default Linux capabilities filter.
 --caps.drop=all - drop all capabilities. --caps.drop=all - drop all capabilities.
--caps.drop=capability,capability - blacklist capabilities filter.
--caps.keep=capability,capability - whitelist capabilities filter.
--caps.print=name|pid - print the caps filter.
--cgroup=tasks-file - place the sandbox in the specified control group.
--chroot=dirname - chroot into directory.
--cpu=cpu-number,cpu-number - set cpu affinity.
--cpu.print=name|pid - print the cpus in use.
--csh - use /bin/csh as default shell.
--debug - print sandbox debug messages.
--debug-blacklists - debug blacklisting.
--debug-caps - print all recognized capabilities.
--debug-check-filename - debug filename checking.
--debug-errnos - print all recognized error numbers.
--debug-protocols - print all recognized protocols.
--debug-syscalls - print all recognized system calls.
--debug-whitelists - debug whitelisting.
--defaultgw=address - configure default gateway.
 --dns=address - set DNS server. --dns=address - set DNS server.
--dns.print=name|pid - print DNS configuration.
--env=name=value - set environment variable.
--force - attempt to start a new sandbox inside the existing sandbox.
--fs.print=name|pid - print the filesystem log.
--get=name|pid filename - get a file from sandbox container.
--help, -? - this help screen.
--hostname=name - set sandbox hostname.
--hosts-file=file - use file as /etc/hosts.
--ignore=command - ignore command in profile files.
--interface=name - move interface in sandbox.
 --ip=address - set interface IP address. --ip=address - set interface IP address.
--ip=none - no IP address and no default gateway are configured.
--ip6=address - set interface IPv6 address.
--iprange=address,address - configure an IP address in this range.
 --ipc-namespace - enable a new IPC namespace. --ipc-namespace - enable a new IPC namespace.
--join=name|pid - join the sandbox.
--join-filesystem=name|pid - join the mount namespace.
--join-network=name|pid - join the network namespace.
--join-or-start=name|pid - join the sandbox or start a new one.
--list - list all sandboxes.
--ls=name|pid dir_or_filename - list files in sandbox container.
--mac=xx:xx:xx:xx:xx:xx - set interface MAC address.
--machine-id - preserve /etc/machine-id
--mtu=number - set interface MTU.
--name=name - set sandbox name.
--net=bridgename - enable network namespaces and connect to this bridge.
 --net=ethernet_interface - enable network namespaces and connect to this Ethernet interface. --net=ethernet_interface - enable network namespaces and connect to this Ethernet interface.
--net=none - enable a new, unconnected network namespace.
 --netfilter[=filename] - enable the default client network filter. --netfilter[=filename] - enable the default client network filter.
--netfilter6=filename - enable the IPv6 network filter.
 --netns=name - Run the program in a named, persistent network namespace. --netns=name - Run the program in a named, persistent network namespace.
--netstats - monitor network statistics.
 --nice=value - set nice value. --nice=value - set nice value.
 --no3d - disable 3D hardware acceleration. --no3d - disable 3D hardware acceleration.
 --noblacklist=filename - disable blacklist for file or directory . --noblacklist=filename - disable blacklist for file or directory .
 --noexec=filename - remount the file or directory noexec nosuid and nodev. --noexec=filename - remount the file or directory noexec nosuid and nodev.
 --nogroups - disable supplementary groups. --nogroups - disable supplementary groups.
 --nonewprivs - sets the NO_NEW_PRIVS prctl. --nonewprivs - sets the NO_NEW_PRIVS prctl.
--noprofile - do not use a security profile.
 --nosound - disable sound system. --nosound - disable sound system.
 --novideo - disable video devices. --novideo - disable video devices.
 --nowhitelist=filename - disable whitelist for file or directory . --nowhitelist=filename - disable whitelist for file or directory .
--output=logfile - stdout logging and log rotation.
--overlay - mount a filesystem overlay on top of the current filesystem.
--overlay-named=name - mount a filesystem overlay on top of the current filesystem, and store it in name directory.
--overlay-tmpfs - mount a temporary filesystem overlay on top of the current filesystem.
--overlay-clean - clean all overlays stored in $HOME/.firejail directory.
 --private - temporary home directory. --private - temporary home directory.
 --private=directory - use directory as user home. --private=directory - use directory as user home.
 --private-home=file,directory - build a new user home in a temporary --private-home=file,directory - build a new user home in a temporary
filesystem, and copy the files and directories in the list in the new home.
 --private-bin=file,file - build a new /bin in a temporary filesystem and copy the programs in the list. --private-bin=file,file - build a new /bin in a temporary filesystem and copy the programs in the list.
 --private-dev - create a new /dev directory. Only dri, null, full, zero,tty, pst, ptms, random, snd, urandom, log and shm devices are available. --private-dev - create a new /dev directory. Only dri, null, full, zero,tty, pst, ptms, random, snd, urandom, log and shm devices are available.
 --private-etc=file,directory - build a new /etc in a temporary filesystem, and copy the files and directories in the list. --private-etc=file,directory - build a new /etc in a temporary filesystem, and copy the files and directories in the list.
 --private-tmp - mount a tmpfs on top of /tmp directory. --private-tmp - mount a tmpfs on top of /tmp directory.
 --private-opt=file,directory - build a new /opt in a temporary filesystem. --private-opt=file,directory - build a new /opt in a temporary filesystem.
--profile=filename - use a custom profile.
--profile-path=directory - use this directory to look for profile files.
--protocol=protocol,protocol,protocol - enable protocol filter.
--protocol.print=name|pid - print the protocol filter.
--put=name|pid src-filename dest-filename - put a file in sandbox container.
--quiet - turn off Firejail´s output.
 --read-only=filename - set directory or file read-only.. --read-only=filename - set directory or file read-only..
--read-write=filename - set directory or file read-write..
--rlimit-fsize=number - set the maximum file size that can be created by a process.
 --rlimit-nofile=number - set the maximum number of files that can be opened by a process. --rlimit-nofile=number - set the maximum number of files that can be opened by a process.
 --rlimit-nproc=number - set the maximum number of processes that can be created for the real user ID of the calling process. --rlimit-nproc=number - set the maximum number of processes that can be created for the real user ID of the calling process.
--rlimit-sigpending=number - set the maximum number of pending signals for a process.
 --rmenv=name - remove environment variable in the new sandbox. --rmenv=name - remove environment variable in the new sandbox.
--scan - ARP-scan all the networks from inside a network namespace.
 --seccomp - enable seccomp filter and apply the default blacklist. --seccomp - enable seccomp filter and apply the default blacklist.
Enable seccomp filter and blacklist the syscalls in the default list. The default list is as follows: mount, umount2, ptrace, kexec_load, kexec_file_load, open_by_handle_at, init_module, finit_module, delete_module, iopl, ioperm, swapon, swapoff, syslog, process_vm_readv, process_vm_writev, sysfs,_sysctl, adjtimex, clock_adjtime, lookup_dcookie, perf_event_open, fanotify_init, kcmp, add_key, request_key, keyctl, uselib, acct, modify_ldt, pivot_root, io_setup, io_destroy, io_getevents, io_submit, io_cancel, remap_file_pages, mbind, get_mempolicy, set_mempolicy, migrate_pages, move_pages, vmsplice, perf_event_open and chroot.
 --seccomp=syscall,syscall,syscall --seccomp=syscall,syscall,syscall
Enable seccomp filter, blacklist the default list and the syscalls specified by the command.
Example: firejail --seccomp=utime,utimensat,utimes firefox
--seccomp.drop=syscall,syscall,syscall
Enable seccomp filter, and blacklist the syscalls specified by the command.
Example: firejail --seccomp.drop=utime,utimensat,utimes
--seccomp.keep=syscall,syscall,syscall - enable seccomp filter, and whitelist the syscalls specified by the command.
--seccomp.<errno>=syscall,syscall,syscall - enable seccomp filter, and return errno for the syscalls specified by the command.
--seccomp.print=name|pid - print the seccomp filter for the sandbox identified by name or PID.
 --shell=none- run the program directly without a user shell. --shell=none- run the program directly without a user shell.
--shell=program - set default user shell.
--shutdown=name|pid - shutdown the sandbox identified by name or PID.
--tmpfs=dirname - mount a tmpfs filesystem on directory dirname.
--top - monitor the most CPU-intensive sandboxes.
--trace - trace open, access and connect system calls.
--tracelog - add a syslog message for every access to files or directories blacklisted by the security profile.
--tree - print a tree of all sandboxed processes.
--version - print program version and exit.
--veth-name=name - use this name for the interface connected to the bridge.
--whitelist=filename - whitelist directory or file.
--writable-etc - /etc directory is mounted read-write.
--writable-var - /var directory is mounted read-write.
--writable-var-log - use the real /var/log directory, not a clone.
 --x11 - enable X11 sandboxing. The software checks first if Xpra is installed, then it checks if Xephyr is installed. If all fails, it will attempt to use X11 security extension. --x11 - enable X11 sandboxing. The software checks first if Xpra is installed, then it checks if Xephyr is installed. If all fails, it will attempt to use X11 security extension.
--x11=none - disable access to X11 sockets.
--x11=xephyr - enable Xephyr X11 server. The window size is 800x600.
 --x11=xorg - enable X11 security extension. --x11=xorg - enable X11 security extension.
--x11=xpra - enable Xpra X11 server.
--x11=xvfb - enable Xvfb X11 server.
--zsh - use /usr/bin/zsh as default shell.
Examples:
$ firejail firefox
start Mozilla Firefox
$ firejail --debug firefox
debug Firefox sandbox
$ firejail --private --sna=8.8.8.8 firefox
start Firefox with a new, empty home directory, and a well-known DNS-server setting.
$ firejail --net=eth0 firefox
start Firefox in a new network namespace
$ firejail --x11=xorg firefox
start Firefox and sandbox X11
$ firejail --list
list all running sandboxes
License GPL version 2 or later
Homepage: http://firejail.wordpress.com
"Mit Firejail lässt sich das Risiko erheblich reduzieren, das von bis dato ungepatchten Sicherheitslücken in Programmen ausgeht.", www.kuketz-blog.de/firejail-linux-haerten-teil4
Firejail has got two very interesting options: --profile, what is done with default.profile by default as much as one profile for each program resp. process out of a hugh amount from /etc/firejail and --private. Last one completes the sandbox in a whole. Refering to linfw3, for still blocking all trojans resp. backdoors, use the already listed firejail-option --profile=/home/surfuser, especially the pregiven (and already listed) profiles.
Resign from firejail, if firefox does not work correctly, until firejail gets reconfigured well enough !
"SECure COMPuting with filters (like seccomp within firejail)
===========================================
Introduction
------------
A large number of system calls are exposed to every userland process with many of them going unused for the entire lifetime of the process. As system calls change and mature, bugs are found and eradicated. A certain subset of userland applications benefit by having a reduced set of available system calls. The resulting set reduces the total kernel surface exposed to the application. System call filtering is meant for use with those applications.
Seccomp filtering provides a means for a process to specify a filter for incoming system calls. The filter is expressed as a Berkeley Packet Filter (BPF) program, as with socket filters, except that the data operated on is related to the system call being made: system call number and the system call arguments. This allows for expressive filtering of system calls using a filter program language with a long history of being exposed to userland and a straightforward data set.
Additionally, BPF makes it impossible for users of seccomp to fall prey to time-of-check-time-of-use (TOCTOU) attacks that are common in system call interposition frameworks. BPF programs may not dereference pointers which constrains all filters to solely evaluating the system call arguments directly.
What it isn´t
-------------
System call filtering isn´t a sandbox.It provides a clearly defined mechanism for minimizing the exposed kernel surface. It is meant to be a tool for sandbox developers to use. Beyond that, policy for logical behavior and information flow should be managed with a combination of other system hardening techniques and, potentially, an LSM of your choosing. Expressive, dynamic filters provide further options down this path (avoiding pathological sizes or selecting which of the multiplexed system calls in socketcall() is allowed, for instance) which could be construed, incorrectly, as a more complete sandboxing solution.
Usage
-----
An additional seccomp mode is added and is enabled using the same prctl(2) call as the strict seccomp. If the architecture has CONFIG_HAVE_ARCH_SECCOMP_FILTER, then filters may be added as below:
...", https://www.pro-linux.de/news/1/25207/sicherheits-audit-von-dnsmasq.html, https://www.kernel.org/doc/Documentation/prctl/seccomp_filter.txt
Firefox mit Tor:
 | sg surfgroup "unshare firejail --nice=19 --profile=/etc/firejail/firefox.profile /usr/lib64/firefox/firefox --no-remote &" && sg surfgroup "unshare firejail --nice=19 --profile=/etc/firejail/tor.profile tor -f /home/surfuser/torrc" && export RESOLV_HOST_CONF="/etc/hosts" |
with default-firefox.profile like default.profile, but without blacklist /home/surfuser/.mozilla and /home/surfuser/.cache (commented in with "#").
Option tor: is used for the anonymizing TorDNS as the remote-DNS-server, what is introduced with Tor at the end of this excurs.
Following the many profile-files in /etc/firejail, the in comparison to sandbox docker-io easy-to-handle Firejail is recommended for all programs resp. processes online and you might not trust like webserver, server, dolphin (what causes a intern restricted bash, so that you should resign from it as much as for quit all processes online. Have a brief look into the configuration file of firejail in /etc/firejail too: many of them refer to single processes resp. programs, some like files named disable*.inc refer to more than it. There, encrypted partitions and directories including sub-directories (blacklist /mnt/) and USB-sticks (blacklist /media/ resp. blacklist /media/directory_for_the_usb-stick) can be secured once more too as much as the block of the intern start of bash-commands refering to outside of private and so on. Now everything online runs not only "two and three times more secure" but even much faster than already fast !
Firejail-options for *.inc-files within /etc/firejail/ :
caps.drop all
ipc-namespace
netfilter
no3d
nogroups
nonewprivs
noroot
nosound
noautopulse
notv
protocol unix,inet,inet6
 seccomp seccomp
 shell none shell none
tracelog
quiet
private-dev
private-bin
private-etc passwd,group,hostname,hosts,resolv.conf,nsswitch.conf,fonts,mailcap,pulse
private-tmp
# ... not all firejail-options should be activated, in order to avoid capacity- and serious hard system-errors!
To the profiles of actual firejail 0.9.48-1.pcclos2017 in /etc/firejail, that is provided preconfigured by us (Gooken) to get downloaded from our section for updates, belong (description see "man firejail")
0ad.profile
2048-qt.profile
140 25. Jun 14:30 7z.profile
1225 25. Jun 14:30 abrowser.profile
704 20. Mai 23:55 akregator.profile
489 25. Jun 14:30 amarok.profile
568 20. Mai 23:55 arduino.profile
499 25. Jun 14:30 ark.profile
347 25. Jun 14:30 atom-beta.profile
342 25. Jun 14:30 atom.profile
535 25. Jun 14:30 atool.profile
410 25. Jun 14:30 atril.profile
267 25. Jun 14:30 audacious.profile
357 25. Jun 14:30 audacity.profile
458 25. Jun 14:30 aweather.profile
1742 20. Mai 23:55 baloo_file.profile
785 20. Mai 23:55 bibletime.profile
271 25. Jun 14:30 bitlbee.profile
488 25. Jun 14:30 bleachbit.profile
488 8. Mai 23:07 bleachbit.profile
595 20. Mai 23:55 blender.profile
492 25. Jun 14:30 bless.profile
492 8. Mai 23:07 bless.profile
535 25. Jun 14:30 brasero.profile
535 8. Mai 23:07 brasero.profile
338 25. Jun 14:30 brave.profile
878 20. Mai 23:55 caja.profile
407 25. Jun 14:30 cherrytree.profile
66 25. Jun 14:30 chromium-browser.profile
695 25. Jun 14:30 chromium.profile
393 25. Jun 14:30 claws-mail.profile
268 25. Jun 14:30 clementine.profile
598 20. Mai 23:55 clipit.profile
340 25. Jun 14:30 cmus.profile
564 25. Jun 14:30 conkeror.profile
262 25. Jun 14:30 corebird.profile
379 25. Jun 14:30 cpio.profile
178 25. Jun 14:30 cryptocat.profile
524 20. Mai 23:55 Cryptocat.profile
582 25. Jun 14:30 cvlc.profile
99 25. Jun 14:30 cyberfox.profile
245 20. Mai 23:55 Cyberfox.profile
304 25. Jun 14:30 deadbeef.profile
366 25. Jun 14:30 default0.profile
366 25. Jun 14:30 default2.profile
607 25. Jun 14:30 default-firefox.profile
371 25. Jun 14:30 default-gftp.profile
367 25. Jun 14:30 default.profile
397 25. Jun 14:30 deluge.profile
526 20. Mai 23:55 dia.profile
450 25. Jun 14:30 dillo.profile
755 20. Mai 23:55 dino.profile
4812 25. Jun 14:30 disable-common0.inc
7239 25. Jun 14:30 disable-common-gftp.inc
3788 25. Jun 14:30 disable-common.inc
3788 11. Mai 15:08 disable-common.inc.rpmsave
7239 25. Jun 14:30 disable-common-kmail.inc
91 25. Jun 14:30 disable-devel-firefox.inc
1470 25. Jun 14:30 disable-devel.inc
725 25. Jun 14:30 disable-firefox.inc
187 25. Jun 14:30 disable-passwdmgr.inc
567 25. Jun 14:30 disable-programs-firefox.inc
4949 25. Jun 14:30 disable-programs.inc
538 25. Jun 14:30 display.profile
770 25. Jun 14:30 dnscrypt-proxy.profile
327 25. Jun 14:30 dnsmasq.profile
831 25. Jun 14:30 dolphin.profile
831 8. Mai 23:07 dolphin.profile
370 25. Jun 14:30 dosbox.profile
529 25. Jun 14:30 dragon.profile
448 25. Jun 14:30 dropbox.profile
562 25. Jun 14:30 elinks.profile
276 25. Jun 14:30 emacs.profile
229 25. Jun 14:30 empathy.profile
535 25. Jun 14:30 enchant.profile
505 25. Jun 14:30 engrampa.profile
376 25. Jun 14:30 eog.profile
374 25. Jun 14:30 eom.profile
609 25. Jun 14:30 epiphany.profile
356 25. Jun 14:30 evince.profile
476 25. Jun 14:30 evolution.profile
630 25. Jun 14:30 exiftool.profile
402 25. Jun 14:30 fbreader.profile
367 25. Jun 14:30 feh.profile
223 25. Jun 14:30 file.profile
514 25. Jun 14:30 file-roller.profile
553 20. Mai 23:55 filezilla.profile
230 20. Mai 23:55 firefox-esr.profile
1819 20. Mai 23:55 firefox.profile
2985 25. Jun 14:30 firejail.config
898 25. Jun 14:30 flashpeak-slimjet.profile
300 25. Jun 14:30 flowblade.profile
544 20. Mai 23:55 fontforge.profile
429 25. Jun 14:30 fossamail.profile
220 20. Mai 23:55 FossaMail.profile
481 25. Jun 14:30 franz.profile
817 25. Jun 14:30 gajim.profile
601 20. Mai 23:55 galculator.profile
543 20. Mai 23:55 geany.profile
621 25. Jun 14:30 gedit.profile
582 25. Jun 14:30 geeqie.profile
36 20. Mai 23:55 gimp-2.8.profile
295 25. Jun 14:30 gimp.profile
418 25. Jun 14:30 git.profile
383 25. Jun 14:30 gitter.profile
833 25. Jun 14:30 gjs.profile
555 20. Mai 23:55 globaltime.profile
653 25. Jun 14:30 gnome-2048.profile
654 25. Jun 14:30 gnome-books.profile
503 25. Jun 14:30 gnome-calculator.profile
431 25. Jun 14:30 gnome-chess.profile
526 25. Jun 14:30 gnome-clocks.profile
499 25. Jun 14:30 gnome-contacts.profile
612 25. Jun 14:30 gnome-documents.profile
543 20. Mai 23:55 gnome-font-viewer.profile
627 25. Jun 14:30 gnome-maps.profile
627 8. Mai 23:07 gnome-maps.profile
329 25. Jun 14:30 gnome-mplayer.profile
552 25. Jun 14:30 gnome-music.profile
663 25. Jun 14:30 gnome-photos.profile
669 25. Jun 14:30 gnome-weather.profile
493 25. Jun 14:30 goobox.profile
704 25. Jun 14:30 google-chrome-beta.profile
670 25. Jun 14:30 google-chrome.profile
76 25. Jun 14:30 google-chrome-stable.profile
732 25. Jun 14:30 google-chrome-unstable.profile
452 25. Jun 14:30 google-play-music-desktop-player.profile
493 25. Jun 14:30 gpa.profile
542 25. Jun 14:30 gpg-agent.profile
530 25. Jun 14:30 gpg.profile
543 25. Jun 14:30 gpicview.profile
458 25. Jun 14:30 gpredict.profile
55 25. Jun 14:30 gtar.profile
370 25. Jun 14:30 gthumb.profile
501 25. Jun 14:30 guayadeque.profile
535 20. Mai 23:55 gucharmap.profile
424 25. Jun 14:30 gwenview.profile
153 25. Jun 14:30 gzip.profile
425 25. Jun 14:30 hedgewars.profile
632 25. Jun 14:30 hexchat.profile
546 25. Jun 14:30 highlight.profile
544 20. Mai 23:55 hugin.profile
1224 25. Jun 14:30 icecat.profile
445 25. Jun 14:30 icedove.profile
99 25. Jun 14:30 iceweasel.profile
508 25. Jun 14:30 img2txt.profile
302 25. Jun 14:30 inkscape.profile
509 25. Jun 14:30 inox.profile
192 25. Jun 14:30 iridium-browser.profile
631 25. Jun 14:30 iridium.profile
479 25. Jun 14:30 jd-gui.profile
479 8. Mai 23:07 jd-gui.profile
326 25. Jun 14:30 jitsi.profile
475 25. Jun 14:30 k3b.profile
475 8. Mai 23:07 k3b.profile
700 25. Jun 14:30 kate.profile
617 20. Mai 23:55 kcalc.profile
219 25. Jun 14:30 keepass2.profile
400 25. Jun 14:30 keepass.profile
630 25. Jun 14:30 keepassx2.profile
630 8. Mai 23:07 keepassx2.profile
673 25. Jun 14:30 keepassxc.profile
673 8. Mai 23:07 keepassxc.profile
427 25. Jun 14:30 keepassx.profile
665 25. Jun 14:30 kino.profile
665 8. Mai 23:07 kino.profile
356 25. Jun 14:30 kmail.profile
356 21. Apr 13:50 kmail.profile
526 20. Mai 23:55 knotes.profile
545 20. Mai 23:55 kodi.profile
288 25. Jun 14:30 konversation.profile
709 20. Mai 23:55 ktorrent.profile
558 20. Mai 23:55 leafpad.profile
122 25. Jun 14:30 less.profile
400 25. Jun 14:30 libreoffice.profile
131 25. Jun 14:30 localc.profile
131 25. Jun 14:30 lodraw.profile
131 25. Jun 14:30 loffice.profile
131 25. Jun 14:30 lofromtemplate.profile
345 25. Jun 14:30 login.users
131 25. Jun 14:30 loimpress.profile
506 25. Jun 14:30 lollypop.profile
506 8. Mai 23:07 lollypop.profile
131 25. Jun 14:30 lomath.profile
131 25. Jun 14:30 loweb.profile
131 25. Jun 14:30 lowriter.profile
349 25. Jun 14:30 luminance-hdr.profile
556 20. Mai 23:55 lximage-qt.profile
579 20. Mai 23:55 lxmusic.profile
263 25. Jun 14:30 lxterminal.profile
533 25. Jun 14:30 lynx.profile
562 20. Mai 23:55 mate-calc.profile
42 20. Mai 23:55 mate-calculator.profile
533 20. Mai 23:55 mate-color-select.profile
579 20. Mai 23:55 mate-dictionary.profile
213 20. Mai 23:55 mathematica.profile
491 25. Jun 14:30 Mathematica.profile
213 8. Mai 23:07 mathematica.profile
387 25. Jun 14:30 mcabber.profile
545 25. Jun 14:30 mediainfo.profile
533 25. Jun 14:30 mediathekview.profile
551 20. Mai 23:55 meld.profile
301 25. Jun 14:30 midori.profile
526 25. Jun 14:30 mousepad.profile
363 25. Jun 14:30 mpv.profile
717 25. Jun 14:30 multimc5.profile
717 8. Mai 23:07 multimc5.profile
734 25. Jun 14:30 mumble.profile
734 8. Mai 23:07 mumble.profile
890 25. Jun 14:30 mupdf.profile
514 25. Jun 14:30 mupen64plus.profile
774 25. Jun 14:30 mutt.profile
859 25. Jun 14:30 nautilus.profile
859 8. Mai 23:07 nautilus.profile
674 20. Mai 23:55 nemo.profile
658 25. Jun 14:30 netsurf.profile
774 25. Jun 14:30 nolocal.net
652 20. Mai 23:55 nylas.profile
554 25. Jun 14:30 odt2txt.profile
542 25. Jun 14:30 okular.profile
284 25. Jun 14:30 openbox.profile
294 25. Jun 14:30 openshot.profile
591 25. Jun 14:30 opera-beta.profile
611 25. Jun 14:30 opera.profile
584 20. Mai 23:55 orage.profile
1601 25. Jun 14:30 palemoon.profile
371 25. Jun 14:30 parole.profile
660 20. Mai 23:55 pcmanfm.profile
439 25. Jun 14:30 pdfsam.profile
439 8. Mai 23:07 pdfsam.profile
541 25. Jun 14:30 pdftotext.profile
363 25. Jun 14:30 pidgin.profile
483 25. Jun 14:30 pithos.profile
483 8. Mai 23:07 pithos.profile
412 25. Jun 14:30 pix.profile
503 25. Jun 14:30 pluma.profile
707 25. Jun 14:30 polari.profile
507 25. Jun 14:30 psi-plus.profile
439 25. Jun 14:30 qbittorrent.profile
452 25. Jun 14:30 qemu-launcher.profile
418 25. Jun 14:30 qemu-system-x86_64.profile
560 20. Mai 23:55 qlipper.profile
405 25. Jun 14:30 qpdfview.profile
448 25. Jun 14:30 qtox.profile
222 25. Jun 14:30 quassel.profile
626 25. Jun 14:30 quiterss.profile
813 25. Jun 14:30 qupzilla.profile
533 25. Jun 14:30 qutebrowser.profile
426 25. Jun 14:30 ranger.profile
353 25. Jun 14:30 rhythmbox.profile
574 20. Mai 23:55 ristretto.profile
360 25. Jun 14:30 rtorrent.profile
885 25. Jun 14:30 scribus.profile
885 8. Mai 23:07 scribus.profile
100 25. Jun 14:30 seamonkey-bin.profile
1293 25. Jun 14:30 seamonkey.profile
355 25. Jun 14:30 server.profile
562 25. Jun 14:30 simple-scan.profile
506 25. Jun 14:30 skanlite.profile
267 25. Jun 14:30 skypeforlinux.profile
243 25. Jun 14:30 skype.profile
624 25. Jun 14:30 slack.profile
349 25. Jun 14:30 snap.profile
131 25. Jun 14:30 soffice.profile
844 25. Jun 14:30 spotify.profile
464 25. Jun 14:30 ssh-agent.profile
287 25. Jun 14:30 ssh.profile
603 25. Jun 14:30 start-tor-browser.profile
386 25. Jun 14:30 steam.profile
546 25. Jun 14:30 stellarium.profile
126 25. Jun 14:30 strings.profile
322 25. Jun 14:30 synfigstudio.profile
301 25. Jun 14:30 tar.profile
62 25. Jun 14:30 telegram.profile
208 20. Mai 23:55 Telegram.profile
62 12. Apr 20:18 telegram.profile
208 8. Mai 23:07 Telegram.profile
37 25. Jun 14:30 thunar.profile
725 20. Mai 23:55 Thunar.profile
540 8. Mai 23:07 Thunar.profile
446 25. Jun 14:30 thunderbird.profile
335 25. Jun 14:30 totem.profile
628 25. Jun 14:30 tracker.profile
618 25. Jun 14:30 transmission-cli.profile
460 25. Jun 14:30 transmission-gtk.profile
457 25. Jun 14:30 transmission-qt.profile
591 25. Jun 14:30 transmission-show.profile
441 25. Jun 14:30 uget-gtk.profile
780 25. Jun 14:30 unbound.profile
235 25. Jun 14:30 unrar.profile
223 25. Jun 14:30 unzip.profile
223 25. Jun 14:30 uudeview.profile
702 25. Jun 14:30 uzbl-browser.profile
609 20. Mai 23:55 viewnior.profile
581 20. Mai 23:55 viking.profile
292 25. Jun 14:30 vim.profile
273 25. Jun 14:30 virtualbox.profile
189 20. Mai 23:55 VirtualBox.profile
69 25. Jun 14:30 vivaldi-beta.profile
540 25. Jun 14:30 vivaldi.profile
534 25. Jun 14:30 vivaldi-stable.profile
398 25. Jun 14:30 vlc.profile
547 25. Jun 14:30 w3m.profile
521 25. Jun 14:30 warzone2100.profile
992 25. Jun 14:30 webserver.net
69 25. Jun 14:30 weechat-curses.profile
408 25. Jun 14:30 weechat.profile
689 25. Jun 14:30 wesnoth.profile
497 25. Jun 14:30 wget.profile
497 8. Mai 23:07 wget.profile
746 25. Jun 14:30 whitelist-common.inc
284 25. Jun 14:30 wine.profile
676 20. Mai 23:55 wire.profile
203 25. Jun 14:30 Wire.profile
609 25. Jun 14:30 wireshark.profile
609 8. Mai 23:07 wireshark.profile
288 25. Jun 14:30 xchat.profile
497 25. Jun 14:30 xed.profile
922 20. Mai 23:55 Xephyr.profile
531 25. Jun 14:30 xfburn.profile
555 20. Mai 23:55 xfce4-dict.profile
657 20. Mai 23:55 xfce4-notes.profile
676 25. Jun 14:30 xiphos.profile
487 25. Jun 14:30 xmms.profile
225 25. Jun 14:30 xonotic-glx.profile
602 25. Jun 14:30 xonotic.profile
602 8. Mai 23:07 xonotic.profile
225 25. Jun 14:30 xonotic-sdl.profile
352 25. Jun 14:30 xpdf.profile
450 25. Jun 14:30 xplayer.profile
512 25. Jun 14:30 xpra.profile
512 8. Mai 23:07 xpra.profile
450 25. Jun 14:30 xreader.profile
1128 20. Mai 23:55 Xvfb.profile
336 25. Jun 14:30 xviewer.profile
154 25. Jun 14:30 xzdec.profile
54 25. Jun 14:30 xz.profile
530 20. Mai 23:55 youtube-dl.profile
393 25. Jun 14:30 zathura.profile
470 25. Jun 14:30 zoom.profile
 /etc/firejail/palemoon.profile: /etc/firejail/palemoon.profile:
...
# For Pale Moon and Tor
################################
# Generic GUI application profile
################################
include /etc/firejail/disable-common.inc
include /etc/firejail/disable-programs.inc
include /etc/firejail/disable-passwdmgr.inc
noblacklist /usr/bin/palemoon
noblacklist /usr/bin/tor
noblacklist ${HOME}/.moon*
noblacklist ${HOME}/keys
noblacklist ${HOME}/lock
noblacklist ${HOME}/state
noblacklist ${HOME}/cached*
noblacklist ${HOME}/ca-bundle.crt
noblacklist ${HOME}/.thumbnails
noblacklist ${HOME}/cache
noblacklist ${HOME}/control_auth_cookie
read-only ${HOME}/geoip
read-only ${HOME}/geoip6
read-only ${HOME}/torrc
read-only ${HOME}/.pale*/moon*/profile.yourprofile/user.js
noblacklist ${HOME}/tmp
blacklist ${HOME}/.local
blacklist ${HOME}/.pulse
blacklist ${HOME}/.kde
blacklist ${HOME}/.kde4
blacklist ${HOME}/.gftp
blacklist ${HOME}/.config
blacklist ${HOME}/.pki
blacklist ${HOME}/.mcop
blacklist ${HOME}/.fontconfig
blacklist ${HOME}/.dbus
blacklist ${HOME}/.bash*
blacklist ${HOME}/.abrt
blacklist ${HOME}/.gconf*
blacklist ${HOME}/.xsession-errors
blacklist ${HOME}/.profile
blacklist ${HOME}/Desktop
blacklist ${HOME}/.mozilla
blacklist ${HOME}/.wine
blacklist ${HOME}/.gnupg
blacklist ${HOME}/.mozilla
blacklist /usr/lib/perl*
blacklist /usr/lib64/perl*
blacklist /etc/shadow
blacklist /etc/shadow-
blacklist /usr/src
blacklist /usr/games
blacklist /etc/init.d
blacklist /etc/rc0.d
blacklist /etc/rc1.d
blacklist /etc/rc2.d
blacklist /etc/rc3.d
blacklist /etc/rc4.d
blacklist /etc/rc5.d
blacklist /etc/rc6.d
blacklist /usr/local
blacklist /etc/rc.d
blacklist /etc/fstab
blacklist /etc/mtab
blacklist /etc/crypttab
blacklist /etc/shadow
blacklist /etc/shadow-
blacklist /etc/passwd
blacklist /boot
blacklist /usr/bin/*
blacklist /bin/*
ipc-namespace
caps.drop all
nodbus
nodvd
nogroups
netfilter
nonewprivs
noroot
protocol unix,inet,netlink
seccomp
shell none
no3d
nosound
nou2f
private-bin which,palemoon,firefox
private-dev
private-tmp
private-etc passwd,group,hostname,hosts,fonts,nsswitch.conf,xdg,resolv.conf,pango
#private-etc
 /etc/firejail/firefox.profile (extraction): /etc/firejail/firefox.profile (extraction):
...
# This file is overwritten during software install.
# Persistent customizations should go in a .local file.
include /etc/firejail/firefox.local
# Firejail profile for Mozilla Firefox (Iceweasel in Debian)
noblacklist ~/.mozilla
noblacklist ~/.cache/mozilla
blacklist ~/.config/qpdfview
blacklist ~/.local/share/qpdfview
blacklist ~/.pki
blacklist /usr/bin
blacklist /usr/sbin
blacklist /usr/src
blacklist /opt
blacklist /sbin
blacklist /usr/libexec
blacklist /bin
blacklist /usr/games
blacklist /etc/init.d
blacklist /etc/rc0.d
blacklist /etc/rc1.d
blacklist /etc/rc2.d
blacklist /etc/rc3.d
blacklist /etc/rc4.d
blacklist /etc/rc5.d
blacklist /etc/rc6.d
blacklist /etc/rc.d
blacklist /etc/fstab
blacklist /etc/mtab
blacklist /etc/crypttab
blacklist /etc/shadow
blacklist /etc/shadow-
blacklist /etc/passwd
blacklist /boot
blacklist /usr/local
blacklist ~./kde4
blacklist ~./config
blacklist ~./gconf
blacklist ~./gconfd
blacklist ~./local
blacklist ~./mcop
blacklist ~./pulse-cookie
blacklist ~./thumbnails
blacklist ~./Desktop
blacklist /home/secret
blacklist /home/toranonym
blacklist /media
blacklist /mnt
noblacklist /usr/bin/xargs
noblacklist /usr/bin/xauth
noblacklist /usr/bin/export
noblacklist /usr/bin/firefox
noblacklist /usr/bin/sg
noblacklist /usr/bin/gftp
noblacklist /usr/bin/gftp-gtk
noblacklist /usr/bin/gftp-text
noblacklist /usr/bin/tor
noblacklist /bin/certtool
noblacklist /bin/certutil
noblacklist /bin/basename
noblacklist /bin/bash.old
noblacklist /bin/p11tool
noblacklist /bin/pk12util
noblacklist /bin/smime
noblacklist /bin/shlibsign
noblacklist /bin/signtool
noblacklist /bin/signver
noblacklist /bin/ssltap
read-only /home/surfuser/.mozilla/firefox/default.profile/user.js
read-only /home/surfuser/torrc
read-only /home/surfuser/.mozilla/firefox/prefs.js
#blacklist ~/."moonchild productions"
include /etc/firejail/disable-common0.inc
include /etc/firejail/disable-programs.inc
include /etc/firejail/disable-devel.inc
 caps.drop all caps.drop all
# caps.drop=CAP_AUDIT_CONTROL,CAP_AUDIT_WRITE,CAP_AUDIT_READ
 ipc-namespace ipc-namespace
 netfilter netfilter
 nogroups nogroups
 nonewprivs nonewprivs
 noroot noroot
 protocol unix,inet,netlink protocol unix,inet,netlink
 seccomp seccomp
 shell none shell none
nosound
noautopulse
notv
# tracelog
 no3d no3d
 nodbus nodbus
 nodvd nodvd
 nosound nosound
 nou2f nou2f
# ... see firejail --help, BEACHTE: Nicht alle Firejail-Optionen funktionieren für Firefox!
mkdir ~/.mozilla
whitelist ~/.mozilla
mkdir ~/.cache/mozilla/firefox
whitelist ~/.cache/mozilla/firefox
whitelist ~/dwhelper
mkdir ~/.pki
whitelist ~/.pki
disable-mnt # or use blacklist /mnt and blacklist /media
private-dev # This might not always work with firefox
# experimental features
# private-bin sh,which,env,dbus-send,dbus-launch
# private-etc passwd,group,hostname,hosts,localtime,nsswitch.conf,resolv.conf,xdg,pango,fonts,firefox,mime.types,mailcap,asound.conf,pulse
private-etc passwd,group,hostname,hosts,resolv.conf,nsswitch.conf,fonts,mailcap,pulse
# private-dev # - prevents video calls going out
private-tmp
noexec ${HOME}
noexec /tmp
noexec /tmp2
... or, in order to start konqueror with priority 18 always by mouseclick out of the K-menu, type "sg surfgroup konqueror && renice -n 18 ´pidof konqueror´ &&kded4" resp. with firejail-options into the command-line, after editing the K-menu with kmenuedit. Konqueror loads websites even with process-priority 18 fabolous fast (its like beaming to visit anything anywhere at once with a Spaceship like Enterprise thanks Spock, as if Google has not been there for a long time...). We also started services like the cookie-management for surfuser named kded4. On our linksites we describe by reports and links more enfastening methods for the browser Firefox.
Notice, that there is a patch for firejail (pclos2017) from year 2017/12 firejail-0.9.52-1.x86_64 making the private-option in all cases really effective. This means for our two examples for firejail for konqueror and firefox better to resign from this option for the first time, until firejail might gets reconfgured. To make firejail already work well without this option, we suggest the following configuration. Also notice, that it won´t fit for all programs (although quit all). In this case, single entries might have to be removed or added to store into new configuration files:
Pale Moon, notice: noscript and RequestBlockPolicyContinned do not block many scripts as they should do!
 /etc/firejail/palemoon.profile /etc/firejail/palemoon.profile
#### Especially for Pale Moon (browser):
blacklist /mnt
blacklist /media
blacklist /etc/cups
blacklist /usr/local
blacklist /usr/sbin
blacklist /sbin
blacklist /usr/libexec
blacklist /usr/games
blacklist /lib
blacklist /home/toruser
blacklist /home/user
blacklist /opt
blacklist /usr/lib
blacklist /usr/lib/python*
blacklist /usr/lib64/python*
blacklist /usr/lib/perl*
blacklist /usr/lib64/perl*
blacklist /etc/shadow
blacklist /etc/shadow-
blacklist ${HOME}/.wine
blacklist ${HOME}/.gnupg
ipc-namespace
caps.drop all
netfilter
nonewprivs
noroot
protocol unix,inet,inet6
seccomp
#nogroup
 shell none shell none
#private-bin which,firefox
private-dev
private-tmp
private-etc passwd,group,hostname,hosts,fonts,nsswitch.conf,xdg,resolv.conf,pango
#
#### end Pale Moon (/etc/firejail/palemoon.profile)
 /etc/firejail/default.profile (preconfigured firejail (fc27, pclos2017, rosa2016.1) from August 2017 can be downloaded from our update section): /etc/firejail/default.profile (preconfigured firejail (fc27, pclos2017, rosa2016.1) from August 2017 can be downloaded from our update section):
################################
# Generic GUI application profile
################################
include /etc/firejail/disable-common.inc
include /etc/firejail/disable-programs.inc
include /etc/firejail/disable-passwdmgr.inc
#
blacklist DOLLAR{HOME}/.wine
blacklist DOLLAR{HOME}/.gnupg
caps.drop all
# netfilter
nonewprivs
noroot
protocol unix,inet,inet6
# seccomp
 shell none # this is very important and suitable for many profiles, even konqueror, kmail and thunderbird, but not all profiles: also notice our comments about /etc/passwd shell none # this is very important and suitable for many profiles, even konqueror, kmail and thunderbird, but not all profiles: also notice our comments about /etc/passwd
/etc/firejail/disable-common.inc of firejail (rosa2014.1), alternatively set ACL-rules (setfacl):
 noexec /usr/bin/bash # for some profiles like for Konqueror noexec /usr/bin/bash # for some profiles like for Konqueror
noexec /bin/bash
# History files in HOME
blacklist-nolog DOLLAR{HOME}/.history
blacklist-nolog {HOME}/.*_history
blacklist {HOME}/.local/share/systemd
blacklist-nolog {HOME}/.adobe
blacklist-nolog {HOME}/.macromedia
read-only {HOME}/.local/share/applications
# X11 session autostart and more
blacklist DOLLAR{HOME}/Desktop
blacklist {HOME}/*.jar
blacklist {HOME}/logs
blacklist {HOME}/tor-browser
blacklist {HOME}/.xinitrc
blacklist {HOME}/.xprofile
blacklist {HOME}/.config/autostart
blacklist /etc/xdg/autostart
blacklist {HOME}/.kde4/Autostart
blacklist {HOME}/.kde4/share/autostart
blacklist {HOME}/.kde/Autostart
blacklist {HOME}/.kde/share/autostart
blacklist {HOME}/.config/plasma-workspace/shutdown
blacklist {HOME}/.config/plasma-workspace/env
blacklist {HOME}/.config/lxsession/LXDE/autostart
blacklist {HOME}/.fluxbox/startup
blacklist {HOME}/.config/openbox/autostart
blacklist {HOME}/.config/openbox/environment
blacklist {HOME}/.gnomerc
read-only /etc
read-only /bin
read-only /usr/bin
read-only /usr/etc
read-only /proc
read-only /sys
read-only /dev
blacklist /etc/X11/Xsession.d/
blacklist /media/ # USB-Sticks / USB-Speicherstifte
blacklist /media/sicher/
blacklist /mnt
blacklist /opt
blacklist /misc
blacklist /secoff
blacklist /sid-root
blacklist /lost+found
blacklist /smack
blacklist /srv
blacklist /net
blacklist /initrd
blacklist /intel-ucode
blacklist /boot-save
blacklist /boot
blacklist /cgroup
blacklist /root
read-only /lib
read-only /lib64
read-only /usr/lib
read-only /usr/lib64 # Firefox: "read-only /usr/lib64/lib*" or read-only /usr/lib64/a*, ..., read-only /usr/lib64/z* without the firefox-directory
read-only /usr/lib64/kde4
blacklist /usr/local
blacklist /usr/bin/ssh*
blacklist /usr/src
read-only /usr/bin/firejail
read-only /usr/ssl
read-only /usr/libexec
read-only /usr/uclibc
read-only /usr/X11R6
read-only /usr/x86_64-linux-uclibc
read-only /usr/etc
read-only /usr/com
read-only /usr/docs
read-only /usr/enthought
read-only /usr/GNUstep
read-only /usr/selenium
read-only /usr/man
read-only /usr/mipsel-linux
read-only /usr/i686-w64-mingw32
read-only /usr/i486-linux-libc5
blacklist /bin/kill
blacklist /bin/rm
blacklist /bin/ping
blacklist /bin/mount*
blacklist /bin/umount*
blacklist /bin/ls*
blacklist /bin/sed*
blacklist /bin/rpm
blacklist /bin/pipeline
blacklist /bin/mv
blacklist /bin/cp
blacklist /bin/csh
blacklist /bin/dd
blacklist /bin/chmod
blacklist /bin/chown
blacklist /bin/dash
blacklist /bin/df
blacklist /bin/dmesg
blacklist /bin/ed
blacklist /bin/find
blacklist /bin/grep
blacklist /bin/exec
blacklist /bin/gunzip
blacklist /bin/gzip
blacklist /bin/gzexe
blacklist /bin/ln
blacklist /bin/login
blacklist /bin/lsblk
blacklist /bin/mail
blacklist /bin/mailx
blacklist /bin/mkdir
blacklist /bin/mksh
blacklist /bin/mknod
blacklist /bin/netstat
# blacklist /bin/ps
blacklist /bin/pwd
blacklist /bin/pipeline
blacklist /bin/rmdir
blacklist /bin/tcsh
blacklist /bin/touch
blacklist /bin/vi
blacklist /bin/zsh
blacklist /bin/tar
blacklist /bin/zless
blacklist /bin/zmore
blacklist /bin/more
blacklist /bin/date
blacklist /bin/dmesg
blacklist /bin/ash
blacklist /bin/awk
blacklist /bin/cg*
blacklist /bin/cd
blacklist /bin/bashb*
blacklist /bin/cat
blacklist /bin/env
blacklist /bin/get*
blacklist /bin/for*
blacklist /bin/homeof
blacklist /bin/foreground
blacklist /usr/bin/rpm*
blacklist /usr/bin/srm
blacklist /usr/bin/shred
blacklist /usr/bin/wipe
blacklist /usr/bin/mount*
blacklist /usr/bin/umount*
blacklist /usr/bin/mouse*
blacklist /usr/bin/ls*
# blacklist /usr/bin/r*
# blacklist /usr/bin/a*
# blacklist /usr/bin/c*
# blacklist /usr/bin/e*
# blacklist /usr/bin/f*
# blacklist /usr/bin/h*
# blacklist /usr/bin/i*
# blacklist /usr/bin/j*
# blacklist /usr/bin/perl*
# blacklist /usr/bin/s*
# blacklist /usr/bin/t*
# blacklist /usr/bin/u*
# blacklist /usr/bin/v*
# blacklist /usr/bin/w*
# blacklist /usr/bin/x*
# blacklist /usr/bin/y*
# blacklist /usr/bin/z*
blacklist /usr/libexec/mysql*
blacklist /usr/bin/mysql*
blacklist /usr/share/autostart
read-only /usr/share/cups
read-only /usr/share/cups/model
blacklist /usr/share/doc
blacklist /var/www
blacklist /var/www/html
# VirtualBox
blacklist DOLLAR{HOME}/.VirtualBox
blacklist DOLLAR{HOME}/VirtualBox VMs
blacklist DOLLAR{HOME}/.config/VirtualBox
# VeraCrypt
blacklist DOLLAR{PATH}/veracrypt
blacklist DOLLAR{PATH}/veracrypt-uninstall.sh
blacklist /usr/share/veracrypt
blacklist /usr/share/applications/veracrypt.*
blacklist /usr/share/pixmaps/veracrypt.*
blacklist DOLLAR{HOME}/.VeraCrypt
# var
blacklist /var/spool/cron
blacklist /var/spool/anacron
blacklist /var/run/acpid.socket
blacklist /var/run/minissdpd.sock
blacklist /var/run/rpcbind.sock
blacklist /var/run/mysqld/mysqld.sock
blacklist /var/run/mysql/mysqld.sock
blacklist /var/lib/mysqld/mysql.sock
blacklist /var/lib/mysql/mysql.sock
blacklist /var/run/docker.sock
# etc
blacklist /etc/cron.*
blacklist /etc/profile.d
blacklist /etc/rc.local
blacklist /etc/anacrontab
blacklist /etc/rpc*
blacklist /etc/rpm*
blacklist /etc/rc*
blacklist /etc/init.d
read-only /etc/printcap
blacklist /etc/pmount*
read-only /etc/PolicyKit
read-only /etc/php.ini
read-only /etc/passwd
read-only /etc/paper*
blacklist /etc/mpasswd
blacklist /etc/modprobe*
blacklist /etc/mke2fs*
blacklist /etc/libuser.conf
blacklist /etc/libvirt
blacklist /etc/ld.so*
read-only /etc/kde
blacklist /etc/init*
blacklist /etc/incron*
blacklist /etc/resolv.conf
blacklist /etc/host*
blacklist /etc/gshadow*
blacklist /etc/fstab*
blacklist /etc/freshclam*
blacklist /etc/dracut*
read-only /etc/Dir_COLORS*
blacklist /etc/dhcp*
read-only /etc/cups
blacklist /etc/crypttab*
blacklist /etc/cron*
blacklist /etc/csh*
blacklist /etc/cvs*
blacklist /etc/cpu*
blacklist /etc/conntrackd.conf
blacklist /etc/color*
blacklist /etc/cloud
blacklist /etc/clam*
blacklist /etc/chrony*
blacklist /etc/chilli*
read-only /etc/bash*
blacklist /etc/at
blacklist /etc/asound*
blacklist /etc/aide*
# General startup files
read-only DOLLAR{HOME}/.xinitrc
read-only DOLLAR{HOME}/.xserverrc
read-only DOLLAR{HOME}/.profile
# Shell startup files
read-only DOLLAR{HOME}/.antigen
read-only DOLLAR{HOME}/.bash_login
read-only DOLLAR{HOME}/.bashrc
read-only DOLLAR{HOME}/.bash_profile
read-only DOLLAR{HOME}/.bash_logout
read-only DOLLAR{HOME}/.zsh.d
read-only DOLLAR{HOME}/.zshenv
read-only DOLLAR{HOME}/.zshrc
read-only DOLLAR{HOME}/.zshrc.local
read-only DOLLAR{HOME}/.zlogin
read-only DOLLAR{HOME}/.zprofile
read-only DOLLAR{HOME}/.zlogout
read-only DOLLAR{HOME}/.zsh_files
read-only DOLLAR{HOME}/.tcshrc
read-only DOLLAR{HOME}/.cshrc
read-only DOLLAR{HOME}/.csh_files
read-only DOLLAR{HOME}/.profile
read-only DOLLAR{HOME}/.gnugp*
read-only DOLLAR{HOME}/gnupg
# Initialization files that allow arbitrary command execution
read-only DOLLAR{HOME}/.caffrc
read-only DOLLAR{HOME}/.dotfiles
read-only DOLLAR{HOME}/dotfiles
read-only DOLLAR{HOME}/.mailcap
read-only DOLLAR{HOME}/.exrc
read-only DOLLAR{HOME}/_exrc
read-only DOLLAR{HOME}/.vimrc
read-only DOLLAR{HOME}/_vimrc
read-only DOLLAR{HOME}/.gvimrc
read-only DOLLAR{HOME}/_gvimrc
read-only DOLLAR{HOME}/.vim
read-only DOLLAR{HOME}/.emacs
read-only DOLLAR{HOME}/.emacs.d
read-only DOLLAR{HOME}/.nano
read-only DOLLAR{HOME}/.tmux.conf
read-only DOLLAR{HOME}/.iscreenrc
read-only DOLLAR{HOME}/.muttrc
read-only DOLLAR{HOME}/.mutt/muttrc
read-only DOLLAR{HOME}/.msmtprc
read-only DOLLAR{HOME}/.reportbugrc
read-only DOLLAR{HOME}/.xmonad
read-only DOLLAR{HOME}/.xscreensaver
read-only /etc/X11
# The user ~/bin directory can override commands such as ls
read-only DOLLAR{HOME}/bin
# top user
blacklist DOLLAR{HOME}/.ssh
blacklist DOLLAR{HOME}/.cert
blacklist DOLLAR{HOME}/.gnome2/keyrings
blacklist DOLLAR{HOME}/.kde4/share/apps/kwallet
blacklist DOLLAR{HOME}/.kde/share/apps/kwallet
blacklist DOLLAR{HOME}/.local/share/kwalletd
blacklist DOLLAR{HOME}/.config/keybase
blacklist DOLLAR{HOME}/.netrc
blacklist DOLLAR{HOME}/.gnupg
blacklist DOLLAR{HOME}/.caff
blacklist DOLLAR{HOME}/.smbcredentials
blacklist DOLLAR{HOME}/*.kdbx
blacklist DOLLAR{HOME}/*.kdb
blacklist DOLLAR{HOME}/*.key
blacklist DOLLAR{HOME}/.muttrc
blacklist DOLLAR{HOME}/.mutt/muttrc
blacklist DOLLAR{HOME}/.msmtprc
blacklist /home/surfuser/.gnupg
blacklist /etc/shadow
blacklist /etc/gshadow
# blacklist /etc/passwd
blacklist /etc/passwd-
blacklist /etc/group-
blacklist /etc/shadow-
blacklist /etc/gshadow-
blacklist /etc/passwd+
blacklist /etc/group+
blacklist /etc/shadow+
blacklist /etc/gshadow+
blacklist /etc/ssh
blacklist /var/backup
# system management
blacklist DOLLAR{PATH}/umount
blacklist DOLLAR{PATH}/mount
blacklist DOLLAR{PATH}/fusermount
blacklist DOLLAR{PATH}/su
blacklist DOLLAR{PATH}/sudo
blacklist DOLLAR{PATH}/xinput
blacklist DOLLAR{PATH}/evtest
blacklist DOLLAR{PATH}/xev
blacklist DOLLAR{PATH}/strace
blacklist DOLLAR{PATH}/nc
blacklist DOLLAR{PATH}/ncat
# system directories
blacklist /sbin
blacklist /usr/sbin
blacklist /usr/local/sbin
# prevent lxterminal connecting to an existing lxterminal session
blacklist /tmp/.lxterminal-socket*
# disable terminals running as server resulting in sandbox escape
blacklist DOLLAR{PATH}/gnome-terminal
blacklist DOLLAR{PATH}/gnome-terminal.wrapper
blacklist DOLLAR{PATH}/xfce4-terminal
blacklist DOLLAR{PATH}/xfce4-terminal.wrapper
blacklist DOLLAR{PATH}/mate-terminal
blacklist DOLLAR{PATH}/mate-terminal.wrapper
blacklist DOLLAR{PATH}/lilyterm
blacklist DOLLAR{PATH}/pantheon-terminal
blacklist DOLLAR{PATH}/roxterm
blacklist DOLLAR{PATH}/roxterm-config
blacklist DOLLAR{PATH}/terminix
blacklist DOLLAR{PATH}/urxvtc
blacklist DOLLAR{PATH}/urxvtcd
blacklist DOLLAR{PATH}/xterm
blacklist DOLLAR{PATH}/konsole
blacklist DOLLAR{PATH}/rxvt
blacklist DOLLAR{PATH}/lxterminal
read-only /etc/firejail
blacklist /usr/bin/ssh*
blacklist /usr/bin/rlogin*
blacklist DOLLAR{HOME}/.gftp/cache
blacklist DOLLAR{HOME}/Dokumente
blacklist DOLLAR{HOME}/Video
blacklist DOLLAR{HOME}/Bilder
blacklist DOLLAR{HOME}/Audio
blacklist DOLLAR{HOME}/Texte
Now start Pale Moon (similar Firefox with default.profile instead of palemoon.profile):
| knemo && sg surgruppe "unshare firejail --nice=19 --profile=/etc/firejail/palemoon.profile /usr/lib64/palemoon/palemoon --no-remote &" && sg surfgruppe "tor -f /etc/tor/torrc&quto; && export RESOLV_HOST_CONF="/etc/hosts" |
It is possible to enter this command-line into a startup under "command." to start Pale Moon by one mouseclick only.
Small disadvantage: Process firejail for the browser has to be killed, before any package-installations are possible. Generally all processed started by the user surfuser can be terminated through the command
"killall -u surfuser", as dnsmasq might run under surfuser at least by the command "killall firejail" from time to time, before too many firejail are running, so that all still running firejail-processes terminate. It is recommended to create a small entry with user root in the K-Menu and/or the same entry for the task line.
 General chroot and suid paranoia General chroot and suid paranoia
chroot is one of the most powerful possibilities to restrict a daemon or a user or another service. Just imagine a jail around your target, which the target cannot escape from (normally, but there are still a lot of conditions that allow one to escape out of such a jail). You can eventually create a modified root environment for the user or service you do not trust. This can use quite a bit of disk space as you need to copy all needed executables, as well as libraries, into the jail. But then, even if the user does something malicious, the scope of the damage is limited to the jail.
Many services running as daemons could benefit from this sort of arrangement. The daemons that you install with your Debian distribution will not come, however, chrooted per default.
This includes: name servers (such as bind), web servers (such as apache), mail servers (such as sendmail) and ftp servers (such as wu-ftpd). It is probably fair to say that the complexity of BIND is the reason why it has been exposed to a lot of attacks in recent years (see Securing BIND, Section 5.7).
However, Debian does provide some software that can help set up chroot environments. See Making chrooted environments automatically (depicted in the following).
Anyway, if you run any service on your system, you should consider running them as secure as possible. This includes: revoking root privileges, running in a restricted environment (such as a chroot jail) or replacing them with a more secure equivalent.
However, be forewarned that a chroot jail can be broken if the user running in it is the superuser. So, you need to make the service run as a non-privileged user. By limiting its environment you are limiting the world readable/executable files the service can access, thus, you limit the possibilities of a privilege escalation by use of local system security vulnerabilities. Even in this situation you cannot be completely sure that there is no way for a clever attacker to somehow break out of the jail. Using only server programs which have a reputation for being secure is a good additional safety measure. Even minuscule holes like open file handles can be used by a skilled attacker for breaking into the system. After all, chroot was not designed as a security tool but as a testing tool.
Making chrooted environments automatically
There are several programs to chroot automatically servers and services. Debian currently (accepted in May 2002) provides Wietse Venema´s chrootuid in the chrootuid package, as well as compartment and makejail. These programs can be used to set up a restricted environment for executing any program (chrootuid enables you to even run it as a restricted user).
Some of these tools can be used to set up the chroot environment easily. The makejail program for example, can create and update a chroot jail with short configuration files (it provides sample configuration files for bind, apache, postgresql and mysql). It attempts to guess and install into the jail all files required by the daemon using strace, stat and Debian´s package dependencies. More information at http://www.floc.net/makejail/. Jailer is a similar tool which can be retrieved from http://www.balabit.hu/downloads/jailer/ and is also available as a Debian package.
https://www.debian.org/doc/manuals/securing-debian-howto/ch-sec-services.en.html#s-chroot
But back to our text about LINFW3: Notice, that the NEW-LINE-BLOCK-only of Linfw3 prevents form all hacker except on established connections opened by the surfer, but not from any backdoors resp. trojans! Always try to use the NEW-LINE-BLOCK with the UID-( and/or GID-)owner-concept for surfuser and surfgroup together with the port-concept, while updates can be performed in the same way by root as the surfuser (and/or surfgroup)! Both, ALLOW-ROOT_LOGIN and ROOT_LOGIN shall be set to "no" and all access-rights upon directories and files set adequately. The computer-system will almost get serious hard hacked, if all this is not regarded!
mouseclick-fast work with the computer also has no chance to take into negative effect by following the methods of our excurs. For an always good and fast mount and umount of the USB-stick, actualize the filesystems to reisferfsprogs-3.6.24, e2fsprogs (1.43.2 from September 2016) resp. btrfs and manage the integration of the module usb_storage by modprobe. This module guarantees the fast secure mount and secure unmount of usb-media. To integrate it permanently for mdv2010 and other Linux, type into file /etc/modprobe.preload. If command chattr should keep its function instead, do not update the filesystem for loosing some kind of "id for owner-rights" But in this case, not much gets restricted, if chattr was not used before.
Our extra security-tip: Always click onto networkmanager-applet´s (el6), "exit" after the first dial-in into resp. after building up the first connection to the internet!
MAC Tomoyo profiles: /etc/tomoyo/*, kernel-boot-options security=tomoyo tomoyo=1.
 # apparmor: application MAC-protection-shield and MAC-kernel-security-module to load within /boot/grub/menu.lst (grub1) by option security=apparmor apparmor=1
# apparmor: application MAC-protection-shield and MAC-kernel-security-module to load within /boot/grub/menu.lst (grub1) by option security=apparmor apparmor=1
# dbus-apparmor&# within /etc/rc.local
# /usr/lib64/apparmorapplet&# /etc/rc.local
# example: apparmor_parser -af /etc/apparmor/profiles/extras/usr.lib.firefox.firefox &&/usr/bin/firefox # ( resp., still in order not to resign from firejail as introduced: ...&&sg surfgroup "firejail --profile=/etc/firejail/firefox-esr.profile /usr/bin/firefox" )
# /etc/apparmor/profiles/extras/* :
885 23. Jul 15:03 bin.netstat
1247 23. Jul 15:03 etc.cron.daily.logrotate
955 23. Jul 15:03 etc.cron.daily.slocate.cron
729 23. Jul 15:03 etc.cron.daily.tmpwatch
1733 23. Jul 15:03 README
1934 23. Jul 15:03 sbin.dhclient
1297 23. Jul 15:03 sbin.dhcpcd
682 23. Jul 15:03 sbin.portmap
855 23. Jul 15:03 sbin.resmgrd
489 23. Jul 15:03 sbin.rpc.lockd
1010 23. Jul 15:03 sbin.rpc.statd
1655 23. Jul 15:03 usr.bin.acroread
791 23. Jul 15:03 usr.bin.apropos
4569 23. Jul 15:03 usr.bin.evolution-2.10
697 23. Jul 15:03 usr.bin.fam
750 23. Jul 15:03 usr.bin.freshclam
1918 23. Jul 15:03 usr.bin.gaim
595 23. Jul 15:03 usr.bin.man
618 23. Jul 15:03 usr.bin.mlmmj-bounce
1041 23. Jul 15:03 usr.bin.mlmmj-maintd
1096 23. Jul 15:03 usr.bin.mlmmj-make-ml.sh
884 23. Jul 15:03 usr.bin.mlmmj-process
587 23. Jul 15:03 usr.bin.mlmmj-recieve
766 23. Jul 15:03 usr.bin.mlmmj-send
821 23. Jul 15:03 usr.bin.mlmmj-sub
803 23. Jul 15:03 usr.bin.mlmmj-unsub
2017 23. Jul 15:03 usr.bin.opera
1003 23. Jul 15:03 usr.bin.passwd
1025 23. Jul 15:03 usr.bin.procmail
1132 23. Jul 15:03 usr.bin.skype
580 23. Jul 15:03 usr.bin.spamc
904 23. Jul 15:03 usr.bin.svnserve
1185 23. Jul 15:03 usr.bin.wireshark
674 23. Jul 15:03 usr.bin.xfs
1022 23. Jul 15:03 usr.lib64.GConf.2.gconfd-2
857 23. Jul 15:03 usr.lib.bonobo.bonobo-activation-server
1258 23. Jul 15:03 usr.lib.evolution-data-server.evolution-data-server-1.10
1604 23. Jul 15:03 usr.lib.firefox.firefox
386 23. Jul 15:03 usr.lib.firefox.firefox.sh
654 23. Jul 15:03 usr.lib.firefox.mozilla-xremote-client
1018 23. Jul 15:03 usr.lib.GConf.2.gconfd-2
1230 23. Jul 15:03 usr.lib.man-db.man
889 23. Jul 15:03 usr.lib.postfix.anvil
2101 23. Jul 15:03 usr.lib.postfix.bounce
1269 23. Jul 15:03 usr.lib.postfix.cleanup
530 23. Jul 15:03 usr.lib.postfix.discard
626 23. Jul 15:03 usr.lib.postfix.error
1701 23. Jul 15:03 usr.lib.postfix.flush
624 23. Jul 15:03 usr.lib.postfix.lmtp
1839 23. Jul 15:03 usr.lib.postfix.local
1887 23. Jul 15:03 usr.lib.postfix.master
2443 23. Jul 15:03 usr.lib.postfix.nqmgr
607 23. Jul 15:03 usr.lib.postfix.oqmgr
859 23. Jul 15:03 usr.lib.postfix.pickup
497 23. Jul 15:03 usr.lib.postfix.pipe
709 23. Jul 15:03 usr.lib.postfix.proxymap
2464 23. Jul 15:03 usr.lib.postfix.qmgr
626 23. Jul 15:03 usr.lib.postfix.qmqpd
670 23. Jul 15:03 usr.lib.postfix.scache
2260 23. Jul 15:03 usr.lib.postfix.showq
1842 23. Jul 15:03 usr.lib.postfix.smtp
2120 23. Jul 15:03 usr.lib.postfix.smtpd
626 23. Jul 15:03 usr.lib.postfix.spawn
791 23. Jul 15:03 usr.lib.postfix.tlsmgr
904 23. Jul 15:03 usr.lib.postfix.trivial-rewrite
628 23. Jul 15:03 usr.lib.postfix.verify
788 23. Jul 15:03 usr.lib.postfix.virtual
1339 23. Jul 15:03 usr.lib.RealPlayer10.realplay
1074 23. Jul 15:03 usr.NX.bin.nxclient
1120 23. Jul 15:03 usr.sbin.cupsd
864 23. Jul 15:03 usr.sbin.dhcpd
6148 23. Jul 15:03 usr.sbin.httpd2-prefork
818 23. Jul 15:03 usr.sbin.imapd
652 23. Jul 15:03 usr.sbin.in.fingerd
1279 23. Jul 15:03 usr.sbin.in.ftpd
590 23. Jul 15:03 usr.sbin.in.ntalkd
825 23. Jul 15:03 usr.sbin.ipop2d
825 23. Jul 15:03 usr.sbin.ipop3d
1365 23. Jul 15:03 usr.sbin.lighttpd
756 23. Jul 15:03 usr.sbin.mysqld
920 23. Jul 15:03 usr.sbin.nmbd
830 23. Jul 15:03 usr.sbin.oidentd
735 23. Jul 15:03 usr.sbin.popper
1331 23. Jul 15:03 usr.sbin.postalias
1017 23. Jul 15:03 usr.sbin.postdrop
829 23. Jul 15:03 usr.sbin.postmap
1091 23. Jul 15:03 usr.sbin.postqueue
3435 23. Jul 15:03 usr.sbin.sendmail
2061 23. Jul 15:03 usr.sbin.sendmail.postfix
1564 23. Jul 15:03 usr.sbin.sendmail.sendmail
946 25. Mai 2012 usr.sbin.slapd
1140 23. Jul 15:03 usr.sbin.smbd
1068 23. Jul 15:03 usr.sbin.spamd
1686 23. Jul 15:03 usr.sbin.squid
3691 23. Jul 15:03 usr.sbin.sshd
1310 23. Jul 15:03 usr.sbin.useradd
1344 23. Jul 15:03 usr.sbin.userdel
1073 23. Jul 15:03 usr.sbin.vsftpd
2413 23. Jul 15:03 usr.sbin.xinetd
We never got any delays during the secure umount of USB-sticks anymore.
mdv2010 mouseclick-fast: Linux runs faster than Windows: mouseclick-fast mdv2010 on SSD. The code of Linux seems to be architectured and optimized well. Nevertheless even Linux can run slow too. Before we ask us, how this can happen and which software to install, we are interested in cpu and RAM killing daemons to deinstall resp. remove from harddisc. That are processes running in the background, for what we need a good process-manager indicating resource-consumption in percent. Therefore we have to start programs like ptree, "ps -All", Systemüberwachung or just by pressing the keys "ESC" and "STRG". In our case packagekit with an enormous consumption of around always 40% was found out to install him for el6, same for nspluginwrapper, leading us to set chmod 000 /usr/bin/nspluginscan. Think about kio_thumbnail, that gets started sometimes for creating symbols within the filemanager for certain files, in dolphin depending on the configuration for preview. The capacities reducing process named "prelinking" should almost be tolerated instead:
"prelink is a program that modifies ELF shared libraries and ELF dynamically linked binaries in such a way, that the time needed for the dynamic linker to perform relocations at startup significantly decreases. Due to fewer relocations, the run-time memory consumption decreases as well (especially the number of unshareable pages). The prelinking information is only used at startup time if none of the dependent libraries have changed since prelinking; otherwise programs are relocated normally."
Depending on configuration in MCC-security, msec_find checks periodically, during the boot or never. In MCC, security, periodical checks you can set many msec-checks from daily to weekly, even better to "manual", if your mainboard does not have more than one #SMP (CPU). After surfing as surfuser or other communications within the net, all processes started by surfuser should be killed again: killall -u surfuser. See our data-sheed: With our decision for mdv2010 and a SSD this aim got reached once more. Also beware the recommended frequency for the RAM-Modules mentioned in the manual the mainboard not to plug in one of a lower frequency. Then all went mouseclick fast already by the mainboard model DDR2 533 Mhz (or higher) 19W, that is recommended in the data sheed below. We already got 533Mhz-nonames assembled in Germany - for free before ... working fine (in spite of DDR2 Kingston 1GB 333 Mhz)! Do not forget: The computer-system with SSD is running once more mouseclick fast, if hdparm (omv2015, rosa2014.1, el7, el6) and sdparm (omv2015, rosa2014.1, el7, el6) is installed.
| SSD resp. HDD capacity used <=80% |
Boot-problems, do you have any problems during the booting? Just press the key for "i" for the interactive mode past the short message with udev. Now, by dialogs, it is possible to start each process manually or to resign from a process during the booting. On problems with the X-Server (graphic-card driver), start all processes except the display manager named "dm". On runlevel four less then five the terminal helps to enter all kind of commands to do the next things (like reinstalling the device driver or downgrading the X-Server from mdv2010.2 to mdv2010.0 by rpm again).
Be careful with the installation of further kernel, as some links in /boot (boot-partition) can mismatch refering to the settings in /boot/grub/menu.lst. Then you have to relink them by ";ln -sf TARGET linkfile" by booting with a repair-CD, a repair-USB-stick or a backuped, mirrored media (we do recommend anyway), in order to mount the boot-partition.
SSD-harddiscs are even better than the manufacturer do specify
publised article from 18. Juni 2014, 08:38 from admin, http://www.ahrens.de/ssd-festplatten-sind-noch-besser-als-die-hersteller-angeben/24906
SSDs are the better replacement for magnetic harddrives, for there do not consist of any mobile parts and hence they are up to 100 × faster during reads and 20 × durings writes and they seemed to be work quit endless. Test show, that they do not only work superfast, but also endure ten times longer as their manunfacturer promise. You can read the explicit test report on Golem.
Online update sources: http://fr2.rpmfind.net (FTP-downloads, here for el6, el7, mdv and mga) and http//pkgs.org (http-downloads for el6, el7, fc down to fc xx, mga down to mga xx), http://rpm.pbone.net/ (http- and ftp-downloads, el6, el7, all popular distros and versions)
The many security-checks within MCC, especially sectools, should be set from "daily", "monthly" and so on to "manually", in order to prevent irritating backgroud-processes.
MCC gives the opportunity in Network->,Network-Center to enable and disable tcp-timestamp, tcp-windows-scaling and dynamic IPv6. IPv6 uses static IP, so latter disabling is recommended.
29. October 2014, 08:49 Uhr, heise open
"The CentOS-team has released Version 6.6 of their Linux-distribution. It sources in Red Hat Enterprise Linux (RHEL) with the same version number Red Hat published two weeks ago. Therefore the new CentOS includes all improvements, under it a plenty of new and actualized driver, a device-mapper-target for the mount of a SSD as a cache for slow storage-media and the intergration of the High Performance Networking (HPN) that was costly up to now. You can get CentOS for free. It promises compatiblity to many distributions and is going to be fostered for a long time. Therefore the already some years old CentOS 6 can be updated by security updates until the 30 of november 2026. Scientificlinux alias CentOS 6.7 is the second clone of RHEL 6.6, for Oracle has released the also cloned from this Oracle Linux 6.6 some days ago."
We found many packages by name already in SuSE 7.3 from year 2003 and Mandrake mdk10.0 from year 2004. The code of their includes must be read out well and better each day. Actual Gentoo-GLSA provides one of the best overview of updates for Linux: https://security.gentoo.org/glsa/, descended ordered by time. Typical cases for updates refer to arbitrary code execution, multiple vulnerabilities (especially buffer overflow), denial of service and information disclosure.In order to make the installation of listed updates possible, glibc has to be actualized. Not all updates from the listed ones like cpio should be installed, while those for tar, bzip, freetype rpm, openssl (tarball) and many other ones do function. Try the belonging tarballs or downgrade again, if not. Notice, that updates provided for the distribution, except named exceptions below, are almost sufficient, for mdv2010.1 and mdv2010.2 you can find them on ftp://fr2.rpmfind.net/linux/Mandriva/official/2010.1/x86_64/media/contrib/updates. fr2.rpmfind.net is a good installation and update source for most linux distribution except Debian (with its own deb-packages). Before a computer system gets updated, it always should be secured completely! For detailed troubleshooting, cases we did not have with mdv2010, sources out of the internet and newsgroup alt.linux.suse might be helpfuf too.
Linux permanently gets functional extended and therefore also the applications and libraries. Packet-Versions change as the distribution its version (by their own version-numbers) do. In order to make a distribution error-free like in our example mdv2010, use a linux-friendly mainboard and install only those packets (and tarballs), that are belonging to the same installed version of a most complex distribution past 2003. In our example they are always ending with "...mdv2010". Pakets of next higher versions like mdv2011 should interest only after upgrading the glibc adequately or experimental. Nevertheless, also think of all the updates referring to the same distribution and its version, marked by name ending with "...version[distributionversion).update-number". To find such packages, take the installation-DVD/CD and make queries for rpmfind.net resp. mirror fr2.rpmfind.net. There, in the resulting listings, all packages are named explicitly in that way, that means by belonging distribution and version, but this might be the exception For mdv2010 a kernel-upgrade to mdv2012 by rpm-packages is possible. We do not recommend to change the distribution from mandriva to any other except many packages from Scientificlinux resp. ALT Linux resp. CentOS 6.7.
Does mdv2010 meet Fedora, actual fc23? Although mdv2010.1 and especially 2010.2 do not need any updates, you can upgrade mdv2010 to any actual linux, by installing the downward compatible C-standard-library glibc of rosa2014.1, mdv2012 or mga3 without rpm glibc itself out of glib2.0-common (fastest: actual pateched el6 or the sixtimes patched one from rosa2014.1 or mga3), glibc (el8, pclos, mga7, mga5, rosa2014.1), glibc-utils (el8, mga7, mga5, el6, rosa2014.1 or mga3), glibc-headers (el8), glibc-common (el8), glibc-utils (el8), glibc-all-langpacks (el8) glibc-profile (mga7, mga5, rosa2014.1 or mga3), glibc-static (el6) or glibc-static-devel (rosa2014.1, mga3), glibc-devel (rosa2014.1 or mga3), glibc-i18ndata (mga7, mga5, rosa2014.1 or mga3), glibc_lsb (mga3), libc6, mm-common (mga3), lib64glimm2 (mdv2010), gettext (rosa2014.1 or mga3), lib64gettext-misc (rosa2014.1), lib64gettextpo0 (rosa2014.1), lib64intl8 (rosa2014.1), lib64png16 (rosa2014.1), glib-networking (el6), lib64nspr4, lib64nss3, locales (rosa2014.1 or mga3), locales-en, locales-de, locales-fr, locales.jp and further more locales and the C++-standard-library stdcc++, all for x86_64 and i586, by ";rpm -U --force --nodeps". For glibc DO NOT INSTALL MORE mga3 OR mdv2012 than the listed ones! Now the hugh gate to any ultimative-mouseclick-fast working linux world on SSD, even actual linux like today´s Fedora core 24, has opened for largest amount of software ever (even if not all of it)! You can upgrade and downgrade like by "elevators" reaching floors of distros and versions provided by listings from fr2.rpmfind.net. Warning: This does not function with all glibc without needing many other packages! You do not need them anymore. We repeat that software should do its function, while the rest is almost made secure by our excurs. After that we might install an actual version of the filesytem like e2fsprogs (1.43.2), reiserfsprogs (omv2015, mdv2011 or el7, el6), btrfsprogs and many updates recommended by Gentoo-GLSA, url see below. At last for our Linux-tuning, following the new filesystem-rpm, copy all files of /lib to /usr/lib, /lib64/* to /usr/lib64, /bin/* to /usr/bin, /sbin/* to /usr/sbin. After all the operations upon glibc, Linux is not able to run faster in future.
glibc (el8, pclos, mga7, mga5, rosa, mga3, mdv2012) complete for x86_64 (64 bit cpu), analogous i586 (32 bit), without making any problems: glibc (mga7, mga5), glibc-headers (el8), glibc-common (el8), glibc-utils (el8), glibc-all-langpacks (el8), glibc-devel, libc6, glibc-i18ndata (mga7, mga5), glibc-profile (mga7, mga5), glibc-utils (mga7, mga5), glibc_lsb, gettext, locales, locales-en, locales-de, ..., gettext-base, lib64gettext-misc, lib64gettext-po0, lib64intl8, lib64png16, glib-gettextsize, glib-networking, glib2.0-common, lib64gio2, lib64glib-networking, lib64glib2.0, lib64glib2.0-devel, lib64glibmm2, lib64gmodule2, lib64gobject2, lib64ffi6, lib64gthread2, lib64stdc++, lib64QtGlib2.0, lib64packagekit-glib2 and prelink or glib2 (el7 or el6 instead of lib64gthread2 (rosa2014.1), lib64gio2 (rosa2014.1) and lib64gobject2 (rosa2014.1), we installed this one for this is el6 )
In order to avoid error-messages of glibc (el8) during system-boot, just remove the line LC_TIME=de_DE.UTF-8 in /etc/sysconfig/i18n ! Eventually install locales (pclos, mga7, mga6), locales-en, locales-de, ... too.
We decided us for the following GNU C Standard Library glibc:
glibc (el8, pclos, mga7, mga5, rosa2014.1), glibc-headers (el8), glibc-common (el8), glibc-utils (el8), glibc-all-langpacks (el8), libc6 (rosa2014.1), compat-glibc (el6), glibc-common (el6), glibc-i18ndata (mga7, mga5, rosa2014.1), glibc-headers (el8, el6), glibc-static (el6), glibc-utils (mga7, mga5, el6), glibc-profile (mga7, mga5, rosa2014.1), glibc-glibc_lsb (rosa2014.1), locales (rosa2014.1), glib2 (el6), prelink (rosa2014.1), lib64stdc++ (fc, pclos, mga, rosa2014.1 und el6) oder auch alles mga7, mga5 oder rosa2014.1
Paket-manager drakrpm offers the option named like "store in cache" in the menu for the seldom cases, where dependencies of packages are not solved correctly. Whenever this happens, downloaded packages should be copied from /var/cache/urpmi/rpm resp. /var/cache/urpmi/partial to any secure place for reinstallaton.
Depending on the graphic-card-driver x11-driver-video-name, for our platform with name=intel choose the X11-Server for mdv2010.0 even before mdv2010.1 refering to all files beginning with x11-server by name. Library-packages have to be installed for the X-Server too that are quit unknown in this context for you. To go sure with the X11-server of mdv2010.1, install all library-packages (lib64....rpm) you need for the program-packages at first, before the installation of the X-Server of mdv2010.1 takes place. So one of the last packages to update are those for the X-Server of mdv2010.1!
Either a programm is working or it is not, that means, it does its introduced functions or it does not. In the first case updates are seldom needed!
Be careful with the installation of many el6-packages. Some can restrict the functionality of mdv2010 (el6, el7), for expample usermode can effect the call by mouseclick of MCC. So collect all previous installed rpm of mdv2010 in a directory for possible reinstallation needs.
For SMP#1 (mainboard with one CPU only), wallpaper´s fly mode of a wallpaper is not recommended.
Method for prevention: already mentioned encryption of the partitons of the harddrive, also from USB-media, at least the encryption of some certain files. You see by all the already red marked passages and text: Although we dare to talk about security for the computer and although all payed amounts and sums in conjunction with computer should be transfered back, of course it is never learnt out.
Data backup and restore
Always keep all installation-packets accessible. During installation phases, even mdv2010 can conflict in some unsolved of the quit infinite package-dependencies.Check out some programs, if the stell do start and run. If the shell or any program does not, use a terminal to start them in order to watch out error-messages as the cause (for packages) why not, in more serious cases use the prefix strace: "strace command-executable-file". If mdv is not booting correctly, the key "i" should be pressed to get into the interactive mode, where almost all should be started except the displaymanager dm.
You can save your SSD possibly forever! Not only two SSD or one more harddrive are needed, you also need a bootable USB-stick or Mindi or Mondo or a Knoppix from DVD resp. on a 250 MB sized partition to execute the command dd for the backup and restore of partitions.
Recommended (PCWelt, 08.08.2015) commands are rsync or fontend grsync, alternatively rdiff, all packages resp. commands are provided for mdv2010. For SSD, in order to save power, work reliable and abstract, we recommend one more SSD or a magnetic backup harddisk, where partitions have to be mirrored 1:1 by partiton manager, rsync its helpful frontend grsync, the command rdiff or special mirror-commands. Such commands full of options really do their best, even over SSH. But for local backups and restores, that means, if you ask us, we just prefer the simple command dd resp. safecopy, depictied below: unbeatbale! Although SSDs do not like dd very much by taking their time with it, dd always seems to reach its end at any time (dd works around 1 GiB per Minute refering to our SSD), or use dd-replacement safecopy, if not. Notice, that dd still does not provide any progress-bar. But do not believe in fairy tales as this certain country is known for, perfer dd, as for example neither the operating system nor oneself does know exactly, what all to backup, which partitions, directories and files, in order to pevent the worst one can happen: new installation, problems during restauration, file manipulation after hacker attacks with vandalism and/or data loss. So resign from so called backup-programs by backuping and restoring always 1:1-partitionwise with dd, here partition sda1 onto partition sdb1:
| dd if=/dev/sda1 of=/dev/sdb1 |
Use sdd instead of dd to see a progressbar.
With the reliable dd, your partitions get always restored, if damaged. Therefore never use any other backup-programs for your partitions, don´t be such fool ! It is dd always terminating fine, only not in the case, its environment got damaged, in our example Knoppix from an own partition from SSD resp. harddisc or DVD. Therefore keep the Knoppix-partition on all media, the backuped one and its backupening, beneath Knoppix on DVD and/or USB-Stick.
The only disadvantage of dd is, that dd does not show any progress bar.
If you want to be even more clever for making backups than even dd allows, use dcfldd. This el6-rpm works on mdv2010 like dd, but does show a progressbar. Some more extensions enable fexible-disc-wipes, an resume on error, the estimation of md5-checksums using additional options like "hash=md5" and "md5log=md5.txt" and splitting the output-files.
Although with dd all data backups managed well, even on SSD, it is warned against the use of this command for SSD. http://ubuntuwiki.de/files/ssd/grundlagen.html :
dd does fills unused and empty sectors and blocks with zero, so that the essential spare-area of SSD will not be free anymore. Even the for speed (access-times) important alignment becomes absurd.
The amount of write-operarations shortens its life-time.
Therefore the command cp and rsync are recommended.[...]
Clonezilla advantages in transferring only the non-empty blocks during the data-transfer.
Linux-Bot-Net, Heartbleed, Shellshock, glibc-Patch, Bad Cow, ... on the way to Zero Updates, zero Patches and zero Bugfixes
Following distribution offer updates for mdv2010: omv2015, mga, rosa2014, mdv, fc, el7 and el6.
In msec, set "allow-root-login" to "yes", during the updating processes, in order to guarantee the usage of bash-commands and the work with the package-manager rpm.
Make a 1:1-partitionswise backup on an extern media by reliable (even on encrypted partitions) working commands like dd from rescue-DVD or Linux on USB-stick, that can be used for restoring too.
One more aim of updating is to set "allow-root-login" again back to "no", to move all logfiles to shm- (RAM-) directory /tmp, to set the root-partition to "ro" (read-only) and to deactivate the journalling feature of linux-filesystems. This is performed at the very end of this section for reiserfs.
Many cases like bash with the so called Shellshock, glibc, Linux-botnets and openSSL and so on tell us about the of essentiality updates.
Security leak "Dirty Cow" within the Linux-kernel enpossibles prohibited extension of access rights: http://www.pro-linux.de/news/1/24096/sicherheitslücke-im-linux-kernel-ermöglicht-lokale-rechteausweitung.html. In this report apparmor is mentioned, that might generally help. Start apparmor in the background for example in /etc/rc.local by /usr/lib64/apparmorapplet&
This security-lack is known by kernel-developer for many years. Nevertheless, with linfw3 and msec level.secure configured as introduced, Dirty Cow becomes no risk, as an intrusion into the system is conditioned, regardless from patching the kernel or not.
Kernel 5.4.110 (PCLinuxOS2019) with mkinitrd (pclos, rosa, mga2), nash (pclos, rosa, mga2), dracut (mga6: version 044, el6: version 004 (leads into manual LUKS-password request even in the case of existing password-key-file!, mdv2011: version 008)) and glibc (el8, pclos, mga6) resp. kernel 2.6.39.4-5.1 (mdv2011) can be patched with patches from year 2011 up to date from http://repository.timesys.com/buildsources/k/kernel/kernel-2.6.39/. We made good experiences with this patched kernel.
Plenty of packages of mdv2010 resp. mdv2011 can be updated with CentOS 6, CentOS 7, Rosa2014.1 and Rosa2012, except KDE-Akonadi-Nepomuk for interal dependency (mdv2010: Version 4.4.5) and a few single packages. KDE can be updated completely.
KDE 4.4.5 includes many updates as mentioned by the report http://var-log.de/page/6/ from year 2008: "For the release of 4.2 the KDE-Team fixed thousand errors and builds in many new features missed in KDE 4.2. This beta release gives the oppurtunity to check last errors and bugs. The KDE Team has published a list with significant improvements in 4.2 Beta 2. Since the first beta less than four weeks ago, 1.665 new errors were found out and 2.243 ones got corrected. Sine the release of KDE 4.1.0 more than 10.000 errors wth a strong view upon the stability of KDE 4.2 were fixed Past KDE 4.2 many monthly updates are expected and finally, in summer 2009, KDE 4.3. Signficant improvements of Plasma and KWin, the KDE Workspace... ."
Our KDE solution: KDE as a mix out of kde 4.4.5/4.4.9 (mdv2010.2, November 2011), kde-4.3.4 (el6, actual patched up to year 2026) and kde (4.4.4, OpenSuSE 11.2, end of year 2013)
By mdv2010.0, mdv2010.1, mdv2010.2 and some mdv2011.0, most versions and releases of RPM-packages got fixed and patched well for functionality for around two years- similar to el6 and el7 from year 2010 to 2026. . All update-rpm listed below will lead into an up to year 2026 actual, well functioning Linux. Only the two up to five times patched KDE 4.4.5 (mdv2010.2) is not upgraded. You can keep it or try KDE (omv2015) or KDE of mandriva-successor Rosa2014.1 from pkgs.org for example. In the case of dependency-conflicts, dare to install by package-manager rpm with the option --force and --nodeps (analog Debian), if you keep the preceeding packages beneath you and if you care for the installation packages that are still required, listed by rpm during the installation-process.
Except for Browser, bash and OpenSSL, mdv2010 and Linfw3 make it possible: processes for net-connections (inclusive server resp. all daemons resp. services to activate explicilty) have to be started, build-up and therefore posessed only by the password-protected user "surfuser" belonging to group "surfgroup", while LINFW3 is blocking all other processes not started by surfuser, even those owned by root. The next thing, Linfw3 does, is opening only those ports belonging to such activated services. Furthermore it should be not allowed to chroot, while surfuser is not a member of any user and not any group except surfgroup. To login as root, a root-login should generally not be allowed by configuration (MCC, security settings), and a user must be a member of the group wheel, in order to login as root, what can reduce the time for different works without riscing to much, if LINFW3 protecting with UID-owner surfuser and GID-owner gets activated. Using MCC security an accessless root access can be configured for the command su. In the device-configuration-file /etc/fstab It is also possible, to set the option "noexec" each partition, especially for the partition including the files owned by the user "surfuser". Then the configuration of file-release within LAN and access-rights for directories and files can even prevent the reading of directories and files with sensible data ("chown non-surfuser; chmod 700"): the concept of UNIX-(file)systems! Its a remaining matter of communication-protocols themselves, that can be used (build-up) by the password-protected surfuser through belonging port-releases only. To be more careful than careful, move all sensilbe data to a one more encryted partition or an encrypted extern media, that should be plugged in or read again only the time, suspect services are not activated (when belonging connections are not build-up). This fact is described more in detail below in our section for LINFW3. You can even resign from many updates. But nevertheless, to go sure (over sure) as promised, we are going to describe, how mdv2010 can be kept uptodate almost by the until 2026 actualized Scientificlinux alias CentOS 6 resp 7.
Good luck: Unix/Linux always consists in main of the same software, kernel, grub/lilo, dracut, glibc, X11-Server, window- and desktop-manager like Gnome and KDE with konqueror and kpim out of kmail, knodes, clamav, firefox, OpenOffice and koffice, gimp and so on. In comparison with non OpenSource, this opensource is checked many times for it is read out well. Notice, that many new updates, patches and bugfixes listed in fr2.prmfind.net for mdv and GLSA Gentoo just rely on functionality extensions. Therefore, do not use them. They might not work!
Everything of mdv2010 will run fine and stable on your SSD, except the KDE leading to sink plasmoid Daisy, belonging to the plasmoids like such for the wheather-forecast for example, exchanging data with extern sources. You can always deinstall and deactivate such insecure behaving plasmoids. Although the upgrade of glibc to rosa2014.1, mga3 or higher widens the possibilities, mdv2010 bewares its sensibilities in the case of the installation of wrong packages, that can lead to serious hard system-breakdowns and hangups. Think like the MCC-packet-manager. Beware previous installed packages, until mdv2010 runs stable (reinstallation: rpm -U --force and/or --nodeps).
Have a look into the changelog of each packet. There you get to know about all modificiations by date and the name of the day of the week in descending order, the modification time, name resp. e-mail-adresse of each author (programmer), who has programmed the modification and a short description of the modification itself. It must be at last the publishing organisation, who has checked all this information out using tools like diff. Some updated resp. patched packages can be found out immediately by their high version release number (el6 and el7) like NetworkManager-xxxx-107 (el6), where 99 stands for the 99th release or in addition by the number after the point at the end of the version number (mdk, mdv, mga) like NetworkManager-xxxx-25.2, where "2" stands for the second patch of the version´s release. If the version number differs in the first ciphers, the package almost contains serious hard changes. If the version number differs in end-ciphers only from the already installed one, it gets more likely, that you can use this package for replacement. Right before the version number resp. the end of the package name the short name for the belonging distribution, followed by the kind of processor is named resp. the "noarch" in the case of independency from the processor type. A third person not named in the changelog and list of the packager names would have as much difficulties with the manipulation of the packets as cracking and hacking the computer with the rpm-command and the files on the storage media.
Filesystem, you have several opportunities: reiserfsprogs (omv2015, omv2014) or reiserfs-utils (fc23, el7, el6), e2fsprogs (1.43.2) with lib64ext2fs (rosa2014.1) without uClibc (omv2014, omv2015), uclibc-lib64ext2fs (omv2014, omv2015)
reiserfs-3.6.24-8.5 (OpenSuSE Factory) with libreiserfs, libreiserfs-progs and libreiserfscore0.
The harddrive (SSD) causes errors for some reiserfs-versions during the system boot and checks by reiserfsck. Therefore our choice consists of reiserfsprogs (omv2015) and e2fprogs (rosa2014.1) together with lib64ext2fs (rosa2014.1)- causing no errors anymore.
hdparm (omv2015, rosa2014.1, el7, el6) and sdparm (omv2015, rosa2014.1, el7, el6): adequate SSD-parameters within /etc/rc.local (hdparm -W1a0A0 /dev/sda) support our aim: all on SSD and mouseclick-fast! MCC, gparted and disk manager Palimpsest provides overview, some administration, benchmarks and partitioning.
Notice, that all package-dependencies have to be installed with one package. Otherwise this can cause a state similar to buffe-overrflows, where CPU and RAM seem to have lost their capacities quit working endless.
Next point: specific microcode-update for the CPU. For the mainboard we introduce in data-sheed, ucode-intel (OpenSuSE) and ucode-intel-blob (OpenSuSE) should be installed to follow our aim of mouseclick-fast PC-working.
All updates (since) mdv2007.0 and mdv2010 do regulary refer to, and this is the advantage of UNIX-Systems: buggish software (not much for mentioned mdv), all net-communication-programs like proxy (squid,...), MySQL, telephony, the browser (using ssl3.0 instead of tls as reported by three members of the Google-Team, that means all firefox up to an actual resp. TLS-using version 34 ( unpacking an easy by menu updateable, actual firefox into a directory like /usr/lib64/firefox and choosing "Update Firefox" out of the menu (same for Thunderbird into /usr/lib64/thunderbird), updating firefox in detail, see our section updating firefox. Such
How to block scripts and ads with an ad- resp. script-blocker like konqueror-adblock.so and adblockplus is much more simple than presented by their typical large resource-killing blocking-lists full of pregiven exceptions:
At first all blocking-scripts like easylist have to be removed out of AdblockPlus resp. other adblocker. Many of them contain exceptions. The special convenience for (more) exceptions has to be deactivated too by clicking upon the hook, so that the hook does not appear anymore.
Now, like firewall linfw3, the "trusted"-strategy, "forbidden is, what is not (explicitly) allowed" should be followed.
Therefore the only existant private ad- resp. scriptfilter should just include the following entries:
@@*.css*
||*.js/*
||*.com/*
||*.net/*
||*.de/*
||*.pl/*
*
 or just the one single char for a star:
or just the one single char for a star:
*
for all, that could ever be blocked from a website!
That´s all ! It is not a bad idea to allow all stylesheets (css) by adding the one more entry @@*.css* right at the top of the filter list. Very brave ones risk webbugs (scripts with an image output) filtered out by other extensions and add @@*.jpg* , @@*.jpeg*, @@*.gif* and @@*.png* too, that can be allowed in ABP resp. ABL as exceptions each website loaded. Filter-lists from elsewhere like the up-to-date to keep EasyList with their many exceptions are not needed anymore! They just were nonsens, as no more entries are needed (eventually except some more top-sublevel-domains (country-codes) in addition to "*.de/*".
So a single char for the star apriori "*"does already do its very best!
Our final solution: Our complete ABP- resp. ABL-filter-list, especially at the very beginning, just has got the includes:
ABP (Firefox <= ESR 52.9.0):
 @@*.png* @@*.png*
@@*.css*
@@||*.gif*
@@||*.jpeg*
@@||*.jpg*
@@||*.svg*
*
*.js*
*.pl*
*
ABL (Pale Moon):
 @@*.png @@*.png
@@*.css
@@*.gif
@@*.jpeg
@@*.jpg
@@*.svg
*.js
*.pl
*
without any further entries and without any imported filter-lists (full of exceptions and superfluous rules) like EasyList.
Good luck: These few snake-speeded entries do not influence the surf-speed measurable much.
In order to make visible now, what should in your eyes be visible from a loaded website, EXCEPTION by exception should be added to the list almost using wildcards resp. regular expressions after the build-up of the side, until the hidden (blocked) parts get visible. At first, if the css-entry should be missing, think of all Stylesheets (css) to consider as exceptions, while especially most or all Javscript (.js) should still be blocked. To go sure, block *.js and *.pl beneath the general "*" from above in future (as already made in our list above). Enter exceptions for not shown images (if belonging exceptions from above should still be missing) by entries like https://.../*.jpg and https://.../*.png too.
After that, the webside should be loaded one more time (refresh) and JavaScript should be disabled again for the next certain time by "javascript.enabled false" passing "about:config". If the filters of ABP resp. ABL are set as recommended above, beware for Firefox-ESR (and, if you want, also Pale Moon) "javascript.enabled true" as all javascript is already filtered out. Listed extensions will really work fine, if set to true.
Do the same with Firefox-Extension RequestPolicyBlockedContinued just to be even more careful or to do it more additionally, as unknown Tracker already got blocked with their first appearance, until they get allowed by the user.
In the first configuration window set all three hooks, therewith new rules entered can be stored durable and not only temporary.
Next configuration window deals with the ruleset. Enter a new rule by electing "block" and entering a * (star) again into all fields for the new rule. Now the self-blockade of a webside (resp. server) has to be prevented by allowing the belonging rule just for the trusted server itself. If not, images and other objects might get blocked.
There are pregiven rules within the ruleset of RequestPolicyBlockContinued located in a directory far sub /home/surfuser/.mozilla/firefox/default-or-standard-profile with the some json-typed files like allow_functionality.json, allow_sameorg.json and so on, that can also be overworked, if you want..
The private mode can be deactivated by clicking upon settings in Firefox ESR, although this won´t be the truth, that means he won´t become really deactivated through using extension Private Tabs. Or take it the other way: activate the private mode and deactivate him by clicking upon the TAB to deactivate the private mode through Private TAB.
 Incognito-mode for the protection of the privacy during surfing, PC-WELT.de, 03.11.2019 Incognito-mode for the protection of the privacy during surfing, PC-WELT.de, 03.11.2019
Windows-10-Browser Edge as much as Google Chrome and Firefox offer a mode leaving no tracks during the surfuing on the PC behind. Howto use this mode in a reliable way:
Whenever you change into the private surf-mode, all during the visit of websites stored information like cookies, history protocols, web-cache, images and videos are deleted resp. removed past the closing of the browser.
This especially interests, if you are surfing with a foreign computer in the web, in order to avoid leaving any tracks behind you. But this is an advantage for your own PC too, as the deletion (removal) of your surf data at the end of each internet-session makes it more difficult for the owner resp. administrators of websites to create user profiles.
[...] Notice, that the private mode does not care for anonymity in the internet Your internet provider (ISP), the administrator of the router of communities or the net administrator in the net of a company is still enabled to evaluate the sites visisted, the links clicked and data transferred.
https://www.pcwelt.de/a/inkognito-modus-privatsphaere-beim-surfen-schuetzen,3450334
Did we mention it, didn´t you know? PHP- and Perl-scripts are interpreted always at first and serversided each website load, before the Javascript and HTML is interpreted client-sided (on the side of the surfer resp. user).
.
In the hope,.that user.js from KaiRaven and other authors is copied into the standard-profile-directory, that linfw3 and firejail got installed and configured, /etc/hosts from far below of this website is located and the DNS (in the priority local followed by remote and pdnsd) configured well, the surfing with Firefox ESR can right begin!
During the surfing, noscript and RequestBlockPolicyContinued have to be analyzed past the load of a website. It is your own, free choice to filter out or to pass listed scripts by. If a webseite requires cookies, they can be allowed by the CookieController.
All, that has to be done now after the configuration of listed extensions too, is to start the browser and to click upon the first and only appearing TAB to make it private (working in private mode).
Nevertheless what we have seen works on the base of "trusted" like linfw3 and openssl upon ssl-certificates and so on might do.
But AdblockPlus changed its layout in November 2017 making such configuration impossible. Try elder versions downloadable from fr2.rpmfind.net named mozilla-adblockplus-2.9.1-27 (fc28, fc27, el7, el6), noscript: mozilla-noscript (-5.1.8.6, 5.1.8.5, 5.1.7-1, fc28, fc27, el7, el6) or seamonkey-noscript (el6, 5.1.9-3, recommended noscript for ff-ESR-52.9.0; contains the xpi-installation-file), http://ftp.pbone.net/mirror/archive.fedoraproject.org/fedora/linux/updates/25/armhfp/Packages/m/mozilla-noscript-5.1.7-1.fc25.noarch.rpm.
Noscript, rpm mozilla-noscript (fc29, el7, el6) can enforce ssl-encryption (https) of addressed websites, by entering in a great text-input-field of register HTTPS:
*
Write exceptions below each other in the field below. Firefox-extension https.everywhere, rpm mozilla-https-everywhere (fc, el6 or mozilla.org), is not needed anymore.
The important Firefox-security-extension RequestPolicyBlockedContinued, rpm: mozilla-requestpolicy (-1.0-0.22.20171019git633302 fc29, el7, el6) might contain some pre-defined rules, but it also enables the adding of temporary as much as persistent new rules for user. They might be set generally under target and therefore not under start, using * for any port. You might want to set them for extern loaded fonts and google like *syndication*:*/*, *analytics*:*/*, *tagmanager*:*/*, *usercontent*.*:*, *google.*:*/* and other targets. Install this extension past ABP, but before noscript.
 Searchplugins (for integrated in search engines) of Firefox /usr/lib64/firefox/browser/searchplugins can be removed except one. If you remove all, the context menu might not build up completely, for example copy and paste of text and links might not function anymore. Searchplugins (for integrated in search engines) of Firefox /usr/lib64/firefox/browser/searchplugins can be removed except one. If you remove all, the context menu might not build up completely, for example copy and paste of text and links might not function anymore.
To go sure, remove the search-parameters within the remaining xml-searchplugin by a text-editor like nano.
 Browser-Fingerprinting: GPU-tracking is possible, trojaner-info.de, heise-online.de, 02.06.2022 Browser-Fingerprinting: GPU-tracking is possible, trojaner-info.de, heise-online.de, 02.06.2022
Browser-Tracking für Webseiten-Betreiber maßgeblich vereinfacht - Leistungscharakteristika einer Grafikeinheit sehr individuell
Auch ohne Tracking-Cookies können beim Browsen mittels Fingerprinting Computer, Notebooks, Smartphones sowie andere Geräte über längere Zeiträume identifiziert werden. Dass sich die Grafikeinheit in einem Gerät zur Nachverfolgung ausnutzen lässt, konnte ein Forschungsverbund aus australischen, israelischen und französischen Universitäten jetzt beweisen.
Über die bei Browsern gängige Grafik-API WebGL lässt die DrawnApart genannte Technik (Paper) kurzweilige Grafikberechnungen laufen. Dabei protokolliert sie per JavaScript Parameter, einen Großteil der Anzahl der Shader-Kerne, die Taktfrequenz und die benötigte Zeit zum Rendern. Die Berechnungen können wahlweise entweder für wenige Sekunden im Vordergrund oder für einen längeren Zeitraum im Hintergrund laufen.
Bisherige Identifizierungstechniken erweitert
Eigentlich identische Hardware lässt sich theoretisch auseinanderhalten, da die Halbleiterbauelemente einzigartig sind. Jede GPU hat nämlich eine eigene Kurve aus Spannung und Takt. Das Forschungsteam machte sich diese Leistungscharakteristika zu Nutze, um bestehende Browser-Fingerprinting-Techniken auszubauen. Bisherige lesen Hardware-Konfigurationen, Browser-Versionen und -Einstellungen aus. Geräte lassen sich nach Software-Updates und umgesteckter Hardware mit den DrawnApart-Daten besser identifizieren, sofern dieselbe GPU zum Einsatz kommt.
Über Monate wurde im Paper und dem Verbund mit DranwnApart einzeln wie gemeinsam auf mehr als 2.500 Geräten die Fingerabdruck-Technik FP Stalker getestet. Das Ergebnis: Die mittlere Tracking-Dauer stieg von 16 auf 30 Tage (+ 66,7 Prozent), wenn alle sechs Tage eine präparierte Webseite besucht wurde. Bei einem Intervall von sieben Tagen stieg die mittlere Tracking-Dauer von 17,5 auf 28 Tage (+ 60 Prozent). Weniger als die Hälfte der Browser-Instanzen ließen sich nach diesen Zeiträumen noch zuverlässig identifizieren.
Unternehmen wie Apple, Microsoft, Google und Mozilla entwickeln aktuell den potenziellen WebGL-Nachfolger WebGU, der neben Grafik- auch komplexe Compute-Shader ausführen kann. Das Forschungsteam ließ Mutex-Funktionen auf allen Shader-Gruppen einer GPU laufen und protokollierte, welche Shader-Gruppe wie schnell die Aufgabe erledigte. Die Dauer zur Identifizierung von etwa acht Sekunden verkürzte sich auf 150 Millisekunden. Und das bei einer Klassifikationsgenauigkeit von 98 Prozent. So plädiert das Forschungsteam dafür, bei der Entwicklung neuer Browser-APIs das Thema Privatsphäre in den Fokus zu rücken.
Quelle: heise online Redaktion
https://www.trojaner-info.de/mobile-security/aktuell/browser-fingerprinting-gpu-tracking-moeglich.html
 Incognito-Mode: Protecting the privacy during the surfing, PC-WELT.de, 06.04.2018 Incognito-Mode: Protecting the privacy during the surfing, PC-WELT.de, 06.04.2018
Windows-10-Browser Edge as well as Google Chrome and Firefox provide a mode keeping from tracking the PC.
[...] Firefox-users have to click upon the icon with the three horizontal bars right up in the menu to choose "private windows" or by pressing the keys STRG-P.
https://www.pcwelt.de/a/inkognito-modus-privatsphaere-beim-surfen-schuetzen,3450334
 Certifcates: Following permissions can be set to the values "Always-ask", "allow" and "block" for each website by clicking on the symbol for the lock and register "Permissions": Certifcates: Following permissions can be set to the values "Always-ask", "allow" and "block" for each website by clicking on the symbol for the lock and register "Permissions":
 Remove (quit) all URL resp. URI the browser (including Pale Moon and Tor-Browser) has stored and lists through about:config Remove (quit) all URL resp. URI the browser (including Pale Moon and Tor-Browser) has stored and lists through about:config
about:config -> type into the address-search-line http -> remove listed URL by clicking upon them and exchanging them through a blank (empty string).
Access Your Location
Intall Add-ons
Load Images
Maintain Offline Storage
Open Pop-up Window
Receive Notifications
Set Cookies
Share the Screen
Use the Camera
Use the Microphone
 Finally one should have read the report for the configuration of firefox-ESR by "about:config": Firefox-Tuning zur Absicherung und Anonymisierung, https://wiki.kairaven.de/open/app/firefox, to understand what we do next. (!!!) Finally one should have read the report for the configuration of firefox-ESR by "about:config": Firefox-Tuning zur Absicherung und Anonymisierung, https://wiki.kairaven.de/open/app/firefox, to understand what we do next. (!!!)
There the configuration of almost overwritten values out of about:config should happen through mozilla.cfg. But this does not work. The include of this file has to be taken over (copied) from mozilla.cfg (installation directory) into defaults/local-settings.js. Now the "forgotten" values are almost set in Firefox ESR.
All entries are listed in http://kb.mozillazine.org/About:config_Entries ´
/******************************************************************************
* /home/surfuser/.mozilla/firefox/your_default_profile_directory00-or-so/user.js *
* https://github.com/pyllyukko/user.js *
One more listing: https://www.ghacks.net/2015/08/18/a-comprehensive-list-of-
firefox-privacy-and-security-settings/
******************************************************************************/
// http://kb.mozillazine.org/User.js_file
//
// always enable mouseclick on links and formular text inputs:
// (user_pref("network.protocol_handler.expose_all", true)
//
//====================================================
// section TOR-BROWSER (ff-ESR) only
// ===================================================
// The meek-http-helper extension uses dump to write its listening port number
/// to stdout.
// user.js for Pale Moon and Firefox-ESR-52.9
// pale moon- and therefore also ff- extension SecretAgent for setting and changing user agents
user_pref("extensions.SecretAgent.StealthMode", true);
// enable javascript, so that ABP (fc29) of ff will work, but disable it for Pale Moon because of ABL. ABL works even, if disabled.
user_pref("javascript.enabled", true);
user_pref("browser.addon-watch.ignore", "");
// block images: 3: from third parties
user_pref("permissions.default.image", 3);
// Next one might block webbugs etc.:
user_pref("security.xcto_nosniff_block_images", true);
//
// disable ftp
user_pref("network.protocol-handler.external.ftp" true);
//
//Proxy: always use anonymizing Tor each ff-start
user_pref("network.http.proxy.pipelining", false);
// Settings won´ get stored, when using: user_pref("network.proxy.no_proxies_on", "");
user_pref("network.proxy.socks", "127.0.0.1");
user_pref("network.proxy.socks_port", 9050);
user_pref("network.proxy.type", 1);
// DNS for Tor: remote DNS lookup at first or local DNS lookup at first. We care especially for the case "false" in future in the excurs-section for DNS-Server
user_pref("network.proxy.socks_remote_dns", false);
// Erhöhung der Privatsphäre gegenüber Suchmaschinen: Wie bereits dargestellt übermittelt Firefox standardmäßig jeden einzelnen Buchstaben bzw. unsere Eingabe an eine
// Suchmaschine, ohne dass wir die Suchabfrage überhaupt abgesendet haben. Diese "Komfortfunktion" wird über die user.js deaktiviert. Wer die Funktion beibehalten möchte, der kann optional
// folgende drei Zeilen einfach entfernen:
// ## Disable location bar LIVE search suggestions
user_pref("browser.search.suggest.enabled", false);
user_pref("browser.urlbar.suggest.searches", false);
// some more settings
//
// Strict user.js: Die strenge user.js blockiert restriktiv vieles, was für Tracking sowie Sicherheit relevant sein könnte. Neben Trackinschutz sollen auch Möglichkeiten für Angriffe auf den Browser minimiert werden.
// Diese Einstellungen sind für Risikogruppen geeignet, die für höhere Sicherheit einige Einschränkungen in Kauf nehmen.
// Javascript Just-in-Time-Compiler sind aus Sicherheitsgründen deaktiviert, was die ausführung von Javascript auf einige Webseiten verlangsamt.
// Anzeige von PDF Dokumenten im Browser ist deaktiviert.
// SVG, Flash, WebGL und WebGL2 sind komplett deaktiviert.
// Auto-Play und Hardware Video Decoding sind deaktiviert.
// Closed Source Video Codecs werden nicht verwendet.
// Favicons werden nicht geladen und nicht gespeichert.
// Es werden keine Login Credentials gespeichert.
// Unverschlüsseltes HTTP und FTP sind abgeschaltet, nur HTTPS möglich.
// Push Services sind deaktiviert.
// Der Download von externen Schriftarten ist auch für Symbole deaktiviert. Um die resultierenden Einschränkungen etwas abzumildern, kann man häufig genutzte Webicon Fonts wie den Awesome Webicon Font lokal
// installieren. Linux Distributionen enthalten passende Pakete:
// Ubuntu: > sudo apt install fonts-font-awesome
// Fedora: > sudo dnf install fontawesome-fonts fontawesome-fonts-web
// https://privacy-handbuch.de/handbuch_21u.htm
user_pref("noscript.preset", "medium");
user_pref("media.video-queue.default-size", 0);
user_pref("status4evar.advanced.status.detectVideo", false);
user_pref("devtools.cache.disabled", false); // must be set to false, true might cause screen-flickering!
user_pref("devtools.browserconsole.filter.secerror", false);
user_pref("devtools.command-button-frames.enabled", false);
user_pref("devtools.command-button-responsive.enabled", false);
user_pref("devtools.command-buttion-splitconsole.enabled", false);
user_pref("media.gmp-manager.certs.2.commonName", "");
user_pref("media.gmp-manager.certs.1.commonName", "");
user_pref("gecko.handlerService.schemes.mailto.0.name", "");
user_pref("gecko.handlerService.schemes.mailto.1.name", "");
user_pref("general.useragent.compatMode.gecko", false);
user_pref("general.useragent.compatMode", 0);
user_pref("general.useragent.override.aol.com", "");
user_pref("general.useragent.override.netflximg.net", "");
user_pref("general.useragent.override.players.brightcove.net", "");
user_pref("general.useragent.override.deviantart.net", "");
user_pref("general.useragent.override.bing.com", "");
user_pref("general.useragent.override.calendar.yahoo.com", "");
user_pref("general.useragent.override.chase.com", "");
user_pref("general.useragent.override.citi.com", "");
user_pref("general.useragent.override.dailymotion.com", "");
user_pref("general.useragent.override.deviantart.com", "");
user_pref("general.useragent.override.dropbox.com", "");
user_pref("general.useragent.override.firefox.com", "");
user_pref("general.useragent.override.gaming.youtube.com", "" );
user_pref("general.useragent.override.github.com", "");
user_pref("general.useragent.override.google.com", "");
user_pref("general.useragent.override.googlevideos.com", "");
user_pref("general.useragent.override.gstatic.com", "");
user_pref("general.useragent.override.humblebundle.com", "");
user_pref("general.useragent.override.mozilla.com", "");
user_pref("general.useragent.override.msn.com", "");
user_pref("general.useragent.override.netflix.com", "");
user_pref("general.useragent.override.outlook.com", "");
user_pref("general.useragent.override.patientaccess.com", "");
user_pref("general.useragent.override.soundcloud.com", "");
user_pref("general.useragent.override.web.whatsapp.com", "");
user_pref("general.useragent.override.www.amazon.com", "");
user_pref("general.useragent.override.yahoo.com", "");
user_pref("general.useragent.override.yuku.com", "");
user_pref("general.useragent.override.addons.mozilla.org", "");
user_pref("general.useragent.override.altibox.dk", "");
user_pref("general.useragent.override.altibox.no", "");
user_pref("general.useragent.override.mozilla.org", "");
user_pref("general.useragent.override.netflximg.com", "");
user_pref("general.useragent.override.youtube.com", "");
user_pref("general.useragent.override.web.de", "");
user_pref("general.useragent.override.privat24.ua", "");
user_pref("general.useragent.override.players.brightcove", "");
user_pref("general.useragent.override.hitbox.tv", "");
user_pref("general.useragent.override.live.com", "");
user_pref("security.ssl.disable_session_identifiers", false);
user_pref("devtools.remote.wifi.scan", false);
user_pref("devtools.gcli.imgurClientID", "");
user_pref("devtools.remote.wifi.visible", false);
user_pref("browser.dom.window.dump.enabled", true);
//
// Enable (here disable) SPDY and HTTP/2 as they are in Firefox 38, for a matching ALPN extension.
// https://trac.torproject.org/projects/tor/ticket/15512
user_pref("network.http.spdy.enabled", false);
user_pref("network.http.spdy.enabled.http2", false);
user_pref("network.http.spdy.enabled.http2draft", false);
user_pref("network.http.spdy.enabled.v3-1", false);
user_pref("network.http.spdy.coalesce-hostnames", false);
//
// https://support.mozilla.org/en-US/questions/1043508
user_pref("dom.disable_beforeunload", true);
// Disable safe mode. In case of a crash, we Don´t want to prompt for a
// safe-mode browser that has extensions disabled.
// https://support.mozilla.org/en-US/questions/951221#answer-410562
user_pref("toolkit.startup.max_resumed_crashes", -1);
//==============================================
// end section TOR-BROWSER
//==============================================
// Set a failsafe blackhole proxy of 127.0.0.1:9, to prevent network interaction
// in case the user manages to open this profile with a normal browser UI (i.e.,
// not headless with the meek-http-helper extension running). Port 9 is
// "discard", so it should work as a blackhole whether the port is open or
// closed. network.proxy.type=1 means "Manual proxy configuration".
// http://kb.mozillazine.org/Network.proxy.type
user_pref("network.proxy.type", 1);
user_pref("network.proxy.socks", "127.0.0.1");
user_pref("network.proxy.socks_port", 9);
// Make sure DNS is also blackholed. network.proxy.socks_remote_dns is
// overridden by meek-http-helper at startup.
user_pref("canvas.capturestream.enabled", false);
user_pref("security.csp.experimentalEnabled", true);
user_pref("privacy.firstparty.isolate", true);
user_pref("privacy.popups.disable_from_plugins", 3);
user_pref("privacy.permissionPrompts.showCloseButton", true);
user_pref("privacy.popups.disable_from_plugins", 3);
user_pref("privacy.resistFingerprinting", true);
user_pref("security.data_uri.block_toplevel_data_uri_navigations", true);
user_pref("security.family_safety.mode", 0);
user_pref("social.directories", "");
user_pref("svg.disabled", true);
user_pref("extensions.enabledAddons", "meek-http-helper@bamsoftware.com:1.0");
user_pref("network.protocol-handler.expose.ftp", false);
user_pref("network.protocol-handler.external.ftp", false);
user_pref("image. animation_mode" "normal");
user_pref("update. interval", 0);
Determines when images should be loaded.
1 (default): Load all images
2: Do not load any images
3: Load images from same (originating) server only
Note: This preference was previously known as
user_pref("permissions.default.image", 1);
//
// PC-Welt.de, https://www.pcwelt.de/ratgeber/Geheime-Tricks-der-Insider-Browser-Geheimnisse-8809751.html
//
user_pref("Media.navigator.enabled", false);
user_pref("Media.peerconnection.enabled", false);
user_pref("Browser.taskbar.previews.enable", false);
user_pref("Privacy.resistFingerprinting", true);
//
//
//
//
// Pale Moon Extension: Block Content Download
//
user_pref("extensions.mdsy.block.script", false);
user_pref("extensions.mdsy.block.xhr", true);
user_pref("extensions.mdsy.block.image", false);
user_pref("extensions.mdsy.block.media", true);
user_pref("extensions.mdsy.block.object", true);
user_pref("extensions.mdsy.block.font", true);
user_pref("extensions.mdsy.block.style", false);
user_pref("permissions.default.image", 3);
user_pref("permissions.default.object", 2);
user_pref("permissions.default.script", 3);
user_pref("permissions.default.stylesheet", 3);
user_pref("permissions.default.subdocument", 3);
//
/******************************************************************************
* SECTION: HTML5 / APIs / DOM *
******************************************************************************/
// recommended for Firefox-ESR
// listed settings contribute to anonymizing and increasing speed of firefox up to 100%
// copy to /home/user/.mozilla/firefox/*your_profile_default_directory/
// PREF: Disable Service Workers
// https://developer.mozilla.org/en-US/docs/Web/API/Worker
// https://developer.mozilla.org/en-US/docs/Web/API/ServiceWorker_API
// https://wiki.mozilla.org/Firefox/Push_Notifications#Service_Workers
// NOTICE: Disabling ServiceWorkers breaks functionality on some sites (Google Street View...)
// Unknown security implications
// CVE-2016-5259, CVE-2016-2812, CVE-2016-1949, CVE-2016-5287 (fixed)
user_pref("dom.serviceWorkers.enabled", false);
// PREF: Disable Web Workers
// https://developer.mozilla.org/en-US/docs/Web/API/Web_Workers_API/Using_web_workers
// https://www.w3schools.com/html/html5_webworkers.asp
// NOTICE: Disabling Web Workers breaks "Download as ZIP" functionality on https://mega.nz/, WhatsApp Web and probably others
user_pref("dom.workers.enabled", false);
user_pref("browser.tabs.closeWindowWithLastTab", false);
// PREF: Disable web notifications
// https://support.mozilla.org/t5/Firefox/I-can-t-find-Firefox-menu-I-m-
trying-to-opt-out-of-Web-Push-and/m-p/1317495#M1006501
user_pref("dom.webnotifications.enabled", false);
// PREF: Disable DOM timing API
// https://wiki.mozilla.org/Security/Reviews/Firefox/NavigationTimingAPI
// https://www.w3.org/TR/navigation-timing/#privacy
user_pref("dom.enable_performance", false);
// PREF: Make sure the User Timing API does not provide a new high resolution timestamp
// https://trac.torproject.org/projects/tor/ticket/16336
// https://www.w3.org/TR/2013/REC-user-timing-20131212/#privacy-security
user_pref("dom.enable_user_timing", false);
// PREF: Disable Web Audio API
// https://bugzilla.mozilla.org/show_bug.cgi?id=1288359
user_pref("dom.webaudio.enabled", false);
// PREF: Disable Location-Aware Browsing (geolocation)
// https://www.mozilla.org/en-US/firefox/geolocation/
user_pref("geo.enabled", false);
// PREF: When geolocation is enabled, use Mozilla geolocation service instead of Google
// https://bugzilla.mozilla.org/show_bug.cgi?id=689252
user_pref("geo.wifi.uri", "https://location.services.mozilla.com/v1/
geolocate?key=%MOZILLA_API_KEY%");
// PREF: When geolocation is enabled, don´t log geolocation requests to the console
user_pref("geo.wifi.logging.enabled", false);
// PREF: Disable raw TCP socket support (mozTCPSocket)
// https://trac.torproject.org/projects/tor/ticket/18863
// https://www.mozilla.org/en-US/security/advisories/mfsa2015-97/
// https://developer.mozilla.org/docs/Mozilla/B2G_OS/API/TCPSocket
user_pref("dom.mozTCPSocket.enabled", false);
// PREF: Disable DOM storage (disabled)
// http://kb.mozillazine.org/Dom.storage.enabled
// https://html.spec.whatwg.org/multipage/webstorage.html
// NOTICE-DISABLED: Disabling DOM storage is known to cause´TypeError: localStorage is null´ errors
user_pref("dom.storage.enabled", false);
// PREF: Disable leaking network/browser connection information via Javascript
// Network Information API provides general information about the system´s connection type (WiFi, cellular, etc.)
// https://developer.mozilla.org/en-US/docs/Web/API/Network_Information_API
// https://wicg.github.io/netinfo/#privacy-considerations
// https://bugzilla.mozilla.org/show_bug.cgi?id=960426
user_pref("dom.netinfo.enabled", false);
// PREF: Disable network API (Firefox< 32)
// https://developer.mozilla.org/en-US/docs/Web/API/Connection/onchange
// https://www.torproject.org/projects/torbrowser/design/#fingerprinting-defenses
user_pref("dom.network.enabled", false);
//
user_pref("network.dns.disableIPv6", true);
//
// PREF: Disable WebRTC entirely to prevent leaking internal IP addresses (Firefox< 42)
// NOTICE: Disabling WebRTC breaks peer-to-peer file sharing tools (reep.io ...)
user_pref("media.peerconnection.enabled", false);
// PREF: Don´t reveal your internal IP when WebRTC is enabled (Firefox>= 42)
// https://wiki.mozilla.org/Media/WebRTC/Privacy
// https://github.com/beefproject/beef/wiki/Module%3A-Get-Internal-IP-WebRTC
user_pref("media.peerconnection.ice.default_address_only", true); // Firefox 42-51
user_pref("media.peerconnection.ice.no_host", true); // Firefox>= 52
// PREF: Disable WebRTC getUserMedia, screen sharing, audio capture, video capture
// https://wiki.mozilla.org/Media/getUserMedia
// https://blog.mozilla.org/futurereleases/2013/01/12/capture-local-
camera-and-microphone-streams-with-getusermedia-now-enabled-in-firefox/
// https://developer.mozilla.org/en-US/docs/Web/API/Navigator
user_pref("media.navigator.enabled", false);
user_pref("media.navigator.video.enabled", false);
user_pref("media.getusermedia.screensharing.enabled", false);
user_pref("media.getusermedia.audiocapture.enabled", false);
// PREF: Disable battery API (Firefox< 52)
// https://developer.mozilla.org/en-US/docs/Web/API/BatteryManager
// https://bugzilla.mozilla.org/show_bug.cgi?id=1313580
user_pref("dom.battery.enabled", false);
// PREF: Disable telephony API
// https://wiki.mozilla.org/WebAPI/Security/WebTelephony
user_pref("dom.telephony.enabled", false);
// PREF: Disable "beacon" asynchronous HTTP transfers (used for analytics)
// https://developer.mozilla.org/en-US/docs/Web/API/navigator.sendBeacon
user_pref("beacon.enabled", false);
// PREF: Disable clipboard event detection (onCut/onCopy/onPaste) via Javascript
// NOTICE: Disabling clipboard events breaks Ctrl+C/X/V copy/cut/paste functionaility in JS-based web applications (Google Docs...)
// https://developer.mozilla.org/en-US/docs/Mozilla/Preferences/Preference_reference/dom.event.clipboardevents.enabled
user_pref("dom.event.clipboardevents.enabled", false);
// PREF: Disable "copy to clipboard" functionality via Javascript (Firefox>= 41)
// NOTICE: Disabling clipboard operations will break legitimate JS-based "copy to clipboard" functionality
// https://hg.mozilla.org/mozilla-central/rev/2f9f8ea4b9c3
user_pref("dom.allow_cut_copy", false);
// PREF: Disable speech recognition
// https://dvcs.w3.org/hg/speech-api/raw-file/tip/speechapi.html
// https://developer.mozilla.org/en-US/docs/Web/API/SpeechRecognition
// https://wiki.mozilla.org/HTML5_Speech_API
user_pref("media.webspeech.recognition.enable", false);
// PREF: Disable speech synthesis
// https://developer.mozilla.org/en-US/docs/Web/API/SpeechSynthesis
user_pref("media.webspeech.synth.enabled", false);
// PREF: Disable sensor API
// https://wiki.mozilla.org/Sensor_API
user_pref("device.sensors.enabled", false);
// PREF: Disable pinging URIs specified in HTML< ping= attributes
// http://kb.mozillazine.org/Browser.send_pings
user_pref("browser.send_pings", false);
// PREF: When browser pings are enabled, only allow pinging the same host as the origin page
// http://kb.mozillazine.org/Browser.send_pings.require_same_host
user_pref("browser.send_pings.require_same_host", true);
// PREF: Disable IndexedDB (disabled)
// https://developer.mozilla.org/en-US/docs/IndexedDB
// https://en.wikipedia.org/wiki/Indexed_Database_API
// https://wiki.mozilla.org/Security/Reviews/Firefox4/IndexedDB_Security_Review
// http://forums.mozillazine.org/viewtopic.php?p=13842047
// https://github.com/pyllyukko/user.js/issues/8
// NOTICE-DISABLED: IndexedDB could be used for tracking purposes, but is required for some add-ons to work (notably uBlock), so is left enabled
user_pref("dom.indexedDB.enabled", false);
// TODO: "Access Your Location" "Maintain Offline Storage" "Show Notifications"
// PREF: Disable gamepad API to prevent USB device enumeration
// https://www.w3.org/TR/gamepad/
// https://trac.torproject.org/projects/tor/ticket/13023
user_pref("dom.gamepad.enabled", false);
// PREF: Disable virtual reality devices APIs
// https://developer.mozilla.org/en-US/Firefox/Releases/36#Interfaces.2FAPIs.2FDOM
// https://developer.mozilla.org/en-US/docs/Web/API/WebVR_API
user_pref("dom.vr.enabled", false);
// PREF: Disable vibrator API
user_pref("dom.vibrator.enabled", false);
// PREF: Disable resource timing API
// https://www.w3.org/TR/resource-timing/#privacy-security
user_pref("dom.enable_resource_timing", false);
// PREF: Disable Archive API (Firefox< 54)
// https://wiki.mozilla.org/WebAPI/ArchiveAPI
// https://bugzilla.mozilla.org/show_bug.cgi?id=1342361
user_pref("dom.archivereader.enabled", false);
// PREF: Disable webGL
// https://en.wikipedia.org/wiki/WebGL
// https://www.contextis.com/resources/blog/webgl-new-dimension-browser-exploitation/
user_pref("webgl.disabled", true);
// PREF: When webGL is enabled, use the minimum capability mode
user_pref("webgl.min_capability_mode", true);
// PREF: When webGL is enabled, disable webGL extensions
// https://developer.mozilla.org/en-US/docs/Web/API/WebGL_API#WebGL_debugging_and_testing
user_pref("webgl.disable-extensions", true);
// PREF: When webGL is enabled, force enabling it even when layer acceleration is not supported
// https://trac.torproject.org/projects/tor/ticket/18603
user_pref("webgl.disable-fail-if-major-performance-caveat", true);
// PREF: When webGL is enabled, do not expose information about the graphics driver
// https://bugzilla.mozilla.org/show_bug.cgi?id=1171228
// https://developer.mozilla.org/en-US/docs/Web/API/WEBGL_debug_renderer_info
user_pref("webgl.enable-debug-renderer-info", false);
// somewhat related...
user_pref("pdfjs.enableWebGL", false);
// PREF: Spoof dual-core CPU
// https://trac.torproject.org/projects/tor/ticket/21675
// https://bugzilla.mozilla.org/show_bug.cgi?id=1360039
user_pref("dom.maxHardwareConcurrency", 2);
/******************************************************************************
* SECTION: Misc *
******************************************************************************/
// PREF: Disable face detection
user_pref("camera.control.face_detection.enabled", false);
// ALWAYS SET A SEARCH ENGINE, OTHERWISE CONTEXT MENU BRAKES! (!!!)
//
// PREF: Set the default search engine to DuckDuckGo (disabled)
// https://support.mozilla.org/en-US/questions/948134
user_pref("browser.search.defaultenginename", "Wikipedia (en)");
user_pref("browser.search.order.1", "");
user_pref("keyword.URL", "");
// PREF: Disable GeoIP lookup on your address to set default search engine region
// https://trac.torproject.org/projects/tor/ticket/16254
// https://support.mozilla.org/en-US/kb/how-stop-firefox-
making-automatic-connections#w_geolocation-for-default-search-engine
user_pref("browser.search.countryCode", "US");
user_pref("browser.search.region", "US");
user_pref("browser.search.geoip.url", "");
// PREF: Set Accept-Language HTTP header to en-US regardless of Firefox localization
// https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Accept-Language
user_pref("intl.accept_languages", "en-US");
user_pref("intl.charset.fallback.override", "UTF-8");
// PREF: Don´t use OS values to determine locale, force using Firefox locale setting
// http://kb.mozillazine.org/Intl.locale.matchOS
user_pref("intl.locale.matchOS", false);
// PREF: Don´t use Mozilla-provided location-specific search engines
user_pref("browser.search.geoSpecificDefaults", false);
// PREF: Do not automatically send selection to clipboard on some Linux platforms
// http://kb.mozillazine.org/Clipboard.autocopy
user_pref("clipboard.autocopy", false);
// PREF: Prevent leaking application locale/date format using JavaScript
// https://bugzilla.mozilla.org/show_bug.cgi?id=867501
// https://hg.mozilla.org/mozilla-central/rev/52d635f2b33d
user_pref("javascript.use_us_english_locale", true);
// PREF: Do not submit invalid URIs entered in the address bar to the default search engine
// http://kb.mozillazine.org/Keyword.enabled
user_pref("keyword.enabled", false);
// PREF: Don´t trim HTTP off of URLs in the address bar.
// https://bugzilla.mozilla.org/show_bug.cgi?id=665580
// Big change for Firefox: Mozilla-Browser eliminates part of the URL (if set to true)
// https://www.chip.de/news/Riesen-Aenderung-bei-Firefox-Jetzt-schafft-auch-der-
Mozilla-Browser-die-URL-ab_182514886.html
user_pref("browser.urlbar.trimURLs", false);
// PREF: Don´t try to guess domain names when entering an invalid domain name in URL bar
// http://www-archive.mozilla.org/docs/end-user/domain-guessing.html
user_pref("browser.fixup.alternate.enabled", false);
// PREF: When browser.fixup.alternate.enabled is enabled, strip password from ´user:password@...´ URLs
// https://github.com/pyllyukko/user.js/issues/290#issuecomment-303560851
user_pref("browser.fixup.hide_user_pass", true);
// PREF: Send DNS request through SOCKS when SOCKS proxying is in use
// https://trac.torproject.org/projects/tor/wiki/doc/TorifyHOWTO/WebBrowsers
//user_pref("NETWORK.PROXY.SOCKS_REMOTE_DNS", false);
// PREF: Don´t monitor OS online/offline connection state
// https://trac.torproject.org/projects/tor/ticket/18945
user_pref("network.manage-offline-status", false);
// PREF: Enforce Mixed Active Content Blocking
// https://support.mozilla.org/t5/Protect-your-privacy/Mixed-content-blocking-in-Firefox/ta-p/10990
// https://developer.mozilla.org/en-US/docs/Site_Compatibility_for_Firefox_23#Non-SSL_contents_on_SSL_pages_are_blocked_by_default
// https://blog.mozilla.org/tanvi/2013/04/10/mixed-content-blocking-enabled-in-firefox-23/
user_pref("security.mixed_content.block_active_content", true);
// PREF: Enforce Mixed Passive Content blocking (a.k.a. Mixed Display Content)
// NOTICE: Enabling Mixed Display Content blocking can prevent images/styles... from loading properly when connection to the website is only partially secured
user_pref("security.mixed_content.block_display_content", false);
// PREF: Disable JAR from opening Unsafe File Types
// http://kb.mozillazine.org/Network.jar.open-unsafe-types
// CIS Mozilla Firefox 24 ESR v1.0.0 - 3.7
user_pref("network.jar.open-unsafe-types", false);
// CIS 2.7.4 Disable Scripting of Plugins by JavaScript
// http://forums.mozillazine.org/viewtopic.php?f=7&t=153889
user_pref("security.xpconnect.plugin.unrestricted", false);
// PREF: Set File URI Origin Policy
// http://kb.mozillazine.org/Security.fileuri.strict_origin_policy
// CIS Mozilla Firefox 24 ESR v1.0.0 - 3.8
user_pref("security.fileuri.strict_origin_policy", true);
// PREF: Disable Displaying Javascript in History URLs
// http://kb.mozillazine.org/Browser.urlbar.filter.javascript
// CIS 2.3.6
user_pref("browser.urlbar.filter.javascript", true);
// PREF: Disable asm.js
// http://asmjs.org/
// https://www.mozilla.org/en-US/security/advisories/mfsa2015-29/
// https://www.mozilla.org/en-US/security/advisories/mfsa2015-50/
// https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-2712
user_pref("javascript.options.asmjs", false);
// PREF: Disable SVG in OpenType fonts
// https://wiki.mozilla.org/SVGOpenTypeFonts
// https://github.com/iSECPartners/publications/tree/master/reports/Tor%20Browser%20Bundle
user_pref("gfx.font_rendering.opentype_svg.enabled", false);
// PREF: Disable in-content SVG rendering (Firefox>= 53)
// NOTICE: Disabling SVG support breaks many UI elements on many sites
// https://bugzilla.mozilla.org/show_bug.cgi?id=1216893
// https://github.com/iSECPartners/publications/raw/master/reports/Tor%20Browser%20
Bundle/Tor%20Browser%20Bundle%20-%20iSEC%20Deliverable%201.3.pdf#16
user_pref("svg.disabled", false);
// PREF: Disable video stats to reduce fingerprinting threat
// https://bugzilla.mozilla.org/show_bug.cgi?id=654550
// https://github.com/pyllyukko/user.js/issues/9#issuecomment-100468785
// https://github.com/pyllyukko/user.js/issues/9#issuecomment-148922065
user_pref("media.video_stats.enabled", false);
// PREF: Don´t reveal build ID
// Value taken from Tor Browser
// https://bugzilla.mozilla.org/show_bug.cgi?id=583181
user_pref("general.buildID.override", "20100101");
user_pref("browser.startup.homepage_override.buildID", "20100101");
// PREF: Prevent font fingerprinting
// https://browserleaks.com/fonts
// https://github.com/pyllyukko/user.js/issues/120
//One more detailed listing: https://www.ghacks.net/2015/08/18/a-comprehensive-
list-of-firefox-privacy-and-security-settings/
user_pref("app.update.staging.enabled", false);
user_pref("privacy.trackingprotection.enabled", true);
user_pref("privacy.trackingprotection.pbmode.enabled", true);
user_pref("browser.send_pings", false);
user_pref("browser.send_pings.require_same_host", true);
user_pref("browser.sessionstore.max_tabs_undo", 0);
user_pref("browser.sessionstore.max_windows_undo", 0);
user_pref("security.ssl.treat_unsafe_negotiation_as_broken", true);
user_pref("security.pki.sha1_enforcement_level", 1);
user_pref("security.mixed_content.send_hsts_priming", false);
user_pref("network.http.spdy.enabled", false);
user_pref("network.http.spdy.enabled.deps", false);
// 2615: disable http2 for now as well
user_pref("network.http.spdy.enabled.http2", false);
user_pref("network.proxy.socks_remote_dns", true);
// 2666: disable HTTP Alternative Services
// https://www.ghacks.net/2015/08/18/a-comprehensive-list-of-firefox-privacy-and-security-settings/#comment-3970881
user_pref("network.http.altsvc.enabled", false);
user_pref("network.http.altsvc.oe", false);
user_pref("devtools.chrome.enabled", false);
// from https://privacy-handbuch.de/handbuch_21n.htm
user_pref("extensions.pocket.enabled", false);
user_pref("extensions.screenshots.disabled", true);
user_pref("identify.fxaccounts.enabled", false);
user_pref("browser.formfill.enabled", false);
user_pref("extensions.formautofill.addresses.enabled", false);
user_pref("extensions.formautofill.creditCards.enabled", false);
user_pref("extensions.heuristics.enabled", false);
user_pref("webgl.disable-extensions", true);
user_pref("webgl.min_capability_mode", true);
user_pref("webgl.disable-fail-if-major-performance-caveat", true);
user_pref("webgl.disabled", true);
user_pref("webgl.enable-webgl2", false);
user_pref("dom.event.clipboardevents.enabled", false);
user_pref("network.http.speculative-parallel-limit", 0);
user_pref("extensions.blocklist.enabled", false);
user_pref("extensions.getAddons.cache.enabled", false);
user_pref("browser.tabs.crashreporting.sendReport", false);
user_pref("datareporting.policy.dataSubmissionEnabled", false);
user_pref("datareporting.healthreport.uploadEnabled", false);
user_pref("toolkit.coverage.endpoint.base", "");
user_pref("toolkit.coverage.opt-out", true);
user_pref("toolkit.telemetry.coverage.opt-out", true);
user_pref("browser.region.update.enabled", false);
user_pref("browser.region.network.url", "");
user_pref("browser.pagethumbnails.capturing_disabled", true);
user_pref("browser.startup.homepage_override.mstone", ignore);
user_pref("browser.newtabpage.activity-stream.asrouter.userprefs.cfr.addons", false);
user_pref("browser.newtabpage.activity-stream.asrouter.userprefs.cfr.features", false);
user_pref("extensions.htmlaboutaddons.recommandations.enabled", false);
user_pref("extensions.ui.lastCategory", "addons://list/extension");
user_pref("browser.vpn_promo.enabled", false);
user_pref("app.normally.enabled", false);
user_pref("extensions.webextensions.restrictedDomains", &quto;");
user_pref("ui.use_standins_for_native_colors", true);
user_pref("ui.systemUsesDarkTheme", 0);
user_pref("network.captive-portal-service.enabled", false);
user_pref("network.connectivity-service.enabled", false);
// from https://www.instructables.com/id/Improve-ADSL-Broadband-Performance/
user_pref("browser.link.open_newwindow.restriction", 1);
user_pref("webgl.enable-webgl2", false);
user_pref("webgl.disable-wgl", true);
user_pref("browser.sessionhistory.max_entries", 3);
user_pref("media.navigator.video.preferred_codec", 126);
user_pref("media.navigator.video.max_fs", 2560);
user_pref("media.navigator.video.h264.level", 22);
user_pref("media.navigator.video.h264.max_mbps", 6000);
user_pref("media.ffmpeg.low-latency.enabled", true);
// Reduce CPU Utilization
// this few settings can reduce the cpu utilization and speeding up web contents.
user_pref("layout.frame_rate", 20);
user_pref("gfx.direct2d.disabled", false);
user_pref("gfx.direct2d.force-enabled", true);
user_pref("layers.prefer-opengl", true);
// from https://www.privacy-handbuch.de/handbuch_21q.htm
// Information about installed fonts can be read out by Javascript, flash or Java and further on get used
// for individual fingerprinting of the browser.
user_pref("browser.display.use_document_fonts", 0);
user_pref("font.blacklist.underline_offset", "");
user_pref("javascript.options.wasm", false);
user_pref("javascript.options.wasm_baselinejit", false);
//
// from wiki.kairaven.de:
//
user_pref("browser.display.use_document_fonts", 0);
user_pref("font.blacklist.underline_offset","");
user_pref("gfx.downloadable_fonts.enabled", false);
user_pref("gfx.downloadable_fonts.woff2.enabled", false);
user_pref("layout.css.font-loading-api.enabled", false);
user_pref("gfx.downloadable_fonts.disable_cache", true);
user_pref("gfx.font_rendering.graphite.enabled", false);
user_pref("layout.css.prefixes.font-features", false);
user_pref("general.useragent.locale","en-US");
user_pref("intl.accept_languages","en-US");
user_pref("javascript.use_us_english_locale", true);
user_pref("network.http.accept-encoding", "gzip, deflate");
user_pref("browser.cache.disk.capacity", 0);
user_pref("browser.cache.disk.enable", false);
user_pref("browser.cache.disk.smart_size.enabled", false);
user_pref("browser.cache.disk_cache_ssl", false);
user_pref("browser.cache.memory.enable", false);
user_pref("browser.cache.offline.capacity", 0);
user_pref("browser.cache.offline.enable", false);
user_pref("devtools.cache.disabled", true);
user_pref("dom.caches.enabled", false);
user_pref("media.cache_size", 0);
user_pref("browser.disk.free_space_hard_limit", 1);
user_pref("browser.disk.free_space_soft_limit", 1);
user_pref("browser.disk.max_chunks_memory_usage", 1);
user_pref("browser.disk.max_entry_size", 4);
user_pref("browser.disk.max_priority_chunks_memory_usage", 4);
user_pref("browser.disk.metadata_memory_limit", 5);
user_pref("browser.disk.parent_directory", "/tmp");
user_pref("browser.cache.disk.smart_size.firt_run", false);
user_pref("browser.cache.disk.cache_ssl", false);
user_pref("browser.cache.frecency_experiment", 1);
user_pref("browser.cache.memory.max_entery_size", 0);
user_pref("browser.cache.offline.capacity", 0);
user_pref("browser.cache.offline.enable", false);
user_pref("dom.caches.enabled", false);
user_pref("extensions.getAddons.cache.enabled", false);
user_pref("gfx.canvas.skiagl.dynamic-cache", false);
user_pref("gfx.downloadable_fonts.disable_cache", true);
user_pref("image.cache.size", 0);
user_pref("media.cache_size", 0);
user_pref("network.buffer.cache.count", 4);
user_pref("network.buffer.cache.size", 512);
user_pref("offline-apps.allow_by_default", false);
user_pref("signon.formlessCapture.enabled", false);
user_pref("browser.safebrowsing.blockedURIs.enabled", false);
user_pref("brwoser.safebrowsing.provider.mozilla.lists" "");
user_pref("brwoser.safebrowsing.provider.google.lists" "");
user_pref("browser.safebrowsing.downloads.remote.enabled", false);
user_pref("dom.ipc.plugins.enabled", false);
user_pref("dom.ipc.plugins.enabled.pname.dll/so", false);
user_pref("dom.ipc.plugins.timeoutSecs", -1);
user_pref("media.eme.enabled", false);
user_pref("media.gmp-gmpopenh264.abi","");
user_pref("media.gmp-gmpopenh264.version","");
user_pref("media.gmp.storage.version.observed", 0);
user_pref("media.eme.apiVisible", false);
user_pref("browser.startup.homepage_override.buildID", 0);
user_pref("browser.eme.ui.enabled ", true);
user_pref("plugin.default.state", 0);
user_pref("plugin.defaultXpi.state", 0);
user_pref("browser.safebrowsing.downloads.enabled", false);
user_pref("browser.tabs.opentabfor.middleclick", true);
user_pref("browser.search.openintab", true);
user_pref("browser.taskbar.previews.enable", true);
user_pref("config.trim_on_minimize", true);
user_pref("font.default.x-western", "serif");
user_pref("font.name.serif.x-western", "serif");
user_pref("font.name.sans-serif.x-western", "sans-serif")
user_pref("font.name.monospace.x-western", "serif")
user_pref("font.default.x-western" "sans-serif");
user_pref("font.language.group", "x-western");
user_pref("middlemouse.paste", true);
user_pref("browser.fixup.alternate.suffix", ".com");
user_pref("network.cookie.lifetime.days", 1);
user_pref("network.dnsCacheExpiration", 9);
user_pref("browser.send_pings", false);
user_pref("network.dns.disableIPv6", true);
user_pref("network.protocol-handler.expose.ftp", false);
user_pref("network.protocol-handler.external.ftp", false);
//
//firecamp.de
//
user_pref("useragentswitcher.1.appname", "Microsoft Internet Explorer");
user_pref("useragentswitcher.1.appversion", "4.0 (compatible; MSIE 6.0; Windows NT 5.1)");
user_pref("useragentswitcher.1.description", "Internet Explorer 6 (Windows XP)");
user_pref("useragentswitcher.1.platform", "Win32");
user_pref("useragentswitcher.1.useragent", "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1)");
user_pref("useragentswitcher.2.appname", "Netscape");
user_pref("useragentswitcher.2.appversion", "4.8 [de] (Windows NT 5.1; U)");
user_pref("useragentswitcher.2.description", "Netscape 4.8 (Windows XP)");
user_pref("useragentswitcher.2.platform", "Win32");
user_pref("useragentswitcher.2.useragent", "Mozilla/4.8 [de] (Windows NT 5.1; U)");
user_pref("useragentswitcher.3.appname", "Opera");
user_pref("useragentswitcher.3.appversion", "7.54 (Windows NT 5.1; U)");
user_pref("useragentswitcher.3.description", "Opera 7.54 (Windows XP)");
user_pref("useragentswitcher.3.platform", "Win32");
user_pref("useragentswitcher.3.useragent", "Opera/7.54 (Windows NT 5.1; U) [de]");
user_pref("useragentswitcher.menu.hide", false);
user_pref("useragentswitcher.reset.onclose", false);
user_pref("useragentswitcher.user.agents.count", 3);
user_pref("accessibility.typeaheadfind", false);
user_pref("accessibility.typeaheadfind.flashBar", 0);
user_pref("browser.display.screen_resolution", 96);
user_pref("browser.history_expire_days", 1);
user_pref("browser.link.open_external", 2);
user_pref("browser.xul.error_pages.enabled", false);
user_pref("extensions.update.lastUpdateDate", 1099489430);
user_pref("browser.download.dir", "/tmp2");
user_pref("browser.dom.window.dump.enabled", false);
user_pref("browser.offline", false);
user_pref("browser.preferences.lastpanel", 5);
user_pref("browser.tabs.loadInBackground", false);
user_pref("downloadmgr.showWhenStarting", true);
user_pref("javascript.options.parallel.parsing", false);
user_pref("javascript.options.strict", true);
user_pref("javascript.options.native_regexp", true);
user_pref("javascript.options.mem.gc_per_zone", true);
user_pref("javascript.options.mem.gc_refresh_frame_slices_enabled", true);
user_pref("font.internaluseonly.changed", false);
user_pref("privacy.cpd.formdata", true);
user_pref("privacy.donottrackheader.enabled", true);
user_pref("privacy.popups.showBrowserMessage", false);
user_pref("privacy.sanitize.migrateFx3Prefs", true);
user_pref("privacy.sanitize.timeSpan", 0);
user_pref("privacy.firstparty.isolate", true); // ff>=58 once more against Canvas Fingerprinting
user_pref("services.sync.declinedEngines", "");
user_pref("storage.vacuum.last.index", 1);
user_pref("storage.vacuum.last.places.sqlite", 1509303910);
user_pref("network.http.max-connections", 32);
user_pref("browser.cache.disk.parent_directory" "/tmp"); // siehe /etc/fstab
user_pref("browser.download.importedFromSqlite", true); // *
user_pref("extensions.checkCompatibility", false);
user_pref("browser.sessionstore.resume_session_once", false);
user_pref("browser.sessionstore.upgradeBackup.latestBuildID", "0");
user_pref("browser.urlbar.matchBehavior", 2);
user_pref("browser.urlbar.matchOnlyTyped", true);
user_pref("browser.urlbar.maxRichResults", 0);
user_pref("gestures.enable_single_finger_input", false);
//
// https://www.philognosie.net/internet/firefox-einstellungen-aboutconfig-praktische-filter-tipps?page=2
//
user_pref("accessibility.typeahead.flashBar", 0);
user_pref("app.releaseNotesURL", "");
user_pref("app.support.baseURL", "");
user_pref("app.update.enabled", false);
user_pref("app.update.url", "");
user_pref("app.update.url.details", "");
user_pref("app.update.url.manual", "");
user_pref("app.vendorURL", "");
user_pref("browser.allTabs.previews", false);
user_pref("browser.autofocus", false);
user_pref("browser.bookmarks.restore_default_bookmarks", false);
user_pref("browser.cache.disk.capacity", 0);
user_pref("browser.cache.disk.filesystem_reported", 0);
user_pref("browser.cache.disk.smart_size.enabled", false);
user_pref("browser.cache.disk.smart_size.first_run", false);
user_pref("browser.cache.disk.smart_size.use_old_max", false);
user_pref("browser.cache.disk_cache_ssl", false);
user_pref("browser.cache.memory.enable", false);
user_pref("browser.cache.offline.capacity", 0);
user_pref("browser.cache.offline.enable", false);
user_pref("browser.contentHandlers.types.0.uri", "");
user_pref("browser.ctrlTab.previews", false);
user_pref("browser.dictionaries.download.url", "");
user_pref("browser.display.use_document_fonts", 0);
user_pref("browser.download.dir", /tmp);
user_pref("browser.download.folderList", 2);
user_pref("browser.download.importedFromSqlite", true);
user_pref("browser.download.panel.shown", true);
user_pref("browser.download.useDownloadDir", true);
user_pref("browser.feedback.url", "");
user_pref("devtools.memory.enabled", false);
user_pref("devtools.errorconsole.enabled", false);
user_pref("devtools.device.url", "");
user_pref("devtools.browserconsole.filter.sharedworkers", false);
user_pref("clipboard.autocopy", false);
user_pref("captivedetect.canonicalURL", "");
user_pref("network.http.keep-alive.timeout", 115);
user_pref("network.http.connection-timeout", 90);
user_pref("network.http:connection-retry-timeout", 250);
user_pref("dom.disable_window_open_feature.menubar", true);
user_pref("keyword.enabled", false);
user_pref("browser.urlbar.maxRichResults", 0);
user_pref("browser.urlbar.clickSelectsAll", false);
user_pref("browser.backspace_action", 2);
user_pref("general.smoothScroll", true);
user_pref("browser.showQuitWarning", false);
user_pref("Browser.download.saveLinkAsFilenameTimeout", 4000);
user_pref("accessibility.typeaheadfind", true);
user_pref("accessibility.typeaheadfind.flashBar", 0);
user_pref("app.releaseNotesURL", "");
user_pref("app.support.baseURL", "");
user_pref("app.update.backgroundErrors", 1);
user_pref("app.update.backgroundMaxErrors", 1);
user_pref("app.vendorURL", "");
user_pref("breakpad.reportURL", "");
user_pref("browser.allTabs.previews", false);
user_pref("browser.autofocus", false);
user_pref("browser.bookmarks.restore_default_bookmarks", false);
user_pref("browser.cache.disk.filesystem_reported", 1);
user_pref("browser.cache.disk.parent_directory", "/tmp");
user_pref("browser.cache.disk.smart_size.enabled", false);
user_pref("browser.cache.disk.smart_size.first_run", false);
user_pref("browser.cache.disk.smart_size.use_old_max", false);
user_pref("image.cache.size", 0);
user_pref("browser.contentHandlers.types.0.uri", "");
user_pref("browser.crashReports.unsubmittedCheck.enabled", false);
user_pref("browser.ctrlTab.previews", false);
user_pref("browser.dictionaries.download.url", "");
user_pref("browser.display.screen_resolution", 96);
user_pref("browser.download.folderList", 2);
user_pref("browser.download.importedFromSqlite", true);
user_pref("browser.download.panel.shown", false);
user_pref("browser.download.save_converter_index", 0);
user_pref("browser.download.useDownloadDir", true);
user_pref("browser.feedback.url", "");
user_pref("browser.fixup.alternate.enabled", false);
user_pref("browser.formfill.saveHttpsForms", false);
user_pref("browser.fullscreen.animateUp", 0);
user_pref("browser.fullscreen.autohide", false);
user_pref("browser.geolocation.warning.infoURL", "");
user_pref("browser.getdevtools.url", "");
user_pref("browser.history_expire_days", 1);
user_pref("browser.link.open_external", 2);
user_pref("browser.link.open_newwindow", 1);
user_pref("browser.link.open_newwindow.disabled_in_fullscreen", false);
user_pref("browser.link.open_newwindow.restriction", 0);
user_pref("browser.migration.version", 19);
user_pref("browser.mixedcontent.warning.infoURL", "");
user_pref("browser.newtab.choice", 0);
user_pref("browser.newtab.url", "about:blank");
user_pref("browser.newtabpage.columns", 0);
user_pref("browser.newtabpage.enabled", true);
user_pref("browser.newtabpage.rows", 0);
user_pref("browser.newtabpage.storageVersion", 1);
user_pref("browser.offline", false);
user_pref("browser.pagethumbnails.storage_version", 3);
user_pref("browser.places.smartBookmarksVersion", 4);
user_pref("browser.preferences.advanced.selectedTabIndex", 2);
user_pref("browser.preferences.lastpanel", 5);
user_pref("browser.preferences.privacy.selectedTabIndex", 2);
user_pref("browser.privatebrowsing.autostart", true);
user_pref("browser.safebrowsing.blockedURIs.enabled", true);
user_pref("browser.safebrowsing.downloads.remote.enabled", false);
user_pref("browser.search.countryCode", "US");
user_pref("browser.search.geoip.timeout", 1);
user_pref("browser.search.geoip.url", "");
user_pref("browser.search.order.1", "");
user_pref("browser.search.region", "US");
user_pref("browser.search.searchEnginesURL", "");
user_pref("browser.search.selectedEngine", "");
user_pref("browser.search.suggest.enabled", false);
user_pref("browser.search.update", false);
user_pref("browser.search.useDBForOrder", true);
user_pref("browser.selfsupport.enabled", false);
user_pref("browser.selfsupport.url", "");
user_pref("browser.send_pings.max_per_link", 0);
user_pref("browser.sessionhistory.max_entries", 5);
user_pref("browser.sessionhistory.max_total_viewers", -1);
user_pref("browser.sessionstore.privacy level", 2);
user_pref("browser.shell.checkDefaultBrowser", false);
user_pref("browser.shell.skipDefaultBrowserCheckOnFirstRun", true);
user_pref("browser.slowStartup.averageTime", 0);
user_pref("browser.slowStartup.maxSamples", 0);
user_pref("browser.slowStartup.notificationDisabled", true);
user_pref("browser.slowStartup.samples", 0);
user_pref("browser.slowstartup.help.url", "");
user_pref("browser.startup.homepage", "about::blank");
user_pref("browser.ustartup.homepage_override.mstone", "ignore");
user_pref("browser.startup.page", 0);
user_pref("browser.syncPromoViewsLeftMap", "{"addons":0,"bookmarks":0}");
user_pref("browser.tabs.closeWindowWithLastTab", false);
user_pref("browser.tabs.crashReporting.sendReport", false);
user_pref("browser.tabs.loadInBackground", false);
user_pref("browser.taskbar.previews.enable", true);
user_pref("browser.trackingprotection.gethashURL", "");
user_pref("browser.trackingprotection.updateURL", "");
user_pref("browser.urlbar.clickSelectsAll", false);
user_pref("browser.urlbar.matchBehavior", 2);
user_pref("browser.urlbar.matchOnlyTyped", true);
user_pref("browser.urlbar.maxRichResults", 0);
user_pref("browser.urlbar.suggest.bookmark", false);
user_pref("browser.xul.error_pages.enabled", false);
user_pref("browser.zoom.siteSpecific", false);
user_pref("camera.control.face_detection.enabled", false);
user_pref("clipboard.autocopy", false);
user_pref("config.trim_on_minimize", true);
user_pref("device.sensors.enabled", false);
user_pref("devtools.browserconcole.filter.csslog", false);
user_pref("devtools.devedition.promo.url", "");
user_pref("devtools.gcli.jquerySrc", "");
user_pref("devtools.gcli.lodashSrc", "");
user_pref("devtools.gcli.underscoreSrc", "");
user_pref("devtools.telemetry.tools.opened.version", "{}");
user_pref("devtools.toolbox.selectedTool", "inspector");
user_pref("devtools.toolsidebar-height.inspector", 350);
user_pref("devtools.toolsidebar-width.inspector", 350);
user_pref("devtools.webconsole.filter.csslogbrowserconcole.filter.csslog", false);
user_pref("disabletarget.extensions", "zip rar exe tar jar xpi gzip gz ace bin");
user_pref("dom.allow_cut_copy", false);
user_pref("dom.disable_window_move_resize", true);
user_pref("dom.disable_window_open_feature.close", true);
user_pref("dom.disable_window_open_feature.menubar", true);
user_pref("dom.disable_window_open_feature.minimizable", true);
user_pref("dom.disable_window_open_feature.personalbar", true);
user_pref("dom.disable_window_open_feature.scrollbars", true);
user_pref("dom.disable_window_open_feature.titlebar", true);
user_pref("dom.disable_window_open_feature.toolbar", true);
user_pref("dom.enable_performance", false);
user_pref("dom.enable_resource_timing", false);
user_pref("dom.enable_user_timing", false);
user_pref("dom.event.contextmenu.enabled", false);
user_pref("dom.gamepad.enabled", false);
user_pref("dom.idle-observers-api.enabled", false);
user_pref("dom.indexedDB.enabled", false);
user_pref("dom.ipc.plugins.enabled.pname.dll/so", false);
user_pref("dom.ipc.plugins.timeoutSecs", -1);
user_pref("dom.keyboardevent.code.enabled", false);
user_pref("dom.maxHardwareConcurrency", 2);
user_pref("dom.mozApps.signed_apps_installable_from", "");
user_pref("dom.mozInputMethod.enabled", false);
user_pref("dom.mozTCPSocket.enabled", false);
user_pref("dom.network.enabled", false);
user_pref("dom.popup_allowed_events", "change click dblclick mouseup pointerup notificationclick reset submit touchend");
user_pref("dom.popup_maximum", 1);
user_pref("dom.server-events.enabled", false);
user_pref("dom.storage.enabled", false);
user_pref("dom.vibrator.enabled", false);
user_pref("dom.webaudio.enabled", false);
user_pref("dom.webnotifications.enabled", false);
user_pref("dom.workers.enabled", false);
user_pref("downloadmgr.showWhenStarting", true);
user_pref("experiments.enabled", false);
user_pref("experiments.manifest.uri", "");
user_pref("experiments.supported", false);
user_pref("network.allow-experiments", false);
//
//https://www.thewindowsclub.com/mozilla-firefox-about-config-tweaks
//
user_pref("browser.tabs.insertRelatedAfterCurrent", true);
user_pref("browser.ctrlTab.previews", false);
user_pref("network.prefetch-next", false);
user_pref("browser.tabs.animate", true);
user_pref("browser.urlbar.clickSelectsAll", false);
user_pref("browser.tabs.animate", true);
//
// https://www.szenebox.org/15-gefaellt-mir/6709-firefox-richtig-einstellen/
//
user_pref("browser.safebrowsing.downloads.enabled", false);
user_pref("datareporting.healthreport.uploadEnabled", false);
user_pref("datareporting.policy.dataSubmissionEnabled", false);
user_pref("falsedatareporting.policy.dataSubmissionEnabled", false);
user_pref("browser.selfsupport.url", "");
//
user_pref("services.sync.engine.tabs", false);
user_pref("services.sync.engineStatusChanged.addons", true);
user_pref("services.sync.engineStatusChanged.bookmarks", true);
user_pref("services.sync.engineStatusChanged.history", true);
user_pref("services.sync.engineStatusChanged.passwords", true);
user_pref("services.sync.engineStatusChanged.prefs", true);
user_pref("services.sync.engineStatusChanged.tabs", true);
user_pref("services.sync.fxa.privacyURL", "");
user_pref("services.sync.fxa.termsURL", "");
user_pref("services.sync.jpake.serverURL", "");
user_pref("services.sync.migrated", true);
user_pref("services.sync.nextSync", 0);
user_pref("services.sync.prefs.sync.browser.safebrowsing.malware.enabled", false);
user_pref("services.sync.prefs.sync.browser.safebrowsing.phishing.enabled", false);
user_pref("services.sync.prefs.sync.browser.search.update", false);
user_pref("services.sync.prefs.sync.browser.sessionstore.restore_on_demand", false);
user_pref("services.sync.prefs.sync.browser.urlbar.autocomplete.enabled", false);
user_pref("services.sync.prefs.sync.browser.urlbar.suggest.searches", false);
user_pref("services.sync.prefs.sync.network.cookie.thirdparty.sessionOnly", false);
user_pref("services.sync.prefs.sync.spellchecker.dictionary", false);
user_pref("services.sync.privacyURL", "");
user_pref("services.sync.serverURL", "");
user_pref("services.sync.tabs.lastSync", 0);
user_pref("services.sync.tabs.lastSyncLocal", 0);
user_pref("services.sync.addons.trustedSourceHostnames", "");
user_pref("services.sync.clients.lastSync", 0);
user_pref("services.sync.clients.lastSyncLocal", 0);
user_pref("services.sync.declinedEngines", "");
user_pref("services.sync.engine.addons", false);
user_pref("services.sync.engine.bookmarks", false);
user_pref("services.sync.engine.history", false);
user_pref("services.sync.engine.passwords", false);
user_pref("services.sync.engine.prefs", false);
user_pref("services.sync.engine.tabs", false);
//
//https://www.maketecheasier.com/28-coolest-firefox-aboutconfig-tricks/
//
user_pref("browser.sessionhistory.max_total_viewers", 0);
user_pref("network.http.max-connections-per-server", 8);
user_pref("network.http.proxy.pipelining", false); // eventl. true
user_pref("browser.urlbar.clickSelectsAll", false);
user_pref("zoom.maxPercent", 300);
user_pref("zoom.minPercent", 30);
user_pref("security.dialog_enable_delay", 0);
user_pref("view_source.editor.external", false);
user_pref("view_source.editor.path", "");
user_pref("Browser.download.saveLinkAsFilenameTimeout", 4000);
user_pref("browser.fullscreen.autohide", false);
user_pref("extensions.getAddons.maxResults", 15);
user_pref("media.getusermedia.screensharing.allowed_domains", ""); // www.ciscoparks.com, ...
CHIP, https://www.chip.de/news/Firefox-Diese-Features-kennen-Sie-noch-nicht_93266205.html
user_pref("browser.tabs.loadBookmarksInTabs", true);
user_pref("findbar.modalHighlight", true);
user_pref("indbar.highlightAll", true);
user_pref("privacy.resistFingerprinting", true);
//
// PREF: Enable only whitelisted URL protocol handlers
// PREF: Enable only whitelisted URL protocol handlers
// http://kb.mozillazine.org/Network.protocol-handler.external-default
// http://kb.mozillazine.org/Network.protocol-handler.warn-external-default
// http://kb.mozillazine.org/Network.protocol-handler.expose.%28protocol%29
// https://news.ycombinator.com/item?id=13047883
// https://bugzilla.mozilla.org/show_bug.cgi?id=167475
// https://github.com/pyllyukko/user.js/pull/285#issuecomment-298124005
// NOTICE: Disabling nonessential protocols breaks all interaction with custom protocols such as mailto:, irc:, magnet: ... and breaks opening third-party mail/messaging/torrent/... clients when clicking on links with these protocols
// TODO: Add externally-handled protocols from Windows 8.1 and Windows 10 (currently contains protocols only from Linux and Windows 7) that might pose a similar threat (see e.g. https://news.ycombinator.com/item?id=13044991)
// TODO: Add externally-handled protocols from Mac OS X that might pose a similar threat (see e.g. https://news.ycombinator.com/item?id=13044991)
// If you want to enable a protocol, set network.protocol-handler.expose.(protocol) to true and network.protocol-handler.external.(protocol) to:
// * true, if the protocol should be handled by an external application
// * false, if the protocol should be handled internally by Firefox
user_pref("network.protocol-handler.warn-external-default", true);
user_pref("network.protocol-handler.external.http", false);
user_pref("network.protocol-handler.external.https", false);
user_pref("network.protocol-handler.external.javascript", false);
user_pref("network.protocol-handler.external.moz-extension", false);
user_pref("network.protocol-handler.external.ftp", true);
user_pref("network.protocol-handler.external.file", false);
user_pref("network.protocol-handler.external.about", false);
user_pref("network.protocol-handler.external.chrome", false);
user_pref("network.protocol-handler.external.blob", false);
user_pref("network.protocol-handler.external.data", false);
user_pref("network.protocol-handler.expose-all", false);
user_pref("network.protocol-handler.expose.http", false);
user_pref("network.protocol-handler.expose.https", false);
user_pref("network.protocol-handler.expose.javascript", false);
user_pref("network.protocol-handler.expose.moz-extension", false);
user_pref("network.protocol-handler.expose.ftp", false);
user_pref("network.protocol-handler.expose.file", false);
user_pref("network.protocol-handler.expose.about", false);
user_pref("network.protocol-handler.expose.chrome", false);
user_pref("network.protocol-handler.expose.blob", false);
user_pref("network.protocol-handler.expose.data", false);
user_pref("browser.sessionhistory.max_entries", 5);
user_pref("dom.ipc.plugins.processLaunchTimeoutSecs", 45);
user_pref("network.http.pipelining.ssl", false);
user_pref("network.negotiate-auth.using-native-gsslib", true);
user_pref("network.predictor.enable-hover-on-ssl", true);
user_pref("security.ssl.enable_alpn", true);
user_pref("security.ssl.enable_false_start", true);
user_pref("security.ssl.enable_npn", true);
user_pref("security.ssl.errorReporting.automatic", false);
user_pref("security.ssl.false_start.require-npn", false);
user_pref("security.ssl.require_safe_negotiation", true); // https://wiki.gentoo.org/wiki/Firefox
user_pref("security.ssl.treat_unsafe_negotiation_as_broken", false); //https://wiki.gentoo.org/wiki/Firefox
user_pref("security.ssl.enable_alpn", true);
user_pref("webchannel.allowObject.urlWhitelist" "");
user_pref("clipboard.plainTextOnly", true);
user_pref("devtools.remote.wifi.scan", false);
user_pref("toolkit.cosmeticAnimations.enabled", false);
user_pref("dom.battery.enabled", false);
user_pref("dom.disable_window_*", true);
user_pref("dom.event.clipboardevents.enabled", false);
user_pref("dom.gamepad.*.enabled", false);
user_pref("dom.mapped_arraybuffer.enabled", false);
user_pref("offline-apps.quota.warn", false);
user_pref("dom.w3c_touch_events.enabled", false);
user_pref("dom.webkitBlink.filesystem.enabled", false);
/******************************************************************************
* SECTION: Extensions / plugins *
******************************************************************************/
// PREF: Ensure you have a security delay when installing add-ons (milliseconds)
// http://kb.mozillazine.org/Disable_extension_install_delay_-_Firefox
// http://www.squarefree.com/2004/07/01/race-conditions-in-security-dialogs/
user_pref("security.dialog_enable_delay", 1000);
// PREF: Require signatures
// https://wiki.mozilla.org/Addons/Extension_Signing; needed for extensions like FireGloves etc.
user_pref("xpinstall.signatures.required", false);
// PREF: Opt-out of add-on metadata updates
// https://blog.mozilla.org/addons/how-to-opt-out-of-add-on-metadata-updates/
user_pref("extensions.getAddons.cache.enabled", false);
// PREF: Opt-out of themes (Persona) updates
// https://support.mozilla.org/t5/Firefox/how-do-I-prevent-autoamtic-updates-in-a-50-user-environment/td-p/144287
user_pref("lightweightThemes.update.enabled", false);
// PREF: Disable Flash Player NPAPI plugin
// http://kb.mozillazine.org/Flash_plugin
user_pref("plugin.state.flash", 0);
// PREF: Disable Java NPAPI plugin
user_pref("plugin.state.java", 0);
// PREF: Disable sending Flash Player crash reports
user_pref("dom.ipc.plugins.flash.subprocess.crashreporter.enabled", false);
// PREF: When Flash crash reports are enabled, don´t send the visited URL in the crash report
user_pref("dom.ipc.plugins.reportCrashURL", false);
// PREF: When Flash is enabled, download and use Mozilla SWF URIs blocklist
// https://bugzilla.mozilla.org/show_bug.cgi?id=1237198
// https://github.com/mozilla-services/shavar-plugin-blocklist
user_pref("browser.safebrowsing.blockedURIs.enabled", true);
// PREF: Disable Shumway (Mozilla Flash renderer)
// https://developer.mozilla.org/en-US/docs/Mozilla/Projects/Shumway
user_pref("shumway.disabled", true);
// PREF: Disable Gnome Shell Integration NPAPI plugin
user_pref("plugin.state.libgnome-shell-browser-plugin", 0);
// PREF: Disable the bundled OpenH264 video codec (disabled)
// http://forums.mozillazine.org/viewtopic.php?p=13845077&sid=28af2622e8bd8497b9113851676846b1#p13845077
user_pref("media.gmp-provider.enabled", false);
// PREF: Enable plugins click-to-play
// https://wiki.mozilla.org/Firefox/Click_To_Play
// https://blog.mozilla.org/security/2012/10/11/click-to-play-plugins-blocklist-style/
user_pref("plugins.click_to_play", false);
// PREF: Updates addons automatically
// https://blog.mozilla.org/addons/how-to-turn-off-add-on-updates/
user_pref("extensions.update.enabled", false);
// PREF: Enable add-on and certificate blocklists (OneCRL) from Mozilla
// https://wiki.mozilla.org/Blocklisting
// https://blocked.cdn.mozilla.net/
// http://kb.mozillazine.org/Extensions.blocklist.enabled
// http://kb.mozillazine.org/Extensions.blocklist.url
// https://blog.mozilla.org/security/2015/03/03/revoking-intermediate-certificates-introducing-onecrl/
// Updated at interval defined in extensions.blocklist.interval (default: 86400)
user_pref("extensions.blocklist.enabled", true);
user_pref("services.blocklist.update_enabled", true);
// PREF: Decrease system information leakage to Mozilla blocklist update servers
// https://trac.torproject.org/projects/tor/ticket/16931
user_pref("extensions.blocklist.url", "https://blocklist.addons.mozilla.org/blocklist/3/%APP_ID%/%APP_VERSION%/");
/******************************************************************************
* SECTION: Firefox (anti-)features / components * *
******************************************************************************/
// PREF: Disable WebIDE
// https://trac.torproject.org/projects/tor/ticket/16222
// https://developer.mozilla.org/docs/Tools/WebIDE
user_pref("devtools.webide.enabled", false);
user_pref("devtools.webide.autoinstallADBHelper", false);
user_pref("devtools.webide.autoinstallFxdtAdapters", false);
// PREF: Disable remote debugging
// https://developer.mozilla.org/en-US/docs/Tools/Remote_Debugging/Debugging_Firefox_Desktop
// https://developer.mozilla.org/en-US/docs/Tools/Tools_Toolbox#Advanced_settings
user_pref("devtools.debugger.remote-enabled", false);
user_pref("devtools.chrome.enabled", false);
user_pref("devtools.debugger.force-local", true);
// PREF: Disable Mozilla telemetry/experiments
// https://wiki.mozilla.org/Platform/Features/Telemetry
// https://wiki.mozilla.org/Privacy/Reviews/Telemetry
// https://wiki.mozilla.org/Telemetry
// https://www.mozilla.org/en-US/legal/privacy/firefox.html#telemetry
// https://support.mozilla.org/t5/Firefox-crashes/Mozilla-Crash-Reporter/ta-p/1715
// https://wiki.mozilla.org/Security/Reviews/Firefox6/ReviewNotes/telemetry
// https://gecko.readthedocs.io/en/latest/browser/experiments/experiments/manifest.html
// https://wiki.mozilla.org/Telemetry/Experiments
user_pref("toolkit.telemetry.enabled", false);
user_pref("toolkit.telemetry.unified", false);
user_pref("experiments.supported", false);
user_pref("experiments.enabled", false);
user_pref("experiments.manifest.uri", "");
// PREF: Disallow Necko to do A/B testing
// https://trac.torproject.org/projects/tor/ticket/13170
user_pref("network.allow-experiments", false);
// PREF: Disable sending Firefox crash reports to Mozilla servers
// https://wiki.mozilla.org/Breakpad
// http://kb.mozillazine.org/Breakpad
// https://dxr.mozilla.org/mozilla-central/source/toolkit/crashreporter
// https://bugzilla.mozilla.org/show_bug.cgi?id=411490
// A list of submitted crash reports can be found at about:crashes
user_pref("breakpad.reportURL", "");
// PREF: Disable sending reports of tab crashes to Mozilla (about:tabcrashed), don´t nag user about unsent crash reports
// https://hg.mozilla.org/mozilla-central/file/tip/browser/app/profile/firefox.js
user_pref("browser.tabs.crashReporting.sendReport", false);
user_pref("browser.crashReports.unsubmittedCheck.enabled", false);
// PREF: Disable FlyWeb (discovery of LAN/proximity IoT devices that expose a Web interface)
// https://wiki.mozilla.org/FlyWeb
// https://wiki.mozilla.org/FlyWeb/Security_scenarios
// https://docs.google.com/document/d/1eqLb6cGjDL9XooSYEEo7mE-zKQ-o-AuDTcEyNhfBMBM/edit
// http://www.ghacks.net/2016/07/26/firefox-flyweb
user_pref("dom.flyweb.enabled", false);
// PREF: Disable the UITour backend
// https://trac.torproject.org/projects/tor/ticket/19047#comment:3
user_pref("browser.uitour.enabled", false);
// PREF: Enable Firefox Tracking Protection
// https://wiki.mozilla.org/Security/Tracking_protection
// https://support.mozilla.org/en-US/kb/tracking-protection-firefox
// https://support.mozilla.org/en-US/kb/tracking-protection-pbm
// https://kontaxis.github.io/trackingprotectionfirefox/
// https://feeding.cloud.geek.nz/posts/how-tracking-protection-works-in-firefox/
user_pref("privacy.trackingprotection.enabled", true);
user_pref("privacy.trackingprotection.pbmode.enabled", true);
// PREF: Enable contextual identity Containers feature (Firefox>= 52)
// NOTICE: Containers are not available in Private Browsing mode
// https://wiki.mozilla.org/Security/Contextual_Identity_Project/Containers
user_pref("privacy.userContext.enabled", true);
// PREF: Enable hardening against various fingerprinting vectors (Tor Uplift project)
// https://wiki.mozilla.org/Security/Tor_Uplift/Tracking
// https://bugzilla.mozilla.org/show_bug.cgi?id=1333933
user_pref("privacy.resistFingerprinting", true);
// PREF: Disable the built-in PDF viewer
// https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-2743
// https://blog.mozilla.org/security/2015/08/06/firefox-exploit-found-in-the-wild/
// https://www.mozilla.org/en-US/security/advisories/mfsa2015-69/
user_pref("pdfjs.disabled", true);
// PREF: Disable collection/sending of the health report (healthreport.sqlite*)
// https://support.mozilla.org/en-US/kb/firefox-health-report-understand-your-browser-perf
// https://gecko.readthedocs.org/en/latest/toolkit/components/telemetry/telemetry/preferences.html
user_pref("datareporting.healthreport.uploadEnabled", false);
user_pref("datareporting.healthreport.service.enabled", false);
user_pref("datareporting.policy.dataSubmissionEnabled", false);
// PREF: Disable Heartbeat (Mozilla user rating telemetry)
// https://wiki.mozilla.org/Advocacy/heartbeat
// https://trac.torproject.org/projects/tor/ticket/19047
user_pref("browser.selfsupport.url", "");
// PREF: Disable Firefox Hello (disabled) (Firefox< 49)
// https://wiki.mozilla.org/Loop
// https://support.mozilla.org/t5/Chat-and-share/Support-for-Hello-discontinued-in-Firefox-49/ta-p/37946
// NOTICE-DISABLED: Firefox Hello requires setting ´media.peerconnection.enabled´ and ´media.getusermedia.screensharing.enabled´ to true, ´security.OCSP.require´ to false to work.
user_pref("loop.enabled", false);
// PREF: Disable Firefox Hello metrics collection
// https://groups.google.com/d/topic/mozilla.dev.platform/nyVkCx-_sFw/discussion
user_pref("loop.logDomains", false);
// PREF: Enable Auto Update (disabled)
// NOTICE: Fully automatic updates are disabled and left to package management systems on Linux. Windows users may want to change this setting.
// CIS 2.1.1
user_pref("app.update.auto", false);
// PREF: Enforce checking for Firefox updates
// http://kb.mozillazine.org/App.update.enabled
// NOTICE: Update check page might incorrectly report Firefox ESR as out-of-date
user_pref("app.update.enabled", false);
// PREF: Enable blocking reported web forgeries
// https://wiki.mozilla.org/Security/Safe_Browsing
// http://kb.mozillazine.org/Safe_browsing
// https://support.mozilla.org/en-US/kb/how-does-phishing-and-malware-protection-work
// http://forums.mozillazine.org/viewtopic.php?f=39&t=2711237&p=12896849#p12896849
// CIS 2.3.4
user_pref("browser.safebrowsing.enabled", false); // Firefox< 50
user_pref("browser.safebrowsing.phishing.enabled", false); // firefox>= 50
// PREF: Enable blocking reported attack sites
// http://kb.mozillazine.org/Browser.safebrowsing.malware.enabled
// CIS 2.3.5
user_pref("browser.safebrowsing.malware.enabled", false);
// PREF: Disable querying Google Application Reputation database for downloaded binary files
// https://www.mozilla.org/en-US/firefox/39.0/releasenotes/
// https://wiki.mozilla.org/Security/Application_Reputation
user_pref("browser.safebrowsing.downloads.remote.enabled", false);
// PREF: Disable Pocket
// https://support.mozilla.org/en-US/kb/save-web-pages-later-pocket-firefox
// https://github.com/pyllyukko/user.js/issues/143
user_pref("browser.pocket.enabled", false);
user_pref("extensions.pocket.enabled", false);
// PREF: Disable SHIELD
// https://support.mozilla.org/en-US/kb/shield
// https://bugzilla.mozilla.org/show_bug.cgi?id=1370801
user_pref("extensions.shield-recipe-client.enabled", false);
user_pref("app.shield.optoutstudies.enabled", false);
// PREF: Disable "Recommended by Pocket" in Firefox Quantum
user_pref("browser.newtabpage.activity-stream.feeds.section.topstories", false);
/******************************************************************************
* SECTION: Automatic connections *
******************************************************************************/
// PREF: Disable prefetching of<link rel="next" URLs
// http://kb.mozillazine.org/Network.prefetch-next
// https://developer.mozilla.org/en-US/docs/Web/HTTP/Link_prefetching_FAQ#Is_there_a_preference_to_disable_link_prefetching.3F
user_pref("network.prefetch-next", false);
// PREF: Disable DNS prefetching
// http://kb.mozillazine.org/Network.dns.disablePrefetch
// https://developer.mozilla.org/en-US/docs/Web/HTTP/Controlling_DNS_prefetching
user_pref("network.dns.disablePrefetch", false);
user_pref("network.dns.disablePrefetchFromHTTPS", false);
// PREF: Disable the predictive service (Necko)
// https://wiki.mozilla.org/Privacy/Reviews/Necko
user_pref("network.predictor.enabled", false);
// PREF: Reject .onion hostnames before passing the to DNS
// https://bugzilla.mozilla.org/show_bug.cgi?id=1228457
// RFC 7686
user_pref("network.dns.blockDotOnion", true);
// PREF: Disable search suggestions in the search bar
// http://kb.mozillazine.org/Browser.search.suggest.enabled
user_pref("browser.search.suggest.enabled", false);
// PREF: Disable "Show search suggestions in location bar results"
user_pref("browser.urlbar.suggest.searches", false);
// PREF: When using the location bar, don´t suggest URLs from browsing history
user_pref("browser.urlbar.suggest.history", false);
// PREF: Disable SSDP
// https://bugzilla.mozilla.org/show_bug.cgi?id=1111967
user_pref("browser.casting.enabled", false);
// PREF: Disable automatic downloading of OpenH264 codec
// https://support.mozilla.org/en-US/kb/how-stop-firefox-making-automatic-connections#w_media-capabilities
// https://andreasgal.com/2014/10/14/openh264-now-in-firefox/
user_pref("media.gmp-gmpopenh264.enabled", false);
user_pref("media.gmp-manager.url", "");
// PREF: Disable speculative pre-connections
// https://support.mozilla.org/en-US/kb/how-stop-firefox-making-automatic-connections#w_speculative-pre-connections
// https://bugzilla.mozilla.org/show_bug.cgi?id=814169
user_pref("network.http.speculative-parallel-limit", 0);
// PREF: Disable downloading homepage snippets/messages from Mozilla
// https://support.mozilla.org/en-US/kb/how-stop-firefox-making-automatic-connections#w_mozilla-content
// https://wiki.mozilla.org/Firefox/Projects/Firefox_Start/Snippet_Service
user_pref("browser.aboutHomeSnippets.updateUrl", "");
// PREF: Never check updates for search engines
// https://support.mozilla.org/en-US/kb/how-stop-firefox-making-automatic-connections#w_auto-update-checking
user_pref("browser.search.update", false);
// PREF: Disable automatic captive portal detection (Firefox>= 52.0)
// https://support.mozilla.org/en-US/questions/1157121
user_pref("network.captive-portal-service.enabled", false);
/******************************************************************************
* SECTION: HTTP *
******************************************************************************/
// PREF: Disallow NTLMv1
// https://bugzilla.mozilla.org/show_bug.cgi?id=828183
user_pref("network.negotiate-auth.allow-insecure-ntlm-v1", false);
// it is still allowed through HTTPS. uncomment the following to disable it completely.
//user_pref("network.negotiate-auth.allow-insecure-ntlm-v1-https", false);
// PREF: Enable CSP 1.1 script-nonce directive support
// https://bugzilla.mozilla.org/show_bug.cgi?id=855326
user_pref("security.csp.experimentalEnabled", true);
// PREF: Enable Content Security Policy (CSP)
// https://developer.mozilla.org/en-US/docs/Web/Security/CSP/Introducing_Content_Security_Policy
// https://developer.mozilla.org/en-US/docs/Web/HTTP/CSP
user_pref("security.csp.enable", true);
// PREF: Enable Subresource Integrity
// https://developer.mozilla.org/en-US/docs/Web/Security/Subresource_Integrity
// https://wiki.mozilla.org/Security/Subresource_Integrity
user_pref("security.sri.enable", true);
// PREF: DNT HTTP header (disabled)
// https://www.mozilla.org/en-US/firefox/dnt/
// https://en.wikipedia.org/wiki/Do_not_track_header
// https://dnt-dashboard.mozilla.org
// https://github.com/pyllyukko/user.js/issues/11
// NOTICE: Do No Track must be enabled manually
user_pref("privacy.donottrackheader.enabled", true);
// PREF: Send a referer header with the target URI as the source
// https://bugzilla.mozilla.org/show_bug.cgi?id=822869
// https://github.com/pyllyukko/user.js/issues/227
// NOTICE: Spoofing referers breaks functionality on websites relying on authentic referer headers
// NOTICE: Spoofing referers breaks visualisation of 3rd-party sites on the Lightbeam addon
// NOTICE: Spoofing referers disables CSRF protection on some login pages not implementing origin-header/cookie+token based CSRF protection
// TODO: https://github.com/pyllyukko/user.js/issues/94, commented-out XOriginPolicy/XOriginTrimmingPolicy = 2 prefs
user_pref("network.http.referer.spoofSource", true);
// PREF: Don´t send referer headers when following links across different domains (disabled)
// https://github.com/pyllyukko/user.js/issues/227
user_pref("network.http.referer.XOriginPolicy", 2);
// PREF: Accept Only 1st Party Cookies
// http://kb.mozillazine.org/Network.cookie.cookieBehavior#1
// NOTICE: Blocking 3rd-party cookies breaks a number of payment gateways
// CIS 2.5.1
// set 1: cookies from third parties only, 2: no cookies (2 recommended, if extension cookie-controller is installed)
user_pref("network.cookie.cookieBehavior", 2);
// PREF: Make sure that third-party cookies (if enabled) never persist beyond the session.
// https://feeding.cloud.geek.nz/posts/tweaking-cookies-for-privacy-in-firefox/
// http://kb.mozillazine.org/Network.cookie.thirdparty.sessionOnly
// https://developer.mozilla.org/en-US/docs/Cookies_Preferences_in_Mozilla#network.cookie.thirdparty.sessionOnly
// user_pref("network.cookie.thirdparty.sessionOnly", false);
// PREF: Spoof User-agent (disabled)
user_pref("general.useragent.override", "Mozilla/5.0 (Windows NT 6.1; rv:45.0) Gecko/20100101 Firefox/45.0");
user_pref("general.appname.override", "Netscape");
user_pref("general.appversion.override", "5.0 (Windows)");
user_pref("general.platform.override", "Win64");
user_pref("general.oscpu.override", "Windows NT 6.1");
/*******************************************************************************
* SECTION: Caching *
******************************************************************************/
// PREF: Permanently enable private browsing mode
// https://support.mozilla.org/en-US/kb/Private-Browsing
// https://wiki.mozilla.org/PrivateBrowsing
// NOTICE: You can not view or inspect cookies when in private browsing: https://bugzilla.mozilla.org/show_bug.cgi?id=823941
// NOTICE: When Javascript is enabled, Websites can detect use of Private Browsing mode
// NOTICE: Private browsing breaks Kerberos authentication
// NOTICE: Disables "Containers" functionality (see below)
// NOTICE: "Always use private browsing mode" (browser.privatebrowsing.autostart) disables the possibility to use password manager: https://support.mozilla.org/en-US/kb/usernames-and-passwords-are-not-saved#w_private-browsing
user_pref("browser.privatebrowsing.autostart", true);
// PREF: Do not download URLs for the offline cache
// http://kb.mozillazine.org/Browser.cache.offline.enable
user_pref("browser.cache.offline.enable", false);
// PREF: Clear history when Firefox closes
// https://support.mozilla.org/en-US/kb/Clear%20Recent%20History#w_how-do-i-make-firefox-clear-my-history-automatically
// NOTICE: Installing user.js will remove your browsing history, caches and local storage.
// NOTICE: Installing user.js **will remove your saved passwords** (https://github.com/pyllyukko/user.js/issues/27)
// NOTICE: Clearing open windows on Firefox exit causes 2 windows to open when Firefox starts https://bugzilla.mozilla.org/show_bug.cgi?id=1334945
user_pref("privacy.sanitize.sanitizeOnShutdown", true);
user_pref("privacy.clearOnShutdown.cache", true);
user_pref("privacy.clearOnShutdown.cookies", true);
user_pref("privacy.clearOnShutdown.downloads", true);
user_pref("privacy.clearOnShutdown.formdata", true);
user_pref("privacy.clearOnShutdown.history", true);
user_pref("privacy.clearOnShutdown.offlineApps", true);
user_pref("privacy.clearOnShutdown.sessions", true);
user_pref("privacy.clearOnShutdown.openWindows", false); // must be set to false, in order to prevent from two loading window instances on startup
// PREF: Set time range to "Everything" as default in "Clear Recent History"
user_pref("privacy.sanitize.timeSpan", 0);
// PREF: Clear everything but "Site Preferences" in "Clear Recent History"
user_pref("privacy.cpd.offlineApps", true);
user_pref("privacy.cpd.cache", true);
user_pref("privacy.cpd.cookies", true);
user_pref("privacy.cpd.downloads", true);
user_pref("privacy.cpd.formdata", true);
user_pref("privacy.cpd.passwords", true);
user_pref("privacy.cpd.history", true);
user_pref("privacy.cpd.sessions", true);
// PREF: Don´t remember browsing history
user_pref("places.history.enabled", false);
// PREF: Disable disk cache
// http://kb.mozillazine.org/Browser.cache.disk.enable
user_pref("browser.cache.disk.enable", false);
// PREF: Disable memory cache (disabled)
// http://kb.mozillazine.org/Browser.cache.memory.enable
user_pref("browser.cache.memory.enable", false);
// PREF: Disable Caching of SSL Pages
// CIS Version 1.2.0 October 21st, 2011 2.5.8
// http://kb.mozillazine.org/Browser.cache.disk_cache_ssl
user_pref("browser.cache.disk_cache_ssl", false);
// PREF: Disable download history
// CIS Version 1.2.0 October 21st, 2011 2.5.5
user_pref("browser.download.manager.retention", 0);
// PREF: Disable password manager
// CIS Version 1.2.0 October 21st, 2011 2.5.2
user_pref("signon.rememberSignons", false);
// PREF: Disable form autofill, don´t save information entered in web page forms and the Search Bar
user_pref("browser.formfill.enable", false);
// PREF: Cookies expires at the end of the session (when the browser closes)
// http://kb.mozillazine.org/Network.cookie.lifetimePolicy#2
user_pref("network.cookie.lifetimePolicy", 2);
// PREF: Require manual intervention to autofill known username/passwords sign-in forms
// http://kb.mozillazine.org/Signon.autofillForms
// https://www.torproject.org/projects/torbrowser/design/#identifier-linkability
user_pref("signon.autofillForms", false);
// PREF: Disable formless login capture
// https://bugzilla.mozilla.org/show_bug.cgi?id=1166947
user_pref("signon.formlessCapture.enabled", false);
// PREF: When username/password autofill is enabled, still disable it on non-HTTPS sites
// https://hg.mozilla.org/integration/mozilla-inbound/rev/f0d146fe7317
user_pref("signon.autofillForms.http", false);
// PREF: Show in-content login form warning UI for insecure login fields
// https://hg.mozilla.org/integration/mozilla-inbound/rev/f0d146fe7317
user_pref("security.insecure_field_warning.contextual.enabled", true);
// PREF: Disable the password manager for pages with autocomplete=off (disabled)
// https://bugzilla.mozilla.org/show_bug.cgi?id=956906
// OWASP ASVS V9.1
// Does not prevent any kind of auto-completion (see browser.formfill.enable, signon.autofillForms)
user_pref("signon.storeWhenAutocompleteOff", false);
// PREF: Delete Search and Form History
// CIS Version 1.2.0 October 21st, 2011 2.5.6
user_pref("browser.formfill.expire_days", 0);
// PREF: Clear SSL Form Session Data
// http://kb.mozillazine.org/Browser.sessionstore.privacy_level#2
// Store extra session data for unencrypted (non-HTTPS) sites only.
// CIS Version 1.2.0 October 21st, 2011 2.5.7
// NOTE: CIS says 1, we use 2
user_pref("browser.sessionstore.privacy_level", 2);
// PREF: Delete temporary files on exit
// https://bugzilla.mozilla.org/show_bug.cgi?id=238789
user_pref("browser.helperApps.deleteTempFileOnExit", true);
// PREF: Do not create screenshots of visited pages (relates to the "new tab page" feature)
// https://support.mozilla.org/en-US/questions/973320
// https://developer.mozilla.org/en-US/docs/Mozilla/Preferences/Preference_reference/browser.pagethumbnails.capturing_disabled
user_pref("browser.pagethumbnails.capturing_disabled", true);
// PREF: Don´t fetch and permanently store favicons for Windows .URL shortcuts created by drag and drop
// NOTICE: .URL shortcut files will be created with a generic icon
// Favicons are stored as .ico files in $profile_dirshortcutCache
user_pref("browser.shell.shortcutFavicons", false);
// PREF: Disable bookmarks backups (default: 15)
// http://kb.mozillazine.org/Browser.bookmarks.max_backups
user_pref("browser.bookmarks.max_backups", 0);
/*******************************************************************************
* SECTION: UI related *
*******************************************************************************/
// PREF: Enable insecure password warnings (login forms in non-HTTPS pages)
// https://blog.mozilla.org/tanvi/2016/01/28/no-more-passwords-over-http-please/
// https://bugzilla.mozilla.org/show_bug.cgi?id=1319119
// https://bugzilla.mozilla.org/show_bug.cgi?id=1217156
user_pref("security.insecure_password.ui.enabled", true);
// PREF: Disable right-click menu manipulation via JavaScript (disabled)
user_pref("dom.event.contextmenu.enabled", false);
// PREF: Disable "Are you sure you want to leave this page?" popups on page close
// https://support.mozilla.org/en-US/questions/1043508
// Does not prevent JS leaks of the page close event.
// https://developer.mozilla.org/en-US/docs/Web/Events/beforeunload
user_pref("dom.disable_beforeunload", true);
// PREF: Disable Downloading on Desktop
// CIS 2.3.2
user_pref("browser.download.folderList", 2);
// PREF: Always ask the user where to download
// https://developer.mozilla.org/en/Download_Manager_preferences (obsolete)
user_pref("browser.download.useDownloadDir", false);
// PREF: Disable the "new tab page" feature and show a blank tab instead
// https://wiki.mozilla.org/Privacy/Reviews/New_Tab
// https://support.mozilla.org/en-US/kb/new-tab-page-show-hide-and-customize-top-sites#w_how-do-i-turn-the-new-tab-page-off
user_pref("browser.newtabpage.enabled", false);
user_pref("browser.newtab.url", "about:blank");
// PREF: Disable Activity Stream
// https://wiki.mozilla.org/Firefox/Activity_Stream
user_pref("browser.newtabpage.activity-stream.enabled", false);
// PREF: Disable new tab tile ads &preload
// http://www.thewindowsclub.com/disable-remove-ad-tiles-from-firefox
// http://forums.mozillazine.org/viewtopic.php?p=13876331#p13876331
// https://wiki.mozilla.org/Tiles/Technical_Documentation#Ping
// https://gecko.readthedocs.org/en/latest/browser/browser/DirectoryLinksProvider.html#browser-newtabpage-directory-source
// https://gecko.readthedocs.org/en/latest/browser/browser/DirectoryLinksProvider.html#browser-newtabpage-directory-ping
// TODO: deprecated? not in DXR, some dead links
user_pref("browser.newtabpage.enhanced", false);
user_pref("browser.newtab.preload", false);
user_pref("browser.newtabpage.directory.ping", "");
user_pref("browser.newtabpage.directory.source", "data:text/plain,{}");
// PREF: Enable Auto Notification of Outdated Plugins (Firefox< 50)
// https://wiki.mozilla.org/Firefox3.6/Plugin_Update_Awareness_Security_Review
// CIS Version 1.2.0 October 21st, 2011 2.1.2
// https://hg.mozilla.org/mozilla-central/rev/304560
user_pref("plugins.update.notifyUser", false);
// PREF: Force Punycode for Internationalized Domain Names
// http://kb.mozillazine.org/Network.IDN_show_punycode
// https://www.xudongz.com/blog/2017/idn-phishing/
// https://wiki.mozilla.org/IDN_Display_Algorithm
// https://en.wikipedia.org/wiki/IDN_homograph_attack
// https://www.mozilla.org/en-US/security/advisories/mfsa2017-02/
// CIS Mozilla Firefox 24 ESR v1.0.0 - 3.6
user_pref("network.IDN_show_punycode", true);
// PREF: Disable inline autocomplete in URL bar
// http://kb.mozillazine.org/Inline_autocomplete
user_pref("browser.urlbar.autoFill", false);
user_pref("browser.urlbar.autoFill.typed", false);
// PREF: Disable CSS :visited selectors
// https://blog.mozilla.org/security/2010/03/31/plugging-the-css-history-leak/
// https://dbaron.org/mozilla/visited-privacy
user_pref("layout.css.visited_links_enabled", false);
// PREF: Disable URL bar autocomplete and history/bookmarks suggestions dropdown
// http://kb.mozillazine.org/Disabling_autocomplete_-_Firefox#Firefox_3.5
user_pref("browser.urlbar.autocomplete.enabled", false);
// PREF: Do not check if Firefox is the default browser
user_pref("browser.shell.checkDefaultBrowser", false);
// PREF: When password manager is enabled, lock the password storage periodically
// CIS Version 1.2.0 October 21st, 2011 2.5.3 Disable Prompting for Credential Storage
user_pref("security.ask_for_password", 2);
// PREF: Lock the password storage every 1 minutes (default: 30)
user_pref("security.password_lifetime", 1);
// PREF: Display a notification bar when websites offer data for offline use
// http://kb.mozillazine.org/Browser.offline-apps.notify
user_pref("browser.offline-apps.notify", true);
/******************************************************************************
* SECTION: Cryptography *
******************************************************************************/
// PREF: Enable HSTS preload list (pre-set HSTS sites list provided by Mozilla)
// https://blog.mozilla.org/security/2012/11/01/preloading-hsts/
// https://wiki.mozilla.org/Privacy/Features/HSTS_Preload_List
// https://en.wikipedia.org/wiki/HTTP_Strict_Transport_Security
user_pref("network.stricttransportsecurity.preloadlist", true);
// PREF: Enable Online Certificate Status Protocol
// https://en.wikipedia.org/wiki/Online_Certificate_Status_Protocol
// https://www.imperialviolet.org/2014/04/19/revchecking.html
// https://www.maikel.pro/blog/current-state-certificate-revocation-crls-ocsp/
// https://wiki.mozilla.org/CA:RevocationPlan
// https://wiki.mozilla.org/CA:ImprovingRevocation
// https://wiki.mozilla.org/CA:OCSP-HardFail
// https://news.netcraft.com/archives/2014/04/24/certificate-revocation-why-browsers-remain-affected-by-heartbleed.html
// https://news.netcraft.com/archives/2013/04/16/certificate-revocation-and-the-performance-of-ocsp.html
// NOTICE: OCSP leaks your IP and domains you visit to the CA when OCSP Stapling is not available on visited host
// NOTICE: OCSP is vulnerable to replay attacks when nonce is not configured on the OCSP responder
// NOTICE: OCSP adds latency (performance)
// NOTICE: Short-lived certificates are not checked for revocation (security.pki.cert_short_lifetime_in_days, default:10)
// CIS Version 1.2.0 October 21st, 2011 2.2.4
user_pref("security.OCSP.enabled", true);
// PREF: Enable OCSP Stapling support
// https://en.wikipedia.org/wiki/OCSP_stapling
// https://blog.mozilla.org/security/2013/07/29/ocsp-stapling-in-firefox/
// https://www.digitalocean.com/community/tutorials/how-to-configure-ocsp-stapling-on-apache-and-nginx
user_pref("security.ssl.enable_ocsp_stapling", true);
// PREF: Enable OCSP Must-Staple support (Firefox>= 45)
// https://blog.mozilla.org/security/2015/11/23/improving-revocation-ocsp-must-staple-and-short-lived-certificates/
// https://www.entrust.com/ocsp-must-staple/
// https://github.com/schomery/privacy-settings/issues/40
// NOTICE: Firefox falls back on plain OCSP when must-staple is not configured on the host certificate
user_pref("security.ssl.enable_ocsp_must_staple", false);
// PREF: Require a valid OCSP response for OCSP enabled certificates
// https://groups.google.com/forum/#!topic/mozilla.dev.security/n1G-N2-HTVA
// Disabling this will make OCSP bypassable by MitM attacks suppressing OCSP responses
// NOTICE: ´security.OCSP.require´ will make the connection fail when the OCSP responder is unavailable
// NOTICE: ´security.OCSP.require´ is known to break browsing on some [captive portals](https://en.wikipedia.org/wiki/Captive_portal)
user_pref("security.OCSP.require", false);
//
// PREF: Disable TLS Session Tickets
// https://www.blackhat.com/us-13/briefings.html#NextGen
// https://media.blackhat.com/us-13/US-13-Daigniere-TLS-Secrets-Slides.pdf
// https://media.blackhat.com/us-13/US-13-Daigniere-TLS-Secrets-WP.pdf
// https://bugzilla.mozilla.org/show_bug.cgi?id=917049
// https://bugzilla.mozilla.org/show_bug.cgi?id=967977
user_pref("security.ssl.disable_session_identifiers", false);
//
//Software::Browser
// Firefox 74 schaltet TLS 1.0 und 1.1 ab
// Firefox 74 setzt die bereits 2018 beschlossene Abschaltung von TLS 1.0 und 1.1 in die Tat um und ergreift Maßnahmen gegen WebRTC-Leaking.
// https://www.pro-linux.de/news/1/27860/firefox-74-schaltet-tls-10-und-11-ab.html
// PREF: Only allow TLS 1.[0-3]
// http://kb.mozillazine.org/Security.tls.version.*
// 1 = TLS 1.0 is the minimum required / maximum supported encryption protocol. (This is the current default for the maximum supported version.)
// 2 = TLS 1.1 is the minimum required / maximum supported encryption protocol.
user_pref("security.tls.version.min", 3);
user_pref("security.tls.version.max", 4);
// user_pref("security.tls.version.enable-deprecated", false);
// PREF: Disable insecure TLS version fallback
// https://bugzilla.mozilla.org/show_bug.cgi?id=1084025
// https://github.com/pyllyukko/user.js/pull/206#issuecomment-280229645
user_pref("security.tls.version.fallback-limit", 3);
// PREF: Enfore Public Key Pinning
// https://en.wikipedia.org/wiki/HTTP_Public_Key_Pinning
// https://wiki.mozilla.org/SecurityEngineering/Public_Key_Pinning
// "2. Strict. Pinning is always enforced."
user_pref("security.cert_pinning.enforcement_level", 2);
// PREF: Disallow SHA-1
// https://bugzilla.mozilla.org/show_bug.cgi?id=1302140
// https://shattered.io/
user_pref("security.pki.sha1_enforcement_level", 1);
// PREF: Warn the user when server doesn´t support RFC 5746 ("safe" renegotiation)
// https://wiki.mozilla.org/Security:Renegotiation#security.ssl.treat_unsafe_negotiation_as_broken
// https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2009-3555
user_pref("security.ssl.treat_unsafe_negotiation_as_broken", false);
// PREF: Disallow connection to servers not supporting safe renegotiation (disabled)
// https://wiki.mozilla.org/Security:Renegotiation#security.ssl.require_safe_negotiation
// https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2009-3555
// TODO: ´security.ssl.require_safe_negotiation´ is more secure but makes browsing next to impossible (2012-2014-... - ´ssl_error_unsafe_negotiation´ errors), so is left disabled
user_pref("security.ssl.require_safe_negotiation", false);
// PREF: Disable automatic reporting of TLS connection errors
// https://support.mozilla.org/en-US/kb/certificate-pinning-reports
// we could also disable security.ssl.errorReporting.enabled, but I think it´s
// good to leave the option to report potentially malicious sites if the user
// chooses to do so.
// you can test this at https://pinningtest.appspot.com/
user_pref("security.ssl.errorReporting.automatic", false);
// PREF: Pre-populate the current URL but do not pre-fetch the certificate in the "Add Security Exception" dialog
// http://kb.mozillazine.org/Browser.ssl_override_behavior
// https://github.com/pyllyukko/user.js/issues/210
user_pref("browser.ssl_override_behavior", 1);
/******************************************************************************
* SECTION: Cipher suites *
******************************************************************************/
// PREF: Disable null ciphers
user_pref("security.ssl3.rsa_null_sha", false);
user_pref("security.ssl3.rsa_null_md5", false);
user_pref("security.ssl3.ecdhe_rsa_null_sha", false);
user_pref("security.ssl3.ecdhe_ecdsa_null_sha", false);
user_pref("security.ssl3.ecdh_rsa_null_sha", false);
user_pref("security.ssl3.ecdh_ecdsa_null_sha", false);
// PREF: Disable SEED cipher
// https://en.wikipedia.org/wiki/SEED
user_pref("security.ssl3.rsa_seed_sha", false);
// PREF: Disable 40/56/128-bit ciphers
// 40-bit ciphers
user_pref("security.ssl3.rsa_rc4_40_md5", false);
user_pref("security.ssl3.rsa_rc2_40_md5", false);
// 56-bit ciphers
user_pref("security.ssl3.rsa_1024_rc4_56_sha", false);
// 128-bit ciphers
user_pref("security.ssl3.rsa_camellia_128_sha", false);
user_pref("security.ssl3.ecdhe_rsa_aes_128_sha", false);
user_pref("security.ssl3.ecdhe_ecdsa_aes_128_sha", false);
user_pref("security.ssl3.ecdh_rsa_aes_128_sha", false);
user_pref("security.ssl3.ecdh_ecdsa_aes_128_sha", false);
user_pref("security.ssl3.dhe_rsa_camellia_128_sha", false);
user_pref("security.ssl3.dhe_rsa_aes_128_sha", false);
// PREF: Disable RC4
// https://developer.mozilla.org/en-US/Firefox/Releases/38#Security
// https://bugzilla.mozilla.org/show_bug.cgi?id=1138882
// https://rc4.io/
// https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2566
user_pref("security.ssl3.ecdh_ecdsa_rc4_128_sha", false);
user_pref("security.ssl3.ecdh_rsa_rc4_128_sha", false);
user_pref("security.ssl3.ecdhe_ecdsa_rc4_128_sha", false);
user_pref("security.ssl3.ecdhe_rsa_rc4_128_sha", false);
user_pref("security.ssl3.rsa_rc4_128_md5", false);
user_pref("security.ssl3.rsa_rc4_128_sha", false);
user_pref("security.tls.unrestricted_rc4_fallback", false);
// PREF: Disable 3DES (effective key size is < 128)
// https://en.wikipedia.org/wiki/3des#Security
// http://en.citizendium.org/wiki/Meet-in-the-middle_attack
// http://www-archive.mozilla.org/projects/security/pki/nss/ssl/fips-ssl-ciphersuites.html
user_pref("security.ssl3.dhe_dss_des_ede3_sha", false);
user_pref("security.ssl3.dhe_rsa_des_ede3_sha", false);
user_pref("security.ssl3.ecdh_ecdsa_des_ede3_sha", false);
user_pref("security.ssl3.ecdh_rsa_des_ede3_sha", false);
user_pref("security.ssl3.ecdhe_ecdsa_des_ede3_sha", false);
user_pref("security.ssl3.ecdhe_rsa_des_ede3_sha", false);
user_pref("security.ssl3.rsa_des_ede3_sha", false);
user_pref("security.ssl3.rsa_fips_des_ede3_sha", false);
// PREF: Disable ciphers with ECDH (non-ephemeral)
user_pref("security.ssl3.ecdh_rsa_aes_256_sha", false);
user_pref("security.ssl3.ecdh_ecdsa_aes_256_sha", false);
// PREF: Disable 256 bits ciphers without PFS
user_pref("security.ssl3.rsa_camellia_256_sha", false);
// PREF: Enable ciphers with ECDHE and key size> 128bits
user_pref("security.ssl3.ecdhe_rsa_aes_256_sha", true); // 0xc014
user_pref("security.ssl3.ecdhe_ecdsa_aes_256_sha", true); // 0xc00a
// PREF: Enable GCM ciphers (TLSv1.2 only)
// https://en.wikipedia.org/wiki/Galois/Counter_Mode
user_pref("security.ssl3.ecdhe_ecdsa_aes_128_gcm_sha256", true); // 0xc02b
user_pref("security.ssl3.ecdhe_rsa_aes_128_gcm_sha256", true); // 0xc02f
// PREF: Enable ChaCha20 and Poly1305 (Firefox>= 47)
// https://www.mozilla.org/en-US/firefox/47.0/releasenotes/
// https://tools.ietf.org/html/rfc7905
// https://bugzilla.mozilla.org/show_bug.cgi?id=917571
// https://bugzilla.mozilla.org/show_bug.cgi?id=1247860
// https://cr.yp.to/chacha.html
user_pref("security.ssl3.ecdhe_ecdsa_chacha20_poly1305_sha256", true);
user_pref("security.ssl3.ecdhe_rsa_chacha20_poly1305_sha256", true);
// PREF: Disable ciphers susceptible to the logjam attack
// https://weakdh.org/
user_pref("security.ssl3.dhe_rsa_camellia_256_sha", false);
user_pref("security.ssl3.dhe_rsa_aes_256_sha", false);
// PREF: Disable ciphers with DSA (max 1024 bits)
user_pref("security.ssl3.dhe_dss_aes_128_sha", false);
user_pref("security.ssl3.dhe_dss_aes_256_sha", false);
user_pref("security.ssl3.dhe_dss_camellia_128_sha", false);
user_pref("security.ssl3.dhe_dss_camellia_256_sha", false);
// PREF: Fallbacks due compatibility reasons
user_pref("security.ssl3.rsa_aes_256_sha", true); // 0x35
user_pref("security.ssl3.rsa_aes_128_sha", true); // 0x2f
//
// Firefox-hardening, https://forum.mxlinux.org/viewtopic.php?t=51318
//
user_pref("app.update.lastUpdateTime.experiments-update-timer",0);
user_pref("browser.backspace_action", 0);
user_pref("browser.cache.check_doc_frequency", 1);
user_pref("browser.cache.frecency_experiment", -1);
user_pref("browser.cache.use_new_backend_temp", false);
user_pref("browser.contentHandlers.types.0.title", "");
user_pref("browser.safebrowsing.blockedURIs.enabled", false);
user_pref("browser.safebrowsing.id", "");
user_pref("browser.search.countryCode", "");
user_pref("browser.search.region", "");
user_pref("browser.send_pings", false);
user_pref("browser.send_pings.require_same_host", false);
user_pref("layers.acceleration.force-enabled", true);
user_pref("intl.accept_languages", "en-US,en;q=0.5");
user_pref("media.decoder-doctor.notifications-allowed", "");
user_pref("extensions.blocklist.enabled", false);
user_pref("media.peerconnection.identity.enabled", false);
user_pref("media.peerconnection.identity.timeout", 1);
user_pref("media.peerconnection.simulcast", false);
user_pref("media.peerconnection.turn.disable", true);
user_pref("media.peerconnection.use_document_iceservers", false);
user_pref"media.peerconnection.video.enabled", false);
user_pref("media.peerconnection.video.vp9_enabled", false);
user_pref("network.captive-portal-service.enabled", false);
user_pref("places.frecency.unvisitedBookmarkBonus", 0);
user_pref("security.ssl.errorReporting.enabled", false);
user_pref("services.sync.telemetry.submissionInterval", 999999999);
user_pref("startup.homepage_override_url", "");
user_pref("startup.homepage_welcome_url", "");
user_pref("urlclassifier.malwareTable", "");
user_pref("urlclassifier.phishTable", "");
//
//https://github.com/pyllyukko/user.js#download
//
// end of user.js
On certificate errros do the following: enter the error causing url into the second field of noscript for https under exceptions, where each http might get blocked by a set * (star) within the first field. If this does not help, formulate error-exceptions with Firefox, by accepting corrputed certificates manually. Enter a remote-host-IP into /etc/resolv.conf: nameserver remote-dns-ip too.
// ======================================================================================
 // Mozilla User Preferences (prefs.js) // Mozilla User Preferences (prefs.js)
// ======================================================================================
 // Mozilla User Preferences (prefs.js) // Mozilla User Preferences (prefs.js)
// Pale Moone: /home/surfuser/.moon*/pale*/your-profile-directory/prefs.js
# Mozilla User Preferences
/* Do not edit this file.
*
* If you make changes to this file while the application is running,
* the changes will be overwritten when the application exits.
*
* To make a manual change to preferences, you can visit the URL about:config
*/
user_pref("accessibility.AOM.enabled", true);
user_pref("accessibility.accesskeycausesactivation", false);
user_pref("accessibility.ipc_architecture.enabled", false);
user_pref("accessibility.typeaheadfind.enablesound", false);
user_pref("accessibility.typeaheadfind.flashBar", 0);
user_pref("app.releaseNotesURL", "");
user_pref("app.support.baseURL", "");
user_pref("app.update.channel", "none");
user_pref("app.update.download.backgroundInterval", 0);
user_pref("app.update.enabled", false);
user_pref("app.update.idletime", -1);
user_pref("app.update.interval", -1);
user_pref("app.update.lastUpdateTime.addon-background-update-timer", 0);
user_pref("app.update.lastUpdateTime.background-update-timer", 0);
user_pref("app.update.lastUpdateTime.blocklist-background-update-timer", 0);
user_pref("app.update.lastUpdateTime.browser-cleanup-thumbnails", 0);
user_pref("app.update.lastUpdateTime.search-engine-update-timer", 1599840640);
user_pref("app.update.lastUpdateTime.user-agent-updates-timer", 1599388459);
user_pref("app.update.timerMinimumDelay", -1);
user_pref("app.update.url", "");
user_pref("app.update.url.details", "");
user_pref("app.update.url.manual", "");
user_pref("app.vendorURL", "");
user_pref("apz.allow_checkerboarding", false);
user_pref("beacon.enabled", false);
user_pref("browser.addon-watch.ignore", "");
user_pref("browser.allTabs.previews", false);
user_pref("browser.autofocus", false);
user_pref("browser.backspace_action", 0);
user_pref("browser.bookmarks.restore_default_bookmarks", false);
user_pref("browser.cache.check_doc_frequency", 0);
user_pref("browser.cache.disk.capacity", 0);
user_pref("browser.cache.disk.enable", false);
user_pref("browser.cache.disk.filesystem_reported", 0);
user_pref("browser.cache.disk.max_entry_size", 0);
user_pref("browser.cache.disk.smart_size.enabled", false);
user_pref("browser.cache.disk.smart_size.first_run", false);
user_pref("browser.cache.disk.smart_size.use_old_max", false);
user_pref("browser.cache.disk_cache_ssl", false);
user_pref("browser.cache.memory.enable", false);
user_pref("browser.cache.offline.capacity", 0);
user_pref("browser.cache.offline.enable", false);
user_pref("browser.contentHandlers.types.0.title", "");
user_pref("browser.contentHandlers.types.0.uri", "");
user_pref("browser.ctrlTab.previews", false);
user_pref("browser.dictionaries.download.url", "");
user_pref("browser.display.use_document_fonts", 0);
user_pref("browser.download.dir", "/tmp2");
user_pref("browser.download.folderList", 2);
user_pref("browser.download.forbid_open_with", true);
user_pref("browser.download.importedFromSqlite", true);
user_pref("browser.download.manager.addToRecentDocs", false);
user_pref("browser.download.panel.shown", true);
user_pref("browser.download.useDownloadDir", true);
user_pref("browser.feedback.url", "");
user_pref("browser.fixup.alternate.enabled", false);
user_pref("browser.fixup.alternate.suffix", ".de");
user_pref("browser.formfill.enable", false);
user_pref("browser.formfill.expire_days", 1);
user_pref("browser.formfill.saveHttpsForms", false);
user_pref("browser.fullscreen.animateUp", 0);
user_pref("browser.fullscreen.autohide", false);
user_pref("browser.geolocation.warning.infoURL", "");
user_pref("browser.getdevtools.url", "");
user_pref("browser.link.open_newwindow", 1);
user_pref("browser.link.open_newwindow.restriction", 0);
user_pref("browser.migration.version", 24);
user_pref("browser.mixedcontent.warning.infoURL", "");
user_pref("browser.newtabpage.columns", 0);
user_pref("browser.newtabpage.rows", 0);
user_pref("browser.newtabpage.storageVersion", 1);
user_pref("browser.offline-apps.notify", false);
user_pref("browser.pagethumbnails.storage_version", 3);
user_pref("browser.places.smartBookmarksVersion", 4);
user_pref("browser.preferences.advanced.selectedTabIndex", 1);
user_pref("browser.preferences.privacy.selectedTabIndex", 0);
user_pref("browser.privatebrowsing.autostart", true);
user_pref("browser.push.warning.infoURL", "");
user_pref("browser.search.defaultenginename", "Wikipedia (en)");
user_pref("browser.search.geoip.timeout", 1);
user_pref("browser.search.geoip.url", "");
user_pref("browser.search.official", false);
user_pref("browser.search.order.1", "");
user_pref("browser.search.order.2", "");
user_pref("browser.search.order.3", "");
user_pref("browser.search.order.4", "");
user_pref("browser.search.searchEnginesURL", "");
user_pref("browser.search.suggest.enabled", false);
user_pref("browser.search.update", false);
user_pref("browser.search.update.interval", -1);
user_pref("browser.send_pings.max_per_link", 0);
user_pref("browser.sessionhistory.max_entries", 4);
user_pref("browser.sessionstore.max_windows_undo", 2);
user_pref("browser.sessionstore.privacy_level", 2);
user_pref("browser.shell.checkDefaultBrowser", false);
user_pref("browser.shell.skipDefaultBrowserCheckOnFirstRun", true);
user_pref("browser.slowStartup.averageTime", 0);
user_pref("browser.slowStartup.maxSamples", 0);
user_pref("browser.slowStartup.notificationDisabled", true);
user_pref("browser.slowStartup.samples", 0);
user_pref("browser.slowstartup.help.url", "");
user_pref("browser.startup.homepage", "about:blank");
user_pref("browser.startup.homepage_override.buildID", "0");
user_pref("browser.startup.homepage_override.mstone", "ignore");
user_pref("browser.startup.page", 0);
user_pref("browser.tabs.closeWindowWithLastTab", false);
user_pref("browser.tabs.loadInBackground", false);
user_pref("browser.urlbar.autocomplete.enabled", false);
user_pref("browser.urlbar.clickSelectsAll", false);
user_pref("browser.urlbar.matchBehavior", 2);
user_pref("browser.urlbar.maxRichResults", 0);
user_pref("browser.urlbar.suggest.bookmark", false);
user_pref("browser.urlbar.suggest.history", false);
user_pref("browser.urlbar.suggest.openpage", false);
user_pref("browser.urlbar.suggest.searches", false);
user_pref("browser.xul.error_pages.enabled", false);
user_pref("browser.zoom.siteSpecific", false);
user_pref("camera.control.face_detection.enabled", false);
user_pref("canvas.poisondata", true);
user_pref("capability.policy.maonoscript.sites", "192.168.178.1 about: about:addons about:blank about:blocked about:certerror about:config about:crashes about:feeds about:home about:memory about:neterror about:plugins about:preferences about:privatebrowsing about:sessionrestore about:srcdoc about:support about:tabcrashed blob: chrome: mediasource: moz-extension: moz-safe-about: resource:");
user_pref("captivedetect.canonicalURL", "");
user_pref("clipboard.autocopy", false);
user_pref("device.sensors.enabled", false);
user_pref("devtools.browserconsole.filter.csserror", false);
user_pref("devtools.browserconsole.filter.error", false);
user_pref("devtools.browserconsole.filter.exception", false);
user_pref("devtools.browserconsole.filter.info", false);
user_pref("devtools.browserconsole.filter.jslog", false);
user_pref("devtools.browserconsole.filter.jswarn", false);
user_pref("devtools.browserconsole.filter.log", false);
user_pref("devtools.browserconsole.filter.netwarn", false);
user_pref("devtools.browserconsole.filter.network", false);
user_pref("devtools.browserconsole.filter.secerror", false);
user_pref("devtools.browserconsole.filter.secwarn", false);
user_pref("devtools.browserconsole.filter.serviceworkers", false);
user_pref("devtools.browserconsole.filter.sharedworkers", false);
user_pref("devtools.chrome.enabled", true);
user_pref("devtools.command-buttion-splitconsole.enabled", false);
user_pref("devtools.command-button-frames.enabled", false);
user_pref("devtools.command-button-responsive.enabled", false);
user_pref("devtools.debugger.client-source-maps-enabled", false);
user_pref("devtools.debugger.enabled", false);
user_pref("devtools.debugger.prompt-connection", false);
user_pref("devtools.debugger.source-maps-enabled", false);
user_pref("devtools.devedition.promo.url", "");
user_pref("devtools.devices.url", "");
user_pref("devtools.errorconsole.deprecation_warnings", false);
user_pref("devtools.errorconsole.enabled", false);
user_pref("devtools.errorconsole.performance_warnings", false);
user_pref("devtools.gcli.imgurUploadURL", "");
user_pref("devtools.gcli.jquerySrc", "");
user_pref("devtools.gcli.lodashSrc", "");
user_pref("devtools.gcli.underscoreSrc", "");
user_pref("devtools.memory.enabled", false);
user_pref("devtools.remote.wifi.scan", false);
user_pref("devtools.remote.wifi.visible", false);
user_pref("devtools.telemetry.supported_performance_marks", "");
user_pref("devtools.telemetry.tools.opened.version", "");
user_pref("devtools.toolbox.selectedTool", "inspector");
user_pref("devtools.webconsole.filter.error", false);
user_pref("devtools.webconsole.filter.secerror", false);
user_pref("devtools.webconsole.inputHistoryCount", 4);
user_pref("devtools.webide.adaptersAddonURL", "");
user_pref("devtools.webide.adbAddonURL", "");
user_pref("devtools.webide.addonsURL", "");
user_pref("devtools.webide.autoinstallADBHelper", false);
user_pref("devtools.webide.autoinstallFxdtAdapters", false);
user_pref("devtools.webide.enabled", false);
user_pref("devtools.webide.simulatorAddonsURL", "");
user_pref("devtools.webide.templatesURL", "");
user_pref("dom.caches.enabled", false);
user_pref("dom.disable_window_move_resize", true);
user_pref("dom.disable_window_open_feature.close", true);
user_pref("dom.disable_window_open_feature.menubar", true);
user_pref("dom.disable_window_open_feature.minimizable", true);
user_pref("dom.disable_window_open_feature.personalbar", true);
user_pref("dom.disable_window_open_feature.titlebar", true);
user_pref("dom.disable_window_open_feature.toolbar", true);
user_pref("dom.enable_performance", false);
user_pref("dom.enable_performance_navigation_timing", false);
user_pref("dom.enable_resource_timing", false);
user_pref("dom.enable_user_timing", false);
user_pref("dom.event.clipboardevents.enabled", false);
user_pref("dom.event.contextmenu.enabled", false);
user_pref("dom.gamepad.enabled", false);
user_pref("dom.idle-observers-api.enabled", false);
user_pref("dom.indexedDB.enabled", false);
user_pref("dom.ipc.plugins.enabled", false);
user_pref("dom.ipc.plugins.flash.subprocess.crashreporter.enabled", false);
user_pref("dom.ipc.plugins.reportCrashURL", false);
user_pref("dom.ipc.plugins.timeoutSecs", -1);
user_pref("dom.keyboardevent.code.enabled", false);
user_pref("dom.maxHardwareConcurrency", 2);
user_pref("dom.mms.requestReadReport", false);
user_pref("dom.mms.requestStatusReport", false);
user_pref("dom.popup_allowed_events", "change click dblclick mouseup pointerup notificationclick reset submit ");
user_pref("dom.popup_maximum", 1);
user_pref("dom.push.serverURL", "");
user_pref("dom.storage.enabled", false);
user_pref("dom.vibrator.enabled", false);
user_pref("dom.webaudio.enabled", false);
user_pref("dom.webnotifications.enabled", false);
user_pref("dom.workers.enabled", false);
user_pref("extensions.@no-resource-uri-leak.sdk.baseURI", "resource://no-resource-uri-leak/");
user_pref("extensions.@no-resource-uri-leak.sdk.domain", "no-resource-uri-leak");
user_pref("extensions.@no-resource-uri-leak.sdk.load.reason", "startup");
user_pref("extensions.@no-resource-uri-leak.sdk.rootURI", "jar:file:///home/surfuser/.moonchild%20productions/pale%20moon/profile.default/
extensions/@no-resource-uri-leak.xpi!/");
user_pref("extensions.@no-resource-uri-leak.sdk.version", "1.1.0");
user_pref("extensions.@no-resource-uri-leak.uri.about.restricted", true);
user_pref("extensions.@no-resource-uri-leak.uri.chrome.blocking.enabled", true);
user_pref("extensions.CanvasBlocker@kkapsner.de.blockMode", "blockEverything");
user_pref("extensions.CanvasBlocker@kkapsner.de.sdk.baseURI", "resource://canvasblocker-at-kkapsner-dot-de/");
user_pref("extensions.CanvasBlocker@kkapsner.de.sdk.domain", "canvasblocker-at-kkapsner-dot-de");
user_pref("extensions.CanvasBlocker@kkapsner.de.sdk.load.reason", "startup");
user_pref("extensions.CanvasBlocker@kkapsner.de.sdk.rootURI", "jar:file:///home/surfuser/.moonchild%20productions/pale%20moon/profile.default/extensions/CanvasBlocker@kkapsner.de.xpi!/");
user_pref("extensions.CanvasBlocker@kkapsner.de.sdk.version", "0.3.8-Release");
user_pref("extensions.CanvasBlocker@kkapsner.de.whiteList");
user_pref("extensions.CanvasBlocker@legacy.blockMode", "blockEverything");
user_pref("extensions.CanvasBlocker@legacy.protectWindow", true);
user_pref("extensions.CanvasBlocker@legacy.sdk.baseURI", "resource://canvasblocker-at-legacy/");
user_pref("extensions.CanvasBlocker@legacy.sdk.domain", "canvasblocker-at-legacy");
user_pref("extensions.CanvasBlocker@legacy.sdk.load.reason", "startup");
user_pref("extensions.CanvasBlocker@legacy.sdk.rootURI", "jar:file:///home/surfuser/.moonchild%20productions/
pale%20moon/profile.default/extensions/CanvasBlocker@legacy.xpi!/");
user_pref("extensions.CanvasBlocker@legacy.sdk.version", "0.2");
user_pref("extensions.CanvasBlocker@legacy.whiteList");
user_pref("extensions.PrivacyBadger@PaleMoon.doNotTrackDefaultEnabled", true);
user_pref("extensions.PrivacyBadger@PaleMoon.sdk.baseURI", "resource://privacybadger-at-palemoon/");
user_pref("extensions.PrivacyBadger@PaleMoon.sdk.domain", "privacybadger-at-palemoon");
user_pref("extensions.PrivacyBadger@PaleMoon.sdk.load.reason", "startup");
user_pref("extensions.PrivacyBadger@PaleMoon.sdk.rootURI", "jar:file:///home/surfuser/.moonchild%20productions/
pale%20moon/profile.default/extensions/PrivacyBadger@PaleMoon.xpi!/");
user_pref("extensions.PrivacyBadger@PaleMoon.sdk.version", "2.0.4");
user_pref("extensions.SecretAgent.EntropyLevel", "session");
user_pref("extensions.SecretAgent.ShowHijackRedirectAlerts", false);
user_pref("extensions.SecretAgent.ShowSpikeHijackRedirectAlerts", false);
user_pref("extensions.SecretAgent.SpikeHijackRedirectLocation", "about:blank");
user_pref("extensions.SecretAgent.SpikeHijackRedirects", true);
user_pref("extensions.SecretAgent.UserAgentList"Privoxy/1.0
Privoxy/1.0)");
user_pref("extensions.SecretAgent.Whitelist", "fr2.rpmfind.net
*.pro-linux.de
*.ebay.*
*.palemoon.org
");
user_pref("extensions.SecretAgent.WhitelistAcceptBehaviour", "override");
user_pref("extensions.SecretAgent.WhitelistOSCPUBehaviour", "override");
user_pref("extensions.SecretAgent.WhitelistUserAgent", "Mozilla/5.0 (compatible; Googlebot/2.1; +http://www.google.com/bot.html)");
user_pref("extensions.SecretAgent.WhitelistUserAgentBehaviour", "override");
user_pref("extensions.SecretAgent.showStartupAlert", false);
user_pref("extensions.adblockplus.currentVersion", "5.0.8");
user_pref("extensions.adblockplus.documentation_link", "");
user_pref("extensions.adblockplus.notificationdata", "{\"lastCheck\":1578864747154,\"softExpiration\":
1566545165716,\"hardExpiration\":1543866785218,\"data\":{\"notifications\":[],\"version\":\"201812011851\"},
\"lastError\":1578843883688,\"downloadStatus\":\"synchronize_invalid_url\",\"downloadCount\":46}");
user_pref("extensions.adblockplus.notificationurl", "");
user_pref("extensions.adblockplus.report_submiturl", "");
user_pref("extensions.adblockplus.subscriptions_antiadblockurl", "");
user_pref("extensions.adblockplus.subscriptions_autoupdate", false);
user_pref("extensions.adblockplus.subscriptions_exceptionsurl", "");
user_pref("extensions.adblockplus.subscriptions_fallbackurl", "");
user_pref("extensions.adblockplus.subscriptions_listurl", "");
user_pref("extensions.blocklist.detailsURL", "");
user_pref("extensions.blocklist.itemURL", "");
user_pref("extensions.blocklist.pingCountTotal", 209);
user_pref("extensions.blocklist.pingCountVersion", -1);
user_pref("extensions.blocklist.url", "");
user_pref("extensions.bootstrappedAddons", "{\"rpcontinued@amo.requestpolicy.org\": ...
user_pref("extensions.changerefererbutton.showInStatusBar", true);
user_pref("extensions.compatibility.url", "");
user_pref("extensions.cookieController.1stPartyOnlyCount", 3);
user_pref("extensions.cookieController.allowCookiesCount", 23);
user_pref("extensions.cookieController.safeMode", true);
user_pref("extensions.cookieController.sessionOnlyCount", 1);
user_pref("extensions.databaseSchema", 16);
user_pref("extensions.disable-about-something@clear-code.com.about.accounts", false);
user_pref("extensions.disable-about-something@clear-code.com.about.addons", true);
user_pref("extensions.disable-about-something@clear-code.com.about.config", true);
user_pref("extensions.disable-about-something@clear-code.com.about.downloads", false);
user_pref("extensions.disable-about-something@clear-code.com.about.permissions", false);
user_pref("extensions.disable-about-something@clear-code.com.about.profiles", false);
user_pref("extensions.disable-about-something@clear-code.com.about.sync-*", false);
user_pref("extensions.eclipsedmoon.device.laptop.useragent", "");
user_pref("extensions.eclipsedmoon.device.laptop.weights.os", "Linux = 1
Mac = 9
Windows = 13
");
user_pref("extensions.eclipsedmoon.device.laptop.weights.ua", "Vivaldi = 3
Firefox = 5
Chrome = 6
Other = 21");
user_pref("extensions.eclipsedmoon.mode", "smart");
user_pref("extensions.eclipsedmoon.staticUserAgent", "Mozilla/5.0 (compatible; Googlebot/2.1; +http://www.google.com/bot.html)");
user_pref("extensions.ematrix.cloudStorage.myRulesPane", "");
user_pref("extensions.ematrix.legacyToolbarButtonAdded", true);
user_pref("extensions.ematrix.paneContentPaddingTop", "86px");
user_pref("extensions.enabledAddons", "%7B8eb2e77d-73aa-4...
user_pref("extensions.getAddons.browseAddons", "");
user_pref("extensions.getAddons.get.url", "");
user_pref("extensions.getAddons.getWithPerformance.url", "");
user_pref("extensions.getAddons.recommended.browseURL", "");
user_pref("extensions.getAddons.recommended.url", "");
user_pref("extensions.getAddons.search.browseURL", "");
user_pref("extensions.getAddons.search.url", "");
user_pref("extensions.getMoreThemesURL", "");
user_pref("extensions.jid1-4fe6b55d552d870d@jetpack.sdk.baseURI", "resource://jid1-4fe6b55d552d870d-at-jetpack/");
user_pref("extensions.jid1-4fe6b55d552d870d@jetpack.sdk.domain", "jid1-4fe6b55d552d870d-at-jetpack");
user_pref("extensions.jid1-4fe6b55d552d870d@jetpack.sdk.load.reason", "startup");
user_pref("extensions.jid1-4fe6b55d552d870d@jetpack.sdk.rootURI", "jar:file:///home/surfuser/.moonchild%20productions/pale%20moon/profile.default/extensions/jid1-4fe6b55d552d870d@jetpack.xpi!/");
user_pref("extensions.jid1-4fe6b55d552d870d@jetpack.sdk.version", "0.7.7");
user_pref("extensions.jid1-BoFifL9Vbdl2zQ@jetpack.sdk.baseURI", "resource://jid1-bofifl9vbdl2zq-at-jetpack/");
user_pref("extensions.jid1-BoFifL9Vbdl2zQ@jetpack.sdk.domain", "jid1-bofifl9vbdl2zq-at-jetpack");
user_pref("extensions.jid1-BoFifL9Vbdl2zQ@jetpack.sdk.load.reason", "startup");
user_pref("extensions.jid1-BoFifL9Vbdl2zQ@jetpack.sdk.rootURI", "jar:file:///home/surfuser/.moonchild%20productions/pale%20moon/profile.default/extensions/jid1-BoFifL9Vbdl2zQ@jetpack.xpi!/");
user_pref("extensions.jid1-BoFifL9Vbdl2zQ@jetpack.sdk.version", "1.4.2");
user_pref("extensions.lastAppVersion", "28.13.0");
user_pref("extensions.lastPlatformVersion", "4.6.0");
user_pref("extensions.mdsy.block.font", true);
user_pref("extensions.mdsy.block.media", true);
user_pref("extensions.mdsy.block.object", true);
user_pref("extensions.mdsy.block.xhr", true);
user_pref("extensions.pcookie.allowCookiesCount", 2);
user_pref("extensions.pcookie.firstRun", false);
user_pref("extensions.pcookie.sessionOnlyCount", 8);
user_pref("extensions.pendingOperations", false);
user_pref("extensions.permissionsplus.firstrun", false);
user_pref("extensions.pm-localeswitch{at}palemoon{dot}org.isFirstRun", false);
user_pref("extensions.pm-localeswitch{at}palemoon{dot}org.lastRecordedVersion", "v3.0");
user_pref("extensions.pure-url@palemoon.firstrun", false);
user_pref("extensions.pure-url@palemoon.request_hook_enabled", false);
user_pref("extensions.pure-url@palemoon.shorteners", "");
user_pref("extensions.pure-url@palemoon.toolsmenu", true);
user_pref("extensions.requestpolicy.allowedOriginsToDestinations", "");
user_pref("extensions.requestpolicy.defaultPolicy.allowSameDomain", false);
user_pref("extensions.requestpolicy.initialSetupDialogShown", false);
user_pref("extensions.requestpolicy.lastAppVersion", "28.13.0");
user_pref("extensions.requestpolicy.lastVersion", "1.0.beta13.2");
user_pref("extensions.requestpolicy.privateBrowsingPermanentWhitelisting", true);
user_pref("extensions.requestpolicy.welcomeWindowShown", true);
user_pref("extensions.sdk-button-location.action-button--1607f7ec-8262-4016-b51f-f9f5b43d43f1-self-destructing-cookies",
"nav-bar,action-button--b5af16a6-105d-4a14-a5a6-c2b358b06a04-js-btn-show");
user_pref("extensions.sdk-button-location.action-button--b5af16a6-105d-4a14-a5a6-c2b358b06a04-js-btn-show", "nav-bar,");
user_pref("extensions.sdk-button-location.toggle-button--privacybadgerpalemoon-pb-button", "nav-bar,change-referer-button-toolbarbutton");
user_pref("extensions.shownSelectionUI", true);
user_pref("extensions.torbutton.security_slider", 1);
user_pref("extensions.torbutton.startup", true);
user_pref("extensions.torlauncher.torrc_fixup_version", 2);
user_pref("extensions.ui.dictionary.hidden", true);
user_pref("extensions.ui.lastCategory", "addons://list/extension");
user_pref("extensions.ui.locale.hidden", true);
user_pref("extensions.update.autoUpdateDefault", false);
user_pref("extensions.update.background.url", "");
user_pref("extensions.update.enabled", false);
user_pref("extensions.update.url", "");
user_pref("extensions.webservice.discoverURL", "");
user_pref("extensions.{b5af16a6-105d-4a14-a5a6-c2b358b06a04}.sdk.baseURI", "resource://b5af16a6-105d-4a14-a5a6-c2b358b06a04/");
user_pref("extensions.{b5af16a6-105d-4a14-a5a6-c2b358b06a04}.sdk.domain", "b5af16a6-105d-4a14-a5a6-c2b358b06a04");
user_pref("extensions.{b5af16a6-105d-4a14-a5a6-c2b358b06a04}.sdk.load.reason", "startup");
user_pref("extensions.{b5af16a6-105d-4a14-a5a6-c2b358b06a04}.sdk.rootURI", "jar:file:///home/surfuser/.moonchild%20productions/pale%20moon/profile.default/extensions/%7Bb5af16a6-105d-4a14-a5a6-c2b358b06a04%7D.xpi!/");
user_pref("extensions.{b5af16a6-105d-4a14-a5a6-c2b358b06a04}.sdk.version", "1.2.2.010");
user_pref("font.blacklist.underline_offset", "");
user_pref("font.default.x-western", "sans-serif");
user_pref("font.internaluseonly.changed", true);
user_pref("font.language.group", "x-western");
user_pref("gecko.handlerService.schemes.irc.0.name", "");
user_pref("gecko.handlerService.schemes.irc.0.uriTemplate", "");
user_pref("gecko.handlerService.schemes.irc.1.name", "");
user_pref("gecko.handlerService.schemes.irc.1.uriTemplate", "");
user_pref("gecko.handlerService.schemes.irc.2.name", "");
user_pref("gecko.handlerService.schemes.irc.2.uriTemplate", "");
user_pref("gecko.handlerService.schemes.irc.3.name", "");
user_pref("gecko.handlerService.schemes.irc.3.uriTemplate", "");
user_pref("gecko.handlerService.schemes.ircs.0.name", "");
user_pref("gecko.handlerService.schemes.ircs.0.uriTemplate", "");
user_pref("gecko.handlerService.schemes.ircs.1.name", "");
user_pref("gecko.handlerService.schemes.ircs.1.uriTemplate", "");
user_pref("gecko.handlerService.schemes.ircs.2.name", "");
user_pref("gecko.handlerService.schemes.ircs.2.uriTemplate", "");
user_pref("gecko.handlerService.schemes.ircs.3.name", "");
user_pref("gecko.handlerService.schemes.ircs.3.uriTemplate", "");
user_pref("gecko.handlerService.schemes.mailto.0.name", "");
user_pref("gecko.handlerService.schemes.mailto.0.uriTemplate", "");
user_pref("gecko.handlerService.schemes.mailto.1.name", "");
user_pref("gecko.handlerService.schemes.mailto.1.uriTemplate", "");
user_pref("gecko.handlerService.schemes.mailto.2.name", "");
user_pref("gecko.handlerService.schemes.mailto.2.uriTemplate", "");
user_pref("gecko.handlerService.schemes.mailto.3.name", "");
user_pref("gecko.handlerService.schemes.mailto.3.uriTemplate", "");
user_pref("gecko.handlerService.schemes.webcal.0.name", "");
user_pref("gecko.handlerService.schemes.webcal.0.uriTemplate", "");
user_pref("gecko.handlerService.schemes.webcal.1.name", "");
user_pref("gecko.handlerService.schemes.webcal.1.uriTemplate", "");
user_pref("gecko.handlerService.schemes.webcal.2.name", "");
user_pref("gecko.handlerService.schemes.webcal.2.uriTemplate", "");
user_pref("gecko.handlerService.schemes.webcal.3.name", "");
user_pref("gecko.handlerService.schemes.webcal.3.uriTemplate", "");
user_pref("general.useragent.compatMode", 0);
user_pref("general.useragent.compatMode.firefox", false);
user_pref("general.useragent.compatMode.gecko", false);
user_pref("general.useragent.compatMode.version", "");
user_pref("general.useragent.site_specific_overrides", false);
user_pref("general.useragent.updates.enabled", false);
user_pref("general.useragent.updates.interval", 0);
user_pref("general.useragent.updates.lastupdated", "0");
user_pref("general.useragent.updates.retry", 0);
user_pref("general.useragent.updates.url", "");
user_pref("general.warnOnAboutConfig", false);
user_pref("geo.enabled", false);
user_pref("geo.wifi.uri", "");
user_pref("gestures.enable_single_finger_input", false);
user_pref("gfx.blacklist.canvas2d.acceleration.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.direct2d.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.direct3d11angle.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.hardwarevideodecoding.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.layers.direct3d10-1.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.layers.direct3d10.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.layers.direct3d11.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.layers.direct3d9.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.layers.opengl.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.stagefright.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.webgl.angle.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.webgl.msaa.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.webgl.opengl.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.webrtc.hw.acceleration.decode.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.webrtc.hw.acceleration.encode.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.blacklist.webrtc.hw.acceleration.failureid", "FEATURE_FAILURE_OPENGL_1");
user_pref("gfx.canvas.skiagl.dynamic-cache", false);
user_pref("gfx.direct2d.disabled", true);
user_pref("gfx.downloadable_fonts.disable_cache", true);
user_pref("gfx.downloadable_fonts.enabled", false);
user_pref("gfx.downloadable_fonts.woff2.enabled", false);
user_pref("identity.fxaccounts.auth.uri", "");
user_pref("idle.lastDailyNotification", 1599826369);
user_pref("image.cache.size", 0);
user_pref("intl.accept_languages", "en-us");
user_pref("intl.charset.fallback.override", "UTF-8");
user_pref("javascript.enabled", false);
user_pref("javascript.options.wasm", false);
user_pref("javascript.options.wasm_baselinejit", false);
user_pref("keyword.enabled", false);
user_pref("layers.shared-buffer-provider.enabled", false);
user_pref("layout.css.font-loading-api.enabled", false);
user_pref("layout.css.prefixes.font-features", false);
user_pref("layout.css.visited_links_enabled", false);
user_pref("layout.spellcheckDefault", 0);
user_pref("lightweightThemes.update.enabled", false);
user_pref("mathml.disabled", true);
user_pref("media.autoplay.enabled", false);
user_pref("media.cache_size", 0);
user_pref("media.decoder-doctor.notifications-allowed", "");
user_pref("media.encoder.webm.enabled", false);
user_pref("media.ffmpeg.enabled", false);
user_pref("media.getusermedia.screensharing.allowed_domains", "");
user_pref("media.getusermedia.screensharing.enabled", false);
user_pref("media.gmp-manager.certs.1.commonName", "");
user_pref("media.gmp-manager.certs.2.commonName", "");
user_pref("media.gmp-manager.url", "");
user_pref("media.hardware-video-decoding.enabled", false);
user_pref("media.mediasource.enabled", false);
user_pref("media.mediasource.mp4.enabled", false);
user_pref("media.mediasource.webm.audio.enabled", false);
user_pref("media.mediasource.webm.enabled", false);
user_pref("media.mp4.enabled", false);
user_pref("media.ogg.enabled", false);
user_pref("media.ogg.flac.enabled", false);
user_pref("media.ondevicechange.enabled", false);
user_pref("media.opus.enabled", false);
user_pref("media.play-stand-alone", false);
user_pref("media.seekToNextFrame.enabled", false);
user_pref("media.video-queue.default-size", 0);
user_pref("media.video_stats.enabled", false);
user_pref("media.wave.enabled", false);
user_pref("media.webaudio.enabled", false);
user_pref("media.webm.enabled", false);
user_pref("network.allow-experiments", false);
user_pref("network.cookie.cookieBehavior", 2);
user_pref("network.cookie.lifetimePolicy", 2);
user_pref("network.cookie.prefsMigrated", true);
user_pref("network.dns.blockDotOnion", false);
user_pref("network.dns.disableIPv6", true);
user_pref("network.dnsCacheEntries", 0);
user_pref("network.http.accept.default", "application/xml,application/xhtml+xml,text/html;q=0.9,text/plain;q=0.8,image/png,*/*;q=0.5");
user_pref("network.http.max-connections", 16);
user_pref("network.http.pipelining", false);
user_pref("network.http.pipelining.reschedule-on-timeout", false);
user_pref("network.http.pipelining.ssl", false);
user_pref("network.http.referer.XOriginPolicy", 2);
user_pref("network.http.referer.spoofSource", true);
user_pref("network.http.referer.trimmingPolicy", 2);
user_pref("network.http.sendRefererHeader", 0);
user_pref("network.http.spdy.allow-push", false);
user_pref("network.http.spdy.coalesce-hostnames", false);
user_pref("network.notify.IPv6", false);
user_pref("network.protocol-handler.warn-external-default", false);
user_pref("network.proxy.no_proxies_on", ".pro-linux.de, .rpmfind.net, .palemoon.org");
user_pref("network.proxy.socks", "127.0.0.1");
user_pref("network.proxy.socks_port", 9050);
user_pref("network.proxy.type", 1);
user_pref("network.websocket.max-connections", 1);
user_pref("network.websocket.max-message-size", 1);
user_pref("network.websocket.timeout.close", 1);
user_pref("network.websocket.timeout.open", 1);
user_pref("network.websocket.timeout.ping.response", 1);
user_pref("noscript.ABE.cspHeaderDelim", "ABE0-28605766426066737");
user_pref("noscript.ABE.migration", 1);
user_pref("noscript.ABE.wanIpCheckURL", "");
user_pref("noscript.allowHttpsOnly", 2);
user_pref("noscript.allowWhitelistUpdates", false);
user_pref("noscript.cascadePermissions", true);
user_pref("noscript.clearClick.exceptions", "");
user_pref("noscript.clearClick.subexceptions", "");
user_pref("noscript.contentBlocker", true);
user_pref("noscript.default", "about:blank about:pocket-signup about:pocket-saved");
user_pref("noscript.filterXExceptions", "^https?://[a-z]+\.wikipedia\.org/wiki/[^\"<>?%]+$
");
user_pref("noscript.firstRunRedirection", false);
user_pref("noscript.firstRunRedirection.pending", "5.1.8.7");
user_pref("noscript.fixLinks", false);
user_pref("noscript.forbidBGRefresh.exceptions", "");
user_pref("noscript.forbidBookmarklets", true);
user_pref("noscript.forbidIFrames", true);
user_pref("noscript.forbidMetaRefresh", true);
user_pref("noscript.forbidMetaRefresh.exceptions", "");
user_pref("noscript.forbidWebGL", true);
user_pref("noscript.frameOptions.parentWhitelist", "");
user_pref("noscript.global", true);
user_pref("noscript.gtemp", "");
user_pref("noscript.httpsForced", "*");
user_pref("noscript.httpsForcedBuiltIn", "");
user_pref("noscript.httpsForcedExceptions", "mirror.centos.org
ftp.scientificlinux.org
ftp.pbone.net
ftp.ntua.gr
archive.ubuntu.com
");
user_pref("noscript.ignorePorts", false);
user_pref("noscript.inclusionTypeChecking.exceptions", "");
user_pref("noscript.notify", false);
user_pref("noscript.notify.bottom", false);
user_pref("noscript.notify.hide", true);
user_pref("noscript.notify.hideDelay", 2);
user_pref("noscript.options.tabSelectedIndexes", "1,1,2");
user_pref("noscript.restrictSubdocScripting", true);
user_pref("noscript.showAddress", true);
user_pref("noscript.showDomain", true);
user_pref("noscript.siteInfoProvider", "");
user_pref("noscript.statusLabel", true);
user_pref("noscript.subscription.lastCheck", 2112788290);
user_pref("noscript.surrogate.360Haven.sources", "");
user_pref("noscript.surrogate.ab_adsense.sources", "");
user_pref("noscript.surrogate.ab_adtiger.sources", "");
user_pref("noscript.surrogate.ab_bidvertiser.sources", "");
user_pref("noscript.surrogate.ab_binlayer.sources", "");
user_pref("noscript.surrogate.ab_mirago.sources", "");
user_pref("noscript.surrogate.ab_mirando.sources", "");
user_pref("noscript.surrogate.adagionet.sources", "");
user_pref("noscript.surrogate.addthis.sources", "");
user_pref("noscript.surrogate.adfly.sources", "");
user_pref("noscript.surrogate.amo.sources", "");
user_pref("noscript.surrogate.digg.sources", "");
user_pref("noscript.surrogate.dimtus.sources", "");
user_pref("noscript.surrogate.disqus-theme.sources", "");
user_pref("noscript.surrogate.ga.sources", "");
user_pref("noscript.surrogate.gigya.sources", "");
user_pref("noscript.surrogate.glinks.sources", "");
user_pref("noscript.surrogate.googleThumbs.sources", "");
user_pref("noscript.surrogate.googletag.sources", "");
user_pref("noscript.surrogate.gravatar.sources", "");
user_pref("noscript.surrogate.imagebam.sources", "");
user_pref("noscript.surrogate.imagebunk.sources", "");
user_pref("noscript.surrogate.imdb.sources", "");
user_pref("noscript.surrogate.imgreserve.sources", "");
user_pref("noscript.surrogate.interstitialBox.sources", "");
user_pref("noscript.surrogate.invodo.sources", "");
user_pref("noscript.surrogate.microsoftSupport.sources", "");
user_pref("noscript.surrogate.nscookie.sources", "");
user_pref("noscript.surrogate.picbucks.sources", "");
user_pref("noscript.surrogate.picsee.sources", "");
user_pref("noscript.surrogate.plusone.sources", "");
user_pref("noscript.surrogate.popunder.exceptions", "");
user_pref("noscript.surrogate.qs.sources", "");
user_pref("noscript.surrogate.skimlinks.sources", "");
user_pref("noscript.surrogate.stripe.sources", "");
user_pref("noscript.surrogate.twitter.sources", "");
user_pref("noscript.surrogate.uniblue.sources", "");
user_pref("noscript.surrogate.yieldman.sources", "");
user_pref("noscript.temp", "");
user_pref("noscript.untrusted", "127777.com ad-js.chip.de addthis.com admeira.ch adnxs.com adobedtm.com adrivo.com ads-twitter.com adsafeprotected.com adscale.de adserver.trojaner-info.de adtech.de adtm.chip.de ajax.googleapis.com akamaihd.net amazon-adsystem.com apa.at aspnetcdn.com assets-cdn.github.com assets.mtb-news.de assets.pons.com backbeatmedia.com bdi-services.de bf-ad.net bf-tools.net bootstrapcdn.com braintreegateway.com brightcove.net btstatic.com byu.edu cbsistatic.com cdn-dena.com cdn3.tekrevue.com cdn6.wn.com chartbeat.com clicktripz.com cloudflare.com cmp2.pcwelt.de cookielaw.org coveo.com d2zv5rkii46miq.cloudfront.net dealer.com deviantart.net disqus.com dropbox.com dynamicyield.com ensighten.com epfl.ch epoq.de etracker.com facebook.net fastly-insights.com filestorage.chip.de fontawesome.com geoedge.be go-mpulse.net google-analytics.com google.com googleadservices.com googlesyndication.com googletagmanager.com googletagservices.com gravatar.com gstatic.com h-bid.com hs-scripts.com hscta.net indexww.com instagram.com ioam.de jobs.net jquery.com jumpstarttaggingsolutions.com ligatus.com lots.co.in lp4.io maps.googleapis.com maxcdn.com mhcache.com mps-gba.de myvisualiq.net neads.delivery netdna-ssl.com onesignal.com onthe.io openx.net opinary.com opta.net optimizely.com outbrain.com p7s1.com parastorage.com permutive.com pinterest.com pixel-static.spotify.com polldaddy.com pololu-files.com polyfill.io ravenjs.com redhat.com regmedia.co.uk reutersmedia.net s2-prod.cornwalllive.com s3.reutersmedia.net s4.reutersmedia.net scdn.co sekindo.com servedby-buysellads.com shareaholic.com sharethis.com siteswithcontent.com skimresources.com smartredirect.de speedcurve.com static.ancientfaces.com static.zdassets.com staticcontent.fxstreet.com stats.wp.com stripe.com stroeerdigitalgroup.de subscribers.com teads.tv thomsonreuters.com tinypass.com tiqcdn.com tm-awx.com twimg.com twitter.com typekit.net usercentrics.eu vi-serve.com webmasterplan.com wordpress.com wp.com www.google.com www.instagram.com www8.hp.com yieldlove.com youtube.com zdassets.com zendesk.com http://127777.com http://addthis.com http://admeira.ch http://adnxs.com http://adobedtm.com http://adrivo.com http://ads-twitter.com http://adsafeprotected.com http://adscale.de http://adtech.de http://akamaihd.net http://amazon-adsystem.com http://apa.at http://aspnetcdn.com http://backbeatmedia.com http://bdi-services.de http://bf-ad.net http://bf-tools.net http://bootstrapcdn.com http://braintreegateway.com http://brightcove.net http://btstatic.com http://byu.edu http://cbsistatic.com http://cdn-dena.com http://chartbeat.com http://clicktripz.com http://cloudflare.com http://cookielaw.org http://coveo.com http://dealer.com http://deviantart.net http://disqus.com http://dropbox.com http://dynamicyield.com http://ensighten.com http://epfl.ch http://epoq.de http://etracker.com http://facebook.net http://fastly-insights.com http://fontawesome.com http://geoedge.be http://go-mpulse.net http://google-analytics.com http://google.com http://googleadservices.com http://googlesyndication.com http://googletagmanager.com http://googletagservices.com http://gravatar.com http://gstatic.com http://h-bid.com http://hs-scripts.com http://hscta.net http://indexww.com http://instagram.com http://ioam.de http://jobs.net http://jquery.com http://jumpstarttaggingsolutions.com http://ligatus.com http://lp4.io http://maxcdn.com http://mhcache.com http://mps-gba.de http://myvisualiq.net http://neads.delivery http://netdna-ssl.com http://onesignal.com http://onthe.io http://openx.net http://opinary.com http://opta.net http://optimizely.com http://outbrain.com http://p7s1.com http://parastorage.com http://permutive.com http://pinterest.com http://polldaddy.com http://pololu-files.com http://polyfill.io http://ravenjs.com http://redhat.com http://reutersmedia.net http://scdn.co http://sekindo.com http://servedby-buysellads.com http://shareaholic.com http://sharethis.com http://siteswithcontent.com http://skimresources.com http://smartredirect.de http://speedcurve.com http://stripe.com http://stroeerdigitalgroup.de http://subscribers.com http://teads.tv http://thomsonreuters.com http://tinypass.com http://tiqcdn.com http://tm-awx.com http://twimg.com http://twitter.com http://typekit.net http://usercentrics.eu http://vi-serve.com http://webmasterplan.com http://wordpress.com http://wp.com http://yieldlove.com http://youtube.com http://zdassets.com http://zendesk.com https://127777.com https://addthis.com https://admeira.ch https://adnxs.com https://adobedtm.com https://adrivo.com https://ads-twitter.com https://adsafeprotected.com https://adscale.de https://adserver.idg.de https://adtech.de https://akamaihd.net https://amazon-adsystem.com https://apa.at https://aspnetcdn.com https://backbeatmedia.com https://bdi-services.de https://bf-ad.net https://bf-tools.net https://bootstrapcdn.com https://braintreegateway.com https://brightcove.net https://btstatic.com https://byu.edu https://cbsistatic.com https://cdn-client.medium.com https://cdn-dena.com https://cdn.afterdawn.fi https://cdn.netzpolitik.org https://chartbeat.com https://clicktripz.com https://cloudflare.com https://cmp.chip.de https://cmp.focus.de https://cookielaw.org https://coveo.com https://dealer.com https://deviantart.net https://dialogue.sp-prod.net https://disqus.com https://dr.habracdn.net https://dropbox.com https://dynamicyield.com https://ensighten.com https://epfl.ch https://epoq.de https://etracker.com https://facebook.net https://fastly-insights.com https://fontawesome.com https://geoedge.be https://go-mpulse.net https://google-analytics.com https://google.com https://googleadservices.com https://googlesyndication.com https://googletagmanager.com https://googletagservices.com https://gravatar.com https://gstatic.com https://h-bid.com https://hs-scripts.com https://hscta.net https://hsto.org https://indexww.com https://instagram.com https://ioam.de https://jobs.net https://jquery.com https://jumpstarttaggingsolutions.com https://ligatus.com https://lp4.io https://maxcdn.com https://mhcache.com https://mps-gba.de https://myvisualiq.net https://neads.delivery https://netdna-ssl.com https://onesignal.com https://onthe.io https://openx.net https://opinary.com https://opta.net https://optimizely.com https://outbrain.com https://p7s1.com https://parastorage.com https://permutive.com https://pinterest.com https://polldaddy.com https://pololu-files.com https://polyfill.io https://ravenjs.com https://redhat.com https://reutersmedia.net https://s3-eu-central-1.amazonaws.com https://s3.amazonaws.com https://scdn.co https://sekindo.com https://servedby-buysellads.com https://shareaholic.com https://sharethis.com https://siteswithcontent.com https://skimresources.com https://smartredirect.de https://speedcurve.com https://static.cdn.prismic.io https://static.cleverpush.com https://static.criteo.net https://static.faz.net https://static.zeit.de https://stripe.com https://stroeerdigitalgroup.de https://subscribers.com https://teads.tv https://thomsonreuters.com https://tinypass.com https://tiqcdn.com https://tm-awx.com https://twimg.com https://twitter.com https://typekit.net https://unpkg.com https://usercentrics.eu https://vi-serve.com https://webmasterplan.com https://wordpress.com https://wp.com https://www.afterdawn.dk https://www.tagesschau.de https://yieldlove.com https://youtube.com https://zdassets.com https://zdwidget3-bs.sphereup.com https://zendesk.com");
user_pref("noscript.version", "2.9.0.13");
user_pref("noscript.visibleUIChecked", true);
user_pref("noscript.xss.checkInclusions.exceptions", "");
user_pref("offline-apps.allow_by_default", false);
user_pref("offline-apps.permissions", 0);
user_pref("permissions.default.image", 3);
user_pref("permissions.default.object", 3);
user_pref("permissions.default.script", 3);
user_pref("permissions.default.stylesheet", 3);
user_pref("permissions.default.subdocument", 3);
user_pref("places.database.lastMaintenance", 1599512467);
user_pref("places.frecency.unvisitedBookmarkBonus", 0);
user_pref("places.history.enabled", false);
user_pref("places.history.expiration.transient_current_max_pages", 22381);
user_pref("plugin.default.state", 0);
user_pref("plugins.click_to_play", false);
user_pref("plugins.update.url", "");
user_pref("pref.browser.language.disable_button.down", false);
user_pref("pref.general.disable_button.default_browser", false);
user_pref("pref.privacy.disable_button.cookie_exceptions", false);
user_pref("print.print_bgcolor", false);
user_pref("print.print_bgimages", false);
user_pref("print.print_duplex", 0);
user_pref("print.print_evenpages", true);
user_pref("print.print_in_color", true);
user_pref("print.print_margin_bottom", "0.5");
user_pref("print.print_margin_left", "0.5");
user_pref("print.print_margin_right", "0.5");
user_pref("print.print_margin_top", "0.5");
user_pref("print.print_oddpages", true);
user_pref("print.print_orientation", 0);
user_pref("print.print_page_delay", 50);
user_pref("print.print_paper_data", 0);
user_pref("print.print_paper_height", " 11,69");
user_pref("print.print_paper_name", "iso_a4");
user_pref("print.print_paper_size_unit", 0);
user_pref("print.print_paper_width", " 8,27");
user_pref("print.print_scaling", " 1,00");
user_pref("print.print_shrink_to_fit", true);
user_pref("print.print_to_file", false);
user_pref("print.print_to_filename", "/home/secret/Dokumente/mozilla.pdf");
user_pref("print.print_unwriteable_margin_bottom", 56);
user_pref("print.print_unwriteable_margin_left", 25);
user_pref("print.print_unwriteable_margin_right", 25);
user_pref("print.print_unwriteable_margin_top", 25);
user_pref("print_printer", "Brother-DCP-115C");
user_pref("privacy.clearOnShutdown.connectivityData", true);
user_pref("privacy.clearOnShutdown.offlineApps", true);
user_pref("privacy.clearOnShutdown.passwords", true);
user_pref("privacy.clearOnShutdown.siteSettings", true);
user_pref("privacy.cpd.connectivityData", true);
user_pref("privacy.cpd.offlineApps", true);
user_pref("privacy.cpd.passwords", true);
user_pref("privacy.cpd.siteSettings", true);
user_pref("privacy.donottrackheader.enabled", true);
user_pref("privacy.donottrackheader.value", 1);
user_pref("privacy.item.cookies", true);
user_pref("privacy.popups.disable_from_plugins", 3);
user_pref("privacy.popups.showBrowserMessage", false);
user_pref("privacy.sanitize.didShutdownSanitize", true);
user_pref("privacy.sanitize.migrateFx3Prefs", true);
user_pref("privacy.sanitize.sanitizeOnShutdown", true);
user_pref("privacy.sanitize.timeSpan", 0);
user_pref("privacy.trackingprotection.enabled", true);
user_pref("privacy.trackingprotection.pbmode.enabled", true);
user_pref("privacy.trackingprotection.ui.enabled", true);
user_pref("privacy.userContext.enabled", false);
user_pref("privacy.userContext.longPressBehavior", 0);
user_pref("privacy.userContext.ui.enabled", true);
user_pref("reader.parse-on-load.enabled", false);
user_pref("security.OCSP.enabled", 0);
user_pref("security.cert_pinning.hpkp.enabled", true);
user_pref("security.csp.experimentalEnabled", true);
user_pref("security.disable_button.openCertManager", false);
user_pref("security.disable_button.openDeviceManager", false);
user_pref("security.remember_cert_checkbox_default_setting", false);
user_pref("security.ssl.errorReporting.url", "");
user_pref("security.ssl.require_safe_negotiation", true);
user_pref("security.ssl3.dhe_rsa_camellia_128_sha", false);
user_pref("security.ssl3.ecdhe_ecdsa_aes_128_sha", false);
user_pref("security.ssl3.ecdhe_rsa_aes_128_sha", false);
user_pref("security.ssl3.rsa_aes_128_sha", false);
user_pref("security.tls.version.min", 3);
user_pref("security.xcto_nosniff_block_images", true);
user_pref("security.xpconnect.plugin.unrestricted", false);
user_pref("services.sync.addons.trustedSourceHostnames", "");
user_pref("services.sync.clients.lastSync", "0");
user_pref("services.sync.clients.lastSyncLocal", "0");
user_pref("services.sync.declinedEngines", "");
user_pref("services.sync.fxa.privacyURL", "");
user_pref("services.sync.fxa.termsURL", "");
user_pref("services.sync.globalScore", 0);
user_pref("services.sync.jpake.serverURL", "");
user_pref("services.sync.lastversion", "1.54.1");
user_pref("services.sync.log.appender.console", "Error");
user_pref("services.sync.migrated", true);
user_pref("services.sync.miscURL", "");
user_pref("services.sync.nextSync", 0);
user_pref("services.sync.outdated.url", "");
user_pref("services.sync.prefs.sync.dom.event.contextmenu.enabled", false);
user_pref("services.sync.prefs.sync.extensions.ematrix.cloudStorage.myRulesPane", true);
user_pref("services.sync.privacyURL", "");
user_pref("services.sync.serverURL", "");
user_pref("services.sync.statusURL", "");
user_pref("services.sync.syncKeyHelpURL", "");
user_pref("services.sync.tabs.lastSync", "0");
user_pref("services.sync.tabs.lastSyncLocal", "0");
user_pref("services.sync.termsURL", "");
user_pref("services.sync.tokenServerURI", "");
user_pref("signon.autologin.proxy", true);
user_pref("signon.formlessCapture.enabled", false);
user_pref("signon.importedFromSqlite", true);
user_pref("signon.rememberSignons", false);
user_pref("startup.homepage_override_url", "");
user_pref("startup.homepage_welcome_url", "");
user_pref("status4evar.advanced.status.detectVideo", false);
user_pref("status4evar.firstRun", false);
user_pref("status4evar.migration", 8);
user_pref("storage.vacuum.last.index", 1);
user_pref("storage.vacuum.last.places.sqlite", 1598197230);
user_pref("svg.display-lists.hit-testing.enabled", false);
user_pref("svg.display-lists.painting.enabled", false);
user_pref("svg.in-content.enabled", false);
user_pref("svg.marker-improvements.enabled", false);
user_pref("svg.path-caching.enabled", false);
user_pref("svg.transform-box.enabled", true);
user_pref("toolkit.startup.last_success", 1599840550);
user_pref("toolkit.telemetry.reportingpolicy.firstRun", false);
user_pref("webextensions.storage.sync.serverURL", "");
user_pref("webgl.disable-DOM-blit-uploads", true);
user_pref("webgl.disable-angle", true);
user_pref("webgl.disable-extensions", true);
user_pref("webgl.disable-fail-if-major-performance-caveat", true);
user_pref("webgl.disable-wgl", true);
user_pref("webgl.disabled", true);
user_pref("webgl.min_capability_mode", true);
user_pref("webgl.restore-context-when-visible", false);
user_pref("xpinstall.whitelist.add", "");
user_pref("xpinstall.whitelist.required", true);
/usr/lib64/firefox/distribution/policies.json, examples and explanation see wiki.kairaven.de
//
user.js (with some internal changes by us, Gooken) from https://www.ghacks.net/2015/08/18/a-comprehensive-list-of-firefox-privacy-and-security-settings/
/******
* name: ghacks user.js
* date: 11 Feb 2017
* version: 0.11 FINAL : The [White?] House of the Rising Pants,
* NOTICE: GOOKEN MADE SOME INTERNAL CHANGES!!!
* "My mother was a tailor, she sewed my new blue pants"
* FF version: 51 (DESKTOP)
* authors: FLOTUS: Pants
VICE PRESIDENT: earthling (birth certificate on request)
SECRETARY: Martin Brinkmann
SPEAKER: Tom Hawack
CABINET: Just me, Conker, Rockin´ Jerry, Ainatar, Parker Lewis
* url: http://www.ghacks.net/2015/08/18/a-comprehensive-list-of-firefox-privacy-and-security-settings/
* required reading: http://kb.mozillazine.org/User.js_file
* README/IMPORTANT:
<font color=#ff3333>End users of this list/file are expected to know what they are doing. These are the author´s
settings. The author does NOT expect (or indeed want) end users to just run with it as is.
Use it as a comprehensive list, or as a template for your own.</font> Extensive links and comments
have been added to help. Before using this user.js, if necessary, you should change, remove or
comment out with two forward slashes any preferences you´re not happy with or not sure about.
The settings in this file (user.js) OVERWRITE the ones in your prefs (prefs.js - these are
accessed via about:config) when FF is started. See the required reading above.
* BACKUP FIRST:
Backup your profile first, or even just the PREFS.JS. Go to your profile directory and copy
prefs.js, rename it (eg to prefs.js.backup). That way, if you have problems, to restore FF
to the state it was in beforehand, close FF, delete the prefs.js, rename your backup copy of
prefs back to prefs.js, RENAME the user.js so it doesn´t overwrite everything again, then
start FF. IF you have any problems, you can also ask in the comments at ghacks.
* PURPOSE:
This is not a "comprehensive" list of ALL things privacy/security (otherwise it would be huge)
It is more like a list of settings that generally differ from their defaults, and is aimed at
improving security and privacy, at making a "quieter" FF, and at reducing fingerprinting and
tracking, while allowing functionality. There will be trade-offs and conflicts between these.
* COMMON ISSUES:
Some prefs will break some sites (it´s inevitable). If you are having issues search for
"WARNING:" in this document, especially the ones listed just below.
<font color=#ff3333>This user.js uses the author´s settings, so you need to check these EACH release because
the author prefers anonymity, security, and privacy over functionality [eg being able to
paste in Facebook, downloadable fonts, and other minor inconveniences]. You have been warned.</font>
0202 &0204 &0207 &0208: search, language and locale settings
0903 &0904: master password (author set his up to last 5 minutes, default is once per session)
1007 &1008: disabling/reducing session store saves affects recently closed tabs history
1204: security.ssl.require_safe_negotiation
1206: security.OCSP.require
1208: security.cert_pinning.enforcement_level
1209: TLS min and max
1210: disable 1024-DH Encryption
1211: disable SHA-1
1212: disable SSL session tracking
1401 &1406: browser.display.use_document_fonts <font color=#ff3333>[author blocked fonts]</font>
1404: default fonts <font color=#ff3333>[author changed default fonts]</font>
1805: plugin.scan.plid.all <font color=#ff3333>[author blocked all plugins]</font>
1807: disable auto-play of HTML5 media (may break some sites´ playback)
2025: enable/disable media types <font color=#ff3333>[author´s settings, choose your own]</font>
2201: dom.event.contextmenu.enabled
2300´s: workers/service.workers/push notifications etc may affect twitter, street view and other sites
2402: dom.event.clipboardevents.enabled
2404: dom.indexedDB.enabled <font color=#ff3333>[author killed indexedDB]</font>
2415b: limit popup events
2421: two JS preferences that cause the odd issue (commented out, not worth the performance loss)
2507: keyboard fingerprinting (android + physical keyboard)
2508: hardware acceleration (performance vs lots of video, also fonts render differently)
<font color=#ff3333>[author killed hardware acceleration]</font>
2509: dom.w3c_touch_events.enabled (you will want to change this if you use touch)
2619: network.http.redirection-limit
2627: various User Agent and navigator objects
2662: browser.download.forbid_open_with
2698: privacy.firstparty.isolate
2705: dom.storage.enabled
* THANKS:
Special thanks to Martin Brinkmann and the ghacks community
Lots of websites, lots of people, too many to list but here are some excellent resources
- https://github.com/pyllyukko/user.js
- https://www.wilderssecurity.com/threads/firefox-lockdown.368003/
- http://12bytes.org/articles/tech/firefoxgecko-configuration-guide-for-privacy-and-performance-buffs
- https://www.privacy-handbuch.de/handbuch_21.htm (German)
******/
// START: internal custom pref to test for syntax errors (thanks earthling)
// Yes, this next pref setting is redundant, but I like it!
// https://en.wikipedia.org/wiki/Dead_parrot
// https://en.wikipedia.org/wiki/Warrant_canary
/*** 0100: STARTUP ***/
// 0101: disable "slow startup" options
// warnings, disk history, welcomes, intros, EULA, default browser check
user_pref("browser.slowStartup.notificationDisabled", true);
user_pref("browser.slowStartup.maxSamples", 0);
user_pref("browser.slowStartup.samples", 0);
user_pref("browser.rights.3.shown", true);
user_pref("browser.startup.homepage_override.mstone", "ignore");
user_pref("startup.homepage_welcome_url", "");
user_pref("startup.homepage_welcome_url.additional", "");
user_pref("startup.homepage_override_url", "");
user_pref("browser.laterrun.enabled", false);
user_pref("browser.shell.checkDefaultBrowser", false);
user_pref("browser.usedOnWindows10.introURL", "");
// 0102: set start page (0=blank, 1=home, 2=last visited page, 3=resume previous session)
// home = browser.startup.homepage preference
// You can set all of this from Options>General>Startup
// user_pref("browser.startup.page", 0);
/*** 0200: GEOLOCATION ***/
// 0201: disable location-aware browsing
user_pref("geo.enabled", false);
user_pref("geo.wifi.uri", "https://127.0.0.1");
user_pref("geo.wifi.logging.enabled", false);
// (hidden pref)
user_pref("browser.search.geoip.url", "");
user_pref("geo.wifi.xhr.timeout", 1);
user_pref("browser.search.geoip.timeout", 1);
// 0202: disable GeoIP-based search results
// NOTE: may not be hidden if Mozilla have changed your settings due to your locale
// https://trac.torproject.org/projects/tor/ticket/16254
user_pref("browser.search.countryCode", "US");
// (hidden pref)
user_pref("browser.search.region", "US");
// (hidden pref)
// 0203: disable using OS locale, force APP locale
user_pref("intl.locale.matchOS", false);
// 0204: set APP local
user_pref("general.useragent.locale", "en-US");
// 0206: disable geographically specific results/search engines eg: "browser.search.*.US"
// i.e ignore all of Mozilla´s multiple deals with multiple engines in multiple locales
user_pref("browser.search.geoSpecificDefaults", false);
user_pref("browser.search.geoSpecificDefaults.url", "");
// 0207: set language to match
// WARNING: reset this to your default if you don´t want English
user_pref("intl.accept_languages", "en-US, en");
// 0208: enforce US English locale regardless of the system locale
// https://bugzilla.mozilla.org/show_bug.cgi?id=867501
user_pref("javascript.use_us_english_locale", true);
// (hidden pref)
/*** 0300: QUIET FOX [PART 1]
No auto-phoning home for anything. You can still do manual updates. It is still important
to do updates for security reasons. If you don´t auto update, make sure you do manually.
There are many legitimate reasons to turn off AUTO updates, including hijacked monetized
extensions, time constraints, legacy issues, and fear of breakage/bugs ***/
// 0301: disable browser auto update
// Options>Advanced>Update>Never check for updates
user_pref("app.update.enabled", false);
// Options>Advanced>Update>Use a background service to install updates
user_pref("app.update.service.enabled", false);
// ensure update information is not suppressed
user_pref("app.update.silent", false);
// disable background update staging
user_pref("app.update.staging.enabled", false);
// 0302: disable browser auto installing update when you do a manual check
user_pref("app.update.auto", false);
// 0303: disable search update (Options>Advanced>Update>Automatically update: search engines)
user_pref("browser.search.update", false);
// 0304: disable add-ons auto checking for new versions
user_pref("extensions.update.enabled", false);
// 0305: disable add-ons auto update
user_pref("extensions.update.autoUpdateDefault", false);
// 0306: disable add-on metadata updating
// sends daily pings to Mozilla about extensions and recent startups
user_pref("extensions.getAddons.cache.enabled", false);
// 0307: disable auto updating of personas (themes)
user_pref("lightweightThemes.update.enabled", false);
// 0309: disable sending Flash crash reports
user_pref("dom.ipc.plugins.flash.subprocess.crashreporter.enabled", false);
// 0310: disable sending the URL of the website where a plugin crashed
user_pref("dom.ipc.plugins.reportCrashURL", false);
// 0320: disable extension discovery
// featured extensions for displaying in Get Add-ons panel
user_pref("extensions.webservice.discoverURL", "http://127.0.0.1");
// 0330a: disable telemetry
// https://gecko.readthedocs.org/en/latest/toolkit/components/telemetry/telemetry/preferences.html
// the pref (.unified) affects the behaviour of the pref (.enabled)
// IF unified=false then .enabled controls the telemetry module
// IF unified=true then .enabled ONLY controls whether to record extended data
// so make sure to have both set as false
user_pref("toolkit.telemetry.unified", false);
user_pref("toolkit.telemetry.enabled", false);
// 0330b: set unifiedIsOptIn to make sure telemetry respects OptIn choice and that telemetry
// is enabled ONLY for people that opted into it, even if unified Telemetry is enabled
user_pref("toolkit.telemetry.unifiedIsOptIn", true);
// (hidden pref)
// 0331: remove url of server telemetry pings are sent to
user_pref("toolkit.telemetry.server", "");
// 0332: disable archiving pings locally - irrelevant if toolkit.telemetry.unified is false
user_pref("toolkit.telemetry.archive.enabled", false);
// 0333a: disable health report
user_pref("datareporting.healthreport.uploadEnabled", false);
user_pref("datareporting.healthreport.documentServerURI", "");
// (hidden pref)
user_pref("datareporting.healthreport.service.enabled", false);
// (hidden pref)
// 0333b: disable about:healthreport page (which connects to Mozilla for locale/css+js+json)
// If you have disabled health reports, then this about page is useless - disable it
// If you want to see what health data is present, then these must be set at default
user_pref("datareporting.healthreport.about.reportUrl", "data:text/plain,");
// 0334a: disable new data submission, master kill switch (FF41+)
// If disabled, no policy is shown or upload takes place, ever
// https://bugzilla.mozilla.org/show_bug.cgi?id=1195552
user_pref("datareporting.policy.dataSubmissionEnabled", false);
// 0335: remove a telemetry clientID
// if you haven´t got one, be proactive and set it now for future proofing
user_pref("toolkit.telemetry.cachedClientID", "");
// 0336: disable "Heartbeat" (Mozilla user rating telemetry)
// https://trac.torproject.org/projects/tor/ticket/18738
user_pref("browser.selfsupport.enabled", false);
// (hidden pref)
user_pref("browser.selfsupport.url", "");
// 0340: disable experiments
// https://wiki.mozilla.org/Telemetry/Experiments
user_pref("experiments.enabled", false);
user_pref("experiments.manifest.uri", "");
user_pref("experiments.supported", false);
user_pref("experiments.activeExperiment", false);
// 0341: disable Mozilla permission to silently opt you into tests
user_pref("network.allow-experiments", false);
// 0350: disable crash reports
user_pref("breakpad.reportURL", "");
// 0351: disable sending of crash reports (FF44+)
user_pref("browser.tabs.crashReporting.sendReport", false);
// 0360: disable new tab tile ads &preload &marketing junk
user_pref("browser.newtab.preload", false);
user_pref("browser.newtabpage.directory.ping", "data:text/plain,");
user_pref("browser.newtabpage.directory.source", "data:text/plain,");
user_pref("browser.newtabpage.enabled", false);
user_pref("browser.newtabpage.enhanced", false);
user_pref("browser.newtabpage.introShown", true);
// 0370: disable "Snippets" (Mozilla content shown on about:home screen)
// https://wiki.mozilla.org/Firefox/Projects/Firefox_Start/Snippet_Service
// MUST use HTTPS - arbitrary content injected into this page via http opens up MiTM attacks
user_pref("browser.aboutHomeSnippets.updateUrl", "https://127.0.0.1");
// 0373: disable "Pocket" (third party "save for later" service) &remove urls for good measure
// NOTE: Important: Remove the pocket icon from your toolbar first
// https://www.gnu.gl/blog/Posts/multiple-vulnerabilities-in-pocket/
user_pref("extensions.pocket.enabled", false);
user_pref("extensions.pocket.api", "");
user_pref("extensions.pocket.site", "");
user_pref("extensions.pocket.oAuthConsumerKey", "");
// 0374: disable "social" integration
// https://developer.mozilla.org/en-US/docs/Mozilla/Projects/Social_API
user_pref("social.whitelist", "");
user_pref("social.toast-notifications.enabled", false);
user_pref("social.shareDirectory", "");
user_pref("social.remote-install.enabled", false);
user_pref("social.directories", "");
user_pref("social.share.activationPanelEnabled", false);
user_pref("social.enabled", false);
// (hidden pref)
// 0375: disable "Reader View"
user_pref("reader.parse-on-load.enabled", false);
// 0376: disable FlyWeb, a set of APIs for advertising and discovering local-area web servers
// https://wiki.mozilla.org/FlyWeb
// http://www.ghacks.net/2016/07/26/firefox-flyweb/
user_pref("dom.flyweb.enabled", false);
// 0380: disable sync
user_pref("services.sync.enabled", false);
// (hidden pref)
/*** 0400: QUIET FOX [PART 2]
This section has security &tracking protection implications vs privacy concerns.
These settings are geared up to make FF "quiet" &private. I am NOT advocating no protection.
If you turn these off, then by all means please use something superior, such as uBlock Origin.
<font color=#ff3333>IMPORTANT: This entire section is rather contentious. Safebrowsing is designed to protect
users from malicious sites. Tracking protection is designed to lessen the impact of third
parties on websites to reduce tracking and to speed up your browsing experience. These are
both very good features provided by Mozilla. They do rely on third parties: Google for
safebrowsing and Disconnect for tracking protection (someone has to provide the information).
Additionally, SSL Error Reporting helps makes the internet more secure for everyone.
If you do not understand the ramifications of disabling all of these, then it is advised that
you enable them by commenting out the preferences and saving the changes, and then in
about:config find each entry and right-click and reset the preference´s value.</font> ***/
// 0401: DON´T disable extension blocklist, but sanitize blocklist url - SECURITY
// It now includes updates for "revoked certificates" - security trumps privacy here
// https://blog.mozilla.org/security/2015/03/03/revoking-intermediate-certificates-introducing-onecrl
// https://trac.torproject.org/projects/tor/ticket/16931
user_pref("extensions.blocklist.enabled", true);
user_pref("extensions.blocklist.url", "https://blocklist.addons.mozilla.org/blocklist/3/%APP_ID%/%APP_VERSION%/");
// 0402: disable/enable various Kinto blocklist updates (FF50+)
// What is Kinto?: https://wiki.mozilla.org/Firefox/Kinto#Specifications
// As FF transitions to Kinto, the blocklists have been broken down (more could be added). These contain
// block entries for certs to be revoked, add-ons and plugins to be disabled, and gfx environments that
// cause problems or crashes. Here you can remove the collection name to prevent each specific list updating
user_pref("services.blocklist.update_enabled", true);
user_pref("services.blocklist.signing.enforced", true);
user_pref("services.blocklist.onecrl.collection", "certificates");
// Revoked certificates
user_pref("services.blocklist.addons.collection", "addons");
user_pref("services.blocklist.plugins.collection", "");
// I have no plugins
user_pref("services.blocklist.gfx.collection", "");
// I have gfx hw acceleration disabled
// 0410: disable safe browsing
// I have redesigned this sub-section to differentiate between "real-time"/"user initiated"
// data being sent to Google from all other settings such as using local blocklists/whitelists
// and updating those lists. There SHOULD be NO privacy issues here. Even *IF* an URL was sent
// to Google, they swear it is anonymized and only used to flag malicious sites/activity. Firefox
// also takes measures such as striping out identifying parameters and storing safe browsing
// cookies in a separate jar. (#Turn on browser.safebrowsing.debug to monitor this activity)
// To use safebrowsing but not "leak" binary download info to Google, only use 0410e and 0410f
// #Required reading: https://feeding.cloud.geek.nz/posts/how-safe-browsing-works-in-firefox/
// https://wiki.mozilla.org/Security/Safe_Browsing
// 0410a: disable "Block dangerous and deceptive content" This setting is under Options>Security
// in FF47 and under this is was titled "Block reported web forgeries"
// this covers deceptive sites such as phishing and social engineering
user_pref("browser.safebrowsing.malware.enabled", false);
user_pref("browser.safebrowsing.phishing.enabled", false);
// (FF50+)
// 0410b: disable "Block dangerous downloads" This setting is under Options>Security
// in FF47 and under this was titled "Block reported attack sites"
// this covers malware and PUPs (potentially unwanted programs)
user_pref("browser.safebrowsing.downloads.enabled", false);
// disable "Warn me about unwanted and uncommon software" Also under Options>Security (FF48+)
user_pref("browser.safebrowsing.downloads.remote.block_potentially_unwanted", false);
user_pref("browser.safebrowsing.downloads.remote.block_uncommon", false);
// yet more prefs added (FF49+)
user_pref("browser.safebrowsing.downloads.remote.block_dangerous", false);
user_pref("browser.safebrowsing.downloads.remote.block_dangerous_host", false);
// 0410c: disable Google safebrowsing downloads, updates
user_pref("browser.safebrowsing.provider.google.updateURL", "");
// update google lists
user_pref("browser.safebrowsing.provider.google.gethashURL", "");
// list hash check
user_pref("browser.safebrowsing.provider.google4.updateURL", "");
// (FF50+)
user_pref("browser.safebrowsing.provider.google4.gethashURL", "");
// (FF50+)
// 0410d: disable mozilla safebrowsing downloads, updates
// NOTE: These two prefs are also used for Tracking Protection (see 0420)
user_pref("browser.safebrowsing.provider.mozilla.gethashURL", "");
// resolves hash conflicts
user_pref("browser.safebrowsing.provider.mozilla.updateURL", "");
// update FF lists
// 0410e: disable binaries NOT in local lists being checked by Google (real-time checking)
user_pref("browser.safebrowsing.downloads.remote.enabled", false);
user_pref("browser.safebrowsing.downloads.remote.url", "");
// 0410f: disable reporting URLs
user_pref("browser.safebrowsing.provider.google.reportURL", "");
user_pref("browser.safebrowsing.reportMalwareMistakeURL", "");
user_pref("browser.safebrowsing.reportPhishMistakeURL", "");
user_pref("browser.safebrowsing.reportPhishURL", "");
user_pref("browser.safebrowsing.provider.google4.reportURL", "");
// (FF50+)
// 0410g: show=true or hide=false the ´ignore this warning´ on Safe Browsing warnings which
// when clicked bypasses the block for that session. This is a means for admins to enforce SB
// https://bugzilla.mozilla.org/show_bug.cgi?id=1226490
// tests: see APPENDIX A: TEST SITES - Section 06
// user_pref("browser.safebrowsing.allowOverride", true);
// 0420: disable tracking protection
// There SHOULD be NO privacy concerns here, but you are better off using an extension such as
// uBlock Origin which is not decided by a third party (disconnect) and is far more effective
// (when used correctly). NOTE: There are two prefs (see 0410d) shared with Safe Browsing
// https://wiki.mozilla.org/Security/Tracking_protection
// https://support.mozilla.org/en-US/kb/tracking-protection-firefox
user_pref("privacy.trackingprotection.enabled", false);
// all windows pref (not just private)
user_pref("privacy.trackingprotection.pbmode.enabled", false);
// private browsing pref
// 0421: enable more Tracking Protection choices under Options>Privacy>Use Tracking Protection
user_pref("privacy.trackingprotection.ui.enabled", true);
// 0430: disable SSL Error Reporting - PRIVACY
// https://gecko.readthedocs.org/en/latest/browser/base/sslerrorreport/preferences.html
user_pref("security.ssl.errorReporting.automatic", false);
user_pref("security.ssl.errorReporting.enabled", false);
user_pref("security.ssl.errorReporting.url", "");
// 0440: disable Mozilla´s blocklist for known Flash tracking/fingerprinting (48+)
// If you don´t have Flash, then you don´t need this enabled
// NOTE: if enabled, you will need to check what prefs (safebrowsing URLs etc) this uses to update
// http://www.ghacks.net/2016/07/18/firefox-48-blocklist-against-plugin-fingerprinting/
// https://bugzilla.mozilla.org/show_bug.cgi?id=1237198
user_pref("browser.safebrowsing.blockedURIs.enabled", false);
/*** 0600: BLOCK IMPLICIT OUTBOUND [not explicitly asked for - eg clicked on] ***/
// 0601: disable link prefetching
// https://developer.mozilla.org/en-US/docs/Web/HTTP/Link_prefetching_FAQ
user_pref("network.prefetch-next", false);
// 0602: disable dns prefetching
// http://www.ghacks.net/2013/04/27/firefox-prefetching-what-you-need-to-know/
// https://developer.mozilla.org/en-US/docs/Web/HTTP/Controlling_DNS_prefetching
user_pref("network.dns.disablePrefetch", true);
user_pref("network.dns.disablePrefetchFromHTTPS", true);
// (hidden pref)
// 0603: disable Seer/Necko
// https://developer.mozilla.org/en-US/docs/Mozilla/Projects/Necko
user_pref("network.predictor.enabled", false);
// 0603a: disable more Necko/Captive Portal
// https://en.wikipedia.org/wiki/Captive_portal
// https://wiki.mozilla.org/Necko/CaptivePortal
user_pref("captivedetect.canonicalURL", "");
user_pref("network.captive-portal-service.enabled", false);
// (FF52+?)
// 0604: disable search suggestions
user_pref("browser.search.suggest.enabled", false);
// 0605: disable link-mouseover opening connection to linked server
// http://news.slashdot.org/story/15/08/14/2321202/how-to-quash-firefoxs-silent-requests
// http://www.ghacks.net/2015/08/16/block-firefox-from-connecting-to-sites-when-you-hover-over-links
user_pref("network.http.speculative-parallel-limit", 0);
// 0606: disable pings (but enforce same host in case)
// http://kb.mozillazine.org/Browser.send_pings
// http://kb.mozillazine.org/Browser.send_pings.require_same_host
user_pref("browser.send_pings", false);
user_pref("browser.send_pings.require_same_host", true);
// 0607: stop links launching Windows Store on Windows 8/8.1/10
// http://www.ghacks.net/2016/03/25/block-firefox-chrome-windows-store/
user_pref("network.protocol-handler.external.ms-windows-store", false);
// 0608: disable predictor / prefetching (FF48+)
user_pref("network.predictor.enable-prefetch", false);
/*** 0800: LOCATION BAR / SEARCH / AUTO SUGGESTIONS / HISTORY / FORMS etc
Not ALL of these are strictly needed, some are for the truly paranoid, but
included for a more comprehensive list (see comments on each one) ***/
// 0801: disable location bar using search - PRIVACY
// don´t leak typos to a search engine, give an error message instead
user_pref("keyword.enabled", false);
// 0802: disable location bar domain guessing - PRIVACY/SECURITY
// domain guessing intercepts DNS "hostname not found errors" and resends a
// request (eg by adding www or .com). This is inconsistent use (eg FQDNs), does not work
// via Proxy Servers (different error), is a flawed use of DNS (TLDs: why treat .com
// as the 411 for DNS errors?), privacy issues (why connect to sites you didn´t
// intend to), can leak sensitive data (eg query strings: eg Princeton attack),
// and is a security risk (eg common typos &malicious sites set up to exploit this)
user_pref("browser.fixup.alternate.enabled", false);
// 0803: disable locationbar dropdown - PRIVACY (shoulder surfers,forensics/unattended browser)
user_pref("browser.urlbar.maxRichResults", 0);
// 0804: display all parts of the url
// why rely on just a visual clue - helps SECURITY
user_pref("browser.urlbar.trimURLs", false);
// 0805: disable URLbar autofill - PRIVACY (shoulder surfers, forensics/unattended browser)
// http://kb.mozillazine.org/Inline_autocomplete
user_pref("browser.urlbar.autoFill", false);
user_pref("browser.urlbar.autoFill.typed", false);
// 0806: disable autocomplete - PRIVACY (shoulder surfers, forensics/unattended browser)
user_pref("browser.urlbar.autocomplete.enabled", false);
// 0808: disable history suggestions - PRIVACY (shoulder surfers, forensics/unattended browser)
user_pref("browser.urlbar.suggest.history", false);
// 0809: limit history leaks via enumeration (PER TAB: back/forward) - PRIVACY
// This is a PER TAB session history. You still have a full history stored under all history
// default=50, minimum=1=currentpage, 2 is the recommended minimum as some pages
// use it as a means of referral (eg hotlinking), 4 or 6 may be more practical
user_pref("browser.sessionhistory.max_entries", 4);
// 0810: disable css querying page history - css history leak - PRIVACY
// NOTE: this has NEVER been fully "resolved": in Mozilla/docs it is stated it´s only in
// ´certain circumstances´, also see latest comments in the bug link
// https://dbaron.org/mozilla/visited-privacy
// https://bugzilla.mozilla.org/show_bug.cgi?id=147777
// https://developer.mozilla.org/en-US/docs/Web/CSS/Privacy_and_the_:visited_selector
user_pref("layout.css.visited_links_enabled", false);
// 0811: disable displaying javascript in history URLs - SECURITY
user_pref("browser.urlbar.filter.javascript", true);
// 0812: disable search and form history
// Under Options>Privacy> if you set Firefox to "use custom settings" there will be a
// setting called "remember search and form history".
// You can clear formdata on exiting Firefox (see 2803)
// user_pref("browser.formfill.enable", false);
// 0813: disable saving form data on secure websites - PRIVACY (shoulder surfers etc)
// For convenience &functionality, this is best left at default true.
// You can clear formdata on exiting Firefox (see 2803)
// user_pref("browser.formfill.saveHttpsForms", false);
// 0815: disable live search suggestions in the urlbar and toggle off the Opt-In prompt (FF41+)
// Setting: Options>Privacy>Location Bar>Related searches from the default search engine
user_pref("browser.urlbar.suggest.searches", false);
user_pref("browser.urlbar.userMadeSearchSuggestionsChoice", true);
// 0816: disable browsing and download history
// Under Options>Privacy> if you set Firefox to "use custom settings" there will be a
// setting called "remember my browsing and download history"
// You can clear history and downloads on exiting Firefox (see 2803)
// user_pref("places.history.enabled", false);
// 0817: disable Jumplist (Windows7+)
user_pref("browser.taskbar.lists.enabled", false);
user_pref("browser.taskbar.lists.frequent.enabled", false);
user_pref("browser.taskbar.lists.recent.enabled", false);
user_pref("browser.taskbar.lists.tasks.enabled", false);
// 0818: disable taskbar preview
user_pref("browser.taskbar.previews.enable", false);
// 0819: disable one-off searches from the addressbar (FF51+)
// http://www.ghacks.net/2016/08/09/firefox-one-off-searches-address-bar/
user_pref("browser.urlbar.oneOffSearches", false);
// 0820: disable search reset (about:searchreset) (FF51+)
// http://www.ghacks.net/2016/08/19/firefox-51-search-restore-feature/
user_pref("browser.search.reset.enabled", false);
user_pref("browser.search.reset.whitelist", "");
/*** 0900: PASSWORDS ***/
// 0901: disable saving passwords
// Options>Security>Logins>Remember logins for sites
// NOTE: this does not clear any passwords already saved
// user_pref("signon.rememberSignons", false);
// 0902: use a master password (recommended if you save passwords)
// There are no preferences for this. It is all handled internally.
// https://support.mozilla.org/en-US/kb/use-master-password-protect-stored-logins
// 0903: set how often Mozilla should ask for the master password
// 0=the first time, 1=every time it´s needed, 2=every n minutes (as per the next pref)
// WARNING: the default is 0, author changed his settings
user_pref("security.ask_for_password", 0);
// 0904: how often in minutes Mozilla should ask for the master password (see pref above)
// in minutes, default is 30
user_pref("security.password_lifetime", 30);
// 0905: disable auto-filling username &password form fields - SECURITY
// can leak in cross-site forms AND be spoofed
// http://kb.mozillazine.org/Signon.autofillForms
// password will still be auto-filled after a user name is manually entered
user_pref("signon.autofillForms", false);
// 0906: ignore websites´ autocomplete="off" (FF30+)
user_pref("signon.storeWhenAutocompleteOff", true);
// 0907: force warnings for logins on non-secure (non HTTPS) pages
// https://bugzilla.mozilla.org/show_bug.cgi?id=1217156
user_pref("security.insecure_password.ui.enabled", true);
// 0908: When attempting to fix an entered URL, do not fix an entered password along with it
// i.e do not turn ~http://user:password@foo into ~http://user:password@(prefix)foo(suffix)
// but instead ~http://user@(prefix)foo(suffix))
user_pref("browser.fixup.hide_user_pass", true);
// 0909: disabling for now (FF51+)
user_pref("signon.formlessCapture.enabled", false);
/*** 1000: CACHE ***/
// 1001: disable disk cache
user_pref("browser.cache.disk.enable", false);
user_pref("browser.cache.disk.capacity", 0);
user_pref("browser.cache.disk.smart_size.enabled", false);
user_pref("browser.cache.disk.smart_size.first_run", false);
// 1002: disable disk caching of SSL pages
// http://kb.mozillazine.org/Browser.cache.disk_cache_ssl
user_pref("browser.cache.disk_cache_ssl", false);
// 1003: disable memory cache as well IF you´re REALLY paranoid
// I haven´t tried it, but I´m sure you´ll take a performance/traffic hit
// user_pref("browser.cache.memory.enable", false);
// 1004: disable offline cache
user_pref("browser.cache.offline.enable", false);
// 1005: disable storing extra session data 0=all 1=http-only 2=none
// extra session data contains contents of forms, scrollbar positions, cookies and POST data
user_pref("browser.sessionstore.privacy_level", 2);
// 1006: disable pages being stored in memory. This is not the same as memory cache.
// Visited pages are stored in memory in such a way that they don´t have to be
// re-parsed. This improves performance when pressing back/forward.
// For the sake of completeness, this option is listed for the truly paranoid.
// 0=none, -1=auto (that´s minus 1), or any other positive integer
// http://kb.mozillazine.org/Browser.sessionhistory.max_total_viewers
// user_pref("browser.sessionhistory.max_total_viewers", 0);
// 1007: disable the Session Restore service completely
// WARNING: This also disables the "Recently Closed Tabs" feature
// It does not affect "Recently Closed Windows" or any history.
user_pref("browser.sessionstore.max_tabs_undo", 0);
user_pref("browser.sessionstore.max_windows_undo", 0);
// 1008: IF you use session restore (see 1007 above), increasing the minimal interval between
// two session save operations can help on older machines and some websites.
// Default is 15000 (15 secs). Try 30000 (30sec), 60000 (1min) etc - your choice.
// WARNING: This can also affect entries in the "Recently Closed Tabs" feature:
// i.e the longer the interval the more chance a quick tab open/close won´t be captured
// this longer interval *MAY* affect history but I cannot replicate any history not recorded
// user_pref("browser.sessionstore.interval", 30000);
// 1009: DNS cache and expiration time (default 400 and 60 - same as TBB)
// user_pref("network.dnsCacheEntries", 400);
// user_pref("network.dnsCacheExpiration", 60);
// 1010: disable randomized FF HTTP cache decay experiments
// https://trac.torproject.org/projects/tor/ticket/13575
user_pref("browser.cache.frecency_experiment", -1);
// 1011: disable permissions manager from writing to disk (requires restart)
// https://bugzilla.mozilla.org/show_bug.cgi?id=967812
// user_pref("permissions.memory_only", true);
// (hidden pref)
// 1012: disable resuming session from crash
user_pref("browser.sessionstore.resume_from_crash", false);
/*** 1200: SSL / OCSP / CERTS / ENCRYPTION / HSTS/HPKP/HTTPS
Note that your cipher and other settings can be used server side as a fingerprint attack vector:
see https://www.securityartwork.es/2017/02/02/tls-client-fingerprinting-with-bro/ . You can either
strengthen your encryption/cipher suite and protocols (security) or keep them at default and let
Mozilla handle them (dragging their feet for fear of breaking legacy sites) ***/
// 1201: block rc4 fallback (default is now false as of at least FF45)
user_pref("security.tls.unrestricted_rc4_fallback", false);
// 1203: enable OCSP stapling
// https://blog.mozilla.org/security/2013/07/29/ocsp-stapling-in-firefox/
user_pref("security.ssl.enable_ocsp_stapling", true);
// 1204: reject communication with servers using old SSL/TLS - vulnerable to a MiTM attack
// https://wiki.mozilla.org/Security:Renegotiation
// WARNING: tested Jan 2017 - still breaks too many sites
// user_pref("security.ssl.require_safe_negotiation", true);
// 1205: display warning (red padlock) for "broken security"
// https://wiki.mozilla.org/Security:Renegotiation
user_pref("security.ssl.treat_unsafe_negotiation_as_broken", true);
// 1206: require certificate revocation check through OCSP protocol
// This leaks information about the sites you visit to the CA (cert authority)
// It´s a trade-off between security (checking) and privacy (leaking info to the CA)
// WARNING: Since FF44 the default is false. If set to true, this may/will cause some
// site breakage. Some users have previously mentioned issues with youtube, microsoft etc
// user_pref("security.OCSP.require", true);
// 1207: query OCSP responder servers to confirm current validity of certificates (default=1)
// 0=disable, 1=validate only certificates that specify an OCSP service URL
// 2=enable and use values in security.OCSP.URL and security.OCSP.signing
user_pref("security.OCSP.enabled", 1);
// 1208: enforce strict pinning
// https://trac.torproject.org/projects/tor/ticket/16206
// PKP (public key pinning) 0-disabled 1=allow user MiTM (such as your antivirus), 2=strict
// WARNING: If you rely on an AV (antivirus) to protect your web browsing
// by inspecting ALL your web traffic, then leave at current default =1
user_pref("security.cert_pinning.enforcement_level", 2);
// 1209: control TLS versions with min and max
// 1=min version of TLS 1.0, 2-min version of TLS 1.1, 3=min version of TLS 1.2 etc
// WARNING: FF/chrome currently allow TLS 1.0 by default, so this is your call.
// http://kb.mozillazine.org/Security.tls.version.*
// https://www.ssl.com/how-to/turn-off-ssl-3-0-and-tls-1-0-in-your-browser/
// user_pref("security.tls.version.min", 2);
// user_pref("security.tls.version.fallback-limit", 3);
// user_pref("security.tls.version.max", 4);
// allow up to and including TLS 1.3
// 1210: disable 1024-DH Encryption
// https://www.eff.org/deeplinks/2015/10/how-to-protect-yourself-from-nsa-attacks-1024-bit-DH
// WARNING: may break obscure sites, but not major sites, which should support ECDH over DHE
user_pref("security.ssl3.dhe_rsa_aes_128_sha", false);
user_pref("security.ssl3.dhe_rsa_aes_256_sha", false);
// 1211: disable or limit SHA-1
// 0 = all SHA1 certs are allowed
// 1 = all SHA1 certs are blocked (including perfectly valid ones from 2015 and earlier)
// 2 = deprecated option that now maps to 1
// 3 = only allowed for locally-added roots (e.g. anti-virus)
// 4 = only allowed for locally-added roots or for certs in 2015 and earlier
// WARNING: when disabled, some man-in-the-middle devices (eg security scanners and antivirus
// products, are failing to connect to HTTPS sites. SHA-1 will eventually become obsolete.
// https://blog.mozilla.org/security/2016/10/18/phasing-out-sha-1-on-the-public-web/
// https://github.com/pyllyukko/user.js/issues/194#issuecomment-256509998
user_pref("security.pki.sha1_enforcement_level", 1);
// 1212: disable SSL session tracking (36+)
// SSL session IDs speed up HTTPS connections (no need to renegotiate) and last for 48hrs.
// Since the ID is unique, web servers can (and do) use it for tracking. If set to true,
// this disables sending SSL3 Session IDs and TLS Session Tickets to prevent session tracking
// WARNING: This will slow down TLS connections (personally I don´t notice it at all)
// https://tools.ietf.org/html/rfc5077
// https://bugzilla.mozilla.org/show_bug.cgi?id=967977
user_pref("security.ssl.disable_session_identifiers", true);
// (hidden pref)
// 1213: disable 3DES (effective key size < 128)
// https://en.wikipedia.org/wiki/3des#Security
// http://en.citizendium.org/wiki/Meet-in-the-middle_attack
// http://www-archive.mozilla.org/projects/security/pki/nss/ssl/fips-ssl-ciphersuites.html
user_pref("security.ssl3.rsa_des_ede3_sha", false);
// 1214: disable 128 bits
user_pref("security.ssl3.ecdhe_ecdsa_aes_128_sha", false);
user_pref("security.ssl3.ecdhe_rsa_aes_128_sha", false);
// 1215: disable Microsoft Family Safety cert (Windows 8.1)
// 0: disable detecting Family Safety mode and importing the root
// 1: only attempt to detect Family Safety mode (don´t import the root)
// 2: detect Family Safety mode and import the root
user_pref("security.family_safety.mode", 0);
// 1216: disable insecure active content on https pages - mixed content
user_pref("security.mixed_content.block_active_content", true);
// 1217: disable insecure passive content (such as images) on https pages - mixed context
// current default=false, leave it this way as too many sites break visually
// user_pref("security.mixed_content.block_display_content", true);
// 1218: disable HSTS Priming (FF51+)
// RISKS: formerly blocked mixed-content may load, may cause noticeable delays eg requests
// time out, requests may not be handled well by servers, possible fingerprinting
// https://bugzilla.mozilla.org/show_bug.cgi?id=1246540#c145
user_pref("security.mixed_content.send_hsts_priming", false);
user_pref("security.mixed_content.use_hsts", false);
// 1219: disable HSTS preload list
// recommended enabled, unless you fully understand the risks and trade-offs
// user_pref("network.stricttransportsecurity.preloadlist", false);
// 1220: disable intermediate certificate caching (fingerprinting attack vector)
// NOTE: This affects login/cert/key dbs. AFAIK the only effect is all active logins start anew
// per session. This may be better handled under FPI (ticket 1323644, part of Tor Uplift)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1334485
// related bug
// https://bugzilla.mozilla.org/show_bug.cgi?id=1216882
// related bug (see comment 9)
// user_pref("security.nocertdb", true);
// (hidden pref)
/*** 1400: FONTS ***/
// 1401: disable websites downloading their own fonts (0=block, 1=allow)
// This setting is under Options>Content>Font &Colors>Advanced>Allow pages to choose...
// If you disallow fonts, this drastically limits/reduces font enumeration (by JS) which
// is a high entropy fingerprinting vector.
// WARNING: Disabling fonts can uglify the web a fair bit.
user_pref("browser.display.use_document_fonts", 0);
// 1402: allow icon fonts (glyphs) (FF41+)
user_pref("gfx.downloadable_fonts.enabled", false);
// 1403: disable rendering of SVG OpenType fonts
// https://wiki.mozilla.org/SVGOpenTypeFonts - iSECPartnersReport recommends to disable this
user_pref("gfx.font_rendering.opentype_svg.enabled", false);
// 1404: use more legible default fonts
// WARNING: These are the author´s settings, comment out if you do not require them
// Been using this for over a year, it really grows on you
//
user_pref("font.name.sans-serif.x-unicode", "Arial");
//
user_pref("font.name.sans-serif.x-western", "Arial");
// default Arial
//
user_pref("font.name.monospace.x-unicode", "Lucida Console");
//
user_pref("font.name.monospace.x-western", "Lucida Console");
// default Courier New
// 1405: disable woff2
user_pref("gfx.downloadable_fonts.woff2.enabled", false);
// 1406: disable CSS Font Loading API
// WARNING: Disabling fonts can uglify the web a fair bit.
user_pref("layout.css.font-loading-api.enabled", false);
// 1407: remove special underline handling for a few fonts which you will probably never use.
// Any of these fonts on your system can be enumerated for fingerprinting. Requires restart.
// http://kb.mozillazine.org/Font.blacklist.underline_offset
user_pref("font.blacklist.underline_offset", "");
// 1408: disable graphite which FF49 turned back on by default
// In the past it had security issues - need citation
user_pref("gfx.font_rendering.graphite.enabled", false);
/*** 1600: HEADERS / REFERERS
Except for 1601 and 1602, these can all be best handled by an extension to block/spoof
all and then whitelist if needed, otherwise too much of the internet breaks.
http://www.ghacks.net/2015/01/22/improve-online-privacy-by-controlling-referrer-information/
#Required reading: https://feeding.cloud.geek.nz/posts/tweaking-referrer-for-privacy-in-firefox/ ***/
// 1601: disable referer from an SSL Website
// to be deprecated in FF52+? - https://bugzilla.mozilla.org/show_bug.cgi?id=1308725
user_pref("network.http.sendSecureXSiteReferrer", false);
// 1602: DNT HTTP header - essentially USELESS - default is off. I recommend off.
// NOTE: "Options>Privacy>Tracking>Request that sites not track you"
// if you use NoScript MAKE SURE to set your noscript.doNotTrack.enabled to match
// http://kb.mozillazine.org/Privacy.donottrackheader.value (pref required since FF21+)
// user_pref("privacy.donottrackheader.enabled", true);
// user_pref("privacy.donottrackheader.value", 1);
// (hidden pref)
// 1603: referer, WHEN to send
// 0=never, 1=send only when links are clicked, 2=for links and images (default)
// user_pref("network.http.sendRefererHeader", 2);
// 1604: referer, SPOOF or NOT (default=false)
// user_pref("network.http.referer.spoofSource", false);
// 1605: referer, HOW to handle cross origins
// 0=always (default), 1=only if base domains match, 2=only if hosts match
// user_pref("network.http.referer.XOriginPolicy", 0);
// 1606: referer, WHAT to send (limit the information)
// 0=send full URI (default), 1=scheme+host+port+path, 2=scheme+host+port
// user_pref("network.http.referer.trimmingPolicy", 0);
/*** 1800: PLUGINS ***/
// 1801: set default plugin state (i.e new plugins on discovery) to never activate
// 0=disabled, 1=ask to activate, 2=active - you can override individual plugins
user_pref("plugin.default.state", 0);
user_pref("plugin.defaultXpi.state", 0);
// 1802: enable click to play and set to 0 minutes
user_pref("plugins.click_to_play", false);
user_pref("plugin.sessionPermissionNow.intervalInMinutes", 0);
// 1802a: make sure a plugin is in a certain state: 0=deactivated 1=ask 2=enabled (Flash example)
// you can set all these plugin.state´s via Add-ons>Plugins or search for plugin.state in about:config
// NOTE: you can still over-ride individual sites eg youtube via site permissions
// http://www.ghacks.net/2013/07/09/how-to-make-sure-that-a-firefox-plugin-never-activates-again/
user_pref("plugin.state.flash", 0);
// 1804: disable plugins using external/untrusted scripts with XPCOM or XPConnect
user_pref("security.xpconnect.plugin.unrestricted", false);
// 1805: disable scanning for plugins
// http://kb.mozillazine.org/Plugin_scanning
// plid.all = whether to scan the directories specified in the Windows registry for PLIDs
// includes: RealPlayer, Next-Generation Java Plug-In, Adobe Flash, Antivirus etc
// WARNING: The author turned off plugins, try it one day. You are not missing much.
//
user_pref("plugin.scan.plid.all", false);
// 1806: Acrobat, Quicktime, WMP are handled separately from 1805 above.
// The string refers to min version number allowed
//
user_pref("plugin.scan.Acrobat", "99999");
//
user_pref("plugin.scan.Quicktime", "99999");
//
user_pref("plugin.scan.WindowsMediaPlayer", "99999");
// 1807: disable auto-play of HTML5 media
// WARNING: This may break youtube video playback (and probably other sites). If you block
// autoplay but occasionally would like a toggle button, try the following add-on
// https://addons.mozilla.org/en-US/firefox/addon/autoplay-toggle
user_pref("media.autoplay.enabled", false);
// 1808: disable audio auto-play in non-active tabs (FF51+)
// http://www.ghacks.net/2016/11/14/firefox-51-blocks-automatic-audio-playback-in-non-active-tabs/
user_pref("media.block-autoplay-until-in-foreground", true);
// 1820: disable all GMP (Gecko Media Plugins)
// https://wiki.mozilla.org/GeckoMediaPlugins
user_pref("media.gmp-provider.enabled", false);
user_pref("media.gmp.trial-create.enabled", false);
// 1825: disable widevine CDM
user_pref("media.gmp-widevinecdm.visible", false);
user_pref("media.gmp-widevinecdm.enabled", false);
user_pref("media.gmp-widevinecdm.autoupdate", false);
// 1830: disable all DRM content (EME: Encryption Media Extension)
user_pref("media.eme.enabled", false);
// Options>Content>Play DRM Content
user_pref("browser.eme.ui.enabled", false);
// hides "Play DRM Content" checkbox, restart required
user_pref("media.eme.apiVisible", false);
// block websites detecting DRM is disabled
// 1840: disable the OpenH264 Video Codec by Cisco to "Never Activate"
// This is the bundled codec used for video chat in WebRTC
// Disable pings to the external update/download server
user_pref("media.gmp-gmpopenh264.enabled", false);
// (hidden pref)
user_pref("media.gmp-gmpopenh264.autoupdate", false);
user_pref("media.gmp-manager.url", "data:text/plain,");
// 1850: disable the Adobe EME "Primetime CDM" (Content Decryption Module)
// https://trac.torproject.org/projects/tor/ticket/16285
user_pref("media.gmp-eme-adobe.enabled", false);
user_pref("media.gmp-eme-adobe.visible", false);
user_pref("media.gmp-eme-adobe.autoupdate", false);
/*** 2000: MEDIA / CAMERA / MIKE ***/
// 2001: disable WebRTC
// https://www.privacytools.io/#webrtc
user_pref("media.peerconnection.enabled", false);
user_pref("media.peerconnection.use_document_iceservers", false);
user_pref("media.peerconnection.video.enabled", false);
user_pref("media.peerconnection.identity.enabled", false);
user_pref("media.peerconnection.identity.timeout", 1);
user_pref("media.peerconnection.turn.disable", true);
// disable video capability for WebRTC
user_pref("media.navigator.video.enabled", false);
// 2001a: pref which improves the WebRTC IP Leak issue, as opposed to completely
// disabling WebRTC. You still need to enable WebRTC for this to be applicable (FF42+)
// https://wiki.mozilla.org/Media/WebRTC/Privacy
user_pref("media.peerconnection.ice.default_address_only", true);
// (FF41-FF50)
user_pref("media.peerconnection.ice.no_host", true);
// (FF51+)
// 2010: disable WebGL, force bare minimum feature set if used &disable WebGL extensions
// http://www.contextis.com/resources/blog/webgl-new-dimension-browser-exploitation/
// https://security.stackexchange.com/questions/13799/is-webgl-a-security-concern
user_pref("webgl.disabled", true);
user_pref("pdfjs.enableWebGL", false);
user_pref("webgl.min_capability_mode", true);
user_pref("webgl.disable-extensions", true);
user_pref("webgl.disable-fail-if-major-performance-caveat", true);
// 2011: don´t make WebGL debug info available to websites
// https://bugzilla.mozilla.org/show_bug.cgi?id=1171228
// https://developer.mozilla.org/en-US/docs/Web/API/WEBGL_debug_renderer_info
user_pref("webgl.enable-debug-renderer-info", false);
// 2012: two more webgl preferences (FF51+)
user_pref("webgl.dxgl.enabled", false);
user_pref("webgl.enable-webgl2", false);
// 2021: disable speech recognition
user_pref("media.webspeech.recognition.enable", false);
user_pref("media.webspeech.synth.enabled", false);
// 2022: disable screensharing
user_pref("media.getusermedia.screensharing.enabled", false);
user_pref("media.getusermedia.screensharing.allowed_domains", "");
user_pref("media.getusermedia.screensharing.allow_on_old_platforms", false);
user_pref("media.getusermedia.browser.enabled", false);
user_pref("media.getusermedia.audiocapture.enabled", false);
// 2023: disable camera stuff
user_pref("camera.control.face_detection.enabled", false);
// 2024: enable/disable MSE (Media Source Extensions)
// http://www.ghacks.net/2014/05/10/enable-media-source-extensions-firefox/
user_pref("media.mediasource.enabled", false);
user_pref("media.mediasource.mp4.enabled", false);
user_pref("media.mediasource.webm.audio.enabled", false);
user_pref("media.mediasource.webm.enabled", false);
// 2025: enable/disable various media types - end user personal choice
// WARNING: this is the author´s settings, choose your own
user_pref("media.mp4.enabled", false);
user_pref("media.flac.enabled", false);
// (FF51+)
user_pref("media.ogg.enabled", ffalse);
user_pref("media.ogg.flac.enabled", false);
// (FF51+)
user_pref("media.opus.enabled", false);
user_pref("media.raw.enabled", false);
user_pref("media.wave.enabled", false);
user_pref("media.webm.enabled", false);
user_pref("media.wmf.enabled", false);
// https://www.youtube.com/html5 - for the two H.264 entries
// 2026: disable canvas capture stream
// https://developer.mozilla.org/en-US/docs/Web/API/HTMLCanvasElement/captureStream
user_pref("canvas.capturestream.enabled", false);
// 2027: disable camera image capture
// https://trac.torproject.org/projects/tor/ticket/16339
user_pref("dom.imagecapture.enabled", false);
// 2028: disable offscreen canvas
// https://developer.mozilla.org/en-US/docs/Web/API/OffscreenCanvas
user_pref("gfx.offscreencanvas.enabled", false);
/*** 2200: UI MEDDLING
see http://kb.mozillazine.org/Prevent_websites_from_disabling_new_window_features ***/
// 2201: disable website control over right click context menu
// WARNING: This will break some sites eg Dropbox, Google Docs? gmail?
user_pref("dom.event.contextmenu.enabled", false);
// 2202: UI SPOOFING: disable scripts hiding or disabling the following on new windows
user_pref("dom.disable_window_open_feature.location", true);
user_pref("dom.disable_window_open_feature.menubar", true);
user_pref("dom.disable_window_open_feature.resizable", true);
user_pref("dom.disable_window_open_feature.status", true);
user_pref("dom.disable_window_open_feature.toolbar", true);
// 2203: POPUP windows - prevent or allow javascript UI meddling
user_pref("dom.disable_window_flip", true);
// window z-order
user_pref("dom.disable_window_move_resize", true);
user_pref("dom.disable_window_open_feature.close", true);
user_pref("dom.disable_window_open_feature.minimizable", true);
user_pref("dom.disable_window_open_feature.personalbar", true);
// bookmarks toolbar
user_pref("dom.disable_window_open_feature.titlebar", true);
user_pref("dom.disable_window_status_change", true);
user_pref("dom.allow_scripts_to_close_windows", false);
// 2204: disable links opening in a new window
// https://trac.torproject.org/projects/tor/ticket/9881
// test url: https://people.torproject.org/~gk/misc/entire_desktop.html
// You can still right click a link and select open in a new window
// This is to stop malicious window sizes and screen res leaks etc in conjunction
// with 2203 dom.disable_window_move_resize=true | 2418 full-screen-api.enabled=false
// user_pref("browser.link.open_newwindow.restriction", 0);
/*** 2300: SERVICE WORKERS ***/
// 2301: disable workers API and service workers API
// https://developer.mozilla.org/en-US/docs/Web/API/Worker
// https://developer.mozilla.org/en-US/docs/Web/API/ServiceWorker_API
// http://www.ghacks.net/2016/03/02/manage-service-workers-in-firefox-and-chrome/
// WARNING: WILL break sites as this gains traction: eg mega.nz requires workers
user_pref("dom.workers.enabled", false);
user_pref("dom.serviceWorkers.enabled", false);
// 2302: disable service workers cache and cache storage
user_pref("dom.caches.enabled", false);
// 2303: disable push notifications (FF44+) [requires serviceWorkers to be enabled]
// web apps can receive messages pushed to them from a server, whether or
// not the web app is in the foreground, or even currently loaded
// https://developer.mozilla.org/en/docs/Web/API/Push_API
// WARNING: may affect social media sites like Twitter
user_pref("dom.push.enabled", false);
user_pref("dom.push.connection.enabled", false);
user_pref("dom.push.serverURL", "");
user_pref("dom.push.userAgentID", "");
// 2304: disable web/push notifications
// https://developer.mozilla.org/en-US/docs/Web/API/notification
// NOTE: you can still override individual domains under site permissions (FF44+)
// WARNING: may affect social media sites like Twitter
user_pref("dom.webnotifications.enabled", false);
user_pref("dom.webnotifications.serviceworker.enabled", false);
/*** 2400: DOM &JAVASCRIPT ***/
// 2402: disable website access to clipboard events/content
// http://www.ghacks.net/2014/01/08/block-websites-reading-modifying-clipboard-contents-firefox/
// WARNING: This will break some sites functionality such as pasting into Facebook
// this applies to onCut, onCopy, onPaste events - i.e is you have to interact with
// the website for it to look at the clipboard
user_pref("dom.event.clipboardevents.enabled", false);
// 2403: disable clipboard commands (cut/copy) from "non-priviledged" content
// this disables document.execCommand("cut"/"copy") to protect your clipboard
// https://bugzilla.mozilla.org/show_bug.cgi?id=1170911
user_pref("dom.allow_cut_copy", false);
// (hidden pref)
// 2404: disable JS storing data permanently
// If you block indexedDB but would like a toggle button, try the following add-on
// https://addons.mozilla.org/en-US/firefox/addon/disable-indexeddb/
// This setting WAS under about:permissions>All Sites>Maintain Offline Storage
// NOTE: about:permissions is no longer available since FF46 but you can still override
// individual domains: use info icon in urlbar etc or right click on a web page>view page info
// WARNING: If set as false (disabled), this WILL break some [old] add-ons and DOES break
// a lot of sites´ functionality. Applies to websites, add-ons and session data.
user_pref("dom.indexedDB.enabled", false);
// 2405: https://wiki.mozilla.org/WebAPI/Security/WebTelephony
user_pref("dom.telephony.enabled", false);
// 2410: disable User Timing API
// https://trac.torproject.org/projects/tor/ticket/16336
user_pref("dom.enable_user_timing", false);
// 2411: disable resource/navigation timing
user_pref("dom.enable_resource_timing", false);
// 2412: disable timing attacks - javascript performance fingerprinting
// https://wiki.mozilla.org/Security/Reviews/Firefox/NavigationTimingAPI
user_pref("dom.enable_performance", false);
// 2414: disable shaking the screen
user_pref("dom.vibrator.enabled", false);
// 2415: max popups from a single non-click event - default is 20!
user_pref("dom.popup_maximum", 3);
// 2415b: limit events that can cause a popup
// default is "change click dblclick mouseup notificationclick reset submit touchend"
// WARNING: Author killed all methods but does this with Popup Blocker Ultimate
// in Strict mode with whitelist. Or you can allow all but blacklist. Either way,
// Popup Blocker Ultimate overwrites this pref with a blank (or allows everything!).
// http://kb.mozillazine.org/Dom.popup_allowed_events
user_pref("dom.popup_allowed_events", "click dblclick");
// 2416: disable idle observation
user_pref("dom.idle-observers-api.enabled", false);
// 2418: disable full-screen API
// This setting WAS under about:permissions>All Sites>Fullscreen
// NOTE: about:permissions is no longer available since FF46 but you can still override
// individual domains: use info icon in urlbar etc or right click on a web page>view page info
// set to false=block, set to true=ask
user_pref("full-screen-api.enabled", false);
// 2420: disable support for asm.js ( http://asmjs.org/ )
// https://www.mozilla.org/en-US/security/advisories/mfsa2015-29/
// https://www.mozilla.org/en-US/security/advisories/mfsa2015-50/
// https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-2712
user_pref("javascript.options.asmjs", false);
// 2421: in addition to 2420, these settings will help harden JS against exploits such as CVE-2015-0817
// https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-0817
// WARNING: causes the odd site issue and there is also a performance loss
// Update: Jan-2017: commented out for now, as performance gains outweigh extra security
user_pref("javascript.options.ion", false);
user_pref("javascript.options.baselinejit", false);
// 2425: disable ArchiveAPI i.e reading content of archives, such as zip files, directly
// in the browser, through DOM file objects. Default is false.
user_pref("dom.archivereader.enabled", false);
// 2450: force FF to tell you if a website asks to store data for offline use
// https://support.mozilla.org/en-US/questions/1098540
// https://bugzilla.mozilla.org/show_bug.cgi?id=959985
user_pref("offline-apps.allow_by_default", false);
// Options>Advanced>Network>Tell me when a website asks to store data for offline use
user_pref("browser.offline-apps.notify", true);
// change size of warning quota for offline cache (default 51200)
// Offline cache is only used in rare cases to store data locally. FF will store small amounts
// (default 50MB) of data in the offline (application) cache without asking for permission.
// user_pref("offline-apps.quota.warn", 51200);
/*** 2500: HARDWARE FINGERPRINTING ***/
// 2501: disable gamepad API - USB device ID enumeration
// https://trac.torproject.org/projects/tor/ticket/13023
user_pref("dom.gamepad.enabled", false);
// 2502: disable Battery Status API. Initially a Linux issue (high precision readout) that is now fixed.
// However, it is still another metric for fingerprinting, used to raise entropy.
// eg: do you have a battery or not, current charging status, charge level, times remaining etc
// http://techcrunch.com/2015/08/04/battery-attributes-can-be-used-to-track-web-users/
// https://bugzilla.mozilla.org/show_bug.cgi?id=1124127
// https://www.w3.org/TR/battery-status/
// https://www.theguardian.com/technology/2016/aug/02/battery-status-indicators-tracking-online
// NOTE: From FF52+ Battery Status API is only available in chrome/privileged code.
// https://bugzilla.mozilla.org/show_bug.cgi?id=1313580
user_pref("dom.battery.enabled", false);
// 2503: disable giving away network info
// eg bluetooth, cellular, ethernet, wifi, wimax, other, mixed, unknown, none
// https://developer.mozilla.org/en-US/docs/Web/API/Network_Information_API
// https://wicg.github.io/netinfo/
// https://bugzilla.mozilla.org/show_bug.cgi?id=960426
user_pref("dom.netinfo.enabled", false);
// 2504: disable virtual reality devices
// https://developer.mozilla.org/en-US/docs/Web/API/WebVR_API
user_pref("dom.vr.enabled", false);
user_pref("dom.vr.oculus.enabled", false);
user_pref("dom.vr.osvr.enabled", false);
// (FF49+)
user_pref("dom.vr.openvr.enabled", false);
// (FF51+)
// 2505: disable media device enumeration (FF29+)
// NOTE: media.peerconnection.enabled should also be set to false (see 2001)
// https://wiki.mozilla.org/Media/getUserMedia
// https://developer.mozilla.org/en-US/docs/Web/API/MediaDevices/enumerateDevices
user_pref("media.navigator.enabled", false);
// 2506: disable video statistics - JS performance fingerprinting
// https://trac.torproject.org/projects/tor/ticket/15757
user_pref("media.video_stats.enabled", false);
// 2507: disable keyboard fingerprinting (FF38+) (physical keyboards)
// The Keyboard API allows tracking the "read parameter" of pressed keys in forms on
// web pages. These parameters vary between types of keyboard layouts such as QWERTY,
// AZERTY, Dvorak, and between various languages, eg German vs English.
// WARNING: Don´t use if Android + physical keyboard
// UPDATE: This MAY be incorporated better into the Tor Uplift project (see 2699)
// https://developer.mozilla.org/en-US/docs/Web/API/KeyboardEvent/code
// https://www.privacy-handbuch.de/handbuch_21v.htm
user_pref("dom.keyboardevent.code.enabled", false);
user_pref("dom.beforeAfterKeyboardEvent.enabled", false);
user_pref("dom.keyboardevent.dispatch_during_composition", false);
// 2508: disable graphics fingerprinting (the loss of hardware acceleration is negligible)
// These prefs are under Options>Advanced>General>Use hardware acceleration when available
// NOTE: changing this option changes BOTH these preferences
// https://wiki.mozilla.org/Platform/GFX/HardwareAcceleration
// WARNING: This changes text rendering (fonts will look different)
// If you watch a lot of video, this will impact performance
user_pref("gfx.direct2d.disabled", true);
user_pref("layers.acceleration.disabled", true);
// 2509: disable touch events
// https://developer.mozilla.org/en-US/docs/Web/API/Touch_events
// https://trac.torproject.org/projects/tor/ticket/10286
// fingerprinting attack vector - leaks screen res &actual screen coordinates
// WARNING: If you use touch eg Win8/10 Metro/Smartphone reset this to default
user_pref("dom.w3c_touch_events.enabled", 0);
// 2510: disable Web Audio API (FF51+)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1288359
user_pref("dom.webaudio.enabled", false);
// 2511: disable MediaDevices change detection (FF51+) (enabled by default starting FF52+)
// https://developer.mozilla.org/en-US/docs/Web/Events/devicechange
// https://developer.mozilla.org/en-US/docs/Web/API/MediaDevices/ondevicechange
user_pref("media.ondevicechange.enabled", false);
/*** 2600: MISC - LEAKS / FINGERPRINTING / PRIVACY / SECURITY ***/
// 2601: disable sending additional analytics to web servers
// https://developer.mozilla.org/en-US/docs/Web/API/navigator.sendBeacon
user_pref("beacon.enabled", false);
// 2602: CIS 2.3.2 disable downloading on desktop
user_pref("browser.download.folderList", 2);
// 2603: always ask the user where to download - enforce user interaction for security
user_pref("browser.download.useDownloadDir", false);
// 2604: https://bugzil.la/238789#c19
user_pref("browser.helperApps.deleteTempFileOnExit", true);
// 2605: don´t integrate activity into windows recent documents
user_pref("browser.download.manager.addToRecentDocs", false);
// 2606: disable hiding mime types (Options>Applications) not associated with a plugin
user_pref("browser.download.hide_plugins_without_extensions", false);
// 2607: disable page thumbnail collection
// look in profile/thumbnails directory - you may want to clean that out
user_pref("browser.pagethumbnails.capturing_disabled", true);
// (hidden pref)
// 2608: disable JAR from opening Unsafe File Types
user_pref("network.jar.open-unsafe-types", false);
// 2611: disable WebIDE to prevent remote debugging and add-on downloads
// https://trac.torproject.org/projects/tor/ticket/16222
user_pref("devtools.webide.autoinstallADBHelper", false);
user_pref("devtools.webide.autoinstallFxdtAdapters", false);
user_pref("devtools.debugger.remote-enabled", false);
user_pref("devtools.webide.enabled", false);
// 2612: disable SimpleServiceDiscovery - which can bypass proxy settings - eg Roku
// https://trac.torproject.org/projects/tor/ticket/16222
user_pref("browser.casting.enabled", false);
user_pref("gfx.layerscope.enabled", false);
// 2613: disable device sensor API - fingerprinting vector
// https://trac.torproject.org/projects/tor/ticket/15758
user_pref("device.sensors.enabled", false);
// 2614: disable SPDY as it can contain identifiers
// https://www.torproject.org/projects/torbrowser/design/#identifier-linkability (no. 10)
user_pref("network.http.spdy.enabled", false);
user_pref("network.http.spdy.enabled.deps", false);
// 2615: disable http2 for now as well
user_pref("network.http.spdy.enabled.http2", false);
// 2617: disable pdf.js as an option to preview PDFs within Firefox
// see mime-types under Options>Applications) - EXPLOIT risk
// Enabling this (set to true) will change your option most likely to "Ask" or "Open with
// some external pdf reader". This does NOT necessarily prevent pdf.js being used via
// other means, it only removes the option. I think this should be left at default (false).
// 1. It won´t stop JS bypassing it. 2. Depending on external pdf viewers there is just as
// much risk or more (acrobat). 3. Mozilla are very quick to patch these sorts of exploits,
// they treat them as severe/critical and 4. for convenience
user_pref("pdfjs.disabled", true);
// 2618: when using SOCKS have the proxy server do the DNS lookup - dns leak issue
// http://kb.mozillazine.org/Network.proxy.socks_remote_dns
// https://trac.torproject.org/projects/tor/wiki/doc/TorifyHOWTO/WebBrowsers
// eg in TOR, this stops your local DNS server from knowing your Tor destination
// as a remote Tor node will handle the DNS request
user_pref("network.proxy.socks_remote_dns", false);
// 2619: limit HTTP redirects (this does not control redirects with HTML meta tags or JS)
// WARNING: a low setting of 5 or under will probably break some sites (eg gmail logins)
// Error-Message could be: Firefox has detected that the server is redirecting the request for this address in a way that will never complete.
// To control HTML Meta tag and JS redirects, use an add-on (eg NoRedirect). Default is 20
//
// [SOLVED by Gooken, 03.04.2020]
// Belonging error-message could be for less than 6: "Firefox has detected that the server is redirecting the request for this address in a way that will never complete."
//
user_pref("network.http.redirection-limit", 20);
// 2620: disable middle mouse click opening links from clipboard
// https://trac.torproject.org/projects/tor/ticket/10089
// http://kb.mozillazine.org/Middlemouse.contentLoadURL
user_pref("middlemouse.contentLoadURL", false);
// 2621: disable IPv6 (included for knowledge ONLY - not recommended)
// This is all about covert channels such as MAC addresses being included/abused in the
// IPv6 protocol for tracking. If you want to mask your IP address, this is not the way
// to do it. It´s 2016, IPv6 is here. Here are some old links
// 2010: https://www.christopher-parsons.com/ipv6-and-the-future-of-privacy/
// 2011: https://iapp.org/news/a/2011-09-09-facing-the-privacy-implications-of-ipv6
// 2012: http://www.zdnet.com/article/security-versus-privacy-with-ipv6-deployment/
// NOTE: It is a myth that disabling IPv6 will speed up your internet connection
// http://www.howtogeek.com/195062/no-disabling-ipv6-probably-wont-speed-up-your-internet-connection
// user_pref("network.dns.disableIPv6", true);
// user_pref("network.http.fast-fallback-to-IPv4", true);
// 2622: ensure you have a security delay when installing add-ons (milliseconds)
// default=1000, This also covers the delay in "Save" on downloading files.
// http://kb.mozillazine.org/Disable_extension_install_delay_-_Firefox
// http://www.squarefree.com/2004/07/01/race-conditions-in-security-dialogs/
user_pref("security.dialog_enable_delay", 1000);
// 2623: ensure Strict File Origin Policy on local files
// The default is true. Included for completeness
// http://kb.mozillazine.org/Security.fileuri.strict_origin_policy
user_pref("security.fileuri.strict_origin_policy", true);
// 2624: enforce Subresource Integrity (SRI) (FF43+)
// The default is true. Included for completeness
// https://developer.mozilla.org/en-US/docs/Web/Security/Subresource_Integrity
// https://wiki.mozilla.org/Security/Subresource_Integrity
user_pref("security.sri.enable", true);
// 2625: Applications [non Tor protocol] SHOULD generate an error
// upon the use of .onion and SHOULD NOT perform a DNS lookup.
// https://bugzilla.mozilla.org/show_bug.cgi?id=1228457
user_pref("network.dns.blockDotOnion", true);
// 2626: strip optional user agent token, default is false, included for completeness
// https://developer.mozilla.org/en-US/docs/Web/HTTP/Gecko_user_agent_string_reference
user_pref("general.useragent.compatMode.firefox", false);
// 2627: Spoof default UA &relevant (navigator) parts (also see 0204 for UA language)
// NOTE: may be better handled by an extension (eg whitelisitng), try not to clash with it
// NOTE: this is NOT a complete solution (feature detection, some navigator objects leak, resource URI etc)
// AIM: match latest TBB settings: Windows, ESR, OS etc
// WARNING: If you do not understand fingerprinting then don´t use this section
// test: http://browserspy.dk/browser.php
// http://browserspy.dk/showprop.php (for buildID)
// http://browserspy.dk/useragent.php
// ==start==
// A: navigator.userAgent leaks in JS, setting this also seems to break UA extension whitelisting
// user_pref("general.useragent.override", "Mozilla/5.0 (Windows NT 6.1; rv:45.0) Gecko/20100101 Firefox/45.0");
// (hidden pref)
// B: navigator.buildID (see gecko.buildID in about:config) reveals build time
// down to the second which defeats user agent spoofing and can compromise OS etc
// https://bugzilla.mozilla.org/show_bug.cgi?id=583181
user_pref("general.buildID.override", "20100101");
// (hidden pref)
// C: navigator.appName
user_pref("general.appname.override", "Netscape");
// (hidden pref)
// D: navigator.appVersion
user_pref("general.appversion.override", "5.0 (Windows)");
// (hidden pref)
// E: navigator.platform leaks in JS
user_pref("general.platform.override", "Win64");
// (hidden pref)
// F: navigator.oscpu
user_pref("general.oscpu.override", "Windows NT 6.1");
// (hidden pref)
// 2628: disable UITour backend so there is no chance that a remote page can use it
user_pref("browser.uitour.enabled", false);
user_pref("browser.uitour.url", "");
// 2629: disable remote JAR files being opened, regardless of content type
// https://bugzilla.mozilla.org/show_bug.cgi?id=1215235
user_pref("network.jar.block-remote-files", true);
// 2650: start the browser in e10s mode (48+)
// After restarting the browser, you can check whether it´s enabled by visiting
// about:support and checking that "Multiprocess Windows" = 1
// use force-enable and extensions.e10sblocksenabling if you have add-ons
// user_pref("browser.tabs.remote.autostart", true);
// user_pref("browser.tabs.remote.autostart.2", true);
// (FF49+)
// user_pref("browser.tabs.remote.force-enable", true);
// (hidden pref)
// user_pref("extensions.e10sBlocksEnabling", false);
// 2651: control e10s number of container processes
// http://www.ghacks.net/2016/02/15/change-how-many-processes-multi-process-firefox-uses/
// https://bugzilla.mozilla.org/show_bug.cgi?id=1207306
// user_pref("dom.ipc.processCount", 4);
// 2652: enable console shim warnings for extensions that don´t have the flag
// ´multiprocessCompatible´ set to true
user_pref("dom.ipc.shims.enabledWarnings", true);
// 2660: enforce separate content process for file:
// URLs (FF53+?)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1147911
// http://www.ghacks.net/2016/11/27/firefox-53-exclusive-content-process-for-local-files/
user_pref("browser.tabs.remote.separateFileUriProcess", true);
// 2662: disable "open with" in download dialog (FF50+)
// This is very useful to enable when the browser is sandboxed (e.g. via AppArmor)
// in such a way that it is forbidden to run external applications.
// WARNING: This may interfere with some users´ workflow or methods
// https://bugzilla.mozilla.org/show_bug.cgi?id=1281959
user_pref("browser.download.forbid_open_with", true);
// 2663: disable MathML (FF51+)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1173199
// test: http://browserspy.dk/mathml.php
user_pref("mathml.disabled", true);
// 2664: disable DeviceStorage API
// https://wiki.mozilla.org/WebAPI/DeviceStorageAPI
user_pref("device.storage.enabled", false);
// 2665: sanitize webchannel whitelist
user_pref("webchannel.allowObject.urlWhitelist", "");
// 2666: disable HTTP Alternative Services
// http://www.ghacks.net/2015/08/18/a-comprehensive-list-of-firefox-privacy-and-security-settings/#comment-3970881
user_pref("network.http.altsvc.enabled", false);
user_pref("network.http.altsvc.oe", false);
// 2667: disable various developer tools in browser context
// Devtools>Advanced Settings>Enable browser chrome and add-on debugging toolboxes
// http://github.com/pyllyukko/user.js/issues/179#issuecomment-246468676
user_pref("devtools.chrome.enabled", false);
// 2668: lock down allowed extension directories
// https://mike.kaply.com/2012/02/21/understanding-add-on-scopes/
// archived: http://archive.is/DYjAM
user_pref("extensions.enabledScopes", 1);
// (hidden pref)
user_pref("extensions.autoDisableScopes", 15);
// 2669: strip paths when sending URLs to PAC scripts (FF51+)
// CVE-2017-5384: Information disclosure via Proxy Auto-Config (PAC)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1255474
user_pref("network.proxy.autoconfig_url.include_path", false);
// 2670: close bypassing of CSP via image mime types (FF51+)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1288361
user_pref("security.block_script_with_wrong_mime", true);
// 2671: disable SVG (FF53+)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1216893
user_pref("svg.disabled", true);
/*** 2698: FIRST PARTY ISOLATION (PFI) ***/
// 2698a: enable first party isolation pref and OriginAttribute (FF51+)
// WARNING: breaks lots of cross-domain logins and site funtionality until perfected
// https://bugzilla.mozilla.org/show_bug.cgi?id=1260931
// 2698b: this also isolates OCSP requests by first party domain
// https://bugzilla.mozilla.org/show_bug.cgi?id=1264562
// user_pref("privacy.firstparty.isolate", true);
/*** 2699: TOR UPLIFT: privacy.resistFingerprinting
This preference will be used as a generic switch for a wide range of items.
This section will attempt to list all the ramifications and Mozilla tickets ***/
// 2699a: limit window.screen &CSS media queries providing large amounts of identifiable info.
// POC: http://ip-check.info/?lang=en (screen, usable screen, and browser window will match)
// https://bugzilla.mozilla.org/show_bug.cgi?id=418986
// NOTE: does not cover everything yet - https://bugzilla.mozilla.org/show_bug.cgi?id=1216800
// NOTE: this will probably make your values pretty unique until you resize or snap the
// inner window width + height into standard/common resolutions (mine is at 1366×768)
// To set a size, open a XUL (chrome) page (such as about:config) which is at 100% zoom, hit
// Shift+F4 to open the scratchpad, type window.resizeTo(1366,768), hit Ctrl+R to run. Test
// your window size, do some math, resize to allow for all the non inner window elements
// test: http://browserspy.dk/screen.php
// Common resolutions: http://www.rapidtables.com/web/dev/screen-resolution-statistics.htm
// 2699b: spoof screen orientation
// https://bugzilla.mozilla.org/show_bug.cgi?id=1281949
// 2699c: hide the contents of navigator.plugins and navigator.mimeTypes (FF50+)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1281963
user_pref("privacy.resistFingerprinting", true);
// (hidden pref)
/*** 2700: COOKIES &DOM STORAGE ***/
// 2701: disable cookies on all sites
// you can set exceptions under site permissions or use an extension (eg Cookie Controller)
// 0=allow all 1=allow same host 2=disallow all 3=allow 3rd party if it already set a cookie
//
user_pref("network.cookie.cookieBehavior", 2);
// 2702: ensure that third-party cookies (if enabled, see above pref) are session-only
// https://feeding.cloud.geek.nz/posts/tweaking-cookies-for-privacy-in-firefox/
// http://kb.mozillazine.org/Network.cookie.thirdparty.sessionOnly
//
user_pref("network.cookie.thirdparty.sessionOnly", true);
// 2703: set cookie lifetime policy
// 0=until they expire (default), 2=until you close Firefox, 3=for n days (see next pref)
// If you use custom settings for History in Options, this is the setting under
// Privacy>Accept cookies from sites>Keep until they expire/I close Firefox>
// user_pref("network.cookie.lifetimePolicy", 0);
// 2704: set cookie lifetime in days (see above pref) - default is 90 days
// user_pref("network.cookie.lifetime.days", 90);
// 2705: disable dom storage
// WARNING: this will break a LOT of sites´ functionality.
// You are better off using an extension for more granular control
// user_pref("dom.storage.enabled", false);
// 2706: disable Storage API (FF51+) which gives sites´ code the ability to find out how much space
// they can use, how much they are already using, and even control whether or not they need to
// be alerted before the user agent disposes of site data in order to make room for other things.
// https://developer.mozilla.org/en-US/docs/Web/API/StorageManager
// https://developer.mozilla.org/en-US/docs/Web/API/Storage_API
user_pref("dom.storageManager.enabled", false);
// 2707: clear localStorage and UUID when a WebExtension is uninstalled
// NOTE: both preferences must be the same
// https://developer.mozilla.org/en-US/Add-ons/WebExtensions/API/storage/local
// https://bugzilla.mozilla.org/show_bug.cgi?id=1213990
user_pref("extensions.webextensions.keepStorageOnUninstall", false);
user_pref("extensions.webextensions.keepUuidOnUninstall", false);
/*** 2800: SHUTDOWN ***/
// 2802: enable FF to clear stuff on close
// This setting is under Options>Privacy>Clear history when Firefox closes
user_pref("privacy.sanitize.sanitizeOnShutdown", true);
// 2803: what to clear on shutdown
// These settings are under Options>Privacy>Clear history when Firefox closes>Settings
// These are the settings of the author of this user.js, chose your own
user_pref("privacy.clearOnShutdown.cache", true);
user_pref("privacy.clearOnShutdown.cookies", true);
user_pref("privacy.clearOnShutdown.downloads", true);
user_pref("privacy.clearOnShutdown.formdata", true);
user_pref("privacy.clearOnShutdown.history", true);
user_pref("privacy.clearOnShutdown.offlineApps", true);
user_pref("privacy.clearOnShutdown.sessions", true); // active logins
user_pref("privacy.clearOnShutdown.siteSettings", true);
// 2803a: include all open windows/tabs when you shutdown
// user_pref("privacy.clearOnShutdown.openWindows", true);
// 2804: (to match above) - auto selection of items to delete with Ctrl-Shift-Del
user_pref("privacy.cpd.cache", true);
user_pref("privacy.cpd.cookies", false);
user_pref("privacy.cpd.downloads", true);
user_pref("privacy.cpd.formdata", true);
user_pref("privacy.cpd.history", true);
user_pref("privacy.cpd.offlineApps", true);
user_pref("privacy.cpd.passwords", false);
user_pref("privacy.cpd.sessions", false);
user_pref("privacy.cpd.siteSettings", false);
// 2804a: include all open windows/tabs when you run clear recent history
// user_pref("privacy.cpd.openWindows", true);
// 2805: reset default ´Time range to clear´ for ´clear recent history´ (see 2804 above)
// Firefox remembers your last choice. This will reset the value when you start FF.
// 0=everything 1=last hour, 2=last 2 hours, 3=last 4 hours, 4=today
user_pref("privacy.sanitize.timeSpan", 0);
/*** 3000: PERSONAL SETTINGS
Settings that are handy to migrate and/or are not in the Options interface. Users
can put their own non-security/privacy/fingerprinting/tracking stuff here ***/
// 3001: disable annoying warnings
user_pref("general.warnOnAboutConfig", false);
user_pref("browser.tabs.warnOnClose", false);
user_pref("browser.tabs.warnOnCloseOtherTabs", false);
user_pref("browser.tabs.warnOnOpen", false);
// 3001a: disable warning when a domain requests full screen
// https://developer.mozilla.org/en-US/docs/Web/Guide/API/DOM/Using_full_screen_mode
// user_pref("full-screen-api.warning.delay", 0);
// user_pref("full-screen-api.warning.timeout", 0);
// 3002: disable closing browser with last tab
user_pref("browser.tabs.closeWindowWithLastTab", false);
// 3004: disable backspace (0 = previous page, 1 = scroll up, 2 = do nothing)
user_pref("browser.backspace_action", 2);
// 3005: disable autocopy default (use extensions autocopy 2 © plain text 2)
user_pref("clipboard.autocopy", false);
// 3007: open new windows in a new tab instead
// This setting is under Options>General>Tabs
// 1=current window, 2=new window, 3=most recent window
user_pref("browser.link.open_newwindow", 3);
// 3008: disable "Do you really want to leave this site?" popups
// https://support.mozilla.org/en-US/questions/1043508
user_pref("dom.disable_beforeunload", true);
// 3009: turn on APZ (Async Pan/Zoom) - requires e10s
// http://www.ghacks.net/2015/07/28/scrolling-in-firefox-to-get-a-lot-better-thanks-to-apz/
// user_pref("layers.async-pan-zoom.enabled", true);
// 3010: enable ctrl-tab previews
user_pref("browser.ctrlTab.previews", true);
// 3011: don´t open "page/selection source" in a tab. The window used instead is cleaner
// and easier to use and move around (eg developers/multi-screen).
user_pref("view_source.tab", false);
// 3012: spellchecking: 0=none, 1-multi-line controls, 2=multi-line &single-line controls
user_pref("layout.spellcheckDefault", 1);
// 3013: disable automatic "Work Offline" status
// https://bugzilla.mozilla.org/show_bug.cgi?id=620472
// https://developer.mozilla.org/en-US/docs/Online_and_offline_events
user_pref("network.manage-offline-status", false);
// 3015: disable tab animation, speed things up a little
user_pref("browser.tabs.animate", false);
// 3016: disable fullscreeen animation. Test using F11.
// Animation is smother but is annoyingly slow, while no animation can be startling
user_pref("browser.fullscreen.animate", false);
// 3017: submenu in milliseconds. 0=instant while a small number allows
// a mouse pass over menu items without any submenus alarmingly shooting out
user_pref("ui.submenuDelay", 75);
// (hidden pref)
// 3018: maximum number of daily bookmark backups to keep (default is 15)
user_pref("browser.bookmarks.max_backups", 2);
// 3020: FYI: urlbar click behaviour (with defaults)
user_pref("browser.urlbar.clickSelectsAll", true);
user_pref("browser.urlbar.doubleClickSelectsAll", false);
// 3021: FYI: tab behaviours (with defaults)
// open links in a new tab immediately to the right of parent tab, not far right
user_pref("browser.tabs.insertRelatedAfterCurrent", true);
// switch to the parent tab (if it has one) on close, rather than to the adjacent right tab if
// it exists or to the adjacent left tab if it doesn´t. NOTE: requires browser.link.open_newwindow
// set to 3 (see pref 3007). NOTE: does not apply to middle-click or Ctrl-clicking links.
user_pref("browser.tabs.selectOwnerOnClose", true);
// Options>General>When I open a link in a new tab, switch to it immediately
// default is unchecked = DON´T switch to it = true
user_pref("browser.tabs.loadInBackground", true);
// set behavior of pages normally meant to open in a new window (such as target="_blank"
// or from an external program), but that have instead been loaded in a new tab.
// true: load the new tab in the background, leaving focus on the current tab
// false: load the new tab in the foreground, taking the focus from the current tab.
user_pref("browser.tabs.loadDivertedInBackground", false);
// 3022: hide recently bookmarked items (you still have the original bookmarks) (FF49+)
user_pref("browser.bookmarks.showRecentlyBookmarked", false);
// 3023: disable automigrate, current default is false but may change (FF49+)
// need more info, but lock down for now
user_pref("browser.migrate.automigrate.enabled", false);
// END: internal custom pref to test for syntax errors
/*** 9996: PALEMOON SPECIFIC ( https://www.palemoon.org/ )
Full list maintained by Moonchild: https://forum.palemoon.org/viewtopic.php?f=24&t=3357
If you have issues or questions about any of these, please use the palemoon forums
NOTE: This section is no longer maintained [after version 10] ***/
// 9996-1: (v25.6+) disable canvas fingerprinting
// user_pref("canvas.poisondata", true);
// 9996-2: (v25.2+) control HSTS
// If editing this in about:config PM needs to be fully closed and then restarted
// NOTE: This is a trade-off between privacy vs security. HSTS was designed to increase
// security to stop MiTM attacks but can also be misused as a fingerprinting vector, by
// scrapping previously visited sites. Recommended: security over privacy. Your choice.
// user_pref("network.stricttransportsecurity.enabled", true);
// 9996-3: (v25.0+) controls whether to ignore an expired state of stapled OCSP responses
// If set to true, breaks with RFC6066 (like Firefox) and ignores the fact that stapled
// OCSP responses may be expired. If false (the default) aborts the connection.
// user_pref("security.ssl.allow_unsafe_ocsp_response", false);
// 9996-4: (v25.6+) Controls whether to completely ignore "autocomplete=off" on login fields
// user_pref("signon.ignoreAutocomplete", false);
// 9996-5: (v26.0+) read Moonchild´s description on the palemoon forum thread linked above
// user_pref("dom.disable_beforeunload", true);
/*** 9997: DEPRECATED
Personally confirmed by resetting as well as via documentation and DXR searches.
NOTE: numbers may get re-used ***/
// 2607: (23+) disable page thumbnails, it was around v23, not 100% sure when
// this pref was replaced with browser.pagethumbnails.capturing_disabled
// user_pref("pageThumbs.enabled", false);
// 2408: (31+) disable network API - fingerprinting vector
// user_pref("dom.network.enabled", false);
// 2620: (35+) disable WebSockets
// https://developer.mozilla.org/en-US/Firefox/Releases/35
// user_pref("network.websocket.enabled", false);
// 2023: (37+) disable camera autofocus callback (was in 36, not in 37)
// Not part of any specification, the API will be superceded by the WebRTC Capture
// and Stream API ( http://w3c.github.io/mediacapture-main/getusermedia.html )
// https://developer.mozilla.org/en-US/docs/Mozilla/Firefox_OS/API/CameraControl/
// user_pref("camera.control.autofocus_moving_callback.enabled", false);
// 1804: (41+) disable plugin enumeration
// user_pref("plugins.enumerable_names", "");
// 0420: (42+) disable tracking protection
// this particular pref was never in stable
// labelled v42+ because that´s when tracking protection landed
// user_pref("browser.polaris.enabled", false);
// 2803: (42+) what to clear on shutdown
// https://bugzilla.mozilla.org/show_bug.cgi?id=1102184#c23
// user_pref("privacy.clearOnShutdown.passwords", false);
// 0411: (43+) disable safebrowsing urls &download
// user_pref("browser.safebrowsing.gethashURL", "");
// user_pref("browser.safebrowsing.malware.reportURL", "");
// user_pref("browser.safebrowsing.provider.google.appRepURL", "");
// user_pref("browser.safebrowsing.reportErrorURL", "");
// user_pref("browser.safebrowsing.reportGenericURL", "");
// user_pref("browser.safebrowsing.reportMalwareErrorURL", "");
// user_pref("browser.safebrowsing.reportMalwareURL", "");
// user_pref("browser.safebrowsing.reportURL", "");
// user_pref("browser.safebrowsing.updateURL", "");
// 0420: (43+) disable tracking protection. FF43+ URLs are now part of safebrowsing
// https://wiki.mozilla.org/Security/Tracking_protection (look under Prefs)
// NOTE: getupdateURL = WRONG / never existed. updateURL = CORRECT and has been added FYI
// user_pref("browser.trackingprotection.gethashURL", "");
// user_pref("browser.trackingprotection.getupdateURL", "");
// user_pref("browser.trackingprotection.updateURL", "");
// 1803: (43+) remove plugin finder service
// http://kb.mozillazine.org/Pfs.datasource.url
// user_pref("pfs.datasource.url", "");
// 2403: (43+) disable scripts changing images - test link below
// http://www.w3schools.com/jsref/tryit.asp?filename=tryjsref_img_src2
// WARNING: will break some sites such as Google Maps and a lot of web apps
// user_pref("dom.disable_image_src_set", true);
// 2615: (43+) disable http2 for now as well
// user_pref("network.http.spdy.enabled.http2draft", false);
// 3001a: (43+) disable warning when a domain requests full screen
// replaced by setting full-screen-api.warning.timeout to zero
// user_pref("full-screen-api.approval-required", false);
// 3003: (43+) disable new search panel UI [Classic Theme Restorer can restore the old search]
// user_pref("browser.search.showOneOffButtons", false);
// 1201: (44+) block rc4 whitelist
// https://developer.mozilla.org/en-US/Firefox/Releases/44#Security
// user_pref("security.tls.insecure_fallback_hosts.use_static_list", false);
// 2417: (44+) disable SharedWorkers, which allow the exchange of data between iFrames that
// are open in different tabs, even if the sites do not belong to the same domain.
// https://www.torproject.org/projects/torbrowser/design/#identifier-linkability (no. 8)
// https://bugs.torproject.org/15562
// is used in FF 45and 46 code once, to set it for a test
// user_pref("dom.workers.sharedWorkers.enabled", false);
// 1005: (45+) disable deferred level of storing extra session data 0=all 1=http-only 2=none
// user_pref("browser.sessionstore.privacy_level_deferred", 2);
// 0334b: (46+) disable FHR (Firefox Health Report) v2 data being sent to Mozilla servers
// user_pref("datareporting.policy.dataSubmissionEnabled.v2", false);
// 0373: (46+) disable "Pocket". FF46 replaced these with extensions.pocket.*
// user_pref("browser.pocket.enabled", false);
// user_pref("browser.pocket.api", "");
// user_pref("browser.pocket.site", "");
// user_pref("browser.pocket.oAuthConsumerKey", "");
// 0410e: (46+) safebrowsing
// user_pref("browser.safebrowsing.appRepURL", "");
// Google application reputation check
// 0333b: (47+) disable about:healthreport page UNIFIED
// user_pref("datareporting.healthreport.about.reportUrlUnified", "data:text/plain,");
// 0807: (47+) disable history manipulation
// https://developer.mozilla.org/en-US/docs/Web/Guide/API/DOM/Manipulating_the_browser_history
// WARNING: if set to false it breaks some sites (youtube) ability to correctly show the
// url in location bar and for the forward/back tab history to work
// user_pref("browser.history.allowPopState", false);
// user_pref("browser.history.allowPushState", false);
// user_pref("browser.history.allowReplaceState", false);
// 0806: (48+) disable ´unified complete´: ´Search with [default search engine]´
// this feature has been added back in Classic Theme Restorer
// http://techdows.com/2016/05/firefox-unified-complete-aboutconfig-preference-removed.html
// user_pref("browser.urlbar.unifiedcomplete", false);
// 3006: (48+) disable enforced add-on signing
// NOTE: the preference is still in FF48+, but it´s legacy code and does not work in stable
// user_pref("xpinstall.signatures.required", false);
// 0372: (49+) disable "Hello" (TokBox/Telefonica WebRTC voice &video call PUP) WebRTC (IP leak)
// https://www.mozilla.org/en-US/privacy/firefox-hello/
// https://security.stackexchange.com/questions/94284/how-secure-is-firefox-hello
// https://support.mozilla.org/en-US/kb/hello-status
// user_pref("loop.enabled", false);
// user_pref("loop.server", "");
// user_pref("loop.feedback.formURL", "");
// user_pref("loop.feedback.manualFormURL", "");
// additional facebook loop settings
// user_pref("loop.facebook.appId", "");
// user_pref("loop.facebook.enabled", false);
// user_pref("loop.facebook.fallbackUrl", "");
// user_pref("loop.facebook.shareUrl", "");
// https://groups.google.com/d/topic/mozilla.dev.platform/nyVkCx-_sFw/discussion
// user_pref("loop.logDomains", false);
// 2202: (49+) ONE of the new window UI prefs
// user_pref("dom.disable_window_open_feature.scrollbars", true);
// 2431: (49+) disable ONE of the push notification prefs
// user_pref("dom.push.udp.wakeupEnabled", false);
// 0308: (50+) disable update plugin notifications
// if using Flash/Java/Silverlight, it is best to turn on their own auto-update mechanisms.
// See 1804 below: Mozilla only checks a few plugins and will soon do away with NPAPI
// user_pref("plugins.update.notifyUser", false);
// 0410a: (50+) "Block dangerous and deceptive content" pref name change
// user_pref("browser.safebrowsing.enabled", false);
// FF49 and earlier
// 1202: (50+) disable rc4 ciphers
// https://www.fxsitecompat.com/en-CA/docs/2016/rc4-support-has-been-completely-removed/
// https://trac.torproject.org/projects/tor/ticket/17369
// user_pref("security.ssl3.ecdhe_ecdsa_rc4_128_sha", false);
// user_pref("security.ssl3.ecdhe_rsa_rc4_128_sha", false);
// user_pref("security.ssl3.rsa_rc4_128_md5", false);
// user_pref("security.ssl3.rsa_rc4_128_sha", false);
// 1809: (50+) remove Mozilla´s plugin update URL
// user_pref("plugins.update.url", "");
// 1851: (51+) delay play of videos until they´re visible
// https://bugzilla.mozilla.org/show_bug.cgi?id=1180563
// user_pref("media.block-play-until-visible", true);
// 2504: (51+) disable virtual reality devices
// user_pref("dom.vr.oculus050.enabled", false);
// 2614: (51+) disable SPDY
// user_pref("network.http.spdy.enabled.v3-1", false);
/**- 9998: TO INVESTIGATE - TOR UPLIFT
https://wiki.mozilla.org/Security/Tor_Uplift/Tracking
// RESOLVED
// 1400´s: set whitelisted system fonts only (FF52+)
// If whitelist is empty, then whitelisting is considered disabled and all fonts are allowed.
// https://bugzilla.mozilla.org/show_bug.cgi?id=1121643
// user_pref("font.system.whitelist", "");
// 2698-append: privacy.firstparty.isolate.restrict_opener_access
// https://bugzilla.mozilla.org/show_bug.cgi?id=1319773
// ACTIVE
// 1200´s: Isolate the HSTS and HPKP cache by first party domain
// https://bugzilla.mozilla.org/show_bug.cgi?id=1323644
// 2400´s: reduce precision of time exposed by javascript
// https://bugzilla.mozilla.org/show_bug.cgi?id=1217238
// user_pref("javascript.options.privacy.reduce_time_precision", true);
// 2699-append: resource:
// URIs leak
// https://trac.torproject.org/projects/tor/ticket/8725
// https://bugzilla.mozilla.org/show_bug.cgi?id=863246
// test: https://www.browserleaks.com/firefox
// ASSIGNED
// 2001: preference to fully disable WebRTC JS API
// https://bugzilla.mozilla.org/show_bug.cgi?id=1314443
// 2699-append: enable fingerprinting resistence to WebGL
// https://bugzilla.mozilla.org/show_bug.cgi?id=1217290
// 2699-append: checkbox in about#preferences#privacy for privacy.resistFingerprinting
// when this lands, add note to 2699
// https://bugzilla.mozilla.org/show_bug.cgi?id=1308340
// 2699-append: use UTC timezone (spoof as UTC 0)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1330890
// 2699-append: new window sizes to round to hundreds
// Note: override values, future may enforce a select set of (inner) window measurements
// If override values are too big, the code falls back and determines it for you
// https://bugzilla.mozilla.org/show_bug.cgi?id=1330882
// user_pref("privacy.window.maxInnerWidth", 1366);
// user_pref("privacy.window.maxInnerHeight", 768);
// BACKLOG
// 1400´s: prevent local font enumeration
// https://bugzilla.mozilla.org/show_bug.cgi?id=732096
// 1800´s: disable "This Plugin is Disabled" overlay
// https://bugzilla.mozilla.org/show_bug.cgi?id=967979
// user_pref("privacy.plugin_disabled_barrier.enabled", false);
// 2500´s: disable/mitigate canvas fingerprinting
// https://bugzilla.mozilla.org/show_bug.cgi?id=1041818
// 2500´s: enable prompt (site permission) before allowing canvas data extraction
// https://bugzilla.mozilla.org/show_bug.cgi?id=967895
// 2600´s: window.name
// https://bugzilla.mozilla.org/show_bug.cgi?id=444222
// 2698-append: checkbox in about:preferences#privacy for privacy.firstparty.isolate
// when this lands, add note to 2611
// https://bugzilla.mozilla.org/show_bug.cgi?id=1312655
// 2698-append: FPI and HTTP Alternative Services (see 2666)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1334690
// 2698-append: FPI and SPDY/HTTP2
// https://bugzilla.mozilla.org/show_bug.cgi?id=1334693
// 2699-append: disable keyboard fingerprinting
// Test: https://w3c.github.io/uievents/tools/key-event-viewer.html
// https://bugzilla.mozilla.org/show_bug.cgi?id=1222285
// 2699-append: disable WebSpeech API
// https://bugzilla.mozilla.org/show_bug.cgi?id=1333641
// see also: web speech exposes TTS engines
// https://bugzilla.mozilla.org/show_bug.cgi?id=1233846
// 2699-append: spoof Navigator API
// https://bugzilla.mozilla.org/show_bug.cgi?id=1333651
// 2699-append: set and enforce various prefs with privacy.resistFingerprinting
// https://bugzilla.mozilla.org/show_bug.cgi?id=1333933
// 2699-append: bundle and whitelist fonts with privacy.resistFingerprinting
// https://bugzilla.mozilla.org/show_bug.cgi?id=1336208
***/
/**- 9999: TO INVESTIGATE - OTHER
// 1600´s: restrict the contents of referrers attached to cross-origin requests (FF52+)
// 0- 1- 2-scheme+hostname+port
// user_pref("network.http.referer.XOriginTrimmingPolicy", 2);
// 1600´s: default referrer fallback override? (FF52+?)
// 0-no-referer 1-same-origin 2-strict-origin-when-cross-origin
// 3-no-referrer-when-downgrade (default)
// https://bugzilla.mozilla.org/show_bug.cgi?id=1304623
// user_pref("network.http.referer.userControlPolicy", 3);
// 3000´s: show system add-ons in about:addons (so you can enable/disable them) - NOT landed yet
// https://bugzilla.mozilla.org/show_bug.cgi?id=1231202
// user_pref("extensions.hideSystemAddons", false);
// (hidden pref)
// ^^ keep an eye on extensions.systemAddon* prefs
// dom.presentation.*
// privacy.userContext.* (Containers)
// use a private container for thumbnail loads (FF51+)
// user_pref("privacy.usercontext.about_newtab_segregation.enabled", true);
// browser.newtabpage.remote*
// user_pref("browser.formfill.expire_days", 1);
// user_pref("javascript.options.shared_memory", false);
// user_pref("plugin.disable_full_page_plugin_for_types", "application/pdf");
// network.http.enablePerElementReferrer
// history.length XSHM fix
// https://bugzilla.mozilla.org/show_bug.cgi?id=1315203
// sandbox levels (recommended to leave at what Firefox sets it to)
// http://www.ghacks.net/2017/01/23/how-to-change-firefoxs-sandbox-security-level/
// security.sandbox.content.level
***/
/**- APPENDIX A: TEST SITES
Here is an exhaustive list of various websites in which to test your browser. You should enable
JS on these sites for the tests to present a worst-case scenario. In reality, you should control
JS and XSS (cross site scripting) on sites with add-ons such as NoScript, uMatrix, uBlock Origin,
among others, to reduce the possibility of fingerprinting attacks.
url: http://www.ghacks.net/2015/12/28/the-ultimate-online-privacy-test-resource-list/
// * 01: Fingerprinting
Panopticlick https://panopticlick.eff.org/
JoDonym http://ip-check.info/?lang=en
Am I Unique? https://amiunique.org/
Browserprint https://browserprint.info/test
// * 02: Multiple Tests [single page]
Whoer https://whoer.net/
5who http://5who.net/?type=extend
IP/DNS Leak https://ipleak.net/
IP Duh http://ipduh.com/anonymity-check/
// * 03: Multiple Tests [multi-page]
BrowserSpy.dk http://browserspy.dk/
BrowserLeaks https://www.browserleaks.com/
HTML Security https://html5sec.org/
PC Flank http://www.pcflank.com/index.htm
// * 04: Encryption / Ciphers / SSL/TLS / Certificates
BadSSL https://badssl.com/
DCSec https://cc.dcsec.uni-hannover.de/
Qualys SSL Labs https://www.ssllabs.com/ssltest/viewMyClient.html
Fortify https://www.fortify.net/sslcheck.html
How´s My SSL https://www.howsmyssl.com/
RC4 https://rc4.io/
Heartbleed https://filippo.io/Heartbleed/
Freak Attack https://freakattack.com/clienttest.html
Logjam https://weakdh.org/
Symantec https://cryptoreport.websecurity.symantec.com/checker/views/sslCheck.jsp
// * 05: Other
AudioContext https://audiofingerprint.openwpm.com/
Battery https://pstadler.sh/battery.js/
DNS Leak https://www.dnsleaktest.com/
DNS Spoofability https://www.grc.com/dns/dns.htm
Evercookie https://samy.pl/evercookie/
Firefox Add-ons http://thehackerblog.com/addon_scanner/
localStorage http://www.filldisk.com/
HSTS Supercookie http://www.radicalresearch.co.uk/lab/hstssupercookies
HSTS [sniffly] https://zyan.scripts.mit.edu/sniffly/
HTML5 https://www.youtube.com/html5
Keyboard Events https://w3c.github.io/uievents/tools/key-event-viewer.html
rel=noopener https://mathiasbynens.github.io/rel-noopener/
Popup Killer http://www.kephyr.com/popupkillertest/index.html
Popup Test http://www.popuptest.com/
Redirects https://jigsaw.w3.org/HTTP/300/Overview.html
Referer Headers https://www.darklaunch.com/tools/test-referer
Resouce:
// URI https://www.browserleaks.com/firefox
WebRTC IP Leak https://www.privacytools.io/webrtc.html
// * 06: Safe Browsing, Tracking Protection
Attack https://itisatrap.org/firefox/its-an-attack.html
Blocked https://itisatrap.org/firefox/blocked.html
Malware https://itisatrap.org/firefox/unwanted.html
Phishing https://itisatrap.org/firefox/its-a-trap.html
Tracking https://itisatrap.org/firefox/its-a-tracker.html
***/
/**- APPENDIX B: FIREFOX ADD-ONS
A massive thank you to all the developers and online communities who provide and maintain these.
Sometimes preferences alone are not enough. Here is a list of some essential addons for security,
privacy, and fingerprinting protection. This is not a debate, it´s just a list covering JS, XSS,
AdBlocking, cookies, DOM Storage, UTM, redirects, and other items. Some are global, others allow
granular control. While I believe most of these are the very best of the best, this can be subjective
depending on your needs. Some of these may become obsolete with upcoming FF changes (canvas,
resource:
// URI), some of these are debatable (should we UA spoof?), some I´m still looking for
a better solution, and some I do not use but they will suit a lot of users.
NoScript https://addons.mozilla.org/en-US/firefox/addon/noscript/
uBlock Origin https://addons.mozilla.org/en-US/firefox/addon/ublock-origin/
uMatrix https://addons.mozilla.org/en-US/firefox/addon/umatrix/
*Cookie Controller https://addons.mozilla.org/en-US/firefox/addon/cookie-controller/
*Self-Destructing Cookies https://addons.mozilla.org/en-US/firefox/addon/self-destructing-cookies/
HTTPS Everywhere https://addons.mozilla.org/en-US/firefox/addon/https-everywhere/
CanvasBlocker https://addons.mozilla.org/en-US/firefox/addon/canvasblocker/
No Resource URI Leak https://addons.mozilla.org/en-US/firefox/addon/no-resource-uri-leak/
Decentraleyes https://addons.mozilla.org/en-US/firefox/addon/decentraleyes/
NoRedirect https://addons.mozilla.org/en-US/firefox/addon/noredirect/
UAControl https://addons.mozilla.org/en-US/firefox/addon/uacontrol/
User-Agent JS Fixer https://addons.mozilla.org/en-US/firefox/addon/user-agent-js-fixer/
Popup Blocker Ultimate https://addons.mozilla.org/en-US/firefox/addon/popup-blocker-ultimate/
Pure URL https://addons.mozilla.org/en-US/firefox/addon/pure-url/
**Google Privacy https://addons.mozilla.org/en-US/firefox/addon/google-privacy/
***Quick Java https://addons.mozilla.org/en-US/firefox/addon/quickjava/
* Don´t use both cookie add-ons
** Yes, I use google search sometimes (my choice). I have some global add-ons that address
tracking in URLS, but am still looking for a working, comprehensible solution.
*** It´s not just Java! Covers JS, Cookies, Java, Flash... and more. Customisable controls and defaults
NOTE: At the time of publication the following are not e10s compatible:
Google Privacy, NoRedirect, UAControl, User-Agent JS Fixer, Popup Blocker Ultimate
***/
//
user_pref("extensions.update.enabled", false);
user_pref("toolkit.telemetry.cachedClientID", "");
// 0360: disable new tab tile ads & preload &marketing junk
user_pref("browser.newtab.preload", false);
user_pref("browser.newtabpage.directory.ping", "data:text/plain,");
user_pref("browser.newtabpage.directory.source", "data:text/plain,");
user_pref("browser.newtabpage.enabled", false);
user_pref("browser.newtabpage.enhanced", false);
user_pref("browser.newtabpage.introShown", true);
// 0203: disable using OS locale, force APP locale
user_pref("intl.locale.matchOS", false);
// 0204: set APP local
user_pref("general.useragent.locale", "en-US");
// 0100: STARTUP
user_pref("ghacks_user.js.parrot", "
// 0100 syntax error: the parrot´s dead!");
// 0101: disable "slow startup" options
// warnings, disk history, welcomes, intros, EULA, default browser check
user_pref("browser.slowStartup.notificationDisabled", true);
user_pref("browser.slowStartup.maxSamples", 0);
user_pref("browser.slowStartup.samples", 0);
user_pref("browser.rights.3.shown", true);
user_pref("browser.startup.homepage_override.mstone", "ignore");
user_pref("startup.homepage_welcome_url", "");
user_pref("startup.homepage_welcome_url.additional", "");
user_pref("startup.homepage_override_url", "");
user_pref("browser.laterrun.enabled", false);
user_pref("browser.shell.checkDefaultBrowser", false);
user_pref("browser.usedOnWindows10.introURL", "");
// 0102: set start page (0=blank, 1=home, 2=last visited page, 3=resume previous session)
// home = browser.startup.homepage preference
// You can set all of this from Options>General>Startup
//
user_pref("browser.startup.page", 0);
user_pref("geo.wifi.xhr.timeout", 1);
user_pref("browser.search.geoip.timeout", 1);
// 0206: disable geographically specific results/search engines eg: "browser.search.*.US"
// i.e ignore all of Mozilla´s multiple deals with multiple engines in multiple locales
user_pref("browser.search.geoSpecificDefaults", false);
user_pref("browser.search.geoSpecificDefaults.url", "");
// 0370: disable "Snippets" (Mozilla content shown on about:home screen)
// https://wiki.mozilla.org/Firefox/Projects/Firefox_Start/Snippet_Service
// MUST use HTTPS - arbitrary content injected into this page via http opens up MiTM attacks
user_pref("browser.aboutHomeSnippets.updateUrl", "https://127.0.0.1");
user_pref("browser.link.open_newwindow", 3);
// 3010: enable ctrl-tab previews
user_pref("browser.ctrlTab.previews", false);
// 3012: spellchecking: 0=none, 1-multi-line controls, 2=multi-line &single-line controls
user_pref("layout.spellcheckDefault", 0);
// 3011: don´t open "page/selection source" in a tab. The window used instead is cleaner
// and easier to use and move around (eg developers/multi-screen).
user_pref("view_source.tab", false);
// 3015: disable tab animation, speed things up a little
user_pref("browser.tabs.animate", false);
// 3016: disable fullscreeen animation. Test using F11.
// Animation is smother but is annoyingly slow, while no animation can be startling
user_pref("browser.fullscreen.animate", false);
// 3018: maximum number of daily bookmark backups to keep (default is 15)
user_pref("browser.bookmarks.max_backups", 2);
// 3020: FYI: urlbar click behaviour (with defaults)
user_pref("browser.urlbar.clickSelectsAll", false);
user_pref("browser.urlbar.doubleClickSelectsAll", true);
// 3022: hide recently bookmarked items (you still have the original bookmarks) (FF49+)
user_pref("browser.bookmarks.showRecentlyBookmarked", false);
// 3023: disable automigrate, current default is false but may change (FF49+)
// need more info, but lock down for now
user_pref("browser.migrate.automigrate.enabled", false);
// 2615: (43+) disable http2 for now as well
//
user_pref("network.http.spdy.enabled.http2draft", false);
---------------
Pale Moon
// 9996-1: (v25.6+) disable canvas fingerprinting
user_pref("canvas.poisondata", true);
// 9996-2: (v25.2+) control HSTS
// If editing this in about:config PM needs to be fully closed and then restarted
// NOTE: This is a trade-off between privacy vs security. HSTS was designed to increase
// security to stop MiTM attacks but can also be misused as a fingerprinting vector, by
// scrapping previously visited sites. Recommended: security over privacy. Your choice.
user_pref("network.stricttransportsecurity.enabled", true);
user_pref("privacy.resistFingerprinting", true);
// 9996-3: (v25.0+) controls whether to ignore an expired state of stapled OCSP responses
// If set to true, breaks with RFC6066 (like Firefox) and ignores the fact that stapled
// OCSP responses may be expired. If false (the default) aborts the connection.
user_pref("security.ssl.allow_unsafe_ocsp_response", false);
// 9996-5: (v26.0+) read Moonchild´s description on the palemoon forum thread linked above
user_pref("dom.disable_beforeunload", false);
OCSP should be set to 0 (zero), otherwise any connection-buildup fails.
/usr/lib64/firefox/distribution/policies.json, examples and explanation see wiki.kairaven.de
{
"policies": {
"BlockAboutProfiles": true,
"DisableAppUpdate": true,
"DisableBuiltinPDFViewer": true,
"DisableFeedbackCommands": true,
"DisableFirefoxAccounts": true,
"DisableFirefoxScreenshots": true,
"DisableFirefoxStudies": true,
"DisableFormHistory": true,
"DisableMasterPasswordCreation": true,
"DisablePocket": true,
"DisableProfileImport": true,
"DisableProfileRefresh": true,
"DisableSetDesktopBackground": true,
"DisableSystemAddonUpdate": true,
"DisableTelemetry": true,
"DisplayBookmarksToolbar": true,
"DisplayMenuBar": true,
"DontCheckDefaultBrowser": true,
"EnableTrackingProtection": {
"Locked": true,
"Value": false
},
"FlashPlugin": {
"Default": false,
"Locked": true
},
"Homepage": {
"Locked": true,
"URL": "https://host.domain.tld/"
},
"InstallAddonsPermission": {
"Default": true
},
"OfferToSaveLogins": false,
"OverrideFirstRunPage": "",
"OverridePostUpdatePage": "",
"PopupBlocking": {
"Default": true
},
"SearchBar": "separate"
}
}
 This is not enough! Lookout for all URI resp. URI, for example "http" and ".com" within the listing obtained by about:config and remove quit all of them with some care! You can find more entries in http://kb.mozillazine.org/About:config_Entries . For Firefox, set the system clock and time zone to another value than local and almost UTC. By default your browser trusts 100´s of Certificate Authorities (CAs) from various organizations to guarantee privacy of your encrypted communications with websites. Some CAs have been known for misusing or deliberately abusing this power in the past, and a single malicious CA can compromise all your encrypted communications! Follow this document to only trust a selected, trimmed-down list of CAs. This is not enough! Lookout for all URI resp. URI, for example "http" and ".com" within the listing obtained by about:config and remove quit all of them with some care! You can find more entries in http://kb.mozillazine.org/About:config_Entries . For Firefox, set the system clock and time zone to another value than local and almost UTC. By default your browser trusts 100´s of Certificate Authorities (CAs) from various organizations to guarantee privacy of your encrypted communications with websites. Some CAs have been known for misusing or deliberately abusing this power in the past, and a single malicious CA can compromise all your encrypted communications! Follow this document to only trust a selected, trimmed-down list of CAs.
Set quit all large numbers in about:config resp. user.js to 0 resp. -1, for example the last update times of the browser and its extensions.
 Further hardening Further hardening
This still is not enough too! Here´s some other tips how you can further harden Firefox (52.9):
By default your browser trusts 100´s of Certificate Authorities (CAs) from various organizations to guarantee privacy of your encrypted communications with websites. Some CAs have been known for misusing or deliberately abusing this power in the past, and a single malicious CA can compromise all your encrypted communications! Follow this document to only trust a selected, trimmed-down list of CAs.
Keep your browser updated! If you check Firefox´s security advisories, you´ll see that pretty much every new version of Firefox contains some security updates. If you don´t keep your browser updated, you´ve already lost the game.
Disable/uninstall all unnecessary extensions and plugins!
Use long and unique passwords/passphrases for each website/service.
Prefer open-source, reviewed and audited software and operating systems whenever possible.
Do not transmit information meant to be private over unencrypted communication channels.
Use a search engine that doesn´t track its users, and set it as default search engine.
If a plugin is absolutely required, check for plugin updates
Create different profiles for different purposes
Change the Firefox´s built-in tracking protection to use the strict list
Change the timezone for Firefox by using the TZ environment variable (see here) to reduce it´s value in browser fingerprinting
If you are concerned about more advanced threats, use specialized hardened operating systems and browsers such as Tails or Tor Brower Bundle
Disable Safe Browsing service
Safe Browsing offers phishing protection and malware checks, however it may send user information (e.g. URL, file hashes, etc.) to third parties like Google.
To disable the Safe Browsing service, in about:config set:
browser.safebrowsing.malware.enabled to false
browser.safebrowsing.phishing.enabled to false
In addition disable download checking, by setting
browser.safebrowsing.downloads.enabled to false.
Set a new timezone, set the timezone by starting firefox through the command:
TZ=UTC firefox
https://github.com/pyllyukko/user.js#download
https://wiki.archlinux.org/index.php/Firefox_privacy#Change_browser_time_zone
Browser Display Statistics - W3Schools
Screen Resolution Statistics. As of January 2017, about 95% of our visitors have a screen resolution of 1024x768 pixels or higher.
www.w3schools.com/browsers/browsers_display.asp
Back to our main text:
To the main risks during the surfing with the browser belong:
JS.Inject: malicious JavaScript-scenes integrating malicious code into HTML-code of websides.
JS.BtcMine: JavaScript-Scenes aimed to hidden cryptominning.
Trojan.SpyBot.699: spyware logging key strokes of the keyboard, executing commands of cyber criminals, stealing trustful data and money from bank accounts.
This is, what you can do against these risks:
- JavaScript is actitated. In this case special browser extensions (especially script blocker) like for Firefox are strongly recommended. Configure them well like recommended (on this webside in the following).
- The browser, at least the profiles, are stored in the home-, even better onto an extra small partition, that can be mounted read-only in fstab, additionally with the option "noexec", or by the command "mount -o remount ro partition-device-file". Test, if the browser is still starting.
- Set ACL-access-rights (setfacl) within the home-directory of surfuser: setfacl -m u:surfuser:r-x /home/surfuser, setfacl -m u:surfuser:r-x /home/surfuser/.mozila, setfacl -m u:surfuser:r-x /home/surfuser/.mozilla/firefox and so on. (notice, that this is not possible for all directories within the home-directory).
- To go sure: deactivate JavaScript (by the disadvantage, that some sides do not present everything or resctrict functions)
All itmes introduced green hook by green hook should be applied and Linfw3 should be in use. Install OpenSourced software only, Download it from trusted sources (perform packet-signature- and md5-checksum-verification).
After each installation, eventually scan for malicious software through a virus scanner.
Firefox-52.9.0
 ftp://ftp.pbone.net/mirror/ftp5.gwdg.de/pub/opensuse/repositories/home:/linux4humans:/sle11_ ftp://ftp.pbone.net/mirror/ftp5.gwdg.de/pub/opensuse/repositories/home:/linux4humans:/sle11_
software:/firefox/openSUSE_Evergreen_11.4/x86_64/
MozillaFirefox-52.9.0-10.2.x86_64.rpm (from 02/2019)
https://slackware.pkgs.org/14.0/salix-x86_64/mozilla-firefox-52.9.0esr-x86_64-1gv.txz.html (slack14.0)
http://download.salixos.org/x86_64/14.0/salix/xap/mozilla-firefox-52.9.0esr-x86_64-1gv.txz (slack14.0)
https://fr2.rpmfind.net/linux/mageia/distrib/6/x86_64/media/core/updates/firefox-52.9.0-1.mga6.x86_64.rpm
https://rpm.pbone.net/index.php3/stat/4/idpl/54051369/dir/opensuse_leap_15/com/MozillaFirefox-52.9.0-lp150.5.1.x86_64.rpm.html
https://rpm.pbone.net/index.php3/stat/4/idpl/55298083/dir/opensuse/com/MozillaFirefox-52.9.0-4.5.x86_64.rpm.html
 Security warnings against Firefox-extensions WOT, disconnect, Ghostery, ... Security warnings against Firefox-extensions WOT, disconnect, Ghostery, ...
More details see News&Links#Computer
 Millionen users affected: 500 Chrome-extensions eavesdrop surf data, CHIP, 14.02.2020 Millionen users affected: 500 Chrome-extensions eavesdrop surf data, CHIP, 14.02.2020
Browser-Erweiterungen sind bei vielen Nutzern beliebt, weil sie damit nützliche Funktionen nachrüsten können. Auf der anderen Seite sorgen die Zusatz-Tools für Chrome und Firefox immer wieder für Datenskandale.
Das passiert leider viel zu häufig, sodass man das auch schnell wieder vergisst und zur Tagesordnung übergeht: Zur Erinnerung, im letzten Jahr wurden 4 Millionen Nutzer durch Browser-Erweiterungen ausspioniert, Firefox war davon zwar auch betroffen, aber hauptsächlich hat es Chrome-Nutzer erwischt. Jetzt deckten Sicherheitsexperten eine noch größere Sache auf: Über 500 Chrome-Erweiterungen haben Nutzerdaten angezapft und Werbung in den Browser eingeschleust.
https://www.chip.de/news/Millionen-Nutzer-betroffen-500-Chrome-Erweiterungen-spionieren-Surfdaten-aus_181480214.html
Brian Krebs: Security expert warns: That´s why you should not use (quit) no browser-extensions, STERN.de, 08.03.2020
Mit Extensions lassen sich Browser wie Chrome oder Firefox einfach um zusätzliche Funktionen erweitern. Doch die kleinen Programme sind mächtiger als man glaubt - und werden zum Teil von dubiosen Firmen aufgekauft und missbraucht.
[...] Doch den Einsatz der Erweiterungen sollte man sich genau überlegen.
Das rät der etablierte Sicherheits-Experte Brian Krebs. Der Anlass ist ein aktueller Fall. Völlig aus blauem Himmel war die Webseite der US-Gesundheitsversicherer Blue Shield of California von mehreren Antivirenprogrammen als bösartige Seite markiert worden, berichtet Krebs in seinem Blog. Bei einer Untersuchung stellte man fest, dass eine Browsererweiterung Schuld war, die einer der Seiten-Entwickler sich heruntergeladen und in seinem Chrome-Browser installiert hatte.
Umbau zur Werbeschleuder
Die schuldige Erweiterung Page Ruler soll Entwicklern helfen, die Größe von Bildern und andere Elementen auf von ihnen erstellten Webseiten korrekt einzuschätzen. Die etwa 400.000 Mal installierte Erweiterung war eigentlich mit guten Absichten erstellt worden. Das Problem: Der Entwickler hatte sie irgendwann an eine Werbefirma verkauft - und die hatte daraus ein Schadprogramm gemacht, das heimlich Werbeeinblendungen auf damit erstellten Webseiten einbaut. Die Antivirenprogramme hatten auf den untergeschmuggelten Programmcode reagiert und eine unschuldige Firma galt auf einmal als gefährlich.
Der Vorfall zeige ein ganz grundlegendes Problem der Erweiterungen, argumentiert Krebs. Zum einen seien sie oft deutlich mächtiger, als die meisten Nutzer ahnten. So können sie mit den richtigen Berechtigungen alles mitlesen, was im Browser geschieht oder den Nutzer auf andere Webseiten wie Fakeshops umleiten. Zum anderen seien die oft von Hobby-Entwicklern irgendwann mal zusammengeschusterten und nicht mehr gepflegten Erweiterungen anfällig, von Werbefirmen aufgekauft zu werden. Die Firmen bekommen so ein bereits etabliertes Programm, der Entwickler verdient an einem Projekt, um das er sich ohnehin nicht mehr gekümmert hatte.
https://www.stern.de/digital/computer/sicherheits-experte-warnt--darum-sollten-sie--fast--keine-browser-erweiterungen-nutzen-9172600.html
Nevertheless - in all cases - the browser-extensions (especiall ad- resp. script-blocker) should be installed.
OpenSource-firefox-browser-extensions recommended by Jondofox for Firefox ESR and Tor-Browser (Firefox ESR) are listed, we think, they are a must for installation ( and updating ):
 useragent-overrider (ff, enhanceable lists), SecretAgent (extension from palemoon.org for Firefox-ESR-52.9, Tor and Pale Moon, our TOP-recommendation under the "overrider": session-, tab- or sidewise rotating user-agents, stealth mode, normal mode, Hijanking-Protection, Javascript-OSCPU-Strings, etags&cacheing, proxy headers, Referer-Spoofing, Privacy-Tuning and more) or UserAgentSwitcher (ff, Pale Moon, enhancable lists) (analogous Konqueror through menu or configuration file /home/surfuser/.kde4/share/config/kio_httprc), useragent-overrider (ff, enhanceable lists), SecretAgent (extension from palemoon.org for Firefox-ESR-52.9, Tor and Pale Moon, our TOP-recommendation under the "overrider": session-, tab- or sidewise rotating user-agents, stealth mode, normal mode, Hijanking-Protection, Javascript-OSCPU-Strings, etags&cacheing, proxy headers, Referer-Spoofing, Privacy-Tuning and more) or UserAgentSwitcher (ff, Pale Moon, enhancable lists) (analogous Konqueror through menu or configuration file /home/surfuser/.kde4/share/config/kio_httprc),
noscript (Adblocker, rpm mozilla-adblockplus mit OpenSource src.rpm (fc29, el7, el6), recommended by NRW-TV 2013; includes Cross-Site-Scripting-Protection, ABE, Clear-Click-Protection, automatical exchange of http with https, secure Cookie-Managerment, ping-protection and so on) and
 ublock-origin (excellent, resource-bewaring ad- and scriptblocker recommended by trojaner-board.de), firefox-ublock_origin (alt1, pkgs.org, mozilla.org), or ublock-origin (excellent, resource-bewaring ad- and scriptblocker recommended by trojaner-board.de), firefox-ublock_origin (alt1, pkgs.org, mozilla.org), or
 1. AdblockPlus (ABP resp. AdblockLatitude (ABL) for Pale Moon, a rpm with belonging OpenSource, an src.rpm from fc or alt-linux) (we recommend this one), https://fr2.rpmfind.net/linux/fedora-secondary/releases/29/Everything/i386/os/Packages/m/mozilla-adblockplus-2.9.1-4.fc29.noarch.rpm, https://fr2.rpmfind.net/linux/epel/6/x86_64/Packages/m/mozilla-adblockplus-2.6.6-1.el6.noarch.rpm, and 1. AdblockPlus (ABP resp. AdblockLatitude (ABL) for Pale Moon, a rpm with belonging OpenSource, an src.rpm from fc or alt-linux) (we recommend this one), https://fr2.rpmfind.net/linux/fedora-secondary/releases/29/Everything/i386/os/Packages/m/mozilla-adblockplus-2.9.1-4.fc29.noarch.rpm, https://fr2.rpmfind.net/linux/epel/6/x86_64/Packages/m/mozilla-adblockplus-2.6.6-1.el6.noarch.rpm, and
 2. (past 1. ABP and before 3. noscript) RequestPolicy(-BlockContinued) against Cross-Site-Attacks like Cross-Site-Scripting and Cross-Tracking upon the website-intern blocking of server-transfers ( rpm: mozilla-requestpolicy (-1.0-0.22.20171019git633302 fc29, el7, el6), actually still unavailable for Firefox Quantum, so, in order to keep Firefox-ESR-52.9, configure about:config followed by extensions.torbuttion.lastUpdateCheck false ), https://fr2.rpmfind.net/linux/fedora-secondary/releases/29/Everything/i386/os/Packages/m/mozilla-adblockplus-2.9.1-4.fc29.noarch.rpm, https://fr2.rpmfind.net/linux/epel/6/x86_64/Packages/m/mozilla-adblockplus-2.6.6-1.el6.noarch.rpm, and/or 2. (past 1. ABP and before 3. noscript) RequestPolicy(-BlockContinued) against Cross-Site-Attacks like Cross-Site-Scripting and Cross-Tracking upon the website-intern blocking of server-transfers ( rpm: mozilla-requestpolicy (-1.0-0.22.20171019git633302 fc29, el7, el6), actually still unavailable for Firefox Quantum, so, in order to keep Firefox-ESR-52.9, configure about:config followed by extensions.torbuttion.lastUpdateCheck false ), https://fr2.rpmfind.net/linux/fedora-secondary/releases/29/Everything/i386/os/Packages/m/mozilla-adblockplus-2.9.1-4.fc29.noarch.rpm, https://fr2.rpmfind.net/linux/epel/6/x86_64/Packages/m/mozilla-adblockplus-2.6.6-1.el6.noarch.rpm, and/or
 3. (past 2. RequestPolicy) uMatrix (uM, https://github.com/gorhill/uMatrix/releases/download/1.4.1b6/uMatrix_1.4.1b6.firefox.signed.xpi) or noscript, like RequestPolicy, but with more options for further protection ( rpm: seamonkey-noscript (el6, 5.1.9-3) or mozilla-noscript (-5.1.8.5 resp. 5.1.8.6, 5.1.8.7-1 fc29, el7, el6), http://ftp.pbone.net/mirror/archive.fedoraproject.org/fedora/linux/updates/25/armhfp/Packages/m/mozilla-noscript-5.1.7-1.fc25.noarch.rpm, and/or 3. (past 2. RequestPolicy) uMatrix (uM, https://github.com/gorhill/uMatrix/releases/download/1.4.1b6/uMatrix_1.4.1b6.firefox.signed.xpi) or noscript, like RequestPolicy, but with more options for further protection ( rpm: seamonkey-noscript (el6, 5.1.9-3) or mozilla-noscript (-5.1.8.5 resp. 5.1.8.6, 5.1.8.7-1 fc29, el7, el6), http://ftp.pbone.net/mirror/archive.fedoraproject.org/fedora/linux/updates/25/armhfp/Packages/m/mozilla-noscript-5.1.7-1.fc25.noarch.rpm, and/or
 No Resource URI Leak: "Deny resource:// access to web content: We fill the hole to defend againt fingerprinting. Very important to Firefox privacy. A direct workaround for bugzil.la/863246. No Resource URI Leak: "Deny resource:// access to web content: We fill the hole to defend againt fingerprinting. Very important to Firefox privacy. A direct workaround for bugzil.la/863246.
Block access to resource:// URIs from the Web, block web-exposed subset of chrome:// URIs, restrict about:pages by default (for paranoids)" and
 Decentraleyes: local emulation of decentralized networks: "protects against tracking by delivering a centralized content. Queries can not be receipt by networks like "Google Hosted Libraries", but they got imitated, so that the websites remain intact. It also adds regular content blocks: Decentraleyes: local emulation of decentralized networks: "protects against tracking by delivering a centralized content. Queries can not be receipt by networks like "Google Hosted Libraries", but they got imitated, so that the websites remain intact. It also adds regular content blocks:
• Completes already installed blocker like uBlock Origin or Adblock Plus etc.
- Supported networks: Google Hosted Libraries, Microsoft Ajax CDN, CDNJS (Cloudflare), jQuery CDN (MaxCDN), jsDelivr (MaxCDN), Yandex CDN, Baidu CDN, Sina Public Resources, und UpYun Libraries.
- Bundled resources: AngularJS, Backbone.js, Dojo, Ember.js, Ext Core, jQuery, jQuery UI, Modernizr, MooTools, Prototype, Scriptaculous, SWFObject, Underscore.js and Web Font Loader" and
 Privacy Protector Plus ( OpenSource ) against webbugs, tracking and more, not obtainable for Pale Moon, Block Content for Pale Moon only or Privoxy ( filtering such website contents, local proxy) and Privacy Protector Plus ( OpenSource ) against webbugs, tracking and more, not obtainable for Pale Moon, Block Content for Pale Moon only or Privoxy ( filtering such website contents, local proxy) and
 Private Tab ( if you are surfing in a private window, Firefox does not store: visited websites, cookies, search queries and temporary files ) Private Tab ( if you are surfing in a private window, Firefox does not store: visited websites, cookies, search queries and temporary files )
 Toggle JavaScript for Pale Moon, a buttom for the fast activation and deactivation of JavaScript and Toggle JavaScript for Pale Moon, a buttom for the fast activation and deactivation of JavaScript and
 Cookie Controller (for effective work, disable cookies in the browser per default, but logins like for ebay might not be possible anymore. In this case, set standard "sessions cookies enabled") and Cookie Controller (for effective work, disable cookies in the browser per default, but logins like for ebay might not be possible anymore. In this case, set standard "sessions cookies enabled") and
 CanvasBlocker (also for Pale Moon) in order to avoid Canvas Fingerprinting and CanvasBlocker (also for Pale Moon) in order to avoid Canvas Fingerprinting and
 RefControl (Pale Moon: Change Referer Buttom) for the control of referers and RefControl (Pale Moon: Change Referer Buttom) for the control of referers and
 Link Cleaner cares for shortened URLs for copying through the removal of superflicious tracking-parameters and Link Cleaner cares for shortened URLs for copying through the removal of superflicious tracking-parameters and
 Link Redirect Fixer (not for Pale Moon) in order to skip pages that some pages use before redirecting to a final page and Link Redirect Fixer (not for Pale Moon) in order to skip pages that some pages use before redirecting to a final page and
 CSS Exfil Protection by Mike Gualtieri ( download from https://addons.cdn.mozilla.net/user-media/addons/931864/css_exfil_protection-1.0.17-an+fx.xpi ) and (eventually...) CSS Exfil Protection by Mike Gualtieri ( download from https://addons.cdn.mozilla.net/user-media/addons/931864/css_exfil_protection-1.0.17-an+fx.xpi ) and (eventually...)
 Librefox: https://github.com/intika/Librefox/releases/download/Librefox-v2.1-v64.0.0/Librefox-2.1-Firefox-Linux-64.0.0.zip Librefox: https://github.com/intika/Librefox/releases/download/Librefox-v2.1-v64.0.0/Librefox-2.1-Firefox-Linux-64.0.0.zip
 disable_about_something: This makes your Firefox, Pale Moon and Thunderbird more secure from accidental operations on dangerous "about:*" pages. disable_about_something: This makes your Firefox, Pale Moon and Thunderbird more secure from accidental operations on dangerous "about:*" pages.
To block loading of an "about:*" page, you just have to define a new boolean preference "extensions.disable-about-something@clear-code.com.about.*" with the value "false". For example if you want to block loading of "about:permissions", just set "extensions.disable-about-something@clear-code.com.about.permissions" to "false". Otherwise - with no value or "true", the page is never blocked.
There are similar addons for specific "about:*" pages. They disables related menu items and others for the page, so they are recommended for general cases.
* "about:addons" : Disable Addons https://addons.mozilla.org/addon/disable-addons/
* "about:accounts" and "about:sync-*" : Disable Sync https://addons.mozilla.org/addon/disable-sync/
* "about:config" : Disable about:config https://addons.mozilla.org/addon/disable-aboutconfig/
extensions.disable-about-something@clear-code.com.about.permissions false
extensions.disable-about-something@clear-code.com.about.addons false
extensions.disable-about-something@clear-code.com.about.accounts false
extensions.disable-about-something@clear-code.com.about.sync-* false
extensions.disable-about-something@clear-code.com.about.profiles false
extensions.disable-about-something@clear-code.com.about.downloads false
..., but be careful with about:config !
Software::Browser
Mozilla protects Firefox ( gt;68 ) better against Fingerprinting and Crypto-Mining, PRO-LINUX, 10.04.2019
Mozilla integrates one more extended protection against tracking through fingerprinting and cryptomining.
https://www.pro-linux.de/news/1/26958/mozilla-sch%C3%BCtzt-firefox-besser-gegen-fingerprinting-und-krypto-mining.html
Integrierter Schutz vor Cross-Site-Tracking: Firefox >= 64
 "Palesomething" is a port of Firesomething for Pale Moon. This extension was originally written by Michael O´Rourke. "Palesomething" is a port of Firesomething for Pale Moon. This extension was originally written by Michael O´Rourke.
Since Firesomething´s final release for Firefox in May of 2007, Mozilla has abandoned its own technologies in favor of poor parody of Google´s protocols (WebExtensions), leaving many developers, including this one, disillusioned with the direction the Mozilla is taking. In contrast, Pale Moon has stepped into place as an XUL-centric browser, keeping backward compatibility better than Mozilla´s own flagship project. Palesomething was ported to Pale Moon to bring back some of that early optimism which Firefox has long since lost.
Palesomething is free for use or modification without limitation. It is released under the GNU General Public License with no warranty or guarantee of any kind. That being said, you can still ask any questions in the Comments section below, or contact me directly for assistance.
Change the product name in various parts of the browser. Random name generation ensures perpetual humor.
All your branding are belong to Firesomething. This extension will give Firefox an identity crisis by generating a new randomized browser name every time you open a new window. Confuse your friends and family with names like "Mozilla Firebadger" and "Mozilla Poweroyster". It´s as fun as you want it to be!
Features:
- Modifies the product name in the browser titlebar, Help menu, and About dialog titlebar.
- Generates random names using multiple name lists.
- Allows you to have a new name generated for each browser window, or use the same name for all windows.
- Optionally modifies the browser´s User-Agent string to reflect your custom browser name.
- Allows you to easily change the image in the About dialog.
- Keyboard shortcut Ctrl+´ (grave accent) in the browser window generates a new product name.
- Adds about:firefox and about:firesomething, newly discovered passages from the Book of Mozilla"
 *fonts:false* and geoip:disabled by about:config *fonts:false* and geoip:disabled by about:config
 and "javascript.enabled false", in order to disable JavaScript for the next time, what we suggest right up from the time past the filter-configuration of ABP (resp. ABL) in main, even much better is to set it the time before any filter-configuration - nevertheless until certain websites require it all too much. and "javascript.enabled false", in order to disable JavaScript for the next time, what we suggest right up from the time past the filter-configuration of ABP (resp. ABL) in main, even much better is to set it the time before any filter-configuration - nevertheless until certain websites require it all too much.
Site isolation - How to enable First-Party Isolation in Firefox, ghacks.net, 22.11.2017
First-Party Isolation is a new privacy feature of the Firefox web browser that Mozilla implemented in Firefox 55 for the first time.
[..] The following items are affected by First-Party Isolation: cookies, cache, HTTP Authentication, DOM Storage, Flash cookies, SSL and TLS session resumption, Shared Workers, blob URIs, SPDY and HTTP/2, automated cross-origin redirects, window.name, auto-form fill, HSTS and HPKP supercookies, broadcast channels, OCSP, favicons, mediasource URIs and Mediastream, speculative and prefetched connections.
https://www.ghacks.net/2017/11/22/how-to-enable-first-party-isolation-in-firefox/
Firefox-52-ESR: in "about:config" set "privacy.firstparty.isolate" to true or use ff-extension first_party_isolation.xpi by enpacking it into /home/surfuser/.mozilla/firefox/ and "setting privacy.firstparty.isolate" to true after typing in "about:config".
 Firefox ESR > 52 with Container-Tab (similar to privateTAB, but of isolating nature) for banking, personal, work and shopping: Drag its icon out of the icon-field for "Additional Tools and Features" (that can be obtained by customizing) and drop it into the symbol line followed by a mouseclick upon it Firefox ESR > 52 with Container-Tab (similar to privateTAB, but of isolating nature) for banking, personal, work and shopping: Drag its icon out of the icon-field for "Additional Tools and Features" (that can be obtained by customizing) and drop it into the symbol line followed by a mouseclick upon it
 Facebook-Container against tracking, at this time für Firefox >= 57 only: "Mozilla knows about the increasing care of facebook-user for their privacy and reacts with an Add-on "Facebook Container" deleting all cookies at first in conjunction with Facebook and logs them out. Next visit a container is created preventing from forwarding user behavior from outside the social network to Facebook. Links to other websites can be followed without getting stored. Altough this is not a protection against data abuse, it helps to gain more control about, what Facebook gets to know.". Facebook-Container against tracking, at this time für Firefox >= 57 only: "Mozilla knows about the increasing care of facebook-user for their privacy and reacts with an Add-on "Facebook Container" deleting all cookies at first in conjunction with Facebook and logs them out. Next visit a container is created preventing from forwarding user behavior from outside the social network to Facebook. Links to other websites can be followed without getting stored. Altough this is not a protection against data abuse, it helps to gain more control about, what Facebook gets to know.".
 Google-Container for Firefox >= 57 similar to the Facbook-Container Google-Container for Firefox >= 57 similar to the Facbook-Container
ABL of Pale Moon does not make any problems here, but the filter of ABP of Firefox-ESR (rpm mozilla-adblockplus (fc29, el7, el6) gets invisble and ineffective by disabling JavaScript, until JavaScript gets enabled by "javascript.enabled true" again.
Pale Moon (ideal browser with the three engines Firefox Quantum (we would like to recommend), Firefox-gecko (old api) and intern to elect) can be downloaded from PCLinuxOS (pclos) from http://ftp.pbone.net/mirror/www.pclinuxos.com/pclinuxos/apt/pclinuxos/64bit/RPMS.x86_64/ or https://ftp.nluug.nl/ftp/pub/os/Linux/distr/pclinuxos/pclinuxos/ and much more addresses, Pale Moon - extensions from https://addons.palemoon.org/extensions/
... and eventually like
Jondofox
the plugins (that only should be activated, if needed) like
flash-plugin (respective resign from it to be more careful)
and mplayerplugin and firefox-language-files
(everything execpt RequestPolicy is provided as sepearte RPMs (packages to download and install) )
or use Linux-Standard-Browser Konqueror with our adblocker-list (runs fine) for the integrated adblocker adblock.so or privoxy, adfilter (if not automatically by themselves), man-pages (always install actual ones like from mga6, de: man-pages-de (mga6)), wget (gnu-software for http- and ftp-downloadings), cups direct from cups.org for new printers, sane-backends for scanner, rootkit-hunter rkhunter (and only for the need going once more secure), software with security-lacks for server XAMPP announced by news and newsgroups like openssl from openssl.org in April 2014, similar to (still harmless) Shellshock end of September 2014 of bash, update from http://ftp.hosteurope.de/mirror/ftp.gnu.org/gnu/bash/. Not only Tarballs but also newest packages can be obtained especially from ALT Linux resp. CentOS 6.5 and 6.7 (el5 and el6). For mdv2007 zip, tar and bzip2 should not be forgotten - independent from the operating system do not forget Java, Adobe Reader (Adobe acroread and flashplayer: we strongly recommend to prefer offered Tarballs instead of rpm. (warning: In this case a backup especially of KDE (konqueror) should be made before unpacking the Tarball and copying the files into their directories!) , the router-software and all year the virus-scanner like clamav from http://clamav.net against the case of email-viruses or viruses in e-mail-attachements..., "and that might be already the list"- quit independent from the version of the operating system! Notice, that the size of firefox exceeded from Version 3 to Version 35 from around 4MB to more than 40 MB. Prefering browser like Konquerer might be the right consequence! Konqueror is the one, who lets TLS-(SSL-)certificates confirm each ssl-connection, what is based on gnutls.
Firefox: Certiftcate-error with message
Problem:
A self-signed certificate could not be stored permanently. The possible exception is grayed out.
Cause:
Chronic as much as zertificate are not stored permanenlty in private mode.
Solution:
"browser.privatebrowsing.autostart" should be set to "false", in order to store the certificate permanently. Alternatively leave the private mode. Now you can use the exception, which is not grayed out anymore.
https://www.linuxmuster.net/wiki/anwenderwiki:firefox:ausnahmeregeln
Root Certificates from many countries for import (click onto PEM (automatically), JSON, txt): https://ssl-tools.net/certificates and rpm: rootcertificates and ca-certificates
In this matter, we´d like to repeat the following case:
[ SOLVED by Gooken ]: Certifcates have to be confirmed each website-build-up, even if already confirmed.
Change to certs by cd /etc/pki/tls/certs and exchange the onto nothing linking or empty file ca-bundle.crt with its backup like ca-bundle.crt.rpmnew within the same directory certs: cp -fp ca-bundle.crt.rpmnew ca-bundle.crt.
Like Firefox Pale Moon should always be started with the option "--no-remote".
 Firefox (gecko): System Add-ons Firefox (gecko): System Add-ons
Packaged with Firefox are a bunch of system add-ons which are installed without your consent and they are essentially hidden (they are not listed in about:addons). Some of these add-ons have been and may currently be used for controversial purposes such as collecting data about how users interact with search engines, the browser, etc.. Typically i remove all of them, however you may want to keep some them after researching what they do and whether they preserve your privacy. On Linux these add-ons may be found at /usr/lib/firefox/browser/features and for Windows in \Program Files (x86)\Firefox\browser�eatures or \Program Files\Firefox\browser�eatures. You can delete them in Linux using the terminal:
cd /usr/lib/firefox/browser/features
sudo rm *.xpi
https://12bytes.org/articles/tech/firefox/firefoxgecko-configuration-guide-for-privacy-and-performance-buffs
 Firefox (gecko): Prevent from Supercookies Firefox (gecko): Prevent from Supercookies
Prevent trackable ff-extension-IDs containing supercookies, by deleting their contents and by commanding "chattr +i" upon their files, making them integer, that means readable only:
echo "" >> /home/surfuser/.mozilla/firefox/profile.default/SiteSecurityServiceState.txt
chattr +i /home/surfuser/.mozilla/firefox/profile.default/SiteSecurityServiceState.txt
echo "" >> /home/surfuser/.mozilla/firefox/profile.default/SiteSecurityServiceState.old
chattr +i /home/surfuser/.mozilla/firefox/profile.default/SiteSecurityServiceState.old
https://12bytes.org/articles/tech/firefox/firefoxgecko-configuration-guide-for-privacy-and-performance-buffs
 Firfox (gecko): Search engines Firfox (gecko): Search engines
I recommend reading Firefox Search Engine Cautions and Recommendations which offers information about how Mozilla monetizes Firefox with the
https://12bytes.org/articles/tech/firefox/firefox-search-engine-cautions-and-recommendations
source: https://12bytes.org/articles/tech/firefox/firefoxgecko-configuration-guide-for-privacy-and-performance-buffs
 Security for Firefox (Gecko): more links Security for Firefox (Gecko): more links
 https://12bytes.org/articles/tech/firefox/firefoxgecko-configuration-guide-for-privacy-and-performance-buffs https://12bytes.org/articles/tech/firefox/firefoxgecko-configuration-guide-for-privacy-and-performance-buffs
https://12bytes.org/articles/tech/firefox/the-firefox-privacy-guide-for-dummies
https://12bytes.org/articles/tech/encrypting-dns-traffic
https://12bytes.org/articles/tech/alternative-search-engines-that-respect-your-privacy
https://www.ghacks.net/2015/08/18/a-comprehensive-list-of-firefox-privacy-and-security-settings/
http://kb.mozillazine.org/About:config_Entries
http://anonymous-proxy-servers.net/en/jondofox.html
https://developer.mozilla.org/en-US/docs/Web/API/IndexedDB_API/Browser_storage_limits_and_eviction_criteria
https://browserleaks.com/webrtc
https://www.ghostery.com/blog/ghostery-news/cookies-fingerprinting-co-tracking-methods-clearly-explained/
https://en.wikipedia.org/wiki/Cross-site_scripting
https://www.mycryptopedia.com/crypto-mining-scripts/
https://www.mike-gualtieri.com/css-exfil-vulnerability-tester
https://www.bleepingcomputer.com/news/security/css-is-so-overpowered-it-can-deanonymize-facebook-users/
https://developer.mozilla.org/en-US/docs/Web/API/Web_Storage_API
https://www.theguardian.com/us-news/edward-snowden
https://www.theatlantic.com/technology/archive/2017/03/encryption-wont-stop-your-internet-provider-from-spying-on-you/521208/
https://wordpress.org/plugins/evercookie/
https://filterlists.com/
https://www.techspot.com/guides/44-firefox2-tweak-guide/page16.html
https://www.ghacks.net/2015/03/27/firefox-39-tracking-protection-for-private-browsing-mode/
https://www.mozilla.org/en-US/privacy/firefox/
https://wordpress.org/plugins/evercookie/
https://filterlists.com/
https://www.ghacks.net/2015/03/27/firefox-39-tracking-protection-for-private-browsing-mode/
https://support.mozilla.org/en-US/questions/1097368
https://www.mozilla.org/en-US/privacy/firefox/
https://github.com/pyllyukko/user.js/tree/master
https://blog.mozilla.org/metrics/2012/09/21/firefox-health-report/
https://wiki.archlinux.org/index.php/Firefox/Privacy
https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/User-Agent/Firefox
https://www.ghacks.net/2007/05/04/flash-cookies-explained/
https://www.google.com/intl/en/chrome/privacy/
https://www.ghacks.net/2014/06/02/block-automatic-connections-firefox-makes/
https://support.mozilla.org/en-US/questions/980227
https://tor.stackexchange.com/questions/4336/how-to-import-tor-browser-profile
https://www.ghacks.net/2015/10/16/how-to-prevent-hsts-tracking-in-firefox/
https://support.mozilla.org/en-US/kb/how-stop-firefox-making-automatic-connections
https://www.cookiebot.com/en/website-tracking/
https://www.sitepoint.com/html5-browser-storage-past-present-future/
https://www.ghacks.net/2015/01/22/improve-online-privacy-by-controlling-referrer-information/
https://archive.vn/99sDW
https://www.lexology.com/library/detail.aspx?g=34ef3aca-bc16-425b-842a-e39ebea0d030
https://ip-check.info/?lang=en
https://ip-check.info/description.php
https://ipleak.net/
https://heimdalsecurity.com/blog/javascript-malware-explained/
https://en.wikipedia.org/wiki/List_of_HTTP_header_fields
https://en.wikipedia.org/wiki/Man-in-the-middle_attack
https://resources.infosecinstitute.com/means-and-methods-of-web-tracking-its-
effects-on-privacy-and-ways-to-avoid-getting-tracked/
https://blog.mozilla.org/blog/2014/10/16/mozilla-and-telefonica-partner-to-simplify-voice-and-video-calls-on-the-web/
https://developer.mozilla.org/en-US/docs/Mozilla/Preferences/Mozilla_networking_preferences
https://www.theregister.co.uk/2014/11/12/mozilla_google_financing/
https://www.google.com/intl/en/chrome/privacy/
https://micro.nicholaswilson.me.uk/post/65681505329/mozilla-vs-google-on-user-privacy-websockets
https://wiki.mozilla.org/Privacy/Reviews/Necko
https://developer.mozilla.org/en-US/docs/Web/API/Network_Information_API
https://andreasgal.com/2014/10/14/openh264-now-in-firefox/
https://wiki.archlinux.org/index.php/Profile-sync-daemon
https://support.mozilla.org/en-US/kb/profiles-where-firefox-stores-user-data
https://blog.mozilla.org/nnethercote/2014/11/12/quantifying-the-effects-of-firefoxs-tracking-protection/
https://en.wikipedia.org/wiki/SPDY
https://tails.boum.org/
https://www.vice.com/en_us/article/gv5jwj/the-fbi-is-classifying-its-tor-browser-exploit
https://www.mozilla.org/en-US/about/manifesto/
https://medium.com/@optimiseordie/the-ultimate-guide-to-using-google-analytics-for-
cross-device-optimisation-e56636b54618#.2y91ctpwy
https://css-tricks.com/potential-dangers-of-third-party-javascript/
https://www.torproject.org/download/
https://support.mozilla.org/en-US/kb/what-happened-tracking-protection?
redirectlocale=en-US&redirectslug=tracking-protection
https://github.com/uBlock-LLC/uBlock/wiki
https://www.howtogeek.com/180175/warning-your-browser-extensions-are-spying-on-you/
https://en.wikipedia.org/wiki/Web_storage
https://www.makeuseof.com/tag/what-are-supercookies-and-why-are-they-dangerous/
https://www.ctrl.blog/entry/firefox-fpi.html
https://archive.is/20180823134103/
https://wholeftopenthecookiejar.eu/static/tpc-paper.pdf
https://restoreprivacy.com/browser-fingerprinting/
https://restoreprivacy.com/
https://restoreprivacy.com/firefox-privacy/
https://restoreprivacy.com/antivirus-privacy/
https://restoreprivacy.com/cyber-security-statistics/
https://restoreprivacy.com/vpn-vs-tor/
https://restoreprivacy.com/contact/ Secure email: Tutanota or ProtonMail, https://tutanota.com/, https://restoreprivacy.com/go/protonmail
https://restoreprivacy.com/contact/ Secure Messenger: Wire or Signal, https://wire.com/, https://signal.org/
Some Articles in German language for the discussion of /etc/hosts:
Block google-fonts and ads through /etc/hosts
Das Nachladen externer Schriften durch eine Webseite ist meist überflüssig, kostet Performance und kann potenziell ein Tracking-Problem darstellen.
http://netz10.de/2014/02/10/googles-schriften-blockieren
In diesem Gastartikel, möchte ich dir eine wirklich sehr simple Möglichkeit nahebringen, Werbung im Internet effektiv zu blockieren.
Werbung blockieren mit Bordmitteln
Wie du sicherlich weißt, gibt es zahlreiche Plugins für die verschiedensten Browser, mit dessen Hilfe man unerwünschte Werbung aus Webseiten herausfiltern kann. Was viele Menschen nicht wissen: Es geht jedoch auch noch einfacher und zwar ganz ohne den Einsatz von Zusatzsoftware. Der Vorteil der von mir vorgestellten Methode ist, dass nicht nur die Werbung beim Surfen mit dem Browser blockiert wird, sondern die gesamte Werbeauslieferung zu deinem System. Das heißt, dass so auch die Werbung im Emailclient oder im Messagingprogramm keine Chance mehr hat.
In jedem Windowssystem existiert im Ordner c:windowssystem32driveretc eine Datei namens "hosts". Falls du mit dem freien Betriebssystem Linux arbeitest, so ist diese Datei im Verzeichnis /etc/ zu finden. Die Systax ist analog zur Windowsvariante. Mit Hilfe dieser Datei, kann man einem beliebigen Hostnamen eine "feste" IP zuweisen. Der Name wird zukünftig nicht mehr per DNS aufgelöst.
Zur Erklärung für die Nicht-TI-ler: Wenn man einen Adresse im Browser eingibt, so wird zuerst in der hosts-Datei nachgeschaut, ob die Zieladresse bereits bekannt ist. Falls die Adresse nicht bekannt ist, wird der DNS-Server (Nameserver des Providers) gefragt. Dieser liefert dann die zur Adresse gehörige IP-Adresse zurück und dein Rechner kann Kontakt zum Zielcomputer aufnehmen.
[...] Eine Liste mit Adressen bekannter Werbeanbieter, die gesperrt werden können, findest du hier:
http://www.mvps.org/winhelp2002/hosts.txt
Du musst sie nur noch in deine hosts-Datei einfügen.
[...] Die Auslieferung an den Browser ist hier nur beispielsweise genannt, analog werden natürlich auch Anfragen vom Emailclient oder Messagingprogramm behandelt und entsprechend umgeleitet. Zusätzlich zum Blockieren von Werbung kannst du dieses Vorgehen auch nutzen um diverse Programme vom "Nach-Hause-Telefonieren" abzuhalten, wie es viele Produkte von Microsoft oder google gerne machen.
http://www.plerzelwupp.de/werbung-effektiv-blocken-ohne-zusatzsoftware/
WordPress-Plug-in Popup Builder
Attackers use the popular webside-configuraiton Wordpress. Several updates are necessary, in order to keep the user secure, trojaner-info.de, 10.02.2021
Admins, die auf ihren WordPress-Websites das Plug-in Popup Builder einsetzen, sollten es zeitnah auf den aktuellen Stand bringen. Ansonsten könnten Angreifer Seiten attackieren und beispielsweise Newsletter mit Links zu Malware verschicken oder Seiten-Abonnenten löschen.
https://www.trojaner-info.de/business-security/aktuell/wordpress-plug-in-popup-builder-8177.html
WordPress: Block spam-IP per .htaccess,perun.net (in german lang.)
So alle 3-4 Wochen gibt es einen Scherzkeks der witzig findet eine kleine Spam-Attacke auf dieses Blog zu starten. Neulich war es jemand aus China und ...
http://www.perun.net/2012/03/05/wordpress-spam-ip-per-htaccess-sperren/
Linux: Block IP-addresses by hosts.allow and hosts.deny (in german lang.), 15.11.2016
Sollen bestimmte IP-Adressen oder Netzbereiche für den Zugriff auf einen Server gesperrt werden, so gibt es mehrere Möglichkeiten:
iptables ist eine komplexe Firewall
über die .htaccess IPs für den Zugriff auf den Webserver sperren
über die Dateien /etc/hosts.allow und /etc/hosts.deny IPs für einige Dienste sperren
In diesem Beitrag spreche ich die letztgenannte Möglichkeit an
Als erstes sollte der localhost in /etc/hosts.allow eingetragen werden, damit der sich nicht selbst aussperren kann:
ALL: 127.0.0.1,localhost
Hier gehören zusätzlich weitere IPs/Full Qualified Domain Names hinein, die immer Zugriff erhalten sollen.
Folgende Einträge sind in der /etc/hosts.deny möglich und dienen zum Sperren von IP-Adressen oder Netzbereichen:
# IP 1.2.3.4 komplett sperren:
ALL: 1.2.3.4
# Alle Adressen im Netz 4.5.6.x sperren (Netzmaske 4.5.6.0/24)
# Jede der Zeilen ist eine mögliche Eingabeform und bewirken das gleiche:
ALL: 4.5.6.
ALL: 4.5.6.0/24
ALL: 4.5.6.0/255.255.255.0
Es besteht die Möglichkeit die Sperren einzuschränken - in diesen Beispielen sperre ich alles aus (erkennbar am ALL). Für Details siehe man-Page zu hosts.deny.
Seien Sie aber vorsichtig: Sie können sich versehentlich selbst aussperren! Schalten Sie daher Ihre eigene IP vorher in /etc/hosts.allow frei.
https://www.it-muecke.de/node/20161115-hosts-allow-und-deny
Konqueror since 3.x.x: Features
based on Qt3, Qt4 and C++
Powerful and flexible file manager
Standard compliant: Qt-browser-widget and therefore browser-engine: KHTML
SSL 2.0 / 3.0 and TLS 1.0 with SHA1 and the secure SHA2
SSL vs. TLS vs STARTTLS | Blog | Limilabs
http://www.limilabs.com/blog/ssl-vs-tls-vs-starttls-stls
tls stands for Transport Layer Security and the current version is 1.2. tls is the successor to ssl.Despite having tls in the name, STARTtls doesn´t mean tls will be used. Both ssl and tls are acceptable protocols for securing the communication.
Embedded viewing of files thanks to KParts
Multiple split views and tabs
Sidebars and extensions to provide additional functionality
Integration with other KDE applications like KGet Download Manager and Akregator Feed Reader
Remote and pseudo-filesystem file management through KIO
Deactivate the browser-chronik resp. -history if possible or take care of its automatic deletion each time..
Bootloader of our FSE-system: grub (rosa2014.1, el6, mdv2010.2)
Konqueror 4.4.5 working upon openssl seems to manage everything and very secure to become our favorite browser (although still crashing from time to time, if at least belonging rpm JavaScript js for mdv2010.2 is not installed. Konqueror by our short study about him is not crashing except on Facebook, never, if JavaScript is disabled) and file-manager past Dolphin, prejunction: the cache-size of the konqueror should be set to at least 50256 KB by configuration. In order to avoid certificate-requests, ca-certificates (rpm) helps to automize them.
On our website for News&Links we describe, how konqueor gets upgraded, below, how updated. We do not recommend the upgrade very much, because kde-library baseapps has to be upgraded completely too.
[ SOLVED by Gooken ]: Certifcates have to be confirmed each website-build-up, even if already confirmed.
Change to certs by cd /etc/pki/tls/certs and exchange the onto nothing linking or empty file ca-bundle.crt with its backup like ca-bundle.crt.rpmnew within the same directory certs: cp -fp ca-bundle.crt.rpmnew ca-bundle.crt.
Adjust settings for Adobe Flash Player in systemsettings or gnome-control-center to reach more security. The best you can do is to deactivate Adobe in the browser or to resign from it.
Before the tarball for the driver is installed, a config file is checking out the system-environment to produce a MAKEFILE to compile with the command make. In order to install the three essential patches and the patch against Shellshock for the bash, for mdv2010 we installed the following packages from rpmfind.net: bash-4.1.2-33.el6.x86_64.rpm with adequate bash-completion, bash-doc, dialog, ncurses, ncurses-base and ncurses-libs of el6 that means ALT Linux resp. CentOS 6.7 resp. 7.
el6 stands especially for CentOS, but also Repoforge (RPMforge), Scientific Linux, ALT Linux, ATrpms Testing, NauLinux School, PN Testing and other rpm-distributions.
Update-guarantee: until year 2026
Update-sources:
http://fr2.rpmfind.net (FTP-downloads, here for el6, el7, fc, mdv and mga) and http//pkgs.org (http-downloads for el6, el7, fc down to fc xx, mga down to mga xx), http://rpm.pbone.net/ (http- and ftp-downloads, el6, el7, all popular distributions and versions
Update-sources: http://fr2.rpmfind.net (ftp-downloads, el6, el7, fc, mdv and mga) and http//pkgs.org (http-downloads für el6, el7, fc down to fc xx, mga down to mga xx), http://rpm.pbone.net/ (http- and ftp-downloads, el6, el7, alle bekannten Distributionen and Versionen)
Updates (el6.7, el7, rosa2014.1): http://rpm.pbone.net/index.php3/stat/14/idka/262900/datan/2015-10-11
Updates (el6.7, el7) (2), actual; newest updates are marked yellow with "new" each week or each second week: http://fr2.rpmfind.net/linux/RPM/CentOS/updates/6.7/x86_64/Unknown.html
actual updates of the last three month, el6.7 (3): ftp://ftp.scientificlinux.org/linux/scientific/6rolling/x86_64/updates/security/
Packets (and almost with tarballs through links): http://fr2.rpmfind.net
https://security.gentoo.org/glsa/ (Gentoo), 20.09.2015, https://infra-status.gentoo.org/:
"Web Services Maintenance
The following web services are currently unavailable:
security.gentoo.org (GLSA)
piwik.gentoo.org (this will cause other gentoo websites to exhibit a ´never stops loading´behavior)
overlays.gentoo.org
We expect the services to return shortly."
http://www.pro-linux.de/sicherheit/1/1/1.html (CentOS el6, CentOS el7); notice all updates of different distributions listed there almost refer to any distribution (each)! el6 and el7 from pkgs.org offer most of such updates.
nss, lib64nss: The Mozilla Network Security Service (NSS) is a library implementing security features like SSL v2/v3, TLS, PKCS #5, PKCS #7, PKCS #11, PKCS #12, S/MIME and X.509 certificates.
SSL and TLS by openssl: http://openssl.org (which is used by browsers like Konqueror), actual version: openssl-1.0.2d. This version leaves Heartbleed and six more errors for mdv2010 behind.
TLS and SSL by gnutls (3.4.3) and nettle (3.1.1): Their Programmers would not have such experience to improve the mess of its code, meant the opensource developer Howard Chu on Twitter, althoguh now, with version 3.4.3 this might has happened.
Packets for OpenSSL instead of Tarball: openssl (el7), openssl-libs (el7), openssl-perl (el6), perl-Crypt-OpenSSL-random (el6), perl-Crypt-OpenSSL-RSA (el6) and pyOpenSSL (el6)
Packets for gnutls i.e.: gnutls (el7), gnutls-c++ (el7), gnutls-dane (el7), gnutls-utils (el7), ldns (el6), libtasn1 (el7), libtasn1-tools (el7), nettle (el7), p11-kit (el7), p11-kit-trust (el7), trousers (el6), unbound-libs (el6), xmlsec1 (el6), xmlsec1-gcrypt (el6) and xmlsec1-gnutls (el6)
mbedtls (el7, el6): Light-weight cryptographic and SSL/TLS library
SHA2, secure: tls and sha2 and not SSLv3 and/or sha1: sha2-1.0.1-1.el6.nux.x86_64 (el6) and perl-Digest-SHA2-1.1.1-1.el6.rf.x86_64 (el6)
ca-certificates, p11kit, p11kit-trust, celtx CentOS6.7 (el6) instead of weak equipped root-certificates from fr2.rpmfind.net for mdv2010: let your browser (Konqueror) know at least the certification handling organisations for the authorizations of serversided exposed SSL-certificates (cost: free up to several thousand us-dollars the year the certificate), so that manual confirmations of problematic certificates by the surfer right before the built-up of ssl-connections become more automized and therefore unnecessary. Problematic certificates can result in unknown certification organization, certificates expiring dates and their incorrect exposed data like different names for the refered website. Now, you do not have to annoy by always having to click "OK", in ordert to accept such problematic certificates offered by webservers over webservers..
Manpages and xz, the successor of lzma-compression, needed for the newest, five times more seized manpages in diffferent languages like for mga5: Get xz from http://tukaani.org/xz/ (Tarball) or fr2.rpmfind.net (rpm). Adopt the compression in /etc/man.config by writing (resp. modifying to ) the two lines " .lzma /usr/bin/xz --format=alone --decompress --stdout" and ".xz --format=xz --decompress --stdout" . xz still might not work or work incorrectly. In this case reinstall the rpm xz for the installed distribution, in our case mdv2010, type "rpm -i --force xz-version-release-update.rpm". Now actual (and therefore the many new) man-pages can always been read by the command "man any-command", even those actual ones in different languages by manpages for mageia5, mga5
Anonymizing Proxies: tor (el6), torsocks (el6), JAP (el6)
XAMPP/LAMP: all-in-one out of the internet instead single rpm for the distribution consisting of webserver Apache, FTP-Server proftpd and MySQL
Firefox about:
about:addons
about:blank
about:blocked
about:certerror
about:config
about:crashes
about:feeds
about:home
about:memory
about:neterror
about:newtab
about:plugins
about:pocket-saved
about:pocket-signup
about:preferences
about:privatebrowsing
about:sessionrestore
about:srcdoc
about:support
about:tabcrashed
... Es gibt aber auch Einträge, die man über das Menü nicht findet. Wer mehr über Abstürze wissen will, kann sich in "about:crashes" die Absturzberichte reinziehen, "about:telemetry" informiert über Browser-Hänger und verzögerte Schreibvorgänge. Über "about:memory" können Sie Details zur Speicherbelegung einsehen und über einen kleinen Schalter bei "Free memory" sogar die Speichernutzung minimieren. Hinter "about:performance" verbirgt sich übrigens der Firefox-eigene Task-Manager und "about:profiles" informiert über verschiedene Firefox-Profile auf dem Rechner.
https://www.chip.de/news/Firefox-Diese-Features-kennen-Sie-noch-nicht_93266205.html
Chromium, for all people, who do not like Konqueror and Firefox: GLSA >= 44357.130, Tarball from
http://code.google.com/p/chromium/downloads/list?
can=1&q=&colspec=Filename+Summary+Uploaded+ReleaseDate+Size+DownloadCount
 Firefox - The Fox hole Firefox - The Fox hole
Even with everything we´ve done, you´re still vulnerable to being tracked and profiled, however you´re in a better position now then when you started out, except for one little problem: Your Internet Service Provider!
At the very least your ISP can see what websites you visit, when you´re surfing the web and when you´re not. They may even inject ads, malware or other garbage in your data stream. The solution: Hijack your neighbors unprotected WiFi and... Kidding!
https://12bytes.org/articles/tech/firefox/the-firefox-privacy-guide-for-dummies
 What you can do against this: try VPN and/or TOR. We talk about both soon, later on in our excurs! What you can do against this: try VPN and/or TOR. We talk about both soon, later on in our excurs!
 Encryption won´t stop your internet provider from spying on you, The Atlantic Encryption won´t stop your internet provider from spying on you, The Atlantic
Data patterns alone can be enough to give away what video you´re watching on YouTube.
https://www.theatlantic.com/technology/archive/2017/03/encryption-wont-stop-your-internet-provider-from-spying-on-you/521208/
Survey
36 millionen euro: ZITiS builds supercomputer for encryption, netzpolitik.org, 16.10.2018
https://netzpolitik.org/2018/36-millionen-euro-zitis-baut-supercomputer-zur-entschluesselung/
Back to the main text of our excurs:
Games, see data sheed: From more than 500 Games of mdv2010, only the starter-file-package of openarena named openarena needs to be downgraded, if the x-server of mdv2010.0 is still running on mdv2010.2. Otherwise, the game does not close the menu after playing. smc, SuperMario-chronicles does run fine, but the tray-applet xrandr_tray is needed to set the old screen resolution after playing Megamario Only Vegastrike did not run (in this casis, you almost have to change the starter file too).
If a game does not have a screen, change from fullscreen to windows mode or choose another screen resolution (our computer with IGP from Intel: 1366×768, 1366×704, 1280×720... ). Please notice, that marsshooter (mdv2010.2) does not start each call from terminal, so try marsshooter (rosa2014.1).
Gentoo-GLSA (actual rpm security list): Therefore, glibc from at least mdv2012 has to be installed for mdv2010 as described above. But not all updates from actual fedora do function as it did for mdv2010 right before, so do not update in some cases like grub > mdv2012, util-linux (es genügt 2.19), ghostscript, perl, e2fsprogs (1.43.2), bash (von el6), pango, lib64cairo, Paketmanager von drakrpm and so on. Alternatively use Tarballs offered by different websites or the well updated rpm especially for ALT Linux resp. CentOS el6. We repeat, that one has to be a little bit careful with the installations of actual packages from fedora sometimes.
The GNU C library (glibc) itself should always be kept secure by updates too. PCWelt still reported about the necessarity of updating glibc in 02.18.2016, see News&Links#computer.
An update for GNU C (rosa2014.1) is possible from http://mirror.rosalab.ru/rosa/rosa2014.1/repository/x86_64/main/updates/ .
After those updates, some programs like miro and gftp do not function anymore. To avoid this, we finally recommend to update with glibc (el8, rosa2014.1) and all other glibc-rpm (el8, el6): compat-glibc (el6 without further measures past this installation), glibc-common (el8, el6), glibc-utils (el8, el6), glibc-static (el6), glibc-headers (el8, el6), glibc-all-langpacks (el8), glib2 (el6) and glib2-static (el6).
In order to avoid error-messages of glibc (el8) during system-boot, just remove the line LC_TIME=de_DE.UTF-8 in /etc/sysconfig/i18n ! Eventually install locales (pclos, mga7, mga6), locales-en, locales-de, ... too.
Actual updates for mdv like 2010 were found and some of them are listed by the Gentoo GLSA. mdv-updates themselves last for about two years since the date of appearance of the mdv-distribution, before those from el6 become mandatory. Notice, that with a firewall like Linfw3 you do not really need most resp. all of the following updates except browser and SSL/TLS, but to go sure, it is better to install them quit all.
https://security.gentoo.org/glsa/, Gentoo.org, 09.20.2015, https://infra-status.gentoo.org/:
"Web Services Maintenance
The following web services are currently unavailable:
security.gentoo.org (GLSA)
piwik.gentoo.org (this will cause other gentoo websites to exhibit a ´never stops loading´behavior)
overlays.gentoo.org
We expect the services to return shortly."
Remove (rpm -e): tracker, codeina, xguest, billreminder
For the very first time using cups eventually restart the computer-system twice. Then the printer is almost working fine.
KDE (and therefore MySQL, akonadi, nepmomuk and ilmbase too): KDE 4.10 (el7 or el6) or KDE 4.14 (rosa2014.1). KDE 4.14 is named for this matter by packages named mandriva, but requires haldaemon hal (rosa2014.1) and lob64hal (rosa2014.1) ... or just keep 4.4.5 from mdv2010.2, what we like to recommend; changelog of kdelibs (el6):
2015-03-25 - Lukas Tinkl <ltinkl@redhat.com> - 6:4.3.4-23
- Resolves: rhbz#1206181 - The kate editor does not retain
printing preferences
2015-03-25 - Lukas Tinkl <ltinkl@redhat.com> - 6:4.3.4-22
- Resolves rhbz#1206180 - Opening a terminal in Konqueror / Dolphin does
not
inherit environment variables
2014-07-02 - Daniel Vrátil <dvratil@redhat.com> - 6:4.3.4-21
- Resolves bz#1025417, wallpaper not applied on second screen when on
dualhead
2013-06-10 - Than Ngo <than@redhat.com> - 6:4.3.4-20
- Resolves: bz#882895, crash when switching activity of 2 desktops from
activity applet
2012-10-18 - Than Ngo <than@redhat.com> - 6:4.3.4-19
- fix multilib conflict
2012-10-17 - Than Ngo <than@redhat.com> - 6:4.3.4-18
- Resolves: bz#866230, CVE-2012-4512 CVE-2012-4513
2012-09-07 - Than Ngo <than@redhat.com> - 4.3.4-17
- Resolves: bz#754161, bz#587016, bz#682611, bz#734734, bz#826114, respin
2012-08-28 - Than Ngo <than@redhat.com> - 6:4.3.4-16
- Resolves: bz#754161, stop/warn when a subdir is not accessible when
copying
2012-08-22 - Than Ngo <than@redhat.com> - 6:4.3.4-15
- Resolves: bz#587016, print dialogue does not remember previous settings
- Resolves: bz#682611, Konqueror splash page in zh_TW is wrong
- Resolves: bz#734734, plasma eating up cpu-time when systemtray some icon
- Resolves: bz#826114, konqueror crash when trying to add Terminal
Emulator" to main menu bar
2012-02-02 - Than Ngo <than@redhat.com> - 6:4.3.4-14
- Resolves: bz#698286, big endian issue on s390(x)
Unsolved serious hard KDE errors: reinstall KDE-packages. We had this seldom case for having installed gamin (el6), although gamin (mdv2010.2) does its work only.
Get rescued forever, update Linux most popular browser and file manager Konqueror:
Update: Konqueror
 Konqueror is patched in main up to date now, although he got downgraded from 4.4.5 (mdv2010.2) to 4.4.4 (OpenSuSE) or 4.3.4 (el6). Nevertheless, new set links within /usr/lib64 can be relinked back onto their old konqueror-files. This can be recognized for example, if you click on the bookmarks of this browser´s menu bar. In order to prevent this, overwrite the old with the new files within this directiory (/usr/lib64) by just using the command "cp -f new_file old_file".
Konqueror is patched in main up to date now, although he got downgraded from 4.4.5 (mdv2010.2) to 4.4.4 (OpenSuSE) or 4.3.4 (el6). Nevertheless, new set links within /usr/lib64 can be relinked back onto their old konqueror-files. This can be recognized for example, if you click on the bookmarks of this browser´s menu bar. In order to prevent this, overwrite the old with the new files within this directiory (/usr/lib64) by just using the command "cp -f new_file old_file".
If KDE won´t start, use another windows manager like LXDE, in order to reinstall KDE-packages.
alternatively by "yum install konqueror", (source: http://konqueror.org/download/)
Python and Perl (el6): see our update-list (universal-linux.php this server)
Kernel: kernel-headers (el6) and kernel-firmware (el6 from year 2015, you can install both rpm for the previous mdv2012-kernel too), coreutils (el6), coreutils-libs (el6), binutils (el6), nss-softokn (el6) and nss-softokn-freebl (el6)
To go sure that at least one kernel still does the booting-up of the whole system, add one more belonging new item to this kernel into the configuration file of grub (/boot/grub/menu.lst), grubby or grub2.
Firmware: kernel-firmware (el6), kernel-firmware-extra (rosa2014.1, mdv2010.2, all kernel), alsa-firmware (el6), alsa-tools-firmware (el6), broadcom (broadcom wireless devices), madwifi (wireless LAN), iscan-firmware (el6, Espon flatbed scanner), aic94xx-firmware (el6, Adaptec Sequencer resp. Aic94xx SAS/SATA-Treiber), atmel-firmware (el6, ATMEL wireless network chip), bfa-firmware (el6, Brocade Fibre Channel HBA Firmware), iwlxxx-firmware (el6), crystalhd-firmware (el6, Broadcom Crystal HD video decoder), libcrystalhd (el6), ipw2100-firmware (el6), radeon-firmware (AMD/ATI graphic cards), ralink-firmware (rosa2014.1), ivtv-firmware (el6, Hauppauge PVR cards), iwl-firmware (el6I, ntel® PRO/Wireless 3945 A/B/G network adaptors), rt-xxx (Realtek, el6), rtlwifi-firmware (el6), kmod-iwlwifi-dup (el6), kmod...
 More firmware:kernel-firmware-extra (pclos.1, rosa2014.1+OpenSuSE13.2+OpenSuSE42.2), linux-firmware (fc27, rosa2014.1), aica-firmware (pclos), asihpi-firmware (pclos), atmel-firmware (pclos), b43-firmware (pclos), alsa-firmware (el6), alsa-tools-firmware (el6), bcm43xx-firmware (pclos), bcm2033-firmware (pclos), bluez-firmare (pclos), bluez-firmware-broadcom (pclos), cs46xx-firmware (pclos), ctefx-firmware (pclos), ctspeg-firmware (pclos), emagic-firmware (pclos), broadcom (kabellose Geräte von Broadcom), emu1010-firmware (pclos), ipw2100-firmware (pclos), ipw2200-firmware (pclos), korg1212-firmware (pclos), maestro3-firmware (pclos), marvel-firmware (pclos), nouveau-firmware (pclos), nvidia-firmware-installer (pclos), pcmcia-cis-firmware (pclos), prism54-firmware (pclos), rt61-firmware (pclos), rt73-firmware (pclos), rtl-sdr (pclos), rtl8192se-firmware (pclos), sb16-firmware (pclos), sb16_csp (pclos), speedtouch-firmware (pclos), turtlebeach-firmware (pclos), ueagle-firmware (pclos), yamaha-firmware (pclos), zd1201-firmware (pclos), zd1211-firmware (pclos), madwifi (wireless LAN), iscan-firmware (el6, Espon flatbed scanner), aic94xx-firmware (el6, Adaptec Sequencer bzw. Aic94xx SAS/SATA-Treiber), atmel-firmware (el6, ATMEL kabelloser Netzwerkchip), bfa-firmware (el6, Brocade Fibre Channel HBA Firmware), iwlxxx-firmware (el6), crystalhd-firmware (el6, Broadcom Crystal HD video decoder), libcrystalhd (el6), radeon-firmware (rosa2014.1, ATI/AMD Radeon Graphikkarten), ipw2100-firmware (el6), ivtv-firmware (el6, Hauppauge PVR cards), iwl-firmware (el6, Intel® PRO/Wireless 3945 A/B/G Netzwerkadapter), ralink-firmware, rt-xxx (Realtek, el6), rtlwifi-firmware (el6), kmod-iwlwifi-dup (el6), kmod..., ALL KIND of FIRMWARE by many additional packages, libminiupnpc (OpenSuSE 13.2, mdv2011, Library and tool to control NAT in UPnP-enabled routers / The MiniUPnP project offers software which supports the UPnP Internet Gateway
Device (IGD) specifications.) More firmware:kernel-firmware-extra (pclos.1, rosa2014.1+OpenSuSE13.2+OpenSuSE42.2), linux-firmware (fc27, rosa2014.1), aica-firmware (pclos), asihpi-firmware (pclos), atmel-firmware (pclos), b43-firmware (pclos), alsa-firmware (el6), alsa-tools-firmware (el6), bcm43xx-firmware (pclos), bcm2033-firmware (pclos), bluez-firmare (pclos), bluez-firmware-broadcom (pclos), cs46xx-firmware (pclos), ctefx-firmware (pclos), ctspeg-firmware (pclos), emagic-firmware (pclos), broadcom (kabellose Geräte von Broadcom), emu1010-firmware (pclos), ipw2100-firmware (pclos), ipw2200-firmware (pclos), korg1212-firmware (pclos), maestro3-firmware (pclos), marvel-firmware (pclos), nouveau-firmware (pclos), nvidia-firmware-installer (pclos), pcmcia-cis-firmware (pclos), prism54-firmware (pclos), rt61-firmware (pclos), rt73-firmware (pclos), rtl-sdr (pclos), rtl8192se-firmware (pclos), sb16-firmware (pclos), sb16_csp (pclos), speedtouch-firmware (pclos), turtlebeach-firmware (pclos), ueagle-firmware (pclos), yamaha-firmware (pclos), zd1201-firmware (pclos), zd1211-firmware (pclos), madwifi (wireless LAN), iscan-firmware (el6, Espon flatbed scanner), aic94xx-firmware (el6, Adaptec Sequencer bzw. Aic94xx SAS/SATA-Treiber), atmel-firmware (el6, ATMEL kabelloser Netzwerkchip), bfa-firmware (el6, Brocade Fibre Channel HBA Firmware), iwlxxx-firmware (el6), crystalhd-firmware (el6, Broadcom Crystal HD video decoder), libcrystalhd (el6), radeon-firmware (rosa2014.1, ATI/AMD Radeon Graphikkarten), ipw2100-firmware (el6), ivtv-firmware (el6, Hauppauge PVR cards), iwl-firmware (el6, Intel® PRO/Wireless 3945 A/B/G Netzwerkadapter), ralink-firmware, rt-xxx (Realtek, el6), rtlwifi-firmware (el6), kmod-iwlwifi-dup (el6), kmod..., ALL KIND of FIRMWARE by many additional packages, libminiupnpc (OpenSuSE 13.2, mdv2011, Library and tool to control NAT in UPnP-enabled routers / The MiniUPnP project offers software which supports the UPnP Internet Gateway
Device (IGD) specifications.)
We try to list security updates from pro-linux.de, the update list for CentOS el6 und el7 from fr2.rpmfind.net and pkgs.org year 2010 up to year 2026, update list for Rosa2014.1 and Rosa2012.1 (http://mirror.rosalab.ru/rosa/rosa2014.1/repository/x86_64/main/updates/), pbone.net (u.a. http://rpm.pbone.net/index.php3/stat/14/idka/262900/datan/2015-10-11), pro-linux.de (http://www.pro-linux.de/sicherheit/1/1/1.html) and Gentoo GLSA (https://security.gentoo.org/glsa/) and more security updates for mdv2010 (el6), omv2013 up to omv2015 (pkgs.org), mga1 up to mga5 (fr2.rpmfind.net), fc18 up to fc24 (pkgs.org and fr2.rpmfind.net) and so on:
actualization list with packages from CentOS 6, CentOS 7 and Rosa 2014.1
... that might be all, date: 04.02.2016. Packages are keeping the system up to date. Only a few of them belong to the security updates. For more acutalizations, have a look into the package-manager of MCC and decide it by yourself. Notice, that most, but not all packages can be actualized.
Past all those actualizations up to now installed, you just need to follow the list of most actual update-rpm from rpmfind for CentOS 6 and http://www.pro-linux.de/sicherheit/1/1/1.html up from that rpm, where our listing ends. All you got is a "Universal-Linux" patched from 2010 up to 2026 by fixed versions, that are updated and patched just in their releases. This is the best criteria for security, you can imagine! Except OpenSSL, gnutls and Firefox, CentOS 6 seems to be patched ready past its six year, while new released versions of distribution do only prolong this matter again. After year 2016, at last 2026, we dare to say, that not any updates and patches become necessary anymore - only spinner do believe, that past 2026 updates will really update.,
"Februray, 15. 2016 Offering of informationen in libgcrypt", source: pro-linux.de. You see: Regardless from openssl or gnutls and so on, a patch was provided late, much too late!
dmesg does not show any errors now! If there are some loops during system-shutdown that almost do not really matter, complete or modify belonging packages or downgrade them again (so do not despair). Loops might indicate, that a daemon/service fails to start. Programs are named solving such loops automatically.
rpm libbsd: "libbsd provides useful functions commonly found on BSD systems and lacking on others like GNU systems, thus making it easier to port projects with strong BSD origins, without needing to embed the same code over and over again on each project."
"Ragel (el7, Russian Fedora) compiles finite state machines from regular languages into executable C, C++, Objective-C, or D code. Ragel state machines can not only recognize byte sequences as regular expression machines do, but can also execute code at arbitrary points in the recognition of a regular language. Code embedding is done using inline operators that do not disrupt the regular language syntax", pkgs.org
Forensics, forensic-tools (el6): look for Forensics in our data-sheed.
Stormbaancoureur: This 3D-game should be started with option -indirect on graphical errors.
If the icon of klipper should be not shown in the system-tray, what happened to us for one time only, just reinstall qt (Qt4, el6). Klipper (rosa2014.1) still running upon the old libraries (mdv2010) can also be taken instead of klipper (mdv2010.2).
Games: SDL-games and many other ones (rosa2014.1), for our TFT see data-sheed in screen-resolution: 4096×1096, ..., 1366×768 (auto), 1366×704, 1360×704, 1280×720, ...
Loudseaker test: speaker-test
Office: beneath calligra (mdv2011): koffice (mdv2010.2 to keep out of kword (text processing), kspread (spreadsheets), kcharts (integrated charts), kformula (mathematics formula), kplato (project management, that can generate Grantt-style charts), kpresenter (presentation), kugar (report generator), krita (digital painting and image processing), karbon (vector drawing), kivio (flow charts), kexi (local databasis)), but also libreoffice (el6, el7, rosa2014.1, mdv2010.2) and openoffice (rosa2014.1, mdv2010.2 running fine or actual version from openoffice.org, again with text processing, spreadsheets, database, presentation, drawing, formulas and many submittals... )
Nepomuk: if KDE-4.4.5 (mdv2010.2) is kept, following packages for nepomuk can be updated: lib64nepomukcore4 (rosa2014.1), lib64nepomukutils (rosa2014.1), lib64nepomukwidgets (rosa2014.1), lib64smokebase3 (rosa2014.1, installation by rpm -i --force --nodeps), lib64smokenepomuk3 (rosa2014.1) und lib64smokenepomukquery3 (rosa2014.1), who wants, shared-desktop-ontologies too, but not lib64nepomuk4 (rosa2014.1).
Now it´s time to make a backup of akonadi through akonaditray.
Listing containing this by an extraction only showing even the newest updates marked by "new": http://fr2.rpmfind.net/linux/RPM/CentOS/updates/6.7/x86_64/Unknown.html
SDL2: the successor of SDL1 can be downloaded from http://libsdl.org (two SDL2-tarballs), although SDL2 is not essential for mdv2010-games.
.core-files: mdv2010 enhancement prosody of el6 and rosa2014.1 do not work. They declared to write the cause into a core-file within the actual directory you can delete whenever appearing.
UEFI: UEFITool (rpm from OpenSuSE 13.1 and other distributions); pkgs.org: "UEFITool is a cross-platform C++/Qt program for parsing, extracting and modifying UEFI firmware images. It supports parsing of full BIOS images starting with the flash descriptor or any binary files containing UEFI volumes. Original development was started at MDL forums as a cross-platform analog to PhoenixTool´s structure mode with some additional features, but the program´s engine was proven to be useful for another projects like UEFIPatch, UBU and OZMTool."
Time synchronization via ntp (el6)
Realtime clocks of modern PC do have less exactness than the cheapest watches for example. This article describes automatic adjustment of the system clock with a time server: http://www.pool.ntp.org/en/use.html
Service activation and deactviation: systemd for the service/service-administration remains without much usage for our system, because of MCC -> Services and the terminal based, chkconfig, x11-friendly ntsysv (el7, el6) ; nevertheless, if you still want to install systemd (what is possible for mdv2010), take one for el7, mdv2011, mga1 up to mga3, omv2015 or rosa2014.1. Alternatively activate, restart or stop services manually by the command "sh /etc/init.d/servicename start (resp. restart or stop).
[solved by Gooken: msec-gui (mdv2010 up to mdv2012, mga1 up to mga5 and rosa2014.1) of MCC (mdv2010.2) does not function ]
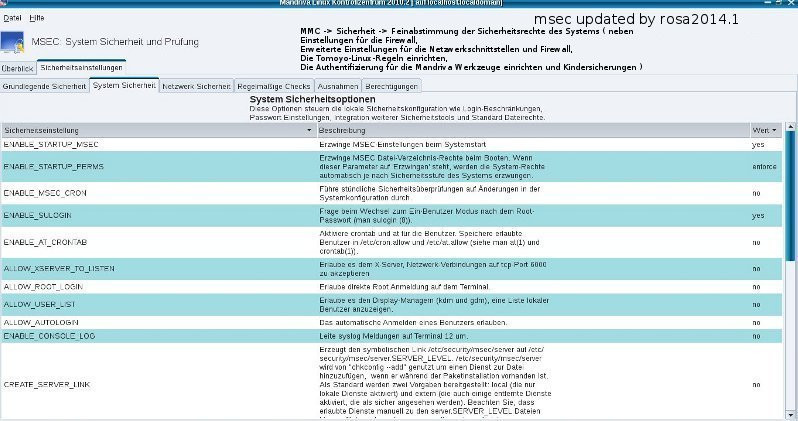
After all these updates, msec-gui (file /usr/share/msec/msecgui.py), part of MCC, does not function anymore, but we still can use msec, even rosa2014.1. Even all the games mentioned in datasheed do sill run.
error-message msec-gui (msecgui.py):
"ERROR: Attempt to add property GtkSettings::gtk-button-images after class was initialised.". This GLib-GObject-WARNING resulted from a modification in actual gtk+.
In order to avoid this error, you have to do the following, enter: nano /usr/share/msec/msecgui.py, and add:
.
import warnings
warnings.filterwarnings("ignore") anstelle warnings.filterwarnings("error")
This report helped us to solve the problem: http://stackoverflow.com/questions/20708657/python-gtk-how-to-suppress-warnings
Now you can even install the well-patched msec-gui and msec of mga5 or rosa2014.1, once again this correction sould be made, if.
[solved by Gooken: error-message of some GTK-programs like scorched3d instead of their start: ]
/usr/games/scorched3d: Symbol ´_ZTV12wxBufferedDC´ has different size in shared object, consider re-linking
/usr/games/scorched3d: Symbol ´_ZTV10wxClientDC´ has different size in shared object, consider re-linking
/usr/games/scorched3d: Symbol ´_ZTV10wxMemoryDC´ has different size in shared object, consider re-linking
/usr/games/scorched3d: Symbol ´_ZTV17wxBufferedPaintDC´ has different size in shared object, consider re-linking
Fatal Error: Mismatch between the program and library build versions detected.
The library used 2.8 (no debug,Unicode,compiler with C++ ABI 1002,wx containers,compatible with 2.4,compatible with 2.6),
and your program used 2.8 (no debug,Unicode,compiler with C++ ABI 1002,wx containers,compatible with 2.6).
GTK and gdk got updated. Just install the rpm named lib64wxGTK (mdv2010.1) and lib64wxpython (mdv2010.1). Now programs like scorched3d do start again.
[solved by Gooken: Miroplayer and gramps do not start and show error-messages containing python-files (.py)t: ]
Reinstall both from el6, if they should not start again, reinstall all lib64gtk- and lib64gdk-packages (mdv2010.1), eventually Python (mdv2010.1 und mdv2010.2) too.
You see by this amount of packages, that an update and upgrade of the X-Server remains quit risky.
... a first X11-server-troubleshooting ( assuming you can still read this text on your computer-monitor): Installing the X11-server can be the hardest thing you can install. On errors, have a look into the logfile /var/log/xorg.0.log. Maybe the kind of error is listed there. The amount of packages for the X11-Server to install is incomparible high over 50 with about 10 library-packages. In many cases it is helpful to edit the configuraiton file: nano /etc/X11/xorg.conf. In emergency, enter the standard driver "fbdev" or "vesa", otherwise you should keep the driver of your graphic card, eventually named by the manufacturer. Also keep all packages of X11 themselve in separate directories, both, those of the successor and predecessor version of X11-server. drm: reinstall the driver-package. More troubleshooting is provided on many websites in the internet.
Click here to get the list for the X11-Server-packages needed: It conisists of graphic card driver (Xorg), keyboard and mouse driver, touchpad driver and so on. You might just need to update with package xorg-x11-server-common (el6), xorg-x11-server-common (el6), libX11 (el6), libxcb (el6) and libxcb-python (el6) using rpm with option --force and -nodeps
Linux-devices in /dev:
fd0 floppy disc
fd1
sda s-ata-HD/SSD
sdb
sdc
sda1 first partition on sda
sdb7 seventh partition on sdb
sr0 first CD-ROM-device
sr1 second CD-ROM-device
ttyS0 first serial port (Port 0, known as COM1 under MS DOS)
ttyS1 second serial port
psaux PS/2-mouse
gpmdata pseudo-device, transferring data from the GPM-(mouse-)daemon
cdrom symbolic link to the CD-ROM-device
mouse symbolic link to the device-file of the mouse
null Alles, was an dieses Gerät geschickt wird, verschwindet
zero device to read an infinite amount of zeroes from this device
psmouse PS/2-mouse (should be detected automatically)
usbhid USB-mouse (should be detected automatically)
sermouse most serial mices
logibm Bus-Maus, adapted on a logitech-adapter
inport Bus-Maus, adapted in an ATI or Microsoft InPort-card
Keyboard and mouse get almost configured automatically by hal, alternatively by MCC or systemsettings and gnome-control-center. Manually they can be configured in /etc/X11/xorg.conf for the common PS/2-wheel-mouse by lines like these:
Section "InputDevice"
Identifier "Mymouse1"
Driver "mouse"
Option "CorePointer"
# Option "Device" "/dev/psaux"
# Option "Device" "/dev/ttyS0"
Option "Device" "/dev/input/mice"
# Option "Device" "/dev/ttyS0"
Option "Protocol" "ImPS/2"
Option "Protocol" "Auto"
# Option "Protocol" "ExplorerPS/2"
# Option "Protocol" "auto"
Option "ZAxisMapping" "4 5"
Option "Emulate3Buttons" "true"
EndSection
###################################################################################################################################################################################
# xorg.conf with automatic hardware detection
# WARNING: TRY TO CONCETRATE ON A FEW SETTINGS ONLY FOR THE FIRST TRIALS, IF X-SERVER DOES NOT START:
# if Xorg doesn´t start, consult /var/log/Xorg.0.log, in order to look out for errors (EE) and warnings (WW) !!
###################################################################################################################################################################################
#
# Einzelheiten: "man xorg.conf"
# File generated by XFdrake (rev )
# **********************************************************************
# Refer to the xorg.conf man page for details about the format of
# this file.
# ******
# ****************************************************************
Section "ServerLayout"
Identifier "XFree86 Configured"
Screen 0 "Screen0" 0 0
InputDevice "Keyboard0" "CoreKeyboard"
InputDevice "Mymouse1" "CorePointer"
Option "AIGLX" "true"
EndSection
Section "ServerFlags"
Option "DontVTSwitch" "true"
Option "DontZap" "true" # disable <Ctrl><Alt><BS> (server abort)
Option "AllowMouseOpenFail" "true" # allows the server to start up even if the mouse does not work
DontZoom # disable <Ctrl><Alt><KP_+>/<KP_-> (resolution switching)
Option "DPMS" "true"
Option "Xinerama" "true"
# Option "DRI2" "true"
Option "UseDefaultFontPath" "true"
# Option "Pixmap" "32"
Option "IgnoreABI" "true"
Option "AutoAddDevices" "true"
Option "AutoEnableDevices" "true"
EndSection
Section "Files"
ModulePath "/usr/lib64/xorg/modules/extensions,/usr/lib64/xorg/modules"
FontPath "/usr/share/fonts/X11/misc:unscaled"
# FontPath "/usr/share/fonts/X11/cyrillic"
FontPath "/usr/share/fonts/X11/100dpi/:unscaled"
FontPath "/usr/share/fonts/X11/75dpi/:unscaled"
FontPath "/usr/share/fonts/X11/Type1"
FontPath "/usr/share/fonts/X11/100dpi"
FontPath "/usr/share/fonts/X11/75dpi"
FontPath "/usr/share/fonts/truetype"
FontPath "built-ins"
EndSection
Section "Module"
Load "dbe" # Double-Buffering Extension
Load "v4l" # Video for Linux
Load "type1"
Load "freetype"
Load "glx" # 3D layer
Load "dri" # direct rendering
Load "record" # Developer extension, usually not needed ( ... but this is speeding up KI !)
Load "extmod"
# Load "speedo" # Speedo fonts, this module doesn´t exist in Xorg 7.0.17
# The following are deprecated/unstable/unneeded in Xorg 7.0
# Load "ddc" # ddc probing of monitor, this should be never present, as it gets automatically loaded.
# Load "GLcore" # This should be never present, as it gets automatically loaded.
# Load "bitmap" # Should be never present, as it gets automatically loaded. This is a font module, and loading it in xorg.conf makes X try to load it twice.
SubSection "extmod"
Option "omit xfree86-dga"
EndSubSection
EndSection
Section "Extensions"
# compiz needs Composite, but it can cause bad (end even softreset-resistant)
# effects in some graphics cards, especially nv.
Option "Composite" "Enable"
EndSection
Section "Monitor"
Identifier "Monitor0"
ModelName "Generic Monitor"
# HorizSync 47.7
# VertRefresh 59.8
Option "PreferredMode" "1366x768"
# DisplaySize 361 203
# Beware having to wear glasses! Vesa values! You can comment in following Modeline for Monitor AOC e943FwS preferred modeline (59.8 Hz vsync, 47.7 kHz hsync, ratio 16/9, 84 dpi)
# ModeLine "1366×768" 85.5 1366 1436 1579 1792 768 771 774 798 +hsync +vsync
# ModeLine "1368×768_120" 185.67 1368 1472 1624 1880 768 769 772 823 -hSync +vsync
# ModeLine "1368×768_100" 151.73 1368 1464 1616 1864 768 769 772 814 -hSync +vsync
# ModeLine "1368×768_85" 125.67 1368 1456 1600 1832 768 769 772 807 -hSync +vsync
# ModeLine "1368×768_75" 110.19 1368 1456 1600 1832 768 769 772 802 -hSync +vsync
# ModeLine "1368×768_60" 85.86 1368 1440 1584 1800 768 769 772 795 -hSync +vsync
# ModeLine "1368×768" 85.86 1368 1440 1584 1800 768 769 772 795 -hSync +vsync
# ModeLine "1368×768_50" 69.92 1368 1424 1568 1768 768 769 772 791 -hSync +vsync
# Option "MonitorLayout" "LVDS,AUTO"
EndSection
Section "Device"
Identifier "Card0"
# Driver (chipset) autodetect
VendorName "All"
BoardName "All"
# BusID "PCI:1:0:0"
# VendorName "Intel Corporation"
# BoardName "Intel 810 and later"
# Driver "intel"
Screen 0
# BusID "PCI:0:2:0"
Option "DPMS"
# Option "AccelMethod" "EXA"
# Option "AccelMethod" "sna"
Option "AccelMethod" "glamor"
Option "AddARGBGLXVisuals" "true"
Option "fbdev" "true"
Option "DRI" "true"
Option "DRI" "2"
# Option "DRI" "3"
### Available Driver options
# sw_cursor is needed for some ati and radeon cards
# Option "sw_cursor"
# Option "hw_cursor"
# Option "NoAccel"
# Option "ShowCache"
# Option "ShadowFB"
# Option "UseFBDev"
# Option "Rotate"
# Option "VideoKey"
# Option "Linear Framebuffer <bool>
# Option "SwapbuffersWait" <bool>
# Option "XvPreferOverlay" <bool>
# Option "Backlight" <str>
# Option "ColorKey" <i>
# Option "HotPlug" true
# Option "XvMC" <bool>
# Option "RelaxedFencing" <bool>
#Option "RelaxedFencing" # [<bool>]
#Option "Throttle" # [<bool>]
#Option "ZaphodHeads" # <str>
#Option "DelayedFlush" # [<bool>]
#Option "TearFree" # [<bool>]
#Option "PerCrtcPixmaps" # [<bool>]
#Option "FallbackDebug" # [<bool>]
#Option "DebugFlushBatches" # [<bool>]
#Option "DebugFlushCaches" # [<bool>]
#Option "DebugWait" # [<bool>]
#Option "BufferCache" # [<bool>]
#Option "TripleBuffer" # [<bool>]
Option "DisableGLXRootClipping" "true"
Option "EnablePageFlip" "true"
Option "ColorTiling2D" "true"
Option "TripleBuffer" "true"
Option "MigrationHeuristic" "greedy"
Option "ColorTiling" "true"
Option "TearFree" "true"
Option "ZaphodHeads" "VGA1"
# Tweaks for the xorg 7.4 (otherwise broken) "intel" driver
Option "Tiling" "no"
Option "Legacy3D" "false"
# compiz, beryl 3D-Support with DRI &Composite
Option "XAANoOffscreenPixmaps"
Option "AllowGLXWithComposite" "true"
# These two lines are (presumably) needed to prevent fonts from being scrambled
Option "XaaNoScanlineImageWriteRect" "true"
Option "XaaNoScanlineCPUToScreenColorExpandFill" "true"
EndSection
Section "Screen"
Identifier "Screen0"
Device "Card0"
Monitor "Monitor0"
DefaultColorDepth 24
Option "AddARGBGLXVisuals" "true"
Option "DisableGLXRootClipping" "true"
SubSection "Display"
Depth 24
Modes "1366×768"
EndSubSection
SubSection "Display"
Depth 32
Modes "1366×768"
EndSubSection
SubSection "Display"
Depth 16
Modes "1366×768"
EndSubSection
SubSection "Display"
Depth 15
Modes "1366×768"
EndSubSection
EndSection
Section "DRI"
Mode 0666
EndSection
Section "InputDevice"
Identifier "Mymouse1"
Driver "mouse"
# Option "Device" "/dev/ttyS0"
Option "Protocol" "ImPS/2"
# Option "Device" "/dev/psaux"
# Option "Device" "/dev/ttyS0"
Option "Device" "/dev/input/mice"
Option "Emulate3Buttons" "true"
Option "CorePointer"
# Option "Protocol" "Auto"
# Option "Protocol" "ExplorerPS/2"
# Option "Protocol" "auto"
Option "ZAxisMapping" "4 5"
# Option "ZAxisMapping" "4 5 6 7"
EndSection
Section "InputDevice"
# generated from default
Identifier "Keyboard0"
Driver "kbd"
Option "XkbModel" "pc105"
Option "XkbLayout" "de"
Option "CoreKeyboard"
Option "XkbRules" "xorg"
Option "AccelerationProfile" "0"
EndSection
Used driver: xorg-x11-drv-intel (el, 2016)
So have a look into "man xorg.conf" and "man mousedrv".
X11-error-log: /var/log/Xorg.0.log
Try X11 without any /etc/xorg.conf too!
Depending on the graphic card, special options for optimization should be set in /etc/X11/xorg.conf, see "man xorg.conf" and other websites out of the internet.
Power Management: /etc/udev/rules.d/30-intel-pm.rules
KERNEL=="dri/card0", SUBSYSTEM=="drm", DRIVERS=="intel", ATTR{device/power_method}="profile", ATTR{device/power_profile}="high"
intel.audio=1 intel.modeset=1 intel.dpm=1 in /boot/grub/menu.lst
kernel (hd0,7)/vmlinuz-5.4.110-pclos1 BOOT_IMAGE=drc008win2smp root=UUID=ab849ba-13b3-42bd-21f3-3ab44cc32261 rootfstype=reiserfs elevator=deadline nosmp security=none speedboot=yes panic=0 disable=IPV6 apparmor=0 selinux=0 audit=0 iomem=strict hibernate=protect_image KEYMAP=de LANG=de_DE.UTF-8 intel.audio=1 intel.modeset=1 intel.dpm=1 rd.luks=1 rd.multipath=0 rd.dm=0 rd.lvm=0 rd.md=0 rd.shell=0 rd.luks.allow-discards rd.luks.uuid=f2132a42-421e-124b-a426-daa321821b2c vga=792 video=VGA-1:1366×768
/etc/drirc
<driconf>
<!-- Please always enable app-specific workarounds for all drivers and screens. -->
<device driver="i915">
<application name="Default">
<option name="stub_occlusion_query" value="true" />
<option name="fragment_shader" value="true" />
</application>
...
</driconf>
~/.drirc
<driconf>
<device screen="0" driver="i915">
<application name="Default">
<option name="force_s3tc_enable" value="true" />
<option name="no_rast" value="false" />
<option name="always_flush_cache" value="true" />
<option name="shader_precompile" value="true" />
<option name="always_flush_batch" value="true" />
<option name="bo_reuse" value="1" />
<option name="vblank_mode" value="3" />
<option name="force_glsl_extensions_warn" value="true" />
<option name="disable_throttling" value="true" />
<option name="disable_glsl_line_continuations" value="true" />
<option name="disable_blend_func_extended" value="true" />
<option name="early_z" value="false" />
</application>
<application name="Unigine Sanctuary" executable="Sanctuary">
<option name="force_s3tc_enable" value="true" />
<option name="force_glsl_extensions_warn" value="true" />
<option name="disable_blend_func_extended" value="false" />
<option name="vblank_mode" value="3" />
<option name="always_flush_cache" value="true" />
</application>
<application name="Unigine Tropics" executable="Tropics">
<option name="force_s3tc_enable" value="true" />
<option name="force_glsl_extensions_warn" value="true" />
<option name="disable_blend_func_extended" value="false" />
</application>
<application name="Unigine Heaven (32-bit)" executable="heaven_x86">
<option name="force_glsl_extensions_warn" value="true" />
<option name="disable_blend_func_extended" value="true" />
</application>
<application name="Unigine Heaven (64-bit)" executable="heaven_x64">
<option name="force_glsl_extensions_warn" value="true" />
<option name="disable_blend_func_extended" value="true" />
</application>
<application name="Unigine Valley (32-bit)" executable="valley_x86">
</application>
<application name="Unigine Valley (64-bit)" executable="valley_x64">
</application>
<application name="Unigine OilRush (32-bit)" executable="OilRush_x86">
<option name="disable_blend_func_extended" value="true" />
</application>
<application name="Unigine OilRush (64-bit)" executable="OilRush_x64">
<option name="disable_blend_func_extended" value="true" />
</application>
<application name="Savage 2" executable="savage2.bin">
<option name="disable_glsl_line_continuations" value="true" />
</application>
<application name="Topogun (32-bit)" executable="topogun32">
</application>
<application name="Topogun (64-bit)" executable="topogun64">
</application>
<application name="Dead Island" executable="DeadIslandGame">
</application>
<application name="Second Life" executable="do-not-directly-run-secondlife-bin">
</application>
</device>
</driconf>
/etc/modprobe.de/i915.conf
options i915 enable_fbc=1
options i915 enable_guc=2
options i915 fastboot=1
/etc/environment
COGL_ATLAS_DEFAULT_BLIT_MODE=framebuffer
modul (graphic card driver) are named vesa (norm for the case you don´t know), fbdev (one more standard driver for the case other ones do not work), dummy (dummy card, for the case you don´t know), intel, nv (nvidia), nvidia173, nvidia96xx, nvidia-current, ati (Radeon Rage, RagePro, ...), r128 (ATI Rage128), amdgpu, radeonhd (also many amdgpu), radeon (AMD with previous ATI), fglrx (AMD/ATI Radeon 2000 and higher, ..., includes the popular AMD-/ATI-proprietary driver named catalyst), trident, nv (nvidia), nouveau (nvidia), dummy, openchrome (including unichrome drivers), sis, sisdrv (sis), sisimedia (sis), v4l, vga, xgixp, uncommon mit: tga, tseng, voodoo, siliconmotion, rendition, newport, apm, ark, chips
Packets for many graphic card driver: X11, xorg, x11-driver-video-modulname (mdv, mga, rosa) resp.. xorg-x11-drv->modulname< (el6, el7), radeon-firmware (rosa2014.1, rosa2016.1; already included within packet kernel-firmware or kernel), libdrm (el6), mesa (el6, el7, fc, ..., OpenGL-Treiber), packets for X11 in detail (el6, rosa, mdv) see the listing in our section "Universal Linux 2010" - Updates; akmod-catalyst, kmod-catalyst (fc21), xorg-x11-driver-catalyst (fc21), xorg-x11-driver-catalyst-libs (fc21) or x11-video-drivers-fglrx (mdv, rosa), dkms (mdv), dkms-fglrx (mdv), fglrx-control-center (mdv, mga, rosa), xf86-video-fbdev (arch-linux), xf86-video-vesa (arch-linux), nvidia-utils (arch-linux), lib64-nvidia-utils (arch-linux), nvidia-390xx (arch-linux), nvidia-390xx-utils (ach-linux), lib64-nvidia-390xx-utils (arch-linux), nvidia-340xx (arch-linux), nvidia-340xx-utils (arch-linux), lib64-nvidia-340xx-utils (arch-linux)
The Linux kernel includes open-source video drivers and support for hardware accelerated framebuffers. However, userland support is required for OpenGL and 2D acceleration in X11.
First, identify your card:
lspci | grep -e VGA -e 3D
Then install an appropriate driver. You can search the package database for a complete list of open-source video drivers:
rpm -i --force xf86-video # Arch Linux
Xorg searches for installed drivers automatically:
If it cannot find the specific driver installed for the hardware (listed below), it first searches for fbdev (xf86-video-fbdev).
If that is not found, it searches for vesa (xf86-video-vesa), the generic driver, which handles a large number of chipsets but does not include any 2D or 3D acceleration.
If vesa is not found, Xorg will fall back to kernel mode setting, which includes GLAMOR acceleration (see modesetting(4)).
In order for video acceleration to work and often to expose all the modes, that the GPU can set, a proper (resp. proprietary - manufacturer) video driver is required:
...
https://wiki.archlinux.org/index.php/xorg
https://wiki.archlinux.org/index.php/ATI
generate xorg.conf from current configuration
Oh man, would that be helpful!
Does the logfile help you at all?
Code:
/var/log/Xorg.0.log
I´m pulling my hair out trying to get an old laptop going because Xorg & HAL aren´t able to auto-detect the display´s available resolutions properly (for whatever reason).
So, I´m looking around trying to piece together which bits I need from the automatically detected configuration, and which bits I need to supply.
I have been looking at the logfile and while it doesn´t supply a ready formatted, complete xorg.conf it will give you a lot of details to generate one from.
But I´m still looking for a better solution...
Advanced reply Adv Reply
May 14th, 2010 #4
Gatemaze
Distro
Ubuntu 10.04 Lucid Lynx
Re: generate xorg.conf from current configuration
Thanks P&C, it is some progress... but still a "write_xorg" of the current configuration would be ideal
Advanced reply Adv Reply
May 19th, 2010 #5
Distro
Ubuntu 9.10 Karmic Koala
Re: generate xorg.conf from current configuration
I´ve spent some more time looking at this and it would appear that it is possible afterall...
In my case, (Ubuntu 9.10) I booted into the recovery mode and ran
Code:
Xorg -configure
This tells you that it generates the configuration file: /root/xorg.conf.new
It also says that running the following will test it:
Code:
X -config /root/xorg.conf.new
However, in my case I was pleasantly greated with black text on a black background with a black cursor - either that or it didn´t work...
2nd time around:
Code:
cp /root/xorg.conf.new /etc/X11/xorg.conf
shutdown -r now
This appears to startup my laptop "normally", so I now have a configuration file to start playing with.
I have yet to check the logfile, etc, but I thought it answered your original post, so I thought I´d post asap.
Hope it helps you (or anyone else!) out...
https://ubuntuforums.org/showthread.php?t=1478310
Portability, new platform or graphic card: One worse thing, that can happen, and this is a nightmare: a darkscreen (ASUS ITX 220): Graphic cards themselves seldom get out of order. Exchange the CMOS-battery and/or unplug the BIOS-chip out of its socket to plug it into again (even think of a spare parted BIOS-chip). Also make a copy of xorg.conf like xorg-save.conf and preconfigure files with MCC -> graphic card for different cards and standard driver vesa, fbdev and fglrx. Test and save each new created pre-configuration file xorg.conf to xorg-nv.conf, xorg-ati.conf, ..., xorg-vesa.conf, xorg-fbdev.conf and xorg-fglrx.conf. The best thing one can do is to order one more graphic card of same manufacturer to keep it spare-parted.
The graphic card drivers itself can be found in /usr/lib64/xorg/modules/drivers (or any subdirectory).
If the methods above do not help, that means if testing fails, just rename the graphic card drivers in right this directory or a subdirectory depending on the location (of the driver), after a new graphic card is plugged or in use, while /etc/xorg.conf with the named old driver remained still unchanged by module name. Other parts of /etc/X11/xorg.conf should be tuned well instead - following the through MCC preconfigured xorg-xxx.conf from above.
In the normal case, the X-server creates a new /etc/X11/xorg.conf belonging to the any graphic card automatically after it got deleted (removed), but one can not guarantee, he really does ....
Samba (for the LAN): samba-client (el6), samba-common (el6), samba-winbind (el6), samba-winbind-clients (el6), libtdb (el6) and libtevent (el6), LDAP. openldap (el6)
... and the computer keeps what he promises to be. Even dmesg is listing no errors and no warnings at all (polkit and mandriva-galaxy got updated)! As we told, we recommend to take all these updates, although mdv2010 did run fine before.
The only in unicode from el6 differing python (mdv2010.2) and perl (mdv2010.2), same version like el6, should not be updated or changed, but the modules of python (el6) might be still necessary like python-gobject2 (2010.1 for the miroplayer), python-dbus (mdv2010.1) and python-pycurl (el6, both for the miroplayer for example)
Update by installing rpm and/or tarballs (URL for downloading the tarballs are listed in fr2.rpmfind.net). You have to wait some time, until the newest update-packages for el6 appear.
More packages from el6 and el7, but not indexed for Gentoo-GLSA: dropwatch (to watch packages dropped by iptables), acl (el6, access control lists), passwd (el6, to set the password), cronie (el6, Cron, task-daemon), cronie-anacron, cronie-noanacron and crontabs, cpufrequtils (el6), x86info (el6), wireless-tools (el6), eventually, but we do not recommend this perl ad python of quit the same version, but different rpm-libraries and unicode. Some tray-applets do not function anymore, if), alsa-firmware (el7), alsa-tools-firmware (el7), ca-certificates-2015 (el6), libnghttp (el7), libpng (el7), brasero (el6), noiz2sa (mdv2010 or mga4, game)
Think of the removal of the online-update-tool mdkonline (if installed) by "rpm -e mdkonline" as mdv2010.2 might sometimes makes unsuccessfully password-request caused by urpmi.update and consolehelper, if not.
Only rpm networkmanager and pam_mount from mdv2010.0 should not be updated from mdv2010.2, so take the versions for mdv2010.2 resp. mdv2011.0 from fr2.rpmfind.net.
All those updates are included in our mdv2010.2 from SSD. We only gurantee GLSA-actuality of the offered SSD until 31.08.2015. With an actual browser and LINFW3, we do not see many problems causing in less updating in future.
 LUKS/dm-crypt: You can install well-patched rpm for cryptsetup like cryptsetup (rosa2014.1) or cryptsetup-luks (el6), cryptsetup-libs (el6), cryptsetu-reencrypt (el6), cryptsetup-reencrypt-libs (el6) in future, but actually there is still no update essential, so that the cryptsetup of mdv2010 and 2011 can be kept. Do not take cryptsetup of mdv2012, what can lead into serious hard errors.
LUKS/dm-crypt: You can install well-patched rpm for cryptsetup like cryptsetup (rosa2014.1) or cryptsetup-luks (el6), cryptsetup-libs (el6), cryptsetu-reencrypt (el6), cryptsetup-reencrypt-libs (el6) in future, but actually there is still no update essential, so that the cryptsetup of mdv2010 and 2011 can be kept. Do not take cryptsetup of mdv2012, what can lead into serious hard errors.
Java (Oracle) for Linux: http://java.com/de/download/help/linux_x64rpm_install.xml
Howto update firefox
Firefox > ESR (rosa2014.1, el7, el6): adwaita-cursor-theme (el7), adwaita-icon-theme (el7), atk (el7), cairo (el7), cairo-gobject (el7), colord-libs (el7), gtk3 (el7), lib64udev1 (rosa2014.1), rest (el7), mozilla-filesystem (el7, el6)
Firefox Release Notes (Changelog): http://www.mozilla.org/en-US/firefox/releases
Update by installing the newest release: tarball or el6, el7
Update by yum: yum update firefox
Update Mozilla Firefox to an actual Firefox under Linfw3 by unpacking the firefox-tarball and copying all files into /usr/lib64/firefox-oldversion, then, if links should be missed, link again the executable files firefox-bin and firefox with those out of /usr/lib64/firefox-olderversion. For Firefox 32 you still need some additional libraries, that you can get from rpmfind.net, all on our DVD 2. It is best to update to 32 or newer automatically by setting LInfw3 to state-new-lineblocks, calling firefox by su (superuser), click onto register named help for updating firefox, chmod 755 -R /usr/lib64/firefox* and finally by activating Linfw3 once again, so that the state-NEW-line-block is deactivated automatically. Update Firefox-Addons like ublock-origin and noscript by register extras -gt; Addons and checkout plugins. Configure ublock-origin by clicking on "dashboard" in the left upper corner.
It might be more secure to download the actual tarball for firefox from mozilla.org and to enpack him into the directory, the firewall was stored before. Then the owner for this directory and its files has to be set by chown root -R /home/user/firefox. We recommend owner root by the usual virus-free chmod 755 -R /usr/lib64/firefox.
Pale Moon (28.1.0) - main features:
Optimized for modern processors
Based on our own optimized layout engine (Goanna)
Safe: forked from mature Mozilla code and regularly updated
Secure: Additional security features and security-aware development
Supported by our user community, and fully non-profit
Familiar, efficient, fully customizable interface
Support for full themes: total freedom over any element´s design
Support for easily-created lightweight themes (skins)
Smooth and speedy page drawing and script processing
Increased stability: experience fewer browser crashes
Support for many Firefox extensions
Support for a growing number of Pale Moon exclusive extensions
Extensive and growing support for existing web standards
Many customization and configuration options
https://www.palemoon.org/
 Deinstall: all insecure browser-plugins, especially those, who can not be deactivated:
Deinstall: all insecure browser-plugins, especially those, who can not be deactivated:
Link /home/surfuser/.mozilla/plugins with /usr/lib64/mozilla/plugins:
ln -sf /usr/lib64/mozilla/plugins /home/surfuser/.mozilla/plugins
rm -df /usr/lib64/mozilla/plugins/libswfdec* (Shockwave Flush)
rm -df /usr/lib64/mozilla/plugins/more-plugins.
Firefox 2.0.0.12 up to an actual Firefox (actual ESR) resp updated shortly timed by root (!) and linfw3 in mode "lined-block-only" to Firefox ESR can be tuned more securely by adding addon ublock-origin (resp. more plugins like privacy for the case of flash-supercookies, evtl. use another browser) and typing in about:config into the address-line to set
general.useragent.override (what does the same as configuration-file /home/surfuser/.kde4/share/config/kio_httprc for Konqueror), browser.safebrowsing.enabled, browser.safebrowsing.remote.lookups and browser.safebrowsing.malware.enabled.
same for all so called phishing preventing safebrowsing (almost by URI-exchanges with Google) by searching for it too as much as
for "tracking".
Also do this for "geo.location.enabled" setting to false.
 It is known for years, that a hand full of geo data is enough for the identification of persons, netzpolitik.org, 23.07.2021 It is known for years, that a hand full of geo data is enough for the identification of persons, netzpolitik.org, 23.07.2021
https://netzpolitik.org/2021/datenhandel-grindr-beendet-karriere/
Disable the history/chroniology of the browser and delete all session-cookies after its usage. Surf in private mode. Drag and drop the special symbol for chronic-content-deletion into the symbol-bar of Firefox to click on it.
Also notice the proxy-configuration in the section for the SSL-Proxy from Arif. All of mdv can be configured by MCC (drakconf.real) and the control-center in an easy, if not childish way. And who emulation of even foreign computer- resp. operating systems like Basilisk for Macintosh and Wine for MS Windows applications is not enough and can not resign from Debian - if a RPM (installation packet) should have ever been missed - just has the opportunity to install Debian´s packet-manager like apt. From thousand of progs, only f-spot from originally SuSE does not always function - always finding alternatives!
Cookies can be blocked by an adequate browser-configuration by options like "session-cookies only" or "generally forbid all cookies". Inspite of this, addons like Betterprivacy still are needed to delete supercookies (LSO flash objects, flash-player-standard-cookies, DOM Storage Objects, eBay long-time-tracing), that are obtained and set by flash-plugins and stored onto the computer-hard-drive for an undetermined long time. But this must be seldom enough to say, such files still never have been found on my computer. Both, noscript and Betterprivacy also disable click-ping-tracing. This might work as the name tells us.. Notice, that a replacement for Third-Party-cookies is planned through AdID, details see our linkside! The best one can do is to use the rotate-13, base-64 SSL-proxy-service with the IP and DNS exchanging PHP-Proxy programmed by Abdullah Arif, see our section for downloads, that can also be enabled to block all kind of scripts.
Graphic-card: standard-vesa-driver from installation-DVD, packets (almost x11-driver-video-...), http://www.x.org, or manufacturer
Sound: http://www.alsa-project.org
Printer driver: pdd-file from driver-CD/DVD, http://cups.org, http://linuxfoundation.org, http://www.linuxfoundation.org/collaborate/workgroups/openprinting and http://openprinting.org, http://turboprint.com, ...
GNU-software:
gnupg (OpenPGP Internet Standard following RFC4880 (zuvor RFC2440) for digital encryption and signatur, version 2 incl. the S/MIME-standard and Secure Shell Agent), from Werner Koch: http://www.gnu.org/software/gnupg/
wget: http://www.gnu.org/software/wget
bash: http://www.gnu.org/software/bash, http://ftp.hosteurope.de/mirror/ftp.gnu.org/gnu/bash/, fr2.rpmfind.net, for mdv2010 choose those for el6
...
Virus scanner: mdv2010 with clamav-0.98.4-65.el6, openssl-1.0.2d and clamd-0.98.4-1(!), yearly: virus-definition-file daily.cvd, main.cvd and bytecode.cld from http://clamav.net or by command "freshclam" . UID and GID should be set to user named clam or try the NEW-LINE-Block instead..
Squid: http://www.squid-cache.org/Versions
gramps (genealogy) is also running fine; for the first start LINFW3 might has to be set to "lineblock NEW".
One is enabled not only to update packets mdv-2010.0 by MCC (packet manager rpmdrake) but also from mdv2010.0 to mdv2010.1 and to the computer final stated mdv2010.2. All solutions and the sending of emails are most stable and secure, as rpmdrake notices all dependencies, by suggesting belonging packets or, if you do not have installed them, forbidding the installation otherwise. Depending on the graphic-card-driver, nevertheless be a little bit careful with the new X-Server resp. graphic-card-driver of mdv2010.1 or keep the one from mdv2010.0!
[ solved by Gooken: mdv2010.2, KDE 4.4.5: akonadiserver and nepomuk do not start ]
Akonadi and nepomuk (mdv2010.2): The best one can do past reconfiguring akonadi by akonadi_console and akonaditray is to install the following packages from fr2.rpmfind.net: akonadi-kde-4.4.9, lib64akonadi-filestore4-4.4.92, lib64kmindexreader4-4.4.92 and eventually strigi including strigi-gui and do not forget soprano. nepomuk for mdv2011 like nepomuk-datamanager can interest for mdv2010 too. Now all works fine, including annotate of dolphin´s and konqueror܌ context-menu works and emails can not only be received but also be sent without waiting for any "mood of KDE 4.4.5". In mdv 2010.0 with KDE 4.3.4 akonadi and nepomuk are already functioning.
Avoid problems with X11-upgrades, by listing X11-packets from fr2.rpmfind.net by categories, in this case category X11 and not A-Z. Although packets are devloped further on, a change to mdv2010.1 and 2010.2 does not provide much advantage.
For upgrades keep in mind the following dependencies from eachother, so that kmail (4.4.5) and Dolphin (4.4.5) do work: KDE (4.4.5) - akonadi (4.4.5) - nepomuk (4.4.5) - soprano (mdv2010.1) - virtuoso (mdv2010.1) and MySQL (rosa2012.1 or mdv2010.2).
Now, past this installations of packages for mdv2010.2, not only mdv2010.0, but also mdv2010.2 does not have any errors, akonadi (el6 or mdv2010) and nepomuk (strigi-libs (el6) resp. strigidaemon and eventually soprano (el6) ) do also work, if the amount of directories to index with strigi, that is configurable by the applet nepomuksearchclient is not set too low:
65 GB + x unlimited software error-free (only a few games depend on special drivers for certain graphic-cards)
If mysql is updated by mysql from el6, akonadi has to be reconfigured, for example using akonaditray. Set the path to mysqld to /usr/libexec for previous /usr/sbin is not valid anymore. For registration on dbus use dbus of mdv2010.1 and like akonadi not the lower versioned dbus of el6. Otherwise it is more difficult to configure akonadi through akonadiconsole.
If you can not believe in mdv2010 (resp. mdk10.1 or mdv2007) running such secure, or if you make other experiences with some software for this version, we remember, that one can select packages from fr2.rpmfind.net for long three years mdv: mdv2010.0 up to mdv2011 resp. mdv2012.0 up to mga2 and mga4, that are around 100.000 packets. Notice, that mdv is also almost downward-compatible. The only main thing you have to do for this yearly jumpover is to upgrade glibc.
One (quit everlasting) update-source out of the internet for mdv2010.0 is named ftp://fr2.rpmfind.net/linux/Mandriva/official/2010.0/x86_64/media/contrib/release. This URL should be entered into the MCC section update-sources installing all updates before the same address, but changed to mdv2010.1 and mdv2010.2 is entered. At first, nevertheless it was the right way to update mdv2010.0 with updates to this version before mdv2010.1 and mdv2010.2.
In order to start the kde-(kmail-)database-server akonadi successfully, akonditray should be started and configured to local mysql. If error-messages appear, delete all files in the user-directory
~/kde4/share/apps/akonadi, and start akonadi again. Akonadi can also be installed from el6, what does not influence previous installed akonadi for mdv2010. Configure nepomuk by systemsetttings or, like KDE4.4.5, still manually in ~/.kde4/config/share/apps/nepomuk... Now a nepomuk-icon appears in the system area of the control line after the booting of the system for further configurations of the semantic searches. Akonadi is handled by akonaditray and akonadiconsole.
The start of the semantic search by terminal, alternatively desktop-icon or out of Konqueror and Dolphin if provided by clicking on belonging buttons or by typing in "nepomuksearchclient".
The full functionality is pregiven by already made configurations on mdv2010.2 from our SSD.
Browser: Konqueror (4.4.5) is a comfortable open-sourced, secure browser with an own adfilter, that can be trained like the firefox-addon adblockplus. To present images from websides, the UA-specification and the adfilter might have to be configured adequately.
SSL Certificate SHA-1 to SHA-2 Transition, http://www.qualityssl.com/en/support/ssl-certificate-sha1-to-sha2-transition.lasso
Due to the discovery of vulnerabilities in the SHA-1 algorithm and the continual increase in computing power, the feasibility of breaking the SHA-1 hash will increase over time. Internet browsers and Certificate Authorities (CAs) have already started to phase out SHA-1 in favour of the new SHA-2 algorithm. However, recent announcements from Google about depreciating support for SHA-1 based certificates with an expiry date in 2016 or later means that you will have to take action now to make sure your SSL setup is not affected by the accelerated transition. This article offers you more information on how this will effect your SSL setup and how you can move to SHA-2 certificates.
As of 2014, SHA-1 is still acceptable, but with the continual increase in computing power, the security of SHA-1 will become a concern in the future.
As your security partner, QualitySSL has already made SHA-256 the default hash algorithm for all new QualitySSL Certificates since September 2014.
Important Dates
As part of their SHA-2 migration plan, Google, Microsoft and Mozilla have announced that they will stop trusting SHA-1 SSL certificates. Google will begin phasing out trust in SHA-1 certificates by the end of 2014, while Microsoft and Mozilla will begin phasing out trust for SHA-1 certificates in 2016.
November 2014 - SHA-1 SSL Certificates expiring any time in 2017 will show a warning in Chrome 39.
December 2014 - SHA-1 SSL Certificates expiring after May 31, 2016 will show a warning in Chrome 40.
January 2015 - SHA-1 SSL Certificates expiring any time in 2016 will show a warning in Chrome 41.
January 1, 2016 - Microsoft ceases to trust Code Signing Certificates that use SHA-1.
January 1, 2017 - Mozilla Firefox and Microsoft ceases to trust SSL Certificates that use SHA-1.
SHA-2 Compatibility
The good news is that most commonly used operating systems, browsers, mail clients and mobile devices already support SHA-2. We have put together a compatibility list for known SHA-2 support, as there are some older operating systems such as Windows XP SP2 that do not currently support SHA-2.
The following list gives an overview of operating systems/browsers that currently support SHA-2:
Apple iOS 3.0+
Android 2.3+
Blackberry 5+
Internet Explorer 6+ (with Win XP SP3+)
Safari with Mac OS X 10.5+
Firefox 1.5+
Netscape 7.1+
Mozilla 1.4+
Opera 9.0+
Konqueror 3.5.6+
Mozilla based browsers since 3.8+
OpenSSL 0.9.8o+
Java 1.4.2+ based products
Chrome 26+
Windows Phone 7+
Online Banking with the (we believe because of integrated opensourced OpenSSL from openssl.org only) maybe almost secure browser Konqueror, here version 4.4.5: adblocker depending on configuration activated or inactive, useragent: active, cookies: active, JavaScript active or depending on the bank inactive, plugins: active or inactive, Java: inactive; Konquerer seems to remain stable and secure until his fullfilled norms are too low.
FHS 2.1 (quit all Linux): /boot (the best is a separate boot-partition with initramfs from dracut), / root-directory, /bin (executable files), /sbin (shell-scripts), /lib (coded libraries), /usr, /usr/bin, /usr/sbin, /usr/games/bin/, /usr/lib64, /usr/src (sources), /usr/share/docs (manuals), /dev (device files resp. device-driver-api-files ), /opt ("third party software"), good mountpoints: /media, /mnt, /mnt/any, /proc (process information), /sys, /var (files, that do change their content very often), /var/log (Logfiles), /var/lib/drakbackup (backups, if not done extern), ..., configuration of mdv2010 (Linux): drakconf (MCC), systemsettings, gnome-control-center, directories and files within /etc and pointed files and pointed directories wihtin the user-directory ¨, also .kde/... and .kde4/share/config for the apps of KDE4 and /boot/grub/menu.lst for the configuration of the bootmanager grub and grub2
So turn off the Journalling now, set the root-partition to ro (readonly) and forbid the shell for root in /etc/passwd
Finally, after all the recommended updates and security updates (el6, el7, rosa2014.1) and even the downgrade to the well-patched Konqueror 4.3.4 are installed and the opearting system always is starting in the several times we hope always "OK" signing text mode instead of the graphic mode in MCC->System-Start with xscreensaver and plymouth disabled (chmod 000 /usr/bin/plymouth, chmod 000 /usr/bin/xscreensaver* or rm -df, killall plymouthd), programs, that present their own login-masks from time to time and increase the time for system-restart and system-shutdown, and after all (even the many games) is running stable and fine and a 1:1-backup has been made on an extern media, in order to resign from overhead to enlarging the life-time of the used SSD, you can think about the deactivation of the last state backupening journalling-feature of reiserfs (analogous ext3 and ext4) just by using the
mount option nolog the lines for the reiserfs based partitons in /etc/fstab. Notice, that options are separated by colons only in this file, no blanks at all.
notail deactivates the storage of small files in the inodes (information knodes, index entry) of the filesystem, so this option can also be set.
ro stands for read-only, that can be set for the root-partition. Notice, that no installs, updates and configuration in /etc is allowed anymore.
"The option "nolog" and "nojou" turn off the journalling feature of ReiserFS. This gives performance gain for some applications, but you lose fault tolerance. That is, you must properly umount your disk, or else you will have to repair the filesystem using reiserfsck(8) on the subsequent boot.(or by a rescue usb-stick/CD/DVD)", Quelle: http://www.botik.ru/doc/reiserfsprogs/html/fs.html .
A journalling filesystem enpossibles to increase the efficiency and security of the data- and memory-management by storing the data temporarily in a journal right before they are stored and administrated in the filesystem.
An extra memory place is reservated for this journal. The journal guarants data consistency too, as it is keeping a consistent, reconstructable state in the case of troubles during write operations. This has got the advantage, that in the case of system hangons and -breakdowns the data are not only reconstructable, but also, that routines for the check and repair are not needed anymore during the systemstart.
Examples for Journaling filesystems are: ReiserFS, NTFS, ext3/ext4 (Linux), JFS1/JFS2, HFJS (Hierarchical File Journaling System), BeFS (Be File System, BeOS) FFS (Berkeley Fast File System, BSD), SFS (SmartFilesystem) and PFS (Professional File System (Amiga)). Journalling filesystems can still be repaired by fsck resp. reiserfsck from a rescue-CD/DVD and -usb-sticks.
For SSD following options might interest: nojou,nolog,notail,noatime,nodiratime,data=writeback,discard,user=xattr,iocharset=utf-8.
At last, eacht time after updating resp. especially after updating the X-server, we set the variable
"allow-root-login" like "allow-remote-login" again to "no". This has to be stored by "msec -s actual-security-level".
 All shell-logins should be disabled in /etc/passwd and therefore set to /sbin/nologin, except for surfuser, /bin/bash is still assigned to.
All shell-logins should be disabled in /etc/passwd and therefore set to /sbin/nologin, except for surfuser, /bin/bash is still assigned to.
 The root-partiton should always be set read-only as already described.
The root-partiton should always be set read-only as already described.
 We summarize: The total secure OpenSource-Computersystem
We summarize: The total secure OpenSource-Computersystem
-
founds in certified, revisioned hardware with many exchangeable, compatible parts and components and socked, crashfree bios (see our data-sheed) and
-
has already been updated and patched on a daily-update-channel over decades like pro-linux.de and been configured well,
-
runs, including USB-memory-sticks full system encrypted (FSE),
-
offers a small rescue-partition for emegancies (out of Knoppix resp. Debian Linux, mindi or mondo etc.) upon one and the same solide state disk (SSD),
-
and no magnetic one,
-
does always run stable after solving the dependencies, never breaks down,
-
cares for enough free capacities (data-compressing, data-rubbish-deletion etc., new hardware )
-
provdies logins with restrictve amounts of login-attempts (almost three attempts) of increasing intervals of time-waits between them,
-
always works mouseclick-fast,
-
can be compiled and linked in error-free from source (here by command "make"),
-
forbids arbitrary program-execution and software-installation (only allowd within the root-mode, partitionwise option noexec)
-
protocols critical and emergency-states in logfiles, if still really needed,
-
supports with manpages (Manuals), info- and doc-files
-
works upon a scentific base, common standards and norms
-
includes a zero-emission-pad against the receipt of reconstractable monitor-gamma-radiation,
-
blocks as ruled in /etc/security/msec/level.* right from the beginning the root-login and its remote, the remote-root-login,
-
contains an effective sandbox like the access for the shell denying firejail,
-
blocks all pings (ICMP), all hacker and all backdoors and all trojans beginning with portscans (Portscan-Detection, PSD), working with a stringfilter upon data-payloads (main informaiton parts of transfered packages) like firewall linfw3,
-
eventually also uses an Intrusion Detection System (IDS, for example aide),
-
performs network analyzis from time to time (ethereal, wireshark, netstat),
-
minimizes the amount of running services by the system-configuration (resp. daemons like systemd) and autostarted programs
-
uses a local instead of a dynamic DNS-server (dnsmasq)
-
and dynamic (from time to time changing) IP-addresses of the old address-room IPv4,
-
changes or hides the UA-specification of the browser, blocks scripts over self-learnt (inner-completed) browser-ad- and scriptblocker, deactivating Java, JavaScript, extensions and history,
-
limits and secures the access through access rights already set within /etc/security/msec each system boot),
-
solves file-release etc. as much as
-
all requirments of the user through surface-covering software(-packages) and compiled-in tarballs,
-
checks out partition for errors and optimization each system boot,
-
permits single read-only (no write-operation allowed) upon the separate boot- and the root-partition,
-
evenutally controls the mandatory access ( MAC, Mandatory Access Control like acl, SELinux or Tomoyo) for secured interprocess-communication,
-
eventually contains a virus-scanner to check out attachements for any mail-viruses on the home-Partion,
-
encrypts all connections (best: end-to-end) and passwords well,
-
cares for Two-Factor-Authentification for submits,
-
is free from any maintenance (Task-)planer (cron),
-
might control access upon files from the background (incron)
-
automazises everything possible, even without user ( automatic powering on and off, suspend mode, sdparm, hdparm), task planner (cron), E-Mail-absence-notificaiton (vacation,...)
-
makes self-checks (part of msec) superfluos after having perfomed them first times,
-
learns itself from errors made,
-
reacts suitable for disabled too,
-
keeps user from making the wrong decision by requests (asking back) before operating,
-
does not cost much, consumpts rare power (<= electric bulb), runs on UPS in emergencies,
-
does even not need to make use of the journalling-feature of journalling-filesystems (restoring the last state right before the error occurs) against the cost of ( reached ) security and
-
blocking the login for all system user including root except the custom user in /etc/passwd .
Principe
32-Bit-programs run on 64-bit-systems, but 32-Bit-Systems require 32-Bit-programs only. Actually not all programs are made of 64-Bit. The 64-Bit-version of Windows contains an emulator (WOW64) to run 32-bit-software. Packages for Linux like mdv are already compiled without such emulator in the two ways either x86_64 (64 bit) or i586 (32 bit), although both are running on 64-bit-systems. So we talk about mdv2010.x86_64, mdv2010.i586 and the source-code for both.
For more IS-demands we can find a lot of software for security on the market and its amount is increasing day by day. And if you ask us, what is needed from it, it would be so much to encounter, that it is resulting in around nothing but zero and therefore around none at all!
MS Windows never has been a problem for hacking professionals.
Early black-coded MS Windows like 95 and SE did neiter run more stable than SuSE 7.3 nor they were running by a satisfying security-equipment. Updates have been provided over years and decandencies for successor XP by SP1 up to SP3 in the volume larger than its installation-CD of more than 750 MB . The following editions cared for security improvement - without constating, if ever enough. Generally, in conjunction with software, only the one performing the main functionalities regardless from lacks in security is the right, along software by software - regardelss from exploits, updates, but stability! The excursion resigns from all those software from markets by preferring complex,
the almost the POSIX-standard fulfilling Open-Source UNIX-/Linux distribution of high-schools from almost one DVD. Although SuSE 7.3 from year 2002 did not run very stable, it seemed to be already well-equipped for security-tasks as in its core by file-systems like reiserfs. And, as we know, even MAC-OS from Apple inc. is a derivation from UNIX. Linux is used by supercomputers too. It always consists for a directory-structure out of boot out of ramdisc, kernel and boot-manager, bin and sbin for the exectuable system-files similar to usr with bin and lib for the applications, opt for large software-packages, etc for configuration, proc for details about processes, var for files like log-files created by processes, tmp for temporary files and so on. Even the NSA is using Linux by "The NSA Security Enhanced Linux kernel" selinux, a linux kernel with Mandatory Access Control (MAC).
An illustrated introduction for MAC Tomoyo-Linux for mdv like 2010 is presented here.
In our eyes, Mandriva-final with its hugh repertoire of all kind of driver and software and Gentoo belong to the most secure Linux-Distros.Gentoo describes itself as a meta-distribution. The source code is compiled to binary applications on the user´s machine allowing near-unlimited adaptability and complete retraceability of the program logic. Beneath our best experiences with Mandriva-2007 and 2010-final and together wite belonging Source-DVD (DVD 3) we do not like to resign from recommending them.
AppArmor gives you network application security via mandatory access control for programs, protecting against the exploitation of software flaws and compromised systems.
https://de.opensuse.org/AppArmor
To the kernel-security-modules belong apparmor, selinux, tomoyo and smurf, apparmor is most recommended. Start it by entering the boot-option security=apparmor into /boot/grub/menu.lst (analogous grub2):
| kernel (hd0,1)/vmlinuz-4.9.49 BOOT_IMAGE=4.9.49 root=UUID=... rootfstype=reiserfs elevator=deadline audit=0 panic=0 security=apparmor speedboot=yes apparmor=1 selinux=0 nosmp hibernate=protect_image disable=IPV6 iomem=strict intel.audio=1 intel.modeset=1 intel.dpm=1 KEYMAP=de LANG=de_DE.UTF-8 rd.luks=1 rd.multipath=0 rd.dm=0 rd.lvm=0 rd.md=0 rd.luks.allow-discards rd.luks.uuid=... vga=795 video=VGA-1:1366×768 desktop=kde tz=Europe/Berlin |
Nevertheless our computer-system might does its best (mouseclick-fast, security) using apparmor. Notice, that the additionally installed rsbac-kernel (in our case kernel-rsbac-desktop-mdv2012, 3.1.1-1) got also activated by above boot-options "rsbac_softmode" and "rsbac_um_no_excl". .
Another report from 2001 in conjunction with encrpytion from the Cambridge University Computer Laboratory about so called Zero Emission : "Decades ago international secret services use the fact, that all electronic devices, even PCs, do emit traitorous "compromitting" radiation. Out of a distance of many meters, even through walls, the image from the computer-monitor can be reproduced. Only a few users are conscious about this danger. The most popular method to reduce the danger of this radiation is to use expensive, special computers, consisting of a surface out of aluminium. They cost a mulitple of the unproteceted equivalent and must be maintained periodically. Such computer are called TEMPEST-secure (TEMPEST: Transient Electromagnetic Pulse Emanation Standard). Interesting to know of some sellers of such hardware do forward the addresses of their customers to organizations standing nearest to secret services. Further methodes base on radiation absorbing tents and special interfering transmitter. Together with our partner (partner from Steganos inc.), the Cambridge University from Geat Britain, we offer you the possiblity to make this radiation irrelevant by software ("Soft-Tempest"). Therefore the freeware texteditor Zero Emission Pad is developed to support as a worldwide, even for Unix (Linux) emulateable Editor the display with in certain kind reduced radiation (Patent GB 9801745.2)."

and especially

| allow_remote_root_login = no |
in /etc/security/msec über

msec: level 3 for "secure" resp. "server" or "server-mode" "limited remote only"). The many security-functions set for this level are listed in MCC, section "system security and check". Level 3 is for server and systems, that shall beware security. Since this time, our computer does not have any bluescreens, blackouts or anything else, while the first installation of mdv2010 got under massive attack like aiming to destroy everything of your computer with more than received 50 spam per day until we set it... Once this command is entered or this level is chosen by MCC out of /etc/security/msec/level.secure, the suneater is forced in main to stand outside...:
 /etc/security/msec/level.secure (to go sure, overwrite all /etc/security/level.* and activate msec automatically within /etc/rc.local by command "msec -f secure"):
/etc/security/msec/level.secure (to go sure, overwrite all /etc/security/level.* and activate msec automatically within /etc/rc.local by command "msec -f secure"):
ACCEPT_BOGUS_ERROR_RESPONSES=no
ACCEPT_BROADCASTED_ICMP_ECHO=no
ACCEPT_ICMP_ECHO=no
ALLOW_AUTOLOGIN=no
ALLOW_CURDIR_IN_PATH=no
ALLOW_REBOOT=yes
ALLOW_REMOTE_ROOT_LOGIN=no # The remote root login by sshd is not allowed.
ALLOW_ROOT_LOGIN=no # no chrooting and no login as superuser root allowed at the first login. Be careful: in the case of LUKS-encryption, a rescue system needs LUKS resp. cryptsetup to set this variable to "yes" again. Soon, after configuring Linfw3 the right way and considering other points of the following, there is at our knowledge no login from outside possible, even if the passwords are known, in the worst case only a very restricted access on unimportant data!
ALLOW_SUDO_TO_WHEEL=no
ALLOW_USER_LIST=no
ALLOW_XAUTH_FROM_ROOT=no
ALLOW_XSERVER_TO_LISTEN=no
ALLOW_X_CONNECTIONS=no
AUTHORIZE_SERVICES=no
BASE_LEVEL=secure
CHECK_CHKROOTKIT=yes
CHECK_FIREWALL=manual
CHECK_GROUPS=yes
CHECK_ON_BATTERY=no
CHECK_OPEN_PORT=no
CHECK_PASSWD=yes
CHECK_PERMS=daily
CHECK_PERMS_ENFORCE=yes
CHECK_PROMISC=manual
CHECK_RPM_INTEGRITY=manual
CHECK_RPM_PACKAGES=manual
CHECK_SECTOOL=manual
CHECK_SECTOOL_LEVEL=4
CHECK_SECURITY=yes
CHECK_SGID=yes
CHECK_SHADOW=yes
CHECK_SHOSTS=manual
CHECK_SUID_MD5=yes
CHECK_SUID_ROOT=yes
CHECK_UNOWNED=yes
CHECK_USERS=yes
CHECK_USER_FILES=manual
CHECK_WRITABLE=yes
CREATE_SERVER_LINK=no
ENABLE_AT_CRONTAB=yes
ENABLE_CONSOLE_LOG=no
ENABLE_DNS_SPOOFING_PROTECTION=yes
ENABLE_IP_SPOOFING_PROTECTION=yes
ENABLE_LOG_STRANGE_PACKETS=yes
ENABLE_MSEC_CRON=yes
ENABLE_PAM_ROOT_FROM_WHEEL=no
ENABLE_PAM_WHEEL_FOR_SU=yes
ENABLE_PASSWORD=yes
ENABLE_STARTUP_MSEC=yes
ENABLE_STARTUP_PERMS=enforce
ENABLE_SULOGIN=no
EXCLUDE_REGEXP="*root* *.gpg *.asc"
FIX_UNOWNED=yes
IGNORE_PID_CHANGES=no
LOG_RETENTION=4
MAIL_EMPTY_CONTENT=no
MAIL_USER=root
MAIL_WARN=no
NOTIFY_WARN=yes
PASSWORD_HISTORY=4
PASSWORD_LENGTH=8,1,1
ROOT_UMASK=077
SECURE_TMP=no
SHELL_HISTORY_SIZE=100
SHELL_TIMEOUT=600
SYSLOG_WARN=yes
TTY_WARN=yes
USER_UMASK=077
WIN_PARTS_UMASK=077
/etc/rc.local sh /etc/rc.local out of any runlevel-init-script within /etc/init.d/:
#!/bin/sh
#
### BEGIN INIT INFO
# 1 SSD-Optimization
hdparm -W1a0A0 /dev/sda
echo deadline> /sys/block/sda/queue/scheduler
echo 500> /proc/sys/vm/dirty_writeback_centisecs
echo 20> /proc/sys/vm/dirty_ratio
echo 5> /proc/sys/vm/dirty_background_ratio
touch /var/lock/subsys/local
rm -df /var/spool/cups/a*
rm -df /var/spool/cups/b*
rm -df /var/spool/cups/c*
rm -df /var/spool/cups/d*
rm -df /var/spool/cups/e*
rm -df /var/spool/cups/f*
rm -df /var/spool/cups/g*
rm -df /var/spool/cups/h*
rm -df /home/surfuser/.xauth*
rm -df /home/toruser/.xauth*
rm -df /home/user/kde4/share/apps/kmail/mail/Spam/cur/*
# 2 Services
# sh /etc/init.d/incrond start # IDS Intrusion Detection Access Detection
# sh /etc/init.d/noflushd start
# gpg-agent --daemon --use-standard-socket
sh /etc/init.d/syslog start
sh /etc/init.d/xfs start
#sh /etc/init.d/psad start
# dhclient -4 -cf /etc/dhcp/dhclient.conf eth0 &
# artsd&
# acpid&
# /usr/lib64/apparmorapplet&
# apparmor-dbus&
# killall plymouthd
# 3 securityfs
mount -t securityfs -o rw,noatime /sys/kernel/security /mnt2
# 4 apparmor - protection shield for kernel, dbus and apps
#apparmor_parser -af /etc/apparmor/profiles/extras/usr.lib.firefox.firefox &
#apparmor_parser -af /etc/apparmor/profiles/extras/sbin.dhclient &
#apparmor_parser -af /etc/apparmor/profiles/extras/usr.bin.man &
#apparmor_parser -af /etc/apparmor/profiles/extras/usr.bin/passwd &
#apparmor_parser -af /etc/apparmor/profiles/extras/usr.lib.firefox.sh &
# 5 msec (MCC) - security options
echo "ALLOW_REBOOT=yes"
echo "BASE_LEVEL=secure">> /etc/security/msec/security.conf
echo "ENABLE_STARTUP_MSEC=yes"> /etc/security/msec/security.conf
echo "ENABLE_STARTUP_PERMS=enforce"> /etc/security/msec/security.conf
msec -f secure
# 6 ACL for X-Windows
xhost -
xhost +si:localuser:user
xhost -si:localuser:root
xhost -si:localuser:toruser
xhost -si:localuser:surfuser
xhost -inet6:user@
xhost -nis:user@
xhost - 192.168.178.1
exit
All xhost commends can be placed in /etc/rc.local, but "man xhost" recommends to store them in a file to create named /etc/X0.hosts :
"The initial access control list for display number n may be set by the file /etc/Xn.hosts, where n is the display number of the server. See Xserver(1) for details."
Unixboard.de: "Take care, that system-user do not have a shell anymore( so set all system-user including mysql, uuid and the actual user, but (almost) without user root (for root el6 waits until year 2026) and without our user named surfuser in /etc/passwd from /bin/bash to /sbin/nologin, /sbin/false resp. /usr/bin/rssh, comment by Gooken. Notice: Terminals do not work anymore except konsole reserved in /etc/fstab and the six screen-terminals before each login CTRL+ALT+F1-F6+F7; konsole still enables the login as superuser root). Install the hardened-packages, secure up server-tools correctly and care for those service only accessable from outside, that ought to be. Set correct limits in limits.conf, patch the kernel with a Stack-Smashing-Guard and the system is secured up well. If you are entirely paranoid, also use an IDS filtering out the unwanted taffict (for examle the traffic including the NOPs or shell-codes not corresponding to the meant protocol and so on). Then, Tripwire or AIDE help to notice all changes within the file-sytem and to perform regular checks of files. SSH-Login should be restricted to key-authentification and with ACLs (SELinux, tomoyo or acl, cmt. by Gooken) it is possible, that user can only view the files they are using. Temporary-directories (not only) of the webservers should be mounted by option noexec (to add in /etc/fstab, cmt. by Gooken), so that no programs can be let through and installed with the help of the webserver, even if allowed by CGI-script-errrors making it possible. CGI-scripts should never have access on files outside the document-root, one should know, what is task of the scripts. Use skipfish to detect directory-traversal-access-points and similiar typical access-points, bevor such scripts are provided on the server. Now a server is secured-up well. As long as Linux-kernel consists of new lacks in security, Linux will never be secure on the computer. Therefore fast updating makes up the security for server.
If a hacker can access a shell, the situation is lost. Then even a chroot-environment does not help. This is not worth the trouble. Use the standards for securing up server.
Of course a direct root-login via ssh should be impossible. One can not exclude the case like user loosing ssh-keys. This should be no reason, to go on with bruteforce-methods like a passoword-login via ssh, if you are such paranoid.
Apart from that I do not know any true and honest webshoster providing a shell for his user. Such hoster forbidding shell-accounts amost use a restricted shell only enpossibles the start of certain commands. Access-rights within the file-system are performed by ACLs. Going sure, that webscripts can not access system directories, the webserver-process should be chrooted, but not all user. This process can be run in within a VM, from where it is more difficult to break out than by chroot. Alternatively use SELinux and restrict the access-rights by roles. Doing so, you can simply care for webserver not starting any programs. This is, what it is made for.
[...] One more addditions to the helpful hints from bitmuncher: One oppportunity for isolaiton is provided by OpenVZ. This makes it possible to set a virtual instance each user. [...]. For example for webhosting, using a reverse proxy for the server would make sense. The advanage is, that n+1 Webserver have to be started and run. If done by Apache or a more light-weighted alternative, this is the other question. At the moment, I use lighttpd + fastCGI PHP, where PHP-Instances are running with their own user. Of course, Apache manages this too. And I am more with the configuration of Apache."
http://www.unixboard.de/threads/linux-kernsystem-absichern-durch-chroots-und-gute-rechtevergabe.46522/
 All system and user accounts should have a password. Set it, if not and All system and user accounts should have a password. Set it, if not and
 many, if not most (unneeded) accounts ( within /etc/passwd ) can be locked. Do so by terminal-command or MCC->System-> User-Administration -> Edit an account -> lock the account except for user root, surfuser and toruser: many, if not most (unneeded) accounts ( within /etc/passwd ) can be locked. Do so by terminal-command or MCC->System-> User-Administration -> Edit an account -> lock the account except for user root, surfuser and toruser:
passwd -l user
resp.
passwd -u user
with Option -l for lock and -u for unlock. Depending on the pam.d-configuration the user named "user" can be locked too, if he always gets automatically logged into KDE, what can be configured by the login manager. Then an unlocking of the screenlock gets impossible for user.
cat /etc/passwd (be a little bit careful with these settings, cups for your printer might not work anymore): nano /etc/passwd respective,after the root-login got locked too by /sbin/nologin, "user account administration" out of MCC (the system-configuration) enpossibles the following configuration of the shell-logins each user (if not locked, in this case: additionally and optionally)::
 Now all accounts depending on pamd and an automized desktop login including (!) the normal user, in our example toruser, except surfuser should be passwort-protected and locked and be associated with the login /sbin/nologin. Lock him by clicking upon user administration of MCC, clicking upon it to set the belonging hook. Before the Tor-browser can be used for anonymous surfing with Tor, the login for the toruser-account has to be reset to /bin/bash.
Now all accounts depending on pamd and an automized desktop login including (!) the normal user, in our example toruser, except surfuser should be passwort-protected and locked and be associated with the login /sbin/nologin. Lock him by clicking upon user administration of MCC, clicking upon it to set the belonging hook. Before the Tor-browser can be used for anonymous surfing with Tor, the login for the toruser-account has to be reset to /bin/bash.
root:x:0:0:root:/root:/sbin/nologin # "Sanked terminal-root-login": olala, the right pam.d-configuration makes it possible, ... what an important contribute to security! Notice: Now a reset to /bin/bash again can only be made by the user-administration of MCC or booted Rescue-USB-Stick and so on after a mount and reset to /bin/bash within this configuraton file.
toruser:x:506:504:torgroup:/home/toruser:/sbin/nologin # to use tor-browser, reset last value from /sbin/nologin to /bin/bash. Do so for tor-browser and eventulally other processes resp. programs going online except ftp-clients (ftp, sftp, ..) and the browser, that should still start for user surfuser and group surfgroup. For the other processes, additionally use firejail with option shell none (of the configuation-file within /etc/firejail). Notice, that such settings for the shell-access for different user should be made by MCC (system-configuration) within the user-administration, as they can not be done in each by terminal in each case.
How the onion-router and anonymizing browser Tor with belonging account has to be installed and configured under Linfw3, is described here (please click here).
bin:x:1:1:bin:/bin:/sbin/nologin
-1:x:-1::::/sbin/nologin # block all unknown user (and buggish programs. If the computer should have ever slown down, this was the cause!)
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/sbin/nologin
shutdown:x:6:0:shutdown:/sbin:/sbin/nologin
halt:x:7:0:halt:/sbin:/sbin/nologin
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
news:x:9:13:news:/var/spool/news:/sbin/nologin
uucp:x:10:14:uucp:/var/spool/uucp:/sbin/nologin
operator:x:11:0:operator:/var:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
nobody:x:65534:65534:Nobody:/sbin/nologin
polkituser:x:16:16:system user for policykit:/sbin/nologin
haldaemon:x:17:17:system user for hal:/sbin/nologin
user:x:501:501:user:/home/user:/sbin/nologin
mysql:x:71:71:system user for mysql:/var/lib/mysql:/sbin/nologin
clamav:x:72:72:system user for clamav:/var/lib/clamav:/sbin/nologin
surfuser:x:500:500:surfuser:/home/surfuser:/bin/bash
uuidd:x:20:0:uuidd:/home/uuidd:/sbin/nologin
anonymous:x:510:504:anonymous:/home/anonymous:/sbin/nologin
user:10000:10000:user:/home/user:/sbin/nologin# does not work on mdv-USB-stick, so set /bin/bash
rpcuser:x:29:29:RPC Service User:/var/lib/nfs:/sbin/nologin
popa3d:x:93:93:system user for popa3d:/var/empty:/sbin/nologin
toruser:x:415:415:system user for tor:/:/sbin/nologin
openvpn:x:420:421:system user for openvpn:/var/lib/openvpn:/bin/true
ossec:x:82:114:system user for ossec-hids:/var/lib/ossec:/sbin/nologin
usbmux:x:90:90:system user for usbmuxd:/proc:/sbin/nologin
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
sync:x:5:0:sync:/sbin:/bin/sync
messagebus:x:13:101:system user for dbus:/sbin/nologin
avahi:x:14:102:system user for avahi:/var/avahi:/sbin/nologin
avahi-autoipd:x:15:103:system user for avahi:/var/avahi:/sbin/nologin
rpm:x:18:18:system user for rpm:/var/lib/rpm:/sbin/nologin
tkit:x:19:107:system user for rtkit:/proc:/sbin/nologin
vcsa:x:69:69:virtual console memory owner:/dev:/sbin/nologin
htdig:x:70:108::/var/lib/htdig:/sbin/nologin
postfix:x:73:73:system user for postfix:/var/spool/postfix:/sbin/nologin
apache:x:74:74:system user for apache-conf:/var/www:/sbin/nologin
gdm:x:75:75:system user for gdm:/var/lib/gdm:/sbin/nologin
halevt:x:76:76:system user for halevt:/var/lib/halevt:/sbin/nologin
mpd:x:77:81:system user for mpd:/var/lib/mpd:/sbin/nologin
saned:x:78:78:system user for saned:/home/saned:/sbin/nologin
squid:x:79:79:system user for squid:/var/spool/squid:/sbin/nologin
prelude-manager:x:80:112:system user for prelude-manager:/var/lib/prelude-manager:/sbin/nologin
vdr:x:81:113:system user for vdr:/var/lib/vdr:/bin/nologin
ossec:x:82:114:system user for ossec-hids:/var/lib/ossec:/sbin/nologin
dansguardian:x:83:115:system user for dansguardian:/var/lib/dansguardian:/sbin/nologin
torrent:x:84:84:system user for bittorrent:/var/lib/bittorrent:/sbin/nologin
mythtv:x:85:85:system user for mythtv:/var/lib/mythtv:/sbin/nologin
freevo:x:86:86:system user for freevo:/usr/share/freevo:/sbin/nologin
gnump3d:x:87:87:system user for gnump3d:/var/cache/gnump3d:/sbin/nologin
partimag:x:88:117::/home/partimag:/sbin/nologin
torrent:x:84:84:system user for bittorrent:/var/lib/bittorrent:/sbin/nologin
audit:x:404:404:RSBAC security auditor:/dev/null:/sbin/nologin
firebird:x:418:418:system user for firebird:/var/lib/firebird/data:/sbin/nologin
usbmux:x:90:90:system user for usbmuxd:/proc:/sbin/nologin
asterisk:x:91:91:system user for asterisk:/var/lib/asterisk:/sbin/nologin
ups:x:92:92:system user for nut:/var/state/ups:/sbin/nologin
boinc:x:421:422:system user for boinc-client:/var/lib/boinc:/sbin/nologin
postgres:x:399:399:system user fo postgresql8.4:/var/lib/pgsql:/sbin/nologin
rrdcached:x:398:398:system user for rrdtool:/var/lib/rrdcached:/sbin/nologin
puppet:x:397:397:system user for puppet:/var/lib/puppet:/sbin/nologin
smolt:x:393:393:system user for smolt:/usr/share/smolt:/sbin/nologin
clam:x:388:498:Clam Anti Virus Checker:/var/lib/clamav:/sbin/nologin
znc:x:387:497:Account for ZNC to run as:/var/lib/znc:/sbin/nologin
toranon:x:386:496:TOR anonymizing user:/var/lib/tor:/sbin/nologin
icecast:x:385:385:icecast streaming server:/usr/share/icecast:/sbin/nologin
munge:x:383:494:Runs Uid ´N´ Gid Emporium:/var/run/munge:/sbin/nologin
nm-openconnect:x:382:493:NetworkManager user for OpenConnect:/:/sbin/nologin
zabbix:x:381:492:Zabbix Monitoring System:/var/lib/zabbix:/sbin/nologin
ident:x:98:491::/:/sbin/nologin
unbound:x:380:490:Unbound DNS resolver:/etc/unbound:/sbin/nologin
cacti:x:379:379::/usr/share/cacti:/sbin/nologin
pulse:x:378:488:PulseAudio System Daemon:/var/run/pulse:/sbin/nologin
abrt:x:173:173::/etc/abrt:/sbin/nologin
dockerroot:x:172:172:Docker User:/var/lib/docker:/sbin/nologin
amandabackup:x:33:6:Amanda user:/var/lib/amanda:/sbin/nologin
mailnull:x:47:47::/var/spool/mqueue:/sbin/nologin
smmsp:x:51:51::/var/spool/mqueue:/sbin/nologin
clam-update:x:171:483:clamav-unofficial-sigs user account:/var/lib/clamav-unofficial-sigs:/sbin/nologin
vtl:x:170:481:VTL daemon:/opt/mhvtl:/sbin/nologin
chilli:x:208:208::/usr/share/chilli:/sbin/nologin
usbmuxd:x:501:100:usbmuxd:/home/usbmuxd:/sbin/nologin
vnstat:x:207:207:vnStat user:/var/lib/vnstat:/sbin/nologin
ez-ipupd:x:201:480:Dynamic DNS Client:/var/cache/ez-ipupdate:/sbin/nologin
ricci:x:140:140:ricci daemon user:/var/lib/ricci:/sbin/nologin
qemu:x:502:100:qemu:/home/qemu:/sbin/nologin
luci:x:141:141:luci high availability management application:/var/lib/luci:/sbin/nologin
lighttpd:x:499:479:lighttpd web server:/var/www/lighttpd:/sbin/nologin
zope:x:94:94:system user for zope:/var/lib/zope/default:/sbin/nologin
fax:x:95:95:system user for mgetty:/var/spool/fax:/sbin/nologin
ntp:x:96:96:system user for openntpd:/var/empty:/sbin/nologin
secoff:x:400:400:RSBAC security officer:/secoff:/sbin/nologin
audit:x:404:404:RSBAC security auditor:/dev/null:/sbin/nologin
redis:x:505:508:redis:/home/redis:/sbin/nologin
...
/etc/security/msec/perm.secure (to be careful, overwrite all /etc/security/msec/perm.*):
directory_or_file owner.group access-rights force
chkstat of permissions (OpenSuSE 13.2) and /etc/security/msec/perm.secure (overwrite all /etc/security/msec/perm.* and activate it in /etc/rc.local by the command "msecperms -q"), but be careful, your printer might not work and no sound can be heart anymoure after the following settings. So comment "msecperms -q" in by a leading "#" and start it from terminal. Alsa might has to be restarted too.
file_or_directory user.group access-right force acl
 / root.root 0111 force
/ root.root 0111 force
/bin/ root.root 751 force
/bin/mount root.root 4755 force # ... this first cipher with 4: setuid-/setgid- resp.suid-bit for user, 2: 2xxx sgid for group, 1: 1xxxx t for other, 0: no suid-bit; suid effects the process into rights of the owner of the executed file instead those of its executing user. This might be dangerous as processes of non privliged user can achieve dangerous more priviligues. Therefore such suid-files are aimed for attacks. More details, see "man chmod" In the last row, acl for other user, groups and other can also be set following the command setfacl, details see man setfacl, https://wiki.ubuntuusers.de/ACL/ and the explanation in msec-gui for access-rights, short example: setfacl -m u:user1:- directory_or_file1,g:group1:r-x directory_or_file2,.u:... Masks can also be set. Set acl are shown in the listing of a directory or directory-contents by a "+" behind the access-rights. For this do not forget the activation by opton acl for the root partition in /etc/fstab.
/bin/umount root.root 4755 force
/boot/ root.root 710 force
/root root.root 700 force
/dev root.root 751 force
/etc/ root.root 751 force
/etc/fstab root.root 644 force
/etc/init.d root.root 700 force # chmod 700 -R /etc/init.d
/etc/init.d/functions root.root 600 force
/etc/init.d/* root.root 700 force
/etc/rc*.d root.root 700 force
/etc/passwd root.root 644 force
/etc/shadow root.root 400 force
/home/ root.root 711 force
/home/user/usr root.root 700 force
/home/user/usr/* root.root 700 force
/home/user/.a* user.user 700 force
/home/user/.b* user.user 700 force
/home/user/.d* user.user 700 force
/home/user/.e* user.user 700 force
/home/user/.f* user.user 700 force
/home/user/.g* user.user 700 force
/home/user/.h* user.user 700 force
/home/user/.i* user.user 700 force
/home/user/.j* user.user 700 force
/home/user/.k* user.user 700 force
/home/user/.l* user.user 700 force
/home/user/.m* user.user 700 force
/home/user/.n* user.user 700 force
/home/user/.o* user.user 700 force
/home/user/.p* user.user 700 force
/home/user/.q* user.user 700 force
/home/user/.r* user.user 700 force
/home/user/.s* user.user 700 force
/home/user/.u* user.user 700 force
/home/user/.v* user.user 700 force
/home/user/.w* user.user 700 force
/home/user/.x* user.user 700 force
/home/user/.y* user.user 700 force
/home/user/.z* user.user 700 force
/home/user/a* user.user 700 force
/home/user/b* user.user 700 force
/home/user/d* user.user 700 force
/home/user/e* user.user 700 force
/home/user/f* user.user 700 force
/home/user/k* user.user 700 force
/home/user/l* user.user 700 force
/home/user/m* user.user 700 force
/home/user/M* user.user 700 force
/home/user/n* user.user 700 force
/home/user/N* user.user 700 force
/home/user/o* user.user 700 force
/home/user/.kde4/share user.user 500 force
/home/user/.kde4 user.user 500 force
/home/user/.kde4/share/apps user.user 700 force
/home/user/.kde4/share/apps/kmail user.user 700 force
/home/user/.kde4/share/apps/kmail/mail user.user 700 force
/home/user/.kde4/share/apps/kmail/mail/* user.user 700 force
/home/user/.kde4/share/apps/kmail/mail/inbox user.user 700 force
/home/user/.kde4/share/apps/kmail/mail/inbox/* user.user 700 force
/home/user/.kde4/share/apps/kmail/mail/outbox/* user.user 700 force
/home/user/Dokumente user.user 700 force
/home/surfuser surfuser.surfuser 700 force
/home/surfuser/.mozilla surfuser.surfuser 300 force
/home/surfuser/.mozilla/* surfuser.surfuser 700 force
/home/surfuser/JAP* surfuser.surfuser 400 force
/include root.root 751 force
/lib/ root.root 751 force
/lib64 root.root 751 force
/media root.root 711 force
/mnt/ root.root 750 force
/opt root.root 751 force
/proc root.root 555 force
/sbin/ root.root 751 force
/sbin/init root.root 750 force
/sbin/udevd root.root 750 force
/sys root.root 751 force
/sys/* root.root 751 force
/tmp/ root.root 1777 force
/usr root.root 751 force
/usr/* root.root 755 force
/usr/bin/ping root.root 0755 force
/usr/bin/rlogin root.root 4755 force
/usr/bin/cc root.root 750 force
/usr/bin/finger root.root 750 force
/usr/bin/g++* root.root 750 force
/usr/bin/gcc* root.root 750 force
/usr/bin/kdm root.root 750 force
/usr/bin/ssh root.root 750 force
/usr/bin/telnet root.root 750 force
/usr/bin/users root.root 750 force
/usr/bin/w root.root 750 force
/usr/bin/who root.root 750 force
/usr/bin/gpasswd root.shadow 0755 force
/usr/bin/passwd root.shadow 0755 force
/usr/bin/rlogin root.root 0750 force
/usr/bin/uucp uucp.uucp 6555 force
/usr/bin/uustat uucp.uucp 6555 force
/usr/bin/newrole root.root 0755 force
/usr/bin/uux uucp.uucp 6555 force
/usr/bin/rsh root.root 0700 force
/usr/bin/chfn root.shadow 0700 force
/usr/bin/chage root.shadow 0700 force
/usr/bin/chsh root.shadow 0700 force
/usr/bin/v4l-conf root.video 0755 force
/usr/bin/wall root.tty 0755 force
/usr/bin/write root.tty 0755 force
/usr/games root.root 751 force
/usr/include root.root 751 force
/usr/etc root.root 751 force
/usr/java root.root 751 force
/usr/lib64 root.root 751 force
/usr/lib64/kde4/libexec/kcheckpass root.shadow 4755 force
/usr/lib64/kde4/libexec/kdesud root.nogroup 2755 force
/usr/lib64/kde4/libexec/start_kdeinit root.root 4755 force
/usr/lib root.root 751 force
/usr/lib/cups root.root 775 force
/usr/lib/cups/filter root.root 775 force
/var/spool/cups root.sys 711 force
/var/cache/cups root.sys 775 force
/usr/libexec/rtkit-daemon root.root 750 force
/usr/libexec/polkit-1/polkitd root.root 750 force
/usr/libexec/postfix/master root.root 750 force
/usr/man root.root 751 force
/usr/share/docs root.root 755 force
/usr/libexec root.root 751 force
/usr/local root.root 751 force
/usr/local/bin root.root 751 force
/usr/src root.root 700 force
/usr/src/rpm root.root 700 force
/usr/src/rpm/SOURCES root.root 700 force
/usr/src/* root.root 700 force
/usr/share root.root 751 force
/usr/share/* root.root 755 force
/usr/sbin/ root.root 751 force
/usr/sbin/mtr root.dialout 0750 force
/usr/sbin/lockdev root.lock 2755 force
/usr/sbin/pppoe-wrapper root.dialout 4750 force
/usr/sbin/chroot root:root 4700 force
/usr/sbin/gpm root.root 750 force
/usr/sbin/init root.root 750 force
/usr/sbin/sendmail.postfix root.root 711 force
/usr/sbin/prelink root.root 750 force
/usr/sbin/mingetty root.root 750 force
/usr/share/doc root.root 755 force
/usr/share/man root.root 755 force
/usr/ssl root.root 751 force
/usr/tmp root.root 1777 force
/usr/uclibc root.root 751 force
/usr/X11R6 root.root 751 force
/var/tmp root.root 1777 force
/etc/rc.d/init.d/ root.root 700 force
/etc/rc.d/init.d/* root.root 700 force
/etc/shutdown.allow root.root 640 force
/etc/sysconfig root.root 755 force
/etc/syslog.conf root.root 640 force
/etc/updatedb.conf root.root 644 force
/etc/printcap root.lp 640 force
/bin/ping root.root 4750 force
/bin/rpm rpm.rpm 750 force
/dev/ root.root 751 force
/etc/conf.modules root.root 640 force
/etc/cron.daily/ root.root 750 force
/etc/cron.hourly/ root.root 750 force
/etc/cron.monthly/ root.root 750 force
/etc/cron.weekly/ root.root 750 force
/etc/crontab root.root 640 force
/etc/dhcpcd/ root.root 750 force
/etc/dhcpcd/* root.root 640 force
/etc/ftpaccess root.root 640 force
/etc/ftpconversions root.root 640 force
/etc/ftpgroups root.root 640 force
/etc/ftphosts root.root 640 force
/etc/ftpusers root.root 640 force
/etc/gettydefs root.root 640 force
/etc/hosts.allow root.root 644 force
/etc/hosts.deny root.root 644 force
/etc/hosts.equiv root.root 640 force
/etc/httpd/modules.d/*.conf root.root 640 force
/etc/httpd/conf/*.conf root.root 640 force
/etc/httpd/conf/addon-modules/* root.root 640 force
/etc/httpd/conf/vhosts.d/* root.root 640 force
/etc/httpd/conf/webapps.d/* root.root 640 force
/etc/init.d root.root 700 force
/etc/init.d/* root.root 700 force
/etc/inetd.conf root.root 640 force
/etc/inittab root.root 640 force
/etc/ld.so.conf root.root 640 force
/etc/mandrake-release root.root 644 force
/etc/modules.conf root.root 640 force
/etc/motd root.root 644 force
/etc/rc.d/ root.root 700 force
/etc/rc.d/init.d/functions root.root 600
/etc/rc.d/init.d/mandrake_consmap root.root 644
/etc/rc.d/init.d/xprint root.root 700
/etc/securetty root.root 640
/etc/security root.root 700 force
/etc/security/msec root.root 500 force
/etc/security/msec/* root.root 500 force
/etc/sendmail.cf root.root 640 force
/etc/ssh/ssh_config root.root 644 force
/etc/ssh/ssh_host_*key root.root 600 force
/etc/ssh/ssh_host_*key.pub root.root 644 force
/etc/ssh/sshd_config root.root 640 force
/etc/X11 root.root 710 force
/etc/X11/xorg.conf root.root 400 force
/etc/shadow root.shadow 0640 force
/etc/hosts root.root 0644 force
/etc/hosts.allow root.root 0644 force
/etc/hosts.deny root.root 0644 force
/etc/hosts.equiv root.root 0644 force
/etc/ld.so.conf root.root 0644 force
/etc/ppp/ root.dialout 0750 force
/etc/ssh/ssh_host_rsa_key root.root 0600 force
/etc/ssh/ssh_host_rsa_key.pub root.root 0644 force
/usr/sbin/traceroute root.root 0755 force
/etc/crontab root.root 0600 force
/etc/ftpusers root.root 0644 force
/etc/syslog.conf root.root 0600 force
/bin/ping root.root 4750 force
/home/* current.current 751
/usr/lib/rpm/rpm? rpm.rpm 750 force
/usr/sbin/sendmail.sendmail root.root 2711
/usr/sbin/traceroute root.root 4750 force
/var/ root.root 751 force
/var/lib/rpm/Packages rpm.rpm 640 force
/var/lib/pcp/tmp root.root 0755 force
/var/lib/pcp/tmp/pmlogger root.root 0755 force
/var/lib/pcp/tmp/pmie/ root.root 0755 force
/var/lock/subsys root.root 750 force
/var/log/ root.root 751 force
/var/log/* root.root 640 force
/var/log/btmp root.utmp 600 force
/var/log/wtmp root.utmp 664 force
/var/log/Xorg.0.log root.root current
/var/log/lp-errs lp.lp 600 root
/var/log/*/* root.root 600 force
/var/log/*/*/* root.root 600 force
/var/log/*/. root.root 700 force
/var/log/*/*/. root.root 700 force
/var/log/intraline/. root.root 750 force
/var/log/mailman/ root.root 2770 force
/var/log/mailman/* root.root 660 force
/var/log/ConsoleKit root.root 751 force
/var/log/ConsoleKit/history root.root 644 force
/var/log/squid squid.root 0750 force
/var/spool root.root 0755 force
/var/spool/mqeue root.root 0700 force
/var/spool/news news:news 0755 force
/var/spool/uucp uucp:uucp 0755 force
/var/spool/mail root.root 1777 force
/var/cache/man root.root 1777 force
/var/log/lastlog root.root 0644 force
/var/log/lastlog root.root 0644 force
/var/log/faillog root.root 000 force
/var/log/wtmp root.utmp 0664 force
/var/log/btmp root.root 0600 force
/var/run/utmp root.utmp 0664 force
/var/spool root.root 0755 force
/var/www root.root 751 force
/bin root.root 751 force
/sbin root.root 751 force
/srv root.root 751 force
/sys root.root 751 force
/lib root.root 751 force
/lib64 root.root 751 force
/etc root.root 751 force
/proc root.root 555 force
/secoff root.root 710 force
/var root.root 711 force
/misc root.root 710 force
/media root.root 755 force
/opt root.root 711 force
/mnt root.root 755 force
/dev/ root.root 751 force
/dev/zero root.root 666 force
/dev/null root.root 666 force
/dev/full root.root 666 force
/dev/ip root.root 660 force
/dev/initrd root.disk 660 force
/dev/kmem root.kmem 640 force
/etc/opiekeys root.root 600 force
/etc/ppp/ root.dialout 750 force
/etc/ppp/chap-secrets root.root 600 force
/etc/ppp/pap-secrets root.root 600 force
/etc/sysconfig/network/providers/ root.root 700 force
/usr/sbin/utempter root.utmp 2755 force
/usr/lib/utempter/utempter root.utmp 2755 force
/etc/ssh/ssh_host_key root.root 600 force
/etc/ssh/ssh_host_key.pub root.root 644 force
/etc/ssh/ssh_host_dsa_key root.root 600 force
/etc/ssh/ssh_host_dsa_key.pub root.root 644 force
/etc/ssh/ssh_host_rsa_key root.root 600 force
/etc/ssh/ssh_host_rsa_key.pub root.root 644 force
/etc/ssh/ssh_config root.root 644 force
/etc/ssh/sshd_config root.root 640 force
/usr/bin/suidperl root.root 755 force
/usr/sbin/papd root.lp 0755 force
/var/games/ root.root 0755 force
/usr/bin/ziptool root.root 0750 force
/lib/udev/devices/net/tun root.root 0666 force
/lib/udev/devices/null root.root 0666 force
/lib/udev/devices/ptmx root.tty 0666 force
/lib/udev/devices/tty root.tty 0666 force
/lib/udev/devices/zero root.root 0666 force
/var/lib/named/dev/null root.root 0666 force
/var/lib/named/dev/random root.root 0666 force
/usr/bin/opiesu root.root 0755 force
/usr/bin/wodim root.root 0755 force
do nothing set within: /var/spool (the mouse-pointer can stand still; thats because of postfix noticing changing owner-rights) ...
ACL: setfacl (for setfacl, alternatively resp. additionally set configuration files of sandbox firejail within /etc/firejail/. While ACL-rules (setfacl) refer to a user or a group, configuration files of firejail almost refer to programs and MAC like Tomoyo to domains (resp. processes). We recommend all, but especially ACL. For ACL the mount-option acl and user_xattr have to be set in /etc/fstab for the belonging partition.
Insert an ACL by the command "setfacl -m u:anyuser:access-rights with access-rights out of rwx- and delete an ACL by the command "setfacl -x a_user path_to_directory_or_file". Here are our recommended ACLs to build up a most secure system:
Set setfacl -m u:surfuser:- within /usr/bin onto all files except executables (setfacl -x surfuser /usr/bin/executable):
bash*
dbus*
firejail*
firefox*
gftp*
X*
kde*
konqueror*
knemo*
sg*
and all other programs (exectuables resp. commands out of /usr/bin/) together wie alls commands they also need, that should be started by surfuser. Resign from dbus*, if Konqueror is not needed for the surfing. Do the same with some care within /bin, /sbin/, /usr/sbin and /usr/libexec and so on - but never within the libraries ( /lib, /usr/lib64/, ...)..
For such all other programs like tor and tor-browser, xchat and so on think about one more surfuser like toruser belonging to the group like torgroup..Do not restrict toruser that serious hard like surfuser, as the Tor-Browser (Tor) needs a lot of access-rights, but you can run Tor (Tor-Browser) within an own sandbox (see section configuration of Tor)..
In other words (but notice, that setfacl for surfuser within /usr/bin have been made already in the configuration right above):
Now we obtain a linfw3 perfectly completing, allround-protection for the computer performing, totally securing sandbox upon quit all directories and files Linux provides without restricting program executions. Notice, that you have to set the ACL-rights again for overwritten executable files within /bin, /sbin, /usr/bin, /usr/sbin, /usr/share/ and /usr/libexec following past each (rpm-/deb-/Tarball-) reinstallation and -update. ACL for samba, httpd and other server are missing, so they still have to be added:
 setfacl -m u:surfuser:- /usr/libexec/gam_server # One brake less...; also exchange gamin (mdv2010) with gamin (fc29, pclos2017) and copy /usr/libexec/gam_server to /usr/lib/
setfacl -m u:surfuser:- /usr/libexec/gam_server # One brake less...; also exchange gamin (mdv2010) with gamin (fc29, pclos2017) and copy /usr/libexec/gam_server to /usr/lib/
setfacl -m u:surfuser:- /usr/libexec/gam_server
setfacl -m u:toruser:- /usr/libexec/gam_server
setfacl -m u:root:- /usr/libexec/gam_server
setfacl -m u:surfuser:- /usr/lib/gam_server
setfacl -m u:toruser:- /usr/lib/gam_server
setfacl -m u:root:- /usr/lib/gam_server
setfacl -m u:root:- /usr/libexec/gam_server
setfacl -m u:-1:- /usr/libexec/gam_server # -1: all unknown user
setfacl -m u:surfuser:- /usr/lib/gam_server # for gamin-server (fc26, OpenSuSE 13.2 and so on) ...
setfacl -m u:root:- /usr/lib/gam_server #
setfacl -m u:-1:- /usr/lib/gam_server #
setfacl -m u:user:- /usr/bin/nspluginscan* # ... one more brake less
setfacl -m u:user:- /usr/bin/application-browser* # ... and once more a brake less
setfacl -m u:surfuser:- /usr/bin/nspluginscan*
setfacl -m u:surfuser:- /usr/bin/application-browser*
setfacl -m u:surfuser:- /boot # if not already set to read-only (ro)
setfacl -m u:user:- /boot # if not already set to read-only (ro)
setfacl -m u:surfuser:- /*
setfacl -m u:toruser:- /mnt # Tor-Browser
setfacl -m u:toruser:- /media
setfacl -m u:toruser:- /home/user
setfacl -m u:toruser:- /home/surfuser
 setfacl -m u:toruser:- /usr/bin/su setfacl -m u:toruser:- /usr/bin/su
setfacl -m u:toruser:- /bin/su
setfacl -m u:toruser:- /bin/mount
setfacl -m u:toruser:- /usr/bin/mount
setfacl -m u:toruser:- /usr/bin/rsh
setfacl -m u:toruser:- /usr/bin/rlogin
setfacl -m u:toruser:- /usr/bin/ssh
setfacl -m u:toruser:- /bin/ssh # and to not forget to use firejail with option "shell none" before starting processes by toruser
setfacl -m u:toruser:- /opt
setfacl -m u:toruser:- /sbin
setfacl -m u:toruser:- /usr/local
setfacl -m u:toruser:- /etc/fstab*
setfacl -m u:toruser:- /etc/mtab*
setfacl -m u:toruser:- /etc/crypttab*
setfacl -m u:toruser:- /usr/libexec/gam_server
setfacl -m u:toruser:- /usr/bin/knotify*
setfacl -m u:toruser:- /usr/bin/nspluginscan*
setfacl -m u:toruser:- /usr/libexec/mysql*
setfacl -m u:toruser:- /usr/bin/mysql*
setfacl -m u:toruser:- /etc/shadow*
setfacl -m u:surfuser:--x /home/surfuser
setfacl -m u:surfuser:--x /usr/bin
setfacl -m u:surfuser:- /usr/sbin/*
setfacl -x surfuser /usr/sbin/dnsmasq
setfacl -x surfuser /usr/sbin/unbound
setfacl -m u:surfuser:--x /bin
setfacl -m u:surfuser:--x /sbin
setfacl -m u:surfuser:--x /usr/games
setfacl -m u:surfuser:--x /usr/lib64
setfacl -m u:surfuser:--x /lib64
setfacl -m u:surfuser:--x /usr/libexec
setfacl -m u:surfuser:--x /lib/modules
setfacl -m u:surfuser:--x /lib
setfacl -m u:surfuser:--x /home
setfacl -x surfuser /bin
setfacl -x surfuser /etc
setfacl -x surfuser /sbin
setfacl -m u:surfuser:r-x /lib64
setfacl -x surfuser /home
setfacl -x surfuser /run
setfacl -x surfuser /tmp
setfacl -x surfuser /proc
setfacl -x surfuser /secoff
setfacl -x surfuser /dev
setfacl -x surfuser /current
setfacl -m u:surfuser:- /bin/*
setfacl -m u:surfuser:- /bin/*
setfacl -x surfuser /bin/arch #
setfacl -x surfuser /bin/basename #
 setfacl -x surfuser /bin/bash setfacl -x surfuser /bin/bash
setfacl -x surfuser /bin/grep* # you might block it too
setfacl -x surfuser /bin/cp # try to disable cp too
setfacl -x surfuser /bin/cut #
setfacl -x surfuser /bin/mktemp #
setfacl -x surfuser /bin/ps #
setfacl -x surfuser /bin/sed # sed might be needed
setfacl -x surfuser /bin/sort #
setfacl -x surfuser /bin/uname # or keep uname blocked
setfacl -x surfuser /bin/hostname #
setfacl -m u:surfuser:- /bin/su
setfacl -m u:surfuser:- /usr/bin/su
setfacl -m u:surfuser:- /usr/libexec/mysql*
setfacl -m u:root:r-x /etc/resolv.conf # after configuration of dnsmasq
setfacl -m u:surfuser:- /mnt # standard mount-point
 setfacl -m u:surfuser:- /media # block access to USB-memory-sticks and so on setfacl -m u:surfuser:- /media # block access to USB-memory-sticks and so on
setfacl -m u:user:- /home/surfuser
setfacl -m u:surfuser:- /home/user
setfacl -m u:surfuser:- /home/user/.kde4/share/apps/kmail/mail
setfacl -m u:root:- /home/user
setfacl -m u:root:- /home/surfuser
setfacl -m u:surfuser:- /home/uuid*
setfacl -m u:root:- /home/user/.wine
setfacl -m u:root:- /home/surfuser/.wine
setfacl -m u:surfuser:- /home/surfuser/.gnupg
setfacl -m u:surfuser:- /home/user/.gnupg
setfacl -m u:surfuser:- /etc/*
setfacl -x surfuser /etc/acpi*
setfacl -x surufser /etc/alternatives*
setfacl -x surufser /etc/alternatives/java*
setfacl -x surfuser /etc/bash*
setfacl -x:surfuser /etc/cups
setfacl -x surfuser /etc/default*
setfacl -x surfuser /etc/dbus*
setfacl -x surfuser /etc/dnsmasq*
setfacl -x surfuser /etc/firejail*
setfacl -x surfuser /etc/firefox*
setfacl -x surfuser /etc/firebird*
setfacl -x surfuser /etc/font*
setfacl -m u:user:r-x /etc/fstab
setfacl -x surfuser /etc/ld.so*
setfacl -x surfuser /etc/nsswitch*
setfacl -x surfuser /etc/profile*
setfacl -x surfuser /etc/pam*
setfacl -x surfuser /etc/pango*
setfacl -x surfuser /etc/passwd*
setfacl -x surfuser /etc/services*
setfacl -x surfuser /etc/tor*
setfacl -x surfuser /etc/host*
setfacl -m u:surfuser:r-x /etc/resolv.conf
setfacl -x surfuser /etc/resolv.dnsmasq*
setfacl -m u:surfuser:- /sbin
setfacl -m u:surfuser:- /usr/sbin
setfacl -m u:user:- /usr/lib64/firefox
setfacl -m u:user:- /usr/lib64/thunderbird
setfacl -m u:surfuser:- /usr/local # oder
setfacl -m u:surfuser:- /usr/local/LINFW3
setfacl -m u:surfuser:- /usr/lib/modules*
setfacl -m u:surfuser:- /root
setfacl -m u:surfuser:- /initrd
setfacl -m u:surfuser:- /srv
setfacl -m u:surfuser:- /smack
setfacl -m u:surfuser:- /net
setfacl -m u:surfuser:- /misc
setfacl -m u:surfuser:- /var/lib/rpm
setfacl -m u:surfuser:- /opt
setfacl -m u:surfuser:- /secoff
setfacl -m u:surfuser:- /sid-root
setfacl -m u:surfuser:- /cgroup
setfacl -m u:surfuser:- /lost+found
setfacl -m u:surfuser:- /sbin
ssetfacl -m u:surfuser:r-x /lib64
setfacl -m u:surfuser:- /lib
setfacl -m u:surfuser:- /usr/*
setfacl -x surfuser /usr/lib
setfacl -x surfuser:r-x /usr/lib64
setfacl -x surfuser /usr/bin
setfacl -x surfuser /usr/libexec
setfacl -x surfuser /usr/share
setfacl -x surfuser /usr/ssl
setfacl -x surfuser /usr/tmp
setfacl -x surfuser /usr/var
etfacl -m u:surfuser:- /usr/src
setfacl -m u:surfuser:- /usr/sbin
setfacl -x surfuser /usr/sbin/traceroute*
setfacl -m u:surfuser:r-x /usr/lib
setfacl -m u:surfuser:r-x /usr/lib64/kde4
setfacl -m u:surfuser:rwx /usr/lib64/tor-browser # sandboxed tor-browser for chown -R surfuser:surfuser -R /usr/lib64/tor-browser
setfacl -m u:surfuser:- /usr/libexec # miroplayer. setfacl -m u:surfuser:r-x /usr/libexec
setfacl -m u:surfuser:- /usr/share/* ##
setfacl -x surfuser /usr/share/app*
setfacl -x surfuser /usr/share/font*
setfacl -x surfuser /usr/share/cups*
setfacl -x surfuser /usr/share/freetuxtv*
setfacl -x surfuser /usr/share/gnome-translate*
setfacl -x surfuser /usr/share/gftp*
setfacl -x surfuser /usr/share/gvfs*
setfacl -x surfuser /usr/share/icon*
setfacl -x surfuser /usr/share/java*
setfacl -x surfuser /usr/share/konqueror*
setfacl -x surfuser /usr/share/locale*
setfacl -x surfuser /usr/share/miro*
setfacl -x surfuser /usr/share/merkaartor*
setfacl -x surfuser /usr/share/mime*
setfacl -x surfuser /usr/share/net*
setfacl -x surfuser /usr/share/pidgin*
setfacl -x surfuser /usr/share/pixmap*
setfacl -x surfuser /usr/share/tor*
setfacl -m u:surfuser:- /usr/games/*
setfacl -x surfuser /usr/games/gtkatlantic*
setfacl -x surfuser /usr/games/maniadrive*
setfacl -x surfuser /usr/games/eternallands*
setfacl -x surfuser /usr/games/brutalchess*
setfacl -x surfuser /usr/games/eboard*
setfacl -x surfuser /usr/games/xboard*
setfacl -x surfuser /usr/games/openmortal*
setfacl -x surfuser /usr/games/secondlife # and so on for all games to play online
setfacl -m u:surfuser:- /usr/bin # ...
setfacl -x surfuser /usr/bin/blogilo
setfacl -x surfuser /usr/bin/blogtk
setfacl -x surfuser /usr/bin/bash*
setfacl -x surfuser /usr/bin/choqok
setfacl -x surfuser /usr/bin/mplayer # mplayer-browser-plugin
setfacl -x surfuser /usr/bin/ciao_get*
setfacl -x surfuser /usr/bin/cp # try to disable cp too
# almost not needed: setfacl -x surfuser /usr/bin/dbus*
setfacl -x surfuser /usr/bin/dnsmasq*
setfacl -x surfuser /usr/bin/env*
setfacl -x surfuser /usr/bin/firefox* # sandoxed firefox, quit the same for chrome; additionally firejail can be used in both cases too.
setfacl -x surfuser /usr/bin/freetuxtv
setfacl -x surfuser /usr/bin/frostwire
setfacl -x surfuser /usr/bin/firejail
setfacl -x surfuser /usr/bin/gdict*
setfacl -x surfuser /usr/bin/xfce4-dict*
setfacl -x surfuser /usr/bin/gdb
setfacl -x surfuser /usr/bin/glinuxsms
setfacl -x surfuser /usr/bin/gnome-translate*
setfacl -x surfuser /usr/bin/gtk-gnutella
setfacl -x surfuser /usr/bin/gconf*
setfacl -x surfuser /usr/bin/gftp*
setfacl -x surfuser /usr/bin/id
setfacl -x surfuser /usr/bin/java*
setfacl -x surfuser /usr/bin/jovie*
setfacl -x surfuser /usr/bin/kiax*
setfacl -x surfuser /usr/bin/kphone*
setfacl -x surfuser /usr/bin/linphone*
setfacl -x surfuser /usr/bin/ekiga*
setfacl -x surfuser /usr/bin/kaddressbookmigrator
setfacl -x surfuser /usr/bin/kbookmarkmerger
setfacl -x surfuser /usr/bin/keditbookmarks*
setfacl -x surfuser /usr/bin/konqueror*
setfacl -x surfuser /usr/bin/konversation
setfacl -x surfuser /usr/bin/kopete*
setfacl -x surfuser /usr/bin/klaunch*
setfacl -x surfuser /usr/bin/kcm*
setfacl -x surfuser /usr/bin/kcheckrunning*
setfacl -x surfuser /usr/bin/kcachegrind*
setfacl -x surfuser /usr/bin/kcookiejar4*
setfacl -x surfuser /usr/bin/kded*
setfacl -x surfuser /usr/bin/kdeinit*
setfacl -x surfuser /usr/bin/kdekillall*
setfacl -x surfuser /usr/bin/kdepasswd*
setfacl -x surfuser /usr/bin/kdestroy*
setfacl -x surfuser /usr/bin/kde_generate_export*
setfacl -x surfuser /usr/bin/knemo
setfacl -x surfuser /usr/bin/konqueror # sandoxed konqueror (kde-browser); additionally firejail can be used too.
setfacl -x surfuser /usr/bin/kopete*
setfacl -x surfuser /usr/bin/krunner*
setfacl -x surfuser /usr/bin/ktts*
setfacl -x surfuser /usr/bin/kwrite*
setfacl -x surfuser /usr/bin/gedit*
setfacl -x surfuser /usr/bin/kvirc*
setfacl -x surfuser /usr/bin/kate*
setfacl -x surfuser /usr/bin/marble
setfacl -x surfuser /usr/bin/merkaartor
setfacl -x surfuser /usr/bin/miro
setfacl -x surfuser /usr/bin/new*
setfacl -x surfuser /usr/bin/nettle*
setfacl -x surfuser /usr/bin/pavuk
setfacl -x surfuser /usr/bin/perl* # needed for drakfax or keep perl blocked
setfacl -x surfuser /usr/bin/pidgin*
setfacl -x surfuser /usr/bin/ping* # especially for server
setfacl -x surfuser /usr/bin/putty
setfacl -x surfuser /usr/bin/sed
setfacl -x surfuser /usr/bin/sg
setfacl -x surfuser /usr/bin/strace
setfacl -x surfuser /usr/bin/tor*
setfacl -x surfuser /usr/bin/tvbrowser
setfacl -x surfuser /usr/bin/vlc # vlc-player-browser-plugin
setfacl -x surfuser /usr/bin/wget
setfacl -x surfuser /usr/bin/whereis
setfacl -x surfuser /usr/bin/whois
setfacl -x surfuser /usr/bin/xauth
setfacl -m surfuser:- /usr/bin/xauth_switch_to_sun-des*
setfacl -x surfuser /usr/bin/xchat
setfacl -x surfuser /usr/bin/zenity
setfacl -m surfgroup:- /usr/bin/*
setfacl -x surfgroup /usr/bin/blogilo
setfacl -x surfgroup /usr/bin/blogtk
setfacl -x surfgroup /usr/bin/basename
setfacl -x surfgroup /usr/bin/bash*
setfacl -x surfgroup /usr/bin/choqok
setfacl -x surfgroup /usr/bin/ciao_get*
setfacl -x surfgroup /usr/bin/clear
setfacl -x surfgroup /usr/bin/cp # ggfls. ohne cp
# setfacl -x surfgroup /usr/bin/dbus* # ggfls ohne
setfacl -x surfgroup /usr/bin/dirname
setfacl -x surfgroup /usr/bin/dnsmasq*
setfacl -x surfgroup /usr/bin/env*
setfacl -x surfgroup /usr/bin/firefox* # sandboxed Firefox (!!!), ähnlich Chrome, außerdem bietet sich zusätzlich noch Sandbox firejail an (!)
setfacl -x surfgroup /usr/bin/freetuxtv
setfacl -x surfgroup /usr/bin/frostwire
setfacl -x surfgroup /usr/bin/firejail
setfacl -x surfgroup /usr/bin/gdb
setfacl -x surfgroup /usr/bin/glinuxsms
setfacl -x surfgroup /usr/bin/gtk-gnutella
setfacl -x surfgroup /usr/bin/gconf*
setfacl -x surfgroup /usr/bin/gdict*
setfacl -x surfgroup /usr/bin/jovie*
setfacl -x surfgroup /usr/bin/kiax*
setfacl -x surfgroup /usr/bin/kphone*
setfacl -x surfgroup /usr/bin/linphone*
setfacl -x surfgroup /usr/bin/ekiga*
setfacl -x surfgroup /usr/bin/ktts*
setfacl -x surfgroup /usr/bin/kaddressbookmigrator
setfacl -x surfgroup /usr/bin/kbookmarkmerger
setfacl -x surfgroup /usr/bin/keditbookmarks*
setfacl -x surfgroup /usr/bin/konversation*
setfacl -x surfgroup /usr/bin/kwrite
setfacl -x surfgroup /usr/bin/gedit
setfacl -x surfgroup /usr/bin/xfce4-dict*
setfacl -x surfgroup /usr/bin/gftp*
setfacl -x surfgroup /usr/bin/gnome-translate*
setfacl -x surfgroup /usr/bin/id
setfacl -x surfgroup /usr/bin/java*
setfacl -x surfgroup /usr/bin/konqueror* # sandboxed Konqueror, außerdem bietet sich zusätzlich noch firejail an (!)
setfacl -x surfgroup /usr/bin/konversation
setfacl -x surfgroup /usr/bin/kopete*
setfacl -x surfgroup /usr/bin/klaunch*
setfacl -x surfgroup /usr/bin/kcm*
setfacl -x surfgroup /usr/bin/kcheckrunning*
setfacl -x surfgroup /usr/bin/kcachegrind*
setfacl -x surfgroup /usr/bin/kcookiejar4*
setfacl -x surfgroup /usr/bin/kded*
setfacl -x surfgroup /usr/bin/kdeinit*
setfacl -x surfgroup /usr/bin/kdekillall*
setfacl -x surfgroup /usr/bin/kdepasswd*
setfacl -x surfgroup /usr/bin/kdestroy*
setfacl -x surfgroup /usr/bin/kde_generate_export*
setfacl -x surfgroup /usr/bin/knemo
setfacl -x surfgroup /usr/bin/konqueror
setfacl -x surfgroup /usr/bin/kopete*
setfacl -x surfgroup /usr/bin/krunner*
setfacl -x surfgroup /usr/bin/kwrite*
setfacl -x surfgroup /usr/bin/kvirc*
setfacl -x surfgroup /usr/bin/kate*
setfacl -x surfgroup /usr/bin/marble
setfacl -x surfgroup /usr/bin/merkaartor
setfacl -x surfgroup /usr/bin/miro
setfacl -x surfgroup /usr/bin/mplayer # mplayer-browser-plugin
setfacl -x surfgroup /usr/bin/new*
setfacl -x surfgroup /usr/bin/nettle*
setfacl -x surfgroup /usr/bin/pavuk
setfacl -x surfgroup /usr/bin/perl # needed for drakfax or keep perl blocked
setfacl -x surfgroup /usr/bin/pidgin*
setfacl -x surfgroup /usr/bin/ping* # especially for server
setfacl -x surfgroup /usr/bin/putty
setfacl -x surfgroup /usr/bin/rhythmbox*
setfacl -x surfgroup /usr/bin/sg
setfacl -x surfgroup /usr/bin/tor*
setfacl -x surfgroup /usr/bin/tvbrowser
setfacl -x surfgroup /usr/bin/vlc # vlc-browser-plugin
setfacl -x surfgroup /usr/bin/wget
setfacl -x surfgroup /usr/bin/whereis
setfacl -x surfgroup /usr/bin/whois
setfacl -x surfgroup /usr/bin/xauth
setfacl -m surfgroup:- /usr/bin/xauth_switch_to_sun-des*
setfacl -x surfgroup /usr/bin/xchat
setfacl -m u:surfuser:- /usr/libexec/* #check, if following exceptions are complete
setfacl -x surfuser /usr/libexec/accessx*
setfacl -x surfuser /usr/libexec/at-spi*
setfacl -x surfuser /usr/libexec/cheese*
setfacl -x surfuser /usr/libexec/certmonger*
setfacl -x surfuser /usr/libexec/clang*
setfacl -x surfuser /usr/libexec/clean*
setfacl -x surfuser /usr/libexec/dbus-daemon-launch*
setfacl -x surfuser /usr/libexec/docker*
setfacl -x surfuser /usr/libexec/fprintd*
setfacl -x surfuser /usr/libexec/gconf*
setfacl -x surfuser /usr/libexec/gedit-2*
setfacl -x surfuser /usr/libexec/ikiwiki*
setfacl -x surfuser /usr/libexec/kde4*
setfacl -x surfuser /usr/libexec/nm*
setfacl -x surfuser /usr/libexec/openldap* # maybe openssh too
setfacl -x surfuser /usr/libexec/pulse*
setfacl -x surfuser /usr/libexec/squid*
setfacl -m u:surfuser:- /usr/libexec/kde4/ksendbugm*
setfacl -m u:surfuser:- /usr/libexec/ktelnet*
setfacl -m u:surfuser:- /usr/libexec/test*
setfacl -m u:surfuser:- /usr/libexec/kdesu*
setfacl -m u:surfuser:- /usr/lib64/kde4/libexec/kdesud
setfacl -m u:surfuser:- /usr/lib64/kde4/libexec/krootimage
setfacl -m u:surfuser:- /usr/lib64/kde4/libexec/knetattach
setfacl -m u:surfuser:- /usr/lib64/kde4/libexec/lnusertemp*
setfacl -m u:surfuser:r-x /usr/lib64/mozilla/plugins/*
setfacl -m u:surfuser:r-x /usr/lib64/netscape/plugins/*
setfacl -m u:surfuser:- /var/*
setfacl -x surfuser /var/lib
setfacl -x surfuser /var/tmp
setfacl -m u:surfuser:- /var/run/*
setfacl -x surfuser /var/run/tor
setfacl -m u:surfuser:- /var/lib/*
setfacl -x surfuser /var/lib/dbus*
setfacl -m u:surfuser:- /var/spool/*
setfacl -m u:surfuser:- /var/spool/cups # print-server
setfacl -m u:surfuser:- /home/surfuser/.gnupg
setfacl -m u:surfuser:- /home/user/.gnupg
setfacl -m u:surfuser:- /home/surfuser/.history
setfacl -m u:surfuser:- /home/surfuser/.*history
setfacl -m u:surfuser:- /home/surfuser/.local/share/systemd
setfacl -m u:surfuser:r-x /home/surfuser/.local/share/applications
setfacl -m u:surfuser:- /home/surfuser/.xinitrc
setfacl -m u:surfuser:- /home/surfuser/.xprofile
setfacl -m u:surfuser:- /home/surfuser/.config/autostart
setfacl -m u:surfuser:- /home/surfuser/.kde4/share/autostart
setfacl -m u:surfuser:- /home/surfuser/.conifg/plasma-workspace
setfacl -m u:surfuser:- /home/surfuser/.conifg/plasma-workspace
setfacl -m u:surfuser:- /home/surfuser/.config/plasma-workspace*
setfacl -m u:surfuser:- /home/surfuser/.config/lxsession*
setfacl -m u:surfuser:-/home/surfuser/ /.fluxbox/startup
setfacl -m u:surfuser:-/home/surfuser/ /.config/openbox/autostart
setfacl -m u:surfuser:- /home/surfuser/config/openbox/.autostart
setfacl -m u:surfuser:- /home/surfuser/config/openbox/.environment*
setfacl -m u:surfuser:- /home/surfuser/.gnomerc
setfacl -m u:surfuser:- /home/surfuser/.xserverrc
setfacl -m u:surfuser:r-x /home/surfuser/.profile*
setfacl -m u:surfuser:r-x /home/surfuser/.antigen
setfacl -m u:surfuser:r-x /home/surfuser/.bash*
setfacl -m u:surfuser:r-x /home/surfuser/.zsh*
setfacl -m u:surfuser:r-x /home/surfuser/.zlogin*
setfacl -m u:surfuser:r-x /home/surfuser/..zprofile*
setfacl -m u:surfuser:r-x /home/surfuser/..tcsh*
setfacl -m u:surfuser:r-x /home/surfuser/.csh*
setfacl -m u:surfuser:r-x /home/surfuser/.profile
setfacl -m u:surfuser:r-x /home/surfuser/.caffrc
setfacl -m u:surfuser:r-x /home/surfuser/.dotfiles
setfacl -m u:surfuser:r-x /home/surfuser/.mailcap
setfacl -m u:surfuser:r-x /home/surfuser/.exrc
setfacl -m u:surfuser:r-x /home/surfuser/.vim*
setfacl -m u:surfuser:r-x /home/surfuser/.gvim*
setfacl -m u:surfuser:r-x /home/surfuser/.ssh*
setfacl -m u:surfuser:r-x /home/surfuser/.cert*
setfacl -m u:surfuser:r-x /home/surfuser/.gnome2-keyrings*
setfacl -m u:surfuser:- /home/surfuser/.kde4/share/apps/kwallet
setfacl -m u:surfuser:- /home/surfuser/.kde/share/apps/kwallet
setfacl -m u:surfuser:- /home/surfuser/.local/share/kwallet*
setfacl -m u:surfuser:- /home/surfuser/.config/keybase*
setfacl -m u:surfuser:- /home/surfuser/.netrc*
setfacl -m u:surfuser:- /home/surfuser/.gnupg
setfacl -m u:surfuser:- /home/surfuser/.kde4
setfacl -m u:surfuser:- /home/surfuser/.kde4/share
setfacl -m u:surfuser:- /home/surfuser/.kde4/share/apps
setfacl -m u:surfuser:- /home/surfuser/.kde4/share/apps/kmail
setfacl -m u:surfuser:- /home/user/.kde4/share/apps/kmail
setfacl -m u:surfuser:- /home/user/.kde4/share/apps
setfacl -m u:surfuser:- /home/user/.kde4/share
setfacl -m u:surfuser:- /home/user/.kde4
setfacl -m u:surfuser:- /home/redis
setfacl -x surfuser /usr/java # tvbrowser
setfacl -m u:redis:- /home/surfuser
setfacl -m u:root:- /home/surfuser
setfacl -m u:root:- /home/user
setfacl -m u:root:- /usr/games/*
setfacl -m u:user:- /etc/security
setfacl -m u:surfuser:- /etc/security
setfacl -m u:adm:- /home/surfuser
setfacl -m u:adm:- /home/user
setfacl -m u:adm:- /mnt
setfacl -m u:adm:- /media
setfacl -m u:haldaemon:- /home/surfuser
setfacl -m u:messagebus:- /home/surfuser
setfacl -m u:postfix:- /media
setfacl -m u:postfix:- /mnt
setfacl -m u:postfix:- /tmp
setfacl -m u:haldaemon:- /tmp
setfacl -m u:pdnsd:- /usr/libexec
setfacl -m u:pdnsd:- /bin
setfacl -m u:pdnsd:- /sbin
setfacl -m u:pdnsd:- /usr/bin
setfacl -m u:pdnsd:- /usr/sbin/*
setfacl -x:pdnsd /usr/sbin/pdnsd*
setfacl -m u:pdnsd:- /mnt
setfacl -m u:pdnsd:- /media
setfacl -m u:pdnsd:- /etc/fstab*
setfacl -m u:pdnsd:- /etc/mtab*
setfacl -m u:pdnsd:- /etc/crypttab*
setfacl -m u:-1:- /tmp # -1: all unknown user
setfacl -m u:-1:- /home/user
setfacl -m u:-1:- /home/surfuser
setfacl -m u:-1:- /media
setfacl -m u:-1:- /mnt
setfacl -m u:-1:- /
setfacl -m g:-1:- /
----------------------------------------------------------------------------
Those ACL are enough for securing quit all up, but here are some single rules of the already included from above just to think about:
----------------------------------------------------------------------------
setfacl -m u:surfuser:- /usr/bin/su*
setfacl -m u:surfuser:- /bin/su*
setfacl -m u:surfuser:- /usr/bin/knotify4 # ... one more brake less...this zombie-process knotify4 out of kdebase4-runtime (mdv2010, 4.4.5) can be exchanged with kdebase4-runtime (OpenSuSE, 4.4.4-3.1.5 from year 2012/2013, more actual (el6)) using the archiv-manager file-roller or set "chmod 000 /usr/bin/knotify4". If there is no welcome-melody to hear at system-startup, enter a new desktop-file into /usr/share/autostart with "exec=mplayer .../startmelody.wav".
setfacl -m u:-1:- / # -1: all unknown user
setfacl -m u:-1:- /usr/bin/knotify4 #
setfacl -m u:-1:- /usr # -1
setfacl -m g:surfgroup:- /boot
setfacl -m g:surfgroup:- /mnt
setfacl -m g:surfgroup:- /etc/fstab*
setfacl -m g:surfgroup:- /etc/mtab*
setfacl -m g:surfgroup:- /etc/crypttab*
setfacl -m g:surfgroup:- /lib/modules*
setfacl -m g:surfgroup:- /usr/lib/perl*
setfacl -m g:surfgroup:- /usr/lib/python*
setfacl -m g:surfgroup:- /usr/local
setfacl -m g:surfgroup:- /home/user/key-file-LUKS-cryptsetup
setfacl -m g:surfgroup:- /home/user/ # this can be done for all directories within /home except surfuser
setfacl -m g:surfgroup:- /usr/lib/cups
setfacl -m g:surfgroup:- /usr/share/cups
setfacl -m g:surfgroup:- /etc/cups*
setfacl -m g:surfgroup:- /etc/init.d
setfacl -m u:surfuser:- /usr/bin/msyql*
setfacl -m u:surfuser:- /usr/bin/kmail
setfacl -m u:surfuser:- /usr/bin/akonadi*
setfacl -m u:surfuser:- /usr/bin/nepomuk*
setfacl -m u:surfuser:- /usr/bin/ls* # needed by frostwire
setfacl -m u:surfuser:- /usr/bin/python* # but enable access for Miro (miroplayer)
setfacl -m u:surfuser:- /usr/bin/perl*
setfacl -m u:surfuser:- /usr/bin/dolphin*
setfacl -m u:surfuser:- /usr/bin/grep # maybe enable
setfacl -m u:surfuser:- /bin/grep # maybe enable
setfacl -m u:surfuser:- /usr/bin/ssh # enable, if you use SSH
setfacl -m u:surfuser:- /bin/rm # incredible, but this is really possibe!
setfacl -m u:user:- /bin/rm
setfacl -m u:surfuser:- /usr/bin/rm
setfacl -m u:user:- /usr/bin/rm # Beim Entpacken mit Archivierern wie file-roller angelegte temporäre Verzeichnisse werden dann allerdings nicht mehr gelöscht.
setfacl -m u:surfuser:- /bin/ls # but enable access for forstwire (rosa2014.1)
setfacl -m u:surfuser:- /bin/uname # or you might want to allow uname
setfacl -m u:surfuser:- /usr/bin/uname #
setfacl -m u:surfuser:- /bin/cat # or allow cat
setfacl -m u:surfuser:- /usr/bin/cat #
setfacl -m u:surfuser:- /bin/cd # Do you really think, this is possible?
setfacl -m u:surfuser:- /usr/bin/cd #
directory- and file-attributes
Synopsis
chattr [ -RVf ] [ -v version ] [ -p project ] [ mode ] files...
Description
chattr changes the file-attribuntes of a Linux-filesystem.
Formats of a symbolic mode are +-=[aAcCdDeijsStTu].
Important options:
i: integritäty: The file can not be modified or changed..
-R: recursive: directory including its contents
c: compression
u: make undeleteable
example: chattr +iuS textfile.txt
list file attributes: lsattr
 MAC Tomoyo Linux for access controled process-ineraction
MAC Tomoyo Linux for access controled process-ineraction
So far ACL. Mandatory Access Control (MAC) can also restrict the process-interaction. For this matter, msec (rosa2014.1, mdv2010.2) integrates Tomoyo, that can import various standarized profiles and exceptions. TOMOYO Linux is developed since 2003 sponsored by NTT Data with the project manager Toshiharu Harada.
TOMOYO like SELinux uses the LSM-interace and is running as a kernel module. Access rights of processes onto each other are controled on the highest system level. Tomoyo was made to protect applications from unknown leaks in security including Zero-Day-Exploits.
E-mail from info@gooken.de, 05.05.2010
"Hello, sender, how are you? What about decrypting e-mail? You can get my PGP-key from Gooken or by asking a keyserver like hkp://subkeys.pgp.net for info@gooken.de. Copy and paste the key into a new textfile), then import it into your email-client and kgpg resp. kleopatra or any other pgp. Now we can exchange pgp-decrypted e-mail in the TLS- or SSL-decrypted way.
Regards, Gooken (looking for email decrypting recipients)"
Prevent abuse through e-mail getting into effect, by checking sender, contained links, measured spam-probability, missing signatures and certificate, aks for passwords and confidential information, existance of attachments, abstruse offers, origins, origin land and databases collecting such abusive spam and so on to adopt into the spam-filter.
Keylogging resp. audit trace of commands on the server should be prevented from the sight of the user, so look out for commands like "script -f pathtologfile/keylog.log" within /etc/profile enabling the audit of commands entered in bash. Timestamp for commands typed into the bash-history are set by adding "export HISTTIMEFORMAT=´%F %T ´" in /etc/profile.
The CCC told in an interview with ARD, documented by a mp4-video by Tagesschau in 2014, about NSA, that managed to decrypt even encrypted email-transfer. This caused in the mixture of spy- resp. malware to software, especially OpenSource and its decryption would protect against.
Our online-check out of the left menu emphasizes the role of IP and the browser-specification (useragent). In Ipv6 the IP consists of a static natur. With mdv2010 you can still communicate and surf with the dynamic ipv4-address.
DNS: Unbound is designed as a set of modular components, that incorporate modern features, such as enhanced security (DNSSEC) validation, Internet Protocol Version 6 (IPv6), and a client resolver library API as an integral part of the architecture. Originally written for Posix-compatible Unix-like operating system, it runs on FreeBSD, OpenBSD, NetBSD, Linux and other systems.
Following the right strategies and concepts answering questions for security software like "what do (not only) UNIX-user really need
and need to know to achieve sufficient protection/security for their systems independent from any time?", good reports should focus upon the really needed one and that means upon thousandfold tested surface covering prototypes.
In security matters we do not talk of what never can or even could be reached like security - but of security-levels. Aspects like additional filtering, more about prevention, data encryption and rescue, ergonomic aspects and many single points and items are treated in step 2 and the checklist. And beginning with the basic one, it is not sufficient, but fundamental (basic), to disable strangers (hacker) on the one site from passing from the outside into the inside to intrude into the system and on the other site to disable masked enemies (rootkits, trojans, spyware,... ) from passing by ("outgoing") sensible information from the inside to the outside. After a restriction of user, groups and activated services within the system-configuration, this is realized by the concepts access-control, file-release for LAN and packet-filter consisting of firewall (which is illustrated here by the project "The Wall" by Christo in the Gasometer of Oberhausen from year 1999 without proclaiming any correspondence in its meaning). In general, access-control remains ineffective, as there is always one and the same user root from the local inside as much as from the outside, that is established with all access-rights.
So I got my intuition for a native firewall from models like from the mentioned above (where indeed nothing but connected computers from upper areas mark the point of view upon a mysterious wall, that still can be developed for better use of computer-technology) and can be defined as a packet-filter against the intrusion by hacker and the outgoing of most data and much more in general as an instrument for the regulation of traffic online, where fire originates from the block of intrusions by percentages only and dropped packets do not burst off at once. Is there really any need for such walls? At first, you certainly can imagine a need for regulation thinking of all the high-density of known data-highways crashing and therefore trying to "break" in and "steal" out. On this way, OS can be infected by both, hackers and trojans: Many log-protocols in both direction, IN(coming) AND OUT(going), have shown the amount of entries a system can get in conflict with during relative short time. What you see there are many papers full of log-entries with such inputs and outputs in special content including the IP, so that a real, principal demand for good packet-filters indeed can be recorded. Some OS-kernel generally offer
(No) Defragmentations (at all)
 the possibilities to build transparent rules, but you have to find out the correct or effective iptables-/ipchains from a set out of a lot of ineffective, bad structured or just false ones. Intelligent file systems like those for UNIX (resp. Linux) do not need any defragmentation as there are quit no fragments created, source. SuSE 7.3 reference manual. The same for SSD no defragmentation can be made for not having any read/write-heads.
the possibilities to build transparent rules, but you have to find out the correct or effective iptables-/ipchains from a set out of a lot of ineffective, bad structured or just false ones. Intelligent file systems like those for UNIX (resp. Linux) do not need any defragmentation as there are quit no fragments created, source. SuSE 7.3 reference manual. The same for SSD no defragmentation can be made for not having any read/write-heads.
Root-partition with enough memory free
- Requirement for mdv2010: root-partition with at least 60 Gigabyte
To free memory from the root-Partition (and in order to care once more for the aimed "mouseclick-fast" work), do the following:
- Remove all software and packages not needed anymore
- Move and link directories like doc- and/or man from /usr/share to the home-partition: cp -axf /usr/share/doc /home/user/ and rm -dfr /usr/share/doc; profit: around two Gigabytes
- Move and link the Webserver-Directory www from /var to the home-Partition
- Link all temporary-Directories tmp to /tmp: /var/tmp, /usr/tmp, /root/tmp, home/user/tmp,
- Link the browser-caches from /home/user/.kde4 of Konqueror with /tmp: rm -df /home/surfuser/.kde4/cache-localhost.localdomain and ln -sf /tmp /home/surfuser/.kde4/cache-localhost.localdomain
- Perorm data-rubbish-deletion with programs like klen, bleachbit (be careful for using this: it might damage the system!), sweeper etc.
Concept
Although in a few OS implemented file-system might prevent intrusions by setting the system-purpose to "server" resp. remote_root_login and root_login to no by msec or a front-end of it, encryption of the magnetic harddisc resp. (flashed) SSD (click here), online-connections, e-mail-transfer and e-mail themselves, file-release within a LAN (local area network) and access-control, sandboxes in small environments especially around the browsers in the case of file-systems with a less powerful one, it is even more possible not only to block, but also to protocol the intensities cracking the access-control at the very beginning and to keep from reading files. Access control prevents from installing malware by the opening of attachements in e-mail and guarantees read-/write protection within a LAN and in important cases even more local freeness of viruses by commands like
 chmod 755 upon owner root, optional in conjunction with chattr +i for the integrity of files. Therefore virus-scanner for UNIX(Linux)-Systems are only needed to scan Windows-email. After performing our suggestions marked in greed-LED-color, chmod 700 makes files and directories unreadable from the outside. In conjunciton with Linfw3, for security and invisibility for any views from outside, we recommend the following access rights:
chmod 755 upon owner root, optional in conjunction with chattr +i for the integrity of files. Therefore virus-scanner for UNIX(Linux)-Systems are only needed to scan Windows-email. After performing our suggestions marked in greed-LED-color, chmod 700 makes files and directories unreadable from the outside. In conjunciton with Linfw3, for security and invisibility for any views from outside, we recommend the following access rights:
| chmod 555 /; chmod 700 /boot; chmod 700 /boot/grub; chmod 400 /boot/grub/menu.lst; chmod 777 /tmp; chmod 751 /home; chown root ~/.kde4; chgrp root ~/.kde4; chmod 701 ~/.kde4; chown root -R /home/user/.thumbnails; chmod 000 -R /home/user/.thumbnails, chmod 751 /mnt; chown root:root /etc/fstab*; chmod 600 /etc/fstab*; chmod 755 /usr; chmod 755 /etc; chmod 700 -R /etc/init.d; chmod 711 /opt; chmod 700 /usr/src; chmod 600 /etc/mtab*; chmod 600 /etc/cypttab*; chmod 711 /media; chown user:user /home/user/Texte; ...; chmod 700 /home/user/Texte; chmod 700 /home/user/Bilder; ...; chmod 711 /media; chmod 700 -R /home/user/.kde4/share/apps/kmail/mail/*; chown user:user -R /home/user/.kde4/share/apps/kmail/mail/* |
rest chmod 755, eventually less, directories for the e-mail accounts chmod 700. Access-rights for the userdirectories under directory home might depend on an iptables based firewall as it does by the firewall LINFW3 we introduce below, foreclosed chmod 750 or chmod 700, alternatively all by umask, each boot time guaranteed by MCC, section security, access-rights.
Mandatory ACL (so called mandatory access control lists): SELinux and Tomoyo Linux enhance and sharpen the concept of access control by ACLs upon domains, a structure consisting of processes and their parents to get registered and tested and in the next step blocked from other processes and owners. Therefore that also works upon files like the well-known common access control depicted before. mdv2010 emphasize Tomoyo more than SELinux through belonging sections in the MCC under a small refinement in mdv2010.1, making it more transparent and handle. Read details about Tomoyo from a link to the detailed manual from our linksite. Nevertheless in our opinion such additional concepts can be a little bit confusing for users by unwanted blocking of processes (resp. executable files) of processes (files) and are almost not resp. rarely needed to achieve the promised high IT-security-level. Many server like Apache and Squid do add their own ACL to the common access control resp. iptables rules too
The partition with mountpoint root, the root-partition can not be encrypted. Ideally, create such at least ext2-partition consisting of /boot with especially the ramdisk (initrd), bootmanager, kernel vmlinuz and configuration-file only. Now you can encrypt quit the whole hard-disk with methods like AES, Serpent, Two- or Blowfish. Partitions inclusive swap can also be password encrypted by the partition-manager out of the system-configuration resp. direct entries in /etc/fstab, special commands as much as loop-devices for virtual partitions upon regular files, while newer versions prefer LUKE, see links. Notice, that newer Linux-versions might not support the handy Loop-AES-encyption by the partition-manager anymore to encrypt the complete harddisc resp. partitions by methods like dm-crypt/LUKS, who can also encrypt root-partitions (the main-partition with the UNIX/Linux, such with mountpoint /) and therefore the entire harddrive except /boot, see prelonging link from our linkside. To encrypt the SWAP with Loop-AES, you need the packages resp. tarballs for loop-aes, losetup, aescrypt, cryptcat and/or util-linux for that. Most of them might be already installed.
Try
deactivation: swapoff -a
device-configuration-file fstab out of directory /etc: swap-device-file swap swap sw,loop0,encryption=AES128 0 0, with a device-file for this SWAP-partition like /dev/sda6
overwrite of the old swap-partition: dd if=/dev/zero of=/dev/sda6 bs=64k conv=notrunc
create: mkswap /dev/sda6
activation: swapon -a
for the encryption of the swap-partition.
With dd it is also possible to create an image from CD/DVD:
dd if=/dev/cdrom of=/cdimage.img
or to secure and restore the MBR:
dd if=/dev/sdx of=/mnt/sdx.mbr bs=512 count=1 to secure the MBR of harddrive sdx
dd if=/mnt/sdx.mbr of=/dev/sdx bs=512 count=1 to restore the MBR of harddrive sdx
Same with partitions:
dd if=/dev/hdax | gzip > /mnt/image.gz to secure a complete partition by dd in the type gz
gunzip -c /mnt/image.gz | dd of=/dev/hdax to restore the secured partition
Releases in the LAN: howto connect Linux and Windows
Release within the LAN: Howto connect Windows & Linux computers, PCWelt.de, 08.11.2015
The file-manager of Linux supports releases of directories within the context menu
Both, Linux and Windows cooperate well in networks. With the right software and configuration data exchange in both directions will be no problem.
SMB/CIFS is the name of the standard-protcol for windows for releases within the network. It enables Linux, Android and Mac OS X its possiblities too. SMB stands for the "Server Message Block"-protocol. It origins from IBM and the further development under the name CIFS (Common Internet File System) of Microsoft. It is used whenever Windows provides files in the network for the other users or if they want to access them.
Instead of this, Samba delivers Linux-systems functions for such releases. Samba consits of a client and a Server. The client is installed for most Linux-distributions and allows the access of the releases of other hosts. Some distributions make the installation of Samba for server still essential. Then Linux is able to release directories and files even for Windows-user over the network, details:: http://www.pcwelt.de/ratgeber/Windows-und-Linux-Freigaben-einrichten-9790088.html
ddrescue: | ddrescue [ -options ] infile outfile |
Session
Command line
Terminal-Tuning, PCWelt.de, 03.01.2016
There are many ways to configure the terminal to make it perfect and pretty.
http://www.pcwelt.de/ratgeber/Terminal-Tuning__Linux-Tricks_fuer_mehr_Komfort-Kommandozeile-8381668.html
So we type into ~/.bashrc:
alias hi=´echo Hi! How are you?´
alias hallo=´echo Hi! How are you?´
SESSION
Troubleshooting
[SOLVED] Network-Manager: No connection build-up!
Unplug all ethernet-cards not needed.
Update dhclient (el6)
Build up the connection with dhclient (in root-mode). This does almost function, while ifup eth0 doesn´t: terminal -> dhclient.
To solve the problem more concret, compare the following files with your ones and adjust them (with similar content):
Content of /etc/sysconfig/network-scripts/ifcfg-eth0:
DEVICE=eth0
BOOTPROTO=dhcp
IPADDR=0.0.0.0
ONBOOT=no
METRIC=5
MII_NOT_SUPPORTED=yes
USERCTL=yes
DNS1=127.0.0.1
RESOLV_MODS=yes
LINK_DETECTION_DELAY=6
IPV6INIT=no
IPV6TO4INIT=no
ACCOUNTING=yes
DHCP_CLIENT=dhclient
NEEDHOSTNAME=no
PEERDNS=no
PEERYP=no
PEERNTPD=no
MACADDR=92:17:c3:aa:2a:eb # original-MAC-address of the ethernet-card
Content of 70-persistent-net.rules
# This file was automatically generated by the /lib/udev/write_net_rules
# program, run by the persistent-net-generator.rules rules file.
#
# You can modify it, as long as you keep each rule on a single
# line, and change only the value of the NAME= key.
# Drakx-net rule for eth0 (28:01:1b:01:11:a1)
SUBSYSTEM=="net", ACTION=="add", DRIVERS=="?*", ATTR{address}=="ba:ea:a1:17:aa:00", ATTR{type}=="1", KERNEL=="eth*", NAME="eth0"
In this example, ATTR... is assigned with a MAC-Addresse from macchanger started in /etc/rc.local during boot. You should really do this.Otherwise use the original MAC-address again!
Past the tuning of both configuration files delete all Internet-network-configuraitons:
MCC -> Remove a connection -> Delete.
Copy both files into a directory like /boot-save and just eventually also add into /etc/rc.local:
cp -fp /boot-save/ifcfg-eth* /etc/sysconfig/network-scripts/
cp -fp /boot-save/70-persistent-net.rules /etc/udev/rules.d/
chmod 644 /boot-save/ifcfg-eth*
Reboot the system.
Remove all network-profiles in MCC -> Network&Internet -> Profiles.
Before this, deactivate the options IPv6, Proxy and Firewall-IPv6 to create it. Click upon "New profile" and activate it by clicking on "activate".
Reboot the system again. Now Network-Manager should always function!
Now we describe a typical session with UNIX/Linux (mdv2010) with some more network-troubleshooting for other net-problems.
The commands named
and
help to find out your (and some other) username resp. the groups (GID) you (as the user with your own UID) all ought to belong to.
Whoami or "who -m" make especially sense, if one changes between different users or root to an fro, while the prompt does not show the user name.
and
inform about the UID and GID one ownes and about all the groups, one as the user is membered. PCWelt.de, 18.02.2016: "Whoami should not be confounded with "who" listing all user actually logged into the system. After who is entered, all logged-in user together with the login-devices are listed by day and time. With "who -a" this listing becomes more complex, the login-time is listed too for example. One alternative for the command who is provided by the command "id" from above.
"last" lists all user that have been logged in for the last time.
So what"s your name then, computer?
... Braggart!
Where am I? Tell me the pathname:
ls or dir list directories and files (notice, that directories within a path are separated by a simple slash "/" and not an additional pressing of the ALT-key requiring "" like in MS Windows, cd: change directiory, "cd -" means: change to the pregoing directory right before the actual directory, "cd .." move to the upper dirctory, "cd ." move to resp. remain within the actual directory rm: delete files, rm -dfr: deletes files and directories including all subdirectories and their files, cp copies them. Important options, explained by "man cp" are -ax and -f. mkdir newdirectoryname creates a new directory, that can be deleted with rmdir newdirectoryname again, if it is empty. "cat filename" lists the include of the file named filename, especially for text-files, and "cat filename1 filename2 > newfilename" concatonates file with filename 1 with the file named by filename2 into the file named by newfilename.
Are there any processes killing the ressources, even zombies, so that we have to take care for their updates? ESC&ALT, pstree or:
Packagekit with more than 43 % memory ressources has to be removed from our computer.
Now we are building up the network connection to the internet. either by clicking upon the net_applet, we should have compared the size of the coded source with ago, or by typing:
DNS: 127.0.0.1 (dnsmasq). Scan for viruses and remove them:
| clamscan --remove=all -r /home/<userdirectory>/.kde4/share/apps/kmail/mail |
Always boot in the explicit text mode (MCC -> Systemstart -> graphical boot -> text). How did the booting ago, any failures, any packages to update? There should be not any delays, errors and warnings during the boot of mdv2010, almost signed by OK, same during the shutdown (rpm usermode and usermode-consoleonly). So have a look into the systemlog /var/log/messages, MCC -> System -> view logfile or type into terminal
If problems occur, press the key "i" for the interactive mode after udev has started. The display manager "dm" has to be disbaled to solve problems with the X-server. One can use especially editor nano to reconfigure files. The orange and blue colored Mandriva-star-logo should always appear on top on terminal after the system logout.
Like every good company, Linux consists of at least two "departments": one for the crew, one for the boss (root, Sysadmin). For other bosses might want to achieve more rights than the boss getting used to, bosses have to be very carefully. Make fast terminal-operations: If you press key F1 up to F6, the full-screened terminal with the Mandriva-Logo upper left corner is apperaring for "parallel" works on belonging screen tty1 up to tty6. If you press F7, the old graphical modus returns right to the state before such function-keys are pressed and so on. Another thing to remember is, that you should forbid root to login (local graphically by kdm or gdm and so on). If the root-mode is started manually for the first time, dialog might appear to make some requests for the graphic-card and driver. In this situation, you have to press the WINDOWS-Key to move on resp. to get back into the graphic-root-mode.
Start Apache Webserver:
Start MySQL (in the Root-Modus) as user root on localhost):
| msyqld; mysql -h localhost -u root -p |
Are there actually any other ones within the LAN? finger. I see... So list the last 50 users that already logged in, who faild login (lastb) and if there should be ever, tell me exactly when:
| last -n 50, lastb and lastlog or last -t 20110831172600 |
To review recent logins, if the login is from a remote location, it will be associated with a specific IP address outside your network:
| utmpdump /var/log/wtmp | less |
We are creating a pdf for the manual of bash (shell-language UNIX-sh resp. bash) over postscript out of man by using a converter:
| man -t bash> bash.ps; ps2pdf bash.ps |
Searching for files resp. char-sequences within: find, kfind, gtkfind, catfish, grep, ugrep, egrep, sgrep (like grep, but it searches for structured pattern), ngrep (like grep, but for network, within data payloads of packages), ... . PCWelt.de: With ...
| tre-agrep -2 "search-termf" filename.txt |
you are starting in Debian/Ubuntu a search as by grep for the "searched char-sequence" within the file "filename.txt" for the char-sequences with up to two differences. In this example the tolerance is set by the parameter "-2". Allowed is any value between "-0" and "-9", where the "-" marks the parameter and not any kind of minus. In Open Suse, Fedora (mdv2010) and all Red-Hat-variants the program name is "agrep" without the prefix "tre"", but functions and parameters are the same ones.
Beneath package-database-queries through "rpm -qi package-name" for package-info like summary and description, "rpm -qa" and "rpm -qf", the Khelpcenter (kdehelpcenter), kinfocenter and our UNIX-System-Command-Reference with LED-green marked out security-commands this is a quit important manual resp. directory in future!
Autostart should be set in /usr/share/autostart or K-menu -> systemsettings -> user -> Autostart or through the gnome-control-center. There programs can be activated, deactivated, added and removed.
Router-protection, free choice of the DNS-Server
So sichern Sie Ihren Router ab, PC-Welt.de, 23.07.2012 | 13:22 Uhr
Wenn Hacker Ihren Router kapern, können sie Ihre Daten ausspähen, Ihre Internetverbindung missbrauchen und Sie auf gefälschte Internetseiten umlenken. Schützen Sie sich jetzt!
Ihr Router ist das Datendrehkreuz, durch das alle Daten fließen, die Sie innerhalb Ihres lokalen Netzwerks von einem PC auf einen anderen übertragen. Außerdem läuft der gesamte Internetverkehr Ihres Netzwerks durch diese Box. Umso wichtiger ist es, dass die Einstellungen Ihres Routers und der Zugang zur Ihrem WLAN geschützt sind. Ansonsten kann Ihr Internet mitbenutzt und auf alle freigegebenen Daten zugegriffen werden. Schlimmstenfalls konfiguriert Malware Ihren Router um und setzt etwa einen manipulierten DNS-Server ein, der Ihre Internetzugriffe umlenkt. Das kann Ihnen nicht passieren? Seien Sie vorsichtig!
DNS-Hack: Anfang September hat eine türkische Hacker-Gruppe die DNS-Einträge einiger Domain-Registraren gehackt und so den Internet-Traffic zu den Seiten von UPS, Vodafone, National Geografic, Acer und weiteren teilweise umgelenkt.
Speedport-Hack: Ende August wurde bekannt, dass mehrere von T-Online und Vodafone verkaufte WLAN-Router ab Werk einen unsicheren WPA-Schlüssel voreingestellt hatten. Zwei Studenten fanden das System heraus, mit dem der Schlüssel erzeugt wird, und konnten so den Schlüssel jedes Geräts dieser Modellreihen ermitteln.
Gooken empfiehlt die Verwendung lokal in /etc/resolv.conf frei eintragbarer DNS-Server anstelle der beiden DNS aus der Konfigurationsdatei des Routers und desgleichen. Über Verbindungsverwaltung aus MCC entscheidet man sich für die Verwendung der lokalen DNS. Netzwerkverbindungen lassen sich übrigens mit Contrack aus LINFW3, iptraf und netstat -n angeben.
PC-WELT zeigt hier, wie Sie Ihr WLAN und Ihren Router vor Angriffen schützen. Die Vorgehensweise wird anhand einer Fritzbox 7240 erläutert. Die Optionen und Menüs können bei Ihrem Router etwas abweichen.
Wer surft gerade in Ihrem WLAN-Netz?
Beim einfachsten Weg, um herauszufinden, ob Ihr Router oder Ihr WLAN-Schlüssel geknackt wurde, prüfen Sie, ob gerade ein Fremder mit Ihrem Netzwerk verbunden ist.
WLAN-Verbindungen auflisten: Auf einem Computer, mit dem Sie in Ihrem WLAN verbunden sind, starten Sie dazu das Programm Wireless Network Watcher . Das Programm listet daraufhin die IP-Adressen, die Gerätenamen, die Hersteller und die MAC-Adressen zu allen Geräten auf, die gerade mit Ihrem Netzwerk verbunden sind - verkabelt oder kabellos. Sollten das mehr sein, als Sie in Ihrem Haushalt aktuell nutzen, surft ein Fremder mit. Dann sollten Sie schnell handeln.
Wireless Network Watcher
DNS: changing the DNS...
Instruction for Debian- and mdv-Linux
DNS von CCC: 192.76.134.3 world.ccc.de
Changing the DNS to an anonymizing one:
213.73.91.35 (dnscache.berlin.ccc.de)
192.76.134.3 (CCC - Chaos Computer Club Hamburg e.V.)
139.149.4.20 (names.zrz.TU-Berlin.DE)
129.70.182.23 (ns2.uni-bielefeld.de)
129.70.182.7 (ns1.uni-bielefeld.de)
129.70.132.100 (techfac.TechFak.Uni-Bielefeld.DE)
131.188.3.2 (ns.rrze.uni-erlangen.de)
131.188.3.4 (secondary.rrze.uni-erlangen.de)
134.100.33.240 (rzaix240.rrz.uni-hamburg.de)
134.100.9.61 (rzdspc1.informatik.uni-hamburg.de)
134.95.100.208 (mail1.rrz.uni-koeln.de)
134.95.129.23 (noc2.rrz.uni-koeln.de)
85.214.20.141 (FoeBud)
2001:4f8:0:2::14 (f.6to4-servers.net, IPv6, ISC)
194.150.168.168 (dns.as250.net; Berlin/Frankfurt)
DNS-Server-Liste: https://stanar.de - Öffentlicher DNS Server der Telekom, Arcor, 1&1, ...
0) mdv2010: MCC, simple by configuring established connections and by setting your own DNS instead of DNS from the router
or other methods like:
a) DNS by your computer (host), recommended: Set the both DNS in the system-configuration (mdv: drakconf). Change or add both DNS in LINFW3 (also after b) and c)).
b) DNS by router (resp. gateway): Call the GUI for the router-configuration like fritz.box. If the option for DNS is missing: 1. export the router-configuration by securing into a file, 2. change both DNS in this filei, 3. backup: Import the file, 4. restart the connection by the GUI
b) methode from CCC: Change the DNS in /etc/resolv.conf:
If nscd is installed, type
> /etc/init.d/nscd restart
A fast, (local) cacheing DNS-server can be configured with dnsmasq too: http://www.pcwelt.de/ratgeber/Schneller-DNS-Server-unter-Linux-mit-Dnsmasq-9931341.html . Notice, that in /etc/resolv.conf both, nameserver DNS-ip and "nameserver 127.0.0.1", are entered.Adavatage: the IP is only asked one time the requested domain.
 At first the file dnsmasq.conf within directory /etc should be configured:
At first the file dnsmasq.conf within directory /etc should be configured:
nano /etc/dnsmasq.conf or (creating a new configuration file):
touch /etc/dnsmasq.conf
Then this file should be opened:
sudo nano /etc/dnsmasq.conf
Comment out the following five rows or type them in:
listen-address=127.0.0.1
port=53
domain-needed
bogus-priv
resolv-file=/etc/resolv.dnsmasq
cache-size=500
interface=eth0
no-negcache
The entry "listen-address" administrates Dnsmasq to make local requests by the address localhost (127.0.0.1) on port 53 only. Host names out of the LAN are not forwarded to other DNS-server by the option "domain-needed", and "bogus-priv" avoids the resolution of IP-addresses from private subnets (192.168.x.x, 10.x.x.x).
Compact DNS-Server: Dnsmasq as a DNS-Cache requires these eight lines only, last three lines are optional, but cache-size has to be set for cacheing - no caching possible without.
The link "resolv-file" is refering to another configuraiton file "/etc/resolv.dnsmasq", that still has to be created. In this file you enter the IP-address of the (real) DNS-Server like of the provider or the router. The network-interface should also be set and no-negcache cares for cacheing even on errors, what should be kep optional. With
sudo touch /etc/resolv.dnsmasq
this second configuration file is created. Open it with a text editor like nano and enter the addresses of the DNS-Server, dnsmasq needs to resolve the domains. For stationary PCs within local networks the DNS-Server-addresses of the provider resp. of the router (192.168.178.1) should be set.
To be more concrete, what DNS-addresses to take, use the following command:
cat /etc/resolv.conf
Behind "nameserver" the IP to take are shown.
For example, if "192.168.178.1" for the address of a Fritzbox is shown, all to enter into the file "/etc/resolv.dnsmasq" is
nameserver 192.168.178.1
For computers using changing DNS-Server within other LAN/WLANs, the address of a fast public DNS-Server has to be entered as a last ending line too.
Howto start dnsmasq:
dnsmasq is started depending from the usage of systemd or not in different ways by one of the the commands:
sh /etc/init.d/dnsmasq start resp. MCC->system services or, if systemd is not used by
sudo systemctl enable dnsmasq.service
sudo systemctl restart dnsmasq.service
Now /etc/resolv.conf has to be configured by text editors like nano, so that dnsmasq can can forward dns-name-resolution to external DNS-server. Either the network connection has to be reconfigured by system control resp. MCC or directly within /etc/resolv.conf. Go sure, that the local DNS-server (dnsmasq) is entered within the first line at first (127.0.0.1), followed by the lines for the other DNS-server, consisting of at last one .An example for the forwarding to the DNS-cache of the Fritz-Box is:
nameserver 127.0.0.1
nameserver 192.168.178.1
Be careful for WICD. resolv.conf is admininstrated automatically resp. overwritten. Therefore the static DNS must be set in this certain order only.
If NetworkManager is used, resolv.conf does not have to be overworked manually. The network connection within the Networkmanager can be set to "automatic (DHCP), addresses only" or to "manuell".Now IP-addresses of up to three DNS-server can be set - separated by colon - into the belonging field. After this is stored, all is written into resolv.conf.
Check out if local cacheing is possible:
$ dig mandriva.com
Respond:
;; Query time: 0 msec
;; SERVER: 127.0.0.1#53(127.0.0.1)
Nothing more has to be configured anymore, if dnsmasq is just working as a DNS-Server. Computers within the LAN that shall use this DNS-Server have to be configured in such way, that they really use this server.
Router-Update: AVM keeps his promise, to extend the Fritzbox-firmware with new functions by updates form time to time ( so that itself is protected and firewalls like Linfw3 get supplemented ). What all is provided by the new version, is described here: http://www.pcwelt.de/ratgeber/Fritzbox-Das-neue-Fritz-OS-9730440.html
Any good router has got its own router-firewall. The new version is also able to block pings. "Internet -> Filter -> Listen" enpossibles the stealth-Modus. Attacker use the ping-command, in order to scan ports and ip address ranges, if a device reacts by a confirmation (ACK-)package, PCWelt.de, 05.11.2015, http://www.pcwelt.de/ratgeber/Fritzbox-Das-neue-Fritz-OS-9730440.html
Significant commands for net-diagnostics:
administration of network-interfaces:
Listing of such net-interfaces, adminsistration of network-interfaces, list them at first:
helps to reconfigure the X-server
| "ip a", "inxi -i" or more complex information by: "inxi -v7" |
inxi shows not only the local IP-address but also the daily changing public (WAN-)IP. Therefore inxi should be installed by the self-named rpm inxi for el6 or mdv2010..
switches the adapter, here ethernet-adapter "eth0" on (up) and off (down).
| ifconfig eth0 192.168.0.222 |
postulates a new local ip-address from the router. Althoug this command can cause an inconsistent net-configuration, ccess to the front-end of the router is provided. There a wished local domain can be set by an unchangeable ip.
List WLAN-Data (although one should better resign from WLAN...)
Information about the WLAN-interface:
More information about the wireless interfaces like bluetooth, WLAN and UMTS: with rfkill you can switch on (unblock) and off (block) wireless interfaces like bluetooth and WLAN, but also UMTS. The power-consumption can be declined and unnecessary lacks in security be closed by this:
Check a single network-connection:
or check out a complete area (subnet):
This command sends pings to all 255 addresses of the ipv4-addressroom with a list as a result.of net-devices with their host names and ip-addresses.. Complete portscans are made by nmap without parameters: for each host following information are provided: host name, ip-address, MAC-address and a list of opened ports. A single host can be queried by nmap 192.168.178.3 or nmap raspberry ).
Show the mac- and belonging ip-addresses:
Show built-up network-connections:
IP-Adresse of the gateway (flag U: active, G: gateway):
Resolve the IP-address :
Up- and downloads can be made without browser, ssh- and ftp-client:
| wget -r -l8 http://anywebside.de and wput * ftp://ftp-servername.xyz@webside.com/directory/ |
wput works recursive traverse the subdirectories too: Wildcard "*" takes care of all files of the actual directory including their subdirectories. Curl is another method for uploads and downloads, but does not work recursive.
Does a connection not function, for example block transfer and what is the host causing this? Does a referred connection station in any foreign hosts? The way of a connection can be checked out by:
| tcptraceroute [options] host |
where host stands for any finally targeted hostname or end-address-IP.
Serious hard network-problems: PCWelt.de, 29.09.2015: "Networks consist of various hard- and software-components, so the causes according to this fact. Systematic error-analysis isolate the error and help to repair on the right place. It is not easy to find out, what causes the network-problems. The error can cause in the DSL-router, in the cabling, at a switch or in the WLAN-configuration of the router. There might be a network-adpapter out of order or the network is not configured well in Linux. So only systematic analysis do help against plenty of possible causes: http://www.pcwelt.de/ratgeber/Defektes-Linux-Netzwerk-Sechs-Tipps-zur-Reparatur-9787709.html.
Why does the net-communication not function, what is the cause? Where do other computer contact and surf to, and how intensive are the contacts? What are the communication-protocols of ISO-OSI-RM are used? And how much traffic (packets) do such clients and server proclaim for themselves, so that other ones do have to restrict their needs?
In order to solve such network-problems, tools like wirehark (prev. ethereal) are useful too: http://www.pcwelt.de/ratgeber/Netzwerkanalyse-mit-Wireshark-4731857.html.
| su - surfuser; sg surfgroup wireshark |

We can not remember ever having such problems with el6, previously mdv2010: You even seem not need to configure anything for networking with DSL-cable-routers or DSL-modems, if you use the quick auto-configuring MCC wizard for network-interfaces, configuration time: we needed just 10 up to 60 seconds (... but think of VPN). Hugh networks conflict almost in the gateway resp. router, samba.conf, httpd.conf of the Apache Webserver, host.deny, host.allow, resolv.conf and all the ethenet-cards of the LAN-clients. Simple structured firewalls like Linfw3 do their best against more confusion. Network-administrators work with documents like netplans and so on. SuSE Linux 7.3 was handled with four books: reference, configuration, programs and networking. Aternatively, the infocentrum deals with this theme too. PC-magazins often describe specific howto.
Oh, my password seems to be old. I change it by
or gpasswd. Before doing this, I´d like, it should be suggested, most likely an encypted one by makepasswd. But now I can not recognize my own password... Now I am going to talk to some other users listed, but I do not like to send an e-mail: mesg y and talk somewhat.
| talk charly (or charly@anyhost) laberlaber |
It is userful, it is simple: "The talk-server package provides daemon programs for the Internet talk protocol, which allows you to chat with other users on different machines. Talk is a communication program which copies lines from one terminal to the terminal of another user."
And how long did I work with the computer by now? Just type "up" or
Copy files by command cp and move them by command mv. Popular options for the command cp are "-f" and "-ax", see "man cp", for ls "-al". If the computer should list his executable files, change dircetories by cd and list them out by ls. ls should be piped with more, if the amount ist too high, in order to get a better view upon them within the terminal:
| ls -al /bin /sbin /usr/bin /usr/sbin /usr/games/bin | more |
If package sl (for el6 or mdv2010) is installed, a steam lock is shown on the terminal each time command "ls" is accidently permuted with "sl".
The update-Listing from pro-linux-de recommends the update of the bash, so we look out for the installed package to find out the version and requirements:
| rpm -qi --requires packet_nam_includinge_the_version_if_more_than_this_one_package_is_installed |
Do this each time before making any installs and updates!
We want to look out for a file named whatiwrote.txt traverse the subdirectories of dokuments up to the seach-depth 5. Programs like kfind present a graphical frontend, but we try to seach independent from blocking access-rights by using the command find":
| find -L /home/user/documents -maxdepth 5 whatiwrote.txt |
Memory used and memory free:
Such Programs out of /bin, /usr/bin/, /games/bin and so on are started listing important error-messages either by typing
| "./executable_filename", "executalbe_filename" resp. "path_to_their_executalbe_filename/exec_filename" or "/./path_to_their_executable_filename" |
In serious hard cases check all package-dependencies by rpm -qi --requires packagename or use prefix strace for execution:
| "strace ./executable_filename", strace "executalbe_filename" resp. "strace path_to_their_executalbe_filename/exec_filename" or " strace /./path_to_their_executable_filename" |
or use gdb:
| gdb --arg ./executable_file arguments -> run -> show debug |
After we all have typed in
and
one is allowed to laugh about any further questions about UNIX/Linux.
Autostart can be configured in KDE and Gnome graphically by setting checkboxes and adding and administrating items:
There, in el6 resp. mdv2010, we recognize a programm namely to provide video- and audio-codecs and therefore without any plausible function for the autostart listed, that we might going to remove like package (rpm) xguest too. Rootkit-hunter rkhunter indicates one warning after the other one after mdv2010 got updated well and consumps too many cpu-ressources for our taste, after he got started self-automated by msec and other processes from time to time. So we prefer the rootkit-hunter chkrootkit only:
| rpm -e codeina; rpm -e billreminder; rpm -e tracker; rpm -e mdkonline; rpm -e rkhunter |
We deleted rpm mdkonline, billreminder and tracker this way too.
If you want to know any addresses from a database of milliards of records and all this in detail like name, street, city, country, telephone, owner, technique, instance for abuse, email-addresses and so on, the terminal can already do its best by just typing
Do not forget to start all network-commands listed here by "su - surfuser" followed by "sg surfgroup network-command", if you use LINFW3.
host is a command, that is already installed. If lists the IP-Adresse of a web-domain only. To get more information, install and use whois by rpm.
newstart by terminal:
shutdown by terminal:
start the X-(Graphic-card-)Server:
Editors, that do not need X started, are ed, vi, cream (simplifying frontend for) vim and especially
Installation of a tarball (tar.gz-, bz2- and zip-archives and others depending on instructions from file INSTALL):
| ./configure --prefix=/usr && make && make install |
Continuation of this excurs: please click here!
Once described how and howto, you know everything too!

News&Links#Computer
Our rubriques for computer:
Computer |
Monitor |
Printer / Drucker |
SSD |
Network / Netzwerk |
Smartphone |
MS Windows
|
 Gooken
Gooken
 Exkurs
Exkurs
 News&Links
News&Links
 Links
Links
 Gästebuch
Gästebuch
 Worth at mind report from uncut-news.ch:
Worth at mind report from uncut-news.ch:
 ... and if, such decades ago, even my own mother meant... / ... und wenn vor Jahrzehnten sogar die eigene Mutter zum Thema Maja Schmidt schon meinte ( ist das aber fertig: die eigene Mutter dann auch noch, das kriegt ihr aber wieder...!):
... and if, such decades ago, even my own mother meant... / ... und wenn vor Jahrzehnten sogar die eigene Mutter zum Thema Maja Schmidt schon meinte ( ist das aber fertig: die eigene Mutter dann auch noch, das kriegt ihr aber wieder...!):
 Gooken - the at times breaking full, large "china restaurant"... Do you want the everlasting peace with your computer as a system (backported Fedora Core (fc): updates from year 2010-2026 resp. lifetime) with covering software (backported too) on powersaving and cheap lifetime-hardware, providing the incredible high security level? Contribute to Gooken for the manufacturing of the (consistent) IT-security-standard! For correspondent please click here!
Gooken - the at times breaking full, large "china restaurant"... Do you want the everlasting peace with your computer as a system (backported Fedora Core (fc): updates from year 2010-2026 resp. lifetime) with covering software (backported too) on powersaving and cheap lifetime-hardware, providing the incredible high security level? Contribute to Gooken for the manufacturing of the (consistent) IT-security-standard! For correspondent please click here!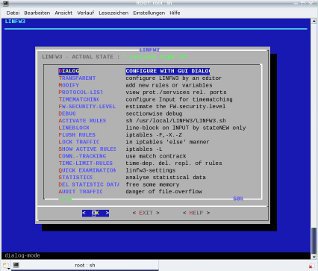
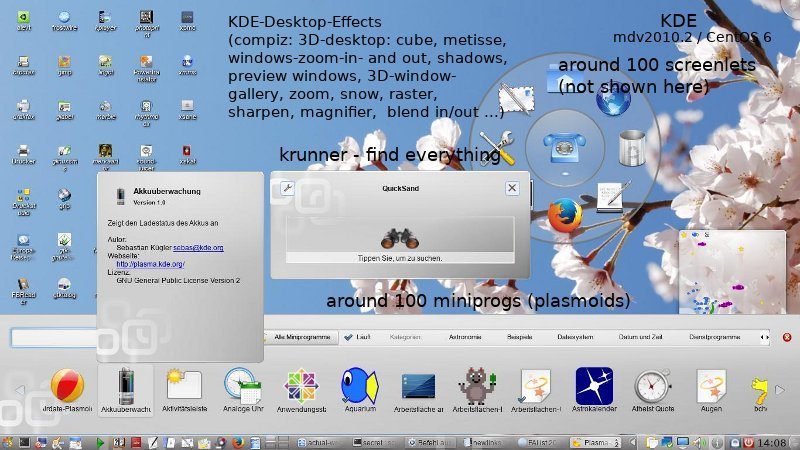
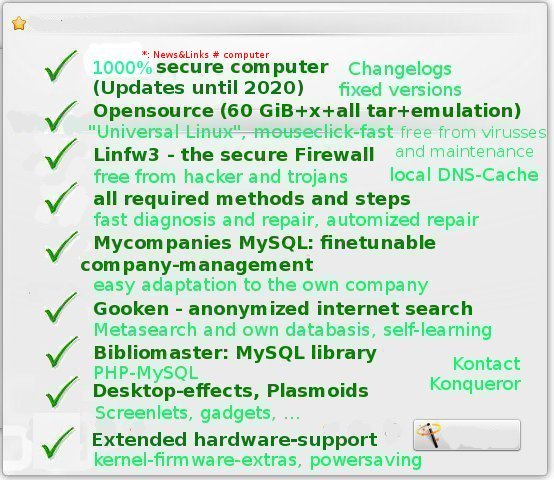

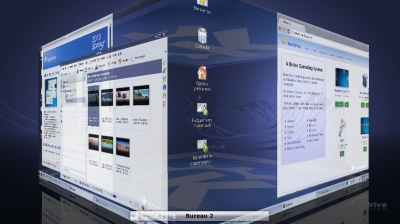
 Regardless from all Linux-distributions, one and the same Linux gets installed package by package, although this might not possible for each distribution as a fault of their specific architectures (library-structure and so on).
Regardless from all Linux-distributions, one and the same Linux gets installed package by package, although this might not possible for each distribution as a fault of their specific architectures (library-structure and so on).


 Instead the platform independent
Instead the platform independent 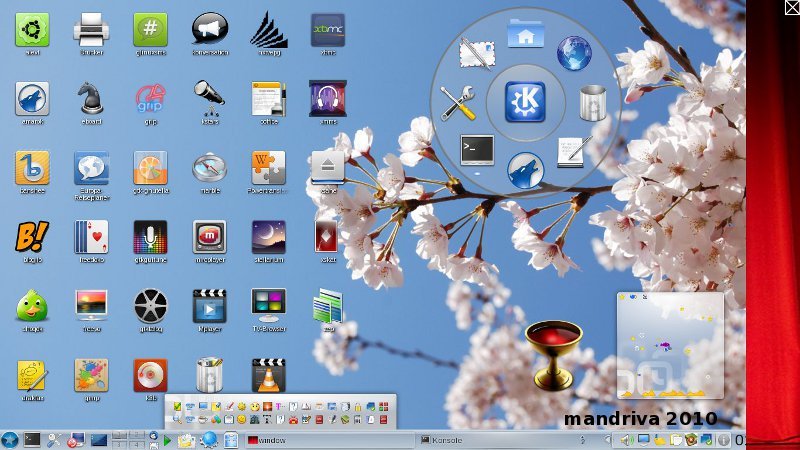



























 Cairo-Dock from http://fr2.rpmfind.net or http://www.glx-dock.org/
Cairo-Dock from http://fr2.rpmfind.net or http://www.glx-dock.org/
 Desktop-Screenlets, image: GUI-Screenlet-administration with more than 100 screenlets additionaly downloadable ones and screenlet-daemon, screenlet in the fore- and background, scalable size, widget-attribute, more attributes like: growing flower ( to give some water from time to time), slideshow, pager, control (to add more screenlets), radio, meter, stocks, speech, sensors, ringssensors, ruler, convert, example of howto create a screenlet, copystack, clear weather von weather.com, ...
Desktop-Screenlets, image: GUI-Screenlet-administration with more than 100 screenlets additionaly downloadable ones and screenlet-daemon, screenlet in the fore- and background, scalable size, widget-attribute, more attributes like: growing flower ( to give some water from time to time), slideshow, pager, control (to add more screenlets), radio, meter, stocks, speech, sensors, ringssensors, ruler, convert, example of howto create a screenlet, copystack, clear weather von weather.com, ...
 Mandriva Metisse takes 3D to a New Level, http://cybernetnews.com/mandriva-metisse-linux-takes-3d-to-a-new-level/
Mandriva Metisse takes 3D to a New Level, http://cybernetnews.com/mandriva-metisse-linux-takes-3d-to-a-new-level/ Abb.: System tray (plasmoid) out of Krandr (screen resolution), kmix, Klipper, parcellite (additional configuration of klipper), NetworkManager, Stardict, USB-connections and encrypted partitions, kgpg, korganizer (calender and. dating planner with reminder function), printer-applet (printer jobs), nepomuk (semantic search), i - information for system messages by kwrited (actually not started, that means still without: knotes or tomboy, tvbrowser, ...), clock with date and calendar and the fast screenlock- and poweron-off-plasmoid; enfastened load of the tray after the deinstallation of interfering draksnapshot
Abb.: System tray (plasmoid) out of Krandr (screen resolution), kmix, Klipper, parcellite (additional configuration of klipper), NetworkManager, Stardict, USB-connections and encrypted partitions, kgpg, korganizer (calender and. dating planner with reminder function), printer-applet (printer jobs), nepomuk (semantic search), i - information for system messages by kwrited (actually not started, that means still without: knotes or tomboy, tvbrowser, ...), clock with date and calendar and the fast screenlock- and poweron-off-plasmoid; enfastened load of the tray after the deinstallation of interfering draksnapshot
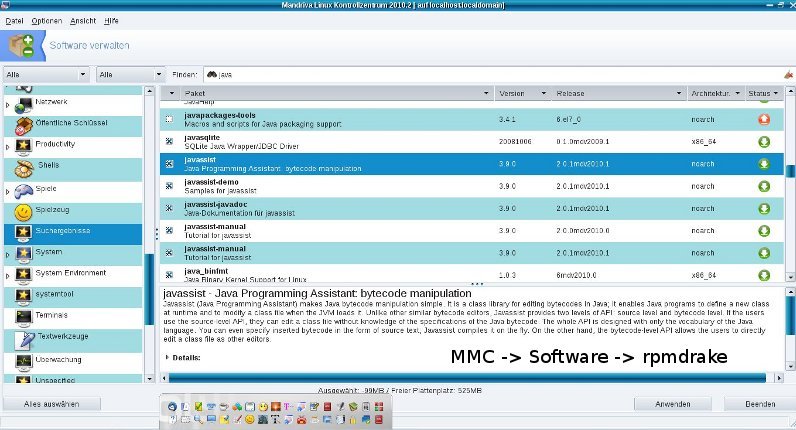
 proprietary software (opensource against liablity, more clearance of question about liablity), cost-traps (here: billing by handies and SMS, overread of additional parts of contracts and the conditions), blackmail for unlocking suddenly locked computers (see our report under links), abuse of copyrights and patents, cult for criminals, billions hard investment into spying software and techniques, missing, confusing or the fluctuating IT-security-concept, hard-disk-scans, defragmentation (unnecessary for many UNIX-file-systems), harddrives (instead of MC-SSD, cite: "A magentic harddrive is much to risky to intrust data. Although a lot of improvements took place, who has not heart or - in worst cases - made the experience of lost data. Therefore enough reasons are relevant." (source: poshtar@datensicherx.com, 13.05.2014)), the demand for a registry, registry-errors (UNIX-systems have no registry), degeneracy of the registry, suddenly or inpredictable lost files, explosion (of net-adapter), fire (net-adapter, porous PC-lautspeaker-cable, ...), your own ununderstandable blackened company (enlighted by our PHP-MySQL-company management Mycompanies), virtual blackmail by encrypting harddrives against ransom, shooting through unmanned flying objects as a technical response to stored data, kontermination (through chipsets, preventable by IGP and all-in-one-mainboards) and radiation, WLAN-radiation (see our linkside), CRT-radiation, CD-burner-radiation, netadapter-radiation, warning high SAR-value (handies), zero-emission (reflectable monitor emissionf or example by special PCMCIA-cards prevented by special editors like the zero emission pad), hardware-recognigtion (standarized driver, Kernel ver. greater 2.6.30), infiltration of social networks, handy-hunts through nets, inconsistency (vs. everlasting science), need for upgrades (new tarballs, zip-archives, functionality), updates, patches and bugfixes (vs. functionality), browser with outdated ssl3.0 (modern usage is provided by TLS), changeovers to different security software, missing changelogs, software-overload on harddisc (Opensource, independency-checks, other introduced methods), hacker (STATE-NEW lined iptables-blocking), large holes in firewalls (iptables block-rate), intrusion and valdalism, viruses (access-rights of UNIX-filesystems), freak (patch or prefer browsers like Firefox or Konqueor instead), abuse by virus scanner (standard opensource clamav), worms, rootkits (rkhunter) resp. botnets and trojans (no botnets and no trojans by correct usage of the OWNER-concept of iptables), manipulation by system-administrators upon software, files and configurations, ddos-attacks (almost on the base of bots and trojans), inactual alarms, false-alarms, forgotten or coded warnings and error-messages, ad- and spyware as much as Trackingscripts (firefox-addons), Driveby-Downloads, Canvas Fingerprinting (see under online check), forced acquisition because of truncated customer support for old operating systems (lifetime installation-support for all mdv/mdk over "pointed 1-" to "pointed 0" versions), product-manufacturing fault right on the surface of installation-CD/-DVD, aggressive marketing, need of updates and upgrades instead of functionality, unknown authors behind the named, burn-errors, problems with the BIOS and during the system-startup resp. boot, flush and reset, intransparent boot-processes, hard undestandable process-names (partial standarizement by UNIX/Linux), unmushed nets (failsafed mushed nets), video- and voice-recording, judge-microphons, observing satellite technique (see under links), spanish flies, night viewers, evaluation of such recordings (audit, protocolling files), text- and image-manipulation, manipulation of websits by webhoster, instability, system-breakdowns, broken USB-Sticks (secure umount and never before, fsck), usage of USB-hubs instead of prolonging USB-cables only, manipulated electric meter and cables (UPS: unbreakablel power supply), ineffective encryption through non scientific based cryptograhic methods from highschools, the search for important function-keys,iweak point human, insufficient set of (security-) system-commands, hangons and newstarts, anomal login attempts (LADS - login anomally detection system), inactual alarms and warnings, installation of malware by the opening of e-mail-attachements, unsigned installation from anywhere, installation by everyone, inportability, defect peripherals and hardware, restricted presentation of websides, keylogger and other malware, wiretrapping bedbugs (from USB-cards and other devices), hack of sensible data from USB-sticks through their microcontroller, crack of WLAN-encryption-keys, spy-nets, false email-sender-addresses (disabled browser-cache, header of email-source-text, digital signatures by public signature-keys, de-Mail), DoS-attacks, root-rights providing buffer-overflows (bugs),
proprietary software (opensource against liablity, more clearance of question about liablity), cost-traps (here: billing by handies and SMS, overread of additional parts of contracts and the conditions), blackmail for unlocking suddenly locked computers (see our report under links), abuse of copyrights and patents, cult for criminals, billions hard investment into spying software and techniques, missing, confusing or the fluctuating IT-security-concept, hard-disk-scans, defragmentation (unnecessary for many UNIX-file-systems), harddrives (instead of MC-SSD, cite: "A magentic harddrive is much to risky to intrust data. Although a lot of improvements took place, who has not heart or - in worst cases - made the experience of lost data. Therefore enough reasons are relevant." (source: poshtar@datensicherx.com, 13.05.2014)), the demand for a registry, registry-errors (UNIX-systems have no registry), degeneracy of the registry, suddenly or inpredictable lost files, explosion (of net-adapter), fire (net-adapter, porous PC-lautspeaker-cable, ...), your own ununderstandable blackened company (enlighted by our PHP-MySQL-company management Mycompanies), virtual blackmail by encrypting harddrives against ransom, shooting through unmanned flying objects as a technical response to stored data, kontermination (through chipsets, preventable by IGP and all-in-one-mainboards) and radiation, WLAN-radiation (see our linkside), CRT-radiation, CD-burner-radiation, netadapter-radiation, warning high SAR-value (handies), zero-emission (reflectable monitor emissionf or example by special PCMCIA-cards prevented by special editors like the zero emission pad), hardware-recognigtion (standarized driver, Kernel ver. greater 2.6.30), infiltration of social networks, handy-hunts through nets, inconsistency (vs. everlasting science), need for upgrades (new tarballs, zip-archives, functionality), updates, patches and bugfixes (vs. functionality), browser with outdated ssl3.0 (modern usage is provided by TLS), changeovers to different security software, missing changelogs, software-overload on harddisc (Opensource, independency-checks, other introduced methods), hacker (STATE-NEW lined iptables-blocking), large holes in firewalls (iptables block-rate), intrusion and valdalism, viruses (access-rights of UNIX-filesystems), freak (patch or prefer browsers like Firefox or Konqueor instead), abuse by virus scanner (standard opensource clamav), worms, rootkits (rkhunter) resp. botnets and trojans (no botnets and no trojans by correct usage of the OWNER-concept of iptables), manipulation by system-administrators upon software, files and configurations, ddos-attacks (almost on the base of bots and trojans), inactual alarms, false-alarms, forgotten or coded warnings and error-messages, ad- and spyware as much as Trackingscripts (firefox-addons), Driveby-Downloads, Canvas Fingerprinting (see under online check), forced acquisition because of truncated customer support for old operating systems (lifetime installation-support for all mdv/mdk over "pointed 1-" to "pointed 0" versions), product-manufacturing fault right on the surface of installation-CD/-DVD, aggressive marketing, need of updates and upgrades instead of functionality, unknown authors behind the named, burn-errors, problems with the BIOS and during the system-startup resp. boot, flush and reset, intransparent boot-processes, hard undestandable process-names (partial standarizement by UNIX/Linux), unmushed nets (failsafed mushed nets), video- and voice-recording, judge-microphons, observing satellite technique (see under links), spanish flies, night viewers, evaluation of such recordings (audit, protocolling files), text- and image-manipulation, manipulation of websits by webhoster, instability, system-breakdowns, broken USB-Sticks (secure umount and never before, fsck), usage of USB-hubs instead of prolonging USB-cables only, manipulated electric meter and cables (UPS: unbreakablel power supply), ineffective encryption through non scientific based cryptograhic methods from highschools, the search for important function-keys,iweak point human, insufficient set of (security-) system-commands, hangons and newstarts, anomal login attempts (LADS - login anomally detection system), inactual alarms and warnings, installation of malware by the opening of e-mail-attachements, unsigned installation from anywhere, installation by everyone, inportability, defect peripherals and hardware, restricted presentation of websides, keylogger and other malware, wiretrapping bedbugs (from USB-cards and other devices), hack of sensible data from USB-sticks through their microcontroller, crack of WLAN-encryption-keys, spy-nets, false email-sender-addresses (disabled browser-cache, header of email-source-text, digital signatures by public signature-keys, de-Mail), DoS-attacks, root-rights providing buffer-overflows (bugs),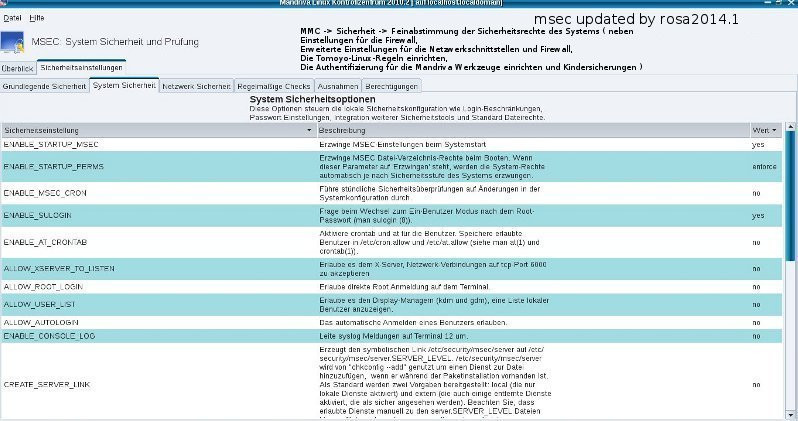
 the possibilities to build transparent rules, but you have to find out the correct or effective iptables-/ipchains from a set out of a lot of ineffective, bad structured or just false ones. Intelligent file systems like those for UNIX (resp. Linux) do not need any defragmentation as there are quit no fragments created, source. SuSE 7.3 reference manual. The same for SSD no defragmentation can be made for not having any read/write-heads.
the possibilities to build transparent rules, but you have to find out the correct or effective iptables-/ipchains from a set out of a lot of ineffective, bad structured or just false ones. Intelligent file systems like those for UNIX (resp. Linux) do not need any defragmentation as there are quit no fragments created, source. SuSE 7.3 reference manual. The same for SSD no defragmentation can be made for not having any read/write-heads.
